Chapter 1. SSL and TLS for Red Hat Quay
The Secure Sockets Layer (SSL) protocol was originally developed by Netscape Corporation to provide a mechanism for secure communication over the Internet. Subsequently, the protocol was adopted by the Internet Engineering Task Force (IETF) and renamed to Transport Layer Security (TLS).
TLS (Transport Layer Security) is a cryptographic protocol used to secure network communications. When hardening system security settings by configuring preferred key-exchange protocols, authentication methods, and encryption algorithms, it is necessary to bear in mind that the broader the range of supported clients, the lower the resulting security. Conversely, strict security settings lead to limited compatibility with clients, which can result in some users being locked out of the system. Be sure to target the strictest available configuration and only relax it when it is required for compatibility reasons.
Red Hat Quay can be configured to use SSL/TLS certificates to ensure secure communication between clients and the Red Hat Quay server. This configuration involves the use of valid SSL/TLS certificates, which can be obtained from a trusted Certificate Authority (CA) or generated as self-signed certificates for internal use.
1.1. Creating a Certificate Authority
Use the following procedure to set up your own CA and use it to issue a server certificate for your domain. This allows you to secure communications with SSL/TLS using your own certificates.
Procedure
Generate the root CA key by entering the following command:
$ openssl genrsa -out rootCA.key 2048Generate the root CA certificate by entering the following command:
$ openssl req -x509 -new -nodes -key rootCA.key -sha256 -days 1024 -out rootCA.pemEnter the information that will be incorporated into your certificate request, including the server hostname, for example:
Country Name (2 letter code) [XX]:IE State or Province Name (full name) []:GALWAY Locality Name (eg, city) [Default City]:GALWAY Organization Name (eg, company) [Default Company Ltd]:QUAY Organizational Unit Name (eg, section) []:DOCS Common Name (eg, your name or your server's hostname) []:quay-server.example.comGenerate the server key by entering the following command:
$ openssl genrsa -out ssl.key 2048Generate a signing request by entering the following command:
$ openssl req -new -key ssl.key -out ssl.csrEnter the information that will be incorporated into your certificate request, including the server hostname, for example:
Country Name (2 letter code) [XX]:IE State or Province Name (full name) []:GALWAY Locality Name (eg, city) [Default City]:GALWAY Organization Name (eg, company) [Default Company Ltd]:QUAY Organizational Unit Name (eg, section) []:DOCS Common Name (eg, your name or your server's hostname) []:quay-server.example.com Email Address []:Create a configuration file
openssl.cnf, specifying the server hostname, for example:Example
openssl.cnffile[req] req_extensions = v3_req distinguished_name = req_distinguished_name [req_distinguished_name] [ v3_req ] basicConstraints = CA:FALSE keyUsage = nonRepudiation, digitalSignature, keyEncipherment subjectAltName = @alt_names [alt_names] DNS.1 = <quay-server.example.com> IP.1 = 192.168.1.112Use the configuration file to generate the certificate
ssl.cert:$ openssl x509 -req -in ssl.csr -CA rootCA.pem -CAkey rootCA.key -CAcreateserial -out ssl.cert -days 356 -extensions v3_req -extfile openssl.cnfConfirm your created certificates and files by entering the following command:
$ ls /path/to/certificatesExample output
rootCA.key ssl-bundle.cert ssl.key custom-ssl-config-bundle-secret.yaml rootCA.pem ssl.cert openssl.cnf rootCA.srl ssl.csr
1.2. Configuring SSL/TLS for standalone Red Hat Quay deployments
For standalone Red Hat Quay deployments, SSL/TLS certificates must be configured by using the command-line interface and by updating your config.yaml file manually.
1.2.1. Configuring custom SSL/TLS certificates by using the command line interface
SSL/TLS must be configured by using the command-line interface (CLI) and updating your config.yaml file manually.
Prerequisites
- You have created a certificate authority and signed the certificate.
