Ce contenu n'est pas disponible dans la langue sélectionnée.
Chapter 29. Migrating from an LDAP Directory to IdM
29.1. An Overview of LDAP to IdM Migration
29.1.1. Planning the Client Configuration
Important
29.1.1.1. Initial Client Configuration (Pre-Migration)
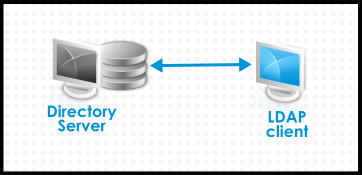
Figure 29.1. Basic LDAP Directory and Client Configuration
/etc/passwd or /etc/shadow. (In real life, the infrastructure may be more complex if a client uses LDAP for identity lookups and Kerberos for authentication or other configurations.)
29.1.1.2. Recommended Configuration for Red Hat Enterprise Linux Clients
pam_sss and nss_sss, respectively) which allow SSSD to be integrated very closely with Identity Management and leverage the full authentication and identity features in Identity Management. SSSD has a number of useful features, like caching identity information so that users can log in even if the connection is lost to the central server; these are described in the Red Hat Enterprise Linux Deployment Guide.
pam_ldap and nss_ldap), SSSD establishes relationships between identity and authentication information by defining domains. A domain in SSSD defines four backend functions: authentication, identity lookups, access, and password changes. The SSSD domain is then configured to use a provider to supply the information for any one (or all) of those four functions. An identity provider is always required in the domain configuration. The other three providers are optional; if an authentication, access, or password provider is not defined, then the identity provider is used for that function.
Note

Figure 29.2. Clients and SSSD with an IdM Backend
ipa-client-install script automatically configured SSSD to use IdM for all four of its backend services, so Red Hat Enterprise Linux clients are set up with the recommended configuration by default.
Note
ipa-client. Older versions of Red Hat Enterprise Linux can be configured as described in Section 29.1.1.3, “Alternative Supported Configuration”.
Note
ipa-client. Older versions of Red Hat Enterprise Linux can be configured as described in Section 29.1.1.3, “Alternative Supported Configuration”.
29.1.1.3. Alternative Supported Configuration
nss_ldap) and to IdM as if it were a regular Kerberos KDC (using pam_krb5).
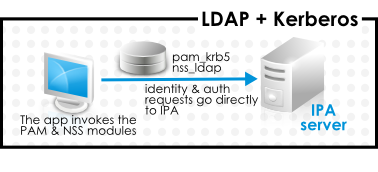
Figure 29.3. Clients and IdM with LDAP and Kerberos
nss_ldap and pam_krb5 to connect to the IdM server. For some maintenance situations and IT structures, a scenario that fits the lowest common denominator may be required, using LDAP for both identity and authentication (nss_ldap and pam_ldap). However, it is generally best practice to use the most secure configuration possible for a client (meaning SSSD and Kerberos or LDAP and Kerberos).
29.1.2. Planning Password Migration
Important
29.1.2.1. Method 1: Using Temporary Passwords and Requiring a Change
29.1.2.2. Method 2: Using the Migration Web Page
https://ipaserver.example.com/ipa/migration29.1.2.3. Method 3: Using SSSD (Recommended)
- A user tries to log into a machine with SSSD.
- SSSD attempts to perform Kerberos authentication against the IdM server.
- Even though the user exists in the system, the authentication will fail with the error key type is not supported because the Kerberos hashes do not yet exist.
- SSSD then performs a plaintext LDAP bind over a secure connection.
- IdM intercepts this bind request. If the user has a Kerberos principal but no Kerberos hashes, then the IdM identity provider generates the hashes and stores them in the user entry.
- If authentication is successful, SSSD disconnects from IdM and tries Kerberos authentication again. This time, the request succeeds because the hash exists in the entry.
29.1.2.4. Migrating Cleartext LDAP Passwords
Note
29.1.2.5. Automatically Resetting Passwords That Do Not Meet Requirements
kinit into the IdM domain.
[jsmith@server ~]$ kinit
Password for jsmith@EXAMPLE.COM:
Password expired. You must change it now.
Enter new password:
Enter it again:29.1.3. Migration Considerations and Requirements
29.1.3.1. LDAP Servers Supported for Migration
ipa migrate-ds, to perform the migration. This script has certain expectations about the structure of the LDAP directory and LDAP entries in order to work. Migration is supported only for LDAPv3-compliant directory services, which include several common directories:
- SunONE Directory Server
- Apache Directory Server
- OpenLDAP
Note
Note
29.1.3.2. Migration Environment Requirements
- A single LDAP directory domain is being migrated to one IdM realm. No consolidation is involved.
- User passwords are stored as a hash in the LDAP directory that the IdM Directory Server can support.
- The LDAP directory instance is both the identity store and the authentication method. Client machines are configured to use
pam_ldapornss_ldapto connect to the LDAP server. - Entries use only standard LDAP schema. Custom attributes will not be migrated to Identity Management.
29.1.3.3. Migration Tools
ipa migrate-ds, to drive the migration process so that LDAP directory data are properly formatted and imported cleanly into the IdM server.
29.1.3.4. Migration Sequence
- Deploy SSSD.
- Reconfigure clients to connect to the current LDAP server and then fail over to IdM.
- Install the IdM server.
- Migrate the user data using the IdM
ipa migrate-dsscript. This exports the data from the LDAP directory, formats for the IdM schema, and then imports it into IdM. - Take the LDAP server offline and allow clients to fail over to Identity Management transparently.
- Install the IdM server.
- Migrate the user data using the IdM
ipa migrate-dsscript. This exports the data from the LDAP directory, formats it for the IdM schema, and then imports it into IdM. - Optional. Deploy SSSD.
- Reconfigure clients to connect to IdM. It is not possible to simply replace the LDAP server. The IdM directory tree — and therefore user entry DNs — is different than the previous directory tree.While it is required that clients be reconfigured, clients do not need to be reconfigured immediately. Updated clients can point to the IdM server while other clients point to the old LDAP directory, allowing a reasonable testing and transition phase after the data are migrated.
Note
Do not run both an LDAP directory service and the IdM server for very long in parallel. This introduces the risk of user data being inconsistent between the two services.