Questo contenuto non è disponibile nella lingua selezionata.
2.3. Certificate System Architecture Overview
2.3.1. Java Application Server
server.xml. The following link provides more information about Tomcat configuration: https://tomcat.apache.org/tomcat-8.0-doc/config/.
web.xml file, which is defined in Java Servlet 3.1 specification. See https://www.jcp.org/en/jsr/detail?id=340 for details.
CS.cfg.
2.3.2. Java Security Manager

pki_security_manager=false option under its own Tomcat section.
# systemctl stop pki-tomcatd@instance_name.serviceor# systemctl stop pki-tomcatd-nuxwdog@instance_name.service(if using thenuxwdogwatchdog)- Open the
/etc/sysconfig/instance_namefile, and setSECURITY_MANAGER="false" # systemctl start pki-tomcatd@instance_name.serviceor# systemctl start pki-tomcatd-nuxwdog@instance_name.service(if using thenuxwdogwatchdog)
pkidaemon from the following files:
/usr/share/pki/server/conf/catalina.policy
/usr/share/tomcat/conf/catalina.policy
/var/lib/pki/$PKI_INSTANCE_NAME/conf/pki.policy
/var/lib/pki/$PKI_INSTANCE_NAME/conf/custom.policy/var/lib/pki/instance_name/conf/catalina.policy.
2.3.2.1. Running Subsystems under a Java Security Manager
2.3.2.1.1. About the Security Manager Policy Files
- The
catalina.policyfile from the default Tomcat policy located in the/usr/share/tomcat/confdirectory; this is updated whenever the general Tomcat files are updated. - A
pki.policyfile, in the/var/lib/pki/instance_name/confdirectory, that is supplied with the subsystem instance. - A
custom.policyfile, in the/var/lib/pki/instance_name/confdirectory, that contains user-defined security policies.
catalina.policy file, also in the /var/lib/pki/instance_name/conf directory, which is used for the instance.
pki.policy file contains permissions that grant unrestricted access to the Tomcat, LDAP, and symkey services used by the PKI subsystems. For example:
// These permissions apply to Tomcat java as utilized by PKI instances
grant codeBase "file:/usr/share/java/tomcat/-" {
permission java.security.AllPermission;
};custom.policy file is empty by default; administrators can write policies in that file which will be used in addition to the given PKI policies and Tomcat policies.
2.3.2.1.2. Starting a Subsystem Instance without the Java Security Manager
pki_security_manager=true under the [Tomcat] section in the /etc/pki/default.cfg file). However, it is possible to start or restart an instance and run it without starting the Java Security Manager, as shown below.
Procedure 2.1. Starting an Instance Without the Java Security Manager
- Stop the instance.
# systemctl stop pki-tomcatd@instance_name.serviceOR# systemctl stop pki-tomcatd-nuxwdog@instance_name.service (if using the nuxwdog watchdog) - Edit the
/etc/sysconfig/instance_namefile and turn off the security manager:SECURITY_MANAGER="false" - Start the instance.
# systemctl start pki-tomcatd@instance_name.serviceORsystemctl start pki-tomcatd-nuxwdog@instance_name.service (if using the nuxwdog watchdog)
2.3.3. Interfaces
2.3.3.1. Servlet Interface
web.xml file, that is, /usr/share/pki/ca/webapps/ca/WEB-INF/web.xml. The same file also defines the URL of each servlet and the security requirements to access the servlets. See Section 2.3.1, “Java Application Server” for more information.
2.3.3.2. Administrative Interface

2.3.3.3. End-Entity Interface
2.3.3.4. Operator Interface

2.3.4. REST Interface
web.xml of the corresponding subsystem. More information about RESTEasy can be found at http://resteasy.jboss.org/.
- CA certificate service:
http://<host_name>:<port>/ca/rest/certs/ - KRA key service:
http://<host_name>:<port>/kra/rest/agent/keys/ - TKS user service:
http://<host_name>:<port>/tks/rest/admin/users/ - TPS group service:
http://<host_name>:<port>/tps/rest/admin/groups/
{
"id":"admin",
"UserID":"admin",
"FullName":"Administrator",
"Email":"admin@example.com",
...
}- user name and password
- client certificate
/usr/share/pki/ca/conf/auth-method.properties.
/usr/share/pki/<subsystem>/conf/acl.properties.
