4.3.2.2. Password Aging
Password aging is another technique used by system administrators to defend against bad passwords within an organization. Password aging means that after a set amount of time (usually 90 days) the user is prompted to create a new password. The theory behind this is that if a user is forced to change his password periodically, a cracked password is only useful to an intruder for a limited amount of time. The downside to password aging, however, is that users are more likely to write their passwords down.
There are two primary programs used to specify password aging under Red Hat Enterprise Linux: the
chage command or the graphical User Manager (system-config-users) application.
The
-M option of the chage command specifies the maximum number of days the password is valid. So, for instance, to set a user's password to expire in 90 days, type the following command:
chage -M 90 <username>
In the above command, replace <username> with the name of the user. To disable password expiration, it is traditional to use a value of
99999 after the -M option (this equates to a little over 273 years).
The graphical User Manager application may also be used to create password aging policies. To access this application, go to the button (on the Panel) => => or type the command
system-config-users at a shell prompt (for example, in an XTerm or a GNOME terminal). Click on the Users tab, select the user from the user list, and click from the button menu (or choose => from the pull-down menu).
Then click the Password Info tab and enter the number of days before the password expires, as shown in Figure 4.1, “Password Info Pane”.
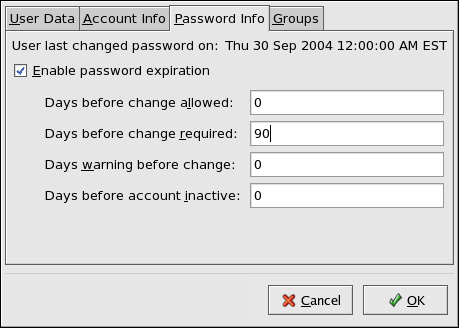
Figure 4.1. Password Info Pane
For more information about user and group configuration (including instructions on forcing first time passwords), refer to the chapter titled User and Group Configuration in the System Administrators Guide. For an overview of user and resource management, refer to the chapter titled Managing User Accounts and Resource Access in the Red Hat Enterprise Linux Introduction to System Adminitration.