Chapter 9. Applying patches with kernel live patching
The Red Hat Enterprise Linux kernel live patching solution patches a running kernel without rebooting or restarting processes. System administrators can immediately apply critical security patches, maintain system uptime, and reduce reboots. Note that not all critical or important CVEs can be addressed through live patching.
Some incompatibilities exist between kernel live patching and other kernel subcomponents. Read the Limitations of kpatch carefully before using kernel live patching.
9.1. Limitations of kpatch
Review the limitations of the kpatch feature to prevent conflicts. * By using the kpatch feature, you can apply simple security and bug fix updates that do not require an immediate system reboot.
-
You must not use the
SystemTaporkprobetool during or after loading a patch. The patch might not take effect until the probes are removed.
9.2. Support for third-party live patching
The kpatch utility is the only kernel live patching utility supported by Red Hat with the RPM modules provided by Red Hat repositories. Red Hat does not support live patches provided by a third party.
9.3. Access to kernel live patches
A kernel module (kmod) implements kernel live patching capability and is provided as an RPM package.
You are provided an access to kernel live patches, which are delivered through the standard channels. However, if you are not subscribed to an extended support offering, you lose access to new patches for the current minor release when the next minor release becomes available. For example, in the standard subscriptions, you are able to live patch RHEL 10.1 kernel until the RHEL 10.2 kernel is released. After the release of RHEL 10.2, live patches for RHEL 10.1 are not available.
The components of kernel live patching are as follows:
- Kernel patch module
- The delivery mechanism for kernel live patches.
- A kernel module built specifically for the kernel being patched.
- The patch module contains the code of the required fixes for the kernel.
-
Patch modules register with the
livepatchkernel subsystem and specify the original functions to replace, along with pointers to the replacement functions. Kernel patch modules are delivered as RPMs. -
The naming convention is
kpatch_<kernel version>_<kpatch version>_<kpatch release>. The "kernel version" part of the name has dots replaced with underscores.
- The
kpatchutility - A command-line utility for managing patch modules.
- The
kpatchservice -
A systemd service required by
multiuser.target. This target loads the kernel patch module at boot time. - The
kpatch-dnfpackage - A DNF plugin delivered in the form of an RPM package. This plugin manages automatic subscription to kernel live patches.
9.4. The process of live patching kernels
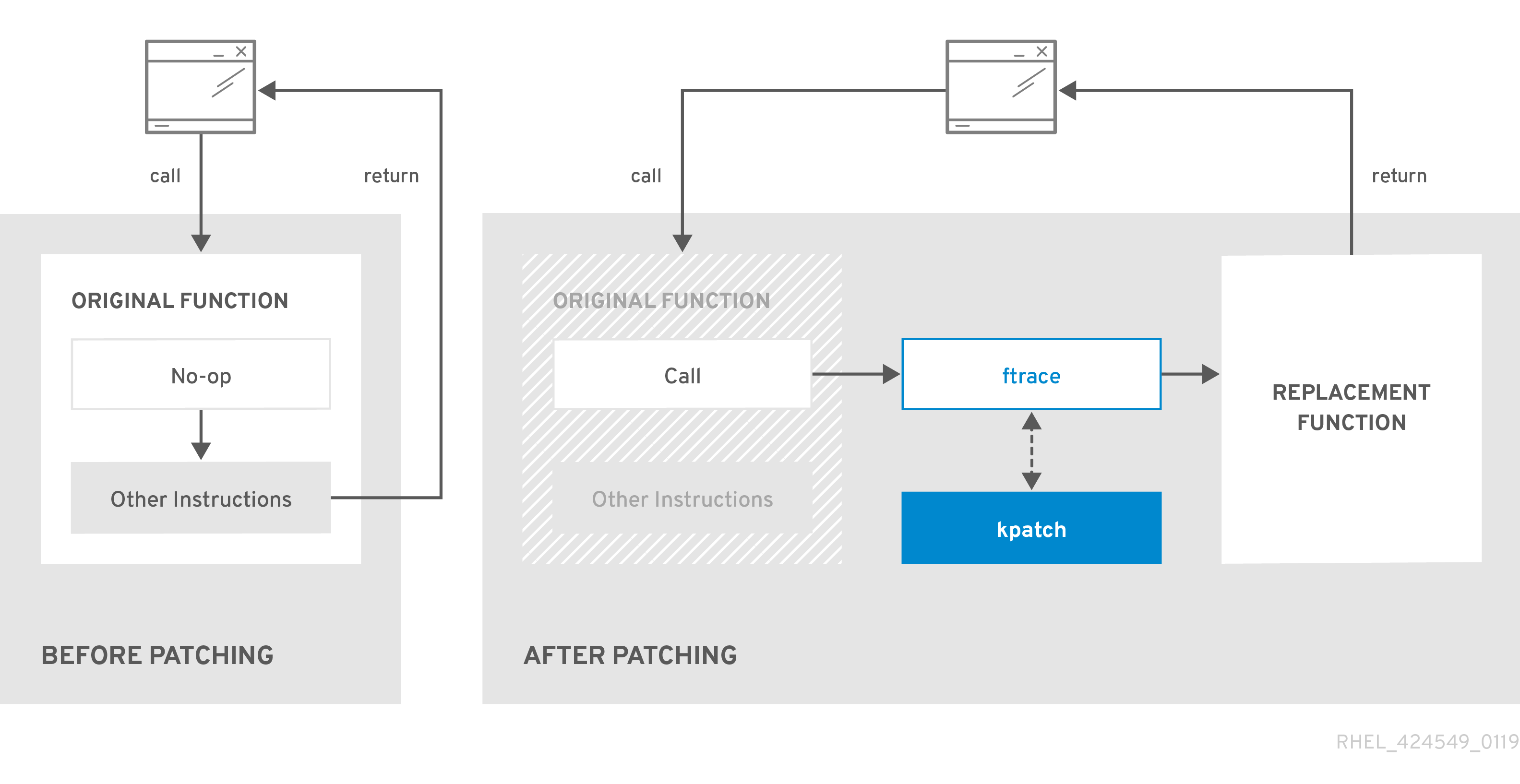
The kpatch kernel patching solution uses the livepatch kernel subsystem to redirect outdated functions to updated ones.
Applying a live kernel patch to a system triggers the following processes:
-
The kernel patch module is copied to the
