3.3. Using the IPA Web UI
In order to use the web UI, the user must be authenticated with the IPA Kerberos domain and have an active Kerberos ticket (Section 3.2, “Logging into IPA”). Generally, the web UI can only be accessed from an IPA server or client machine and the user must be locally authenticated. There are a couple of ways to work around this, either by configuring Kerberos on a non-domain machine to connect to the Kerberos domain (Section 3.3.4, “Using a Browser on Another System”) or by enabling password authentication to the UI (Section 3.3.5, “Enabling Username/Password Authentication in Your Browser”).
3.3.1. Supported Web Browsers
Copy linkLink copied to clipboard!
The only supported browser to access the IPA web UI is Firefox 3.x or 4.x.
3.3.2. Opening the IPA Web UI
Copy linkLink copied to clipboard!
The browser must be properly configured, as described in Section 3.3.3, “Configuring the Browser”, to support Kerberos authentication so that the user can connect to the UI.
To open the web UI:
- Get a valid Kerberos ticket using
kinit, as in Section 3.2, “Logging into IPA”. - Open the IPA URL. The full URL is
https://IPAserver-FQDN/ipa/ui, but this service is also accessed simply by openinghttps://IPAserver-FQDN. For example:https://server.example.com https://server.example.com/ipa/ui
3.3.3. Configuring the Browser
Copy linkLink copied to clipboard!
Firefox can use Kerberos credentials to authenticate to the IPA UI, but Kerberos negotiation needs to be configured to use the IPA domain. At the first log-in attempt, if Firefox has not been configured to support Kerberos authentication, then an error message appears.
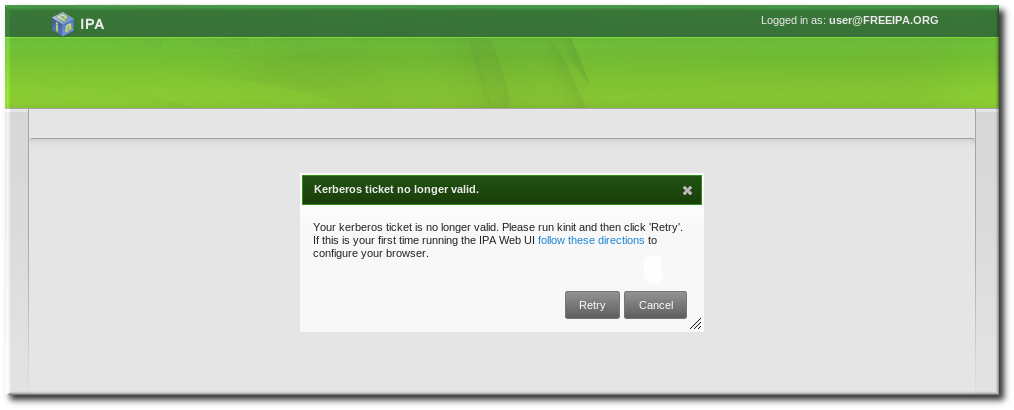
Figure 3.10. Kerberos Authentication Error
If you see that error, then the IPA web UI can perform the required configuration:
- Click the follow these directions link.
- Click the link to import the CA certificate for the IPA server.
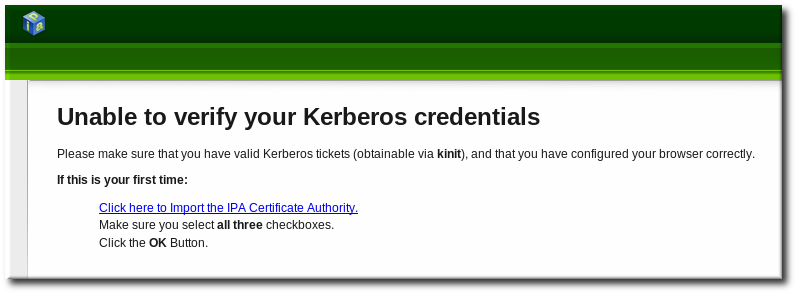
- Set the web site and software developer (first and last) trust bits for the CA certificate.

- Click the Configure Firefox button. This automatically fills out all the
negotiatesettings in the Firefox configuration to use the IPA domain settings.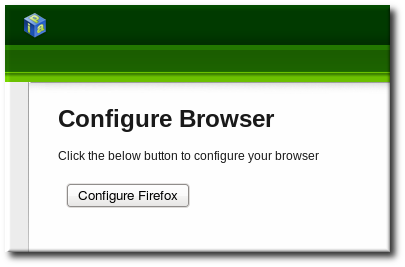 When the process is complete, a success box pops up saying that Firefox has been configured for single sign-on. For there, you are redirected to the IPA web UI.
When the process is complete, a success box pops up saying that Firefox has been configured for single sign-on. For there, you are redirected to the IPA web UI.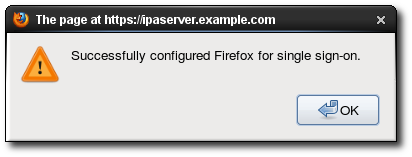
This can also be done manually:
- Open Firefox.
