Ce contenu n'est pas disponible dans la langue sélectionnée.
Chapter 7. Building container images
Building container images involves creating a blueprint for a containerized application. Blueprints rely on base images from other public repositories that define how the application should be installed and configured.
Red Hat Quay supports the ability to build Docker and Podman container images. This functionality is valuable for developers and organizations who rely on container and container orchestration.
7.1. Build contexts
When building an image with Docker or Podman, a directory is specified to become the build context. This is true for both manual Builds and Build triggers, because the Build that is created by Red Hat Quay is not different than running docker build or podman build on your local machine.
Red Hat Quay Build contexts are always specified in the subdirectory from the Build setup, and fallback to the root of the Build source if a directory is not specified.
When a build is triggered, Red Hat Quay Build workers clone the Git repository to the worker machine, and then enter the Build context before conducting a Build.
For Builds based on .tar archives, Build workers extract the archive and enter the Build context. For example:
Extracted Build archive
Imagine that the Extracted Build archive is the directory structure got a Github repository called example. If no subdirectory is specified in the Build trigger setup, or when manually starting the Build, the Build operates in the example directory.
If a subdirectory is specified in the Build trigger setup, for example, subdir, only the Dockerfile within it is visible to the Build. This means that you cannot use the ADD command in the Dockerfile to add file, because it is outside of the Build context.
Unlike Docker Hub, the Dockerfile is part of the Build context on Red Hat Quay. As a result, it must not appear in the .dockerignore file.
7.2. Tag naming for Build triggers
Custom tags are available for use in Red Hat Quay.
One option is to include any string of characters assigned as a tag for each built image. Alternatively, you can use the following tag templates on the Configure Tagging section of the build trigger to tag images with information from each commit:

- ${commit}: Full SHA of the issued commit
- ${parsed_ref.branch}: Branch information (if available)
- ${parsed_ref.tag}: Tag information (if available)
- ${parsed_ref.remote}: The remote name
- ${commit_info.date}: Date when the commit was issued
- ${commit_info.author.username}: Username of the author of the commit
- ${commit_info.short_sha}: First 7 characters of the commit SHA
- ${committer.properties.username}: Username of the committer
This list is not complete, but does contain the most useful options for tagging purposes. You can find the complete tag template schema on this page.
For more information, see Set up custom tag templates in build triggers for Red Hat Quay and Quay.io
7.3. Skipping a source control-triggered build
To specify that a commit should be ignored by the Red Hat Quay build system, add the text [skip build] or [build skip] anywhere in your commit message.
7.4. Viewing and managing builds
Repository Builds can be viewed and managed on the Red Hat Quay UI.
Procedure
- Navigate to a Red Hat Quay repository using the UI.
- In the navigation pane, select Builds.
7.5. Creating a new Build
Red Hat Quay can create new Builds so long as FEATURE_BUILD_SUPPORT is set to to true in their config.yaml file.
Prerequisites
- You have navigated to the Builds page of your repository.
-
FEATURE_BUILD_SUPPORTis set to totruein yourconfig.yamlfile.
Procedure
- On the Builds page, click Start New Build.
- When prompted, click Upload Dockerfile to upload a Dockerfile or an archive that contains a Dockerfile at the root directory.
Click Start Build.
Note- Currently, users cannot specify the Docker build context when manually starting a build.
- Currently, BitBucket is unsupported on the Red Hat Quay v2 UI.
- You are redirected to the Build, which can be viewed in real-time. Wait for the Dockerfile Build to be completed and pushed.
- Optional. you can click Download Logs to download the logs, or Copy Logs to copy the logs.
Click the back button to return to the Repository Builds page, where you can view the Build History.

7.6. Build triggers
Build triggers invoke builds whenever the triggered condition is met, for example, a source control push, creating a webhook call, and so on.
7.6.1. Creating a Build trigger
Use the following procedure to create a Build trigger using a custom Git repository.
