Risk reduction and recovery operations
Backing up data, log monitoring, and managing security updates
Abstract
Providing feedback on Red Hat documentation
We are committed to providing high-quality documentation and value your feedback. To help us improve, you can submit suggestions or report errors through the Red Hat Jira tracking system.
Procedure
Log in to the Jira website.
If you do not have an account, select the option to create one.
- Click Create in the top navigation bar.
- Enter a descriptive title in the Summary field.
- Enter your suggestion for improvement in the Description field. Include links to the relevant parts of the documentation.
- Click Create at the bottom of the window.
Chapter 1. Recovering and restoring a system
To back up and restore your system, Red Hat Enterprise Linux provides the Relax-and-Recover (ReaR) utility.
You can use ReaR as a disaster recovery solution and also for system migration.
By using ReaR, you can perform the following tasks:
- Produce a system backup and a bootable image, and use the image to restore the system from an existing backup.
- Replicate the original storage layout.
- Restore user and system files.
- Restore the system to different hardware.
Additionally, for disaster recovery, you can also integrate certain backup software with ReaR.
1.1. Setting up ReaR and manually creating a backup
To create a rescue system, first install the packages for the Relax-and-Recover (ReaR) utility, adjust ReaR settings, and manually generate a system backup. This prepares your system for potential disaster recovery operations.
Prerequisites
The necessary configurations based on your backup restore plan are ready.
NoteThe following steps use the
NETFSbackup method in example configurations. This method is fully-integrated and built-in with ReaR, and produces a backup in a location specified by theBACKUP_URLconfiguration setting. By default it uses the systemtarutility to create a backup archive namedbackup.tar.gz.You are using the Intel 64 or AMD64 (x86-64) hardware architecture, or the IBM POWER little-endian (ppc64le) architecture.
If you are using the IBM Z architecture, see Using a ReaR rescue image on the 64-bit IBM Z architecture.
On the 64-bit ARM architecture, ReaR is currently provided only as a Technology Preview.
Procedure
Install the ReaR utility:
# dnf install rearModify the ReaR configuration file in an editor of your choice, for example:
# vi /etc/rear/local.confAdd the backup setting details to
/etc/rear/local.conf. For example, in the case of theNETFSbackup method, add the following lines:BACKUP=NETFS OUTPUT=ISO BACKUP_URL=<data-backup-location> OUTPUT_URL=<rescue-image-location>Replace <data-backup-location> with the location for the
tardata backup, and <rescue-image-location> with the location for the rescue systemISOimage. For example:BACKUP=NETFS OUTPUT=ISO # Backup is stored on an external drive BACKUP_URL=file:///run/media/user/external_drive/server_backups/ # The ISO is stored on a dedicated NFS share OUTPUT_URL=nfs://backup-server.local/exports/rear/For further information on the syntax of the
/etc/rear/local.conffile and for supported formats ofBACKUP_URLandOUTPUT_URL, see therear(8)man page.For a list of configuration variables that you can use in
/etc/rear/local.conf, as well as their default values, see the/usr/share/rear/conf/default.conffile.To configure ReaR to keep the previous backup archive when the new one is created, also add the following line to the configuration file:
NETFS_KEEP_OLD_BACKUP_COPY=yTo make the backups incremental, meaning that only the changed files are backed up on each run, add the following line:
BACKUP_TYPE=incrementalIf you are planning to boot the ReaR rescue system on UEFI firmware, add the following line to ensure the boot does not fail:
SECURE_BOOT_BOOTLOADER=/boot/efi/EFI/redhat/shimx64.efi
Create a rescue system and data backup based on your restore plan. For example, when using the
NETFSbackup method, run the following command:# rear mkbackupIf your system is using the 64-bit ARM architecture (
aarch64), use the following line instead:SECURE_BOOT_BOOTLOADER=/boot/efi/EFI/redhat/shimaa64.efi-
If you need to create only the rescue system, use the
rear mkrescuecommand instead -
If you need to create only the data backup, use the
rear mkbackuponlycommand instead.
-
If you need to create only the rescue system, use the
Optional: Schedule regular automatic ReaR backup. You can use a variety of backup methods, based on your use case. For example:
Create a
/etc/cron.d/rearcrontab file, and add the following line:30 1 * * * /usr/sbin/rear mkbackupThis runs the the
rear mkbackupcommand at 1:30 AM every day, which creates a rescue system and a data backup in the location set up in the/etc/rear/local.conffile.- If you use an external backup method, schedule an external backup. The details depend on the backup method that you are using in ReaR.
Verification
Burn the ISO image of the rescue system to a DVD, and attempt to use the DVD to boot.
If this displays a Relax-and-Recover interface after booting, the rescue DVD works correctly.
- Use the ReaR interface to restore the system, and test that the restored system works.
1.2. Using a ReaR rescue image on the 64-bit IBM Z architecture
To quickly recover and restore systems running on the IBM Z architecture, you can use the Relax-and-Recover (ReaR) rescue image.
ReaR provides basic functionality on the 64-bit IBM Z architecture and is fully supported in RHEL 10. You can create a ReaR rescue image on IBM Z only in the z/VM environment. Backing up and recovering logical partitions (LPARs) is not supported.
The only output method currently available is Initial Program Load (IPL). IPL produces a kernel and an initial RAM disk (initrd) that can be used with the zipl boot loader.
Prerequisites
-
You installed the
rearpackage.
Procedure
Install ReaR:
# dnf install rearAdd the following variables to the
/etc/rear/local.conffile to configure ReaR for producing a rescue image on the 64-bit IBM Z architecture:-
To configure the
IPLoutput method, add the`OUTPUT=IPL` line to the configuration. To configure the backup method and destination, add
BACKUPandBACKUP_URLvariables. For example:BACKUP=NETFS BACKUP_URL=nfs://<nfsserver_name>/<share_path>ImportantLocal backup storage is currently not supported on the 64-bit IBM Z architecture.
-
Optional: You can also configure the
OUTPUT_URLvariable to save the kernel andinitrdfiles. By default, theOUTPUT_URLis aligned withBACKUP_URL.
-
To configure the
To perform backup and rescue image creation:
# rear mkbackupThis creates the kernel and initrd files at the location specified by the
BACKUP_URLorOUTPUT_URL(if set) variable, and a backup by using the specified backup method.WarningThe rescue process reformats all the DASDs (Direct Attached Storage Devices) connected to the system. Do not attempt a system recovery if there is any valuable data present on the system storage devices. This also includes the device prepared with the
ziplboot loader, ReaR kernel, andinitrdthat were used to boot into the rescue environment. Ensure to keep a copy.-
To recover the system, use the previously created ReaR kernel and
initrdfiles, and boot from a Direct Attached Storage Device (DASD) or a Fibre Channel Protocol (FCP)-attached SCSI device prepared with theziplboot loader, kernel, andinitrd. -
When the rescue kernel and
initrdare booted, the ReaR rescue environment starts. Proceed with system recovery.
Next steps
1.3. Recovering your system by using ReaR
To recover your RHEL system on new hardware after a failure of the current hardware, use the Relax-and-Recover (ReaR) utility.
Prerequisites
- You have set up ReaR and created a backup. For instructions, see Setting up ReaR and manually creating a backup.
- You have a set of working hardware on which you want to run the system after you recover it.
The hard disk on which you plan to recover your system does not contain any critical data.
ImportantRecovering a system on a hard disk by using ReaR erases all data currently stored on the disk.
Procedure
- Boot the rescue system on the new hardware. For example, you can burn the ISO image of the rescue system to a DVD, and boot from the DVD.
- In the Relax-and-Recover boot menu, select the option to boot to the recovery environment.
In the
RESCUEprompt, run therear recovercommand.The rescue system recreates the partition layout and file systems.
Restore user and system files from the data backup into the
/mnt/local/directory.For example, if you used the
NETFSmethod to create the backup, ReaR automatically performs the restoration process. However, based on your backup settings, ReaR might still require your confirmation in certain points of the restoration.
1.4. Modifying the content of the ReaR backup
When creating a rescue system and data backup by using the Relax-and-Recover (ReaR) utility, certain files and storage components are not included in the backups. To adjust what data and devices are excluded from the backups, modify ReaR configuration.
When creating the rescue image, ReaR creates the /var/lib/rear/layout/disklayout.conf layout file, and embeds the file in the rescue image.
During the recovery process, ReaR uses the layout file to recreate the storage layout of the original system, where the rescue image has been produced, on the disks of the recovered system. The storage layout includes partitions, volume groups, logical volumes, file systems, and other storage components.
Prerequisites
- You have set up ReaR on your system. For instructions, see Setting up ReaR and manually creating a backup.
Procedure
Generate the current layout file.
# rear savelayoutOpen the layout file to examine its configuration. For example:
# vi /var/lib/rear/layout/disklayout.confTo exclude specific files or storage devices from the backup, you can configure ReaR to ignore them when creating the rescue image.
Open the ReaR local configuration file for editing. For example:
# vi /etc/rear/local.confAdjust which storage devices will be excluded from the layout file. You can use a variety of
excludevariables in the/etc/rear/local.conffile, including the following:-
AUTOEXCLUDE_DISKS -
AUTOEXCLUDE_MULTIPATH -
AUTOEXCLUDE_PATH -
EXCLUDE_RECREATE
For information on the functions and syntax of these variables, as well as of the layout file, see the
Layout configurationchapter in the ReaR user guide. This guide is installed with therearpackage, and is available at/usr/share/doc/rear/user-guide/relax-and-recover-user-guide.html.-
By default, when a local disk-based file system is included in the layout file, all files on that file system are backed up when you use the
rear mkbackuporrear mkbackuponlycommands.To configure specific files or a directory tree to be excluded from the backup, use the
BACKUP_PROG_EXCLUDEvariable.The value of
BACKUP_PROG_EXCLUDEmust be an array of glob(3)-style wildcard patterns that tar or rsync uses. Note that you must quote the patterns in order to prevent their expansion by the shell when it reads the configuration file.The default value of this variable is set in the
/usr/share/rear/conf/default.conffile. The default value contains, for example, the/tmp/*pattern that excludes all the files and directories under the/tmpdirectory, but not the/tmpdirectory itself.If you need to exclude other files and directories, append further patterns to the variable. To ensure that the default values are preserved, do not override the variable.
For example, to exclude all files and directories under the directory
/data/temp, use:BACKUP_PROG_EXCLUDE+=( '/data/temp/*' )NoteWhen you exclude all files and directories in a single mounted file system this way, ReaR recreates the file system during recovery, but it will be empty. You can use this for file systems that contain temporary data and do not require preserving, or for data that is backed up by using methods independent of ReaR.
Verification
To ensure that the layout file includes only the required storage components, do the following:
Re-generate the layout file.
# rear savelayoutOpen the new layout file and make sure that your configuration changes had the intended effect.
# vi /var/lib/rear/layout/disklayout.conf
To ensure that the backup excludes specific files, use the
rear mkbackupcommand. This lists the backup exclude patterns in the log.You can find the log file in the
/var/log/reardirectory. Use this to verify the exclude rules before performing a full system recovery. For example, the log can contain the following entries:2025-04-29 10:17:41.312431050 Making backup (using backup method NETFS) 2025-04-29 10:17:41.314369109 Backup include list (backup-include.txt contents): 2025-04-29 10:17:41.316197323 / 2025-04-29 10:17:41.318052001 Backup exclude list (backup-exclude.txt contents): 2025-04-29 10:17:41.319857125 /tmp/* 2025-04-29 10:17:41.321644442 /dev/shm/* 2025-04-29 10:17:41.323436363 /var/lib/rear/output/*In this example, the entire root file system is included in the backup, with the exception of all files and directories under the
/tmp,/dev/shmand/var/lib/rear/outputdirectories.
Chapter 2. Troubleshooting problems by using log files
Use log files to troubleshoot and monitor the system. Log files contain messages about the system, kernel, services, and applications, recorded efficiently using the built-in syslog protocol.
2.1. Services that handle syslog messages
Identify the system services, such as rsyslogd and journald, that handle syslog messages. These services are crucial for capturing, processing, and storing all security-relevant system events.
The following services handle syslog messages:
- The
systemd-journalddaemon Collects messages from the following sources and forwards them to Rsyslog for further processing:
- Kernel
- Early stages of the boot process
- Standard and error output of daemons as they start and run
- Syslog
- The
rsyslogservice -
Sorts syslog messages by type and priority and writes them to the files in the
/var/logdirectory. The/var/logdirectory persistently stores the log messages.
2.2. Subdirectories that store syslog messages
Locate where system logging services store recorded syslog messages. Most log files are kept in the /var/log/ directory, often organized logically into subdirectories based on the application.
The following subdirectories under the /var/log directory store syslog messages:
- /var/log/messages
- all syslog messages except the following
- /var/log/secure
- security and authentication-related messages and errors
- /var/log/maillog
- mail server-related messages and errors
- /var/log/cron
- log files related to periodically executed tasks
- /var/log/boot.log
- log files related to system startup
2.3. Commands for viewing logs
You can view and manage log files by using the Journal, which is a component of systemd. It addresses problems connected with traditional logging, is closely integrated with the rest of the system, and supports various logging technologies and access management for the log files.
You can use the journalctl command to view messages in the system journal, for example:
$ journalctl -b | grep kvm
May 15 11:31:41 localhost.localdomain kernel: kvm-clock: Using msrs 4b564d01 and 4b564d00
May 15 11:31:41 localhost.localdomain kernel: kvm-clock: cpu 0, msr 76401001, primary cpu clock2.3.1. Viewing system information
journalctl- Shows all collected journal entries.
journalctl FILEPATH-
Shows logs related to a specific file. For example, the
journalctl /dev/sdacommand displays logs related to the/dev/sdafile system. journalctl -b- Shows logs for the current boot.
journalctl -k -b -1- Shows kernel logs for the current boot.
