Dieser Inhalt ist in der von Ihnen ausgewählten Sprache nicht verfügbar.
Chapter 10. Managing file system permissions
File system permissions control the ability of user and group accounts to read, modify, and execute the contents of the files and to enter directories. Set permissions carefully to protect your data against unauthorized access.
10.1. Managing file permissions
Every file or directory has three levels of ownership:
- User owner (u).
- Group owner (g).
- Others (o).
Each level of ownership can be assigned the following permissions:
- Read (r).
- Write (w).
- Execute (x).
Note that the execute permission for a file allows you to execute that file. The execute permission for a directory allows you to access the contents of the directory, but not execute it.
When a new file or directory is created, the default set of permissions are automatically assigned to it. The default permissions for a file or directory are based on two factors:
- Base permission.
- The user file-creation mode mask (umask).
10.1.1. Base file permissions
Whenever a new file or directory is created, a base permission is automatically assigned to it. Base permissions for a file or directory can be expressed in symbolic or octal values.
| Permission | Symbolic value | Octal value |
| No permission | --- | 0 |
| Execute | --x | 1 |
| Write | -w- | 2 |
| Write and execute | -wx | 3 |
| Read | r-- | 4 |
| Read and execute | r-x | 5 |
| Read and write | rw- | 6 |
| Read, write, execute | rwx | 7 |
The base permission for a directory is 777 (drwxrwxrwx), which grants everyone the permissions to read, write, and execute. This means that the directory owner, the group, and others can list the contents of the directory, create, delete, and edit items within the directory, and descend into it.
Note that individual files within a directory can have their own permission that might prevent you from editing them, despite having unrestricted access to the directory.
The base permission for a file is 666 (-rw-rw-rw-), which grants everyone the permissions to read and write. This means that the file owner, the group, and others can read and edit the file.
Example 10.1. Permissions for a file
If a file has the following permissions:
$ ls -l
-rwxrw----. 1 sysadmins sysadmins 2 Mar 2 08:43 file-
-indicates it is a file. -
rwxindicates that the file owner has permissions to read, write, and execute the file. -
rw-indicates that the group has permissions to read and write, but not execute the file. -
---indicates that other users have no permission to read, write, or execute the file. -
.indicates that the SELinux security context is set for the file.
Example 10.2. Permissions for a directory
If a directory has the following permissions:
$ ls -dl directory
drwxr-----. 1 sysadmins sysadmins 2 Mar 2 08:43 directory-
dindicates it is a directory. rwxindicates that the directory owner has the permissions to read, write, and access the contents of the directory.As a directory owner, you can list the items (files, subdirectories) within the directory, access the content of those items, and modify them.
-
r-xindicates that the group has permissions to read the content of the directory, but not write - create new entries or delete files. Thexpermission means that you can also access the directory using thecdcommand. ---indicates that other users have no permission to read, write, or access the contents of the directory.As someone who is not a user owner, or as a group, you cannot list the items within the directory, access information about those items, or modify them.
-
.indicates that the SELinux security context is set for the directory.
The base permission that is automatically assigned to a file or directory is not the default permission the file or directory ends up with. When you create a file or directory, the base permission is altered by the umask. The combination of the base permission and the umask creates the default permission for files and directories.
10.1.2. User file-creation mode mask
The user file-creation mode mask (umask) is variable that controls how file permissions are set for newly created files and directories. The umask automatically removes permissions from the base permission value to increase the overall security of a Linux system. The umask can be expressed in symbolic or octal values.
| Permission | Symbolic value | Octal value |
| Read, write, and execute | rwx | 0 |
| Read and write | rw- | 1 |
| Read and execute | r-x | 2 |
| Read | r-- | 3 |
| Write and execute | -wx | 4 |
| Write | -w- | 5 |
| Execute | --x | 6 |
| No permissions | --- | 7 |
The default umask for a standard user is 0002. The default umask for a root user is 0022.
The first digit of the umask represents special permissions (sticky bit, ). The last three digits of the umask represent the permissions that are removed from the user owner (u), group owner (g), and others (o) respectively.
