Experience Red Hat OpenShift Virtualization: Advanced operations and automation
Red Hat® OpenShift® Virtualization allows organizations to run and deploy new and existing virtual machines on a modernized platform. Learn how to manage your environment and perform critical operational tasks often required of virtual machine administrators from day-2 onward.
This learning path is for operations teams or system administrators
Developers may want to check out Foundations of OpenShift on developers.redhat.com.
Security and compliance
The Mega-Sale was a success, but now a critical security audit is looming. We need to demonstrate strict adherence to industry compliance standards for all our virtualized workloads. Our challenge is to ensure a unified approach to security across both VMs and containers. In this module, we will be tasked with scanning our infrastructure with the Red Hat® OpenShift® Compliance Operator and remediating any reported vulnerabilities to ensure that our cluster meets our strict security standards. We will also configure distinct user accounts and access roles to be used by the security auditors that only need limited access to our virtualization infrastructure.
Prerequisites:
- A computer with a web browser and internet access
- A Chromium-based browser is preferred: these are recommended, as some copy/paste functions don’t work in Firefox for the time being
- (Recommended for non-US users) Familiarity with special characters in other countries’ keyboard layouts, since the remote access console uses the US keyboard by default
In this resource, you will:
- Remediate reported vulnerabilities to meet security standards
- Configure distinct user accounts and access roles
Scan infrastructure with the OpenShift Compliance Operator
This section of our lab will focus on making use of the OpenShift Compliance Operator to configure security scans in your OpenShift cluster. The compliance operator can help ensure that the hosts in your OpenShift environment meet specific security standards, and are deployed to meet those standards.
| Note: In our lab environment we will only be scanning and remediating our worker nodes, as it is a virtual hosted environment and doing so with the control plane can cause the cluster to become unstable. |

Figure 1. Compliance overview
- Select Operators and then Installed Operators from the left side navigation menu. Confirm that you have selected All Projects and select the Compliance Operator.
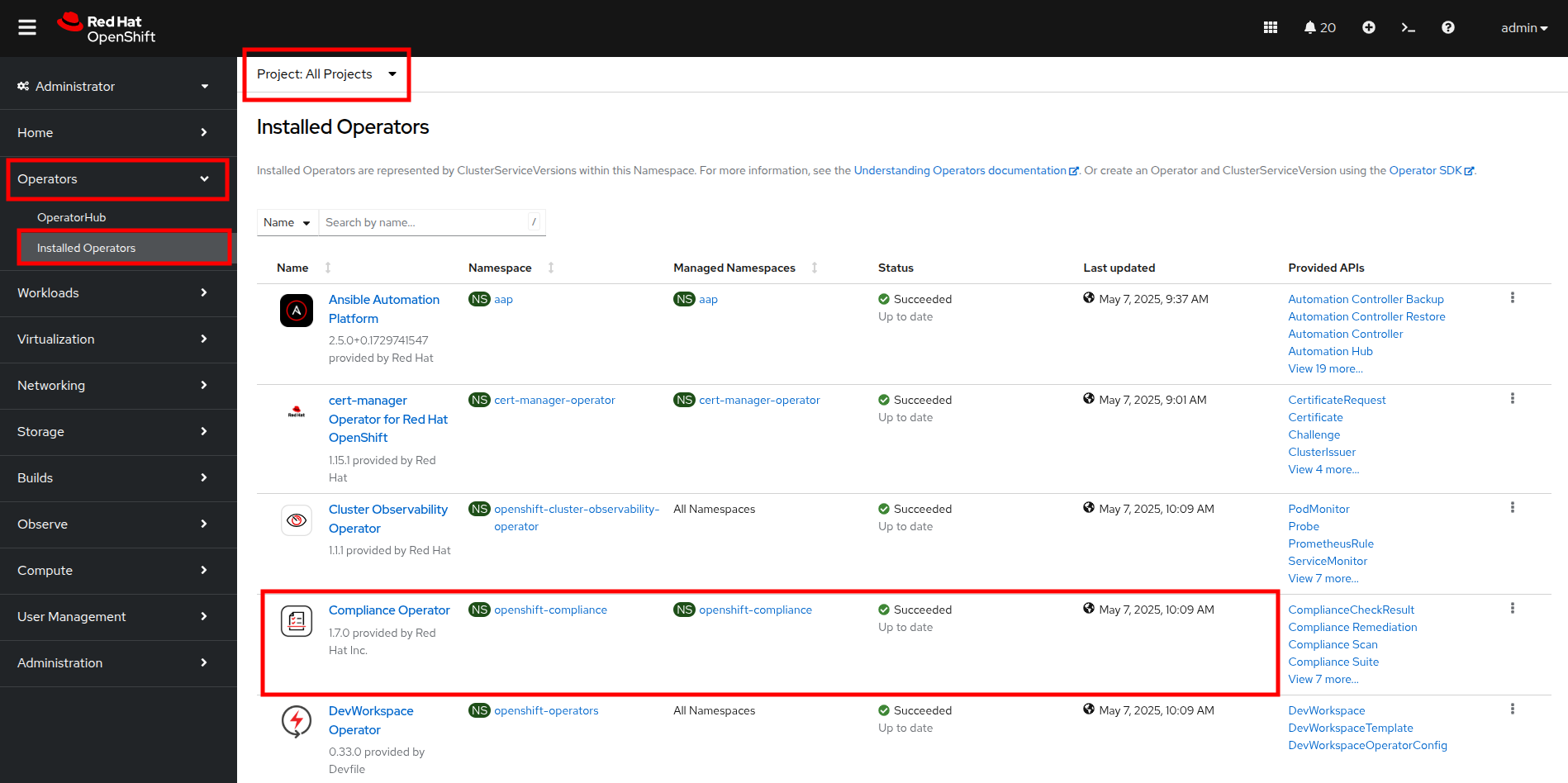
Figure 2. Compliance operator
- This takes you to the Operator details page. Use the horizontal scrollbar to move across and locate the ScanSetting tab.
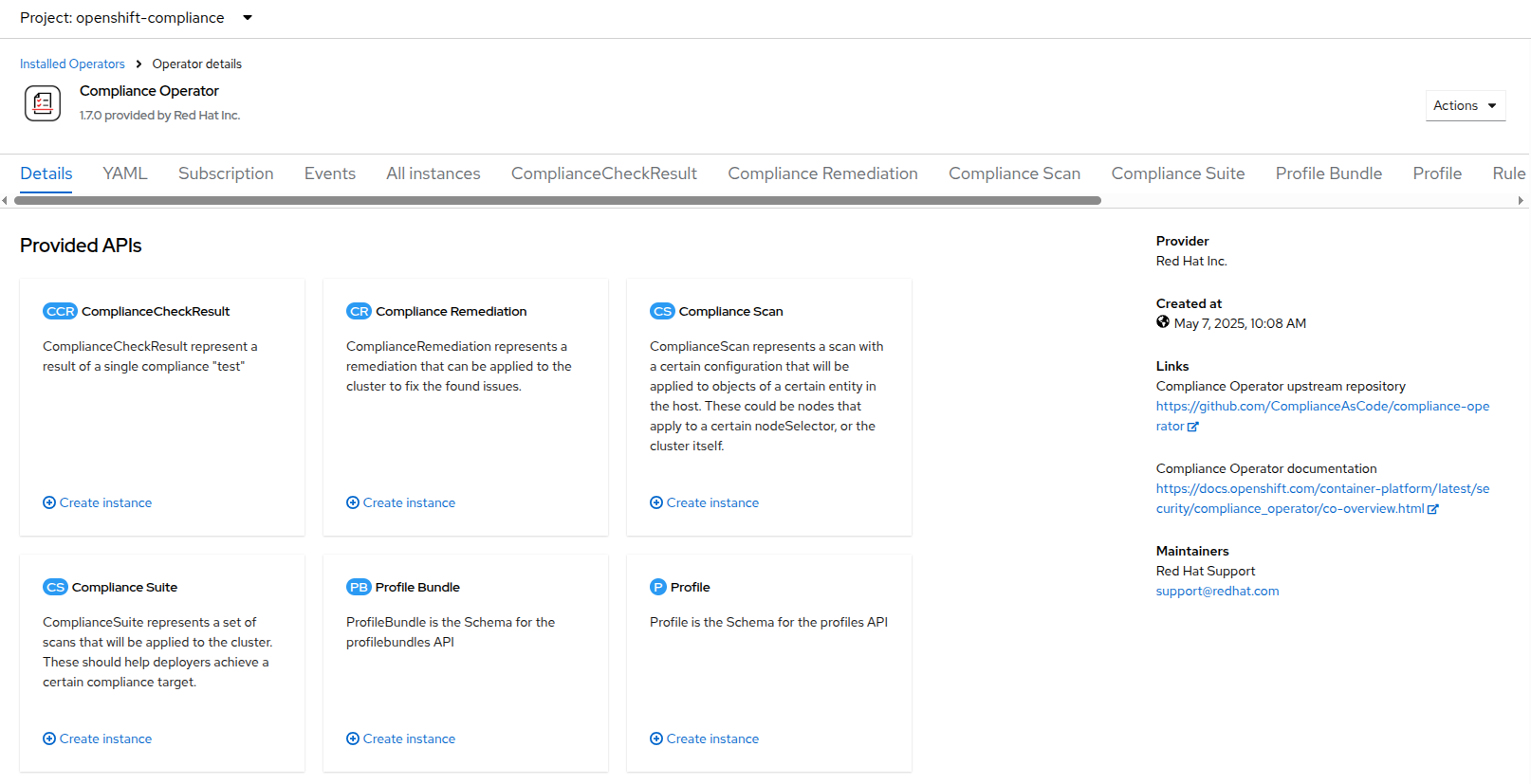
Figure 3. Compliance details
- Click the Create ScanSetting button.
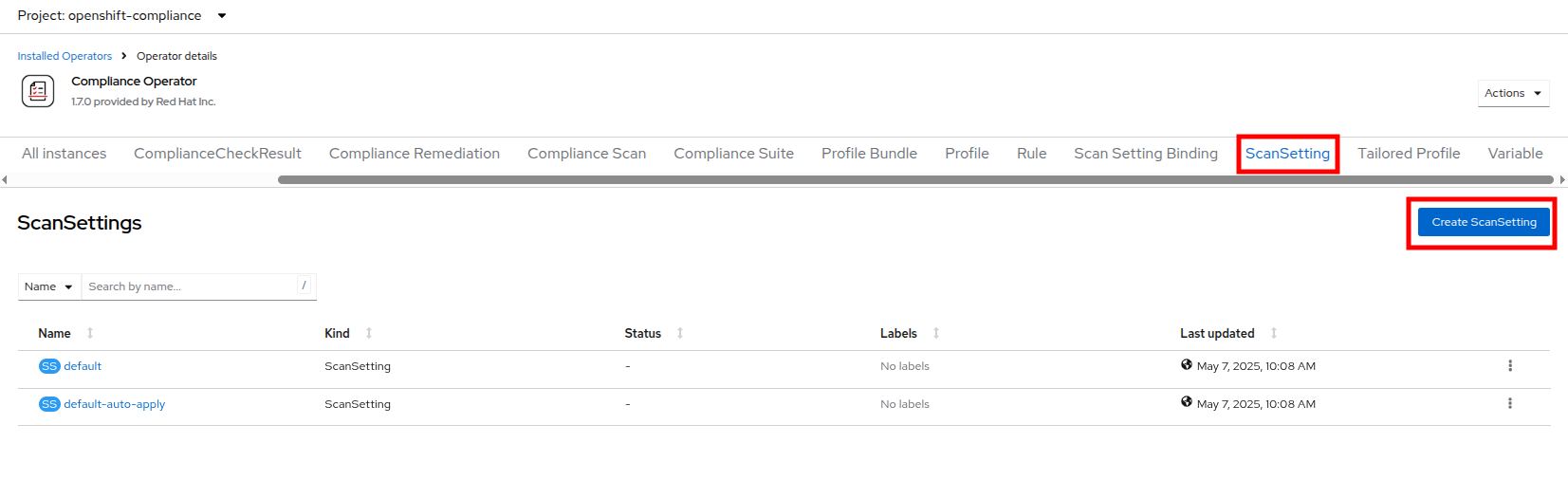
Figure 4. Create ScanSetting button
- On the Create ScanSetting page, set the name of the scan to scan01. Then click the YAML view radio button.
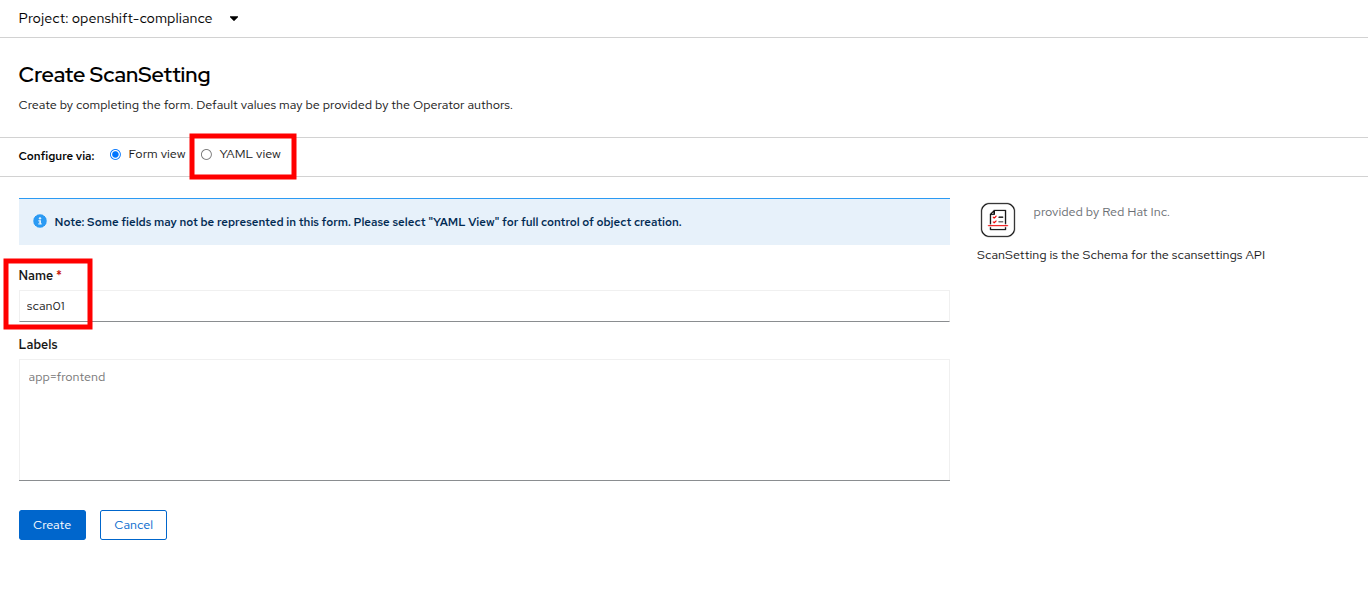
Figure 5. Create Scansetting
- In the ScanSetting YAML details, make note of the following values that are set by default:
- The autoApplyRemediations field is set to false.
- The roles to be scanned by default include entries for master and worker nodes.
- The name field is set to scan01 which you entered on the form view.
- Delete the entry for master to ensure we don’t scan or remediate control plane nodes.
- Click the Create button to create this simple scansetting definition that will only scan worker nodes.
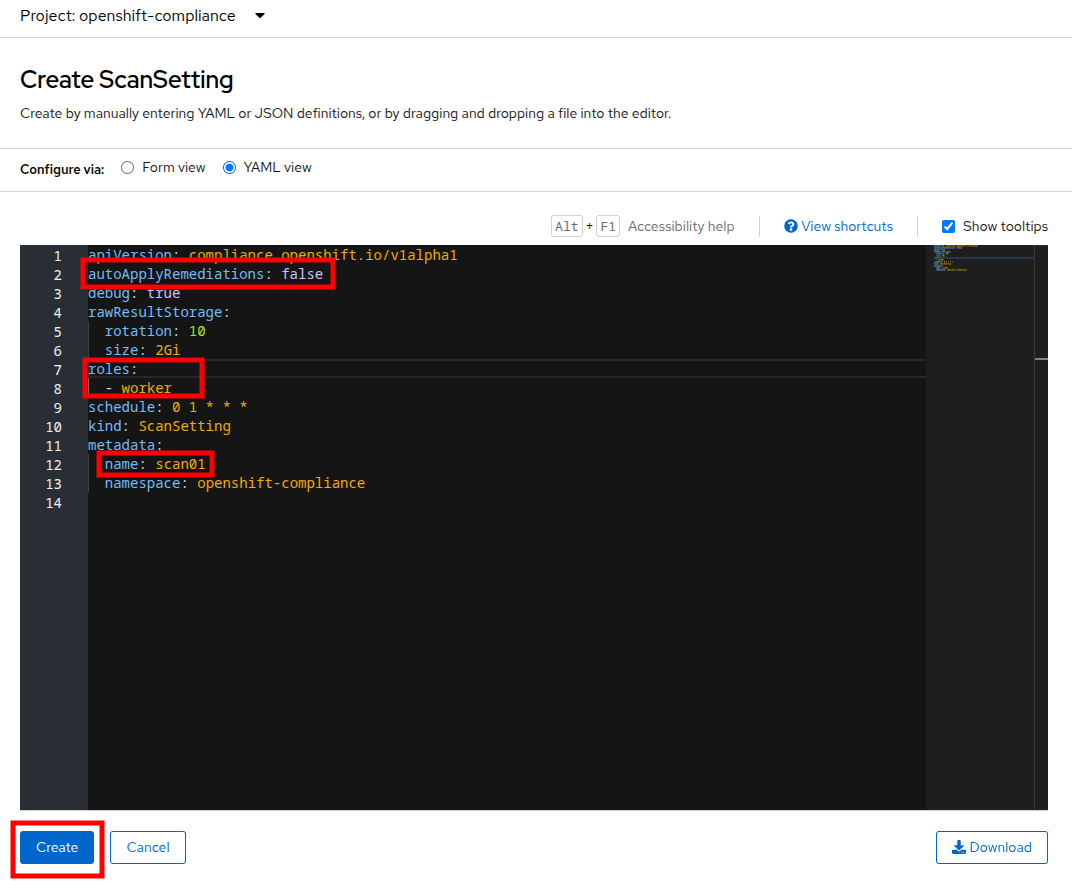
Figure 6. ScanSetting details
- Now click on the Profile tab where there are a number of pre-defined scanning profiles.
- In the search box, type rhcos4 and locate the FedRamp moderate profile rhcos4-moderate in the list.