2.3.5. NSS
2.3.6. JSS
2.3.7. Tomcatjss
tomcatjss as a bridge between the Tomcat Server HTTP engine and JSS, the Java interface for security operations performed by NSS. Tomcatjss is a Java Secure Socket Extension (JSSE) implementation using Java Security Services (JSS) for Tomcat.
- The server is started.
- Tomcat gets to the point where it needs to create the listening sockets for the Certificate System installation.
- The
server.xmlfile is processed. Configuration in this file tells the system to use a socket factory implemented by Tomcatjss. - For each requested socket, Tomcajss reads and processes the included attributes when it creates the socket. The resulting socket will behave as it has been asked to by those parameters.
- Once the server is running, we have the required set of listening sockets waiting for incoming connections to the Tomcat-based Certificate System.
server.xml file, see Section 9.4, “Configuration Files for the Tomcat Engine and Web Services”.
2.3.8. PKCS #11

2.3.8.1. NSS Soft Token (internal token)
Note
/var/lib/pki/instance_name/alias/ directory.
- The default internal PKCS #11 module, which comes with two tokens:
- The internal crypto services token, which performs all cryptographic operations such as encryption, decryption, and hashing.
- The internal key storage token ("Certificate DB token"), which handles all communication with the certificate and key database files that store certificates and keys.
- The FIPS 140 module. This module complies with the FIPS 140 government standard for cryptographic module implementations. The FIPS 140 module includes a single, built-in FIPS 140 certificate database token, which handles both cryptographic operations and communication with the certificate and key database files.
2.3.8.2. Hardware Security Module (HSM, external token)
Note
secmod.db database for the subsystem. The modutil utility is used to modify this file when there are changes to the system, such as installing a hardware accelerator to use for signing operations. For more information on modutil, see Network Security Services (NSS) at Mozilla Developer webpage.
2.3.9. Certificate System Serial Number Management
2.3.9.1. Serial Number Ranges
- Current serial number management is based on assigning ranges of sequential serial numbers.
- Instances request new ranges when crossing below a defined threshold.
- Instances store information about a newly acquired range once it is assigned to the instance.
- Instances continue using old ranges until all numbers are exhausted from it, and then it moves to the new range.
- Cloned subsystems synchronize their range assignment through replication conflicts.
- Part of the current range of the master is transferred to a new clone in the process of cloning.
- New clones may request a new range if the transferred range is below the defined threshold.
[CA] section to the PKI instance override configuration file, and adding the following name=value pairs under that section as needed. Default values which already exist in /etc/pki/default.cfg are shown in the following example:
[CA]
pki_serial_number_range_start=1
pki_serial_number_range_end=10000000
pki_request_number_range_start=1
pki_request_number_range_end=10000000
pki_replica_number_range_start=1
pki_replica_number_range_end=1002.3.9.2. Random Serial Number Management
[CA] section to the PKI instance override file and adding the following name=value pair under that section:
[CA]
pki_random_serial_numbers_enable=True
2.3.10. Security Domain
2.3.11. Passwords and Watchdog (nuxwdog)
<instance_dir>/conf/password.conf. At the same time, an identifying string is stored in the main configuration file CS.cfg as part of the parameter cms.passwordlist.
CS.cfg, is protected by Red Hat Enterprise Linux, and only accessible by the PKI administrators. No passwords are stored in CS.cfg.
password.conf.
password.conf. LDAP publishing is one example where the newly configured Directory Manager password for the publishing directory is entered into password.conf.
Note
password.conf file altogether. On restart, the nuxwdog watchdog program will prompt the administrator for the required passwords, using the parameter cms.passwordlist (and cms.tokenList if an HSM is used) as a list of passwords for which to prompt. The passwords are then cached by nuxwdog in the kernel keyring to allow automated recovery from a server crash. This automated recovery (automatic subsystem restart) happens in case of uncontrolled shutdown (crash). In case of a controlled shutdown by the administrator, administrators are prompted for passwords again.
2.3.12. Internal LDAP Database
pkispawn options will also be needed for installing such Certificate System instance.
