Ce contenu n'est pas disponible dans la langue sélectionnée.
6.6. Security Policy
SwitchYard services can be secured by specifying a list of security policies that are required for that service and configuring the security processing details for the services within a domain.
Note
The security manager gets enabled with additional security policies if you select the Runtime Governance component during installation. Following are the security policies included in JBoss Fuse:
- security.policy- It defines a JVM level permitAll policy.
- kie.policy- It is used by Rule-based services.
- rtgov.policy- It is used for the Runtime Governance REST API.
Note
Support for security policy is limited to bean services (implementation.bean), SOAP endpoints via the SOAP gateway (binding.soap), and HTTP endpoints via the HTTP gateway (binding.http).
6.6.1. Security Interaction Policy
Copier lienLien copié sur presse-papiers!
The Security Interaction Policy is defined using the
requires attribute of a component service definition.
<service name="WorkService" requires="authorization clientAuthentication confidentiality">
Valid values for Security Interaction policy are:
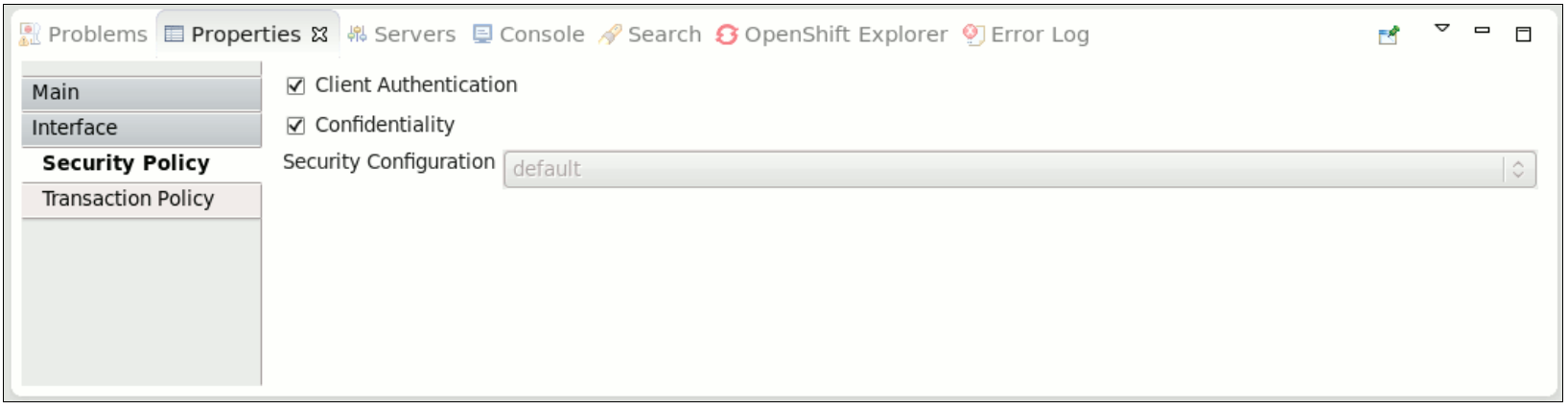
- clientAuthentication: indicates that the client has been authenticated when a service is invoked. If the associated authenticated user principal is not available, SwitchYard runtime generates an error.NoteThere are multiple reasons for why the clientAuthentication policy may not be fulfilled, including incorrect username, incorrect password, or configuration issues. Please check the credentials again. If they seem to be in order engage the support team for further analysis.
- confidentiality: indicates that the request has been made over a secure channel. When a SOAP request is made over SSL and its confidentiality is not verified, SwitchYard runtime generates an error,
Figure 6.3. Security Interaction Policy
6.6.2. Security Implementation Policy
Copier lienLien copié sur presse-papiers!
Security Implementation Policy is specified using the requires attribute of a component implementation definition.
Valid values for Security Implementation policy are:
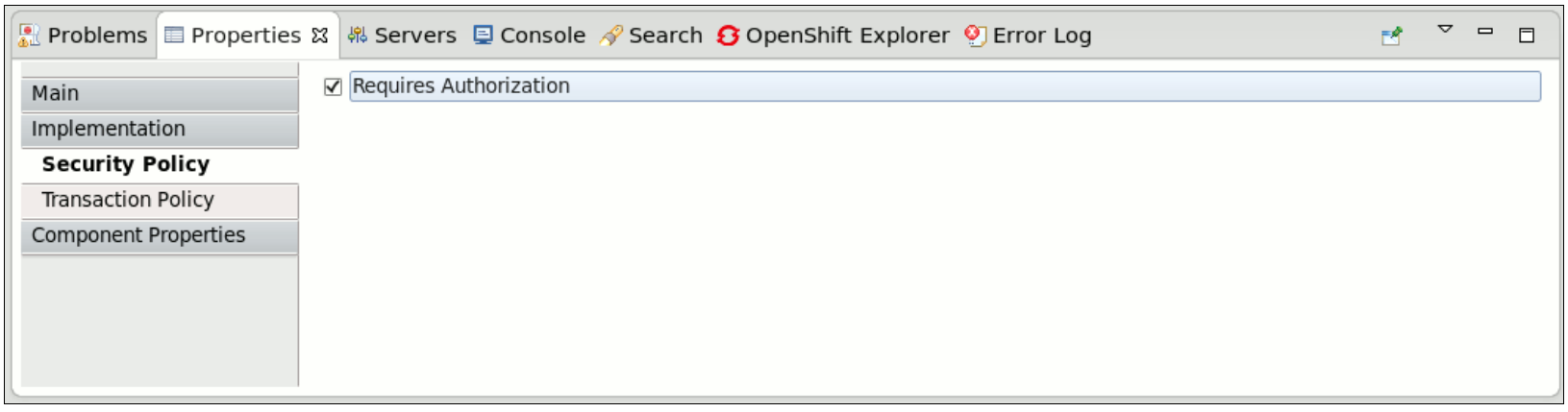
- authorization: indicates that the client is authorized to invoke the service. If the associated authenticated subject does not have an allowed role, SwitchYard runtime generates an error.
Figure 6.4. Security Implementation Policy
6.6.3. Setting Security Policy
Copier lienLien copié sur presse-papiers!
You can define the Security Policy in the following ways:
- Edit the SwitchYard application descriptor (
switchyard.xml) and add therequiresattribute to a service definition.
- Use the
@Requiresattribute in your service implementation to declare security policy for the service. When the application project is built, the SwitchYard application finds@Requiresannotations and automatically generates the required configuration.
6.6.4. Security Processing
Copier lienLien copié sur presse-papiers!
When the container does not automatically provide certain security policies, the SwitchYard application can be configured to process security credentials extracted from the binding-specific data, then provide certain security policies itself (like clientAuthentication). All services within a domain share the same security configuration, which is specified in the
switchyard.xml.
<switchyard>
<domain>
<security callbackHandler="callback-handler-class-name" moduleName"="jaas-domain-name" rolesAllowed="users, administrators" runAs="leaders">
<properties>
<property name="property-name" value="property-value"/>
</properties>
</security>
</domain>
</switchyard>Note
Support for security policy is limited to bean services (implementation.bean), SOAP endpoints via the SOAP gateway (binding.soap), and HTTP endpoints via the HTTP gateway (binding.http).