4.4.3. Limiting Root Access
Rather than completely deny access to the root user, the administrator may want to allow access only via setuid programs, such as
su or sudo.
4.4.3.1. The su Command
Copy linkLink copied to clipboard!
Upon typing the
su command, the user is prompted for the root password and, after authentication, is given a root shell prompt.
Once logged in via the
su command, the user is the root user and has absolute administrative access to the system. In addition, once a user has become root, it is possible for them to use the su command to change to any other user on the system without being prompted for a password.
Because this program is so powerful, administrators within an organization may wish to limit who has access to the command.
One of the simplest ways to do this is to add users to the special administrative group called wheel. To do this, type the following command as root:
usermod -G wheel <username>
In the previous command, replace <username> with the username you want to add to the
wheel group.
To use the User Manager for this purpose, go to the (on the Panel) => => or type the command
system-config-users at a shell prompt. Select the Users tab, select the user from the user list, and click from the button menu (or choose => from the pull-down menu).
Then select the Groups tab and click on the wheel group, as shown in Figure 4.2, “Groups Pane”.
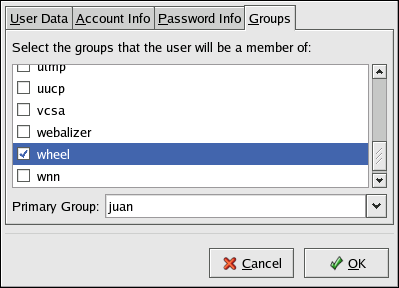
Figure 4.2. Groups Pane
Next, open the PAM configuration file for
su (/etc/pam.d/su) in a text editor and remove the comment # from the following line:
auth required /lib/security/$ISA/pam_wheel.so use_uid
Doing this permits only members of the administrative group
wheel to use the program.
Note
The root user is part of the
wheel group by default.