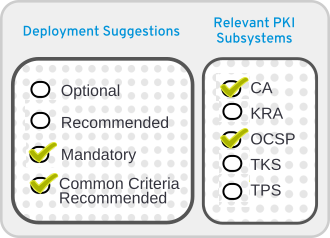
2.3.13. Security-Enhanced Linux (SELinux)
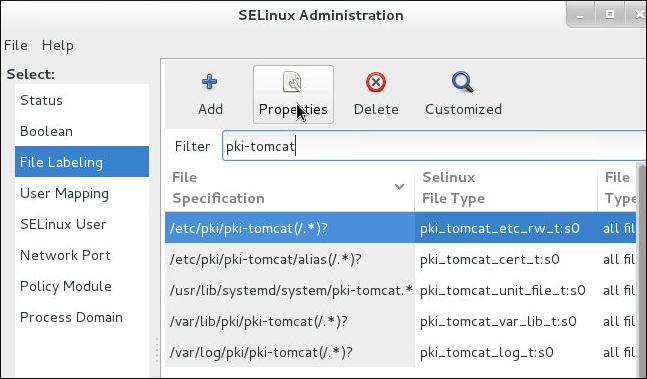
Figure 2.1. CA SELinux Port Policy
- Files and directories for each subsystem instance are labeled with a specific SELinux context.
- The ports for each subsystem instance are labeled with a specific SELinux context.
- All Certificate System processes are constrained within a subsystem-specific domain.
- Each domain has specific rules that define what actions that are authorized for the domain.
- Any access not specified in the SELinux policy is denied to the Certificate System instance.
pkispawn is run to configure a Certificate System subsystem, files and ports associated with that subsystem are labeled with the required SELinux contexts. These contexts are removed when the particular subsystems are removed using pkidestroy.
pki_tomcat_t domain. Certificate System instances are Tomcat servers, and the pki_tomcat_t domain extends the policies for a standard tomcat_t Tomcat domain. All Certificate System instances on a server share the same domain.
unconfined_t) and then transitions into the pki_tomcat_t domain. This process then has certain access permissions, such as write access to log files labeled pki_tomcat_log_t, read and write access to configuration files labeled pki_tomcat_etc_rw_t, or the ability to open and write to http_port_t ports.
2.3.14. Self-tests
# pki-server subsystem-enable <subsystem>2.3.15. Logs
pki_subsystem_log_path when the instance was created with pkispawn. Regular audit logs are located in the log directory with other types of logs, while signed audit logs are written to /var/log/pki/instance_name/subsystem_name/signedAudit. The default location for logs can be changed by modifying the configuration.
2.3.15.1. Audit Log
Note
2.3.15.2. System Log
system, records information about requests to the server (all HTTP and HTTPS requests) and the responses from the server. Information recorded in this log includes the IP address (both IPv4 and IPv6) of the client machine that accessed the server; operations performed, such as search, add, and edit; and the result of the access, such as the number of entries returned:
id_number processor - [date:time] [number_of_operations] [result] servlet: messageExample 2.1. TKS System Log
10439.http-13443-Processor25 - [19/May/2021:14:16:51 CDT] [11] [3] UGSubsystem: Get User Error User not found2.3.15.3. Transactions Log
transactions, records any kind of operation performed or submitted to the subsystem.
id_number.processor - [date:time] [number_of_operations] [result] servlet: messageExample 2.2. Transactions Log
11438.http-8443-Processor25 - [27/May/2021:07:56:18 CDT] [1] [1] archival reqID 4 fromAgent agentID: CA-server.example.com-8443 authenticated by noAuthManager is completed DN requested: UID=recoverykey,E=recoverykey@email.com,CN=recover key serial number: 0x32.3.15.4. Debug Logs
[date:time] [processor]: servlet: message[10/Jun/2021:05:14:51][main]: Established LDAP connection using basic authentication to host localhost port 389 as cn=Directory Managermain, and the message is the message from the server about the LDAP connection, and there is no servlet.
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.requestowner$ value=KRA-server.example.com-8443Example 2.3. CA Certificate Request Log Messages
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.profileapprovedby$ value=admin
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.cert_request$ value=MIIBozCCAZ8wggEFAgQqTfoHMIHHgAECpQ4wDDEKMAgGA1UEAxMBeKaBnzANBgkqhkiG9w0BAQEFAAOB...
