Securing Red Hat Quay
Securing Red Hat Quay
Abstract
Preface
Red Hat Quay offers administrators the ability to secure communication and trusted access to their repositories through the use of Transport Layer Security (TLS), certificate management, and encryption techniques. Properly configuring SSL/TLS and implementing custom certificates can help safeguard data, secure external connections, and maintain trust between Red Hat Quay and the integrated services of your choosing.
The following topics are covered:
- Configuring custom SSL/TLS certificates for standalone Red Hat Quay deployments
- Configuring custom SSL/TLS certificates for Red Hat Quay on OpenShift Container Platform
- Adding additional Certificate Authorities to the Red Hat Quay container
- Adding additional Certificate Authorities to Red Hat Quay on OpenShift Container Platform
Chapter 1. SSL and TLS for Red Hat Quay
The Secure Sockets Layer (SSL) protocol was originally developed by Netscape Corporation to provide a mechanism for secure communication over the Internet. Subsequently, the protocol was adopted by the Internet Engineering Task Force (IETF) and renamed to Transport Layer Security (TLS).
TLS (Transport Layer Security) is a cryptographic protocol used to secure network communications. When hardening system security settings by configuring preferred key-exchange protocols, authentication methods, and encryption algorithms, it is necessary to bear in mind that the broader the range of supported clients, the lower the resulting security. Conversely, strict security settings lead to limited compatibility with clients, which can result in some users being locked out of the system. Be sure to target the strictest available configuration and only relax it when it is required for compatibility reasons.
Red Hat Quay can be configured to use SSL/TLS certificates to ensure secure communication between clients and the Red Hat Quay server. This configuration involves the use of valid SSL/TLS certificates, which can be obtained from a trusted Certificate Authority (CA) or generated as self-signed certificates for internal use.
1.1. Creating a Certificate Authority
Use the following procedure to set up your own CA and use it to issue a server certificate for your domain. This allows you to secure communications with SSL/TLS using your own certificates.
Procedure
Generate the root CA key by entering the following command:
openssl genrsa -out rootCA.key 2048
$ openssl genrsa -out rootCA.key 2048Copy to Clipboard Copied! Toggle word wrap Toggle overflow Generate the root CA certificate by entering the following command:
openssl req -x509 -new -nodes -key rootCA.key -sha256 -days 1024 -out rootCA.pem
$ openssl req -x509 -new -nodes -key rootCA.key -sha256 -days 1024 -out rootCA.pemCopy to Clipboard Copied! Toggle word wrap Toggle overflow Enter the information that will be incorporated into your certificate request, including the server hostname, for example:
Copy to Clipboard Copied! Toggle word wrap Toggle overflow Generate the server key by entering the following command:
openssl genrsa -out ssl.key 2048
$ openssl genrsa -out ssl.key 2048Copy to Clipboard Copied! Toggle word wrap Toggle overflow Generate a signing request by entering the following command:
openssl req -new -key ssl.key -out ssl.csr
$ openssl req -new -key ssl.key -out ssl.csrCopy to Clipboard Copied! Toggle word wrap Toggle overflow Enter the information that will be incorporated into your certificate request, including the server hostname, for example:
Copy to Clipboard Copied! Toggle word wrap Toggle overflow Create a configuration file
openssl.cnf, specifying the server hostname, for example:Example
openssl.cnffileCopy to Clipboard Copied! Toggle word wrap Toggle overflow Use the configuration file to generate the certificate
ssl.cert:openssl x509 -req -in ssl.csr -CA rootCA.pem -CAkey rootCA.key -CAcreateserial -out ssl.cert -days 356 -extensions v3_req -extfile openssl.cnf
$ openssl x509 -req -in ssl.csr -CA rootCA.pem -CAkey rootCA.key -CAcreateserial -out ssl.cert -days 356 -extensions v3_req -extfile openssl.cnfCopy to Clipboard Copied! Toggle word wrap Toggle overflow Confirm your created certificates and files by entering the following command:
ls /path/to/certificates
$ ls /path/to/certificatesCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
rootCA.key ssl-bundle.cert ssl.key custom-ssl-config-bundle-secret.yaml rootCA.pem ssl.cert openssl.cnf rootCA.srl ssl.csr
rootCA.key ssl-bundle.cert ssl.key custom-ssl-config-bundle-secret.yaml rootCA.pem ssl.cert openssl.cnf rootCA.srl ssl.csrCopy to Clipboard Copied! Toggle word wrap Toggle overflow
1.2. Configuring SSL/TLS for standalone Red Hat Quay deployments
For standalone Red Hat Quay deployments, SSL/TLS certificates must be configured by using the command-line interface and by updating your config.yaml file manually.
1.2.1. Configuring custom SSL/TLS certificates by using the command line interface
SSL/TLS must be configured by using the command-line interface (CLI) and updating your config.yaml file manually.
Prerequisites
- You have created a certificate authority and signed the certificate.