- Type
about:configin the address bar. - In the Search field, type
negotiateto filter out the Kerberos-related parameters. - On Red Hat Enterprise Linux, enter the domain name for the URI parameters, including the preceding period (.) and set the
gsslibparameter to true:network.negotiate-auth.trusted-uris .example.com network.negotiate-auth.delegation-uris .example.com network.negotiate-auth.using-native-gsslib true - Open the web UI by going to the fully-qualified domain name of the IPA server such as
http://ipaserver.example.com. Make sure that you can open the web UI and that there are no Kerberos authentication errors. - Next, download the IPA server's CA certificate from
http://ipa.example.com/ipa/config/ca.crt. - Select the first (Trust this CA to identify web sites) and third (Trust this CA to identify software developers) check boxes.
3.3.4. Using a Browser on Another System
Copy linkLink copied to clipboard!
It is possible to connect to the Identity Management web UI from a system which is not a member of the IPA domain. In this case, it is possible to specify an IPA-specific Kerberos configuration file on the external (non-IPA) machine before running
kinit, and then the user can authenticate against the IPA server domain.
This is especially useful there are multiple realms or overlapping domains across your infrastructure.
- Copy the
/etc/krb5.conffile from the IPA server.# scp /etc/krb5.conf root@externalmachine.example.com:/etc/krb5_ipa.confWarning
Do not overwrite the existingkrb5.conffile. - On the external machine, set the terminal session to use the copied IPA Kerberos configuration file:
$ export KRB5_CONFIG=/etc/krb5_ipa.conf - Configure Firefox on the external machine as in Section 3.3.3, “Configuring the Browser”.
3.3.5. Enabling Username/Password Authentication in Your Browser
Copy linkLink copied to clipboard!
If Kerberos authentication fails, then browser login also fails. That prevents access to the IPA web UI. Configuring username/password authentication for the UI allows users to log in even if there are problems with the Kerberos service.
- Open the
ipa.conffile used by the Apache web service.vim /etc/httpd/conf.d/ipa.conf - In the
<Location "/ipa">location definition, change theKrbMethodK5Passwdattribute from off to on.KrbMethodK5Passwd on - Restart the
httpdservice:# service httpd restart
When this is configured, the web UI prompts for an IPA username and password if it can't detect any Kerberos credentials.
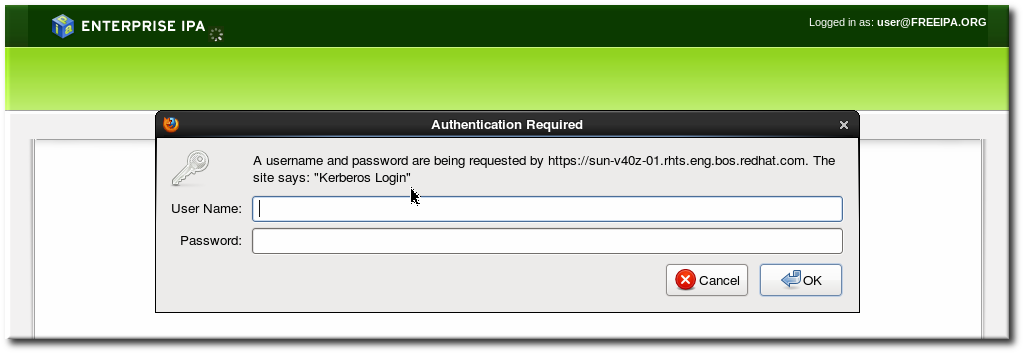
Figure 3.11. IPA Password Prompt
Note
This must be configured on every IPA server in the domain.
3.3.6. Using the UI with Proxy Servers
Copy linkLink copied to clipboard!
Proxy servers can be used to access the web UI without any additional configuration in IPA.
Port forwarding is not supported with the IPA server. However, because it is possible to use proxy servers with IPA, an operation similar to port forwarding can be configured using proxy forwarding with OpenSSH and the SOCKS option. This is described in http://www.meadowy.org/~gotoh/ssh/openssh-socks.html.
3.3.7. Troubleshooting UI Connection Problems
Copy linkLink copied to clipboard!
If negotiate authentication is not working, turn on verbose logging for the authentication process to help diagnose the issue:
- Close all browser windows.
- In a terminal, set the new log levels for Firefox:
export NSPR_LOG_MODULES=negotiateauth:5 export NSPR_LOG_FILE=/tmp/moz.logThis enables verbose logging and logs all information to/tmp/moz.log. - Restart the browser from the same terminal window and attempt t .
Some of the common error messages and workarounds are in Table 3.2, “UI Error Log Messages”.
| Error Log Message | Description and Fix |
|---|---|
| There are no Kerberos tickets. Run kinit. |
| This can occur when you have successfully obtained Kerberos tickets but are still unable to authenticate to the UI. This indicates that there is a problem with the Kerberos configuration. The first place to check is the [domain_realm] section in the /etc/krb5.conf file. Make sure that the IPA Kerberos domain entry is correct and matches the configuration in the Firefox negotiation parameters. For example:
|
| Nothing is in the log file. | It is possible that you are behind a proxy which is removing the HTTP headers required for negotiate authentication. Try to connect to the server using HTTPS instead, which allows the request to pass through unmodified. Then check the log file again. |