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.profile$ value=true
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.cert_request_type$ value=crmf
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.requestversion$ value=1.0.0
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.req_locale$ value=en
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.requestowner$ value=KRA-server.example.com-8443
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.dbstatus$ value=NOT_UPDATED
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.subject$ value=uid=jsmith, e=jsmith@example.com
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.requeststatus$ value=begin
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.auth_token.user$ value=uid=KRA-server.example.com-8443,ou=People,dc=example,dc=com
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.req_key$ value=MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQDreuEsBWq9WuZ2MaBwtNYxvkLP^M
HcN0cusY7gxLzB+XwQ/VsWEoObGldg6WwJPOcBdvLiKKfC605wFdynbEgKs0fChV^M
k9HYDhmJ8hX6+PaquiHJSVNhsv5tOshZkCfMBbyxwrKd8yZ5G5I+2gE9PUznxJaM^M
HTmlOqm4HwFxzy0RRQIDAQAB
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.auth_token.authmgrinstname$ value=raCertAuth
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.auth_token.uid$ value=KRA-server.example.com-8443
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.auth_token.userid$ value=KRA-server.example.com-8443
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.requestor_name$ value=
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.profileid$ value=caUserCert
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.auth_token.userdn$ value=uid=KRA-server.example.com-4747,ou=People,dc=example,dc=com
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.requestid$ value=20
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.auth_token.authtime$ value=1212782378071
[06/Jun/2021:14:59:38][http-8443;-Processor24]: ProfileSubmitServlet: key=$request.req_x509info$ value=MIICIKADAgECAgEAMA0GCSqGSIb3DQEBBQUAMEAxHjAcBgNVBAoTFVJlZGJ1ZGNv^M
bXB1dGVyIERvbWFpbjEeMBwGA1UEAxMVQ2VydGlmaWNhdGUgQXV0aG9yaXR5MB4X^M
DTA4MDYwNjE5NTkzOFoXDTA4MTIwMzE5NTkzOFowOzEhMB8GCSqGSIb3DQEJARYS^M
anNtaXRoQGV4YW1wbGUuY29tMRYwFAYKCZImiZPyLGQBARMGanNtaXRoMIGfMA0G^M
CSqGSIb3DQEBAQUAA4GNADCBiQKBgQDreuEsBWq9WuZ2MaBwtNYxvkLPHcN0cusY^M
7gxLzB+XwQ/VsWEoObGldg6WwJPOcBdvLiKKfC605wFdynbEgKs0fChVk9HYDhmJ^M
8hX6+PaquiHJSVNhsv5tOshZkCfMBbyxwrKd8yZ5G5I+2gE9PUznxJaMHTmlOqm4^M
HwFxzy0RRQIDAQABo4HFMIHCMB8GA1UdIwQYMBaAFG8gWeOJIMt+aO8VuQTMzPBU^M
78k8MEoGCCsGAQUFBwEBBD4wPDA6BggrBgEFBQcwAYYuaHR0cDovL3Rlc3Q0LnJl^M
ZGJ1ZGNvbXB1dGVyLmxvY2FsOjkwODAvY2Evb2NzcDAOBgNVHQ8BAf8EBAMCBeAw^M
HQYDVR0lBBYwFAYIKwYBBQUHAwIGCCsGAQUFBwMEMCQGA1UdEQQdMBuBGSRyZXF1^M
ZXN0LnJlcXVlc3Rvcl9lbWFpbCQ=[07/Jul/2021:06:25:40][http-11180-Processor25]: OCSPServlet: OCSP Request:
[07/Jul/2021:06:25:40][http-11180-Processor25]: OCSPServlet:
MEUwQwIBADA+MDwwOjAJBgUrDgMCGgUABBSEWjCarLE6/BiSiENSsV9kHjqB3QQU2.3.15.5. Installation Logs
pkispawn, an installation file with the complete debug output from the installation, including any errors and, if the installation is successful, the URL and PIN to the configuration interface for the instance. The file is created in the /var/log/pki/ directory for the instance with a name in the form pki-subsystem_name-spawn.timestamp.log.
Example 2.4. CA Install Log
...
