Chapter 7. Managing users and groups
Preventing unauthorized access to files and processes requires accurate user and group management. If you do not manage accounts centrally or you require a user account or group only on a specific system, you can create them locally on a host.
7.1. Introduction to managing user and group accounts
The control of users and groups is a core element of Red Hat Enterprise Linux (RHEL) system administration. Each RHEL user has distinct login credentials and can be assigned to various groups to customize their system privileges.
7.1.1. Introduction to users and groups
A user who creates a file is the owner of that file and the group owner of that file. The file is assigned separate read, write, and execute permissions for the owner, the group, and those outside that group. The file owner can be changed only by the root user. Access permissions to the file can be changed by both the root user and the file owner. A regular user can change group ownership of a file they own to a group of which they are a member of.
Each user is associated with a unique numerical identification number called user ID (UID). Each group is associated with a group ID (GID). Users within a group share the same permissions to read, write, and execute files owned by that group.
7.1.2. Configuring reserved user and group IDs
By default, RHEL reserves user and group IDs below 1000 for system users and groups. You can find the reserved user and group IDs in the setup package. The UID’s and GID’s of users and groups created before you changed the UID_MIN and GID_MIN values do not change. The reserved user and group IDs are documented in the:
/usr/share/doc/setup/uidgidTo assign IDs to the new users and groups starting at 5000, as the reserved range can increase in the future.
Modify the UID_MIN and GID_MIN parameters in the /etc/login.defs file to define a start ID other than the defaults (1000).
Do not raise IDs reserved by the system above 1000 by changing SYS_UID_MAX to avoid conflict with systems that retain the 1000 limit.
Procedure
-
Open the
/etc/login.defsfile in an editor. Set the
UID_MINvariable, for example:# Min/max values for automatic uid selection in useradd # UID_MIN 5000Set the
GID_MINvariable, for example:# Min/max values for automatic gid selection in groupadd # GID_MIN 5000The dynamically assigned UIDs and GIDs for the regular users now start at 5000.
7.1.3. User private groups
RHEL uses the user private group (UPG) system configuration, which makes Linux groups easier to manage. A user private group is created whenever a new user is added to the system. The user private group has the same name as the user for which it was created and that user is the only member of the user private group.
UPGs simplify the collaboration on a project between multiple users. In addition, UPG system configuration makes it safe to set default permissions for a newly created file or directory, as it allows both the user, and the group this user is a part of, to make modifications to the file or directory.
A list of all local groups is stored in the /etc/group configuration file.
7.2. Getting started with managing user accounts
Red Hat Enterprise Linux is a multi-user operating system, which enables multiple users on different computers to access a single system installed on one machine. Every user operates under its own account, and managing user accounts thus represents a core element of Red Hat Enterprise Linux system administration.
The following are the different types of user accounts:
Normal user accounts:
Normal accounts are created for users of a particular system. Such accounts can be added, removed, and modified during normal system administration.
System user accounts:
System user accounts represent a particular applications identifier on a system. Such accounts are generally added or manipulated only at software installation time, and they are not modified later.
WarningSystem accounts are presumed to be available locally on a system. If these accounts are configured and provided remotely, such as in the instance of an LDAP configuration, system breakage and service start failures can occur.
For system accounts, user IDs below 1000 are reserved. For normal accounts, you can use IDs starting at 1000. To define the min/max IDs for users and groups, system users and system groups, see the
/etc/login.defsfile.Group:
A group is an entity which ties together multiple user accounts for a common purpose, such as granting access to particular files.
7.2.1. Managing accounts and groups using command line tools
Use the following basic command-line tools to manage user accounts and groups.
Procedure
Create a new user account:
# useradd example.userAssign a new password to a user account belonging to example.user:
# passwd example.userAdd a user to a group:
# usermod -a -G example.group example.user
7.3. Managing users from the command line
You can manage users and groups using the command-line interface (CLI). This enables you to add, remove, and modify users and user groups in Red Hat Enterprise Linux environment.