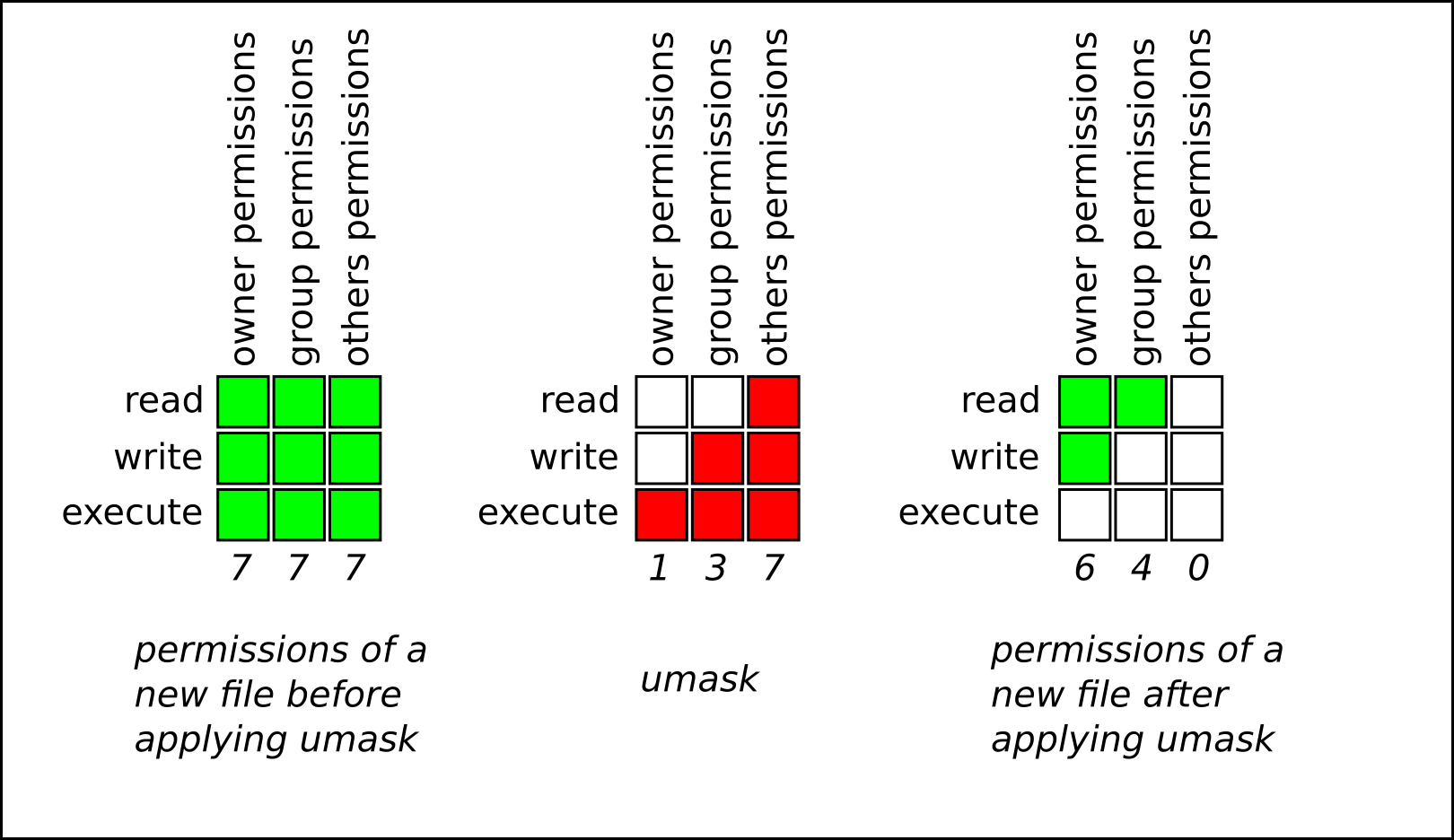
Example 10.3. Applying the umask when creating a file
The following example illustrates how the umask with an octal value of 0137 is applied to the file with the base permission of 777, to create the file with the default permission of 640.
10.1.3. Default file permissions
The default permissions are set automatically for all newly created files and directories. The value of the default permissions is determined by applying the umask to the base permission.
Example 10.4. Default permissions for a directory created by a standard user
When a standard user creates a new directory, the umask is set to 002 (rwxrwxr-x), and the base permissions for a directory are set to 777 (rwxrwxrwx). This brings the default permissions to 775 (drwxrwxr-x).
| Symbolic value | Octal value | |
| Base permission | rwxrwxrwx | 777 |
| Umask | rwxrwxr-x | 002 |
| Default permission | rwxrwxr-x | 775 |
This means that the directory owner and the group can list the contents of the directory, create, delete, and edit items within the directory, and descend into it. Other users can only list the contents of the directory and descend into it.
Example 10.5. Default permissions for a file created by a standard user
When a standard user creates a new file, the umask is set to 002 (rwxrwxr-x), and the base permissions for a file are set to 666 (rw-rw-rw-). This brings the default permissions to 664 (-rw-rw-r--).
| Symbolic value | Octal value | |
| Base permission | rw-rw-rw- | 666 |
| Umask | rwxrwxr-x | 002 |
| Default permission | rw-rw-r-- | 664 |
This means that the file owner and the group can read and edit the file, while other users can only read the file.