Procedure
Copy the certificate file and primary key file to your configuration directory, ensuring they are named
ssl.certandssl.keyrespectively:cp ~/ssl.cert ~/ssl.key /path/to/configuration_directory
cp ~/ssl.cert ~/ssl.key /path/to/configuration_directoryCopy to Clipboard Copied! Toggle word wrap Toggle overflow Navigate to the configuration directory by entering the following command:
cd /path/to/configuration_directory
$ cd /path/to/configuration_directoryCopy to Clipboard Copied! Toggle word wrap Toggle overflow Edit the
config.yamlfile and specify that you want Red Hat Quay to handle SSL/TLS:Example
config.yamlfile# ... SERVER_HOSTNAME: <quay-server.example.com> ... PREFERRED_URL_SCHEME: https # ...
# ... SERVER_HOSTNAME: <quay-server.example.com> ... PREFERRED_URL_SCHEME: https # ...Copy to Clipboard Copied! Toggle word wrap Toggle overflow Optional: Append the contents of the
rootCA.pemfile to the end of thessl.certfile by entering the following command:cat rootCA.pem >> ssl.cert
$ cat rootCA.pem >> ssl.certCopy to Clipboard Copied! Toggle word wrap Toggle overflow Stop the
Quaycontainer by entering the following command:sudo podman stop <quay_container_name>
$ sudo podman stop <quay_container_name>Copy to Clipboard Copied! Toggle word wrap Toggle overflow Restart the registry by entering the following command:
sudo podman run -d --rm -p 80:8080 -p 443:8443 \ --name=quay \ -v $QUAY/config:/conf/stack:Z \ -v $QUAY/storage:/datastorage:Z \ registry.redhat.io/quay/quay-rhel8:v3.13.9
$ sudo podman run -d --rm -p 80:8080 -p 443:8443 \ --name=quay \ -v $QUAY/config:/conf/stack:Z \ -v $QUAY/storage:/datastorage:Z \ registry.redhat.io/quay/quay-rhel8:v3.13.9Copy to Clipboard Copied! Toggle word wrap Toggle overflow
1.2.2. Configuring Podman to trust the Certificate Authority
Podman uses two paths to locate the Certificate Authority (CA) file: /etc/containers/certs.d/ and /etc/docker/certs.d/. Use the following procedure to configure Podman to trust the CA.
Procedure
Copy the root CA file to one of
/etc/containers/certs.d/or/etc/docker/certs.d/. Use the exact path determined by the server hostname, and name the fileca.crt:sudo cp rootCA.pem /etc/containers/certs.d/quay-server.example.com/ca.crt
$ sudo cp rootCA.pem /etc/containers/certs.d/quay-server.example.com/ca.crtCopy to Clipboard Copied! Toggle word wrap Toggle overflow Verify that you no longer need to use the
--tls-verify=falseoption when logging in to your Red Hat Quay registry:sudo podman login quay-server.example.com
$ sudo podman login quay-server.example.comCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
Login Succeeded!
Login Succeeded!Copy to Clipboard Copied! Toggle word wrap Toggle overflow
1.2.3. Configuring the system to trust the certificate authority
Use the following procedure to configure your system to trust the certificate authority.
Procedure