7.3.1. Adding a new user from the command line
You can use the useradd utility to add a new user.
Prerequisites
-
You have
Rootaccess
Procedure
Add a new user, use:
# useradd <options> <username>Replace options with the command-line options for the
useraddcommand, and replace username with the name of the user.Example 7.1. Adding a new user
To add the user
sarahwith user ID5000, use:# useradd -u 5000 sarah
Verification
To verify the new user is added, use the
idutility.# id sarahThe command returns:
uid=5000(sarah) gid=5000(sarah) groups=5000(sarah)
7.3.2. Adding a new group from the command line
You can use the groupadd utility to add a new group.
Prerequisites
-
You have
Rootaccess
Procedure
To add a new group, use:
# groupadd options group-nameReplace options with the command-line options for the
groupaddcommand, and replace group-name with the name of the group.Example 7.2. Adding a new group
To add the group
sysadminswith group ID5000, use:# groupadd -g 5000 sysadmins
Verification
To verify the new group is added, use the
tailutility.# getent group sysadminThe command returns:
sysadmins:x:5000:
7.3.3. Adding a user to a supplementary group from the command line
You can add a user to a supplementary group to manage permissions or enable access to certain files or devices.
Prerequisites
-
You have
rootaccess
Procedure
To add a group to the supplementary groups of the user, use:
# usermod --append -G <group_name> <username>
Verification
To verify the new groups is added to the supplementary groups of the user
sysadmin, use:# groups <username>
7.3.4. Creating a group directory
Under the UPG system configuration, you can apply the set-group identification permission (setgid bit) to a directory. The setgid bit makes managing group projects that share a directory simpler. When you apply the setgid bit to a directory, files created within that directory are automatically assigned to a group that owns the directory. Any user that has the permission to write and execute within this group can now create, modify, and delete files in the directory.
Prerequisites
-
You have
Rootaccess
Procedure
Create a directory:
# mkdir <directory-name>Create a group:
# groupadd <group-name>Add users to the group:
# usermod --append -G <group_name> <username>Associate the user and group ownership of the directory with the group-name group:
# chgrp <group_name> <directory>Set the write permissions to allow the users to create and modify files and directories and set the
setgidbit to make this permission be applied within the directory:# chmod g+rwxs <directory>
Verification
To verify the correctness of set permissions, use:
# ls -ld <directory>The command returns:
*drwx__rws__r-x.* 2 root _group-name_ 6 Nov 25 08:45 _directory-name_
7.3.5. Removing a user on the command line
You can remove a user account by using the command line. In addition, below mentioned are the commands to remove the user account, and optionally remove the user data and metadata, such as their home directory and configuration files.
-
You have
rootaccess. - The user currently exists.
Ensure that the user is logged out:
# loginctl terminate-user user-nameTo only remove the user account, and not the user data:
# userdel user-nameTo remove the user, the data, and the metadata:
Remove the user, their home directory, their mail spool, and their SELinux user mapping:
# userdel --remove --selinux-user user-nameRemove additional user metadata:
# rm -rf /var/lib/AccountsService/users/user-nameThis directory stores information that the system needs about the user before the home directory is available. Depending on the system configuration, the home directory might not be available until the user authenticates at the login screen.
ImportantIf you do not remove this directory and you later recreate the same user, the recreated user will still use certain settings inherited from the removed user.
7.4. Managing user accounts in the web console
The RHEL web console provides a graphical interface for adding, editing, and removing system user accounts.
You can also set password expiration and terminate user sessions in the web console.
7.4.1. Adding new accounts by using the web console
You can add user accounts to the system and set administration rights to the accounts through the RHEL web console.
Prerequisites
- You have installed the RHEL 9 web console.
- You have enabled the cockpit service.
Your user account is allowed to log in to the web console.
For instructions, see Installing and enabling the web console.
Procedure
Log in to the RHEL 9 web console.
For details, see Logging in to the web console.
- Click .
- Click .
In the Full Name field, enter the full name of the user.