The following procedure assumes that you have not included Github credentials in your config.yaml file.
Prerequisites
- You have navigated to the Builds page of your repository.
Procedure
- On the Builds page, click Create Build Trigger.
- Select the desired platform, for example, Github, BitBucket, Gitlab, or use a custom Git repository. For this example, we are using a custom Git repository from Github.
-
Enter a custom Git repository name, for example,
git@github.com:<username>/<repo>.git. Then, click Next. When prompted, configure the tagging options by selecting one of, or both of, the following options:
- Tag manifest with the branch or tag name. When selecting this option, the built manifest the name of the branch or tag for the git commit are tagged.
Add
latesttag if on default branch. When selecting this option, the built manifest with latest if the build occurred on the default branch for the repository are tagged.Optionally, you can add a custom tagging template. There are multiple tag templates that you can enter here, including using short SHA IDs, timestamps, author names, committer, and branch names from the commit as tags. For more information, see "Tag naming for Build triggers".
After you have configured tagging, click Next.
- When prompted, select the location of the Dockerfile to be built when the trigger is invoked. If the Dockerfile is located at the root of the git repository and named Dockerfile, enter /Dockerfile as the Dockerfile path. Then, click Next.
-
When prompted, select the context for the Docker build. If the Dockerfile is located at the root of the Git repository, enter
/as the build context directory. Then, click Next. - Optional. Choose an optional robot account. This allows you to pull a private base image during the build process. If you know that a private base image is not used, you can skip this step.
- Click Next. Check for any verification warnings. If necessary, fix the issues before clicking Finish.
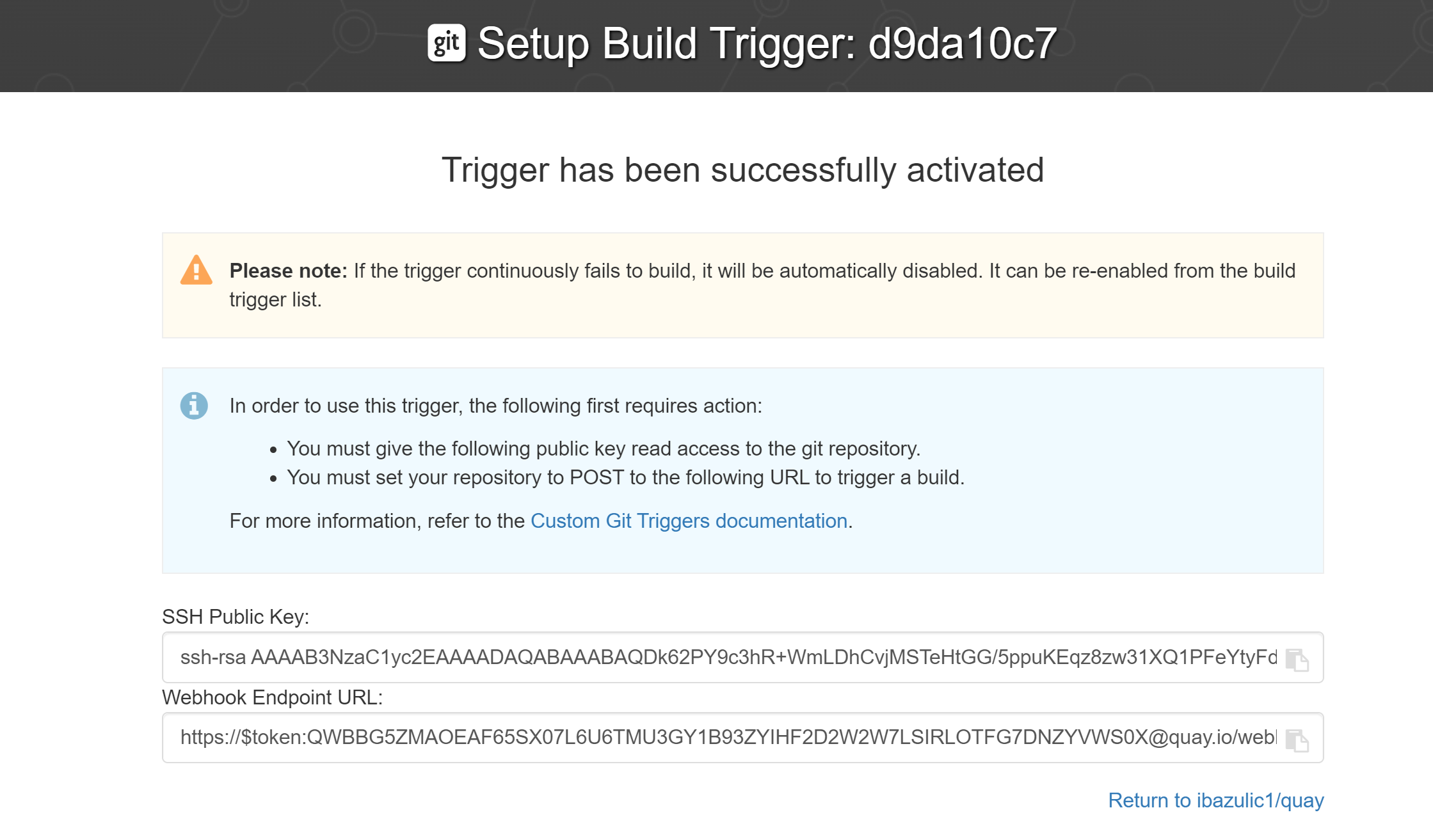
You are alerted that the trigger has been successfully activated. Note that using this trigger requires the following actions:
- You must give the following public key read access to the git repository.
You must set your repository to
POSTto the following URL to trigger a build.Save the SSH Public Key, then click Return to <organization_name>/<repository_name>. You are redirected to the Builds page of your repository.