Enter the following command to copy the
rootCA.pemfile to the consolidated system-wide trust store:sudo cp rootCA.pem /etc/pki/ca-trust/source/anchors/
$ sudo cp rootCA.pem /etc/pki/ca-trust/source/anchors/Copy to Clipboard Copied! Toggle word wrap Toggle overflow Enter the following command to update the system-wide trust store configuration:
sudo update-ca-trust extract
$ sudo update-ca-trust extractCopy to Clipboard Copied! Toggle word wrap Toggle overflow Optional. You can use the
trust listcommand to ensure that theQuayserver has been configured:trust list | grep quay label: quay-server.example.com$ trust list | grep quay label: quay-server.example.comCopy to Clipboard Copied! Toggle word wrap Toggle overflow Now, when you browse to the registry at
https://quay-server.example.com, the lock icon shows that the connection is secure: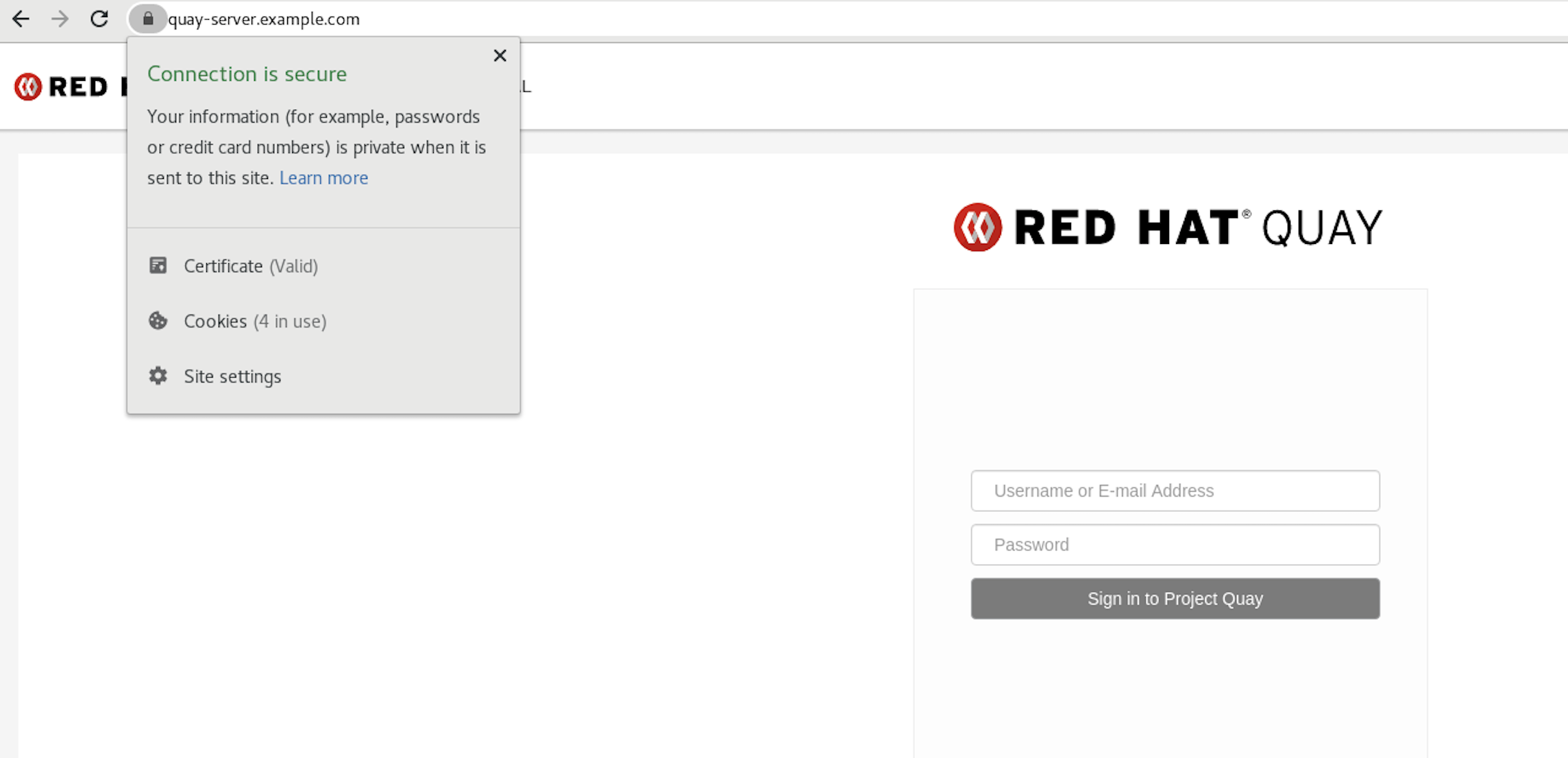
To remove the
rootCA.pemfile from system-wide trust, delete the file and update the configuration:sudo rm /etc/pki/ca-trust/source/anchors/rootCA.pem
$ sudo rm /etc/pki/ca-trust/source/anchors/rootCA.pemCopy to Clipboard Copied! Toggle word wrap Toggle overflow sudo update-ca-trust extract
$ sudo update-ca-trust extractCopy to Clipboard Copied! Toggle word wrap Toggle overflow trust list | grep quay
$ trust list | grep quayCopy to Clipboard Copied! Toggle word wrap Toggle overflow
More information can be found in the RHEL 9 documentation in the chapter Using shared system certificates.
1.3. Configuring custom SSL/TLS certificates for Red Hat Quay on OpenShift Container Platform
When Red Hat Quay is deployed on OpenShift Container Platform, the tls component of the QuayRegistry custom resource definition (CRD) is set to managed by default. As a result, OpenShift Container Platform’s Certificate Authority is used to create HTTPS endpoints and to rotate SSL/TLS certificates.
You can configure custom SSL/TLS certificates before or after the initial deployment of Red Hat Quay on OpenShift Container Platform. This process involves creating or updating the configBundleSecret resource within the QuayRegistry YAML file to integrate your custom certificates and setting the tls component to unmanaged.
When configuring custom SSL/TLS certificates for Red Hat Quay, administrators are responsible for certificate rotation.
The following procedures enable you to apply custom SSL/TLS certificates to ensure secure communication and meet specific security requirements for your Red Hat Quay on OpenShift Container Platform deployment. These steps assumed you have already created a Certificate Authority (CA) bundle or an ssl.key, and an ssl.cert. The procedure then shows you how to integrate those files into your Red Hat Quay on OpenShift Container Platform deployment, which ensures that your registry operates with the specified security settings and conforms to your organization’s SSL/TLS policies.
