8.4. Configuring Publishing to an LDAP Directory
The general process to configure publishing involves setting up a publisher to publish the certificates or CRLs to the specific location. There can be a single publisher or multiple publishers, depending on how many locations will be used. The locations can be split by certificates and CRLs or finer definitions, such as certificate type. Rules determine which type to publish and to what location by being associated with the publisher.
Configuring LDAP publishing is similar to other publishing procedures, with additional steps to configure the directory:
- Configure the Directory Server to which certificates will be published. Certain attributes have to be added to entries and bind identities and authentication methods have to be configured.
- Configure a publisher for each type of object published: CA certificates, cross-pair certificates, CRLs, and user certificates. The publisher declares in which attribute to store the object. The attributes set by default are the X.500 standard attributes for storing each object type. This attribute can be changed in the publisher, but generally, it is not necessary to change the LDAP publishers.
- Set up mappers to enable an entry's DN to be derived from the certificate's subject name. This generally does not need set for CA certificates, CRLs, and user certificates. There can be more than one mapper set for a type of certificate. This can be useful, for example, to publish certificates for two sets of users from different divisions of a company who are located in different parts of the directory tree. A mapper is created for each of the groups to specify a different branch of the tree.For details about setting up mappers, see Section 8.4.3, “Creating Mappers”.
- Create rules to connect publishers to mappers, as described in Section 8.5, “Creating Rules”.
- Enable publishing, as described in Section 8.6, “Enabling Publishing”.
8.4.1. Configuring the LDAP Directory
Copy linkLink copied to clipboard!
Before certificates and CRLs can be published, the Directory Server must be configured to work with the publishing system. This means that user entries must have attributes that allow them to receive certificate information, and entries must be created to represent the CRLs.
- Set up the entry for the CA. For the Certificate Manager to publish its CA certificate and CRL, the directory must include an entry for the CA.
Note
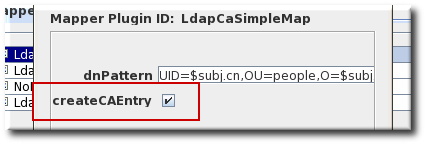
When LDAP publishing is configured, the Certificate Manager automatically creates or converts an entry for the CA in the directory. This option is set in both the CA and CRL mapper instances and enabled by default. If the directory restricts the Certificate Manager from creating entries in the directory, turn off this option in those mapper instances, and add an entry for the CA manually in the directory.When adding the CA's entry to the directory, select the entry type based on the DN of the CA:- If the CA's DN begins with the
cncomponent, create a newpersonentry for the CA. Selecting a different type of entry may not allow thecncomponent to be specified. - If the CA's DN begins with the
oucomponent, create a neworganizationalunitentry for the CA.
The entry does not have to be in thepkiCAorcertificationAuthorityobject class. The Certificate Manager will convert this entry to thepkiCAorcertificationAuthorityobject class automatically by publishing its CA's signing certificate.Note
ThepkiCAobject class is defined in RFC 4523, while thecertificationAuthorityobject class is defined in the (obsolete) RFC 2256. Either object class is acceptable, depending on the schema definitions used by the Directory Server. In some situations, both object classes can be used for the same CA entry.For more information on creating directory entries, see the Red Hat Directory Server documentation. - Add the correct schema elements to the CA and user directory entries.For a Certificate Manager to publish certificates and CRLs to a directory, it must be configured with specific attributes and object classes.
Expand Object Type Schema Reason End-entity certificate userCertificate;binary (attribute) This is the attribute to which the Certificate Manager publishes the certificate.This is a multi-valued attribute, and each value is a DER-encoded binary X.509 certificate. The LDAP object class namedinetOrgPersonallows this attribute. ThestrongAuthenticationUserobject class allows this attribute and can be combined with any other object class to allow certificates to be published to directory entries with other object classes. The Certificate Manager does not automatically add this object class to the schema table of the corresponding Directory Server.If the directory object that it finds does not allow theuserCertificate;binaryattribute, adding or removing the certificate fails.CA certificate caCertificate;binary (attribute) This is the attribute to which the Certificate Manager publishes the certificate.The Certificate Manager publishes its own CA certificate to its own LDAP directory entry when the server starts. The entry corresponds to the Certificate Manager's issuer name.This is a required attribute of thepkiCAorcertificationAuthorityobject class. The Certificate Manager adds this object class to the directory entry for the CA if it can find the CA's directory entry.CRL certificateRevocationList;binary (attribute) This is the attribute to which the Certificate Manager publishes the CRL.The Certificate Manager publishes the CRL to its own LDAP directory entry. The entry corresponds to the Certificate Manager's issuer name.This is an attribute of thepkiCAorcertificationAuthorityobject class. The value of the attribute is the DER-encoded binary X.509 CRL. The CA's entry must already contain thepkiCAorcertificationAuthorityobject class for the CRL to be published to the entry.Delta CRL deltaRevocationList;binary (attribute) This is the attribute to which the Certificate Manager publishes the delta CRL. The Certificate Manager publishes the delta CRL to its own LDAP directory entry, separate from the full CRL. The delta CRL entry corresponds to the Certificate Manager's issuer name.This attribute belongs to thedeltaCRLorcertificationAuthority-V2object class. The value of the attribute is the DER-encoded binary X.509 delta CRL. - Set up a bind DN for the Certificate Manager to use to access the Directory Server.The Certificate Manager user must have read-write permissions to the directory to publish certificates and CRLs to the directory so that the Certificate Manager can modify the user entries with certificate-related information and the CA entry with CA's certificate and CRL related information.The bind DN entry can be either of the following:
- An existing DN that has write access, such as the Directory Manager.