/var/lib/kpatch/directory and registered for re-application to the kernel by systemd on next boot. -
The
kpatchmodule loads into the running kernel and the new functions are registered to theftracemechanism with a pointer to the location in memory of the new code.
When the kernel accesses the patched function, the ftrace mechanism redirects it, bypassing the original functions and leading the kernel to the patched version of the function.
Figure 9.1. How kernel live patching works
9.5. Applying patches with kernel live patching in the web console
You can configure the kpatch framework, which applies kernel security patches without forcing system restarts, in the RHEL web console.
Prerequisites
You have installed the RHEL 10 web console.
For instructions, see Installing and enabling the web console.
Procedure
- Log in to the RHEL 10 web console.
- Click Software Updates.
Check the status of your kernel patching settings.
- If the patching is not installed, click .
To enable kernel patching, click .

- Select the checkbox for applying kernel patches.
- Select whether you want to apply patches for current and future kernels or the current kernel only. If you decide to subscribe to applying patches for future kernels, the system also applies patches for the upcoming kernel releases.
- Click .
Verification
- Check that the kernel patching is now Enabled in the Settings table of the Software updates section.
9.6. Subscribing the currently installed kernels to the live patching stream
To subscribe installed kernels to the live patching stream, install the specific kernel patch module RPMs. These packages are cumulatively updated.
The following procedure explains how to subscribe to all future cumulative live patching updates for a given kernel. Because live patches are cumulative, you cannot select which individual patches are deployed for a given kernel.
Red Hat does not support any third party live patches applied to a Red Hat supported system.
Prerequisites
- You have root permissions on the system.
Procedure
Optional: Check your kernel version:
# uname -r 6.12.0-55.9.1.el10_0.x86_64Search for a live patching package that corresponds to the version of your kernel:
# dnf search $(uname -r)Install the live patching package:
# dnf install kpatchThis command installs and applies the latest cumulative live patches for that specific kernel only.
If the version of a live patching package is 1-1 or higher, the package will contain a patch module. In that case the kernel will be automatically patched during the installation of the live patching package.
The kernel patch module is also installed into the
/var/lib/kpatch/directory to be loaded by the systemd system and service manager during the future reboots.NoteAn empty live patching package will be installed when there are no live patches available for a given kernel. An empty live patching package will have a kpatch_version-kpatch_release of 0-0, for example
kpatch-patch-6_12_0-1-0-0.x86_64.rpm. The installation of the empty RPM subscribes the system to all future live patches for the given kernel.