The web console automatically suggests a user name from the full name and fills it in the User Name field. If you do not want to use the original naming convention, which consists of the first letter of the first name and the entire surname, update the suggestion.
In the Password/Confirm fields, enter the password and retype it for verification that your password is correct.
The color bar below the fields indicates the security level of the entered password, which prevents you from creating a user with a weak password.
- Click to save the settings and close the dialog box.
- Select the newly created account.
- In the Groups drop-down menu, select the groups that you want to add to the new account.
Verification
- You can view the new account in the Accounts settings and use its credentials to connect to the system.
7.4.2. Enforcing password expiration in the web console
By default, user accounts have set passwords to never expire. You can set system passwords to expire after a defined number of days. When the password expires, the user must change its password at the next login attempt before the user can access the system.
Prerequisites
- You have installed the RHEL 9 web console.
- You have enabled the cockpit service.
Your user account is allowed to log in to the web console.
For instructions, see Installing and enabling the web console.
Procedure
- Log in to the RHEL 9 web console.
- Click .
- Select the user account for which you want to enforce password expiration.
Click on the Password line.
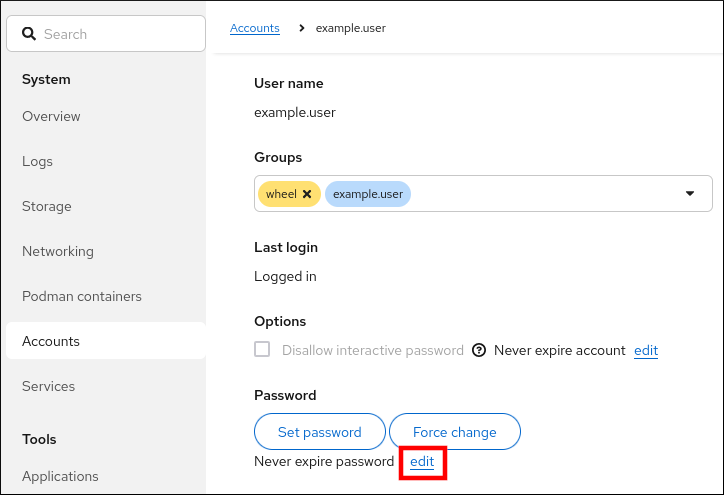
- In the Password expiration dialog box, select Require password change every … days and enter a positive whole number representing the number of days after which the password expires.
Click .
The web console immediately shows the date of the future password change request on the Password line.
7.5. Editing user groups using the command line
A user belongs to a certain set of groups that allow a logical collection of users with a similar access to files and folders. You can edit the primary and supplementary user groups from the command line to change the user’s permissions.
7.5.1. Primary and supplementary user groups
A group is an entity which ties together multiple user accounts for a common purpose, such as granting access to particular files.
On RHEL, user groups can act as primary or supplementary. Primary and supplementary groups have the following properties:
- Primary group
- Every user has just one primary group at all times.
- You can change the user’s primary group.
- Supplementary groups
- You can add an existing user to an existing supplementary group to manage users with the same security and access privileges within the group.
- Users can be members of zero, one, or multiple supplementary groups.
7.5.2. Listing the primary and supplementary groups of a user
You can list the groups of users to see which primary and supplementary groups they belong to.
Procedure
Display the names of the primary and any supplementary group of a user:
$ groups user-nameIf you do not provide a user name, the command displays the group membership for the current user. The first group is the primary group followed by the optional supplementary groups.
Example 7.3. Listing of groups for user sarah:
$ groups sarahThe output displays:
sarah : sarah wheel developerUser
sarahhas a primary groupsarahand is a member of supplementary groupswheelanddeveloper.
7.5.3. Changing the primary group of a user
You can change the primary group of an existing user to a new group.
Prerequisites
-
rootaccess - The new group must exist
Procedure
Change the primary group of a user:
# usermod -g <group-name> <user-name>NoteWhen you change a user’s primary group, the command also automatically changes the group ownership of all files in the user’s home directory to the new primary group. You must fix the group ownership of files outside of the user’s home directory manually.
