Chapter 1. Image Service
This chapter discusses the steps you can follow to manage images and storage in Red Hat OpenStack Platform.
A virtual machine image is a file which contains a virtual disk which has a bootable operating system installed on it. Virtual machine images are supported in different formats. The following formats are available on Red Hat OpenStack Platform:
-
RAW- Unstructured disk image format. -
QCOW2- Disk format supported by QEMU emulator. This format includes QCOW2v3 (sometimes referred to as QCOW3), which requires QEMU 1.1 or higher. -
ISO- Sector-by-sector copy of the data on a disk, stored in a binary file. -
AKI- Indicates an Amazon Kernel Image. -
AMI- Indicates an Amazon Machine Image. -
ARI- Indicates an Amazon RAMDisk Image. -
VDI- Disk format supported by VirtualBox virtual machine monitor and the QEMU emulator. -
VHD- Common disk format used by virtual machine monitors from VMware, VirtualBox, and others. -
VMDK- Disk format supported by many common virtual machine monitors.
While ISO is not normally considered a virtual machine image format, since ISOs contain bootable filesystems with an installed operating system, you can treat them the same as you treat other virtual machine image files.
To download the official Red Hat Enterprise Linux cloud images, your account must have a valid Red Hat Enterprise Linux subscription:
You will be prompted to enter your Red Hat account credentials if you are not logged in to the Customer Portal.
1.1. Understanding the Image Service
The following notable OpenStack Image service (glance) features are available.
1.1.1. Image Signing and Verification
Image signing and verification protects image integrity and authenticity by enabling deployers to sign images and save the signatures and public key certificates as image properties.
By taking advantage of this feature, you can:
- Sign an image using your private key and upload the image, the signature, and a reference to your public key certificate (the verification metadata). The Image service then verifies that the signature is valid.
- Create an image in the Compute service, have the Compute service sign the image, and upload the image and its verification metadata. The Image service again verifies that the signature is valid.
- Request a signed image in the Compute service. The Image service provides the image and its verification metadata, allowing the Compute service to validate the image before booting it.
For information on image signing and verification, refer to the Validate Glance Images chapter of the Manage Secrets with OpenStack Key Manager Guide.
1.1.2. Image conversion
Image conversion converts images by calling the task API while importing an image.
As part of the import workflow, a plugin provides the image conversion. This plugin can be activated or deactivated based on the deployer configuration. Therefore, the deployer needs to specify the preferred format of images for the deployment.
Internally, the Image service receives the bits of the image in a particular format. These bits are stored in a temporary location. The plugin is then triggered to convert the image to the target format and moved to a final destination. When the task is finished, the temporary location is deleted. As a result, the format uploaded initially is not retained by the Image service.
For more information about image conversion, see Enabling image conversion.
The conversion can be triggered only when importing an image. It does not run when uploading an image. For example:
$ glance image-create-via-import \
--disk-format qcow2 \
--container-format bare \
--name NAME \
--visibility public \
--import-method web-download \
--uri http://server/image.qcow21.1.3. Image Introspection
Every image format comes with a set of metadata embedded inside the image itself. For example, a stream optimized vmdk would contain the following parameters:
$ head -20 so-disk.vmdk
# Disk DescriptorFile
version=1
CID=d5a0bce5
parentCID=ffffffff
createType="streamOptimized"
# Extent description
RDONLY 209714 SPARSE "generated-stream.vmdk"
# The Disk Data Base
#DDB
ddb.adapterType = "buslogic"
ddb.geometry.cylinders = "102"
ddb.geometry.heads = "64"
ddb.geometry.sectors = "32"
ddb.virtualHWVersion = "4"By introspecting this vmdk, you can easily know that the disk_type is streamOptimized, and the adapter_type is buslogic. These metadata parameters are useful for the consumer of the image. In Compute, the workflow to instantiate a streamOptimized disk is different from the one to instantiate a flat disk. This new feature allows metadata extraction. You can achieve image introspection by calling the task API while importing the image. An administrator can override metadata settings.