Example 10.6. Default permissions for a directory created by the root user
When a root user creates a new directory, the umask is set to 022 (rwxr-xr-x), and the base permissions for a directory are set to 777 (rwxrwxrwx). This brings the default permissions to 755 (rwxr-xr-x).
| Symbolic value | Octal value | |
| Base permission | rwxrwxrwx | 777 |
| Umask | rwxr-xr-x | 022 |
| Default permission | rwxr-xr-x | 755 |
This means that the directory owner can list the contents of the directory, create, delete, and edit items within the directory, and descend into it. The group and others can only list the contents of the directory and descend into it.
Example 10.7. Default permissions for a file created by the root user
When a root user creates a new file, the umask is set to 022 (rwxr-xr-x), and the base permissions for a file are set to 666 (rw-rw-rw-). This brings the default permissions to 644 (-rw-r—r--).
| Symbolic value | Octal value | |
| Base permission | rw-rw-rw- | 666 |
| Umask | rwxr-xr-x | 022 |
| Default permission | rw-r—r-- | 644 |
This means that the file owner can read and edit the file, while the group and others can only read the file.
For security reasons, regular files cannot have execute permissions by default, even if the umask is set to 000 (rwxrwxrwx). However, directories can be created with execute permissions.
10.1.4. Changing file permissions using symbolic values
You can use the chmod utility with symbolic values (a combination of letters and signs) to change file permissions for a file or directory.
You can assign the following permissions:
- Read (r)
- Write (w)
- Execute (x)
Permissions can be assigned to the following levels of ownership:
- User owner (u)
- Group owner (g)
- Other (o)
- All (a)
To add or remove permissions you can use the following signs:
-
+to add the permissions on top of the existing permissions -
-to remove the permissions from the existing permission -
=to remove the existing permissions and explicitly define the new ones
Procedure
To change the permissions for a file or directory, use:
$ chmod <level><operation><permission> file-nameReplace
<level>with the level of ownership you want to set the permissions for. Replace<operation>with one of the signs. Replace<permission>with the permissions you want to assign. Replace file-name with the name of the file or directory. For example, to grant everyone the permissions to read, write, and execute (rwx)my-script.sh, use thechmod a=rwx my-script.shcommand.See Base file permissions for more details.
Verification
To see the permissions for a particular file, use:
$ ls -l file-nameReplace file-name with the name of the file.
To see the permissions for a particular directory, use:
$ ls -dl directory-nameReplace directory-name with the name of the directory.
To see the permissions for all the files within a particular directory, use:
$ ls -l directory-nameReplace directory-name with the name of the directory.
Example 10.8. Changing permissions for files and directories
To change file permissions for
my-file.txtfrom-rw-rw-r--to-rw------, use:Display the current permissions for
my-file.txt:$ ls -l my-file.txt -rw-rw-r--. 1 username username 0 Feb 24 17:56 my-file.txtRemove the permissions to read, write, and execute (
rwx) the file from group owner (g) and others (o):$ chmod go= my-file.txtNote that any permission that is not specified after the equals sign (
=) is automatically prohibited.Verify that the permissions for
my-file.txtwere set correctly:$ ls -l my-file.txt -rw-------. 1 username username 0 Feb 24 17:56 my-file.txt
To change file permissions for
my-directoryfromdrwxrwx---todrwxrwxr-x, use:Display the current permissions for
my-directory:$ ls -dl my-directory drwxrwx---. 2 username username 4096 Feb 24 18:12 my-directoryAdd the read and execute (
r-x) access for all users (a):$ chmod o+rx my-directoryVerify that the permissions for
my-directoryand its content were set correctly:$ ls -dl my-directory drwxrwxr-x. 2 username username 4096 Feb 24 18:12 my-directory
10.1.5. Changing file permissions using octal values
You can use the chmod utility with octal values (numbers) to change file permissions for a file or directory.
Procedure
To change the file permissions for an existing file or directory, use:
$ chmod octal_value file-nameReplace file-name with the name of the file or directory. Replace octal_value with an octal value. See Base file permissions for more details.
10.2. Managing the Access Control List
Each file and directory can only have one user owner and one group owner at a time. If you want to grant a user permissions to access specific files or directories that belong to a different user or group while keeping other files and directories private, you can utilize Linux Access Control Lists (ACLs).
10.2.1. Setting the Access Control List
You can use the setfacl utility to set the ACL for a file or directory.