Procedure
Copy the certificate file and primary key file to your configuration directory, ensuring they are named
ssl.certandssl.keyrespectively:cp ~/ssl.cert ~/ssl.key /path/to/configuration_directoryNavigate to the configuration directory by entering the following command:
$ cd /path/to/configuration_directoryEdit the
config.yamlfile and specify that you want Red Hat Quay to handle SSL/TLS:Example
config.yamlfile# ... SERVER_HOSTNAME: <quay-server.example.com> ... PREFERRED_URL_SCHEME: https # ...Optional: Append the contents of the
rootCA.pemfile to the end of thessl.certfile by entering the following command:$ cat rootCA.pem >> ssl.certStop the
Quaycontainer by entering the following command:$ sudo podman stop <quay_container_name>Restart the registry by entering the following command:
$ sudo podman run -d --rm -p 80:8080 -p 443:8443 \ --name=quay \ -v $QUAY/config:/conf/stack:Z \ -v $QUAY/storage:/datastorage:Z \ registry.redhat.io/quay/quay-rhel8:v3.13.9
1.2.2. Configuring Podman to trust the Certificate Authority
Podman uses two paths to locate the Certificate Authority (CA) file: /etc/containers/certs.d/ and /etc/docker/certs.d/. Use the following procedure to configure Podman to trust the CA.
Procedure
Copy the root CA file to one of
/etc/containers/certs.d/or/etc/docker/certs.d/. Use the exact path determined by the server hostname, and name the fileca.crt:$ sudo cp rootCA.pem /etc/containers/certs.d/quay-server.example.com/ca.crtVerify that you no longer need to use the
--tls-verify=falseoption when logging in to your Red Hat Quay registry:$ sudo podman login quay-server.example.comExample output
Login Succeeded!
1.2.3. Configuring the system to trust the certificate authority
Use the following procedure to configure your system to trust the certificate authority.
Procedure
Enter the following command to copy the
rootCA.pemfile to the consolidated system-wide trust store:$ sudo cp rootCA.pem /etc/pki/ca-trust/source/anchors/Enter the following command to update the system-wide trust store configuration:
$ sudo update-ca-trust extractOptional. You can use the
trust listcommand to ensure that theQuayserver has been configured:$ trust list | grep quay label: quay-server.example.comNow, when you browse to the registry at
https://quay-server.example.com, the lock icon shows that the connection is secure: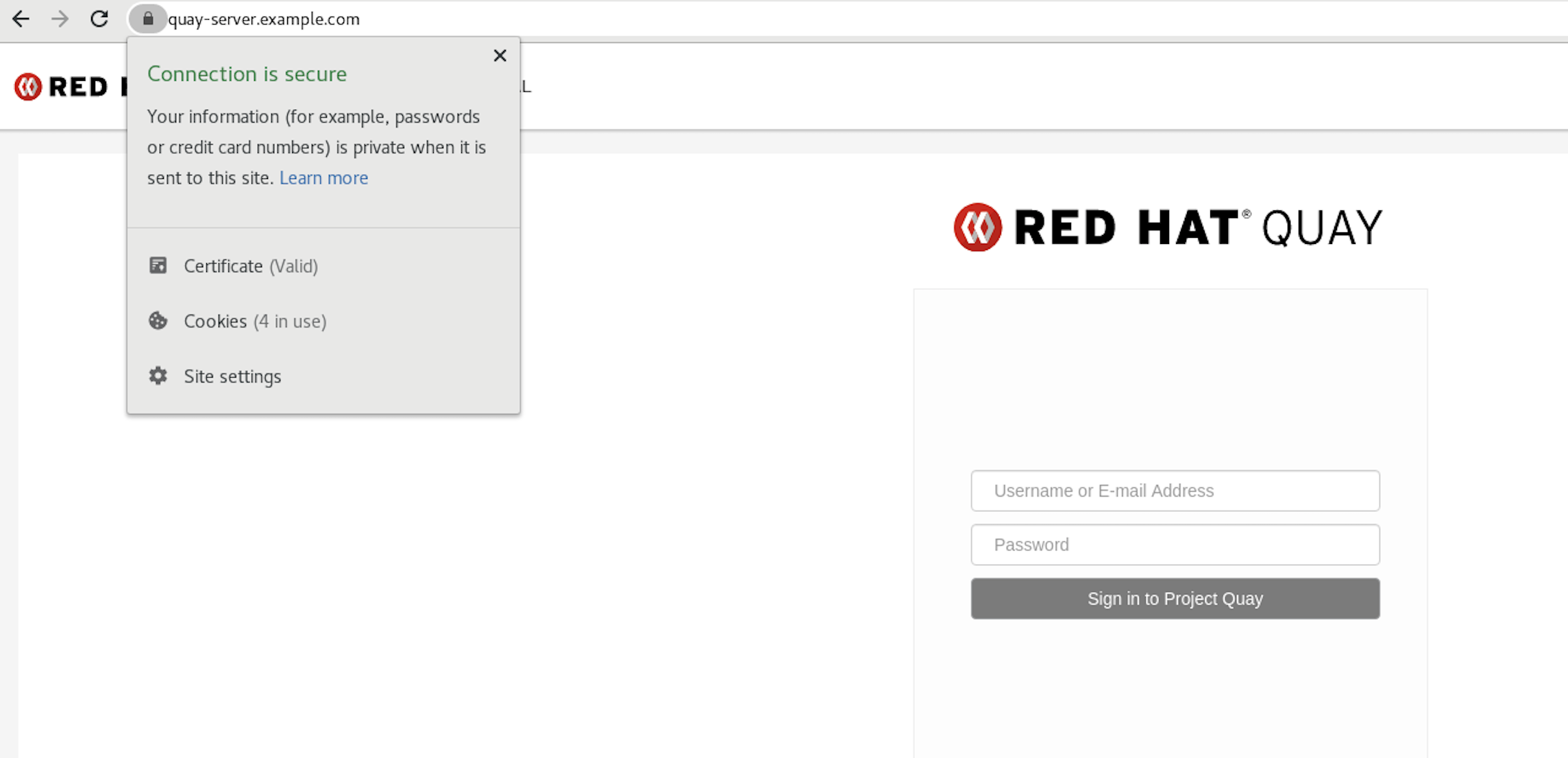
To remove the
rootCA.pemfile from system-wide trust, delete the file and update the configuration:$ sudo rm /etc/pki/ca-trust/source/anchors/rootCA.pem$ sudo update-ca-trust extract$ trust list | grep quay