1.1.4. Interoperable Image Import
The OpenStack Image service provides two methods for importing images using the interoperable image import workflow:
-
web-download(default) for importing images from a URI and -
glance-directfor importing from a local file system.
1.1.5. Improving scalability with Image service caching
Use the glance-api caching mechanism to store copies of images on your local machine and retrieve them automatically to improve scalability. With Image service caching, the glance-api can run on multiple hosts. This means that it does not need to retrieve the same image from back-end storage multiple times. Image service caching does not affect any Image service operations.
To configure Image service caching with the Red Hat OpenStack Platform director (tripleo) heat templates, complete the following steps:
Procedure
In an environment file, set the value of the
GlanceCacheEnabledparameter totrue, which automatically sets theflavorvalue tokeystone+cachemanagementin theglance-api.confheat template:parameter_defaults: GlanceCacheEnabled: true-
Include the environment file in the
openstack overcloud deploycommand when you redeploy the overcloud. Optional: Tune the
glance_cache_prunerto an alternative frequency when you redeploy the overcloud. The following example shows a frequency of 5 minutes:parameter_defaults: ControllerExtraConfig: glance::cache::pruner::minute: '*/5'Adjust the frequency according to your needs to avoid file system full scenarios. Include the following elements when you choose an alternative frequency:
- The size of the files that you want to cache in your environment.
- The amount of available file system space.
- The frequency at which the environment caches images.
1.1.6. Image pre-caching
This feature is available in this release as a Technology Preview, and therefore is not fully supported by Red Hat. It should only be used for testing, and should not be deployed in a production environment. For more information about Technology Preview features, see Scope of Coverage Details.
1.1.6.1. Configuring the default interval for periodic image pre-caching
Because the Red Hat OpenStack Platform director can now pre-cache images as part of the glance-api service, you no longer require glance-registry to pre-cache images. The default periodic interval is 300 seconds. You can increase or decrease the default interval based on your requirements.
Procedure
Add a new interval with the
ExtraConfigparameter in an environment file on the undercloud according to your requirements:parameter_defaults: ControllerExtraConfig: glance::config::glance_api_config: DEFAULT/cache_prefetcher_interval: value: '<300>'Replace <300> with the number of seconds that you want as an interval to pre-cache images.
After you adjust the interval in the environment file in
/home/stack/templates/, log in as thestackuser and deploy the configuration:$ openstack overcloud deploy --templates \ -e /home/stack/templates/<ENV_FILE>.yamlReplace <ENV_FILE> with the name of the environment file that contains the
ExtraConfigsettings that you added.
If you passed any extra environment files when you created the overcloud, pass them again here using the -e option to avoid making undesired changes to the overcloud.
For more information about the openstack overcloud deploy command, see Deployment command in the Director Installation and Usage guide.
1.1.6.2. Using a periodic job to pre-cache an image
Prerequisite
To use a periodic job to pre-cache an image, you must use the glance-cache-manage command connected directly to the node where the glance_api service is running. Do not use a proxy, which hides the node that answers a service request. Because the undercloud might not have access to the network where the glance_api service is running, run commands on the first overcloud node, which is called controller-0 by default.
Complete the following prerequisite procedure to ensure the following actions:
- You run commands from the correct host.
- You have the necessary credentials.