2015-07-22 20:43:13 pkispawn : INFO ... finalizing 'pki.server.deployment.scriptlets.finalization'
2015-07-22 20:43:13 pkispawn : INFO ....... cp -p /etc/sysconfig/pki/tomcat/pki-tomcat/ca/deployment.cfg /var/log/pki/pki-tomcat/ca/archive/spawn_deployment.cfg.20150722204136
2015-07-22 20:43:13 pkispawn : DEBUG ........... chmod 660 /var/log/pki/pki-tomcat/ca/archive/spawn_deployment.cfg.20150722204136
2015-07-22 20:43:13 pkispawn : DEBUG ........... chown 26445:26445 /var/log/pki/pki-tomcat/ca/archive/spawn_deployment.cfg.20150722204136
2015-07-22 20:43:13 pkispawn : INFO ....... generating manifest file called '/etc/sysconfig/pki/tomcat/pki-tomcat/ca/manifest'
2015-07-22 20:43:13 pkispawn : INFO ....... cp -p /etc/sysconfig/pki/tomcat/pki-tomcat/ca/manifest /var/log/pki/pki-tomcat/ca/archive/spawn_manifest.20150722204136
2015-07-22 20:43:13 pkispawn : DEBUG ........... chmod 660 /var/log/pki/pki-tomcat/ca/archive/spawn_manifest.20150722204136
2015-07-22 20:43:13 pkispawn : DEBUG ........... chown 26445:26445 /var/log/pki/pki-tomcat/ca/archive/spawn_manifest.20150722204136
2015-07-22 20:43:13 pkispawn : INFO ....... executing 'systemctl enable pki-tomcatd.target'
2015-07-22 20:43:13 pkispawn : INFO ....... executing 'systemctl daemon-reload'
2015-07-22 20:43:13 pkispawn : INFO ....... executing 'systemctl restart pki-tomcatd@pki-tomcat.service'
2015-07-22 20:43:14 pkispawn : INFO END spawning subsystem 'CA' of instance 'pki-tomcat'
2015-07-22 20:43:14 pkispawn : DEBUG
2.3.15.6. Tomcat Error and Access Logs
- admin.timestamp
- catalina.timestamp
- catalina.out
- host-manager.timestamp
- localhost.timestamp
- localhost_access_log.timestamp
- manager.timestamp
2.3.15.7. Self-Tests Log
CS.cfg file. The information about logs in this section does not pertain to this log. See Section 2.6.5, “Self-Tests” for more information about self-tests.
2.3.15.8. journalctl Logs
systemd and exposed via the journalctl utility.
# journalctl -u pki-tomcatd@instance_name.servicenuxwdog service:
# journalctl -u pki-tomcatd-nuxwdog@instance_name.service# journalctl -f -u pki-tomcatd@instance_name.servicenuxwdog service:
# journalctl -f -u pki-tomcatd-nuxwdog@instance_name.service2.3.16. Instance Layout
/etc/pki/instance_name/server.xml, which is instance-specific, but the CA servlets are defined in /usr/share/pki/ca/webapps/ca/WEB-INF/web.xml, which is shared by all server instances on the system.
2.3.16.1. File and Directory Locations for Certificate System
pki-tomcat; the true value is whatever is specified at the time the subsystem is created with pkispawn.
| Setting | Value |
|---|---|
| Main Directory | /var/lib/pki/pki-tomcat |
| Configuration Directory | /etc/pki/pki-tomcat |
| Configuration File |
/etc/pki/pki-tomcat/server.xml
/etc/pki/pki-tomcat/password.conf
|
| Security Databases | /var/lib/pki/pki-tomcat/alias |
| Subsystem Certificates |
TLS server certificate
Subsystem certificate [a]
|
| Log Files | /var/log/pki/pki-tomcat |
| Web Services Files |
/usr/share/pki/server/webapps/ROOT - Main page
/usr/share/pki/server/webapps/pki/admin - Admin templates
/usr/share/pki/server/webapps/pki/js - JavaScript libraries
|
[a]
The subsystem certificate is always issued by the security domain so that domain-level operations that require client authentication are based on this subsystem certificate.
| |
Note
/var/lib/pki/instance_name/conf/ directory is a symbolic link to the /etc/pki/instance_name/ directory.