On the Builds page, you now have a Build trigger. For example:

7.6.2. Manually triggering a Build
Builds can be triggered manually by using the following procedure.
Procedure
- On the Builds page, Start new build.
- When prompted, select Invoke Build Trigger.
Click Run Trigger Now to manually start the process.
After the build starts, you can see the Build ID on the Repository Builds page.
7.7. Setting up a custom Git trigger
A custom Git trigger is a generic way for any Git server to act as a Build trigger. It relies solely on SSH keys and webhook endpoints. Everything else is left for the user to implement.
7.7.1. Creating a trigger
Creating a custom Git trigger is similar to the creation of any other trigger, with the exception of the following:
- Red Hat Quay cannot automatically detect the proper Robot Account to use with the trigger. This must be done manually during the creation process.
- There are extra steps after the creation of the trigger that must be done. These steps are detailed in the following sections.
7.7.2. Custom trigger creation setup
When creating a custom Git trigger, two additional steps are required:
- You must provide read access to the SSH public key that is generated when creating the trigger.
- You must setup a webhook that POSTs to the Red Hat Quay endpoint to trigger the build.
The key and the URL are available by selecting View Credentials from the Settings, or gear icon.
View and modify tags from your repository
7.7.2.1. SSH public key access
Depending on the Git server configuration, there are multiple ways to install the SSH public key that Red Hat Quay generates for a custom Git trigger.
For example, Git documentation describes a small server setup in which adding the key to $HOME/.ssh/authorize_keys would provide access for Builders to clone the repository. For any git repository management software that is not officially supported, there is usually a location to input the key often labeled as Deploy Keys.
7.7.2.2. Webhook
To automatically trigger a build, one must POST a .json payload to the webhook URL using the following format.
This can be accomplished in various ways depending on the server setup, but for most cases can be done with a post-receive Git Hook.
This request requires a Content-Type header containing application/json in order to be valid.
Example webhook