Verification
Verify that all installed kernels have been patched:
# kpatch list Loaded patch modules: kpatch_6_12_0_1_0_1 [enabled] Installed patch modules: kpatch_6_12_0_1_0_1 (6.12.0.el10_0.x86_64) …The output shows that the kernel patch module has been loaded into the kernel that is now patched with the latest fixes from the
kpatch-patch-6_12_0-0.el10_0.x86_64.rpmpackage.See the
kpatch(1)man page on your system for more information.NoteEntering the
kpatch listcommand does not return an empty live patching package. Use therpm -qa | grep kpatchcommand instead.# rpm -qa | grep kpatch kpatch-dnf-0.4-3.el10.noarch kpatch-0.9.7-2.el10.noarch kpatch-patch-6_12_0-0.el10_0.x86_64
9.7. Automatically subscribing any future kernel to the live patching stream
To subscribe your system to fixes delivered by the kernel patch module, also known as kernel live patches, you can use the kpatch-dnf DNF plugin. The plugin enables automatic subscription for any kernel the system currently uses, and also for kernels to-be-installed in the future.
Prerequisites
- You have root permissions on the system.
Procedure
Optional: Check all installed kernels and the kernel you are currently running:
# dnf list installed | grep kernel Updating Subscription Management repositories. Installed Packages ... kernel-core.x86_64 6.12.0-55.9.1.el10 @beaker-BaseOS kernel-core.x86_64 6.12.0-55.9.1.el10 @@commandline ... # uname -r 6.12.0-55.9.1.el10_0.x86_64Install the
kpatch-dnfplugin:# dnf install kpatch-dnfEnable automatic subscription to kernel live patches:
# dnf kpatch auto Updating Subscription Management repositories. Last metadata expiration check: 1:38:21 ago on Fri 17 Sep 2021 07:29:53 AM EDT. Dependencies resolved. ================================================== Package Architecture ================================================== Installing: kpatch-patch-6_12_0-1 x86_64 kpatch-patch-6_12_0-2 x86_64 Transaction Summary =================================================== Install 2 Packages …This command subscribes all currently installed kernels to receiving kernel live patches. The command also installs and applies the latest cumulative live patches, if any, for all installed kernels.
When you update the kernel, live patches are installed automatically during the new kernel installation process.
The kernel patch module is also installed into the
/var/lib/kpatch/directory that is loaded by the systemd system and service manager during future reboots.NoteAn empty live patching package will be installed when there are no live patches available for a given kernel. An empty live patching package will have a kpatch_version-kpatch_release of 0-0, for example
kpatch-patch-6_12_0-1-0-0.el10.x86_64.rpm.The installation of the empty RPM subscribes the system to all future live patches for the given kernel.
Verification
Verify that all installed kernels are patched:
# kpatch list Loaded patch modules: kpatch_6_12_0_2_0_1 [enabled] Installed patch modules: kpatch_6_12_0_1_0_1 (6.12.0-0.el10.x86_64) kpatch_6_12_0_2_0_1 (6.12.0-0.el10.x86_64)The output shows that both the kernel you are running, and the other installed kernel have been patched with fixes from
kpatch-patch-6_12_0-1-0-1.el10.x86_64.rpmandkpatch-patch-6_12_0-2-0-1.el10.x86_64.rpmpackages.NoteEntering the
kpatch listcommand does not return an empty live patching package. Use therpm -qa | grep kpatchcommand instead.# rpm -qa | grep kpatch kpatch-dnf-0.9.7_0.4-4.el10.noarch kpatch-0.9.7-4.el10.noarch kpatch-patch-6_12_0_1-0-0.el10_0.x86_64
9.8. Disabling automatic subscription to the live patching stream
To disable the automatic installation of kpatch-patch packages, you can turn off the automatic subscription feature after subscribing to kernel patch module fixes.
Prerequisites
- You have root permissions on the system.
Procedure
Optional: Check all installed kernels and the kernel you are currently running:
# dnf list installed | grep kernelUpdating Subscription Management repositories. Installed Packages ... kernel-core.x86_64 6.12.0-0.el10 @beaker-BaseOS kernel-core.x86_64 6.12.0-0.el10 @@commandline ...# uname -r6.12.0-0.el10_0.x86_64Disable automatic subscription to kernel live patches:
# dnf kpatch manualUpdating Subscription Management repositories.See
kpatch(1)anddnf-kpatch(8)manual pages for more information.
Verification
You can check for the successful outcome:
# yum kpatch status... Updating Subscription Management repositories. Last metadata expiration check: 0:30:41 ago on Tue Jun 14 15:59:26 2022. Kpatch update setting: *manual*
9.9. Updating kernel patch modules
To update kernel patch modules, use the standard RPM update process. These modules are delivered as RPM packages and are cumulative.