2.3.16.2. CA Subsystem Information
pki-tomcat; the true value is whatever is specified at the time the subsystem is created with pkispawn.
| Setting | Value |
|---|---|
| Main Directory | /var/lib/pki/pki-tomcat/ca |
| Configuration Directory | /etc/pki/pki-tomcat/ca |
| Configuration File | /etc/pki/pki-tomcat/ca/CS.cfg |
| Subsystem Certificates |
CA signing certificate
OCSP signing certificate (for the CA's internal OCSP service)
Audit log signing certificate
|
| Log Files | /var/log/pki/pki-tomcat/ca |
| Install Logs | /var/log/pki/pki-ca-spawn.YYYYMMDDhhmmss.log |
| Profile Files | /var/lib/pki/pki-tomcat/ca/profiles/ca |
| Email Notification Templates | /var/lib/pki/pki-tomcat/ca/emails |
| Web Services Files |
/usr/share/pki/ca/webapps/ca/agent - Agent services
/usr/share/pki/ca/webapps/ca/admin - Admin services
/usr/share/pki/ca/webapps/ca/ee - End user services
|
2.3.16.3. KRA Subsystem Information
pki-tomcat; the true value is whatever is specified at the time the subsystem is created with pkispawn.
| Setting | Value |
|---|---|
| Main Directory | /var/lib/pki/pki-tomcat/kra |
| Configuration Directory | /etc/pki/pki-tomcat/kra |
| Configuration File | /etc/pki/pki-tomcat/kra/CS.cfg |
| Subsystem Certificates |
Transport certificate
Storage certificate
Audit log signing certificate
|
| Log Files | /var/log/pki/pki-tomcat/kra |
| Install Logs | /var/log/pki/pki-kra-spawn.YYYYMMDDhhmmss.log |
| Web Services Files |
/usr/share/pki/kra/webapps/kra/agent - Agent services
/usr/share/pki/kra/webapps/kra/admin - Admin services
|
2.3.16.4. OCSP Subsystem Information
pki-tomcat; the true value is whatever is specified at the time the subsystem is created with pkispawn.
| Setting | Value |
|---|---|
| Main Directory | /var/lib/pki/pki-tomcat/ocsp |
| Configuration Directory | /etc/pki/pki-tomcat/ocsp |
| Configuration File | /etc/pki/pki-tomcat/ocsp/CS.cfg |
| Subsystem Certificates |
OCSP signing certificate
Audit log signing certificate
|
| Log Files | /var/log/pki/pki-tomcat/ocsp |
| Install Logs | /var/log/pki/pki-ocsp-spawn.YYYYMMDDhhmmss.log |
| Web Services Files |
/usr/share/pki/ocsp/webapps/ocsp/agent - Agent services
/usr/share/pki/ocsp/webapps/ocsp/admin - Admin services
|
2.3.16.5. TKS Subsystem Information
pki-tomcat; the true value is whatever is specified at the time the subsystem is created with pkispawn.
| Setting | Value |
|---|---|
| Main Directory | /var/lib/pki/pki-tomcat/tks |
| Configuration Directory | /etc/pki/pki-tomcat/tks |
| Configuration File | /etc/pki/pki-tomcat/tks/CS.cfg |
| Subsystem Certificates | Audit log signing certificate |
| Log Files | /var/log/pki/pki-tomcat/tks |
| Install Logs | /var/log/pki/pki-tomcat/pki-tks-spawn.YYYYMMDDhhmmss.log |
2.3.16.6. TPS Subsystem Information
pki-tomcat; the true value is whatever is specified at the time the subsystem is created with pkispawn.
| Setting | Value |
|---|---|
| Main Directory | /var/lib/pki/pki-tomcat/tps |
| Configuration Directory | /etc/pki/pki-tomcat/tps |
| Configuration File | /etc/pki/pki-tomcat/tps/CS.cfg |
| Subsystem Certificates | Audit log signing certificate |
| Log Files | /var/log/pki/pki-tomcat/tps |
| Install Logs | /var/log/pki/pki-tps-spawn.YYYYMMDDhhhmmss.log |
| Web Services Files | /usr/share/pki/tps/webapps/tps - TPS services |
2.3.16.7. Shared Certificate System Subsystem File Locations
| Directory Location | Contents |
|---|---|
| /usr/share/pki | Contains common files and templates used to create Certificate System instances. Along with shared files for all subsystems, there are subsystem-specific files in subfolders:
|
| /usr/bin | Contains the pkispawn and pkidestroy instance configuration scripts and tools (Java, native, and security) shared by the Certificate System subsystems. |
| /usr/share/java/pki | Contains Java archive files shared by local Tomcat web applications and shared by the Certificate System subsystems. |