2.3.2. Viewing information about specific services
journalctl -b _SYSTEMD_UNIT=<name.service>-
Filters log to show entries matching the
systemdservice. journalctl -b _SYSTEMD_UNIT=<name.service> _PID=<number>-
Combines matches. For example, this command shows logs for
systemd-unitsthat match<name.service>and the PID<number>. journalctl -b _SYSTEMD_UNIT=<name.service> _PID=<number> + _SYSTEMD_UNIT=<name2.service>-
The plus sign (+) separator combines two expressions in a logical OR. For example, this command shows all messages from the
<name.service>service process with thePIDplus all messages from the<name2.service>service (from any of its processes). journalctl -b _SYSTEMD_UNIT=<name.service> _SYSTEMD_UNIT=<name2.service>-
This command shows all entries matching either expression, referring to the same field. Here, this command shows logs matching a systemd-unit
<name.service>or a systemd-unit<name2.service>.
Chapter 3. Reviewing and filtering logs in the web console
The Red Hat Enterprise Linux web console provides a graphical interface for accessing, reviewing, and filtering logs. You can use the most common functions without memorizing the corresponding commands and options.
3.1. Reviewing logs in the web console
You can quickly access and examine system logs by using the RHEL web console’s dedicated Logs section. This graphical interface helps centralize log monitoring for various system functions across the host and provides a UI for the journalctl utility.
Prerequisites
You have installed the RHEL 10 web console.
For instructions, see Installing and enabling the web console.
Procedure
- Log in to the RHEL 10 web console.
- Click Logs.
- Open log entry details by clicking on your selected log entry in the list.
Next steps
- After clicking to expand the menu, you can use the button to pause new log entries from appearing. Once you resume new log entries, the web console loads all log entries that are reported after you use the button.
- You can filter the logs by time, priority, or identifier. For more information, see Reviewing and filtering logs in the web console.
3.2. Filtering logs in the web console
You can filter system logs directly in the RHEL web console based on time range, priority, or specific identifiers. This capability helps administrators focus only on critical messages for targeted troubleshooting.
Prerequisites
You have installed the RHEL 10 web console.
For instructions, see Installing and enabling the web console.
Procedure
- Log in to the RHEL 10 web console.
- Click Logs.
- Click .
- To change the default log filtering, use the Time, Priority, and Identifier drop-down menus.
Optional: By default, the web console shows the latest log entries. To filter by a specific time range, click the button.

- Click the button (right pointing arrow) to apply your filters.
- To open a log entry, click the selected log entry.
3.3. Text search options for filtering logs in the web console
With the text search syntax and options available in the RHEL web console, you can filter logs effectively. This enables high precision when searching for specific errors or keywords across extensive system logs.
The text search option functionality provides a wide variety of options for filtering logs. If you decide to filter logs by using the text search, you can use the predefined options that are defined in the three drop-down menus, or you can type the whole search yourself.
- Drop-down menus
You can use three drop-down menus to specify the main parameters of your search:
- Time: This drop-down menu contains predefined searches for different time ranges of your search.
-
Priority: This drop-down menu provides options for different priority levels. It corresponds to the
journalctl --priorityoption. The default priority value is Error and above. It is set every time you do not specify any other priority. -
Identifier: In this drop-down menu, you can select an identifier that you want to filter. Corresponds to the
journalctl --identifieroption.
- Quantifiers
- You can use six quantifiers to specify your search. They are covered in the Options for filtering logs table.
- Log fields
- To search for a specific log field, you can specify the field together with its content.
- Free-form text search in log messages
- You can filter any text string of your choice in the log messages. The string can also be in the form of a regular expression.
Example 3.1. Logs filtering based on time
Filter all log messages identified by 'systemd' that happened since October 22, 2020 midnight and journal field 'JOB_TYPE' is either 'start' or 'restart.
-
Type
identifier:systemd since:2020-10-22 JOB_TYPE=start,restartto search field. Check the results.

Example 3.2. Logs containing error and fail messages
Filter all log messages that come from 'cockpit.service' systemd unit that happened in the boot before last and the message body contains either "error" or "fail".
-
Type
service:cockpit boot:-1 error|failto the search field. Check the results.

3.4. Using a text search box to filter logs in the web console
You can filter logs according to different parameters by using the text search box in the web console. The search combines the usage of the filtering drop-down menus, quantifiers, log fields, and free-form string search.
Prerequisites
You have installed the RHEL 10 web console.
For instructions, see Installing and enabling the web console.
Procedure
- Log in to the RHEL 10 web console.
- Click Logs.
Use the drop-down menus to specify the three main quantifiers - time range, priority, and identifier(s) - you want to filter.
The Priority quantifier must have a value. If you do not specify a value, it automatically filters the Error and above priority. The options you set reflect in the text search box.
Specify the log field you want to filter.
You can add several log fields.
- You can use a free-form string to search for anything else. The search box also accepts regular expressions.
3.5. Options for filtering logs
Review the various options available for filtering system logs in the RHEL web console. Options include time range, priority, identifier, and customized text search fields.
You can use journalctl options for filtering logs in the web console. Some of these options are provided as parts of the drop-down menus in the web console interface.
| Option name | Usage | Notes |
|---|---|---|
|
| Filters output by message priorities. Takes a single numeric or textual log level. The log levels are the usual syslog log levels. If a single log level is specified, all messages with this log level or a lower and more important log level are shown. | Covered in the Priority drop-down menu. |
|
| Shows messages for the specified syslog identifier SYSLOG_IDENTIFIER. Can be specified multiple times. | Covered in the Identifier drop-down menu. |
|
| Shows only the most recent journal entries, and continuously prints new entries as they are appended to the journal. | Not covered in a drop-down. |
|
|
Shows messages for the specified |
Is not covered in a drop-down. Corresponds to the |
|
| Shows messages from a specific boot. A positive integer looks up the boots starting from the beginning of the journal, and an equal-or-less-than-zero integer looks up boots starting from the end of the journal. Therefore, 1 means the first boot found in the journal in chronological order, 2 the second, and so on; while -0 is the last boot, -1 the boot before last, and so on. | Covered only as Current boot or Previous boot in the Time drop-down menu. You must specify other options manually. |
|
| Starts showing entries on or newer than the specified date, or on or older than the selected date. Date specifications should be of the format "2012-10-30 18:17:16". If the time part is omitted, "00:00:00" is considered. If only the seconds component is omitted, ":00" is assumed. If the date component is omitted, the current day is assumed. Alternatively, the strings "yesterday", "today", "tomorrow" are understood, which refer to 00:00:00 of the day before the current day, the current day, or the day after the current day. "now" refers to the current time. Finally, relative times might be specified, prefixed with "-" or "+", referring to times before or after the current time. | Not covered in a drop-down. |
Chapter 4. Configuring the systemd journal by using RHEL system roles
With the journald RHEL system role you can automate the systemd journal, and configure persistent logging by using the Red Hat Ansible Automation Platform.
4.1. Configuring persistent logging by using the journald RHEL system role
By default, the systemd journal stores logs only in a small ring buffer in /run/log/journal, which is not persistent. Rebooting the system also removes journal database logs. You can configure persistent logging consistently on multiple systems by using the journald RHEL system role.
Prerequisites
- You have prepared the control node and the managed nodes.
- You are logged in to the control node as a user who can run playbooks on the managed nodes.
-
The account you use to connect to the managed nodes has
sudopermissions for these nodes.
Procedure
Create a playbook file, for example,
~/playbook.yml, with the following content:--- - name: Configure journald hosts: managed-node-01.example.com tasks: - name: Configure persistent logging ansible.builtin.include_role: name: redhat.rhel_system_roles.journald vars: journald_persistent: true journald_max_disk_size: <size> journald_per_user: true journald_sync_interval: <interval>The settings specified in the example playbook include the following:
journald_persistent: true- Enables persistent logging.
journald_max_disk_size: <size>-
Specifies the maximum size of disk space for journal files in MB, for example,
2048. journald_per_user: true-
Configures
journaldto keep log data separate for each user. journald_sync_interval: <interval>Sets the synchronization interval in minutes, for example,
1.For details about all variables used in the playbook, see the
/usr/share/ansible/roles/rhel-system-roles.journald/README.mdfile on the control node.
Validate the playbook syntax:
$ ansible-playbook --syntax-check ~/playbook.ymlNote that this command only validates the syntax and does not protect against a wrong but valid configuration.
Run the playbook:
$ ansible-playbook ~/playbook.yml
Chapter 5. Configuring a remote logging solution
Ensure that logs from various machines in your environment are recorded centrally on a logging server. You can configure the Rsyslog application to forward logs that meet specific criteria from client systems to the server.
5.1. The Rsyslog logging service
The Rsyslog logging service defines rules in the /etc/rsyslog.conf file. Rules classify messages by urgency and topic, determining the action Rsyslog performs.
The Rsyslog application, in combination with the systemd-journald service, provides local and remote logging support in Red Hat Enterprise Linux. The rsyslogd daemon continuously reads syslog messages received by the systemd-journald service from the Journal. rsyslogd then filters and processes these syslog events and records them to rsyslog log files or forwards them to other services according to its configuration.
The rsyslogd daemon also provides extended filtering, encryption-protected relaying of messages, input and output modules, and support for transport that uses the TCP and UDP protocols.
In /etc/rsyslog.conf, which is the main configuration file for rsyslog, you can specify the rules according to which rsyslogd handles the messages. Generally, you can classify messages by their source and topic (facility) and urgency (priority), and then assign an action that should be performed when a message fits these criteria.
In /etc/rsyslog.conf, you can also see a list of log files maintained by rsyslogd. Most log files are located in the /var/log/ directory. Some applications, such as httpd and samba, store their log files in a subdirectory within /var/log/.
For more information, see the rsyslogd(8) and rsyslog.conf(5) man pages on your system. You can also refer to the comprehensive documentation installed with the rsyslog-doc package in the /usr/share/doc/rsyslog/html/index.html file.
5.2. Installing Rsyslog documentation
Install the rsyslog-doc documentation package locally. This provides quick, offline access to the extensive documentation for the Rsyslog application, complementing the online resources.
The Rsyslog application has extensive online documentation that is available at https://www.rsyslog.com/doc/, but you can also install the rsyslog-doc documentation package on your system.
Prerequisites
-
You have activated the
AppStreamrepository on your system. -
You are authorized to install new packages using
sudo.
Procedure
Install the
rsyslog-docpackage:# dnf install rsyslog-doc
Verification
Open the
/usr/share/doc/rsyslog/html/index.htmlfile in a browser of your choice, for example:$ firefox /usr/share/doc/rsyslog/html/index.html &
5.3. Configuring a server for remote logging over TCP
Configure your Rsyslog server to receive remote logs through the reliable TCP protocol. This setup helps ensure high integrity when transferring logs from client systems over the network.
To use remote logging through TCP, configure both the server and the client. The server collects and analyzes the logs sent by one or more client systems.
With the Rsyslog application, you can maintain a centralized logging system where log messages are forwarded to a server over the network. To avoid message loss when the server is not available, you can configure an action queue for the forwarding action. This way, messages that failed to be sent are stored locally until the server is reachable again. Note that such queues cannot be configured for connections that use the UDP protocol.
The omfwd plugin provides forwarding over UDP or TCP. The default protocol is UDP. Because the plugin is built-in, it does not have to be loaded.
By default, rsyslog uses TCP on port 514.
Prerequisites
- Rsyslog is installed on the server system.
-
You are logged in as
rooton the server. -
The
policycoreutils-python-utilspackage is installed for the optional step using thesemanagecommand. -
The
firewalldservice is running.
Procedure
Optional: To use a different port for
rsyslogtraffic, add thesyslogd_port_tSELinux type to port. For example, enable port30514:# semanage port -a -t syslogd_port_t -p tcp 30514Optional: To use a different port for
rsyslogtraffic, configurefirewalldto allow incomingrsyslogtraffic on that port. For example, allow TCP traffic on port30514:# firewall-cmd --zone=<zone_name> --permanent --add-port=30514/tcp success # firewall-cmd --reloadCreate a new file in the
/etc/rsyslog.d/directory named, for example,remotelog.conf, and insert the following content:# Define templates before the rules that use them # Per-Host templates for remote systems template(name="TmplAuthpriv" type="list") { constant(value="/var/log/remote/auth/") property(name="hostname") constant(value="/") property(name="programname" SecurePath="replace") constant(value=".log") } template(name="TmplMsg" type="list") { constant(value="/var/log/remote/msg/") property(name="hostname") constant(value="/") property(name="programname" SecurePath="replace") constant(value=".log") } # Provides TCP syslog reception module(load="imtcp") # Adding this ruleset to process remote messages ruleset(name="remote1"){ authpriv.* action(type="omfile" DynaFile="TmplAuthpriv") *.info;mail.none;authpriv.none;cron.none action(type="omfile" DynaFile="TmplMsg") } input(type="imtcp" port="30514" ruleset="remote1")-
Save the changes to the
/etc/rsyslog.d/remotelog.conffile. Test the syntax of the
/etc/rsyslog.conffile:# rsyslogd -N 1 rsyslogd: version 8.1911.0-2.el8, config validation run... rsyslogd: End of config validation run. Bye.Make sure the
rsyslogservice is running and enabled on the logging server:# systemctl status rsyslogRestart the
rsyslogservice.# systemctl restart rsyslogOptional: If
rsyslogis not enabled, ensure thersyslogservice starts automatically after reboot:# systemctl enable rsyslog
5.4. Configuring remote logging to a server over TCP
You can configure a system for forwarding log messages to a server over the TCP protocol. The omfwd plugin provides forwarding over UDP or TCP. The default protocol is UDP. Because the plugin is built in, you do not have to load it.
Prerequisites
-
The
rsyslogpackage is installed on the client systems that should report to the server. - You have configured the server for remote logging.
- The specified port is permitted in SELinux and open in firewall.
