5.3. Viewing the Current Status and Settings of firewalld
5.3.1. Viewing the Current Status of firewalld
Copy linkLink copied to clipboard!
The firewall service,
firewalld, is installed on the system by default. Use the firewalld CLI interface to check that the service is running.
To see the status of the service:
~]# firewall-cmd --state
For more information about the service status, use the
systemctl status sub-command:
~]# systemctl status firewalld
firewalld.service - firewalld - dynamic firewall daemon
Loaded: loaded (/usr/lib/systemd/system/firewalld.service; enabled; vendor pr
Active: active (running) since Mon 2017-12-18 16:05:15 CET; 50min ago
Docs: man:firewalld(1)
Main PID: 705 (firewalld)
Tasks: 2 (limit: 4915)
CGroup: /system.slice/firewalld.service
└─705 /usr/bin/python3 -Es /usr/sbin/firewalld --nofork --nopid
Furthermore, it is important to know how
firewalld is set up and which rules are in force before you try to edit the settings. To display the firewall settings, see Section 5.3.2, “Viewing Current firewalld Settings”
5.3.2. Viewing Current firewalld Settings
Copy linkLink copied to clipboard!
5.3.2.1. Viewing Allowed Services using GUI
Copy linkLink copied to clipboard!
To view the list of services using the graphical firewall-config tool, press the Super key to enter the Activities Overview, type
firewall, and press Enter. The firewall-config tool appears. You can now view the list of services under the tab.
Alternatively, to start the graphical firewall configuration tool using the command-line, enter the following command:
~]$ firewall-config
The Firewall Configuration window opens. Note that this command can be run as a normal user, but you are prompted for an administrator password occasionally.
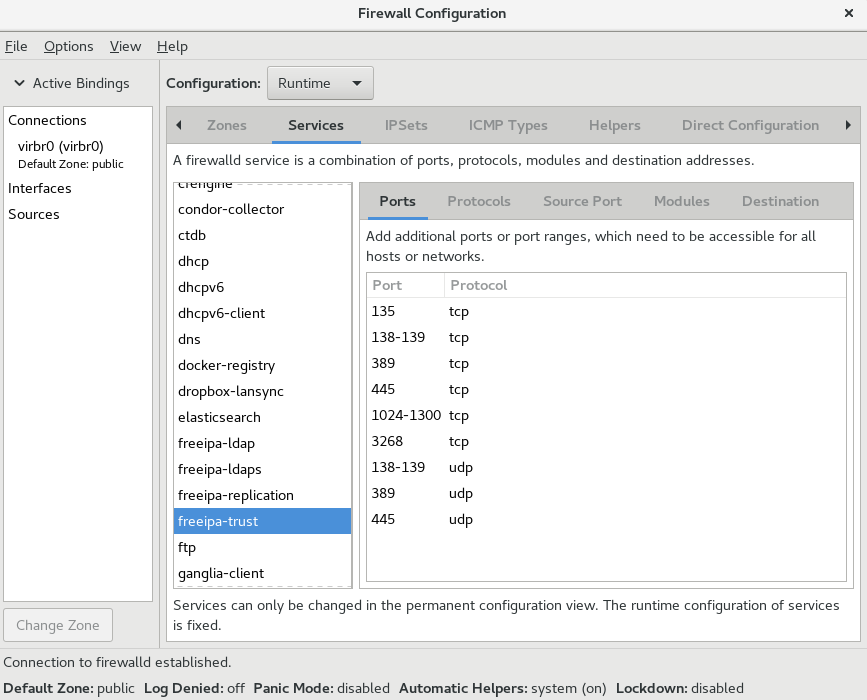
Figure 5.2. The Services tab in firewall-config
5.3.2.2. Viewing firewalld Settings using CLI
Copy linkLink copied to clipboard!
With the CLI client, it is possible to get different views of the current firewall settings. The
--list-all option shows a complete overview of the firewalld settings.
firewalld uses zones to manage the traffic. If a zone is not specified by the --zone option, the command is effective in the default zone assigned to the active network interface and connection.
To list all the relevant information for the default zone:
~]# firewall-cmd --list-all
public
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh dhcpv6-client
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:Note
To specify the zone for which to display the settings, add the
--zone=zone-name argument to the firewall-cmd --list-all command, for example:
~]# firewall-cmd --list-all --zone=home
home
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh mdns samba-client dhcpv6-client
... [output truncated]
To see the settings for particular information, such as services or ports, use a specific option. See the
firewalld manual pages or get a list of the options using the command help:
~]# firewall-cmd --help
Usage: firewall-cmd [OPTIONS...]
General Options
-h, --help Prints a short help text and exists
-V, --version Print the version string of firewalld
-q, --quiet Do not print status messages
Status Options
--state Return and print firewalld state
--reload Reload firewall and keep state information
... [output truncated]
For example, to see which services are allowed in the current zone:
~]# firewall-cmd --list-services
ssh dhcpv6-client
Listing the settings for a certain subpart using the CLI tool can sometimes be difficult to interpret. For example, you allow the
SSH service and firewalld opens the necessary port (22) for the service. Later, if you list the allowed services, the list shows the SSH service, but if you list open ports, it does not show any. Therefore, it is recommended to use the --list-all option to make sure you receive a complete information.