You are running the
glance-cache-managecommands from inside theglance-apicontainer.Log in to the undercloud as the
stackuser and identify the provisioning IP address ofcontroller-0:$ ssh stack@undercloud-0 [stack@undercloud-0 ~]$ source ~/overcloudrc (overcloud) [stack@undercloud-0 ~]$ openstack server list -f value -c Name -c Networks | grep controller overcloud-controller-1 ctlplane=192.168.24.40 overcloud-controller-2 ctlplane=192.168.24.13 overcloud-controller-0 ctlplane=192.168.24.71 (overcloud) [stack@undercloud-0 ~]$To authenticate to the overcloud, copy the credentials that are stored in
/home/stack/overcloudrc, by default, tocontroller-0:(overcloud) [stack@undercloud-0 ~]$ scp ~/overcloudrc heat-admin@192.168.24.71:/home/heat-admin/Connect to
controller-0as theheat-adminuser:(overcloud) [stack@undercloud-0 ~]$ ssh heat-admin@192.168.24.71On
controller-0as theheat-adminuser, identify the IP address of theglance_api service. In the following example, the IP address is172.25.1.105:[heat-admin@controller-0 ~]$ sudo grep -A 10 '^listen glance_api' /var/lib/config-data/puppet-generated/haproxy/etc/haproxy/haproxy.cfg listen glance_api server controller0-0.internalapi.redhat.local 172.25.1.105:9292 check fall 5 inter 2000 rise 2 ...Because the `glance-cache-manage\` command is only available in the
glance_apicontainer, you must create a script to exec into that container where the overcloud authentication environment variables are already set. Create a script calledglance_pod.shin/home/heat-adminoncontroller-0with the following contents:sudo podman exec -ti \ -e NOVA_VERSION=$NOVA_VERSION \ -e COMPUTE_API_VERSION=$COMPUTE_API_VERSION \ -e OS_USERNAME=$OS_USERNAME \ -e OS_PROJECT_NAME=$OS_PROJECT_NAME \ -e OS_USER_DOMAIN_NAME=$OS_USER_DOMAIN_NAME \ -e OS_PROJECT_DOMAIN_NAME=$OS_PROJECT_DOMAIN_NAME \ -e OS_NO_CACHE=$OS_NO_CACHE \ -e OS_CLOUDNAME=$OS_CLOUDNAME \ -e no_proxy=$no_proxy \ -e OS_AUTH_TYPE=$OS_AUTH_TYPE \ -e OS_PASSWORD=$OS_PASSWORD \ -e OS_AUTH_URL=$OS_AUTH_URL \ -e OS_IDENTITY_API_VERSION=$OS_IDENTITY_API_VERSION \ -e OS_COMPUTE_API_VERSION=$OS_COMPUTE_API_VERSION \ -e OS_IMAGE_API_VERSION=$OS_IMAGE_API_VERSION \ -e OS_VOLUME_API_VERSION=$OS_VOLUME_API_VERSION \ -e OS_REGION_NAME=$OS_REGION_NAME \ glance_api /bin/bashSource the
overcloudrcfile and run theglance_pod.shscript to exec into theglance_apicontainer with the necessary environment variables to authenticate to the overcloud Controller node.[heat-admin@controller-0 ~]$ source overcloudrc (overcloudrc) [heat-admin@controller-0 ~]$ bash glance_pod.sh ()[glance@controller-0 /]$Use a command such as
glance image-listto verify that the container can run authenticated commands against the overcloud.()[glance@controller-0 /]$ glance image-list +--------------------------------------+----------------------------------+ | ID | Name | +--------------------------------------+----------------------------------+ | ad2f8daf-56f3-4e10-b5dc-d28d3a81f659 | cirros-0.4.0-x86_64-disk.img | +--------------------------------------+----------------------------------+ ()[glance@controller-0 /]$
Procedure
As the admin user, queue an image to cache:
()[glance@controller-0 /]$ glance-cache-manage --host=<HOST-IP> queue-image <IMAGE-ID>Replace <HOST-IP> with the IP address of the Controller node where the
glance-apicontainer is running, and replace <IMAGE-ID> with the ID of the image that you want to queue. After you queue images that you want to pre-cache, thecache_imagesperiodic job prefetches all queued images concurrently.NoteBecause the image cache is local to each node, if your Red Hat OpenStack Platform is deployed with HA (with 3, 5, or 7 Controllers) then you must specify the host address with the
--hostoption when you run theglance-cache-managecommand.Run the following command to view the images in the image cache:
()[glance@controller-0 /]$ glance-cache-manage --host=<HOST-IP> list-cachedReplace <HOST-IP> with the IP address of the host in your environment.
When you complete this procedure, remove the overcloudrc file from the Controller node.
