Chapter 14. Scanning pods for vulnerabilities
Using the Red Hat Quay Container Security Operator, you can access vulnerability scan results from the OpenShift Container Platform web console for container images used in active pods on the cluster. The Red Hat Quay Container Security Operator:
- Watches containers associated with pods on all or specified namespaces
- Queries the container registry where the containers came from for vulnerability information, provided an image’s registry is running image scanning (such as Quay.io or a Red Hat Quay registry with Clair scanning)
-
Exposes vulnerabilities via the
ImageManifestVulnobject in the Kubernetes API
Using the instructions here, the Red Hat Quay Container Security Operator is installed in the openshift-operators namespace, so it is available to all namespaces on your OpenShift Container Platform cluster.
14.1. Installing the Red Hat Quay Container Security Operator
You can install the Red Hat Quay Container Security Operator from the OpenShift Container Platform web console Operator Hub, or by using the CLI.
Prerequisites
-
You have installed the
ocCLI. - You have administrator privileges to the OpenShift Container Platform cluster.
- You have containers that come from a Red Hat Quay or Quay.io registry running on your cluster.
Procedure
You can install the Red Hat Quay Container Security Operator by using the OpenShift Container Platform web console:
-
On the web console, navigate to Operators
OperatorHub and select Security. - Select the Red Hat Quay Container Security Operator Operator, and then select Install.
-
On the Red Hat Quay Container Security Operator page, select Install. Update channel, Installation mode, and Update approval are selected automatically. The Installed Namespace field defaults to
openshift-operators. You can adjust these settings as needed. - Select Install. The Red Hat Quay Container Security Operator appears after a few moments on the Installed Operators page.
Optional: You can add custom certificates to the Red Hat Quay Container Security Operator. For example, create a certificate named
quay.crtin the current directory. Then, run the following command to add the custom certificate to the Red Hat Quay Container Security Operator:$ oc create secret generic container-security-operator-extra-certs --from-file=quay.crt -n openshift-operators- Optional: If you added a custom certificate, restart the Red Hat Quay Container Security Operator pod for the new certificates to take effect.
-
On the web console, navigate to Operators
Alternatively, you can install the Red Hat Quay Container Security Operator by using the CLI:
Retrieve the latest version of the Container Security Operator and its channel by entering the following command:
$ oc get packagemanifests container-security-operator \ -o jsonpath='{range .status.channels[*]}{@.currentCSV} {@.name}{"\n"}{end}' \ | awk '{print "STARTING_CSV=" $1 " CHANNEL=" $2 }' \ | sort -nr \ | head -1Example output
STARTING_CSV=container-security-operator.v3.8.9 CHANNEL=stable-3.8Using the output from the previous command, create a