Verify that you changed the primary group of the user:
$ groups <username>
7.5.4. Adding a user to a supplementary group from the command line
You can add a user to a supplementary group to manage permissions or enable access to certain files or devices.
Prerequisites
-
You have
rootaccess
Procedure
To add a group to the supplementary groups of the user, use:
# usermod --append -G <group_name> <username>
Verification
To verify the new groups is added to the supplementary groups of the user
sysadmin, use:# groups <username>
7.5.5. Removing a user from a supplementary group
You can remove an existing user from a supplementary group to limit their permissions or access to files and devices.
Prerequisites
-
You have
rootaccess
Procedure
Remove a user from a supplementary group:
# gpasswd -d <user-name> <group-name>
Verification
Verify that you removed the user sarah from the secondary group developers:
$ groups <username>
7.5.6. Changing all of the supplementary groups of a user
You can overwrite the list of supplementary groups that you want the user to remain a member of.
Prerequisites
-
You have
rootaccess. - The supplementary groups must exist.
Procedure
Overwrite a list of user’s supplementary groups:
# usermod -G <group-names> <username>To add the user to several supplementary groups at once, separate the group names using commas and no intervening spaces. For example:
wheel,developer.ImportantIf the user is currently a member of a group that you do not specify, the command removes the user from the group.
Verification
Verify that you set the list of the supplementary groups correct:
# groups <username>
7.6. Changing and resetting the root password
If the existing root password is no longer satisfactory, you can change it both as the root user and a non-root user.
7.6.1. Changing the root password as the root user
You can use the passwd command to change the root password as the root user.
Prerequisites
-
You have
Rootaccess
Procedure
To change the
rootpassword, use:# passwdYou are prompted to enter your current password before you can change it.
7.6.2. Changing or resetting the forgotten root password as a non-root user
You can use the passwd command to change or reset the forgotten root password as a non-root user.
Prerequisites
- You are able to log in as a non-root user.
-
You have permissions to execute commands as root by using
sudo.
Procedure
To change or reset the
rootpassword as a non-root user that belongs to thewheelgroup, use:$ sudo passwd rootYou are prompted to enter your current non-root password before you can change the
rootpassword.
7.6.3. Resetting the root password
If you are unable to log in as root user and have no non-root user with sudo permissions, you can reset the root password or do not belong to the administrative wheel group, you can reset the root password by booting the system into the special mode. In this mode, the boot process stops before the system hands over the control from the initramfs to the actual system.
Procedure
Reboot the system and, on the GRUB boot screen, press the key to interrupt the boot process.
The kernel boot parameters appear.
load_video set gfx_payload=keep insmod gzio linux ($root)/vmlinuz-5.14.0-70.22.1.e19_0.x86_64 root=/dev/mapper/rhel-root ro crash\ kernel=auto resume=/dev/mapper/rhel-swap rd.lvm.lv/swap rhgb quiet initrd ($root)/initramfs-5.14.0-70.22.1.e19_0.x86_64.img $tuned_initrd- Set the cursor to the end of the line that starts with linux.
-
Append
rd.breakto the end of the line that starts withlinux. Press to start the system with the changed parameters.
The
switch_rootprompt appears.Remount the file system as writable:
# mount -o remount,rw /sysrootBy default, the file system is mounted as read-only in the
/sysrootdirectory. Remounting the file system as writable allows you to change the password.Enter the
chrootenvironment:# chroot /sysrootReset the
rootpassword:# passwdFollow the instructions displayed by the command line to finalize the change of the
rootpassword.Enable the SELinux relabeling process on the next system boot:
# touch /.autorelabelExit the
chrootenvironment:# exitExit the
switch_rootprompt, to reboot the system:exit- Wait until the SELinux relabeling process is finished. Note that relabeling a large disk can take a long time. The system reboots automatically when the process is complete.
Verification
-
Log in as the
rootuser by using the new root password. Optional: Display the user name associated with the current effective user ID:
# whoami