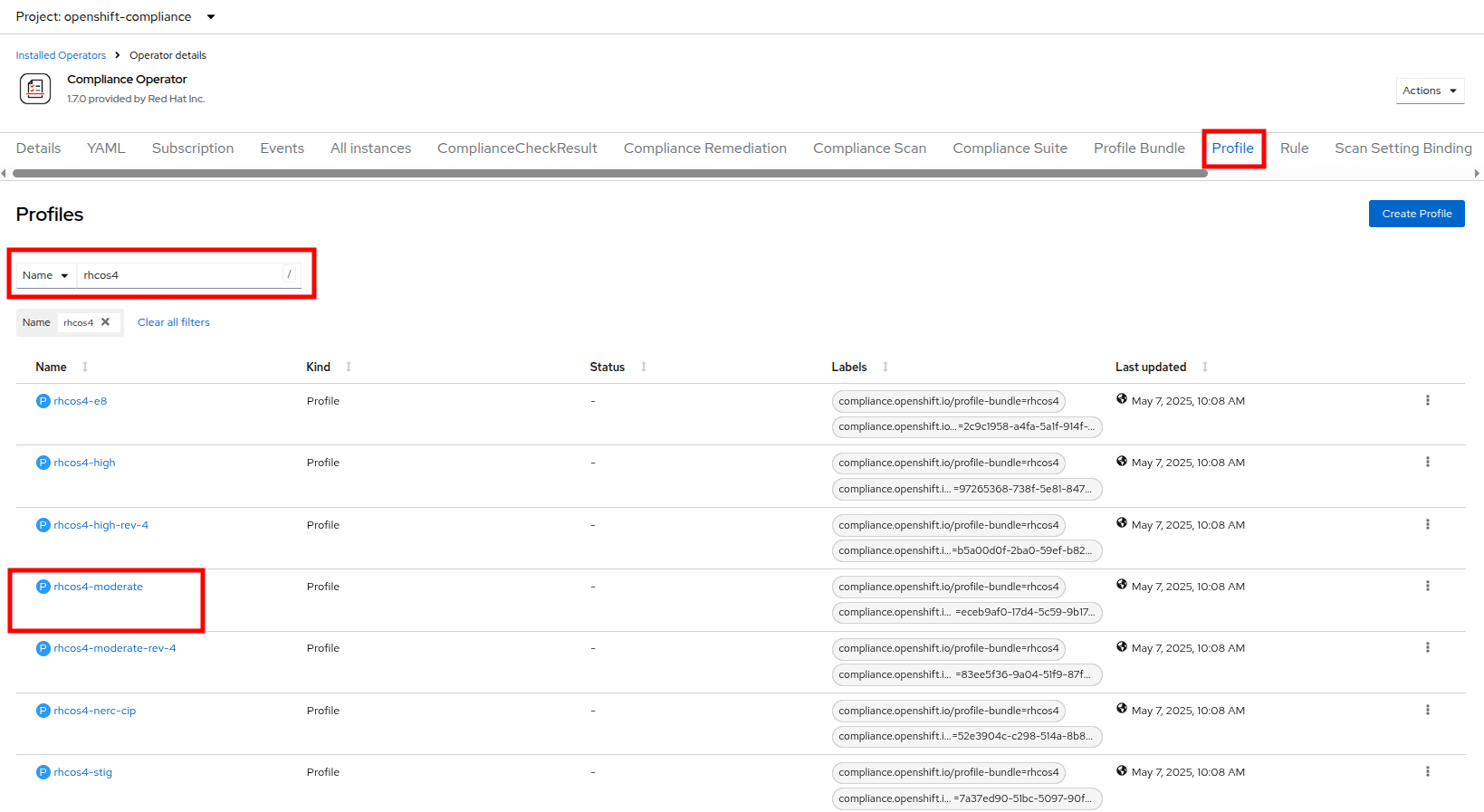
Figure 7. Profiles detail
- Click on rhcos4-moderate and then on the YAML. Scroll down the output to browse the rules that are enforced as a part of this scan. A quick glimpse at the side panel shows that there are quite a few of them.
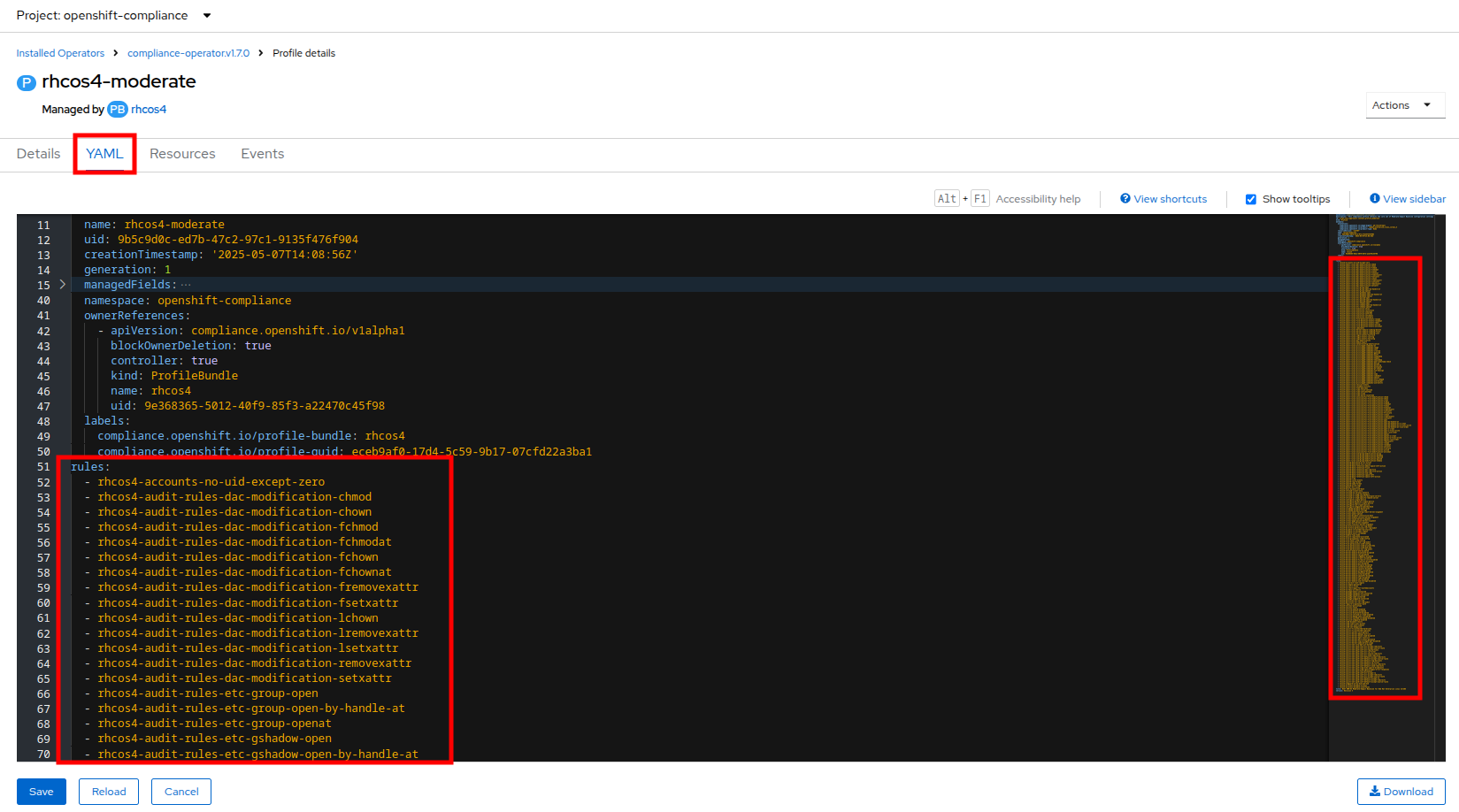
Figure 8. RHCOS4-Moderate rules
- When you are done reviewing the rules, return to the Operator details page by clicking your browser’s back button twice.
- Next we want to create a ScanSettingBinding, pairing a Profile with our ScanSetting definition we created. We do this by navigating to the Scan Setting Binding tab, and clicking the Create ScanSettingBinding button.
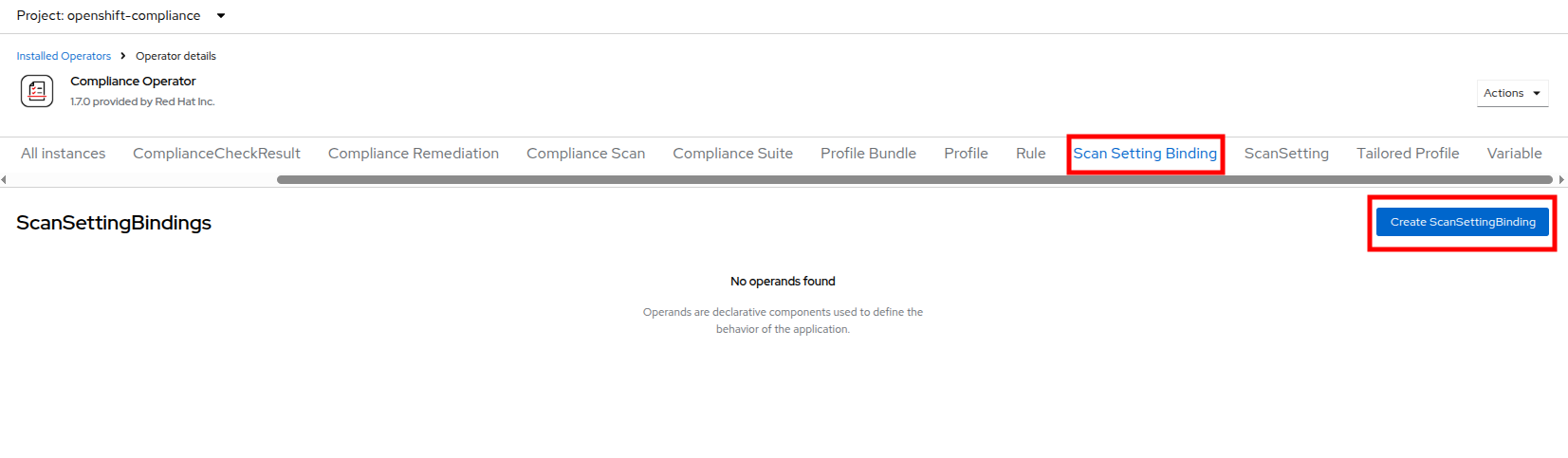
Figure 9. Create ScanSettingBinding
- In the ScanSettingBinding YAML details, let us make a few changes:
- The metadata.name value should be set to fedramp01
- The settingsRef.name field is set to scan01 which we created earlier.
Click the Create button.
Note: The profile is set to rhcos4-moderate (the fedramp moderate profile) by default.
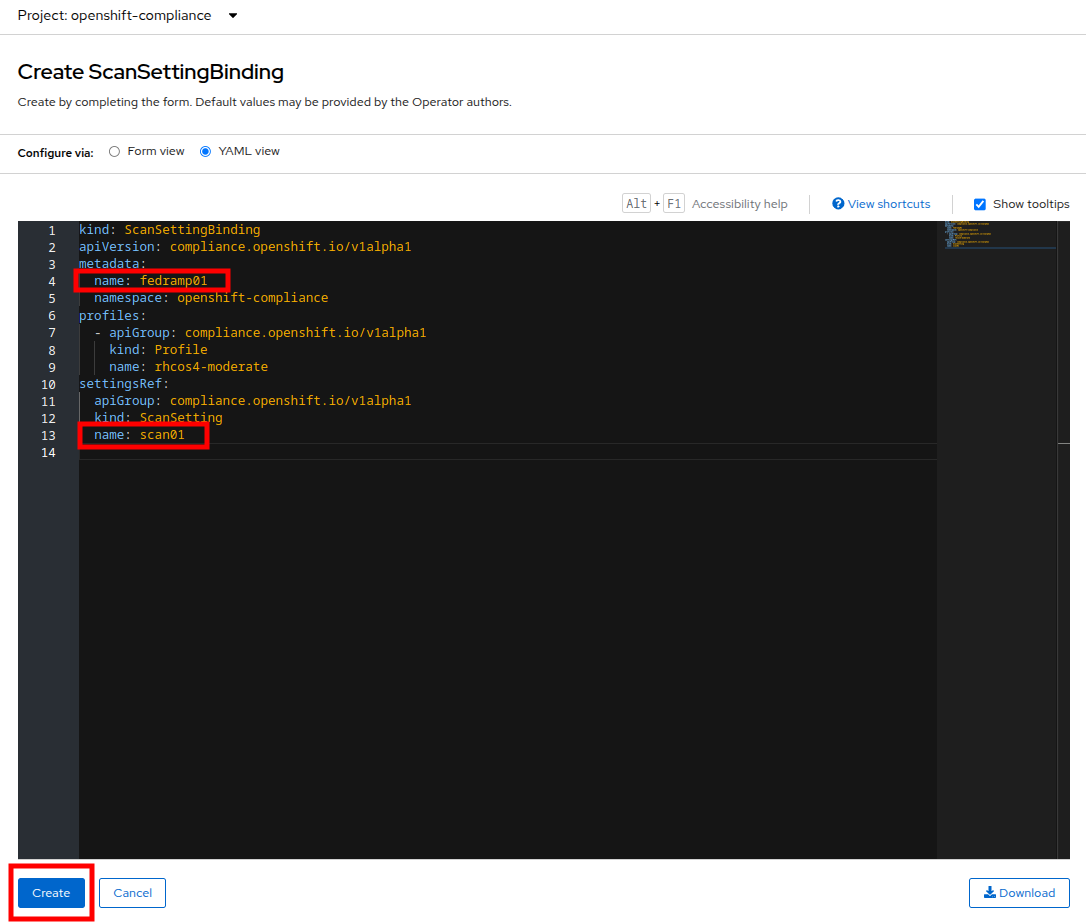
Figure 10. ScanSettingBinding details
- After the ScanSettingBinding is created, the fedramp01 scan will be run automatically. You can view this on the Compliance Suite tab.
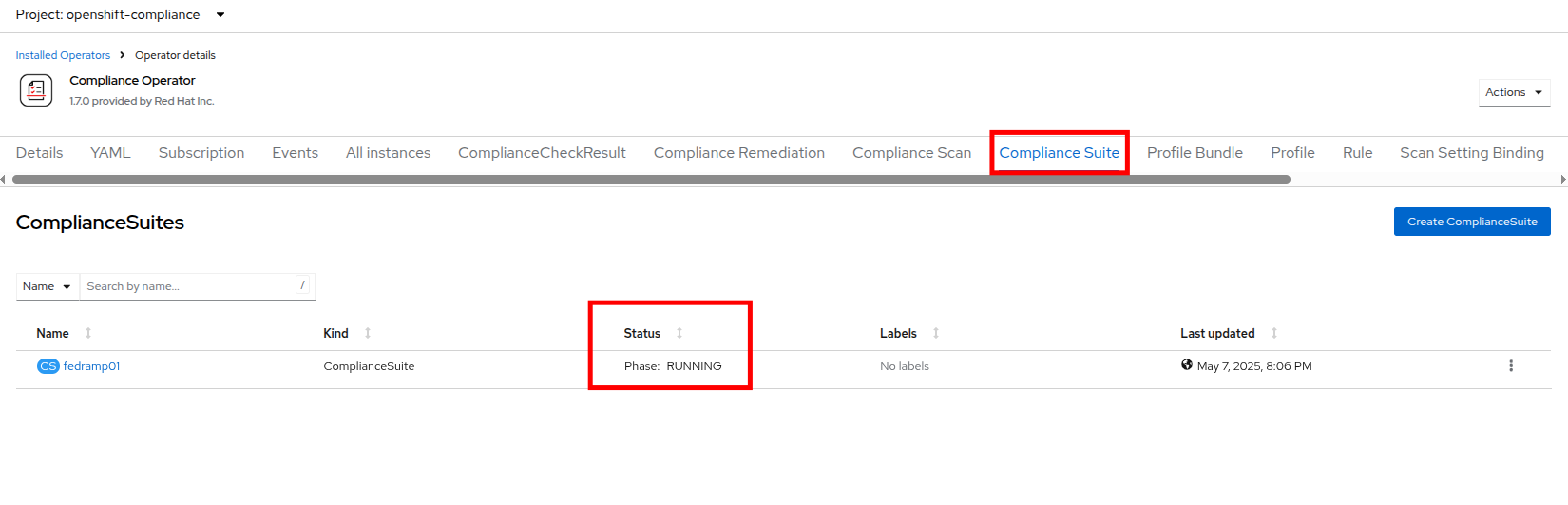
Figure 11. Compliance Suite
- This Compliance Suite runs the defined scans against the specified nodes, in our case the worker nodes defined in scan01.
- For more detailed information you can click on the Compliance Scan tab. There you can watch as the scan proceeds through the steps of RUNNING, AGGREGATING, and DONE.