-
The system contains the
policycoreutils-python-utilspackage, which provides thesemanagecommand for adding a non-standard port to the SELinux configuration.
Procedure
Create a new file in the
/etc/rsyslog.d/directory named, for example,10-remotelog.conf, and insert the following content:*.* action(type="omfwd" queue.type="linkedlist" queue.filename="example_fwd" action.resumeRetryCount="-1" queue.saveOnShutdown="on" target="example.com" port="30514" protocol="tcp" )Where:
-
The
queue.type="linkedlist"setting enables a LinkedList in-memory queue, -
The
queue.filenamesetting defines a disk storage. The backup files are created with theexample_fwdprefix in the working directory specified by the preceding globalworkDirectorydirective. -
The
action.resumeRetryCount -1setting preventsrsyslogfrom dropping messages when retrying to connect if server is not responding, -
The
queue.saveOnShutdown="on"setting saves in-memory data ifrsyslogshuts down. The last line forwards all received messages to the logging server. Port specification is optional.
With this configuration,
rsyslogsends messages to the server but keeps messages in memory if the remote server is not reachable. A file on disk is created only ifrsyslogruns out of the configured memory queue space or needs to shut down, which benefits the system performance.NoteRsyslog processes configuration files
/etc/rsyslog.d/in the lexical order.
-
The
Restart the
rsyslogservice.# systemctl restart rsyslog
Verification
To verify that the client system sends messages to the server:
On the client system, send a test message:
# logger testOn the server system, view the
/var/log/messageslog, for example:# cat /var/log/remote/msg/hostname/root.log Feb 25 03:53:17 hostname root[6064]: testWhere hostname is the hostname of the client system. Note that the log contains the user name of the user that entered the
loggercommand, in this caseroot.
5.5. Configuring TLS-encrypted remote logging
Encrypt remote logging communication by using TLS to secure the data transfer. Configuring TLS on both the server and the client helps protect sensitive logs from network interception.
By default, Rsyslog sends remote logging messages in plain text. To use encrypted transport through TLS, configure both the server and the client. The server collects and analyzes the logs sent by one or more client systems.
You can use either the ossl network stream driver (OpenSSL) or the gtls stream driver (GnuTLS).
If you have a separate system with higher security, for example, a system that is not connected to any network or has stricter authorizations, use the separate system as the certifying authority (CA).
You can customize your connection settings with stream drivers on the server side on the global, module, and input levels, and on the client side on the global and action levels. The more specific configuration overrides the more general configuration. This means, for example, that you can use ossl in global settings for most connections and gtls on the input and action settings only for specific connections.
Prerequisites
-
You have
rootaccess to both the client and server systems. The following packages are installed on the server and the client systems:
-
The
rsyslogpackage. -
For the
osslnetwork stream driver, thersyslog-opensslpackage. -
For the
gtlsnetwork stream driver, thersyslog-gnutlspackage. -
For generating certificates by using the
certtoolcommand, thegnutls-utilspackage.
-
The
On your logging server, the following certificates are in the
/etc/pki/ca-trust/source/anchors/directory, and your system configuration is updated by using theupdate-ca-trustcommand:-
ca-cert.pem- a CA certificate that can verify keys and certificates on logging servers and clients. -
server-cert.pem- a public key of the logging server. -
server-key.pem- a private key of the logging server.
-
On your logging clients, the following certificates are in the
/etc/pki/ca-trust/source/anchors/directory, and your system configuration is updated by usingupdate-ca-trust:-
ca-cert.pem- a CA certificate that can verify keys and certificates on logging servers and clients. -
client-cert.pem- a public key of a client. -
client-key.pem- a private key of a client. - If the server runs RHEL 9.2 or later and FIPS mode is enabled, clients must either support the Extended Master Secret (EMS) extension or use TLS 1.3. TLS 1.2 connections without EMS fail. For more information, see the TLS extension "Extended Master Secret" enforced article (Red Hat Knowledgebase).
-
Procedure
Configure the server for receiving encrypted logs from your client systems:
-
Create a new file in the
/etc/rsyslog.d/directory named, for example,securelogser.conf. To encrypt the communication, the configuration file must contain paths to certificate files on your server, a selected authentication method, and a stream driver that supports TLS encryption. Add the following lines to the
/etc/rsyslog.d/securelogser.conffile:# Set certificate files global( DefaultNetstreamDriverCAFile="/etc/pki/ca-trust/source/anchors/ca-cert.pem" DefaultNetstreamDriverCertFile="/etc/pki/ca-trust/source/anchors/server-cert.pem" DefaultNetstreamDriverKeyFile="/etc/pki/ca-trust/source/anchors/server-key.pem" ) # TCP listener module( load="imtcp" PermittedPeer=["client1.example.com", "client2.example.com"] StreamDriver.AuthMode="x509/name" StreamDriver.Mode="1" StreamDriver.Name="ossl" ) # Start up listener at port 514 input( type="imtcp" port="514" )NoteIf you prefer the GnuTLS driver, use the
StreamDriver.Name="gtls"configuration option. See the documentation installed with thersyslog-docpackage for more information about less strict authentication modes thanx509/name.Optional: To customize the connection configuration, replace the
inputsection with the following:input( type="imtcp" Port="50515" StreamDriver.Name="<driver>" streamdriver.CAFile="/etc/rsyslog.d/<ca1>.pem" streamdriver.CertFile="/etc/rsyslog.d/<server1_cert>.pem" streamdriver.KeyFile="/etc/rsyslog.d/<server1_key>.pem" )-
Replace
<driver>withosslorgtlsdepending on the driver you want to use. -
Replace
<ca1>with the CA certificate,<server1_cert>with the certificate, and<server1_key>with the key of the customized connection.
-
Replace
-
Save the changes to the
/etc/rsyslog.d/securelogser.conffile. Verify the syntax of the
/etc/rsyslog.conffile and any files in the/etc/rsyslog.d/directory:# rsyslogd -N 1 rsyslogd: version 8.1911.0-2.el8, config validation run (level 1)... rsyslogd: End of config validation run. Bye.Make sure the
rsyslogservice is running and enabled on the logging server:# systemctl status rsyslogRestart the
rsyslogservice:# systemctl restart rsyslogOptional: If Rsyslog is not enabled, ensure the
rsyslogservice starts automatically after reboot:# systemctl enable rsyslog
-
Create a new file in the
Configure clients for sending encrypted logs to the server:
-
On a client system, create a new file in the
/etc/rsyslog.d/directory named, for example,securelogcli.conf. Add the following lines to the
/etc/rsyslog.d/securelogcli.conffile:# Set certificate files global( DefaultNetstreamDriverCAFile="/etc/pki/ca-trust/source/anchors/ca-cert.pem" DefaultNetstreamDriverCertFile="/etc/pki/ca-trust/source/anchors/client-cert.pem" DefaultNetstreamDriverKeyFile="/etc/pki/ca-trust/source/anchors/client-key.pem" ) # Set up the action for all messages *.* action( type="omfwd" StreamDriver="ossl" StreamDriverMode="1" StreamDriverPermittedPeers="server.example.com" StreamDriverAuthMode="x509/name" target="server.example.com" port="514" protocol="tcp" )NoteIf you prefer the GnuTLS driver, use the
StreamDriver.Name="gtls"configuration option.Optional: To customize the connection configuration, replace the
actionsection with the following:local1.* action( type="omfwd" StreamDriver="<driver>" StreamDriverMode="1" StreamDriverAuthMode="x509/certvalid" streamDriver.CAFile="/etc/rsyslog.d/<ca1>.pem" streamDriver.CertFile="/etc/rsyslog.d/<client1_cert>.pem" streamDriver.KeyFile="/etc/rsyslog.d/<client1_key>.pem" target="server.example.com" port="514" protocol="tcp" )-
Replace
<driver>withosslorgtlsdepending on the driver you want to use. -
Replace
<ca1>with the CA certificate,<client1_cert>with the certificate, and<client1_key>with the key of the customized connection.
-
Replace
-
Save the changes to the
/etc/rsyslog.d/securelogcli.conffile. Verify the syntax of the
/etc/rsyslog.conffile and other files in the/etc/rsyslog.d/directory:# rsyslogd -N 1 rsyslogd: version 8.1911.0-2.el8, config validation run (level 1)... rsyslogd: End of config validation run. Bye.Make sure the
rsyslogservice is running and enabled on the logging server:# systemctl status rsyslogRestart the
rsyslogservice:# systemctl restart rsyslogOptional: If Rsyslog is not enabled, ensure the
rsyslogservice starts automatically after reboot:# systemctl enable rsyslog
-
On a client system, create a new file in the
Verification
To verify that the client system sends messages to the server:
On the client system, send a test message:
# logger testOn the server system, view the
/var/log/messageslog, for example:# cat /var/log/remote/msg/<hostname>/root.log Feb 25 03:53:17 <hostname> root[6064]: testWhere
<hostname>is the hostname of the client system. Note that the log contains the user name of the user who entered the logger command, in this case,root.
5.6. Configuring a server for receiving remote logging information over UDP
Configure the Rsyslog server to receive remote logs through the high-speed UDP protocol. UDP is suitable when log loss is acceptable, offering faster transmission than TCP.
To use remote logging through UDP, configure both the server and the client. The receiving server collects and analyzes the logs sent by one or more client systems. By default, rsyslog uses UDP on port 514 to receive log information from remote systems.
Prerequisites
- Rsyslog is installed on the server system.
-
You are logged in as
rooton the server. -
The
policycoreutils-python-utilspackage is installed for the optional step that uses thesemanagecommand. -
The
firewalldservice is running.
Procedure
Optional: To use a different port for
rsyslogtraffic than the default port514:Add the
syslogd_port_tSELinux type to the SELinux policy configuration, replacingportnowith the port number you wantrsyslogto use:# semanage port -a -t syslogd_port_t -p udp portnoConfigure
firewalldto allow incomingrsyslogtraffic, replacingportnowith the port number andzonewith the zone you wantrsyslogto use:# firewall-cmd --zone=zone --permanent --add-port=portno/udp success # firewall-cmd --reloadReload the firewall rules:
# firewall-cmd --reload
Create a new
.conffile in the/etc/rsyslog.d/directory, for example,remotelogserv.conf, and insert the following content:# Define templates before the rules that use them # Per-Host templates for remote systems template(name="TmplAuthpriv" type="list") { constant(value="/var/log/remote/auth/") property(name="hostname") constant(value="/") property(name="programname" SecurePath="replace") constant(value=".log") } template(name="TmplMsg" type="list") { constant(value="/var/log/remote/msg/") property(name="hostname") constant(value="/") property(name="programname" SecurePath="replace") constant(value=".log") } # Provides UDP syslog reception module(load="imudp") # This ruleset processes remote messages ruleset(name="remote1"){ authpriv.* action(type="omfile" DynaFile="TmplAuthpriv") *.info;mail.none;authpriv.none;cron.none action(type="omfile" DynaFile="TmplMsg") } input(type="imudp" port="514" ruleset="remote1")Where
514is the port numberrsysloguses by default. You can specify a different port instead.Verify the syntax of the
/etc/rsyslog.conffile and all.conffiles in the/etc/rsyslog.d/directory:# rsyslogd -N 1 rsyslogd: version 8.1911.0-2.el8, config validation run...Restart the
rsyslogservice.# systemctl restart rsyslogOptional: If
rsyslogis not enabled, ensure thersyslogservice starts automatically after reboot:# systemctl enable rsyslog
5.7. Configuring remote logging to a server over UDP
Configure a client system to send its logs to a remote server by using the UDP protocol. UDP is preferred when speed is critical and the occasional loss of a log message is acceptable.
The omfwd plugin provides forwarding over UDP or TCP. The default protocol is UDP. Because the plugin is built in, you do not have to load it.
Prerequisites
-
The
rsyslogpackage is installed on the client systems that should report to the server. - You have configured the server for remote logging as described in Configuring a server for receiving remote logging information over UDP.
Procedure
Create a new
.conffile in the/etc/rsyslog.d/directory, for example,10-remotelogcli.conf, and insert the following content:*.* action(type="omfwd" queue.type="linkedlist" queue.filename="example_fwd" action.resumeRetryCount="-1" queue.saveOnShutdown="on" target="example.com" port="portno" protocol="udp" )Where:
-
The
queue.type="linkedlist"setting enables a LinkedList in-memory queue. -
The
queue.filenamesetting defines a disk storage. The backup files are created with theexample_fwdprefix in the working directory specified by the preceding globalworkDirectorydirective. -
The
action.resumeRetryCount -1setting preventsrsyslogfrom dropping messages when retrying to connect if the server is not responding. -
The
enabled queue.saveOnShutdown="on"setting saves in-memory data ifrsyslogshuts down. -
The
portnovalue is the port number you wantrsyslogto use. The default value is514. The last line forwards all received messages to the logging server, port specification is optional.
With this configuration,
rsyslogsends messages to the server but keeps messages in memory if the remote server is not reachable. A file on disk is created only ifrsyslogruns out of the configured memory queue space or needs to shut down, which benefits the system performance.
NoteRsyslog processes configuration files
/etc/rsyslog.d/in the lexical order.-
The
Restart the
rsyslogservice.# systemctl restart rsyslogOptional: If
rsyslogis not enabled, ensure thersyslogservice starts automatically after reboot:# systemctl enable rsyslog
Verification
To verify that the client system sends messages to the server, follow these steps:
On the client system, send a test message:
# logger testOn the server system, view the
/var/log/remote/msg/hostname/root.loglog, for example:# cat /var/log/remote/msg/hostname/root.log Feb 25 03:53:17 hostname root[6064]: testWhere
hostnameis the hostname of the client system. Note that the log contains the user name of the user that entered the logger command, in this caseroot.
5.8. Load balancing helper in Rsyslog
Configure the load balancing helper in Rsyslog to distribute log traffic across multiple remote logging servers. This improves system resilience and prevents any single server from becoming overwhelmed.