Subscriptioncustom resource for the Red Hat Quay Container Security Operator and save it ascontainer-security-operator.yaml. For example:apiVersion: operators.coreos.com/v1alpha1 kind: Subscription metadata: name: container-security-operator namespace: openshift-operators spec: channel: ${CHANNEL}1 installPlanApproval: Automatic name: container-security-operator source: redhat-operators sourceNamespace: openshift-marketplace startingCSV: ${STARTING_CSV}2 Enter the following command to apply the configuration:
$ oc apply -f container-security-operator.yamlExample output
subscription.operators.coreos.com/container-security-operator created
14.2. Using the Red Hat Quay Container Security Operator
The following procedure shows you how to use the Red Hat Quay Container Security Operator.
Prerequisites
- You have installed the Red Hat Quay Container Security Operator.
Procedure
-
On the OpenShift Container Platform web console, navigate to Home
Overview. Under the Status section, Quay Image Security provides the number of vulnerabilities found. Click Quay Image Security to reveal the Quay Image Security breakdown, which details the severity of the vulnerabilities, whether the vulnerabilities can be fixed, and the total number of vulnerabilities. For example:

You can address detected vulnerabilities in one of two ways:
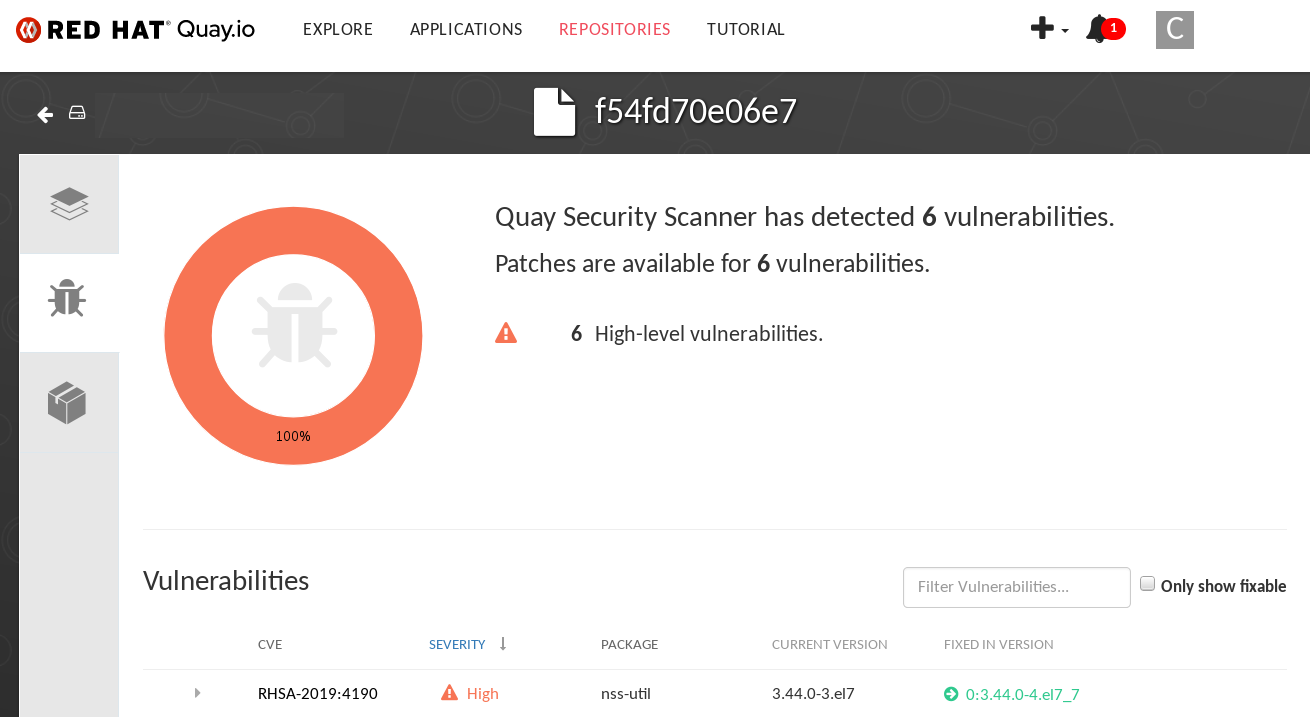
Select the link to the vulnerability. This takes you to the container registry that the container came from, where you can see information about the vulnerability. The following example shows detected vulnerabilities from a Quay.io registry:
Select the namespace link. This takes you to the ImageManifestVuln page, where you can see the name of the selected image and all of the namespaces where that image is running. For example, the following image shows you that a particular vulnerable image is running in the
quay-enterprisenamespace: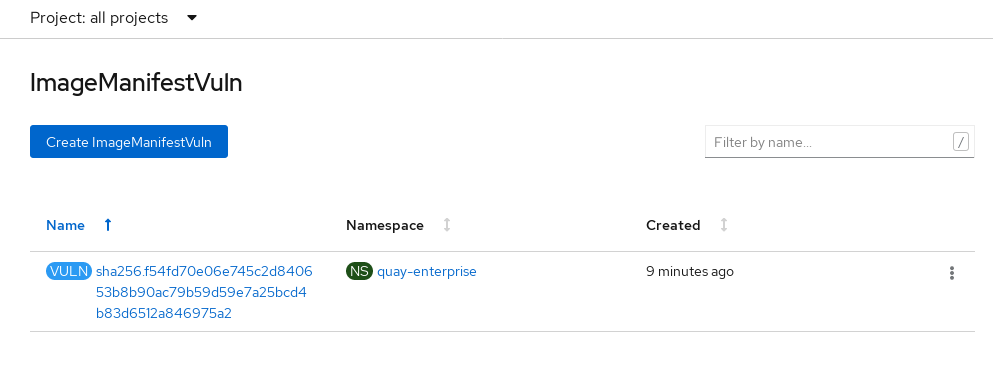
After you have learned what images are vulnerable, how to fix those vulnerabilities, and the namespaces that the images are being run in, you can improve security by performing the following actions:
- Alert anyone in your organization who is running the image and request that they correct the vulnerability.
Stop the images from running by deleting the deployment or other object that started the pod that the image is in.
NoteIf you delete the pod, it might take several minutes for the vulnerability information to reset on the dashboard.
14.3. Querying image vulnerabilities from the CLI
Using the oc command, you can display information about vulnerabilities detected by the Red Hat Quay Container Security Operator.
Prerequisites
- You have installed the Red Hat Quay Container Security Operator on your OpenShift Container Platform instance.
Procedure
Enter the following command to query for detected container image vulnerabilities:
$ oc get vuln --all-namespacesExample output
NAMESPACE NAME AGE default sha256.ca90... 6m56s skynet sha256.ca90... 9m37sTo display details for a particular vulnerability, append the vulnerability name and its namespace to the
oc describecommand. The following example shows an active container whose image includes an RPM package with a vulnerability:$ oc describe vuln --namespace mynamespace sha256.ac50e3752...Example output
Name: sha256.ac50e3752... Namespace: quay-enterprise ... Spec: Features: Name: nss-util Namespace Name: centos:7 Version: 3.44.0-3.el7 Versionformat: rpm Vulnerabilities: Description: Network Security Services (NSS) is a set of libraries...