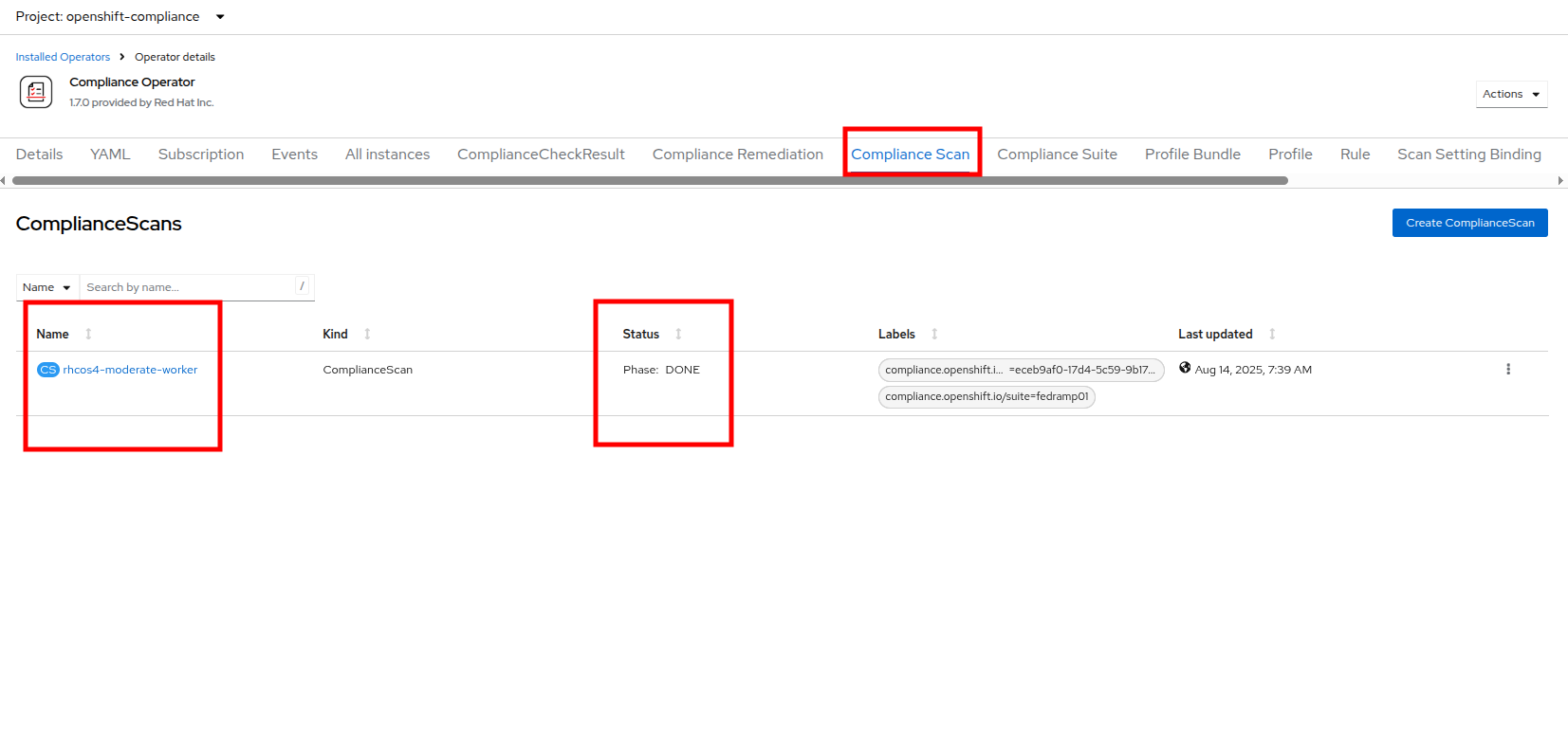
Figure 12. Compliance Scan
- Once the scan completes (3-5 minutes on average) you can check your results by clicking on the ComplianceCheckResult tab. It will list all of the scans that were a part of the compliance suite we chose and their results.
- Change the search bar to Label and apply the following labels:
compliance.openshift.io/check-status=FAILcompliance.openshift.io/check-severity=high
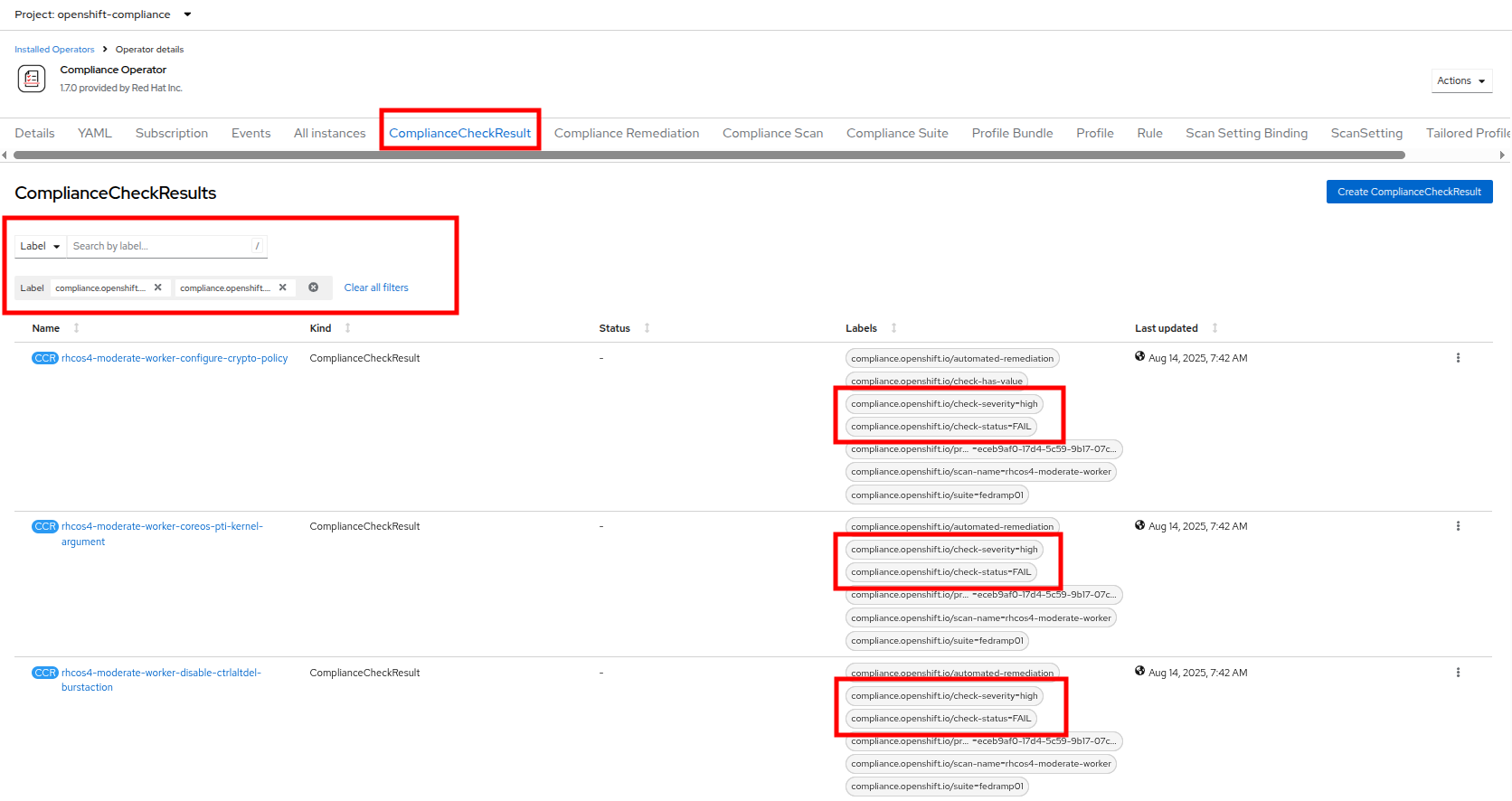
Figure 13. Compliance check results
20. Six high-severity checks have a failed status:
| ComplianceCheckResult | Check-Severity | Check-Status |
|---|---|---|
| rhcos4-moderate-worker-configure-crypto-policy | high | FAIL |
| rhcos4-moderate-worker-coreos-pti-kernel-argument | high | FAIL |
| rhcos4-moderate-worker-disable-ctrlaltdel-burstaction | high | FAIL |
| rhcos4-moderate-worker-disable-ctrlaltdel-reboot | high | FAIL |
| rhcos4-moderate-worker-enable-fips-mode | high | FAIL |
| rhcos4-moderate-worker-no-empty-passwords | high | FAIL |
| Note: This is a table to better organize the view of each failure detected on the scan. You can search for each of these failures manually in the OpenShift console. |
Node remediation with the OpenShift Compliance Operator
When it comes to remediation, it can be performed in one of two ways. Automatically, which may seem simple and the easiest way to do it, but can lead to unexpected results. Or manually, which can be tedious, but allows you to canary test each application, and later automate through a tool like GitOps that checks for failures before proceeding.
| Note: One example of this is the rhcos4-moderate-worker-enable-fips-mode, which was listed as a high severity, fail status on our previous scan. It cannot be applied unless at install time if FIPS mode is enabled. Attempting to auto-remediate this can lead to issues with your cluster. |
In this section, we are going to choose one of our failures from the previous scan and remediate it manually.
Starting from the list above we are going to choose to remediate the following scan result: rhcos4-moderate-worker-coreos-pti-kernel-arguments as required by our audit.
Note: The rhcos4-moderate-worker-coreos-pti-kernel-argument is required to isolate kernel and userspace page tables to prevent attacks.
Click on the Compliance Remediation tab, and in the Name search bar type the term pti-kernel to find the suggested remediation for rhcos4-moderate-worker-coreos-pti-kernel-argument. When the result appears, click the three-dot menu on the right, then select Edit ComplianceRemediation from the menu that appears.
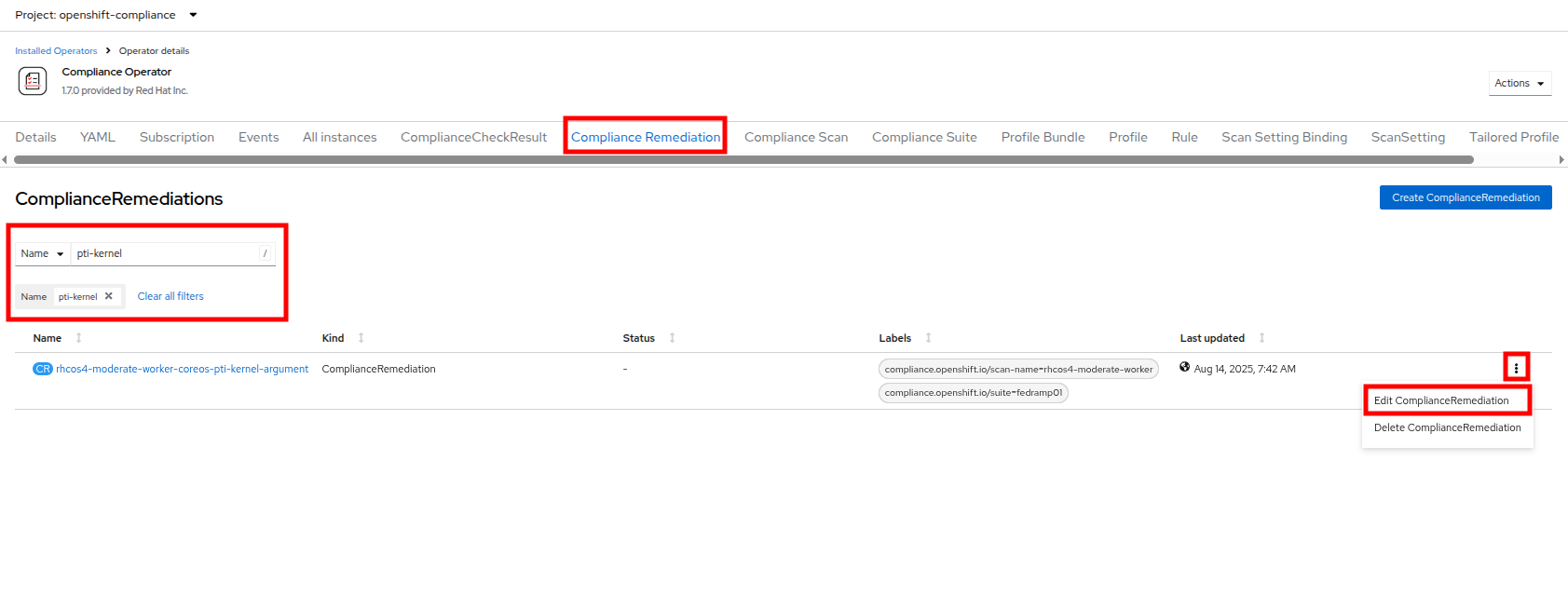
Figure 14. Compliance remediation
- This will launch the ComplianceRemediation details page with a YAML block describing the current status.
- Under the spec section you will see that the current apply state is false, and the kernelArugument that will be applied is that pti=on. Under the status section we see that the remediation state is NotApplied.
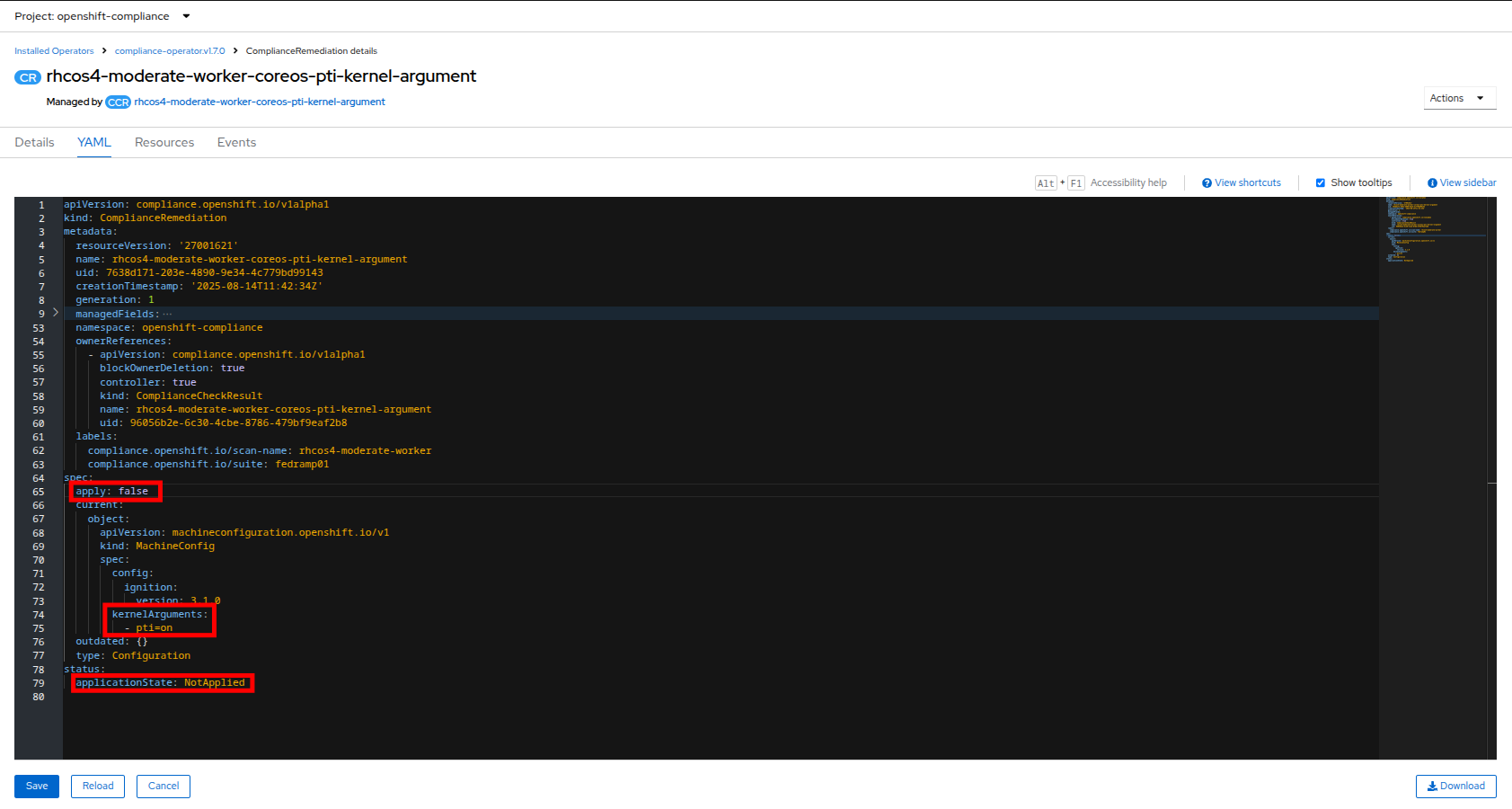
Figure 15. Compliance remediation details
- Under the spec section change the apply field to true and click the Save button.
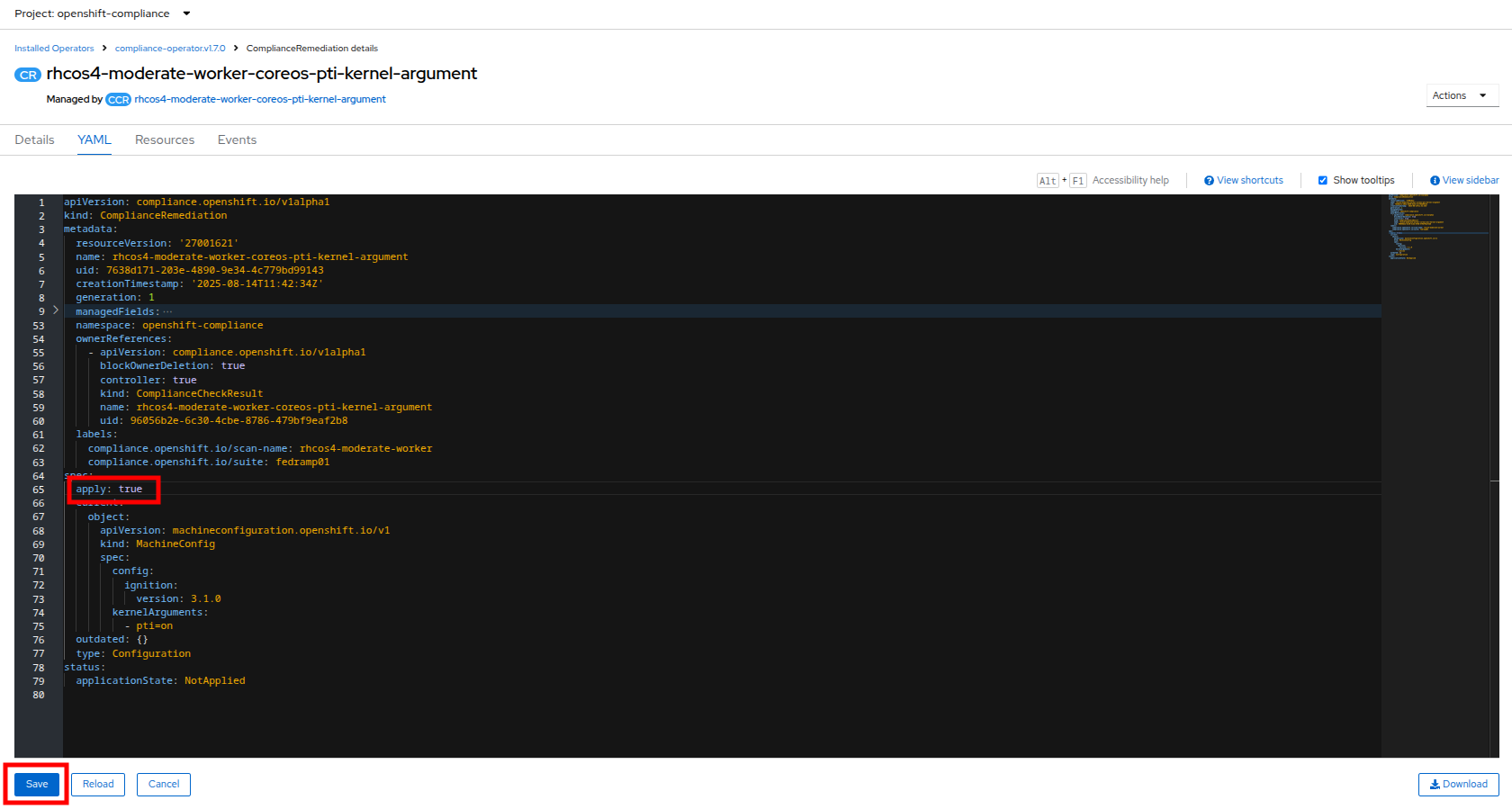
Figure 16. Compliance remediation “true”
- You will be prompted with a message that lets you know that this is a managed resource. Click the Save button to start the remediation process.