More information can be found in the RHEL 9 documentation in the chapter Using shared system certificates.
1.3. Configuring custom SSL/TLS certificates for Red Hat Quay on OpenShift Container Platform
When Red Hat Quay is deployed on OpenShift Container Platform, the tls component of the QuayRegistry custom resource definition (CRD) is set to managed by default. As a result, OpenShift Container Platform’s Certificate Authority is used to create HTTPS endpoints and to rotate SSL/TLS certificates.
You can configure custom SSL/TLS certificates before or after the initial deployment of Red Hat Quay on OpenShift Container Platform. This process involves creating or updating the configBundleSecret resource within the QuayRegistry YAML file to integrate your custom certificates and setting the tls component to unmanaged.
When configuring custom SSL/TLS certificates for Red Hat Quay, administrators are responsible for certificate rotation.
The following procedures enable you to apply custom SSL/TLS certificates to ensure secure communication and meet specific security requirements for your Red Hat Quay on OpenShift Container Platform deployment. These steps assumed you have already created a Certificate Authority (CA) bundle or an ssl.key, and an ssl.cert. The procedure then shows you how to integrate those files into your Red Hat Quay on OpenShift Container Platform deployment, which ensures that your registry operates with the specified security settings and conforms to your organization’s SSL/TLS policies.
-
The following procedure is used for securing Red Hat Quay with an HTTPS certificate. Note that this differs from managing Certificate Authority Trust Bundles. CA Trust Bundles are used by system processes within the
Quaycontainer to verify certificates against trusted CAs, and ensure that services like LDAP, storage backend, and OIDC connections are trusted. -
If you are adding the certificates to an existing deployment, you must include the existing
config.yamlfile in the new config bundle secret, even if you are not making any configuration changes.
1.3.1. Creating a custom SSL/TLS configBundleSecret resource
After creating your custom SSL/TLS certificates, you can create a custom configBundleSecret resource for Red Hat Quay on OpenShift Container Platform, which allows you to upload ssl.cert and ssl.key files.
Prerequisites
-
You have base64 decoded the original config bundle into a
config.yamlfile. For more information, see Downloading the existing configuration. - You have generated custom SSL certificates and keys.