When used in a cluster, you can improve Rsyslog load balancing by modifying the RebindInterval setting. This option specifies an interval at which the current connection is broken and is re-established. This setting applies to TCP, UDP, and RELP traffic. The load balancers perceive it as a new connection and forward the messages to another physical target system.
You can use RebindInterval in scenarios when a target system changes its IP address. The Rsyslog application caches the IP address when the connection is established. Therefore, the messages are sent to the same server. If the IP address changes, the UDP packets are lost until the Rsyslog service restarts. Re-establishing the connection ensures that the IP is resolved by DNS again.
Example 5.1. Usage of RebindInterval for TCP, UDP, and RELP traffic
action(type="omfwd" protocol="tcp" RebindInterval="250" target="example.com" port="514" …)
action(type="omfwd" protocol="udp" RebindInterval="250" target="example.com" port="514" …)
action(type="omrelp" RebindInterval="250" target="example.com" port="6514" …)5.9. Configuring reliable remote logging
Configure reliable remote logging with the Reliable Event Logging Protocol (RELP). This helps guarantee that log messages reach the central server, preventing data loss even during network outages.
With RELP, you can send and receive syslog messages over TCP with a much reduced risk of message loss. RELP reliably delivers event messages, making it useful in environments where message loss is not acceptable. To use RELP, configure the imrelp input module, which runs on the server and receives the logs, and the omrelp output module, which runs on the client and sends logs to the logging server.
Prerequisites
-
You have installed the
rsyslog,librelp, andrsyslog-relppackages on the server and the client systems. - The specified port is permitted in SELinux and open in the firewall.
Procedure
Configure the client system for reliable remote logging:
On the client system, create a new
.conffile in the/etc/rsyslog.d/directory named, for example,relpclient.conf, and insert the following content:module(load="omrelp") *.* action(type="omrelp" target="_target_IP_" port="_target_port_")Where:
-
target_IPis the IP address of the logging server. -
target_portis the port of the logging server.
-
-
Save the changes to the
/etc/rsyslog.d/relpclient.conffile. Restart the
rsyslogservice.# systemctl restart rsyslogOptional: If
rsyslogis not enabled, ensure thersyslogservice starts automatically after reboot:# systemctl enable rsyslog
Configure the server system for reliable remote logging:
On the server system, create a new
.conffile in the/etc/rsyslog.d/directory named, for example,relpserv.conf, and insert the following content:ruleset(name="relp"){ *.* action(type="omfile" file="_log_path_") } module(load="imrelp") input(type="imrelp" port="_target_port_" ruleset="relp")Where:
-
log_pathspecifies the path for storing messages. -
target_portis the port of the logging server. Use the same value as in the client configuration file.
-
-
Save the changes to the
/etc/rsyslog.d/relpserv.conffile. Restart the
rsyslogservice.# systemctl restart rsyslogOptional: If
rsyslogis not enabled, ensure thersyslogservice starts automatically after reboot:# systemctl enable rsyslog
Verification
To verify that the client system sends messages to the server:
On the client system, send a test message:
# logger testOn the server system, view the log at the specified
log_path, for example:# cat /var/log/remote/msg/hostname/root.log Feb 25 03:53:17 hostname root[6064]: testWhere
hostnameis the hostname of the client system. Note that the log contains the user name of the user who entered the logger command, in this case,root.
5.10. Supported Rsyslog modules
Extend Rsyslog functionality by using specific modules that provide additional input, output, or configuration directives that become available after you load the module. These modules customize how the application processes and handles log messages efficiently.
You can list the input and output modules installed on your system by entering the following command:
# ls /usr/lib64/rsyslog/{i,o}m*
You can view the list of all available rsyslog modules in the /usr/share/doc/rsyslog/html/configuration/modules/idx_output.html file after you install the rsyslog-doc package.
5.11. Configuring Netconsole to log kernel messages to a remote host
Configure the netconsole service to forward kernel messages to a remote host. This helps capture critical kernel events, especially when the local system logging functions have failed.
When logging to disk or using a serial console is not possible, you can use the netconsole kernel module and the same-named service to log kernel messages over a network to a remote rsyslog service.
Prerequisites
- A system log service, such as Rsyslog is installed on the remote host.
- The remote system log service is configured to receive incoming log entries from this host.
Procedure
Install the
netconsole-servicepackage:# dnf install netconsole-serviceEdit the
/etc/sysconfig/netconsolefile and set theSYSLOGADDRparameter to the IP address of the remote host:# SYSLOGADDR=192.0.2.1Enable and start the
netconsoleservice:# systemctl enable --now netconsole
Verification
-
Display the
/var/log/messagesfile on the remote system log server.
Chapter 6. Configuring logging by using RHEL system roles
You can use the logging RHEL system role to configure your local and remote hosts as logging servers in an automated fashion to collect logs from many client systems.
Logging solutions provide multiple ways of reading logs and multiple logging outputs.
For example, a logging system can receive the following inputs:
- Local files
-
systemd/journal - Another logging system over the network
In addition, a logging system can have the following outputs:
-
Logs stored in the local files in the
/var/log/directory - Logs sent to Elasticsearch engine
- Logs forwarded to another logging system
With the logging RHEL system role, you can combine the inputs and outputs to fit your scenario. For example, you can configure a logging solution that stores inputs from journald in a local file, whereas inputs read from files are both forwarded to another logging system and stored in the local log files.
6.1. Filtering local log messages by using the logging RHEL system role
You can use the property-based filter of the logging RHEL system role to filter your local log messages based on various conditions.
You can achieve, for example:
- Log clarity: In a high-traffic environment, logs can grow rapidly. The focus on specific messages, like errors, can help to identify problems faster.
- Optimized system performance: Excessive amount of logs is usually connected with system performance degradation. Selective logging for only the important events can prevent resource depletion, which enables your systems to run more efficiently.
- Enhanced security: Efficient filtering through security messages, like system errors and failed logins, helps to capture only the relevant logs. This is important for detecting breaches and meeting compliance standards.
Prerequisites
- You have prepared the control node and the managed nodes.
- You are logged in to the control node as a user who can run playbooks on the managed nodes.
-
The account you use to connect to the managed nodes has
sudopermissions for these nodes.
Procedure
Create a playbook file, for example,
~/playbook.yml, with the following content:--- - name: Deploy the logging solution hosts: managed-node-01.example.com tasks: - name: Filter logs based on a specific value they contain ansible.builtin.include_role: name: redhat.rhel_system_roles.logging vars: logging_inputs: - name: files_input type: basics logging_outputs: - name: files_output0 type: files property: msg property_op: contains property_value: error path: /var/log/errors.log - name: files_output1 type: files property: msg property_op: "!contains" property_value: error path: /var/log/others.log logging_flows: - name: flow0 inputs: [files_input] outputs: [files_output0, files_output1]The settings specified in the example playbook include the following:
logging_inputs-
Defines a list of logging input dictionaries. The
type: basicsoption covers inputs fromsystemdjournal or Unix socket. logging_outputs-
Defines a list of logging output dictionaries. The
type: filesoption supports storing logs in the local files, usually in the/var/log/directory. Theproperty: msg;property: contains; andproperty_value: erroroptions specify that all logs that contain theerrorstring are stored in the/var/log/errors.logfile. Theproperty: msg;property: !contains; andproperty_value: erroroptions specify that all other logs are put in the/var/log/others.logfile. You can replace theerrorvalue with the string by which you want to filter. logging_flows-
Defines a list of logging flow dictionaries to specify relationships between
logging_inputsandlogging_outputs. Theinputs: [files_input]option specifies a list of inputs, from which processing of logs starts. Theoutputs: [files_output0, files_output1]option specifies a list of outputs, to which the logs are sent.
For details about all variables used in the playbook and more information about
rsyslog, see the/usr/share/ansible/roles/rhel-system-roles.logging/README.mdfile andrsyslog.conf(5)andsyslog(3)manual pages on the control node.Validate the playbook syntax:
$ ansible-playbook --syntax-check ~/playbook.ymlNote that this command only validates the syntax and does not protect against a wrong but valid configuration.
Run the playbook:
$ ansible-playbook ~/playbook.yml
Verification
On the managed node, test the syntax of the
/etc/rsyslog.conffile:# rsyslogd -N 1 rsyslogd: version 8.1911.0-6.el8, config validation run... rsyslogd: End of config validation run. Bye.On the managed node, verify that the system sends messages that contain the
errorstring to the log:Send a test message:
# logger errorView the
/var/log/errors.loglog, for example:# cat /var/log/errors.log Aug 5 13:48:31 hostname root[6778]: errorWhere
hostnameis the host name of the client system. Note that the log contains the user name of the user that entered the logger command, in this caseroot.
6.2. Applying a remote logging solution by using the logging RHEL system role
You can use the logging RHEL system role to configure centralized log management across multiple systems. The server receives remote input from the remote_rsyslog and remote_files configurations, and outputs the logs to local files in directories named by remote host names.
As a result, you can cover use cases where you need for example:
- Centralized log management: Collecting, accessing, and managing log messages of multiple machines from a single storage point simplifies day-to-day monitoring and troubleshooting tasks. Also, this use case reduces the need to log in to individual machines to check the log messages.
- Enhanced security: Storing log messages in one central place increases chances they are in a secure and tamper-proof environment. Such an environment makes it easier to detect and respond to security incidents more effectively and to meet audit requirements.
- Improved efficiency in log analysis: Correlating log messages from multiple systems is important for fast troubleshooting of complex problems that span multiple machines or services. That way you can quickly analyze and cross-reference events from different sources.
- Define the ports in the SELinux policy of the server or client system and open the firewall for those ports. The default SELinux policy includes ports 601, 514, 6514, 10514, and 20514. To use a different port, see modify the SELinux policy on the client and server systems.
Prerequisites
- You have prepared the control node and the managed nodes.
- You are logged in to the control node as a user who can run playbooks on the managed nodes.
-
The account you use to connect to the managed nodes has
sudopermissions for these nodes.
Procedure
Create a playbook file, for example,
~/playbook.yml, with the following content:--- - name: Deploy the logging solution hosts: managed-node-01.example.com tasks: - name: Configure the server to receive remote input ansible.builtin.include_role: name: redhat.rhel_system_roles.logging vars: logging_inputs: - name: remote_udp_input type: remote udp_ports: [ 601 ] - name: remote_tcp_input type: remote tcp_ports: [ 601 ] logging_outputs: - name: remote_files_output type: remote_files logging_flows: - name: flow_0 inputs: [remote_udp_input, remote_tcp_input] outputs: [remote_files_output] - name: Deploy the logging solution hosts: managed-node-02.example.com tasks: - name: Configure the server to output the logs to local files in directories named by remote host names ansible.builtin.include_role: name: redhat.rhel_system_roles.logging vars: logging_inputs: - name: basic_input type: basics logging_outputs: - name: forward_output0 type: forwards severity: info target: <host1.example.com> udp_port: 601 - name: forward_output1 type: forwards facility: mail target: <host1.example.com> tcp_port: 601 logging_flows: - name: flows0 inputs: [basic_input] outputs: [forward_output0, forward_output1]The settings specified in the first play of the example playbook include the following:
logging_inputs-
Defines a list of logging input dictionaries. The
type: remoteoption covers remote inputs from the other logging system over the network. Theudp_ports: [ 601 ]option defines a list of UDP port numbers to monitor. Thetcp_ports: [ 601 ]option defines a list of TCP port numbers to monitor. If bothudp_portsandtcp_portsare set,udp_portsis used andtcp_portsis dropped. logging_outputs-
Defines a list of logging output dictionaries. The
type: remote_filesoption makes output store logs to the local files per remote host and program name originated the logs. logging_flows-
Defines a list of logging flow dictionaries to specify relationships between
logging_inputsandlogging_outputs. Theinputs: [remote_udp_input, remote_tcp_input]option specifies a list of inputs, from which processing of logs starts. Theoutputs: [remote_files_output]option specifies a list of outputs, to which the logs are sent.
The settings specified in the second play of the example playbook include the following:
logging_inputs-
Defines a list of logging input dictionaries. The
type: basicsoption covers inputs fromsystemdjournal or Unix socket. logging_outputs-
Defines a list of logging output dictionaries. The
type: forwardsoption supports sending logs to the remote logging server over the network. Theseverity: infooption refers to log messages of informative importance. Thefacility: mailoption refers to the type of system program that is generating the log message. Thetarget: <host1.example.com>option specifies the hostname of the remote logging server. Theudp_port: 601/tcp_port: 601options define the UDP/TCP ports on which the remote logging server listens. logging_flows-
Defines a list of logging flow dictionaries to specify relationships between
logging_inputsandlogging_outputs. Theinputs: [basic_input]option specifies a list of inputs, from which processing of logs starts. Theoutputs: [forward_output0, forward_output1]option specifies a list of outputs, to which the logs are sent.
For details about the role variables and more information about
rsyslog, see the/usr/share/ansible/roles/rhel-system-roles.logging/README.mdfile and thersyslog.conf(5)andsyslog(3)manual pages on the control node.Validate the playbook syntax:
$ ansible-playbook --syntax-check ~/playbook.ymlNote that this command only validates the syntax and does not protect against a wrong but valid configuration.
Run the playbook:
$ ansible-playbook ~/playbook.yml
Verification
On both the client and the server system, test the syntax of the
/etc/rsyslog.conffile:# rsyslogd -N 1 rsyslogd: version 8.1911.0-6.el8, config validation run (level 1), master config /etc/rsyslog.conf rsyslogd: End of config validation run. Bye.Verify that the client system sends messages to the server:
On the client system, send a test message:
# logger testOn the server system, view the
/var/log/<host2.example.com>/messageslog, for example:# cat /var/log/<host2.example.com>/messages Aug 5 13:48:31 <host2.example.com> root[6778]: testWhere
<host2.example.com>is the host name of the client system. Note that the log contains the user name of the user that entered the logger command, in this caseroot.