-
The following procedure is used for securing Red Hat Quay with an HTTPS certificate. Note that this differs from managing Certificate Authority Trust Bundles. CA Trust Bundles are used by system processes within the
Quaycontainer to verify certificates against trusted CAs, and ensure that services like LDAP, storage backend, and OIDC connections are trusted. -
If you are adding the certificates to an existing deployment, you must include the existing
config.yamlfile in the new config bundle secret, even if you are not making any configuration changes.
1.3.1. Creating a custom SSL/TLS configBundleSecret resource
After creating your custom SSL/TLS certificates, you can create a custom configBundleSecret resource for Red Hat Quay on OpenShift Container Platform, which allows you to upload ssl.cert and ssl.key files.
Prerequisites
-
You have base64 decoded the original config bundle into a
config.yamlfile. For more information, see Downloading the existing configuration. - You have generated custom SSL certificates and keys.
Procedure
Create a new YAML file, for example,
custom-ssl-config-bundle-secret.yaml:touch custom-ssl-config-bundle-secret.yaml
$ touch custom-ssl-config-bundle-secret.yamlCopy to Clipboard Copied! Toggle word wrap Toggle overflow Create the
custom-ssl-config-bundle-secretresource.Create the resource by entering the following command:
Copy to Clipboard Copied! Toggle word wrap Toggle overflow - 1
- Where
<config.yaml>is yourbase64 decodedconfig.yamlfile. - 2
- Where
<ssl.cert>is yourssl.certfile. - 3
- Optional. The
--from-file=extra_ca_cert_<name-of-certificate>.crt=ca-certificate-bundle.crtfield allows Red Hat Quay to recognize custom Certificate Authority (CA) files. If you are using LDAP, OIDC, or another service that uses custom CAs, you must add them via theextra_ca_certpath. For more information, see "Adding additional Certificate Authorities to Red Hat Quay on OpenShift Container Platform." - 4
- Where
<ssl.key>is yourssl.keyfile.
Optional. You can check the content of the
custom-ssl-config-bundle-secret.yamlfile by entering the following command:cat custom-ssl-config-bundle-secret.yaml
$ cat custom-ssl-config-bundle-secret.yamlCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
Copy to Clipboard Copied! Toggle word wrap Toggle overflow Create the
configBundleSecretresource by entering the following command:oc create -n <namespace> -f custom-ssl-config-bundle-secret.yaml
$ oc create -n <namespace> -f custom-ssl-config-bundle-secret.yamlCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
secret/custom-ssl-config-bundle-secret created
secret/custom-ssl-config-bundle-secret createdCopy to Clipboard Copied! Toggle word wrap Toggle overflow Update the
QuayRegistryYAML file to reference thecustom-ssl-config-bundle-secretobject by entering the following command:oc patch quayregistry <registry_name> -n <namespace> --type=merge -p '{"spec":{"configBundleSecret":"custom-ssl-config-bundle-secret"}}'$ oc patch quayregistry <registry_name> -n <namespace> --type=merge -p '{"spec":{"configBundleSecret":"custom-ssl-config-bundle-secret"}}'Copy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
quayregistry.quay.redhat.com/example-registry patched
quayregistry.quay.redhat.com/example-registry patchedCopy to Clipboard Copied! Toggle word wrap Toggle overflow Set the
tlscomponent of theQuayRegistryYAML toFalseby entering the following command:oc patch quayregistry <registry_name> -n <namespace> --type=merge -p '{"spec":{"components":[{"kind":"tls","managed":false}]}}'$ oc patch quayregistry <registry_name> -n <namespace> --type=merge -p '{"spec":{"components":[{"kind":"tls","managed":false}]}}'Copy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
quayregistry.quay.redhat.com/example-registry patched
quayregistry.quay.redhat.com/example-registry patchedCopy to Clipboard Copied! Toggle word wrap Toggle overflow Ensure that your
QuayRegistryYAML file has been updated to use the custom SSLconfigBundleSecretresource, and that your andtlsresource is set toFalseby entering the following command:oc get quayregistry <registry_name> -n <namespace> -o yaml
$ oc get quayregistry <registry_name> -n <namespace> -o yamlCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
Copy to Clipboard Copied! Toggle word wrap Toggle overflow
Verification
Confirm a TLS connection to the server and port by entering the following command:
openssl s_client -connect <quay-server.example.com>:443
$ openssl s_client -connect <quay-server.example.com>:443Copy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
Copy to Clipboard Copied! Toggle word wrap Toggle overflow
Chapter 2. Certificate-based authentication between Red Hat Quay and SQL
Red Hat Quay administrators can configure certificate-based authentication between Red Hat Quay and SQL (PostgreSQL and GCP CloudSQL) by supplying their own SSL/TLS certificates for client-side authentication. This provides enhanced security and allows for easier automation for your Red Hat Quay registry.
The following sections shows you how to configure certificate-based authentication between Red Hat Quay and PostgreSQL, and Red Hat Quay and CloudSQL.