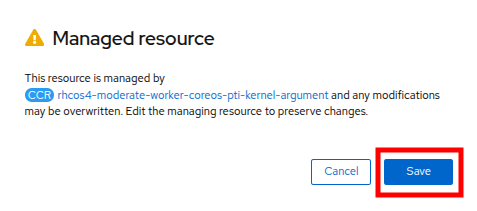
Figure 17. Managed resource prompt
- Once applied, a MachineConfig will be generated to provide the remediation, and each node in the cluster will be cordoned, drained, and remediated in sequence.
- On the left side menu, click on Compute and Nodes to observe the process.
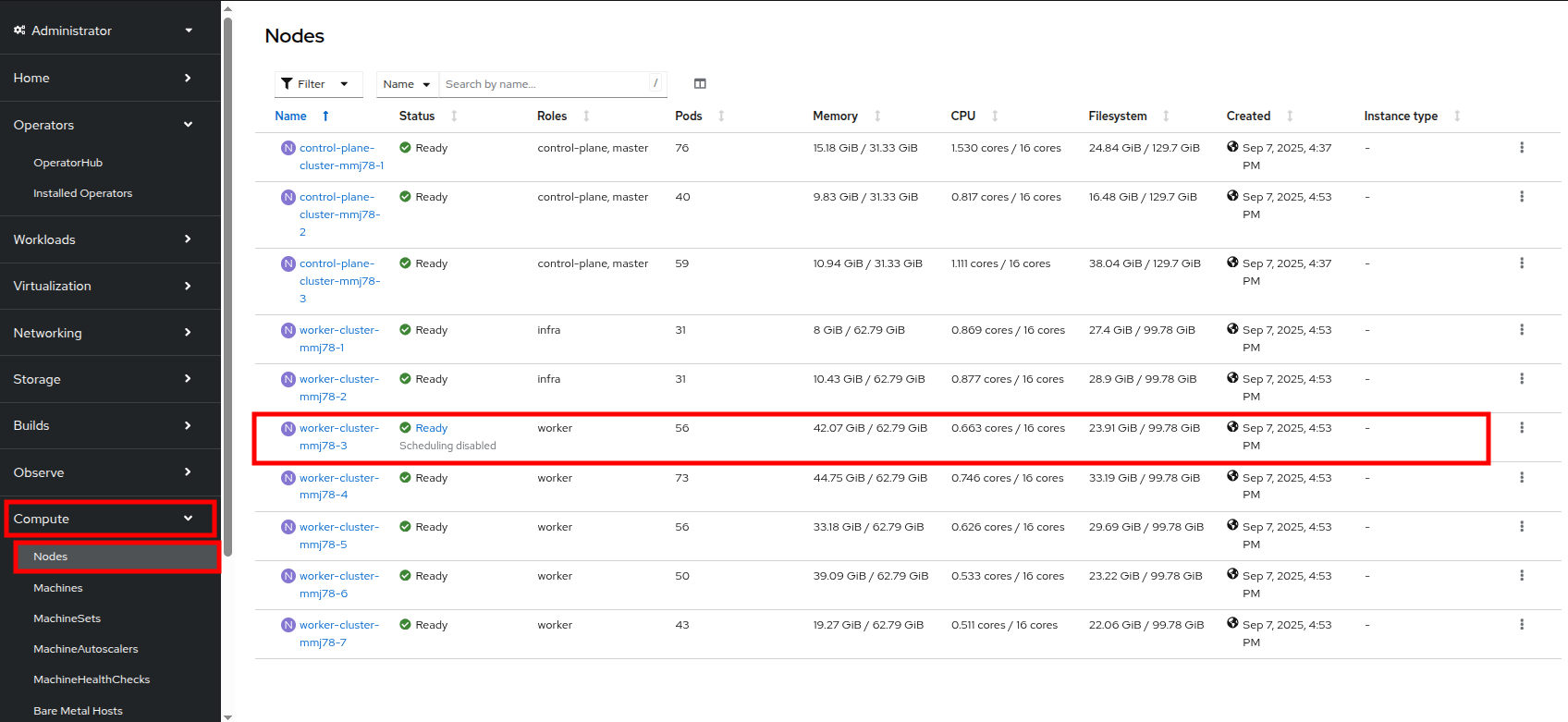
Figure 18. Node 3 cordoned
- You will see a node enter the SchedulingDisabled state to begin its remediation. Click on that node for its Node details page, and notice that the event log shows the node was cordoned to apply the update. You can also see CPU and Memory utilization drop off as the node was successfully drained.
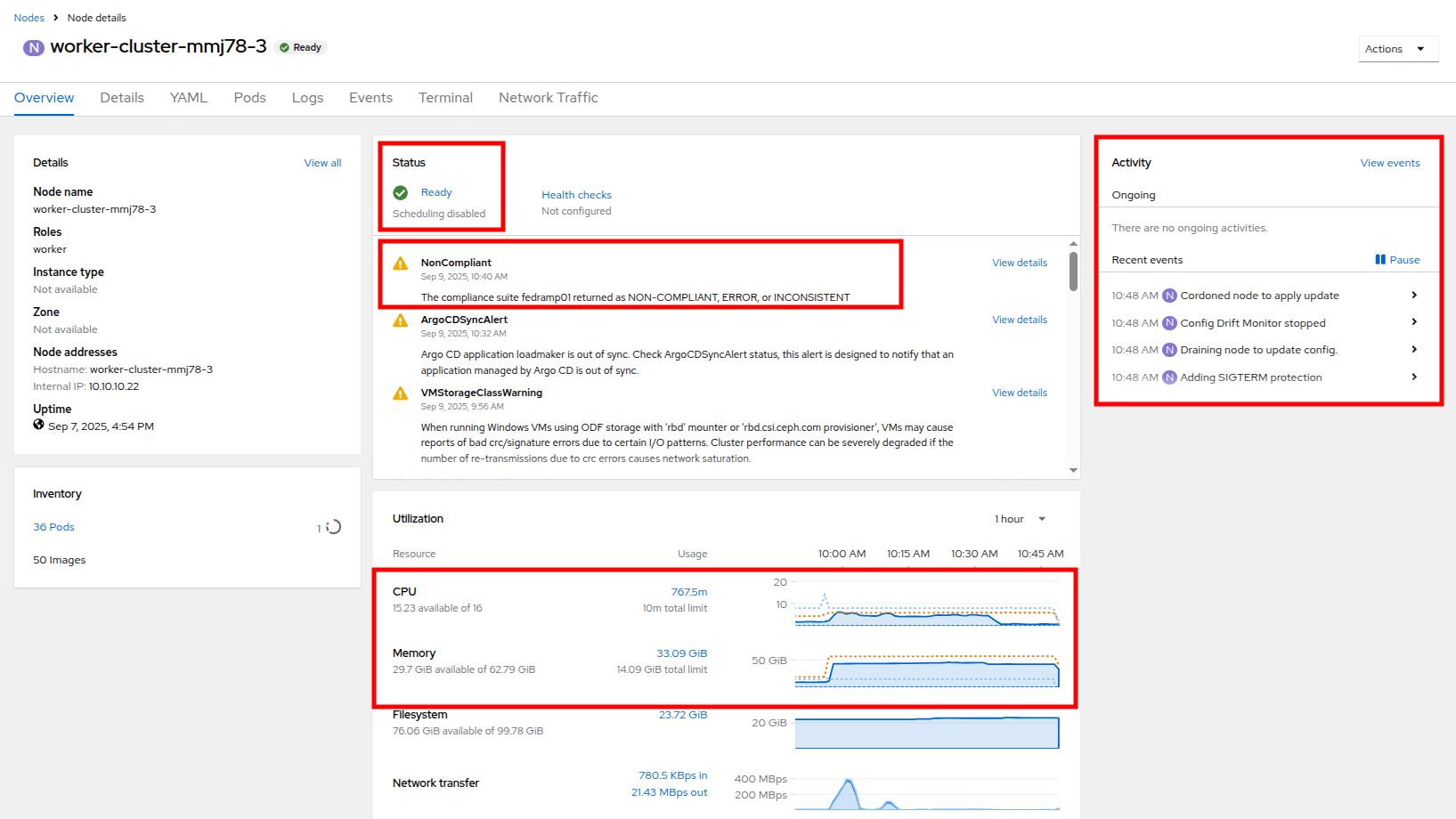
Figure 19. Node 3 Updating
| Note: This process can take quite a bit of time to complete depending on how busy the cluster currently is, and how many nodes there are to remediate as they each have to evict pods safely and reboot to apply the update. Also, you may be logged out of the cluster while the pods are being evacuated. |
- After several minutes the MachineConfig will be applied to each of the worker nodes in our cluster, and we can recheck our Compliance Scan results.
- Return to the Compliance Operator configuration by clicking on Operators and Installed Operators in the left side menu.
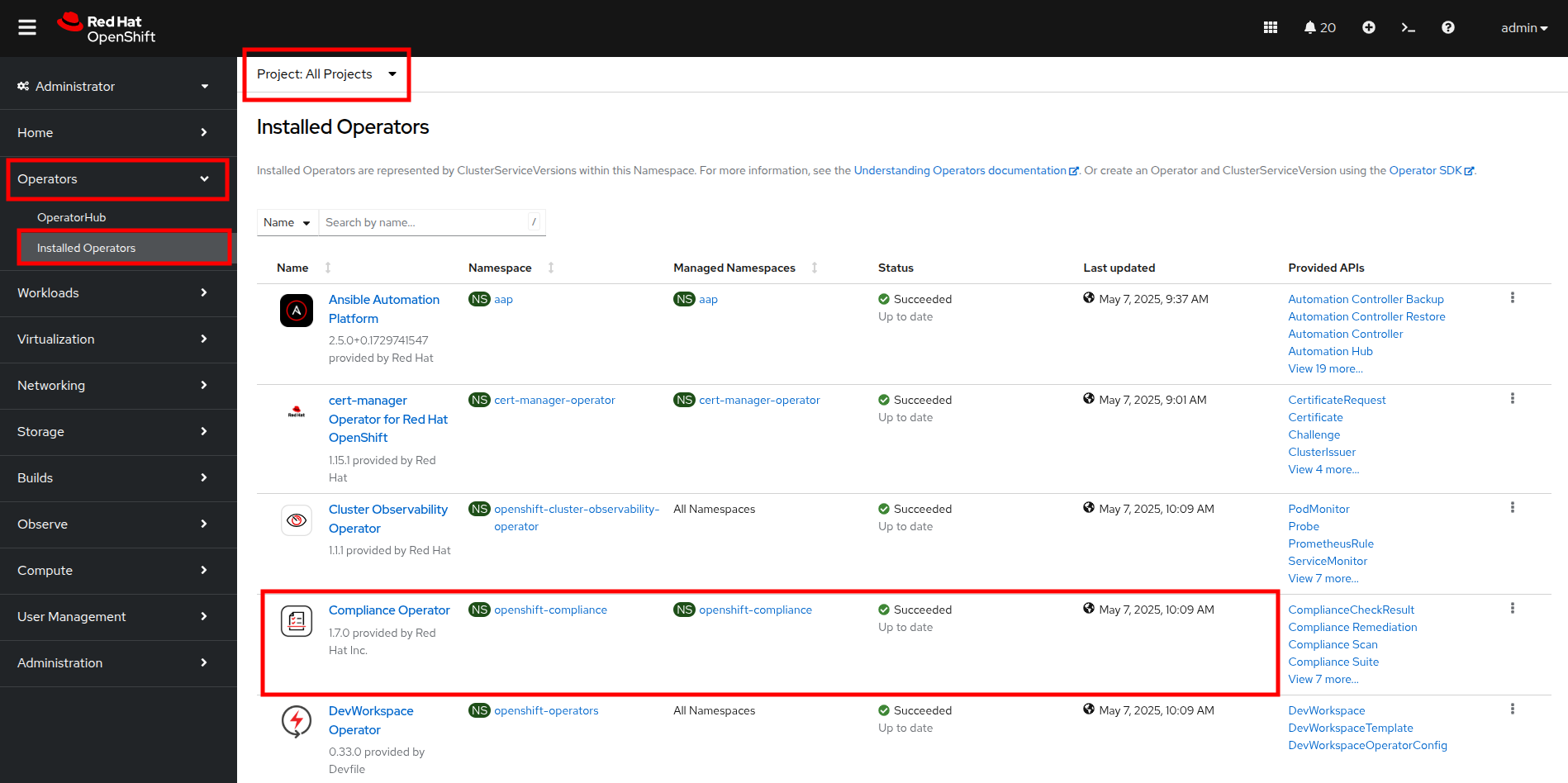
Figure 20. OpenShift Compliance Operator
- Click on the Compliance Scan tab, where you will see the scan we completed earlier. Click the three-dot menu, and select the option to delete the current scan.
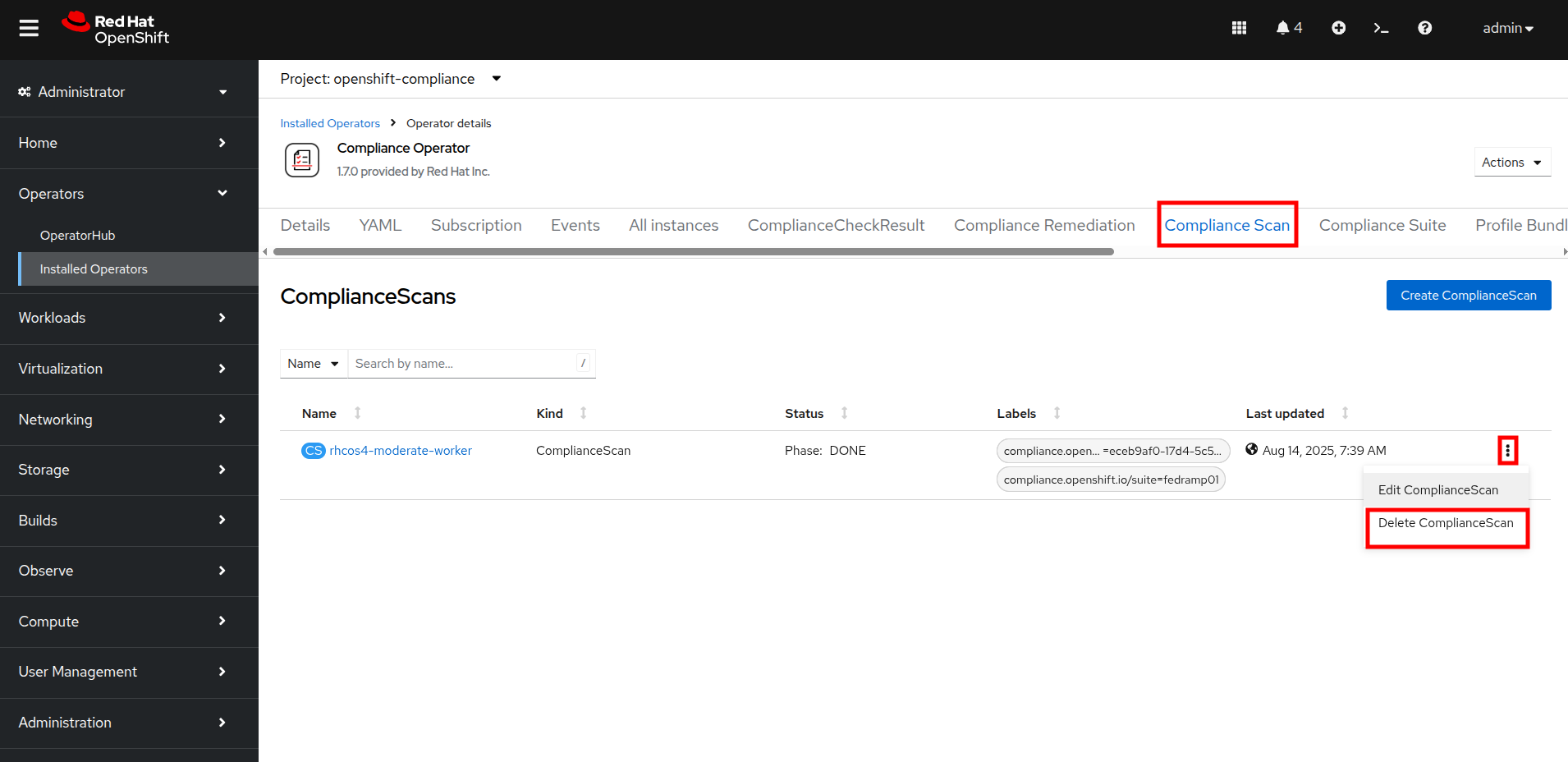
Figure 21. Delete compliance scan
- You will be prompted to be sure that you want to delete the current compliance scan. Click the Delete button.
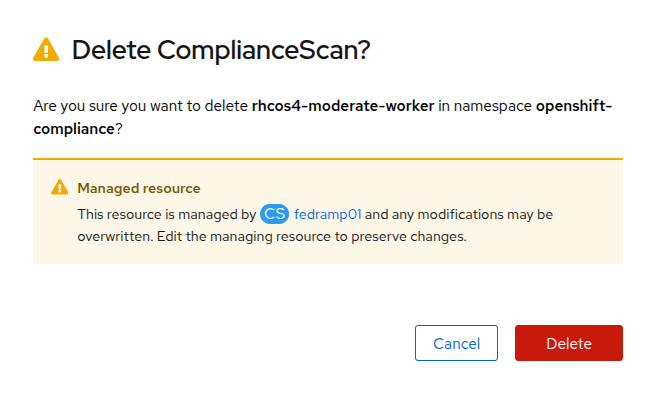
Figure 22. Delete scan prompt
- The Compliance Suite object defined earlier will automatically kick off a new scan which you will see appear on your screen.