Prerequisites
- The system is subscribed to the live patching stream, as described in Subscribing the currently installed kernels to the live patching stream.
Procedure
Update to a new cumulative version for the current kernel:
# dnf update kpatchThis command automatically installs and applies any updates that are available for the currently running kernel. Including any future released cumulative live patches.
Alternatively, update all installed kernel patch modules:
# dnf update kpatchNoteWhen the system reboots into the same kernel, the kernel is automatically live patched again by the
kpatch.servicesystemd service.
9.10. Removing the live patching package
To disable the kernel live patching solution, remove the live patching package.
Prerequisites
- You have root permissions on the system.
- The live patching package is installed.
Procedure
Select the live patching package:
# dnf list installed | grep kpatch-patchkpatch-patch-6.12.0-0.el10_0.x86_64 0-0.el10 @@commandline ...The example output lists live patching packages that you installed.
Remove the live patching package:
# dnf remove kpatch-patch-6.12.0-0.el10_0.x86_64When a live patching package is removed, the kernel remains patched until the next reboot, but the kernel patch module is removed from disk. On future reboot, the corresponding kernel will no longer be patched.
- Reboot your system.
Verify the live patching package is removed:
# dnf list installed | grep kpatch-patchThe command displays no output if the package has been successfully removed.
Verification
Verify the kernel live patching solution is disabled:
# kpatch listLoaded patch modules:The example output shows that the kernel is not patched and the live patching solution is not active because there are no patch modules that are currently loaded.
Currently, Red Hat does not support reverting live patches without rebooting your system. In case of any issues, contact our support team.
9.11. Uninstalling the kernel patch module
To prevent the kernel live patching solution from applying a kernel patch module on subsequent boots, uninstall it.
Prerequisites
- You have root permissions on the system.
- A live patching package is installed.
- A kernel patch module is installed and loaded.
Procedure
Select a kernel patch module:
# kpatch listLoaded patch modules: kpatch_6_12_0_1_0_1 [enabled] Installed patch modules: kpatch_6_12_0_1_0_1 (6.12.0.el10_0.x86_64) ...Uninstall the selected kernel patch module.
# kpatch uninstall kpatch_6_12_0_1_0_1uninstalling kpatch_6_12_0_1_0_1 (6.12.0.el10_0.x86_64)Note that the uninstalled kernel patch module is still loaded:
# kpatch listLoaded patch modules: kpatch_6_12_0_1_0_1 [enabled] Installed patch modules: kpatch_6_12_0_1_0_1 (6.12.0.el10_0.x86_64)When the selected module is uninstalled, the kernel remains patched until the next reboot, but the kernel patch module is removed from disk.
- Reboot your system.
Verification
Verify that the kernel patch module is uninstalled:
# kpatch listLoaded patch modules: ...This example output shows no loaded or installed kernel patch modules, therefore the kernel is not patched and the kernel live patching solution is not active.
9.12. Disabling kpatch.service
To prevent the kernel live patching solution from applying all kernel patch modules globally on subsequent boots, disable the kpatch service.
Prerequisites
- You have root permissions on the system.
- A live patching package is installed.
- A kernel patch module is installed and loaded.
Procedure
Verify
kpatch.serviceis enabled.# systemctl is-enabled kpatch.serviceenabledDisable
kpatch.service:# systemctl disable kpatch.serviceRemoved /etc/systemd/system/multi-user.target.wants/kpatch.service.Note that the applied kernel patch module is still loaded:
# kpatch listLoaded patch modules: kpatch_6_12_0_1_0_1 [enabled] Installed patch modules: kpatch_6_12_0_1_0_1 (6.12.0.el10_0.x86_64)
- Reboot your system.
Optional: Verify the status of
kpatch.service.# systemctl status kpatch.service● kpatch.service - "Apply kpatch kernel patches" Loaded: loaded (/usr/lib/systemd/system/kpatch.service; disabled; vendor preset: disabled) Active: inactive (dead)The example output testifies that
kpatch.serviceis disabled. Thereby, the kernel live patching solution is not active.Verify that the kernel patch module has been unloaded.
# kpatch listLoaded patch modules: Installed patch modules: kpatch_6_12_0_1_0_1 (6.12.0.el10_0.x86_64)The example output shows that a kernel patch module is still installed but the kernel is not patched.
ImportantCurrently, Red Hat does not support reverting live patches without rebooting your system. In case of any issues, contact our support team.