6.3. Using the logging RHEL system role with TLS
You can use the logging RHEL system role to configure a secure transfer of log messages, where one or more clients take logs from the systemd-journal service and transfer them to a remote server while using TLS.
Typically, TLS for transferring logs in a remote logging solution is used when sending sensitive data over less trusted or public networks, such as the Internet. Also, by using certificates in TLS you can ensure that the client is forwarding logs to the correct and trusted server. This prevents attacks like "man-in-the-middle".
6.3.1. Configuring client logging with TLS
You can use the logging RHEL system role to configure logging on RHEL clients and transfer logs to a remote logging system by using TLS encryption.
The role creates a private key and a certificate. Next, it configures TLS on all hosts in the clients group in the Ansible inventory. The TLS protocol encrypts the message transmission for secure transfer of logs over the network.
You do not have to call the certificate RHEL system role in the playbook to create the certificate. The logging RHEL system role calls it automatically when the logging_certificates variable is set.
In order for the CA to be able to sign the created certificate, the managed nodes must be enrolled in an IdM domain.
Prerequisites
- You have prepared the control node and the managed nodes.
- You are logged in to the control node as a user who can run playbooks on the managed nodes.
-
The account you use to connect to the managed nodes has
sudopermissions for these nodes. - The managed nodes are enrolled in an IdM domain.
- If the logging server you want to configure on the managed node runs RHEL 9.2 or later and the FIPS mode is enabled, clients must either support the Extended Master Secret (EMS) extension or use TLS 1.3. TLS 1.2 connections without EMS fail. For more information, see the Red Hat Knowledgebase solution TLS extension "Extended Master Secret" enforced.
Procedure
Create a playbook file, for example,
~/playbook.yml, with the following content:--- - name: Configure remote logging solution by using TLS for secure transfer of logs hosts: managed-node-01.example.com tasks: - name: Deploying files input and forwards output with certs ansible.builtin.include_role: name: redhat.rhel_system_roles.logging vars: logging_certificates: - name: logging_cert dns: ['www.example.com'] ca: ipa principal: "logging/{{ inventory_hostname }}@IDM.EXAMPLE.COM" logging_pki_files: - ca_cert: /local/path/to/ca_cert.pem cert: /local/path/to/logging_cert.pem private_key: /local/path/to/logging_cert.pem logging_inputs: - name: input_name type: files input_log_path: /var/log/containers/*.log logging_outputs: - name: output_name type: forwards target: your_target_host tcp_port: 514 tls: true pki_authmode: x509/name permitted_server: 'server.example.com' logging_flows: - name: flow_name inputs: [input_name] outputs: [output_name]The settings specified in the example playbook include the following:
logging_certificates-
The value of this parameter is passed on to
certificate_requestsin thecertificateRHEL system role and used to create a private key and certificate. logging_pki_filesUsing this parameter, you can configure the paths and other settings that logging uses to find the CA, certificate, and key files used for TLS, specified with one or more of the following sub-parameters:
ca_cert,ca_cert_src,cert,cert_src,private_key,private_key_src, andtls.NoteIf you are using
logging_certificatesto create the files on the managed node, do not useca_cert_src,cert_src, andprivate_key_src, which are used to copy files not created bylogging_certificates.ca_cert-
Represents the path to the CA certificate file on the managed node. The default path is
/etc/pki/tls/certs/ca.pemand the file name is set by the user. cert-
Represents the path to the certificate file on the managed node. The default path is
/etc/pki/tls/certs/server-cert.pemand the file name is set by the user. private_key-
Represents the path to the private key file on the managed node. The default path is
/etc/pki/tls/private/server-key.pemand the file name is set by the user. ca_cert_src-
Represents the path to the CA certificate file on the control node which is copied to the target host to the location specified by
ca_cert. Do not use this if usinglogging_certificates. cert_src-
Represents the path to a certificate file on the control node which is copied to the target host to the location specified by
cert. Do not use this if usinglogging_certificates. private_key_src-
Represents the path to a private key file on the control node which is copied to the target host to the location specified by
private_key. Do not use this if usinglogging_certificates. tls-
Setting this parameter to
trueensures secure transfer of logs over the network. If you do not want a secure wrapper, you can settls: false.
For details about the role variables and more information about
rsyslog, see the/usr/share/ansible/roles/rhel-system-roles.logging/README.mdfile and thersyslog.conf(5)andsyslog(3)manual pages on the control node.Validate the playbook syntax:
$ ansible-playbook --syntax-check ~/playbook.ymlNote that this command only validates the syntax and does not protect against a wrong but valid configuration.
Run the playbook:
$ ansible-playbook ~/playbook.yml
6.3.2. Configuring server logging with TLS
You can use the logging RHEL system role to configure logging on RHEL servers and set them to receive logs from a remote logging system by using TLS encryption.
The role creates a private key and a certificate. Next, it configures TLS on all hosts in the server group in the Ansible inventory.
You do not have to call the certificate RHEL system role in the playbook to create the certificate. The logging RHEL system role calls it automatically.
In order for the CA to be able to sign the created certificate, the managed nodes must be enrolled in an IdM domain.
Prerequisites
- You have prepared the control node and the managed nodes.
- You are logged in to the control node as a user who can run playbooks on the managed nodes.
-
The account you use to connect to the managed nodes has
sudopermissions for these nodes. - The managed nodes are enrolled in an IdM domain.
- If the logging server you want to configure on the managed node runs RHEL 9.2 or later and FIPS mode is enabled, clients must either support the Extended Master Secret (EMS) extension or use TLS 1.3. TLS 1.2 connections without EMS fail. For more information, see the Red Hat Knowledgebase solution TLS extension "Extended Master Secret" enforced.
Procedure
Create a playbook file, for example,
~/playbook.yml, with the following content:--- - name: Configure remote logging solution by using TLS for secure transfer of logs hosts: managed-node-01.example.com tasks: - name: Deploying remote input and remote_files output with certs ansible.builtin.include_role: name: redhat.rhel_system_roles.logging vars: logging_certificates: - name: logging_cert dns: ['www.example.com'] ca: ipa principal: "logging/{{ inventory_hostname }}@IDM.EXAMPLE.COM" logging_pki_files: - ca_cert: /local/path/to/ca_cert.pem cert: /local/path/to/logging_cert.pem private_key: /local/path/to/logging_cert.pem logging_inputs: - name: input_name type: remote tcp_ports: [514] tls: true permitted_clients: ['clients.example.com'] logging_outputs: - name: output_name type: remote_files remote_log_path: /var/log/remote/%FROMHOST%/%PROGRAMNAME:::secpath-replace%.log async_writing: true client_count: 20 io_buffer_size: 8192 logging_flows: - name: flow_name inputs: [input_name] outputs: [output_name]The settings specified in the example playbook include the following:
logging_certificates-
The value of this parameter is passed on to
certificate_requestsin thecertificateRHEL system role and used to create a private key and certificate. logging_pki_filesUsing this parameter, you can configure the paths and other settings that logging uses to find the CA, certificate, and key files used for TLS, specified with one or more of the following sub-parameters:
ca_cert,ca_cert_src,cert,cert_src,private_key,private_key_src, andtls.NoteIf you are using
logging_certificatesto create the files on the managed node, do not useca_cert_src,cert_src, andprivate_key_src, which are used to copy files not created bylogging_certificates.ca_cert-
Represents the path to the CA certificate file on the managed node. The default path is
/etc/pki/tls/certs/ca.pemand the file name is set by the user. cert-
Represents the path to the certificate file on the managed node. The default path is
/etc/pki/tls/certs/server-cert.pemand the file name is set by the user. private_key-
Represents the path to the private key file on the managed node. The default path is
/etc/pki/tls/private/server-key.pemand the file name is set by the user. ca_cert_src-
Represents the path to the CA certificate file on the control node which is copied to the target host to the location specified by
ca_cert. Do not use this if usinglogging_certificates. cert_src-
Represents the path to a certificate file on the control node which is copied to the target host to the location specified by
cert. Do not use this if usinglogging_certificates. private_key_src-
Represents the path to a private key file on the control node which is copied to the target host to the location specified by
private_key. Do not use this if usinglogging_certificates. tls-
Setting this parameter to
trueensures secure transfer of logs over the network. If you do not want a secure wrapper, you can settls: false.
For details about the role variables and more information about
rsyslog, see the/usr/share/ansible/roles/rhel-system-roles.logging/README.mdfile and thersyslog.conf(5)andsyslog(3)manual pages on the control node.Validate the playbook syntax:
$ ansible-playbook --syntax-check ~/playbook.ymlNote that this command only validates the syntax and does not protect against a wrong but valid configuration.
Run the playbook:
$ ansible-playbook ~/playbook.yml
6.4. Using the logging RHEL system roles with RELP
You can use the logging RHEL system role to configure Reliable Event Logging Protocol (RELP) between a RELP client and RELP server.
RELP is a networking protocol for data and message logging over the TCP network. It ensures reliable delivery of event messages and you can use it in environments that do not tolerate any message loss.
The RELP sender transfers log entries in the form of commands and the receiver acknowledges them once they are processed. To ensure consistency, RELP stores the transaction number to each transferred command for any kind of message recovery.
6.4.1. Configuring client logging with RELP
You can use the logging RHEL system role to configure a transfer of log messages stored locally to the remote logging system with RELP.
The RELP configuration uses Transport Layer Security (TLS) to encrypt the message transmission for secure transfer of logs over the network.
Prerequisites
- You have prepared the control node and the managed nodes.
- You are logged in to the control node as a user who can run playbooks on the managed nodes.
-
The account you use to connect to the managed nodes has
sudopermissions for these nodes.
Procedure
Create a playbook file, for example,
~/playbook.yml, with the following content:--- - name: Configure client-side of the remote logging solution by using RELP hosts: managed-node-01.example.com tasks: - name: Deploy basic input and RELP output ansible.builtin.include_role: name: redhat.rhel_system_roles.logging vars: logging_inputs: - name: basic_input type: basics logging_outputs: - name: relp_client type: relp target: logging.server.com port: 20514 tls: true ca_cert: /etc/pki/tls/certs/ca.pem cert: /etc/pki/tls/certs/client-cert.pem private_key: /etc/pki/tls/private/client-key.pem pki_authmode: name permitted_servers: - '*.server.example.com' logging_flows: - name: example_flow inputs: [basic_input] outputs: [relp_client]The settings specified in the example playbook include the following:
target- This is a required parameter that specifies the host name where the remote logging system is running.
port- Port number the remote logging system is listening.
tlsEnsures secure transfer of logs over the network. If you do not want a secure wrapper you can set the
tlsvariable tofalse. By defaulttlsparameter is set to true while working with RELP and requires key/certificates and triplets {ca_cert,cert,private_key} and/or {ca_cert_src,cert_src,private_key_src}.-
If the {
ca_cert_src,cert_src,private_key_src} triplet is set, the default locations/etc/pki/tls/certsand/etc/pki/tls/privateare used as the destination on the managed node to transfer files from control node. In this case, the file names are identical to the original ones in the triplet -
If the {
ca_cert,cert,private_key} triplet is set, files are expected to be on the default path before the logging configuration. - If both triplets are set, files are transferred from the local path on the control node to the specific path of the managed node.
-
If the {
ca_cert-
Represents the path to CA certificate. The default path is
/etc/pki/tls/certs/ca.pemand the file name is set by the user. cert-
Represents the path to certificate. The default path is
/etc/pki/tls/certs/server-cert.pemand the file name is set by the user. private_key-
Represents the path to the private key. The default path is
/etc/pki/tls/private/server-key.pemand the file name is set by the user. ca_cert_src-
Represents local CA certificate file path which is copied to the managed node. If
ca_certis specified, it is copied to the location. cert_src-
Represents the local certificate file path which is copied to the managed node. If
certis specified, it is copied to the location. private_key_src-
Represents the local key file path which is copied to the managed node. If
private_keyis specified, it is copied to the location. pki_authmode-
Accepts the authentication mode as
nameorfingerprint. permitted_servers- List of servers that will be allowed by the logging client to connect and send logs over TLS.
inputs- List of logging input dictionary.
outputs- List of logging output dictionary.
For details about the role variables and more information about
rsyslog, see the/usr/share/ansible/roles/rhel-system-roles.logging/README.mdfile and thersyslog.conf(5)andsyslog(3)manual pages on the control node.Validate the playbook syntax:
$ ansible-playbook --syntax-check ~/playbook.ymlNote that this command only validates the syntax and does not protect against a wrong but valid configuration.
Run the playbook:
$ ansible-playbook ~/playbook.yml
6.4.2. Configuring server logging with RELP
You can use the logging RHEL system role to configure a server for receiving log messages from the remote logging system with RELP.
The RELP configuration uses TLS to encrypt the message transmission for secure transfer of logs over the network.
Prerequisites
- You have prepared the control node and the managed nodes.
- You are logged in to the control node as a user who can run playbooks on the managed nodes.
-
The account you use to connect to the managed nodes has
sudopermissions for these nodes.
Procedure
Create a playbook file, for example,
~/playbook.yml, with the following content:--- - name: Configure server-side of the remote logging solution by using RELP hosts: managed-node-01.example.com tasks: - name: Deploying remote input and remote_files output ansible.builtin.include_role: name: redhat.rhel_system_roles.logging vars: logging_inputs: - name: relp_server type: relp port: 20514 tls: true ca_cert: /etc/pki/tls/certs/ca.pem cert: /etc/pki/tls/certs/server-cert.pem private_key: /etc/pki/tls/private/server-key.pem pki_authmode: name permitted_clients: - '*client.example.com' logging_outputs: - name: remote_files_output type: remote_files logging_flows: - name: example_flow inputs: [relp_server] outputs: [remote_files_output]The settings specified in the example playbook include the following:
port- Port number the remote logging system is listening.
tlsEnsures secure transfer of logs over the network. If you do not want a secure wrapper you can set the
tlsvariable tofalse. By defaulttlsparameter is set to true while working with RELP and requires key/certificates and triplets {ca_cert,cert,private_key} and/or {ca_cert_src,cert_src,private_key_src}.-
If the {
ca_cert_src,cert_src,private_key_src} triplet is set, the default locations/etc/pki/tls/certsand/etc/pki/tls/privateare used as the destination on the managed node to transfer files from control node. In this case, the file names are identical to the original ones in the triplet -
If the {
ca_cert,cert,private_key} triplet is set, files are expected to be on the default path before the logging configuration. - If both triplets are set, files are transferred from the local path on the control node to the specific path of the managed node.