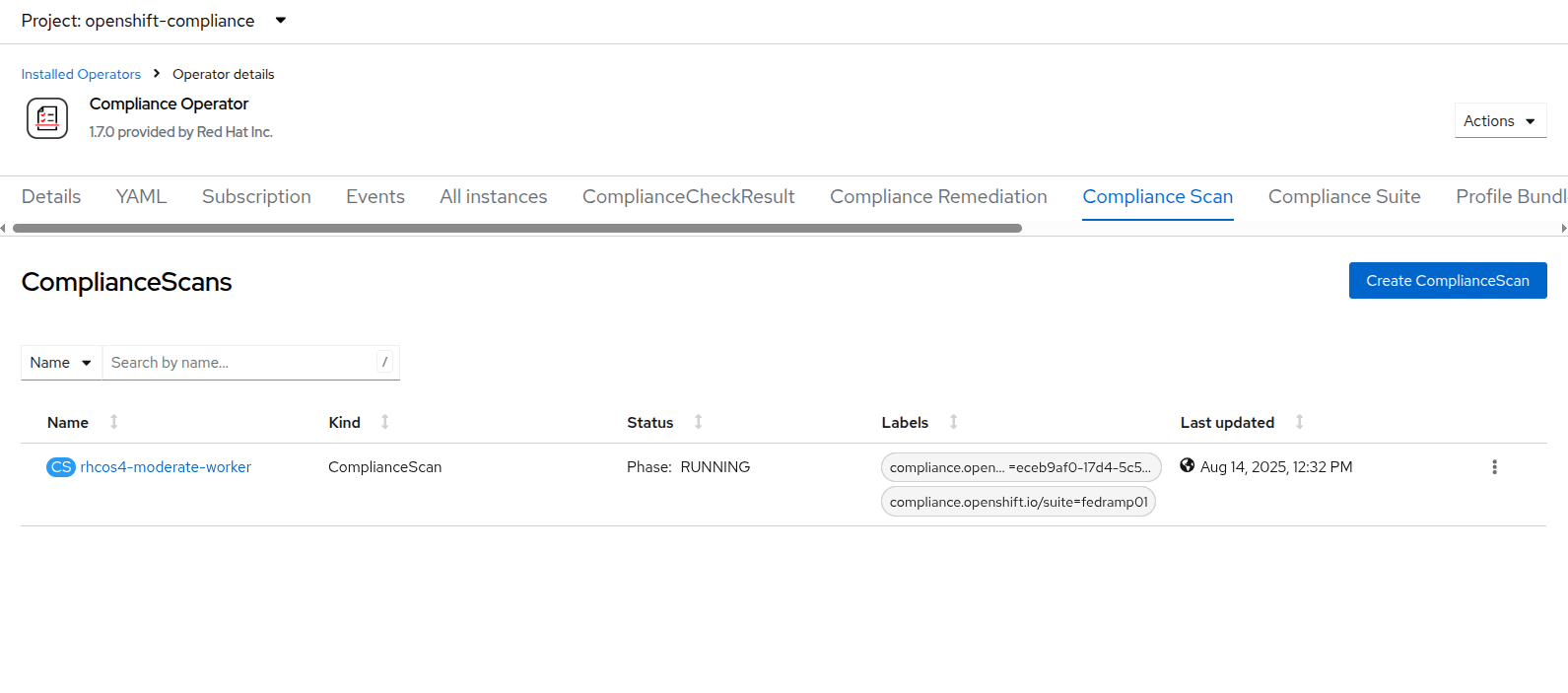
Figure 23. New compliance scan
- As before this scan will take a few minutes to complete. Once it is finished, the results can be viewed by clicking on the ComplianceCheckResult tab and then searching for the rhcos4-moderate-worker-coreos-pti-kernel-argument and noticing that its label is now check-status=PASS instead of FAIL.
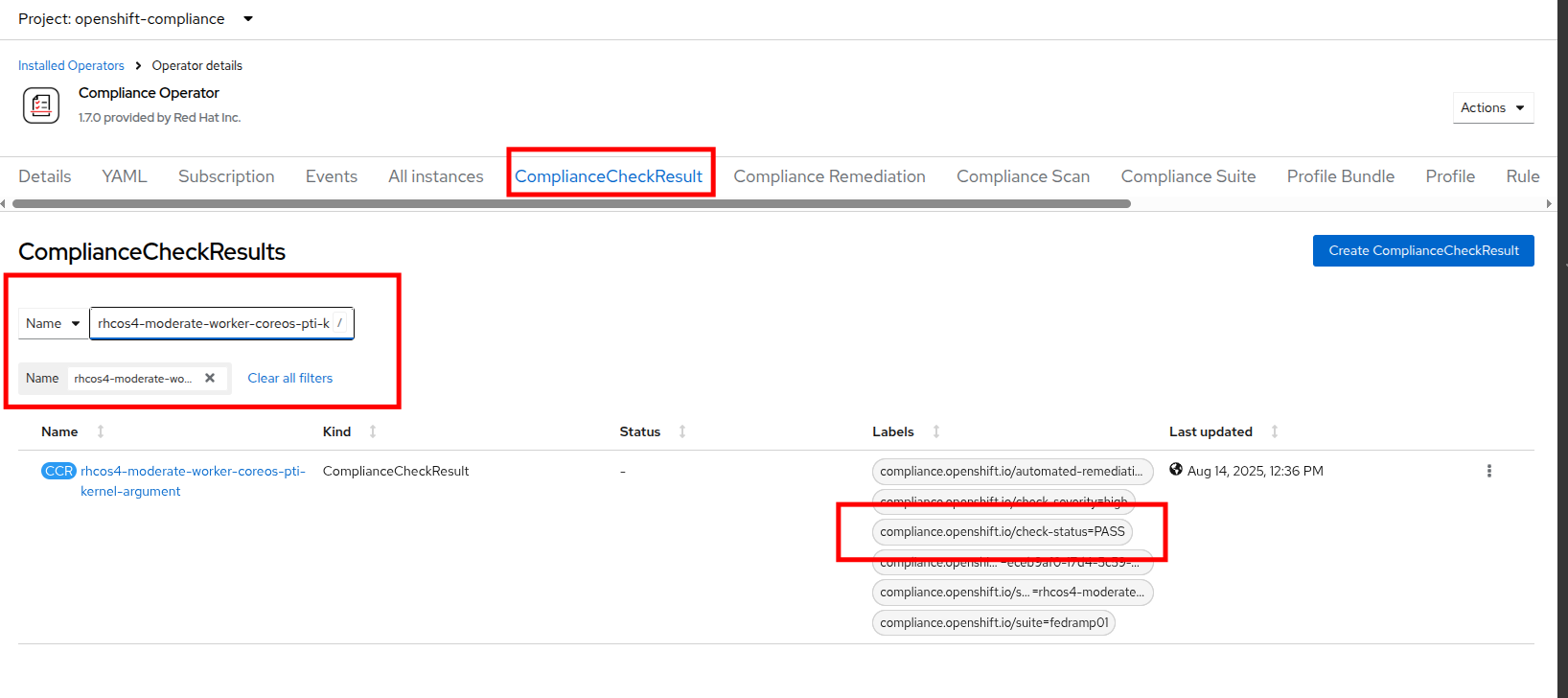
Figure 24. Check status pass
With the completion of these sections we have created a compliance scan and successfully remediated an identified vulnerability using the OpenShift Compliance Operator.
Configure role-based access controls for cluster roles
One of the notable features that OpenShift is known for compared to vanilla Kubernetes is its rich set of role-based access controls for separate user accounts and cluster roles that define what each user is able to do when logged into the cluster. In this section of the module, we are going to create a read-only account for our auditor and explore the limitations by which they are bound.
- Start by clicking on User Management and Users in the left side menu.
- You will see the current admin user that you are logged in as listed, and you will see that the identity is provided by the htpasswd_provider:admin authenticator.
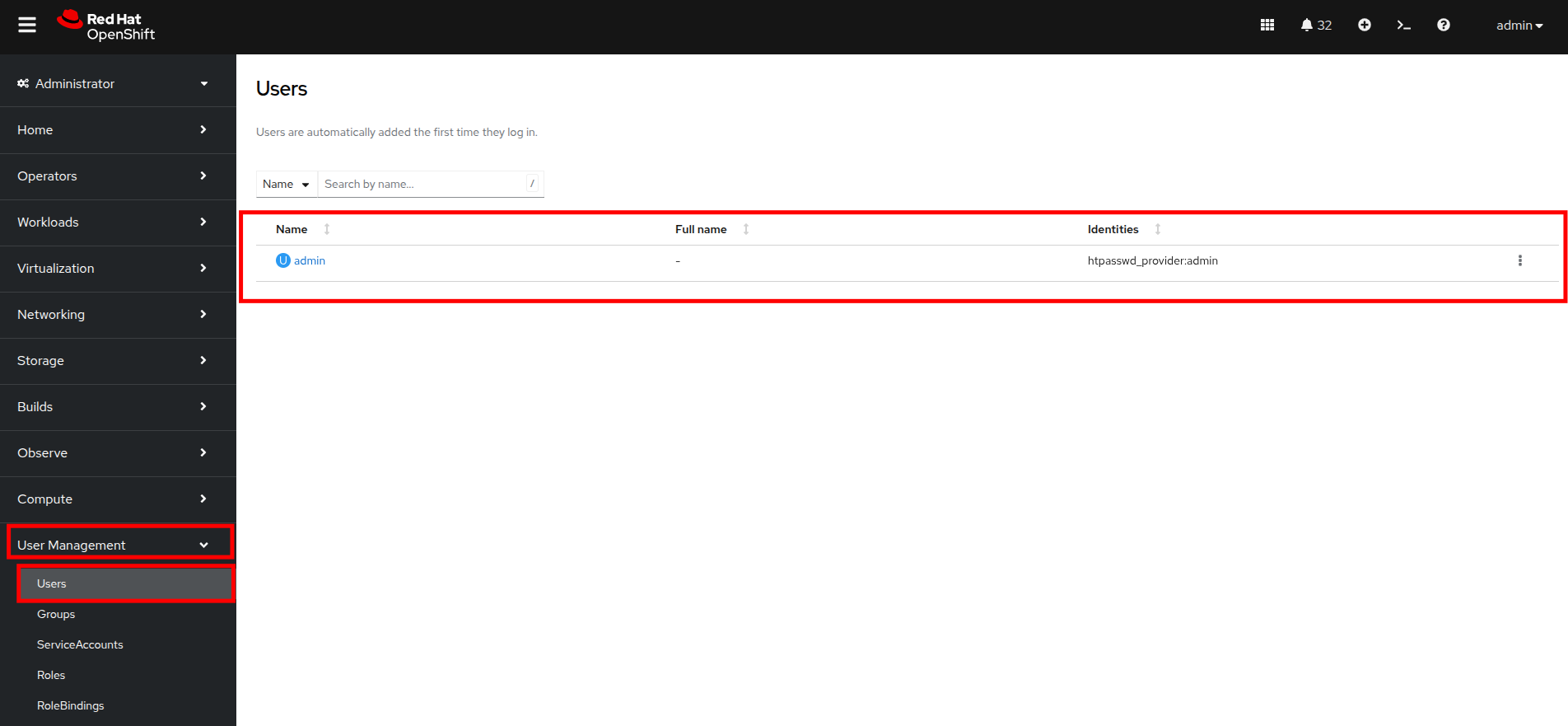
Figure 25. User list
| Note: If no other authentication source has been set up prior and you are logged in as the default kubeadmin account, you will see a wizard here to assist with setting up your first authentication source. |
Create a group
- Now click on Groups in the left menu, then click the button for Create Group.
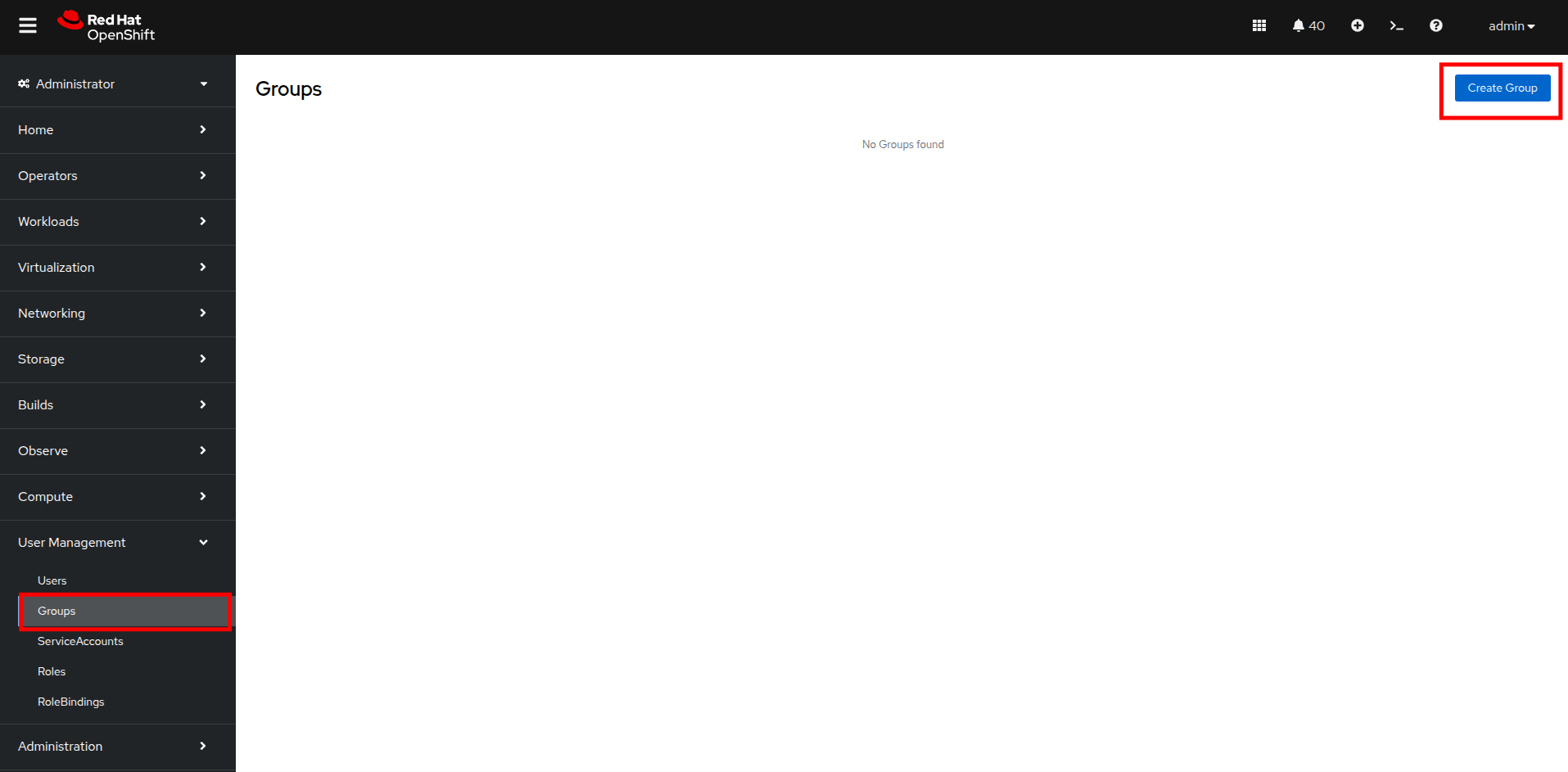
Figure 26. Create group
- In the Create Group YAML dialog, set the name of the group to auditor_readonly and add the users auditor1 and auditor2. Click the Create button.
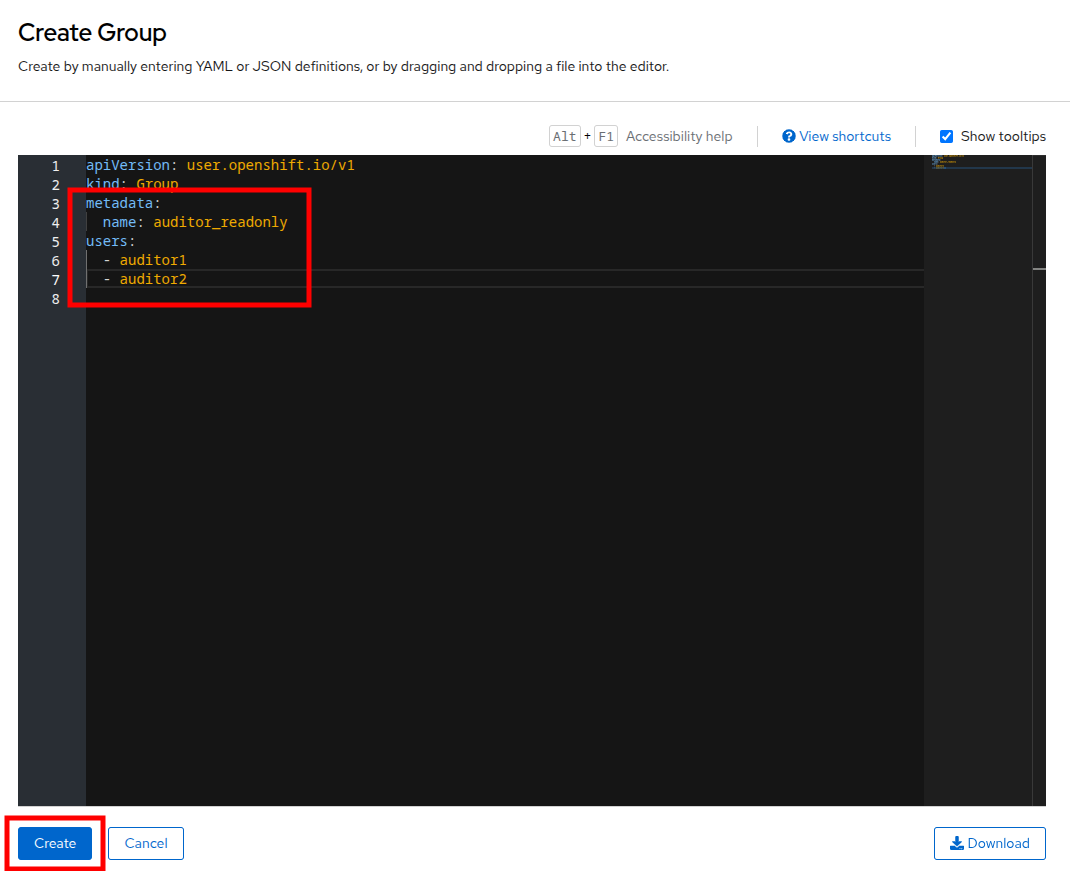
Figure 27. Create group settings
- You will be presented with the Group details screen where you can see the two user accounts listed, and we can define permissions by assigning the group a role binding. Click on the RoleBindings menu.