2.1. Configuring certificate-based authentication with SQL
The following procedure demonstrates how to connect Red Hat Quay with an SQL database using secure client-side certificates. This method ensures both connectivity and authentication through Certificate Trust Verification, as it verifies the SQL server’s certificate against a trusted Certificate Authority (CA). This enhances the security of the connection between Red Hat Quay and your SQL server while simplifying automation for your deployment. Although the example uses Google Cloud Platform’s CloudSQL, the procedure also applies to PostgreSQL and other supported databases.
Prerequisites
-
You have generated custom Certificate Authorities (CAs) and your SSL/TLS certificates and keys are available in
PEMformat that will be used to generate an SSL connection with your CloudSQL database. For more information, see SSL and TLS for Red Hat Quay. -
You have
base64 decodedthe original config bundle into aconfig.yamlfile. For more information, see Downloading the existing configuration. -
You are using an externally managed PostgreSQL or CloudSQL database. For more information, see Using and existing PostgreSQL database with the
DB_URIvariable set. - Your externally managed PostgreSQL or CloudSQL database is configured for SSL/TLS.
-
The
postgrescomponent of yourQuayRegistryCRD is set tomanaged: false, and your CloudSQL database is set with theDB_URIconfiguration variable. The following procedure usespostgresql://<cloudsql_username>:<dbpassword>@<database_host>:<port>/<database_name>.
Procedure
After you have generated the CAs and SSL/TLS certificates and keys for your CloudSQL database and ensured that they are in
.pemformat, test the SSL connection to your CloudSQL server:Initiate a connection to your CloudSQL server by entering the following command:
psql "sslmode=verify-ca sslrootcert=<ssl_server_certificate_authority>.pem sslcert=<ssl_client_certificate>.pem sslkey=<ssl_client_key>.pem hostaddr=<database_host> port=<5432> user=<cloudsql_username> dbname=<cloudsql_database_name>"
$ psql "sslmode=verify-ca sslrootcert=<ssl_server_certificate_authority>.pem sslcert=<ssl_client_certificate>.pem sslkey=<ssl_client_key>.pem hostaddr=<database_host> port=<5432> user=<cloudsql_username> dbname=<cloudsql_database_name>"Copy to Clipboard Copied! Toggle word wrap Toggle overflow
In your Red Hat Quay directory, create a new YAML file, for example,
quay-config-bundle.yaml, by running the following command:touch quay-config-bundle.yaml
$ touch quay-config-bundle.yamlCopy to Clipboard Copied! Toggle word wrap Toggle overflow Create a
postgresql-client-certsresource by entering the following command:oc -n <quay_namespace> create secret generic postgresql-client-certs \ --from-file config.yaml=<path/to/config.yaml> --from-file=tls.crt=<path/to/ssl_client_certificate.pem> --from-file=tls.key=<path/to/ssl_client_key.pem> --from-file=ca.crt=<path/to/ssl_server_certificate.pem>
$ oc -n <quay_namespace> create secret generic postgresql-client-certs \ --from-file config.yaml=<path/to/config.yaml>1 --from-file=tls.crt=<path/to/ssl_client_certificate.pem>2 --from-file=tls.key=<path/to/ssl_client_key.pem>3 --from-file=ca.crt=<path/to/ssl_server_certificate.pem>4 Copy to Clipboard Copied! Toggle word wrap Toggle overflow Edit your
`quay-config-bundle.yamlfile to include the following database connection settings:Important-
The information included in the
DB_CONNECTION_ARGSvariable, for example,sslmode,sslrootcert,sslcert, andsslkeymust match the information appended to theDB_URIvariable. Failure to match might result in a failed connection. -
You cannot specify custom filenames or paths. Certificate file paths for
sslrootcert,sslcert, andsslkeyare hardcoded defaults and mounted into theQuaypod from the Kubernetes secret. You must adhere to the following naming conventions or it will result in a failed connection.
Copy to Clipboard Copied! Toggle word wrap Toggle overflow - 1
- Using
verify-caensures that the database connection uses SSL/TLS and verifies the server certificate against a trusted CA. This can work with both trusted CA and self-signed CA certificates. However, this mode does not verify the hostname of the server. For full hostname and certificate verification, useverify-full. For more information about the configuration options available, see PostgreSQL SSL/TLS connection arguments. - 2
- The
root.crtfile contains the root certificate used to verify the SSL/TLS connection with your CloudSQL database. This file is mounted in theQuaypod from the Kubernetes secret. - 3
- The
postgresql.crtfile contains the client certificate used to authenticate the connection to your CloudSQL database. This file is mounted in theQuaypod from the Kubernetes secret. - 4
- The
postgresql.keyfile contains the private key associated with the client certificate. This file is mounted in theQuaypod from the Kubernetes secret. - 5
- Enables auto-rollback for connections.