-
If the {
ca_cert-
Represents the path to CA certificate. The default path is
/etc/pki/tls/certs/ca.pemand the file name is set by the user. cert-
Represents the path to the certificate. The default path is
/etc/pki/tls/certs/server-cert.pemand the file name is set by the user. private_key-
Represents the path to the private key. The default path is
/etc/pki/tls/private/server-key.pemand the file name is set by the user. ca_cert_src-
Represents local CA certificate file path which is copied to the managed node. If
ca_certis specified, it is copied to the location. cert_src-
Represents the local certificate file path which is copied to the managed node. If
certis specified, it is copied to the location. private_key_src-
Represents the local key file path which is copied to the managed node. If
private_keyis specified, it is copied to the location. pki_authmode-
Accepts the authentication mode as
nameorfingerprint. permitted_clients- List of clients that will be allowed by the logging server to connect and send logs over TLS.
inputs- List of logging input dictionary.
outputs- List of logging output dictionary.
For details about the role variables and more information about
rsyslog, see the/usr/share/ansible/roles/rhel-system-roles.logging/README.mdfile and thersyslog.conf(5)andsyslog(3)manual pages on the control node.Validate the playbook syntax:
$ ansible-playbook --syntax-check ~/playbook.ymlNote that this command only validates the syntax and does not protect against a wrong but valid configuration.
Run the playbook:
$ ansible-playbook ~/playbook.yml
Chapter 7. Auditing the system
Audit your system to record security-relevant events, identify potential intrusions, and verify compliance with security policies. The Linux Audit system is central to this security process.
The Audit system does not provide additional security for your system. Instead, it can detect security policy violations on your system. You can further prevent these violations by additional security measures, such as SELinux.
7.1. Linux Audit
With Linux Audit, you can track security-relevant information about your system. By following preconfigured rules, Audit generates log entries to record as much information as possible about events on your system. This information is crucial to determine the violator of the security policy.
Audit can record, for example, the following information in its log files:
- Date and time, type, and outcome of an event
- Sensitivity labels of subjects and objects
- Association of an event with the identity of the user who triggered the event
- All modifications to Audit configuration and attempts to access Audit log files
- All uses of authentication mechanisms, such as SSH, Kerberos, and others
-
Changes to any trusted database, such as
/etc/passwd - Attempts to import or export information into or from the system
- Include or exclude events based on user identity, subject and object labels, and other attributes
The use of the Audit system is also a requirement for several security-related certifications. Audit is designed to meet or exceed the requirements of the following certifications or compliance guides:
- Controlled Access Protection Profile (CAPP)
- Labeled Security Protection Profile (LSPP)
- Rule Set Base Access Control (RSBAC)
- National Industrial Security Program Operating Manual (NISPOM)
- Federal Information Security Management Act (FISMA)
- Payment Card Industry - Data Security Standard (PCI-DSS)
- Security Technical Implementation Guides (STIG)
Audit has also been evaluated by National Information Assurance Partnership (NIAP) and Best Security Industries (BSI). You can use Audit for:
- Watching file access
- Audit can track whether a file or a directory has been accessed, modified, executed, or the file’s attributes have been changed. This is useful, for example, to detect access to important files and have an Audit trail available in case one of these files is corrupted.
- Monitoring system calls
-
Audit can be configured to generate a log entry every time a particular system call is used. This can be used, for example, to track changes to the system time by monitoring the
settimeofday,clock_adjtime, and other time-related system calls. - Recording commands run by a user
-
Audit can track whether a file has been executed, so rules can be defined to record every execution of a particular command. For example, a rule can be defined for every executable in the
/bindirectory. The resulting log entries can then be searched by user ID to generate an audit trail of executed commands per user. - Recording execution of system path names
- Aside from monitoring file access which translates a path to an inode at rule invocation, Audit can now monitor the execution of a path even if it does not exist at rule invocation, or if the file is replaced after rule invocation. This allows rules to continue to work after upgrading a program executable or before it is even installed.
- Recording security events
-
The
pam_faillockauthentication module is capable of recording failed login attempts. Audit can be set up to record failed login attempts as well and provides additional information about the user who attempted to log in. - Searching for events
-
Audit provides the
ausearchutility, which can be used to filter the log entries and provide a complete audit trail based on several conditions. - Running summary reports
-
The
aureportutility can be used to generate, among other things, daily reports of recorded events. A system administrator can then analyze these reports and investigate suspicious activity further. - Monitoring network access
-
The
nftables,iptables, andebtablesutilities can be configured to trigger Audit events, allowing system administrators to monitor network access.
Audit affects system performance depending on the amount of information collected.
7.2. Audit system architecture
The Audit system consists of two main parts: the user-space applications and utilities, and the kernel-side system call processing. The kernel component receives system calls from user-space applications and filters them through one of the following filters: user, task, fstype, or exit.
After a system call passes the exclude filter, it is sent through one of the aforementioned filters, which, based on the Audit rule configuration, sends it to the Audit daemon for further processing.
The user-space Audit daemon collects information from the kernel and writes entries to a log file. Other Audit user-space utilities interact with the Audit daemon, the kernel Audit component, or the Audit log files:
-
The
auditctlAudit control utility interacts with the kernel Audit component to manage rules and to control many settings and parameters of the event generation process. -
The remaining Audit utilities take the contents of the Audit log files as input and generate output based on the user’s requirements. For example, the
aureportutility generates a report of all recorded events.
In RHEL 10, the Audit dispatcher daemon (audisp) functionality is integrated in the Audit daemon (auditd). By default, configuration files for plugins that enable real-time analytical programs to interact with Audit events are located in the /etc/audit/plugins.d/ directory.
7.3. Audit settings for a secure environment
Configure specific audit rules and settings, such as those provided by STIG, to create a secure audit environment. This helps ensure comprehensive logging of security-relevant events.
The default auditd configuration should be suitable for most environments. However, if your environment must meet strict security policies, you can change the following settings for the Audit daemon configuration in the /etc/audit/auditd.conf file:
log_file-
The directory that holds the Audit log files (usually
/var/log/audit/) should reside on a separate mount point. This prevents other processes from consuming space in this directory and provides accurate detection of the remaining space for the Audit daemon. max_log_file-
Specifies the maximum size of a single Audit log file, must be set to make full use of the available space on the partition that holds the Audit log files. The
max_log_fileparameter specifies the maximum file size in megabytes. The value given must be numeric. max_log_file_action-
Decides what action is taken once the limit set in
max_log_fileis reached, should be set tokeep_logsto prevent Audit log files from being overwritten. space_left-
Specifies the amount of free space left on the disk for which an action that is set in the
space_left_actionparameter is triggered. Must be set to a number that gives the administrator enough time to respond and free up disk space. Thespace_leftvalue depends on the rate at which the Audit log files are generated. If the value ofspace_leftis specified as a whole number, it is interpreted as an absolute size in megabytes (MiB). If the value is specified as a number between 1 and 99 followed by a percentage sign (for example, 5%), the Audit daemon calculates the absolute size in megabytes based on the size of the file system containinglog_file. space_left_action-
It is recommended to set the
space_left_actionparameter toemailorexecwith an appropriate notification method. admin_space_left-
Specifies the absolute minimum amount of free space for which an action that is set in the
admin_space_left_actionparameter is triggered, must be set to a value that leaves enough space to log actions performed by the administrator. The numeric value for this parameter should be lower than the number forspace_left. You can also append a percent sign (for example, 1%) to the number to have the audit daemon calculate the number based on the disk partition size. admin_space_left_action-
Should be set to
singleto put the system into single-user mode and allow the administrator to free up some disk space. disk_full_action-
Specifies an action that is triggered when no free space is available on the partition that holds the Audit log files, must be set to
haltorsingle. This ensures that the system is either shut down or operating in single-user mode when Audit can no longer log events. disk_error_action-
Specifies an action that is triggered in case an error is detected on the partition that holds the Audit log files, must be set to
syslog,single, orhalt, depending on your local security policies regarding the handling of hardware malfunctions. flush-
Should be set to
incremental_async. It works in combination with thefreqparameter, which determines how many records can be sent to the disk before forcing a hard synchronization with the hard drive. Thefreqparameter should be set to100. These parameters assure that Audit event data is synchronized with the log files on the disk while keeping good performance for bursts of activity.
The remaining configuration options should be set according to your local security policy.
7.4. Starting and controlling auditd
Start, stop, and control the auditd service, which manages the system audit records. Maintaining this service is crucial for continuous security monitoring and recording important events.
After auditd is configured, start the service to collect Audit information and store it in the log files. Use the following command as the root user to start auditd:
# service auditd start
To configure auditd to start at boot time:
# systemctl enable auditd
You can temporarily disable auditd with the # auditctl -e 0 command and re-enable it with # auditctl -e 1.
You can perform other actions on auditd by using the service auditd <action> command, where <action> can be one of the following:
stop-
Stops
auditd. restart-
Restarts
auditd. reloadorforce-reload-
Reloads the configuration of
auditdfrom the/etc/audit/auditd.conffile. rotate-
Rotates the log files in the
/var/log/audit/directory. resume- Resumes logging of Audit events after it has been previously suspended, for example, when there is not enough free space on the disk partition that holds the Audit log files.
condrestartortry-restart-
Restarts
auditdonly if it is already running. status-
Displays the running status of
auditd.
The service command is the only way to interact with the auditd daemon correctly. You must use the service command so that the auid value is properly recorded. You can use the systemctl command only for two actions: enable and status.
7.5. Audit log entries
Log entries created by the Audit system provide crucial data for forensic analysis and troubleshooting.
By default, the Audit system stores log entries in the /var/log/audit/audit.log file; if log rotation is enabled, rotated audit.log files are stored in the same directory.
Add the following Audit rule to log every attempt to read or modify the /etc/ssh/sshd_config file:
# auditctl -w /etc/ssh/sshd_config -p warx -k sshd_config
If the auditd daemon is running, for example, using the following command creates a new event in the Audit log file:
$ cat /etc/ssh/sshd_config
This event in the audit.log file looks as follows:
type=SYSCALL msg=audit(1364481363.243:24287): arch=c000003e syscall=2 success=no exit=-13 a0=7fffd19c5592 a1=0 a2=7fffd19c4b50 a3=a items=1 ppid=2686 pid=3538 auid=1000 uid=1000 gid=1000 euid=1000 suid=1000 fsuid=1000 egid=1000 sgid=1000 fsgid=1000 tty=pts0 ses=1 comm="cat" exe="/bin/cat" subj=unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023 key="sshd_config"
type=CWD msg=audit(1364481363.243:24287): cwd="/home/shadowman"
type=PATH msg=audit(1364481363.243:24287): item=0 name="/etc/ssh/sshd_config" inode=409248 dev=fd:00 mode=0100600 ouid=0 ogid=0 rdev=00:00 obj=system_u:object_r:etc_t:s0 nametype=NORMAL cap_fp=none cap_fi=none cap_fe=0 cap_fver=0
type=PROCTITLE msg=audit(1364481363.243:24287) : proctitle=636174002F6574632F7373682F737368645F636F6E666967
The previous event consists of four records, which share the same timestamp and serial number. Records always start with the type= keyword. Each record consists of several name=value pairs separated by a white space or a comma. A detailed analysis of the previous event follows:
Example 7.1. First Record
type=SYSCALL-
The
typefield contains the type of the record. In this example, theSYSCALLvalue specifies that this record was triggered by a system call to the kernel. msg=audit(1364481363.243:24287):The
msgfield records:-
A timestamp and a unique ID of the record in the form
audit(time_stamp:ID). Multiple records can share the same timestamp and ID if they were generated as part of the same Audit event. The timestamp is using the Unix time format - seconds since 00:00:00 UTC on 1 January 1970. -
Various event-specific
name=valuepairs provided by the kernel or user-space applications.