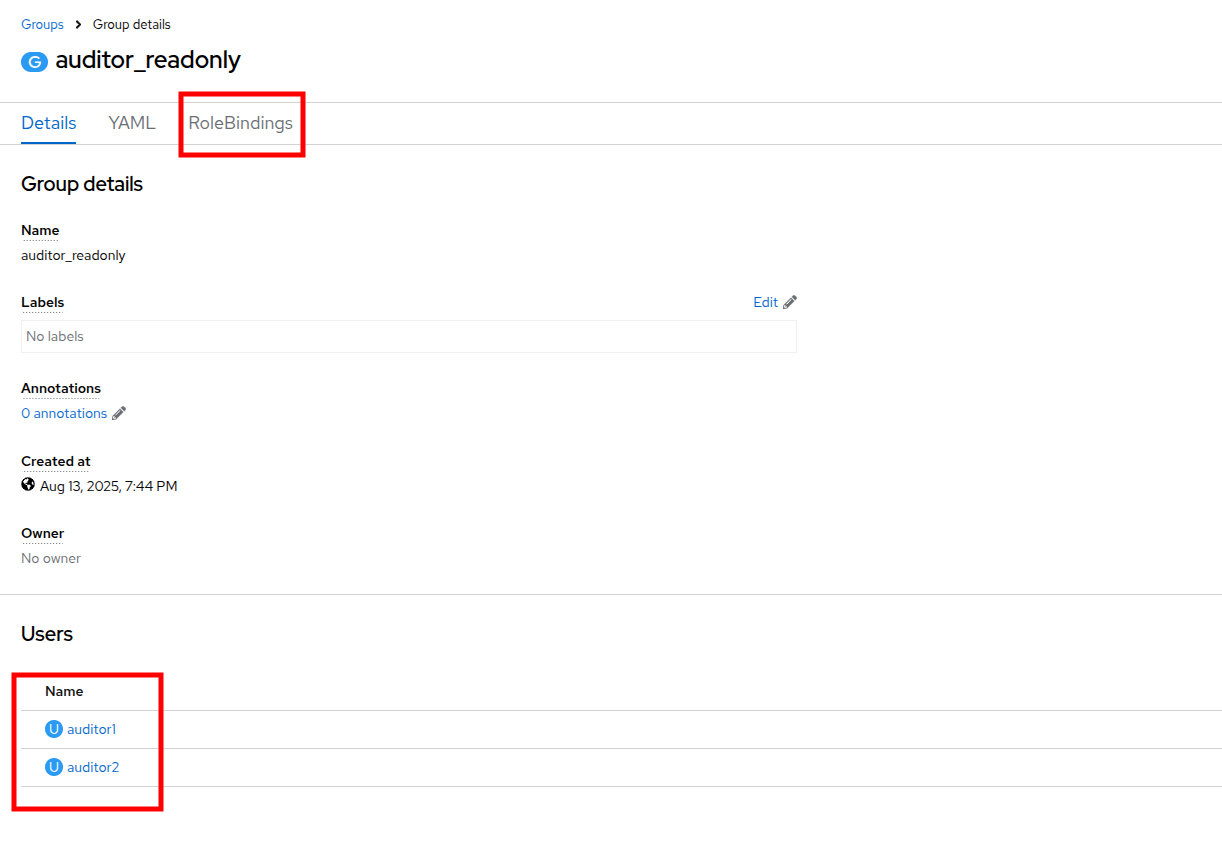
Figure 28. Group details
- After clicking on RoleBindings, click the Create binding button.
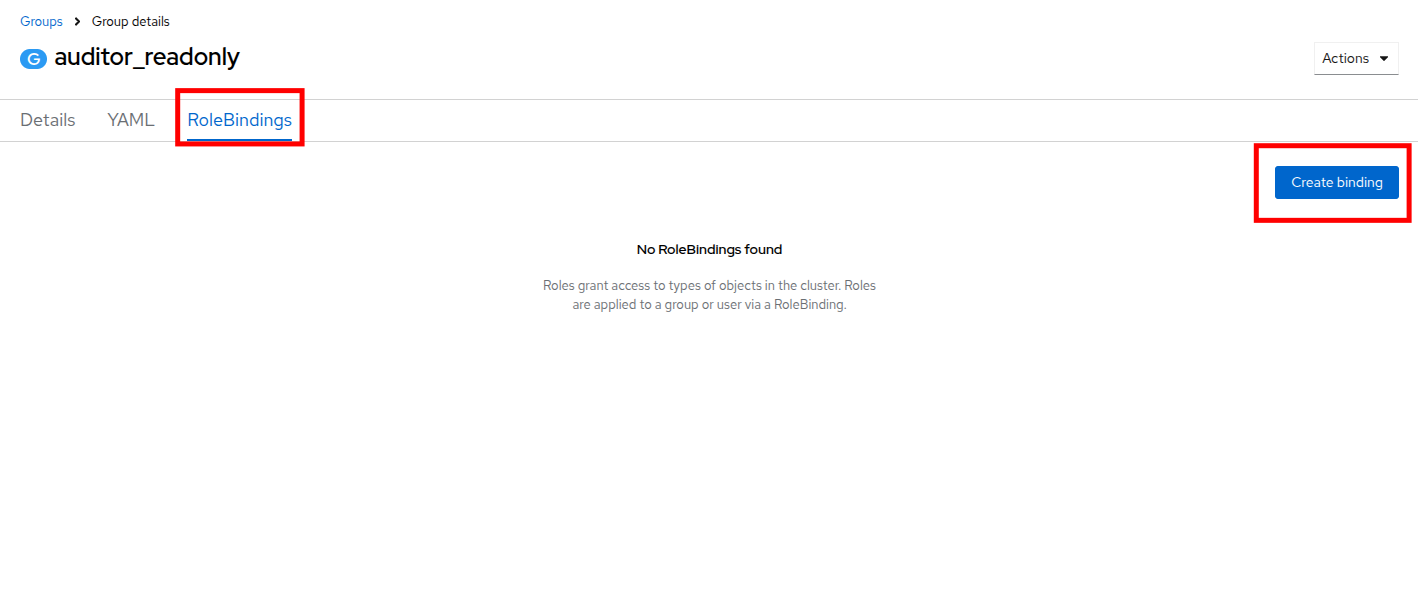
Figure 29. Create binding
- This will bring you to the Create RoleBinding page. On this page, select the following to create a read-only role binding for the auditor, and then click the Create button:
- Binding type: Cluster-wide role binding
- Name: cluster_readonly
- Role name: view
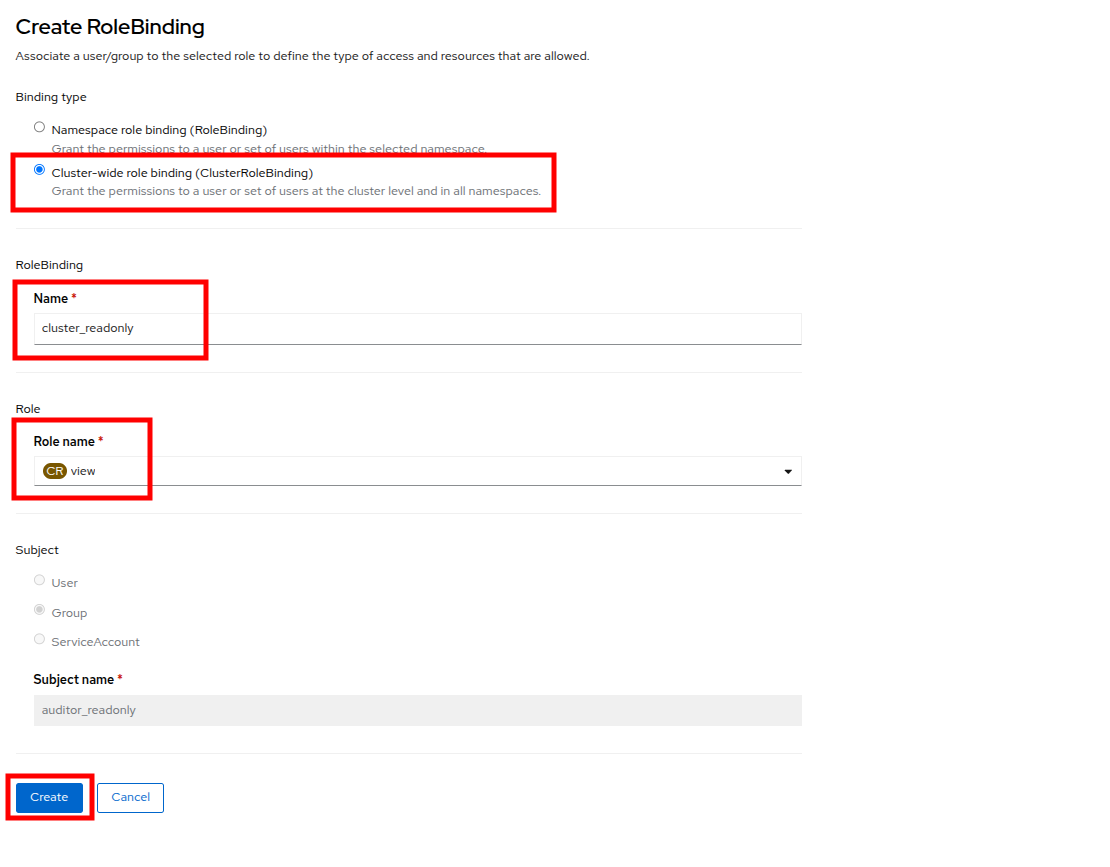
Figure 30. RoleBinding details
Create the user accounts
- With the role binding created, we now need to add our two auditor accounts to our group.
- In the left side menu, click Administration and CustomResourceDefinitions and use the search bar to look for the OAuth entry. When you find it, click it.
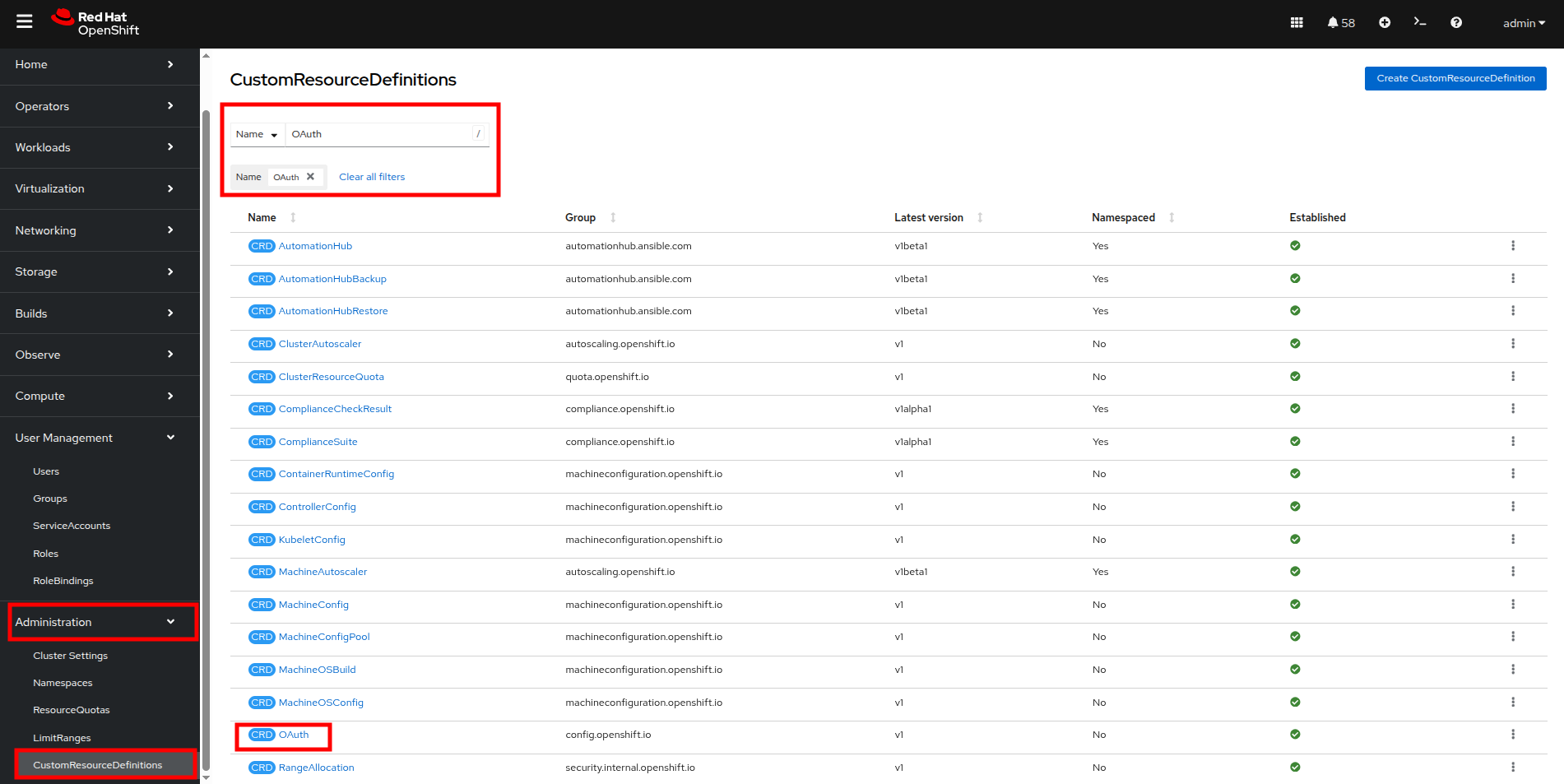
Figure 31. CRDs OAuth
- This will load the details page for the OAuth custom resource definition. On this page, click on Instances and then click on cluster.
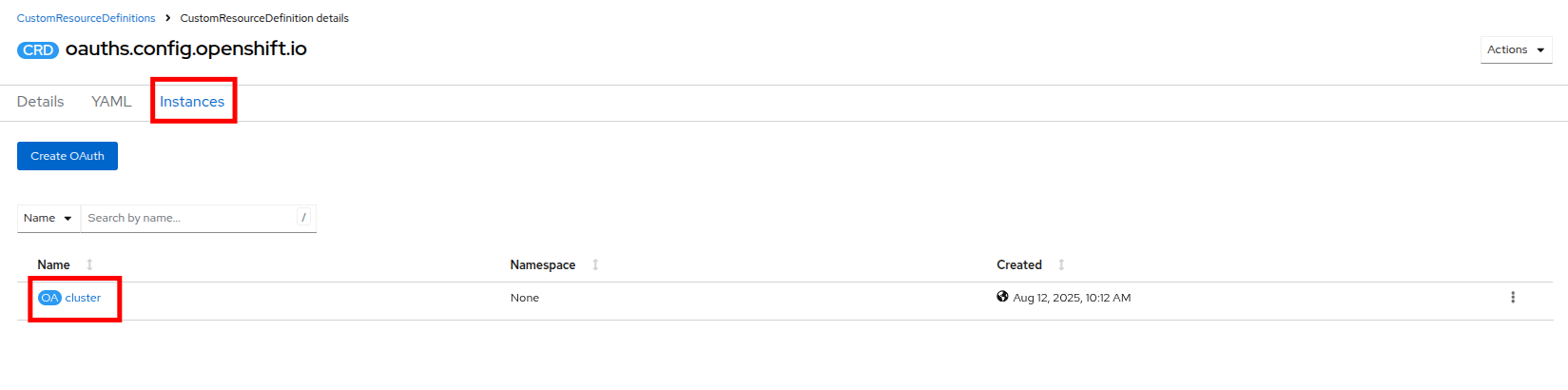
Figure 32. OAuth instances
- On the cluster configuration page you will see where the htpasswd_provider is already currently configured, but there will also be a dropdown menu that has the word Add. You can select another provider from that list. Click and select HTPasswd as the option.
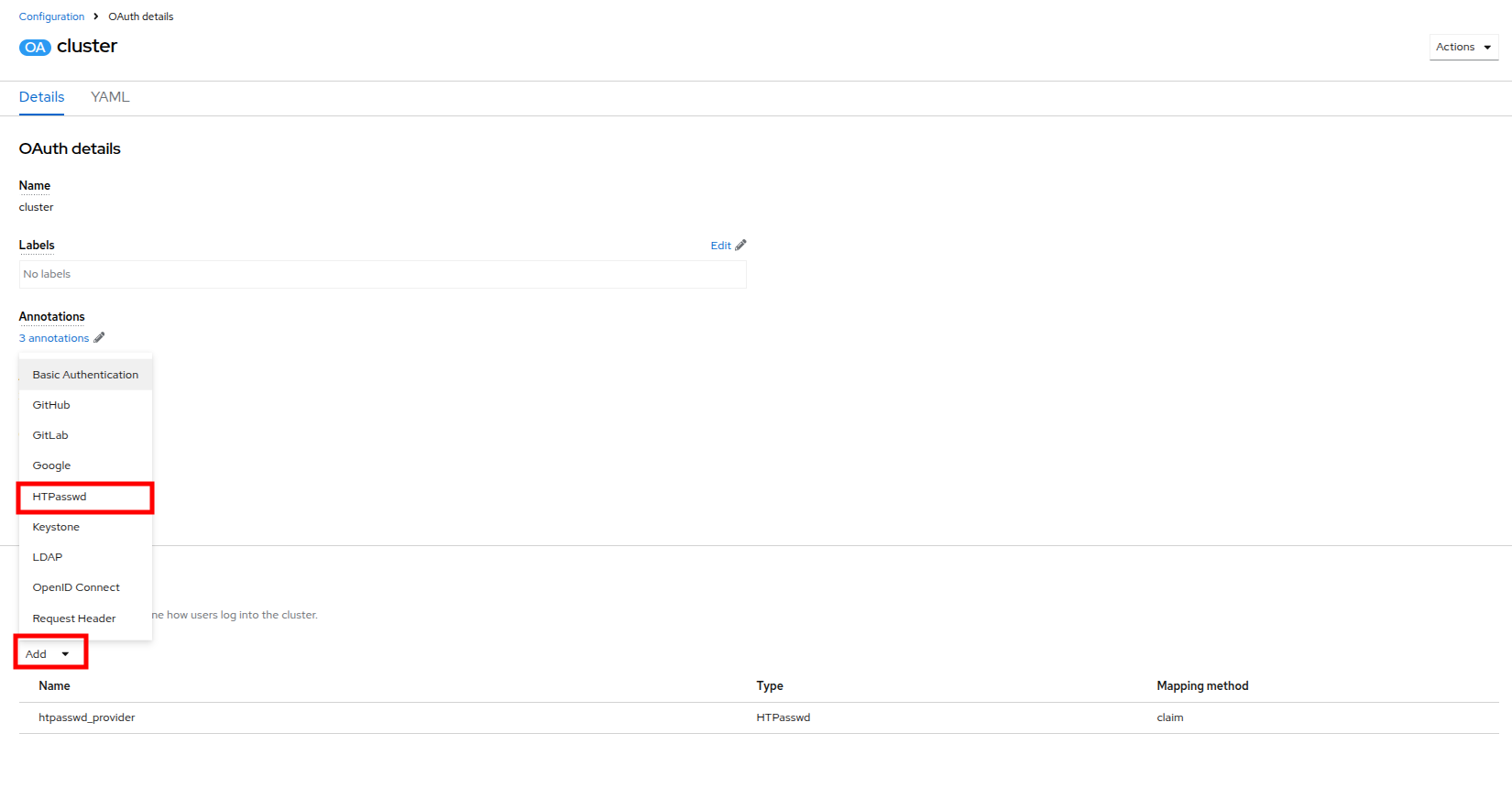
Figure 33. Add authentication
| Note: Notice that in addition to HTPasswd, there are many options that allow you to integrate external authorization and authentication solutions with Red Hat OpenShift, which is perfect for larger enterprises. |
You will be presented with a page that allows you to add in an HTPasswd file or supply usernames and hashed credentials for that purpose. Set the name of the identity provider to auditor_login and paste the following syntax into the text box before clicking the Add button.
