此内容没有您所选择的语言版本。
Chapter 1. Java EE Declarative Security Overview
Rather than embedding security into your business component, the Java EE security model is declarative: you describe the security roles and permissions in a standard XML descriptor. This isolates security from business-level code because security tends to be more a function of where the component is deployed than an inherent aspect of the component's business logic.
For example, consider an Automatic Teller Machine (ATM) component used to access a bank account. The security requirements, roles, and permissions of the component will vary independently of how you access the bank account. How you access your account information may also vary based on which bank is managing the account, or where the ATM is located.
Securing a Java EE application is based on the specification of the application security requirements via the standard Java EE deployment descriptors. You secure access to EJBs and web components in an enterprise application by using the
ejb-jar.xml and web.xml deployment descriptors. The following sections look at the purpose and usage of the various security elements.
1.1. Security References
复制链接链接已复制到粘贴板!
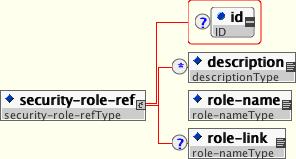
Both Enterprise Java Beans (EJBs) and servlets can declare one or more <security-role-ref> elements. Figure 1.1, “The <security-role-ref> element” describes the <security-role-ref> element, its child elements, and attributes.
Figure 1.1. The <security-role-ref> element
This element declares that a component is using the <role-name> element's
role-nameType attribute value as an argument to the isCallerInRole(String) method. By using the isCallerInRole method, a component can verify whether the caller is in a role that has been declared with a <security-role-ref> or <role-name> element. The <role-name> element value must link to a <security-role> element through the <role-link> element. The typical use of isCallerInRole is to perform a security check that cannot be defined by using the role-based <method-permissions> elements.
Example 1.1, “ejb-jar.xml descriptor fragment” describes the the use of <security-role-ref> in an
ejb-jar.xml file.
Example 1.1. ejb-jar.xml descriptor fragment
Note
This fragment is an example only. In deployments, the elements in this section must contain role names and links relevant to the EJB deployment.
Example 1.2. web.xml descriptor fragment