- 6
- The URI that accesses your CloudSQL database. Must be appended with the
sslmodetype, yourroot.crt,postgresql.crt, andpostgresql.keyfiles. The SSL/TLS information included inDB_URImust match the information provided inDB_CONNECTION_ARGS. If you are using CloudSQL, you must include your database username and password in this variable.
-
The information included in the
Create the
configBundleSecretresource by entering the following command:oc create -n <namespace> -f quay-config-bundle.yaml
$ oc create -n <namespace> -f quay-config-bundle.yamlCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
secret/quay-config-bundle created
secret/quay-config-bundle createdCopy to Clipboard Copied! Toggle word wrap Toggle overflow Update the
QuayRegistryYAML file to reference thequay-config-bundleobject by entering the following command:oc patch quayregistry <registry_name> -n <namespace> --type=merge -p '{"spec":{"configBundleSecret":"quay-config-bundle"}}'$ oc patch quayregistry <registry_name> -n <namespace> --type=merge -p '{"spec":{"configBundleSecret":"quay-config-bundle"}}'Copy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
quayregistry.quay.redhat.com/example-registry patched
quayregistry.quay.redhat.com/example-registry patchedCopy to Clipboard Copied! Toggle word wrap Toggle overflow Ensure that your
QuayRegistryYAML file has been updated to use the extra CA certificateconfigBundleSecretresource by entering the following command:oc get quayregistry <registry_name> -n <namespace> -o yaml
$ oc get quayregistry <registry_name> -n <namespace> -o yamlCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
# ... configBundleSecret: quay-config-bundle # ...
# ... configBundleSecret: quay-config-bundle # ...Copy to Clipboard Copied! Toggle word wrap Toggle overflow
Chapter 3. Adding additional Certificate Authorities for Red Hat Quay
Certificate Authorities (CAs) are used by Red Hat Quay to verify SSL/TLS connections with external services, like ODIC providers, LDAP providers, storage providers, and so on.
The following sections provide information about uploading additional CAs to Red Hat Quay depending on your deployment type.
3.1. Adding additional Certificate Authorities to the Red Hat Quay container
The extra_ca_certs directory is the directory where additional Certificate Authorities (CAs) can be stored to extend the set of trusted certificates. These certificates are used by Red Hat Quay to verify SSL/TLS connections with external services. When deploying Red Hat Quay, you can place the necessary CAs in this directory to ensure that connections to services like LDAP, OIDC, and storage systems are properly secured and validated.
For standalone Red Hat Quay deployments, you must create this directory and copy the additional CA certificates into that directory.
Prerequisites
- You have a CA for the desired service.
Procedure
View the certificate to be added to the container by entering the following command:
cat storage.crt
$ cat storage.crtCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
-----BEGIN CERTIFICATE----- MIIDTTCCAjWgAwIBAgIJAMVr9ngjJhzbMA0GCSqGSIb3DQEBCwUAMD0xCzAJBgNV... -----END CERTIFICATE-----
-----BEGIN CERTIFICATE----- MIIDTTCCAjWgAwIBAgIJAMVr9ngjJhzbMA0GCSqGSIb3DQEBCwUAMD0xCzAJBgNV... -----END CERTIFICATE-----Copy to Clipboard Copied! Toggle word wrap Toggle overflow Create the
extra_ca_certsin the/configfolder of your Red Hat Quay directory by entering the following command:mkdir -p /path/to/quay_config_folder/extra_ca_certs
$ mkdir -p /path/to/quay_config_folder/extra_ca_certsCopy to Clipboard Copied! Toggle word wrap Toggle overflow Copy the CA file to the
extra_ca_certsfolder. For example:cp storage.crt /path/to/quay_config_folder/extra_ca_certs/
$ cp storage.crt /path/to/quay_config_folder/extra_ca_certs/Copy to Clipboard Copied! Toggle word wrap Toggle overflow Ensure that the
storage.crtfile exists within theextra_ca_certsfolder by entering the following command:tree /path/to/quay_config_folder/extra_ca_certs
$ tree /path/to/quay_config_folder/extra_ca_certsCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
/path/to/quay_config_folder/extra_ca_certs ├── storage.crt----
/path/to/quay_config_folder/extra_ca_certs ├── storage.crt----Copy to Clipboard Copied! Toggle word wrap Toggle overflow Obtain the
CONTAINER IDof yourQuayconsider by entering the following command:podman ps