Related information
You can use additional glance-cache-manage commands for the following purposes:
-
list-cachedto list all images that are currently cached. -
list-queuedto list all images that are currently queued for caching. -
queue-imageto queue an image for caching. -
delete-cached-imageto purge an image from the cache. -
delete-all-cached-imagesto remove all images from the cache. -
delete-queued-imageto delete an image from the cache queue. -
delete-all-queued-imagesto delete all images from the cache queue.
1.2. Manage Images
The OpenStack Image service (glance) provides discovery, registration, and delivery services for disk and server images. It provides the ability to copy or snapshot a server image, and immediately store it away. Stored images can be used as a template to get new servers up and running quickly and more consistently than installing a server operating system and individually configuring services.
1.2.1. Creating an Image
This section provides you with the steps to manually create OpenStack-compatible images in the QCOW2 format using Red Hat Enterprise Linux 7 ISO files, Red Hat Enterprise Linux 6 ISO files, or Windows ISO files.
1.2.1.1. Use a KVM Guest Image With Red Hat OpenStack Platform
You can use a ready RHEL KVM guest QCOW2 image:
These images are configured with cloud-init and must take advantage of ec2-compatible metadata services for provisioning SSH keys in order to function properly.
Ready Windows KVM guest QCOW2 images are not available.
For the KVM guest images:
-
The
rootaccount in the image is disabled, butsudoaccess is granted to a special user namedcloud-user. -
There is no
rootpassword set for this image.
The root password is locked in /etc/shadow by placing !! in the second field.
For an OpenStack instance, it is recommended that you generate an ssh keypair from the OpenStack dashboard or command line and use that key combination to perform an SSH public authentication to the instance as root.
When the instance is launched, this public key will be injected to it. You can then authenticate using the private key downloaded while creating the keypair.
If you do not want to use keypairs, you can use the admin password that has been set using the Inject an admin Password Into an Instance procedure.
If you want to create custom Red Hat Enterprise Linux or Windows images, see Create a Red Hat Enterprise Linux 7 Image, Create a Red Hat Enterprise Linux 6 Image, or Create a Windows Image.
1.2.1.2. Create Custom Red Hat Enterprise Linux or Windows Images
Prerequisites:
- Linux host machine to create an image. This can be any machine on which you can install and run the Linux packages.
-
libvirt, virt-manager (run command
dnf groupinstall -y @virtualization). This installs all packages necessary for creating a guest operating system. -
Libguestfs tools (run command
dnf install -y libguestfs-tools-c). This installs a set of tools for accessing and modifying virtual machine images. - A Red Hat Enterprise Linux 7 or 6 ISO file (see RHEL 7.2 Binary DVD or RHEL 6.8 Binary DVD) or a Windows ISO file. If you do not have a Windows ISO file, visit the Microsoft TechNet Evaluation Center and download an evaluation image.
-
Text editor, if you want to change the
kickstartfiles (RHEL only).
If you install the libguestfs-tools package on the undercloud, disable iscsid.socket to avoid port conflicts with the tripleo_iscsid service on the undercloud:
$ sudo systemctl disable --now iscsid.socket
In the following procedures, all commands with the [root@host]# prompt should be run on your host machine.
1.2.1.2.1. Create a Red Hat Enterprise Linux 7 Image
This section provides you with the steps to manually create an OpenStack-compatible image in the QCOW2 format using a Red Hat Enterprise Linux 7 ISO file.
Start the installation using
virt-installas shown below:[root@host]# qemu-img create -f qcow2 rhel7.qcow2 8G [root@host]# virt-install --virt-type kvm --name rhel7 --ram 2048 \ --cdrom /tmp/rhel-server-7.2-x86_64-dvd.iso \ --disk rhel7.qcow2,format=qcow2 \ --network=bridge:virbr0 --graphics vnc,listen=0.0.0.0 \ --noautoconsole --os-type=linux --os-variant=rhel7This launches an instance and starts the installation process.