auditor1:$apr1$VtSYSShP$CikLVoVy5sobCaHCvuxCv. auditor2:$apr1$4Vpe3O5u$OhjtFGDNHnl2RWiNnhlhZ0
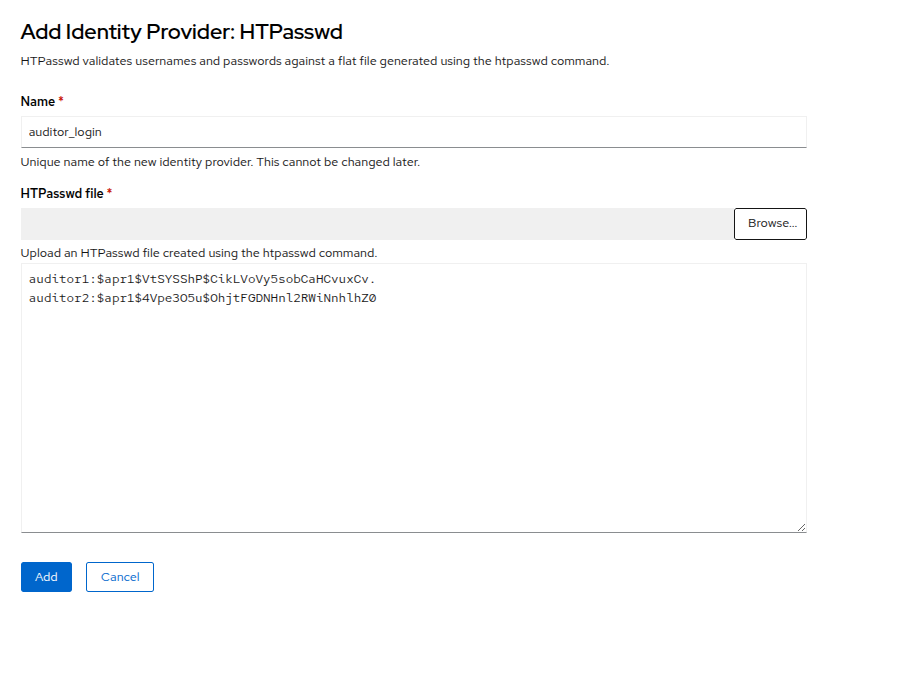
Figure 34. Add identity provider
- Once added you will be returned to the Cluster OAuth details page and you will now see two identity providers listed, along with a blue notice that OAuth is being reconfigured. Click on the link provided for View authentication conditions for reconfiguration status.
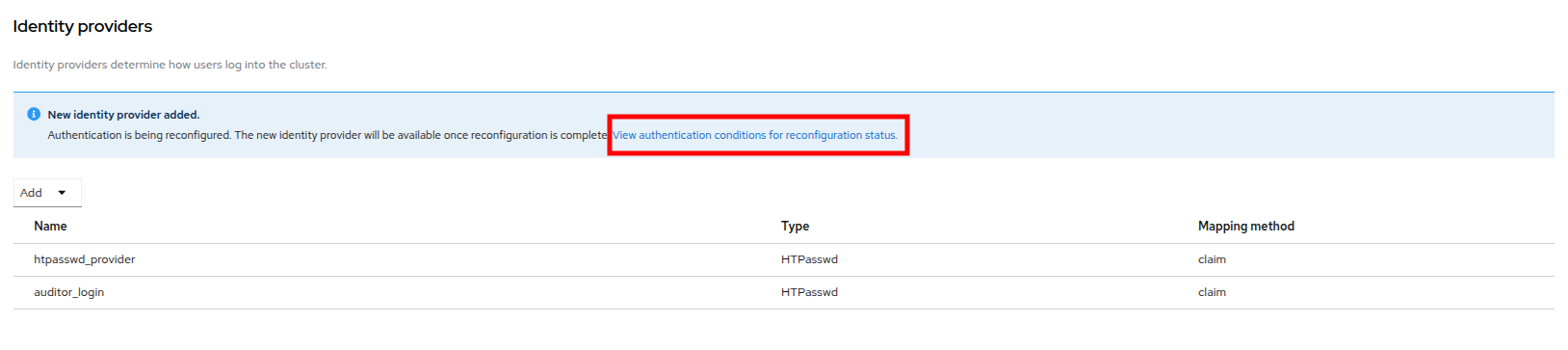
Figure 35. OAuth reconfiguration
- You will be brought to a page that shows the progress as the authentication cluster operator is reconfigured. Once all the pods are restarted, the status will change to Available and the message will say All is well.
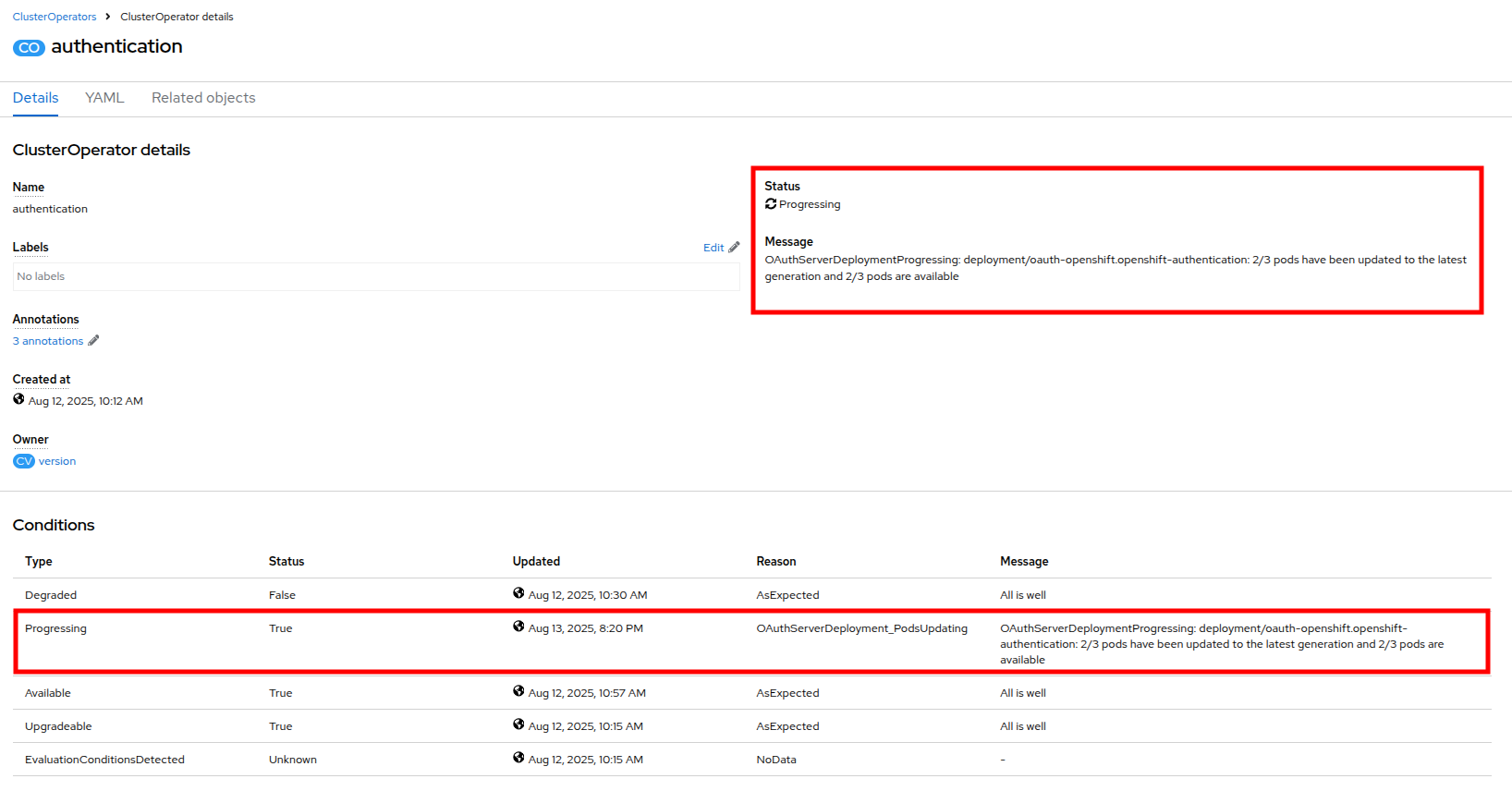
Figure 36. OAuth reconfiguration progressing
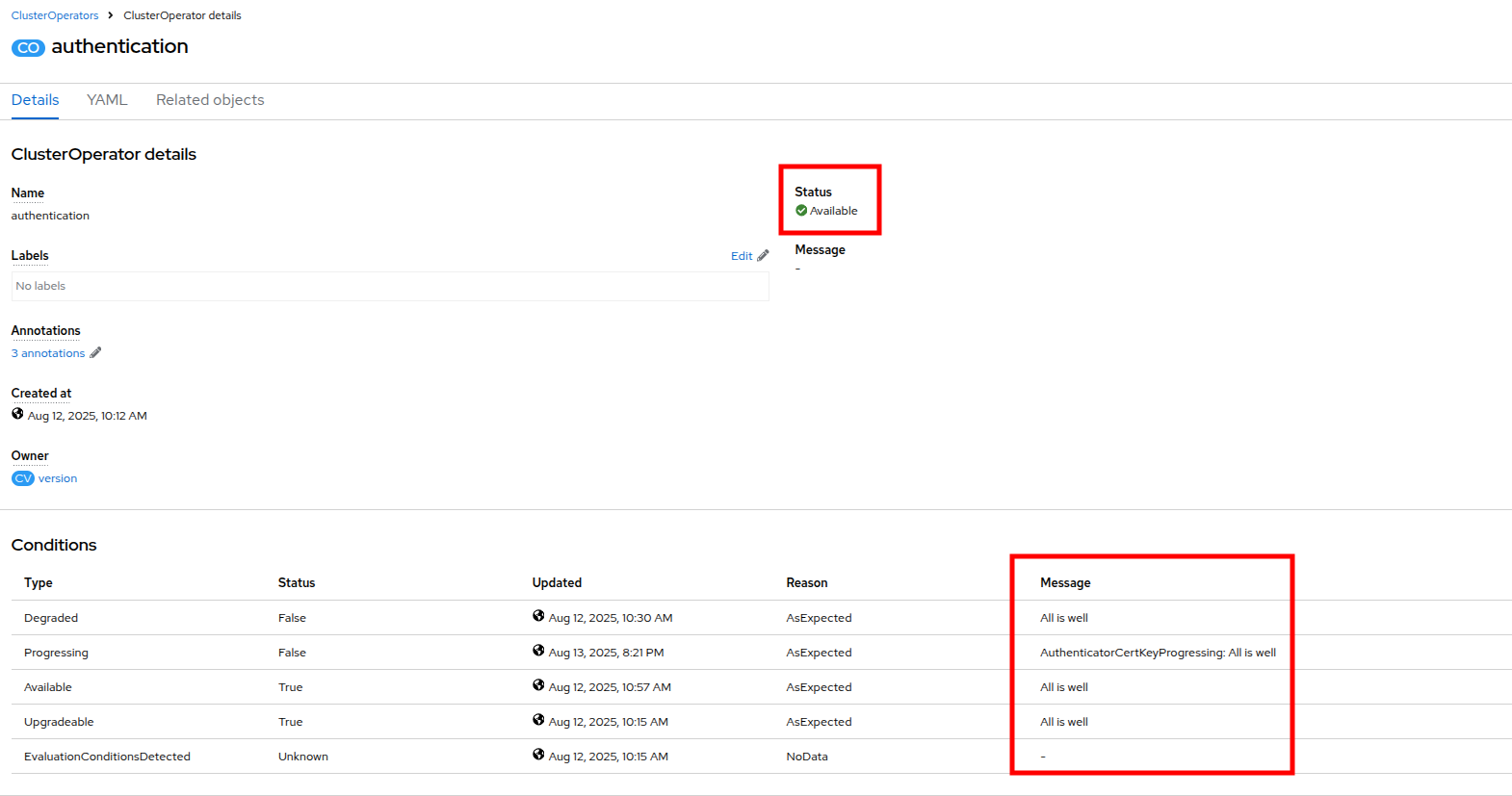
Figure 37. OAuth reconfiguration complete
Test the configuration
- With the OAuth configuration complete, we can now test our auditor login and the limits of their account.
- Log out of OpenShift by clicking on admin at the top, and selecting Log out from the dropdown menu.
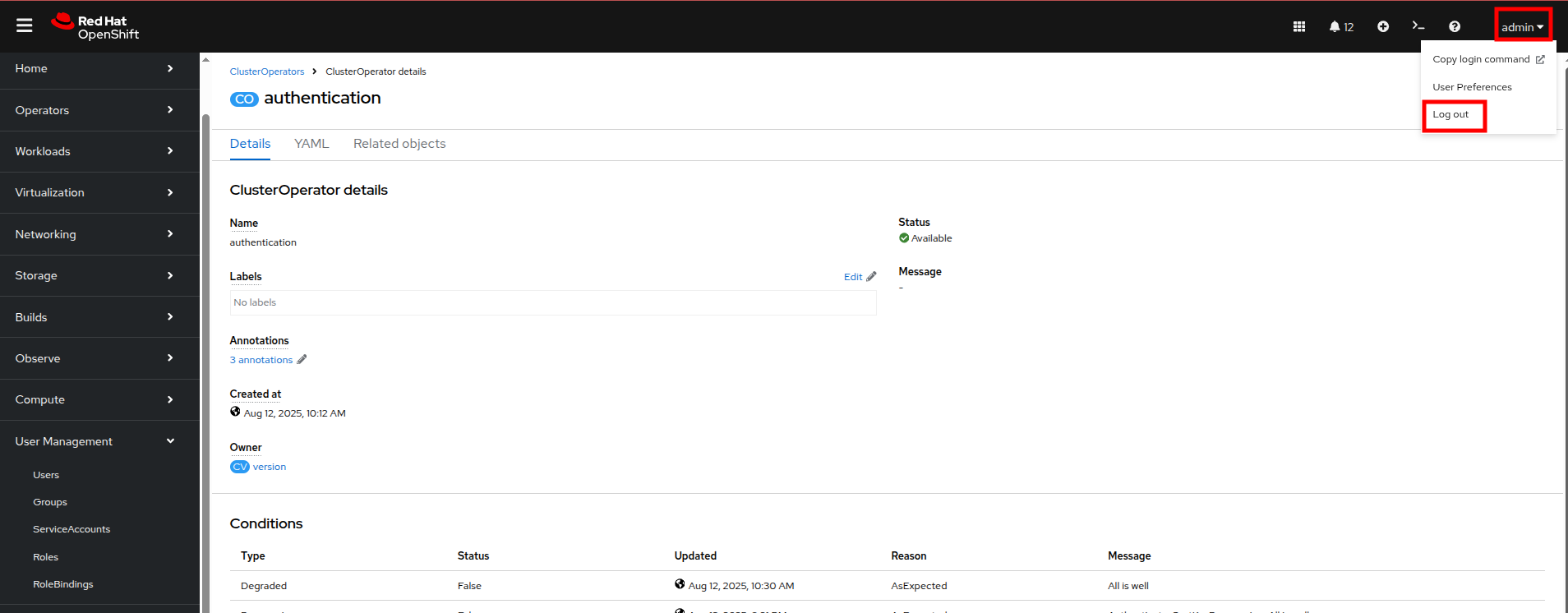
Figure 38. Log out of OpenShift
- There is now an option to login with the auditor_login identity provider on the main OpenShift page.
