이 콘텐츠는 선택한 언어로 제공되지 않습니다.
Chapter 5. Configuring OAuth authorization
This section describes how to connect Red Hat CodeReady Workspaces as an OAuth application to supported OAuth providers.
5.1. Configuring GitHub OAuth
OAuth for GitHub allows for automatic SSH key upload to GitHub.
Procedure
Set up the GitHub OAuth client. The Authorization callback URL is filled in the next steps.
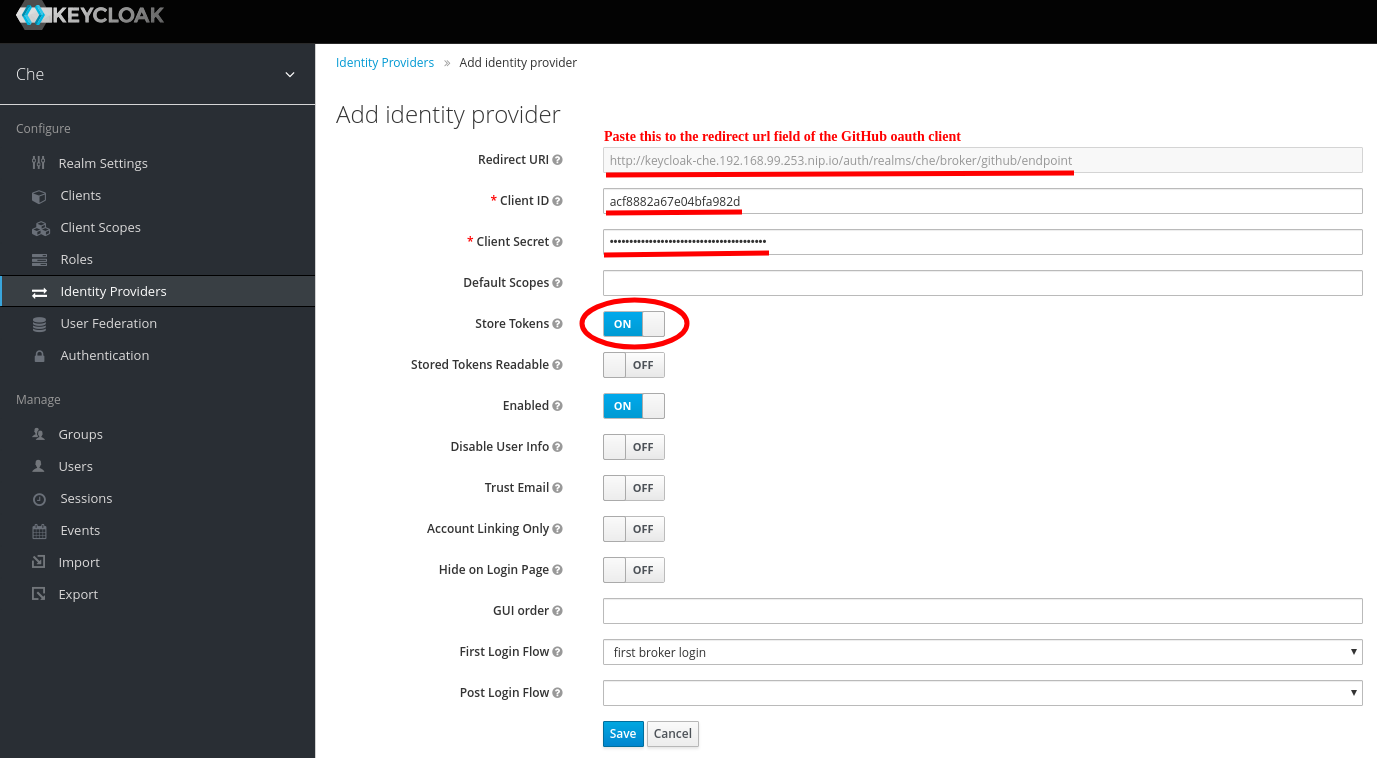
- Go to the RH-SSO administration console and select the Identity Providers tab.
- Select the GitHub identity provider in the drop-down list.
- Paste the Redirect URI to the Authorization callback URL of the GitHub OAuth application.
- Fill the Client ID and Client Secret from the GitHub oauth app.
- Enable Store Tokens.
Save the changes of the Github Identity provider and click Register application in the GitHub oauth app page.
5.2. Configuring OpenShift OAuth
For users to interact with OpenShift, they must first authenticate to the OpenShift cluster. OpenShift OAuth is a process in which users prove themselves to a cluster through an API with obtained OAuth access tokens.
Authentication with the OpenShift connector plugin is a possible way for CodeReady Workspaces users to authenticate with an OpenShift cluster.
The following section describes the OpenShift OAuth configuration options and its use with a CodeReady Workspaces.
Prerequisites
-
The OpenShift command-line tool,
ocis installed.
Procedure
To enable OpenShift OAuth automatically, deployed CodeReady Workspaces using the crwctl with the --os-oauth option. See the crwctl server:start specification chapter.
For CodeReady Workspaces deployed in single-user mode:
Register CodeReady Workspaces OAuth client in OpenShift. See the Register an OAuth client in OpenShift chapter.
$ oc create -f <(echo ' kind: OAuthClient apiVersion: oauth.openshift.io/v1 metadata: name: che secret: "<random set of symbols>" redirectURIs: - "<CodeReady Workspaces api url>/oauth/callback" grantMethod: prompt ')Add the OpenShift SSL certificate to the CodeReady Workspaces Java trust store.
Update the OpenShift deployment configuration.
CHE_OAUTH_OPENSHIFT_CLIENTID: <client-ID> CHE_OAUTH_OPENSHIFT_CLIENTSECRET: <openshift-secret> CHE_OAUTH_OPENSHIFT_OAUTH__ENDPOINT: <oauth-endpoint> CHE_OAUTH_OPENSHIFT_VERIFY__TOKEN__URL: <verify-token-url>-
<client-ID>a name specified in the OpenShift OAuthClient. -
<openshift-secret>a secret specified in the OpenShift OAuthClient. <oauth-endpoint>the URL of the OpenShift OAuth service:- For OpenShift 3 specify the OpenShift master URL.
-
For OpenShift 4 specify the
oauth-openshiftroute.
-
<verify-token-url>request URL that is used to verify the token.<OpenShift master url>/apican be used for OpenShift 3 and 4. - See CodeReady Workspaces configMaps and their behavior.
-