$ podman psCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS 5a3e82c4a75f <registry>/<repo>/quay:{productminv} "/sbin/my_init" 24 hours ago Up 18 hours 0.0.0.0:80->80/tcp, 0.0.0.0:443->443/tcp, 443/tcp grave_kellerCONTAINER ID IMAGE COMMAND CREATED STATUS PORTS 5a3e82c4a75f <registry>/<repo>/quay:{productminv} "/sbin/my_init" 24 hours ago Up 18 hours 0.0.0.0:80->80/tcp, 0.0.0.0:443->443/tcp, 443/tcp grave_kellerCopy to Clipboard Copied! Toggle word wrap Toggle overflow Restart the container by entering the following command
podman restart 5a3e82c4a75f
$ podman restart 5a3e82c4a75fCopy to Clipboard Copied! Toggle word wrap Toggle overflow Confirm that the certificate was copied into the container namespace by running the following command:
podman exec -it 5a3e82c4a75f cat /etc/ssl/certs/storage.pem
$ podman exec -it 5a3e82c4a75f cat /etc/ssl/certs/storage.pemCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
-----BEGIN CERTIFICATE----- MIIDTTCCAjWgAwIBAgIJAMVr9ngjJhzbMA0GCSqGSIb3DQEBCwUAMD0xCzAJBgNV... -----END CERTIFICATE-----
-----BEGIN CERTIFICATE----- MIIDTTCCAjWgAwIBAgIJAMVr9ngjJhzbMA0GCSqGSIb3DQEBCwUAMD0xCzAJBgNV... -----END CERTIFICATE-----Copy to Clipboard Copied! Toggle word wrap Toggle overflow
3.2. Adding additional Certificate Authorities to Red Hat Quay on OpenShift Container Platform
On Red Hat Quay on OpenShift Container Platform, the extra_ca_certs configuration field is is used to populate additional Certificate Authorities (CAs) into the CA directory, which then adds the CAs into the system trust bundle. These certificates are used by Red Hat Quay to verify SSL/TLS connections with external services like LDAP, OIDC, and storage systems.
When deploying or redeploying Red Hat Quay on OpenShift Container Platform, you can add one, or multiple, CAs into the CA directory to ensure that external services are properly secured and validated. On Red Hat Quay on OpenShift Container Platform deployments, you must manually add the extra_ca_certs configuration field to your config.yaml file and re-upload the config.yaml to OpenShift Container Platform.
The following procedures show you how to download your existing configuration file, add additional CAs to your Red Hat Quay on OpenShift Container Platform deployment, and then re-upload the configuration file.
3.2.1. Downloading the existing configuration
The following procedure shows you how to download the existing configuration by locating the Config Bundle Secret.
Procedure
Describe the
QuayRegistryresource by entering the following command:oc describe quayregistry -n <quay_namespace>
$ oc describe quayregistry -n <quay_namespace>Copy to Clipboard Copied! Toggle word wrap Toggle overflow # ... Config Bundle Secret: example-registry-config-bundle-v123x # ...
# ... Config Bundle Secret: example-registry-config-bundle-v123x # ...Copy to Clipboard Copied! Toggle word wrap Toggle overflow Obtain the secret data by entering the following command:
oc get secret -n <quay_namespace> <example-registry-config-bundle-v123x> -o jsonpath='{.data}'$ oc get secret -n <quay_namespace> <example-registry-config-bundle-v123x> -o jsonpath='{.data}'Copy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
{ "config.yaml": "RkVBVFVSRV9VU0 ... MDAwMAo=" }{ "config.yaml": "RkVBVFVSRV9VU0 ... MDAwMAo=" }Copy to Clipboard Copied! Toggle word wrap Toggle overflow Decode the data by entering the following command:
echo 'RkVBVFVSRV9VU0 ... MDAwMAo=' | base64 --decode
$ echo 'RkVBVFVSRV9VU0 ... MDAwMAo=' | base64 --decodeCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
Copy to Clipboard Copied! Toggle word wrap Toggle overflow Optional. You can export the data into a YAML file into the current directory by passing in the
>> config.yamlflag. For example:echo 'RkVBVFVSRV9VU0 ... MDAwMAo=' | base64 --decode >> config.yaml
$ echo 'RkVBVFVSRV9VU0 ... MDAwMAo=' | base64 --decode >> config.yamlCopy to Clipboard Copied! Toggle word wrap Toggle overflow
3.2.2. Adding additional Certificate Authorities to Red Hat Quay on OpenShift Container Platform
The following example shows you how to add additional Certificate Authorities to your Red Hat Quay on OpenShift Container Platform deployment.
Prerequisites
-
You have base64 decoded the original config bundle into a
config.yamlfile. For more information, see Downloading the existing configuration. - You have a Certificate Authority (CA) file or files.