Prerequisites
-
You have the
rootaccess.
Procedure
To display the current ACL for a particular file or directory, run:
$ getfacl file-nameReplace file-name with the name of the file or directory.
- To set the ACL for a file or directory, use:
# setfacl -m u:username:symbolic_value file-name
Replace username with the name of the user, symbolic_value with a symbolic value, and file-name with the name of the file or directory. For more information see the setfacl man page on your system.
Example 10.9. Modifying permissions for a group project
The following example describes how to modify permissions for the group-project file owned by the root user that belongs to the root group so that this file is:
- Not executable by anyone.
-
The user
andrewhas therw-permissions. -
The user
susanhas the---permissions. -
Other users have the
r--permissions.
Procedure
# setfacl -m u:andrew:rw- group-project
# setfacl -m u:susan:--- group-projectVerification
To verify that the user
andrewhas therw-permission, the usersusanhas the---permission, and other users have ther--permission, use:$ getfacl group-projectThe output returns:
# file: group-project # owner: root # group: root user:andrew:rw- user:susan:--- group::r-- mask::rw- other::r--
10.2.2. Interaction between ACLs and standard file permissions
When you configure an Access Control List (ACL) on a file, the behavior of standard file permission tools, such as ls and chmod, changes to accommodate the ACL entries. Understanding this mapping is critical to avoid misinterpreting file permissions or unintentionally restricting access.
10.2.2.1. The ACL mask and the ls command
When a file has an ACL defined, the ls -l command changes its output in two specific ways:
-
The plus sign (): A `` character appears at the end of the permission string (for example,
-rw-rwxr--+). This indicates that the file has extended security information (an ACL) associated with it. The group permissions mapping: The meaning of the middle triplet of permission bits (traditionally the "group" permissions) depends on whether an ACL mask entry exists.
- If an ACL mask entry exists, the group bits correspond to the mask permissions.
- If no mask entry exists, the group bits correspond to the permissions of the owning group.
The ACL mask defines the maximum effective permissions for:
- The owning group.
- All named user entries.
- All named group entries.
This means that when you view a file with ls -l, the "group" column shows the upper limit of permissions granted to any user or group other than the file owner and "other".
10.2.2.2. The behavior of chmod on ACL-enabled files
The behavior of the chmod command mirrors the mapping used by ls -l:
-
If no ACL mask exists:
chmodmodifies the permissions of the owning group, as it does on standard files. -
If an ACL mask exists:
chmodmodifies the mask permissions, not the owning group permissions.
This has a cascading effect:
-
If you lower the permissions of the mask using
chmod, you restrict the effective permissions of all named users and groups that rely on that mask. -
Even if a specific user is granted
rwxin the ACL, if the mask is set tor--viachmod, that user effectively only has read access.
Do not assume that chmod g-w only affects the owning group of the file. On a file with an ACL, this command tightens the mask, potentially blocking write access for specific users you previously authorized with setfacl.
The effect of the ACL mask on permissions
The following example demonstrates how adding an ACL changes the ls -l output and how chmod affects the mask.
Initial state: A file named
file1exists with standard permissions.$ ls -l file1-rw-rw-r--. 1 root root 0 Jul 3 10:00 file1Adding a user: You grant user
johnfull access (rwx) to the file.$ setfacl -m u:john:rwx file1NoteBy default,
setfaclautomatically creates or updates the mask entry to be the union of all permissions affected by the mask. In this case, the mask is set torwxto accommodate the new permissions granted tojohn. You can prevent this automatic recalculation by using the-n(no mask) option.Observing the change: The
ls -loutput now shows a+sign, and the group permission column showsrwx. Thisrwxreflects the new mask (created automatically to accommodatejohn), not the owning group’s permissions.$ ls -l file1-rw-rwxr--+ 1 root root 0 Jul 3 10:05 file1Verifying with
getfacl: Thegetfaclcommand confirms thatjohnhasrwx, the owning group still hasrw-, and the mask isrwx.$ getfacl --omit-header file1user::rw- user:john:rwx group::rw- mask::rwx other::r--Modifying permissions with chmod: You decide to remove write access for the group using standard
chmod.$ chmod g-w file1The Result: This action updates the mask. Consequently,
john’s effective permissions are reduced, even though his specific ACL entry remains `rwx.$ ls -l file1-rw-r-xr--+ 1 root root 0 Jul 3 10:10 file1$ *getfacl --omit-header file1*user::rw- user:john:rwx #effective:r-x group::rw- #effective:r– mask::r-x other::r--Note that the
#effectivecomments indicate the actual permissions enforced by the system.