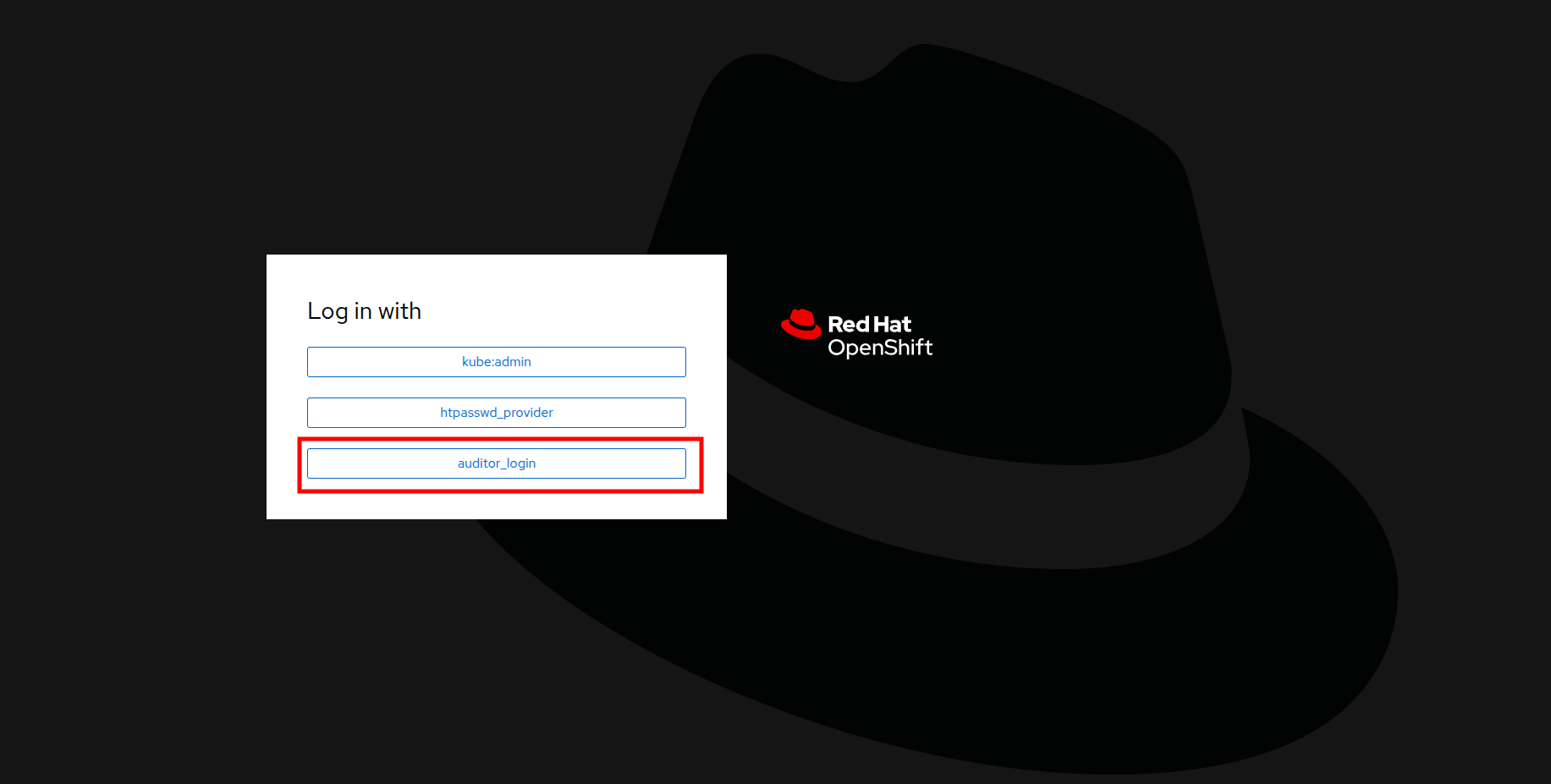
Figure 39. Log in to OpenShift
- Click on auditor_login and when presented use the following username and password combination:
- Username: auditor1
- Password: auditor1pass!
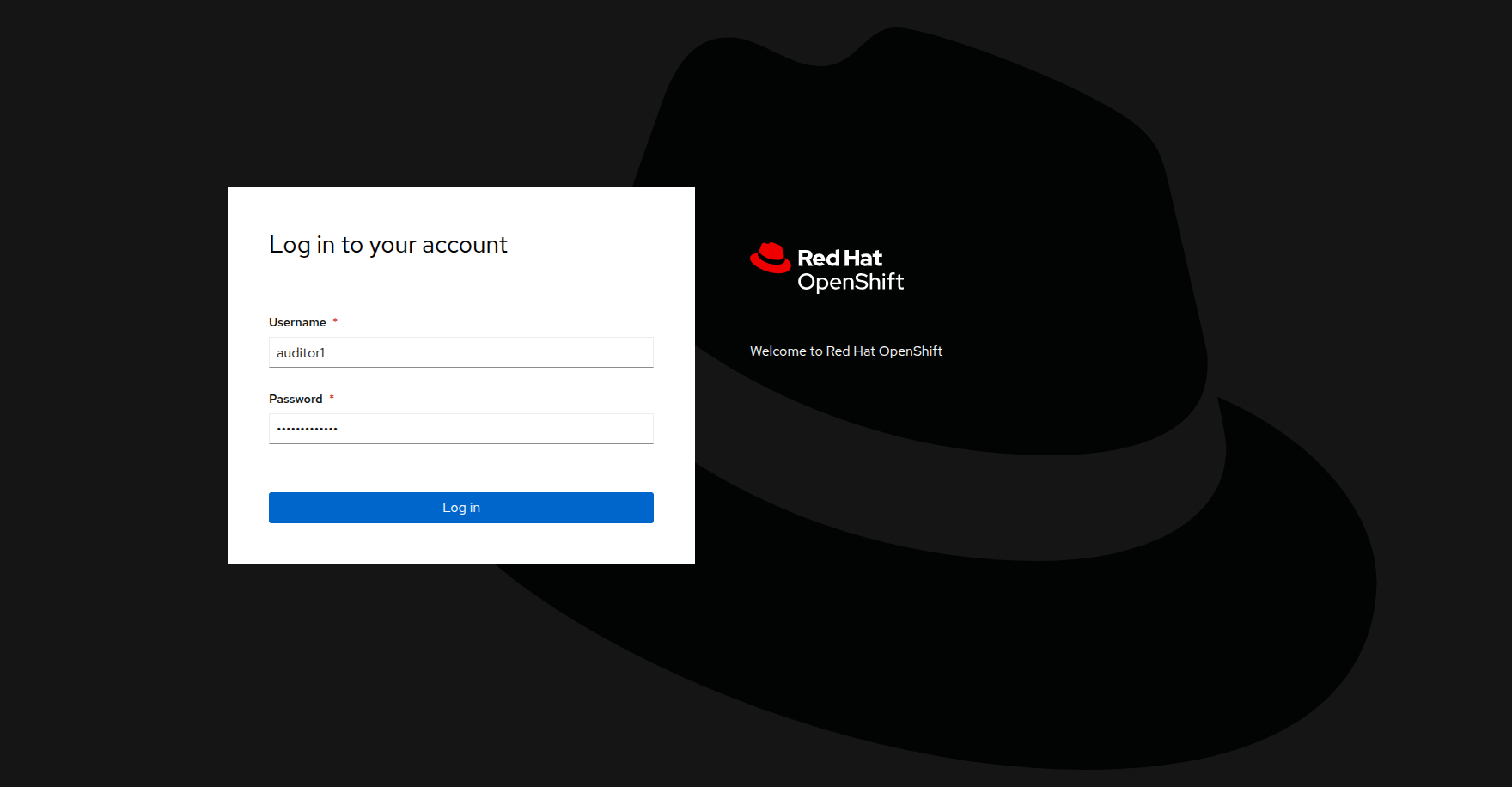
Figure 40. Auditor 1 login
- When the auditor logs in with the read-only permissions, they will be able to see only a limited view of the OpenShift console from the Admin perspective.
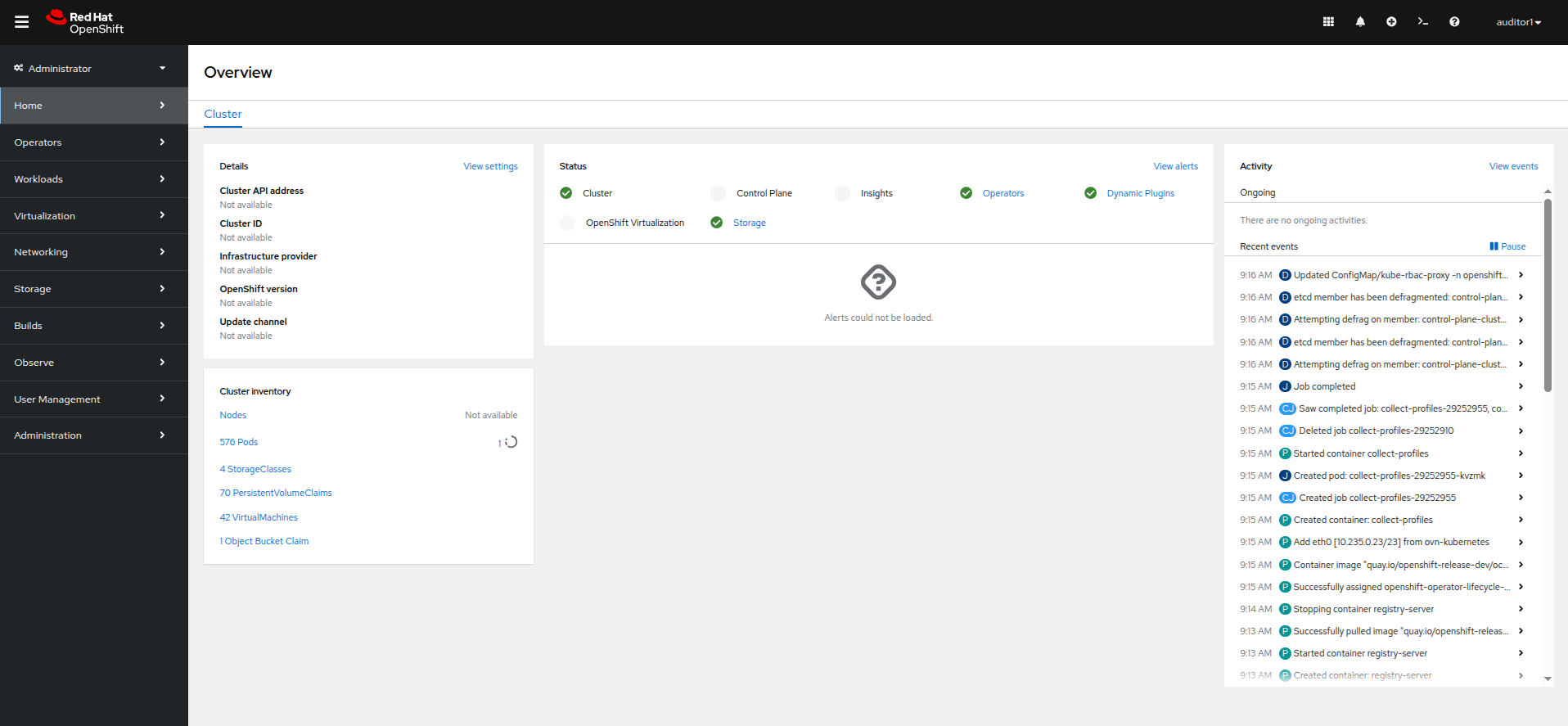
Figure 41. Auditor 1 admin view
- If the auditor needs to validate our virtual machine environment, they can still access that by clicking on Virtualization and VirtualMachines in the left side menu.
- They can see all virtual machines in each project, and their current status.
- The auditor can even click on a specific machine and get additional details. In this case, they want to test the database server in the webapp-vms namespace.
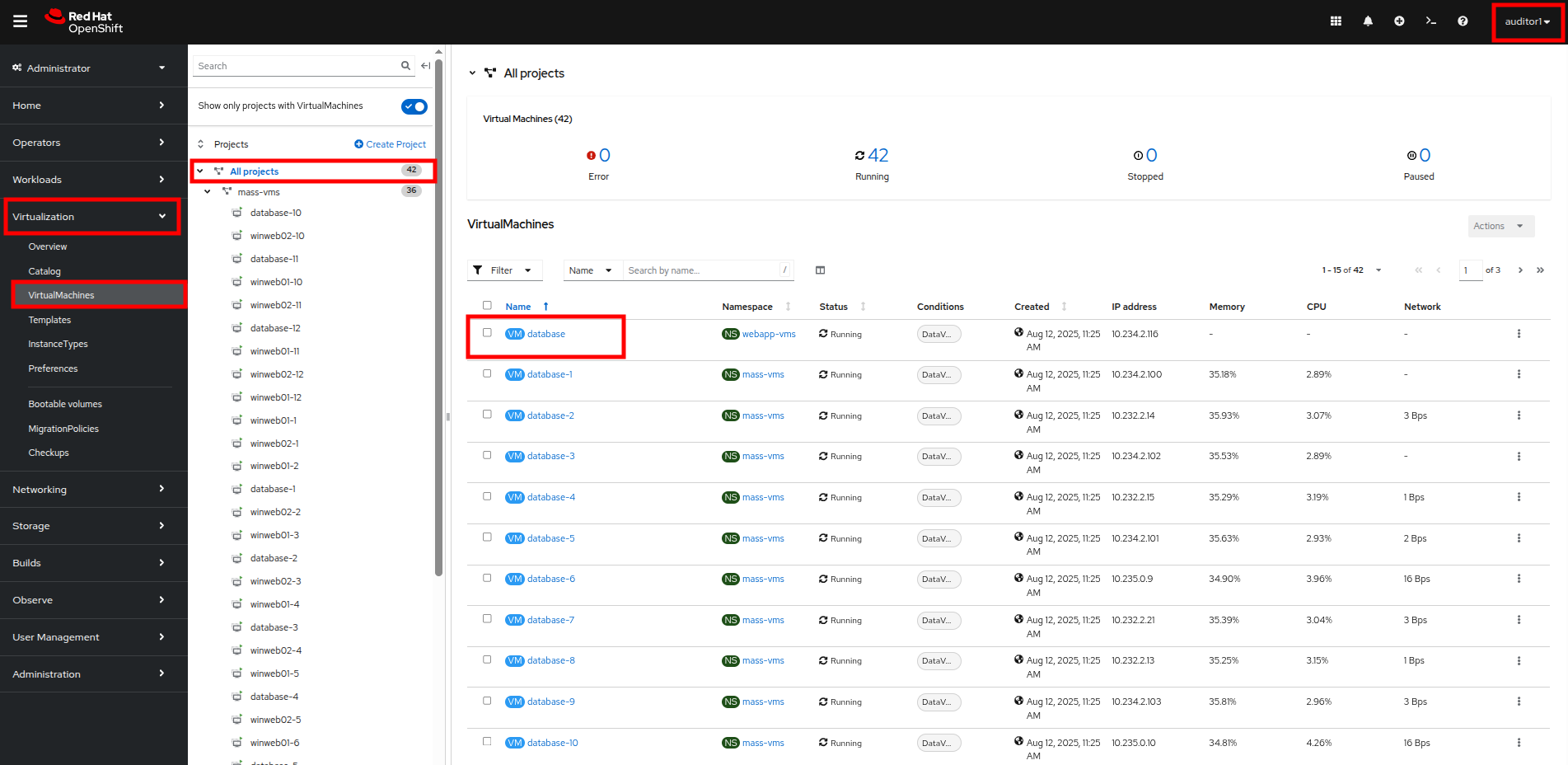
Figure 42. Auditor 1 VM view
- Once they are on the VirtualMachine details page, they can see the information about the virtual guest, including its CPU and memory utilization. However, they are prevented from launching the VNC console or manipulating the machine state in any way, as the buttons are greyed out.
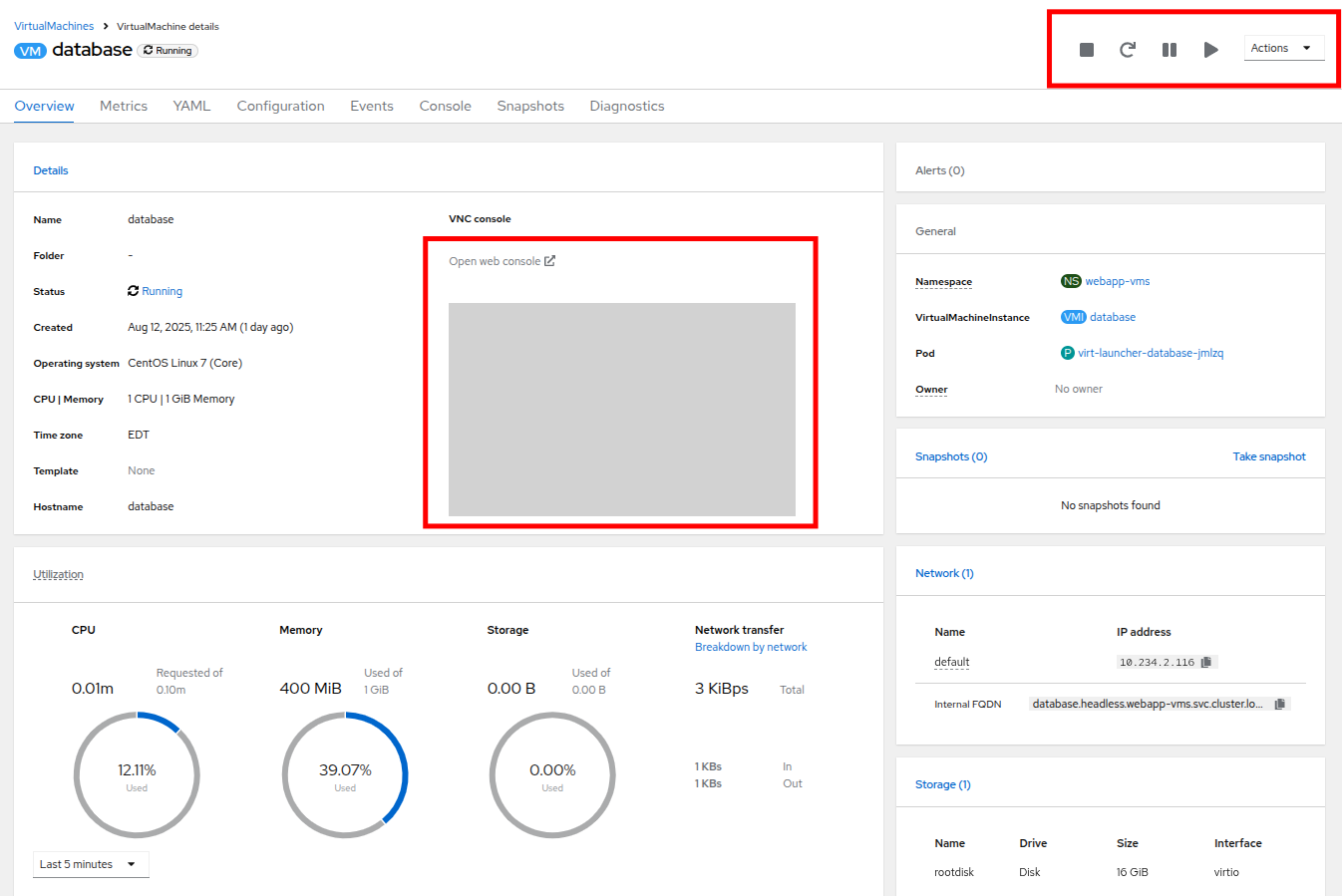
Figure 43. Auditor 1 database ReadOnly
- At your leisure, you may explore the UI and confirm that the Auditor1 account is read-only. When you are finished, proceed to the next module.
In this section of our lab we created a limited read-only account with view permissions for the auditors that will be examining our infrastructure.
Summary
In this module we were preparing for our company’s annual security audit. We can tighten our OpenShift Virtualization security by using the Compliance Operator to automate standard-setting scans and applications. We further strengthen this posture by configuring RBAC to limit access to specific individuals.
In the next lesson, we’ll cover advanced networking and security tasks.