Procedure
Create a new YAML file, for example,
custom-ssl-config-bundle-secret.yaml:$ touch custom-ssl-config-bundle-secret.yamlCreate the
custom-ssl-config-bundle-secretresource.Create the resource by entering the following command:
$ oc -n <namespace> create secret generic custom-ssl-config-bundle-secret \ --from-file=config.yaml=</path/to/config.yaml> \1 --from-file=ssl.cert=</path/to/ssl.cert> \2 --from-file=extra_ca_cert_<name-of-certificate>.crt=ca-certificate-bundle.crt \3 --from-file=ssl.key=</path/to/ssl.key> \4 --dry-run=client -o yaml > custom-ssl-config-bundle-secret.yaml- 1
- Where
<config.yaml>is yourbase64 decodedconfig.yamlfile. - 2
- Where
<ssl.cert>is yourssl.certfile. - 3
- Optional. The
--from-file=extra_ca_cert_<name-of-certificate>.crt=ca-certificate-bundle.crtfield allows Red Hat Quay to recognize custom Certificate Authority (CA) files. If you are using LDAP, OIDC, or another service that uses custom CAs, you must add them via theextra_ca_certpath. For more information, see "Adding additional Certificate Authorities to Red Hat Quay on OpenShift Container Platform." - 4
- Where
<ssl.key>is yourssl.keyfile.
Optional. You can check the content of the
custom-ssl-config-bundle-secret.yamlfile by entering the following command:$ cat custom-ssl-config-bundle-secret.yamlExample output
apiVersion: v1 data: config.yaml: QUxMT1dfUFVMTFNfV0lUSE9VVF9TVFJJQ1RfTE9HR0lORzogZmFsc2UKQVVUSEVOVElDQVRJT05fVFlQRTogRGF0YWJhc2UKREVGQVVMVF9UQUdfRVhQSVJBVElPTjogMncKRElTVFJJQlVURURfU1R... ssl.cert: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUVYakNDQTBhZ0F3SUJBZ0lVTUFBRk1YVWlWVHNoMGxNTWI3U1l0eFV5eTJjd0RRWUpLb1pJaHZjTkFRRUwKQlFBd2dZZ3hDekFKQmdOVkJBWVR... extra_ca_cert_<name-of-certificate>:LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUVYakNDQTBhZ0F3SUJBZ0lVTUFBRk1YVWlWVHNoMGxNTWI3U1l0eFV5eTJjd0RRWUpLb1pJaHZjTkFRRUwKQlFBd2dZZ3hDe... ssl.key: LS0tLS1CRUdJTiBQUklWQVRFIEtFWS0tLS0tCk1JSUV2UUlCQURBTkJna3Foa2lHOXcwQkFRRUZBQVNDQktjd2dnU2pBZ0VBQW9JQkFRQ2c0VWxZOVV1SVJPY1oKcFhpZk9MVEdqaS9neUxQMlpiMXQ... kind: Secret metadata: creationTimestamp: null name: custom-ssl-config-bundle-secret namespace: <namespace>Create the
configBundleSecretresource by entering the following command:$ oc create -n <namespace> -f custom-ssl-config-bundle-secret.yamlExample output
secret/custom-ssl-config-bundle-secret createdUpdate the
QuayRegistryYAML file to reference thecustom-ssl-config-bundle-secretobject by entering the following command:$ oc patch quayregistry <registry_name> -n <namespace> --type=merge -p '{"spec":{"configBundleSecret":"custom-ssl-config-bundle-secret"}}'Example output
quayregistry.quay.redhat.com/example-registry patchedSet the
tlscomponent of theQuayRegistryYAML toFalseby entering the following command:$ oc patch quayregistry <registry_name> -n <namespace> --type=merge -p '{"spec":{"components":[{"kind":"tls","managed":false}]}}'Example output
quayregistry.quay.redhat.com/example-registry patchedEnsure that your
QuayRegistryYAML file has been updated to use the custom SSLconfigBundleSecretresource, and that your andtlsresource is set toFalseby entering the following command:$ oc get quayregistry <registry_name> -n <namespace> -o yamlExample output
# ... configBundleSecret: custom-ssl-config-bundle-secret # ... spec: components: - kind: tls managed: false # ...
Verification
Confirm a TLS connection to the server and port by entering the following command:
$ openssl s_client -connect <quay-server.example.com>:443Example output
# ... SSL-Session: Protocol : TLSv1.3 Cipher : TLS_AES_256_GCM_SHA384 Session-ID: 0E995850DC3A8EB1A838E2FF06CE56DBA81BD8443E7FA05895FBD6FBDE9FE737 Session-ID-ctx: Resumption PSK: 1EA68F33C65A0F0FA2655BF9C1FE906152C6E3FEEE3AEB6B1B99BA7C41F06077989352C58E07CD2FBDC363FA8A542975 PSK identity: None PSK identity hint: None SRP username: None TLS session ticket lifetime hint: 7200 (seconds) # ...