-
A timestamp and a unique ID of the record in the form
arch=c000003e-
The
archfield contains information about the CPU architecture of the system. The value,c000003e, is encoded in hexadecimal notation. When searching Audit records with theausearchcommand, use the-ior--interpretoption to automatically convert hexadecimal values into their human-readable equivalents. Thec000003evalue is interpreted asx86_64. syscall=2-
The
syscallfield records the type of the system call that was sent to the kernel. The value,2, can be matched with its human-readable equivalent in the/usr/include/asm/unistd_64.hfile. In this case,2is theopensystem call. Note that theausyscallutility allows you to convert system call numbers to their human-readable equivalents. Use theausyscall --dumpcommand to display a listing of all system calls along with their numbers. For more information, see theausyscall(8) man page. success=no-
The
successfield records whether the system call recorded in that particular event succeeded or failed. In this case, the call did not succeed. exit=-13The
exitfield contains a value that specifies the exit code returned by the system call. This value varies for a different system call. You can interpret the value to its human-readable equivalent with the following command:# ausearch --interpret --exit -13Note that the previous example assumes that your Audit log contains an event that failed with exit code
-13.a0=7fffd19c5592,a1=0,a2=7fffd19c5592,a3=a-
The
a0toa3fields record the first four arguments, encoded in hexadecimal notation, of the system call in this event. These arguments depend on the system call that is used; they can be interpreted by theausearchutility. items=1-
The
itemsfield contains the number of PATH auxiliary records that follow the syscall record. ppid=2686-
The
ppidfield records the Parent Process ID (PPID). In this case,2686was the PPID of the parent process such asbash. pid=3538-
The
pidfield records the Process ID (PID). In this case,3538was the PID of thecatprocess. auid=1000-
The
auidfield records the Audit user ID, that is theloginuid. This ID is assigned to a user upon login and is inherited by every process even when the user’s identity changes, for example, by switching user accounts with thesu - johncommand. uid=1000-
The
uidfield records the user ID of the user who started the analyzed process. The user ID can be interpreted into user names with the following command:ausearch -i --uid UID. gid=1000-
The
gidfield records the group ID of the user who started the analyzed process. euid=1000-
The
euidfield records the effective user ID of the user who started the analyzed process. suid=1000-
The
suidfield records the set user ID of the user who started the analyzed process. fsuid=1000-
The
fsuidfield records the file system user ID of the user who started the analyzed process. egid=1000-
The
egidfield records the effective group ID of the user who started the analyzed process. sgid=1000-
The
sgidfield records the set group ID of the user who started the analyzed process. fsgid=1000-
The
fsgidfield records the file system group ID of the user who started the analyzed process. tty=pts0-
The
ttyfield records the terminal from which the analyzed process was invoked. ses=1-
The
sesfield records the session ID of the session from which the analyzed process was invoked. comm="cat"-
The
commfield records the command-line name of the command that was used to invoke the analyzed process. In this case, thecatcommand was used to trigger this Audit event. exe="/bin/cat"-
The
exefield records the path to the executable that was used to invoke the analyzed process. subj=unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023-
The
subjfield records the SELinux context with which the analyzed process was labeled at the time of execution. key="sshd_config"-
The
keyfield records the administrator-defined string associated with the rule that generated this event in the Audit log.
Example 7.2. Second Record
type=CWDIn the second record, the
typefield value isCWD- current working directory. This type is used to record the working directory from which the process that invoked the system call specified in the first record was executed.The purpose of this record is to record the current process’s location in case a relative path winds up being captured in the associated PATH record. This way the absolute path can be reconstructed.
msg=audit(1364481363.243:24287)-
The
msgfield holds the same timestamp and ID value as the value in the first record. The timestamp uses the Unix time format - seconds since 00:00:00 UTC on 1 January 1970. cwd="/home/user_name"-
The
cwdfield contains the path to the directory in which the system call was invoked.
Example 7.3. Third Record
type=PATH-
In the third record, the
typefield value isPATH. An Audit event contains aPATH-type record for every path that is passed to the system call as an argument. In this Audit event, only one path (/etc/ssh/sshd_config) was used as an argument. msg=audit(1364481363.243:24287):-
The
msgfield holds the same timestamp and ID value as the value in the first and second record. item=0-
The
itemfield indicates which item, of the total number of items referenced in theSYSCALLtype record, the current record is. This number is zero-based; a value of0means it is the first item. name="/etc/ssh/sshd_config"-
The
namefield records the path of the file or directory that was passed to the system call as an argument. In this case, it was the/etc/ssh/sshd_configfile. inode=409248The
inodefield contains the inode number associated with the file or directory recorded in this event. The following command displays the file or directory that is associated with the409248inode number:# find / -inum 409248 -print /etc/ssh/sshd_configdev=fd:00-
The
devfield specifies the minor and major ID of the device that contains the file or directory recorded in this event. In this case, the value represents the/dev/fd/0device. mode=0100600-
The
modefield records the file or directory permissions, encoded in numerical notation as returned by thestatcommand in thest_modefield. See thestat(2)man page for more information. In this case,0100600can be interpreted as-rw-------, meaning that only the root user has read and write permissions to the/etc/ssh/sshd_configfile. ouid=0-
The
ouidfield records the object owner’s user ID. ogid=0-
The
ogidfield records the object owner’s group ID. rdev=00:00-
The
rdevfield contains a recorded device identifier for special files only. In this case, it is not used as the recorded file is a regular file. obj=system_u:object_r:etc_t:s0-
The
objfield records the SELinux context with which the recorded file or directory was labeled at the time of execution. nametype=NORMAL-
The
nametypefield records the intent of each path record’s operation in the context of a given syscall. cap_fp=none-
The
cap_fpfield records data related to the setting of a permitted file system-based capability of the file or directory object. cap_fi=none-
The
cap_fifield records data related to the setting of an inherited file system-based capability of the file or directory object. cap_fe=0-
The
cap_fefield records the setting of the effective bit of the file system-based capability of the file or directory object. cap_fver=0-
The
cap_fverfield records the version of the file system-based capability of the file or directory object.
Example 7.4. Fourth Record
type=PROCTITLE-
The
typefield contains the type of the record. In this example, thePROCTITLEvalue specifies that this record gives the full command-line that triggered this Audit event, triggered by a system call to the kernel. proctitle=636174002F6574632F7373682F737368645F636F6E666967-
The
proctitlefield records the full command-line of the command that was used to invoke the analyzed process. The field is encoded in hexadecimal notation to not allow the user to influence the Audit log parser. The text decodes to the command that triggered this Audit event. When searching Audit records with theausearchcommand, use the-ior--interpretoption to automatically convert hexadecimal values into their human-readable equivalents. The636174002F6574632F7373682F737368645F636F6E666967value is interpreted ascat /etc/ssh/sshd_config.
7.6. Examples of Audit rules defined with auditctl
Define Audit rules by using the auditctl utility to control which system events are captured in your logs. These examples demonstrate how to monitor file access, system calls, and executable files.
The Linux Audit system operates on a set of rules that define what is captured in the log files. Audit rules can be set either on the command line by using the auditctl utility or in the /etc/audit/rules.d/ directory.
The auditctl command enables you to control the basic functionality of the Audit system and to define rules that decide which Audit events are logged. See the auditctl(8) man page on your system for more information.
Example 7.5. File-system rules
To define a rule that logs all write access to, and every attribute change of, the
/etc/passwdfile:# auditctl -w /etc/passwd -p wa -k passwd_changesTo define a rule that logs all write access to, and every attribute change of, all the files in the
/etc/selinux/directory:# auditctl -w /etc/selinux/ -p wa -k selinux_changes
Example 7.6. System-call rules
To define a rule that creates a log entry every time the
adjtimexorsettimeofdaysystem calls are used by a program, and the system uses the 64-bit architecture:# auditctl -a always,exit -F arch=b64 -S adjtimex -S settimeofday -k time_changeTo define a rule that creates a log entry every time a file is deleted or renamed by a system user whose ID is 1000 or larger:
# auditctl -a always,exit -S unlink -S unlinkat -S rename -S renameat -F auid>=1000 -F auid!=4294967295 -k deleteNote that the
-F auid!=4294967295option is used to exclude users whose login UID is not set.
Example 7.7. Executable-file rules
To define a rule that logs all execution of the
/bin/idprogram, enter the following command:# auditctl -a always,exit -F exe=/bin/id -F arch=b64 -S execve -k execution_bin_id
7.7. Audit persistent rules
Create persistent Audit rules by adding them to the /etc/audit/rules.d/ directory. This helps ensure that your monitoring configuration remains active and effective even after a system reboot.
To define Audit rules that are persistent across reboots, you must either directly include them in the /etc/audit/rules.d/audit.rules file or use the augenrules program that reads rules located in the /etc/audit/rules.d/ directory.
Note that the /etc/audit/audit.rules file is generated whenever the auditd service starts. Files in /etc/audit/rules.d/ use the same auditctl command-line syntax to specify the rules. Empty lines and text following a hash sign (#) are ignored.
Furthermore, you can use the auditctl command to read rules from a specified file by using the -R option, for example:
# auditctl -R /usr/share/audit/sample-rules/30-stig.rules
The augenrules script reads rules located in the /etc/audit/rules.d/ directory and compiles them into an audit.rules file. This script processes all files that end with .rules in a specific order based on their natural sort order. The files in this directory are organized into groups with the following meanings:
- 10
-
Kernel and
auditctlconfiguration - 20
- Rules that could match general rules, but you want a different match
- 30
- Main rules
- 40
- Optional rules
- 50
- Server-specific rules
- 70
- System local rules
- 90
- Finalize (immutable)
Do not use all the rules at once. Plan the policy and copy individual files to /etc/audit/rules.d/. For example, to set a system up in the STIG configuration, copy rules 10-base-config, 30-stig, 31-privileged, and 99-finalize.
Once you have the rules in the /etc/audit/rules.d/ directory, load them by running the augenrules script with the --load directive:
# augenrules --load
/sbin/augenrules: No change
No rules
enabled 1
failure 1
pid 742
rate_limit 0
…
See the audit.rules(8) and augenrules(8) man pages on your system for more information.
7.8. Pre-configured Audit rules files for compliance with standards
Use pre-configured rule files as a baseline to align your Audit system with standards such as PCI-DSS or STIG. These samples demonstrate how to structure rules to meet specific compliance requirements.
To configure Audit for compliance with a specific certification standard, such as OSPP, PCI DSS, or STIG, you can use the set of pre-configured rules files installed with the audit package as a starting point. The sample rules are located in the /usr/share/audit/sample-rules directory.
The Audit sample rules in the sample-rules directory are not exhaustive nor up to date because security standards are dynamic and subject to change. These rules are provided only to demonstrate how Audit rules can be structured and written. They do not ensure immediate compliance with the latest security standards. To bring your system into compliance with the latest security standards according to specific security guidelines, use the SCAP-based security compliance tools.
30-nispom.rules- Audit rule configuration that meets the requirements specified in the Information System Security chapter of the National Industrial Security Program Operating Manual.
30-ospp-v42*.rules- Audit rule configuration that meets the requirements defined in the OSPP (Protection Profile for General Purpose Operating Systems) profile version 4.2.
30-pci-dss-v31.rules- Audit rule configuration that meets the requirements set by Payment Card Industry Data Security Standard (PCI DSS) v3.1.
30-stig.rules- Audit rule configuration that meets the requirements set by Security Technical Implementation Guides (STIG).
To use these configuration files, copy them to the /etc/audit/rules.d/ directory and use the augenrules --load command, for example:
# cd /usr/share/audit/sample-rules/
# cp 10-base-config.rules 30-stig.rules 31-privileged.rules 99-finalize.rules /etc/audit/rules.d/
# augenrules --load
You can order Audit rules by using a numbering scheme. See the /usr/share/audit/sample-rules/README-rules file for more information.
See the audit.rules(7) man page on your system for more information.
7.9. Disabling augenrules
You can turn off the augenrules utility, which switches Audit to use rules defined in the /etc/audit/audit.rules file. This allows for a more straightforward rule management process in specific environments.
Procedure
Copy the
/usr/lib/systemd/system/auditd.servicefile to the/etc/systemd/system/directory:# cp -f /usr/lib/systemd/system/auditd.service /etc/systemd/system/Edit the
/etc/systemd/system/auditd.servicefile in a text editor of your choice, for example:# vi /etc/systemd/system/auditd.serviceComment out the line containing
augenrules, and uncomment the line containing theauditctl -Rcommand:#ExecStartPost=-/sbin/augenrules --load ExecStartPost=-/sbin/auditctl -R /etc/audit/audit.rulesReload the
systemddaemon to fetch changes in theauditd.servicefile:# systemctl daemon-reloadRestart the
auditdservice:# service auditd restart
7.10. Setting up Audit to monitor software updates
Configure Audit to monitor software updates and package installations by using specialized rule files. This setup generates events whenever tools such as DNF or RPM modify the system.
You can use the pre-configured rule 44-installers.rules to configure Audit to monitor the following utilities that install software:
-
dnf[1] -
yum -
pip -
npm -
cpan -
gem -
luarocks
To monitor the RPM utility, install the rpm-plugin-audit package. Audit will then generate SOFTWARE_UPDATE events when it installs or updates a package. You can list these events by entering ausearch -m SOFTWARE_UPDATE on the command line.
Pre-configured rule files cannot be used on systems with the ppc64le and aarch64 architectures.
Prerequisites
-
The
auditdservice is configured in accordance with Section 7.3, “Audit settings for a secure environment”.
Procedure
Copy the pre-configured rule file
44-installers.rulesfrom the/usr/share/audit/sample-rules/directory to the/etc/audit/rules.d/directory:# cp /usr/share/audit/sample-rules/44-installers.rules /etc/audit/rules.d/Load the audit rules:
# augenrules --load
Verification
List the loaded rules:
# auditctl -l -p x-w /usr/bin/dnf-3 -k software-installer -p x-w /usr/bin/yum -k software-installer -p x-w /usr/bin/pip -k software-installer -p x-w /usr/bin/npm -k software-installer -p x-w /usr/bin/cpan -k software-installer -p x-w /usr/bin/gem -k software-installer -p x-w /usr/bin/luarocks -k software-installerPerform an installation, for example:
# dnf reinstall -y vim-enhancedSearch the Audit log for recent installation events, for example:
# ausearch -ts recent -k software-installer –––– time->Thu Dec 16 10:33:46 2021 type=PROCTITLE msg=audit(1639668826.074:298): proctitle=2F7573722F6C6962657865632F706C6174666F726D2D707974686F6E002F7573722F62696E2F646E66007265696E7374616C6C002D790076696D2D656E68616E636564 type=PATH msg=audit(1639668826.074:298): item=2 name="/lib64/ld-linux-x86-64.so.2" inode=10092 dev=fd:01 mode=0100755 ouid=0 ogid=0 rdev=00:00 obj=system_u:object_r:ld_so_t:s0 nametype=NORMAL cap_fp=0 cap_fi=0 cap_fe=0 cap_fver=0 cap_frootid=0 type=PATH msg=audit(1639668826.074:298): item=1 name="/usr/libexec/platform-python" inode=4618433 dev=fd:01 mode=0100755 ouid=0 ogid=0 rdev=00:00 obj=system_u:object_r:bin_t:s0 nametype=NORMAL cap_fp=0 cap_fi=0 cap_fe=0 cap_fver=0 cap_frootid=0 type=PATH msg=audit(1639668826.074:298): item=0 name="/usr/bin/dnf" inode=6886099 dev=fd:01 mode=0100755 ouid=0 ogid=0 rdev=00:00 obj=system_u:object_r:rpm_exec_t:s0 nametype=NORMAL cap_fp=0 cap_fi=0 cap_fe=0 cap_fver=0 cap_frootid=0 type=CWD msg=audit(1639668826.074:298): cwd="/root" type=EXECVE msg=audit(1639668826.074:298): argc=5 a0="/usr/libexec/platform-python" a1="/usr/bin/dnf" a2="reinstall" a3="-y" a4="vim-enhanced" type=SYSCALL msg=audit(1639668826.074:298): arch=c000003e syscall=59 success=yes exit=0 a0=55c437f22b20 a1=55c437f2c9d0 a2=55c437f2aeb0 a3=8 items=3 ppid=5256 pid=5375 auid=0 uid=0 gid=0 euid=0 suid=0 fsuid=0 egid=0 sgid=0 fsgid=0 tty=pts0 ses=3 comm="dnf" exe="/usr/libexec/platform-python3.6" subj=unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023 key="software-installer"
dnf is a symlink in RHEL, the path in the dnf Audit rule must include the target of the symlink. To receive correct Audit events, modify the 44-installers.rules file by changing the path=/usr/bin/dnf path to /usr/bin/dnf-3.