- A new user which is granted write access. The entry can be identified by the Certificate Manager's DN, such as
cn=testCA, ou=Research Dept, o=Example Corporation, st=California, c=US.Note
Carefully consider what privileges are given to this user. This user can be restricted in what it can write to the directory by creating ACLs for the account. For instructions on giving write access to the Certificate Manager's entry, see the Directory Server documentation.
- Set the directory authentication method for how the Certificate Manager authenticates to Directory Server. There are three options: basic authentication (simple username and password); SSL without client authentication (simple username and password); and SSL with client authentication (certificate-based).See the Red Hat Directory Server documentation for instructions on setting up these methods of communication with the server.
8.4.2. Configuring LDAP Publishers
Copy linkLink copied to clipboard!
The Certificate Manager creates, configures, and enables a set of publishers that are associated with LDAP publishing. The default publishers (for CA certificates, user certificates, CRLs, and cross-pair certificates) already conform to the X.500 standard attributes for storing certificates and CRLs and do not need to be changed.
| Publisher | Description |
|---|---|
| LdapCaCertPublisher | Publishes CA certificates to the LDAP directory. |
| LdapCrlPublisher | Publishes CRLs to the LDAP directory. |
| LdapDeltaCrlPublisher | Publishes delta CRLs to the LDAP directory. |
| LdapUserCertPublisher | Publishes all types of end-entity certificates to the LDAP directory. |
| LdapCrossCertPairPublisher | Publishes cross-signed certificates to the LDAP directory. |
8.4.3. Creating Mappers
Copy linkLink copied to clipboard!
Mappers are only used with LDAP publishing. Mappers define a relationship between a certificate's subject name and the DN of the directory entry to which the certificate is published. The Certificate Manager needs to derive the DN of the entry from the certificate or the certificate request so it can determine which entry to use. The mapper defines the relationship between the DN for the user entry and the subject name of the certificate or other input information so that the exact DN of the entry can be determined and found in the directory.
When it is configured, the Certificate Manager automatically creates a set of mappers defining the most common relationships. The default mappers are listed in Table 8.2, “Default Mappers”.
| Mapper | Description |
|---|---|
| LdapUserCertMap | Locates the correct attribute of user entries in the directory in order to publish user certificates. |
| LdapCrlMap | Locates the correct attribute of the CA's entry in the directory in order to publish the CRL. |
| LdapCaCertMap | Locates the correct attribute of the CA's entry in the directory in order to publish the CA certificate. |
To use the default mappers, configure each of the macros by specifying the DN pattern and whether to create the CA entry in the directory. To use other mappers, create and configure an instance of the mapper. For more information, see Section C.2, “Mapper Plug-in Modules ”.
- Log into the Certificate Manager Console.
pkiconsole https://server.example.com:8443/ca
pkiconsole https://server.example.com:8443/caCopy to Clipboard Copied! Toggle word wrap Toggle overflow - In the Configuration tab, select Certificate Manager from the navigation tree on the left. Select Publishing, and then Mappers.The Mappers Management tab, which lists configured mappers, opens on the right.
- To create a new mapper instance, click . The Select Mapper Plugin Implementation window opens, which lists registered mapper modules. Select a module, and edit it. For complete information about these modules, see Section C.2, “Mapper Plug-in Modules ”.
- Edit the mapper instance, and click .See Section C.2, “Mapper Plug-in Modules ” for detailed information about each mapper.
8.4.4. Completing Configuration: Rules and Enabling
Copy linkLink copied to clipboard!
After configuring the mappers for LDAP publishing, configure the rules for the published certificates and CRLs, as described in Section 8.5, “Creating Rules”.
Once the configuration is complete, enable publishing, as described in Section 8.6, “Enabling Publishing”.