10.3. Managing the umask
You can use the umask utility to display, set, or change the current or default value of the umask.
10.3.1. Displaying the current value of the umask
You can use the umask utility to display the current value of the umask in symbolic or octal mode.
Procedure
To display the current value of the umask in symbolic mode, use:
$ umask -STo display the current value of the umask in the octal mode, use:
$ umaskNoteWhen displaying the umask in octal mode, you may notice it displayed as a four digit number (
0002or0022). The first digit of the umask represents a special bit (sticky bit, SGID bit, or SUID bit). If the first digit is set to0, the special bit is not set.
10.3.2. Setting the umask using symbolic values
You can use the umask utility with symbolic values (a combination letters and signs) to set the umask for the current shell session
You can assign the following permissions:
- Read (r)
- Write (w)
- Execute (x)
Permissions can be assigned to the following levels of ownership:
- User owner (u)
- Group owner (g)
- Other (o)
- All (a)
To add or remove permissions you can use the following signs:
-
+to add the permissions on top of the existing permissions -
-to remove the permissions from the existing permission =to remove the existing permissions and explicitly define the new onesNoteAny permission that is not specified after the equals sign (
=) is automatically prohibited.
Procedure
To set the umask for the current shell session, use:
$ umask -S <level><operation><permission>Replace
<level>with the level of ownership you want to set the umask for. Replace<operation>with one of the signs. Replace<permission>with the permissions you want to assign. For example, to set the umask tou=rwx,g=rwx,o=rwx, useumask -S a=rwx.See User file-creation mode for more details.
NoteThe umask is only valid for the current shell session.
10.3.3. Setting the umask using octal values
You can use the umask utility with octal values (numbers) to set the umask for the current shell session.
Procedure
To set the umask for the current shell session, use:
$ umask octal_valueReplace octal_value with an octal value. See User file-creation mode mask for more details.
NoteThe umask is only valid for the current shell session.
10.3.4. Changing the default umask for the non-login shell
You can change the default bash umask for standard users by modifying the /etc/bashrc file.
Prerequisites
-
You have the
rootaccess.
Procedure
-
Open the
/etc/bashrcfile in the editor. Modify the following sections to set a new default
bashumask:if [ $UID -gt 199 ] && [ “id -gn" = “id -un” ]; then umask 002 else umask 022 fiChanging the
UID -gt 199, will apply the new umask for allIDs >= 199and impact services and security.
Replace the default octal value of the umask (002) with another octal value. See User file-creation mode mask for more details.
- Save the changes and exit the editor.
10.3.5. Changing the default umask for the login shell
You can change the default bash umask for the root user by modifying the /etc/profile file.
Prerequisites
-
rootaccess
Procedure
-
As
root, open the/etc/profilefile in the editor. Modify the following sections to set a new default
bashumask:if [ $UID -gt 199 ] && [ “/usr/bin/id -gn” = “/usr/bin/id -un” ]; then umask 002 else umask 022 fiReplace the default octal value of the umask (
022) with another octal value. See User file-creation mode mask for more details.- Save the changes and exit the editor.
10.3.6. Changing the default umask for a specific user
You can change the default umask for a specific user by modifying the .bashrc for that user.
Procedure
Append the line that specifies the octal value of the umask into the
.bashrcfile for the particular user.$ echo 'umask octal_value' >> /home/username/.bashrcReplace octal_value with an octal value and replace username with the name of the user. See User file-creation mode mask for more details.
10.3.7. Setting default permissions for newly created home directories
You can change the permission modes for home directories of newly created users by modifying the /etc/login.defs file.
Procedure
-
As
root, open the/etc/login.defsfile in the editor. Modify the following section to set a new default HOME_MODE:
# HOME_MODE is used by useradd(8) and newusers(8) to set the mode for new # home directories. # If HOME_MODE is not set, the value of UMASK is used to create the mode. HOME_MODE 0700Replace the default octal value (
0700) with another octal value. The selected mode will be used to create the permissions for the home directory.- If HOME_MODE is set, save the changes and exit the editor.
If HOME_MODE is not set, modify the UMASK to set the mode for the newly created home directories:
# Default initial "umask" value used by login(1) on non-PAM enabled systems. # Default "umask" value for pam_umask(8) on PAM enabled systems. # UMASK is also used by useradd(8) and newusers(8) to set the mode for new # home directories if HOME_MODE is not set. # 022 is the default value, but 027, or even 077, could be considered # for increased privacy. There is no One True Answer here: each sysadmin # must make up their mind. UMASK 022Replace the default octal value (
022) with another octal value. See User file-creation mode mask for more details.- Save the changes and exit the editor.