7.11. Monitoring user login times with Audit
Use the ausearch and aureport tools to monitor and display user login times and session activities. This provides a clear overview of when users access the system without requiring custom configuration.
Prerequisites
-
The
auditdservice is configured in accordance with Section 7.3, “Audit settings for a secure environment”.
Procedure
Search the Audit log for the
USER_LOGINmessage type:# ausearch -m USER_LOGIN -ts '12/02/2020' '18:00:00' -sv no time->Mon Nov 22 07:33:22 2021 type=USER_LOGIN msg=audit(1637584402.416:92): pid=1939 uid=0 auid=4294967295 ses=4294967295 subj=system_u:system_r:sshd_t:s0-s0:c0.c1023 msg='op=login acct="(unknown)" exe="/usr/sbin/sshd" hostname=? addr=10.37.128.108 terminal=ssh res=failed'-
You can specify the date and time with the
-tsoption. If you do not use this option,ausearchprovides results from today, and if you omit time,ausearchprovides results from midnight. -
You can use the
-sv yesoption to filter out successful login attempts and-sv nofor unsuccessful login attempts.
-
You can specify the date and time with the
Pipe the raw output of the
ausearchcommand into theaulastutility, which displays the output in a format similar to the output of thelastcommand. For example:# ausearch --raw | aulast --stdin root ssh 10.37.128.108 Mon Nov 22 07:33 - 07:33 (00:00) root ssh 10.37.128.108 Mon Nov 22 07:33 - 07:33 (00:00) root ssh 10.22.16.106 Mon Nov 22 07:40 - 07:40 (00:00) reboot system boot 4.18.0-348.6.el8 Mon Nov 22 07:33Display the list of login events by using the
aureportcommand with the--login -ioptions.# aureport --login -i Login Report ============================================ # date time auid host term exe success event ============================================ 1. 11/16/2021 13:11:30 root 10.40.192.190 ssh /usr/sbin/sshd yes 6920 2. 11/16/2021 13:11:31 root 10.40.192.190 ssh /usr/sbin/sshd yes 6925 3. 11/16/2021 13:11:31 root 10.40.192.190 ssh /usr/sbin/sshd yes 6930 4. 11/16/2021 13:11:31 root 10.40.192.190 ssh /usr/sbin/sshd yes 6935 5. 11/16/2021 13:11:33 root 10.40.192.190 ssh /usr/sbin/sshd yes 6940 6. 11/16/2021 13:11:33 root 10.40.192.190 /dev/pts/0 /usr/sbin/sshd yes 6945
Chapter 8. Managing and monitoring security updates
Install security updates and display additional details about the updates to keep your Red Hat Enterprise Linux systems secured against newly discovered threats and vulnerabilities.
8.1. Identifying security updates
Keeping enterprise systems secure from current and future threats requires regular security updates. Red Hat Product Security provides the guidance you need to confidently deploy and maintain enterprise solutions.
8.1.1. What are security advisories
Red Hat Security Advisories (RHSA) document the information about security flaws being fixed in Red Hat products and services.
Each RHSA includes the following information:
- Severity
- Type and status
- Affected products
- Summary of fixed issues
- Links to the tickets about the problem. Note that not all tickets are public.
- Common Vulnerabilities and Exposures (CVE) numbers and links with additional details, such as attack complexity.
Red Hat Customer Portal provides a list of Red Hat Security Advisories published by Red Hat. You can display details of a specific advisory by navigating to the advisory’s ID from the list of Red Hat Security Advisories.
Figure 8.1. List of security advisories
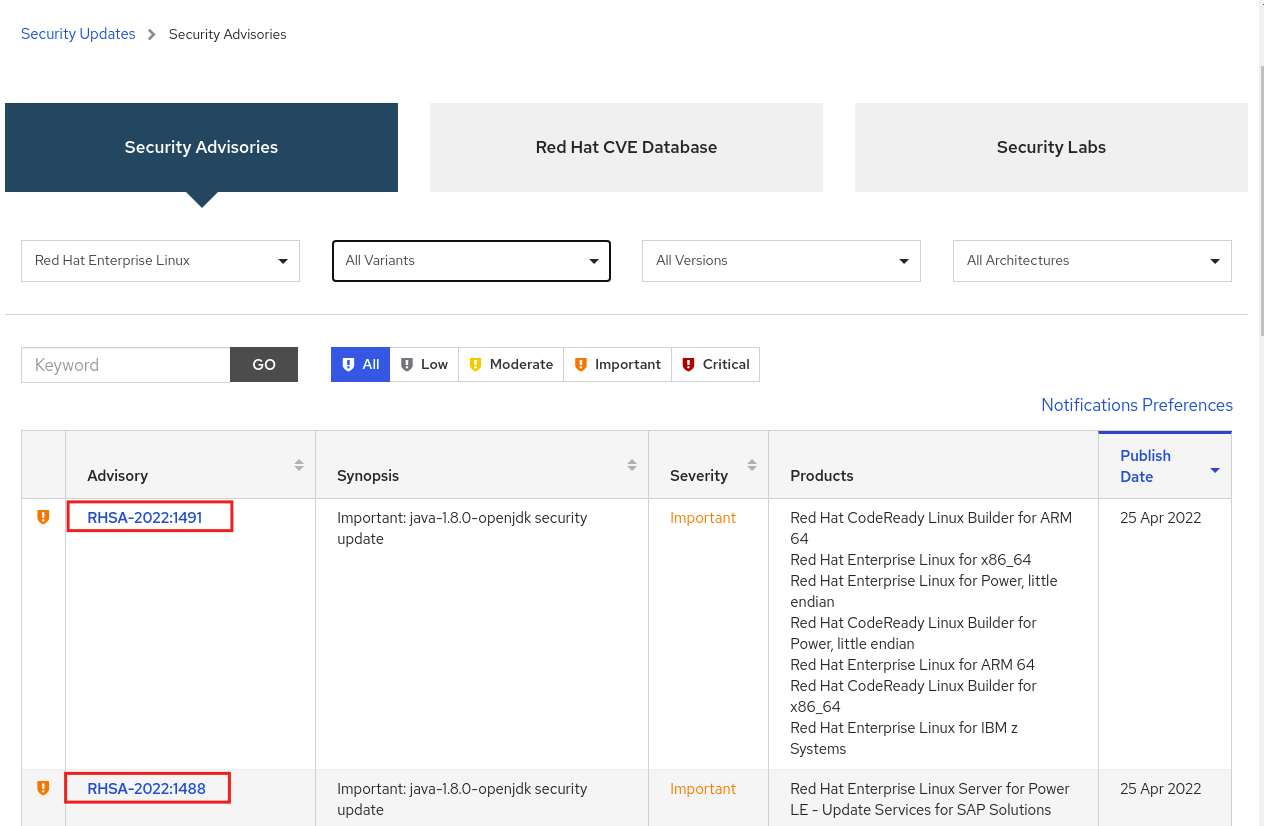
Optionally, you can also filter the results by specific product, variant, version, and architecture. For example, to display only advisories for Red Hat Enterprise Linux 9, you can set the following filters:
- Product: Red Hat Enterprise Linux
- Variant: All Variants
- Version: 9
- Optionally, select a minor version.
8.1.2. Displaying security updates that are not installed on a host
Display all security updates that are currently not installed on your host system to identify critical packages that require immediate action or installation.
You can list all available security updates for your system by using the DNF utility.
Prerequisites
- A Red Hat subscription is attached to the host.
Procedure
List all available security updates which have not been installed on the host:
# dnf updateinfo list updates security … RHSA-2019:0997 Important/Sec. platform-python-3.6.8-2.el8_0.x86_64 RHSA-2019:0997 Important/Sec. python3-libs-3.6.8-2.el8_0.x86_64 RHSA-2019:0990 Moderate/Sec. systemd-239-13.el8_0.3.x86_64 …
8.1.3. Displaying security updates that are installed on a host
Display security updates that are already installed on your host. This helps you verify that required fixes are applied and track your system’s current security posture.
You can list installed security updates for your system by using the DNF utility.
Procedure
List all security updates which are installed on the host:
# dnf updateinfo list security --installed … RHSA-2019:1234 Important/Sec. libssh2-1.8.0-7.module+el8+2833+c7d6d092 RHSA-2019:4567 Important/Sec. python3-libs-3.6.7.1.el8.x86_64 RHSA-2019:8901 Important/Sec. python3-libs-3.6.8-1.el8.x86_64 …If multiple updates of a single package are installed,
dnflists all advisories for the package. In the previous example, two security updates for thepython3-libspackage have been installed since the system installation.
8.1.4. Displaying a specific advisory by using DNF
Use the DNF utility to display detailed information about a specific security advisory. This helps you understand the related bug, its severity, and which packages are included in the fix.
Prerequisites
- A Red Hat subscription is attached to the host.
- You know the ID of the security advisory.
- The update provided by the advisory is not installed.
Procedure
Display a specific advisory, for example:
# dnf updateinfo info RHSA-2019:0997 ==================================================================== Important: python3 security update ==================================================================== Update ID: RHSA-2019:0997 Type: security Updated: 2019-05-07 05:41:52 Bugs: 1688543 - CVE-2019-9636 python: Information Disclosure due to urlsplit improper NFKC normalization CVEs: CVE-2019-9636 Description: …
8.2. Installing security updates
In Red Hat Enterprise Linux, you can install a specific security advisory and all available security updates. You can also configure the system to download and install security updates automatically.
8.2.1. Installing all available security updates
Install all available Red Hat security updates by using the DNF utility. This helps patch all known vulnerabilities and quickly brings the system into full compliance.
Prerequisites
- A Red Hat subscription is attached to the host.
Procedure
Install security updates by using the DNF utility:
# dnf update --securityWithout the
--securityparameter,dnf updateinstalls all updates, including bug fixes and enhancements.Confirm and start the installation by pressing y:
… Transaction Summary =========================================== Upgrade … Packages Total download size: … M Is this ok [y/d/N]: yOptional: List processes that require a manual restart of the system after installing the updated packages:
# dnf needs-restarting 1107 : /usr/sbin/rsyslogd -n 1199 : -bashThe previous command lists only processes that require a restart, and not services. That is, you cannot restart processes listed by using the
systemctlcommand. For example, thebashprocess shown in the output terminates when the user who owns it logs out.
8.2.2. Installing a security update provided by a specific advisory
Install a security update associated with a specific advisory ID by using the DNF utility. This enables targeted patching of critical vulnerabilities without updating all packages.
In certain situations, you should install only specific updates. For example, if a specific service can be updated without scheduling downtime, you can install security updates for that service only and install the remaining updates later.
Prerequisites
- A Red Hat subscription is attached to the host.
You know the ID of the security advisory that you want to update.
For more information, see the Identifying the security advisory updates section.
Procedure
Install a specific advisory, for example:
# dnf update --advisory=RHSA-2019:0997Alternatively, update to apply a specific advisory with a minimal version change by using the
dnf upgrade-minimalcommand, for example:# dnf upgrade-minimal --advisory=RHSA-2019:0997Confirm and start the installation by pressing
y:… Transaction Summary =========================================== Upgrade … Packages Total download size: … M Is this ok [y/d/N]: yOptional: List the processes that require a manual restart of the system after installing the updated packages:
# dnf needs-restarting 1107 : /usr/sbin/rsyslogd -n 1199 : -bashThe previous command lists only processes that require a restart, and not services. That is, you cannot restart processes listed by using the
systemctlcommand. For example, thebashprocess shown in the output terminates when the user who owns it logs out.
8.2.3. Installing security updates automatically
Configure the dnf-automatic tool to download and install security updates automatically. Automating this task helps ensure that your systems remain protected against newly discovered threats without manual intervention.
See the dnf-automatic(8) man page on your system for more information.
Prerequisites
- A Red Hat subscription is attached to the host.
-
The
dnf-automaticpackage is installed.
Procedure
In the
/etc/dnf/automatic.conffile, in the[commands]section, make sure theupgrade_typeoption is set to eitherdefaultorsecurity:[commands] # What kind of upgrade to perform: # default = all available upgrades # security = only the security upgrades upgrade_type = securityEnable and start the systemd timer unit:
# systemctl enable --now dnf-automatic-install.timer
Verification
Verify that the timer is enabled:
# systemctl status dnf-automatic-install.timer