Chapter 6. Ports required for communication between IdM and AD
To enable communication between your Active Directory (AD) and Identity Management (IdM) environments, open the following ports on the firewalls of your AD Domain Controllers and IdM servers.
| Service | Port | Protocol |
|---|---|---|
| Endpoint resolution portmapper | 135 | TCP |
| NetBIOS-DGM | 138 | TCP and UDP |
| NetBIOS-SSN | 139 | TCP and UDP |
| Microsoft-DS | 445 | TCP and UDP |
| Dynamic RPC | 49152-65535 | TCP |
| AD Global Catalog | 3268 | TCP |
| LDAP | 389 | TCP and UDP |
The TCP port 389 is not required to be open on IdM servers for trust, but it is necessary for clients communicating with the IdM server.
The TCP port 135 is required for the DCE RPC end-point mapper to work and is used during the IdM-AD trust creation.
To open ports, you can use the following methods:
firewalldservice — you can enable the particular ports or enable the following services which includes the ports:- FreeIPA trust setup
- FreeIPA with LDAP
- Kerberos
- DNS
For details, see the
firewall-cmdman page on your system.The RHEL web console, which is a UI with firewall settings based on the
firewalldservice.
For details about firewall configuration through the web console, see Enabling services on the firewall using the web console
| Service | Port | Protocol |
|---|---|---|
| Kerberos | 88, 464 | TCP and UDP |
| LDAP | 389 | TCP |
| DNS | 53 | TCP and UDP |
| Service | Port | Protocol |
|---|---|---|
| Kerberos | 88 | UDP and TCP |
The libkrb5 library uses UDP and falls back to the TCP protocol if the data sent from the Key Distribution Center (KDC) is too large. Active Directory attaches a Privilege Attribute Certificate (PAC) to the Kerberos ticket, which increases the size and requires to use the TCP protocol. To avoid the fall-back and resending the request, SSSD uses TCP for user authentication by default. If you want to configure the size before libkrb5 uses TCP, set the udp_preference_limit in the /etc/krb5.conf file. For details, see the krb5.conf(5) man page on your system.
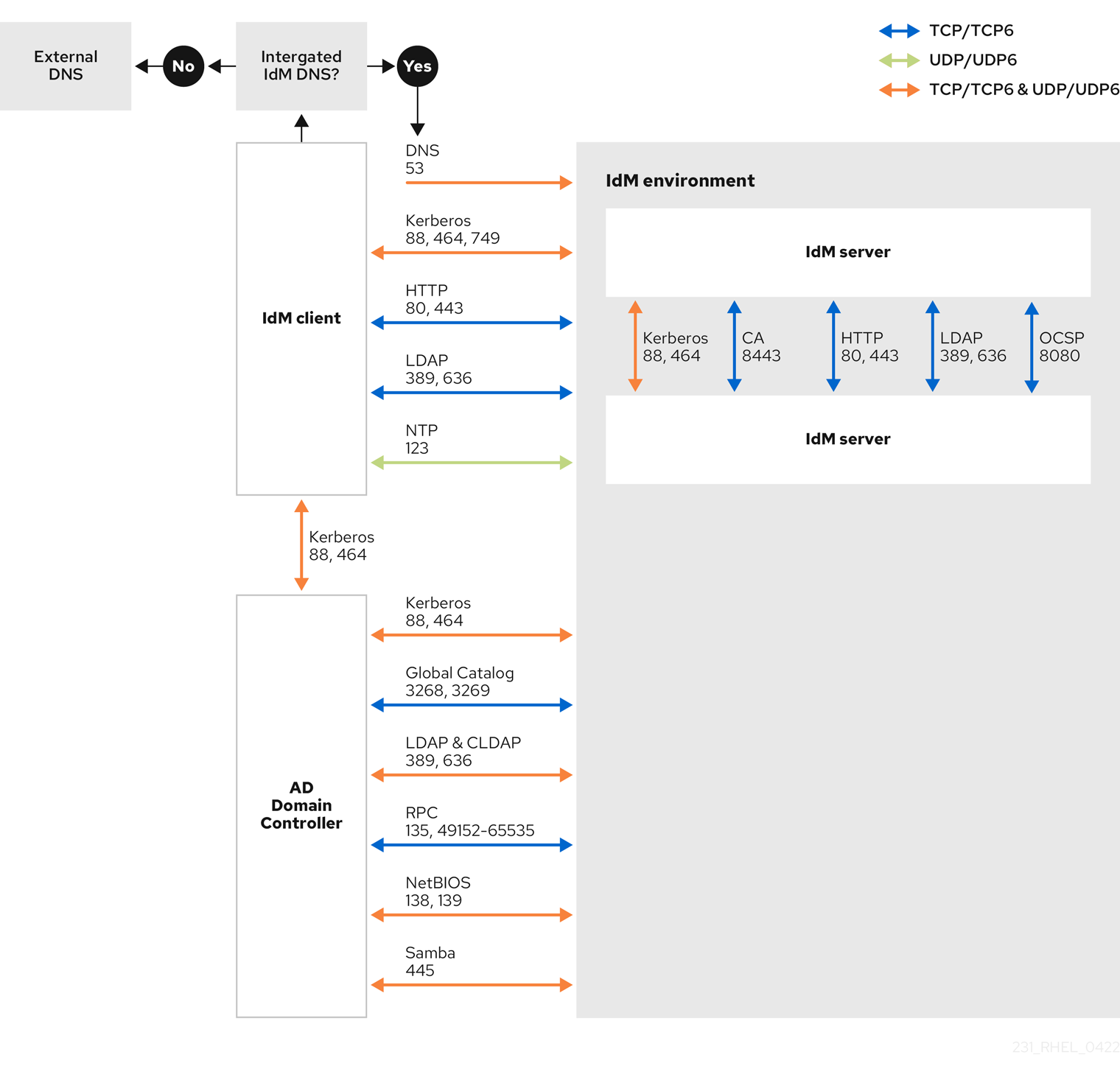
The following diagram shows communication sent by IdM clients, and received and responded to by IdM servers and AD Domain Controllers. To set the incoming and outgoing ports and protocols on your firewall, use the firewalld service, which already has definitions for FreeIPA services.
The default and recommended configuration for establishing a trust uses port 389 (LDAP). This connection is secured by SASL/GSSAPI, which provides strong, built-in encryption. For compatibility with specific Active Directory (AD) environments that are configured to reject this default method and mandate LDAPS, communication over port 636 is also possible. This is a non-standard configuration and should only be used if your AD policy makes it strictly necessary. Consult your AD administrator to confirm your environment’s requirements before configuring your firewall. If you are in this scenario, open a support case.