Procedure
Create a new YAML file, for example,
extra-ca-certificate-config-bundle-secret.yaml:touch extra-ca-certificate-config-bundle-secret.yaml
$ touch extra-ca-certificate-config-bundle-secret.yamlCopy to Clipboard Copied! Toggle word wrap Toggle overflow Create the
extra-ca-certificate-config-bundle-secretresource.Create the resource by entering the following command:
Copy to Clipboard Copied! Toggle word wrap Toggle overflow
Optional. You can check the content of the
extra-ca-certificate-config-bundle-secret.yamlfile by entering the following command:cat extra-ca-certificate-config-bundle-secret.yaml
$ cat extra-ca-certificate-config-bundle-secret.yamlCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
Copy to Clipboard Copied! Toggle word wrap Toggle overflow Create the
configBundleSecretresource by entering the following command:oc create -n <namespace> -f extra-ca-certificate-config-bundle-secret.yaml
$ oc create -n <namespace> -f extra-ca-certificate-config-bundle-secret.yamlCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
secret/extra-ca-certificate-config-bundle-secret created
secret/extra-ca-certificate-config-bundle-secret createdCopy to Clipboard Copied! Toggle word wrap Toggle overflow Update the
QuayRegistryYAML file to reference theextra-ca-certificate-config-bundle-secretobject by entering the following command:oc patch quayregistry <registry_name> -n <namespace> --type=merge -p '{"spec":{"configBundleSecret":"extra-ca-certificate-config-bundle-secret"}}'$ oc patch quayregistry <registry_name> -n <namespace> --type=merge -p '{"spec":{"configBundleSecret":"extra-ca-certificate-config-bundle-secret"}}'Copy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
quayregistry.quay.redhat.com/example-registry patched
quayregistry.quay.redhat.com/example-registry patchedCopy to Clipboard Copied! Toggle word wrap Toggle overflow Ensure that your
QuayRegistryYAML file has been updated to use the extra CA certificateconfigBundleSecretresource by entering the following command:oc get quayregistry <registry_name> -n <namespace> -o yaml
$ oc get quayregistry <registry_name> -n <namespace> -o yamlCopy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
# ... configBundleSecret: extra-ca-certificate-config-bundle-secret # ...
# ... configBundleSecret: extra-ca-certificate-config-bundle-secret # ...Copy to Clipboard Copied! Toggle word wrap Toggle overflow
3.3. Adding custom SSL/TLS certificates when Red Hat Quay is deployed on Kubernetes
When deployed on Kubernetes, Red Hat Quay mounts in a secret as a volume to store config assets. Currently, this breaks the upload certificate function of the superuser panel.
As a temporary workaround, base64 encoded certificates can be added to the secret after Red Hat Quay has been deployed.
Use the following procedure to add custom SSL/TLS certificates when Red Hat Quay is deployed on Kubernetes.
Prerequisites
- Red Hat Quay has been deployed.
-
You have a custom
ca.crtfile.
Procedure
Base64 encode the contents of an SSL/TLS certificate by entering the following command:
cat ca.crt | base64 -w 0
$ cat ca.crt | base64 -w 0Copy to Clipboard Copied! Toggle word wrap Toggle overflow Example output
...c1psWGpqeGlPQmNEWkJPMjJ5d0pDemVnR2QNCnRsbW9JdEF4YnFSdVd3PT0KLS0tLS1FTkQgQ0VSVElGSUNBVEUtLS0tLQo=
...c1psWGpqeGlPQmNEWkJPMjJ5d0pDemVnR2QNCnRsbW9JdEF4YnFSdVd3PT0KLS0tLS1FTkQgQ0VSVElGSUNBVEUtLS0tLQo=Copy to Clipboard Copied! Toggle word wrap Toggle overflow Enter the following
kubectlcommand to edit thequay-enterprise-config-secretfile:kubectl --namespace quay-enterprise edit secret/quay-enterprise-config-secret
$ kubectl --namespace quay-enterprise edit secret/quay-enterprise-config-secretCopy to Clipboard Copied! Toggle word wrap Toggle overflow Add an entry for the certificate and paste the full
base64encoded stringer under the entry. For example:custom-cert.crt: c1psWGpqeGlPQmNEWkJPMjJ5d0pDemVnR2QNCnRsbW9JdEF4YnFSdVd3PT0KLS0tLS1FTkQgQ0VSVElGSUNBVEUtLS0tLQo=
custom-cert.crt: c1psWGpqeGlPQmNEWkJPMjJ5d0pDemVnR2QNCnRsbW9JdEF4YnFSdVd3PT0KLS0tLS1FTkQgQ0VSVElGSUNBVEUtLS0tLQo=Copy to Clipboard Copied! Toggle word wrap Toggle overflow Use the
kubectl deletecommand to remove all Red Hat Quay pods. For example:kubectl delete pod quay-operator.v3.7.1-6f9d859bd-p5ftc quayregistry-clair-postgres-7487f5bd86-xnxpr quayregistry-quay-app-upgrade-xq2v6 quayregistry-quay-database-859d5445ff-cqthr quayregistry-quay-redis-84f888776f-hhgms
$ kubectl delete pod quay-operator.v3.7.1-6f9d859bd-p5ftc quayregistry-clair-postgres-7487f5bd86-xnxpr quayregistry-quay-app-upgrade-xq2v6 quayregistry-quay-database-859d5445ff-cqthr quayregistry-quay-redis-84f888776f-hhgmsCopy to Clipboard Copied! Toggle word wrap Toggle overflow Afterwards, the Red Hat Quay deployment automatically schedules replace pods with the new certificate data.