NoteIf the instance does not launch automatically, run the
virt-viewercommand to view the console:[root@host]# virt-viewer rhel7Set up the virtual machine as follows:
-
At the initial Installer boot menu, choose the
Install Red Hat Enterprise Linux 7.X option.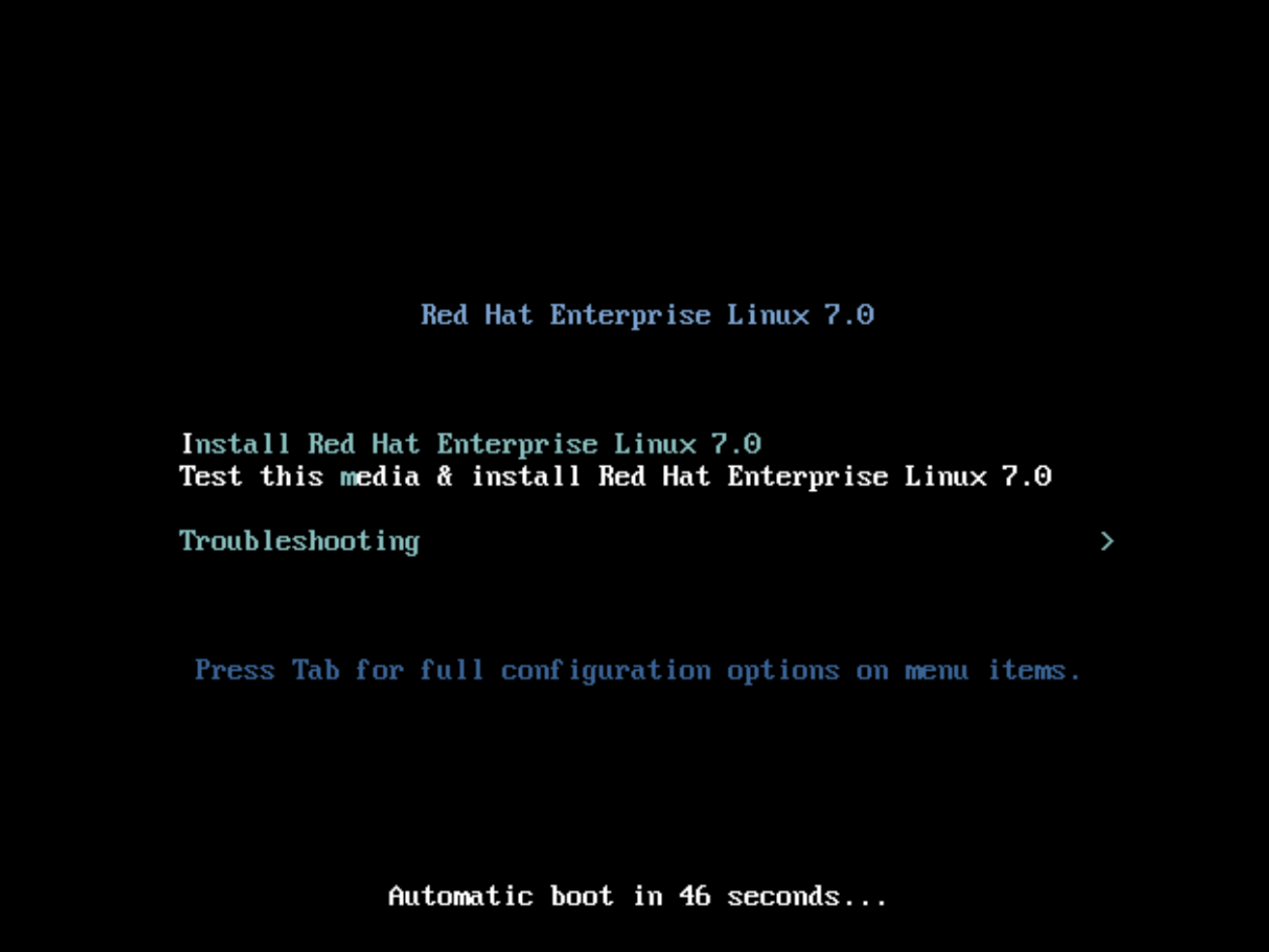
- Choose the appropriate Language and Keyboard options.
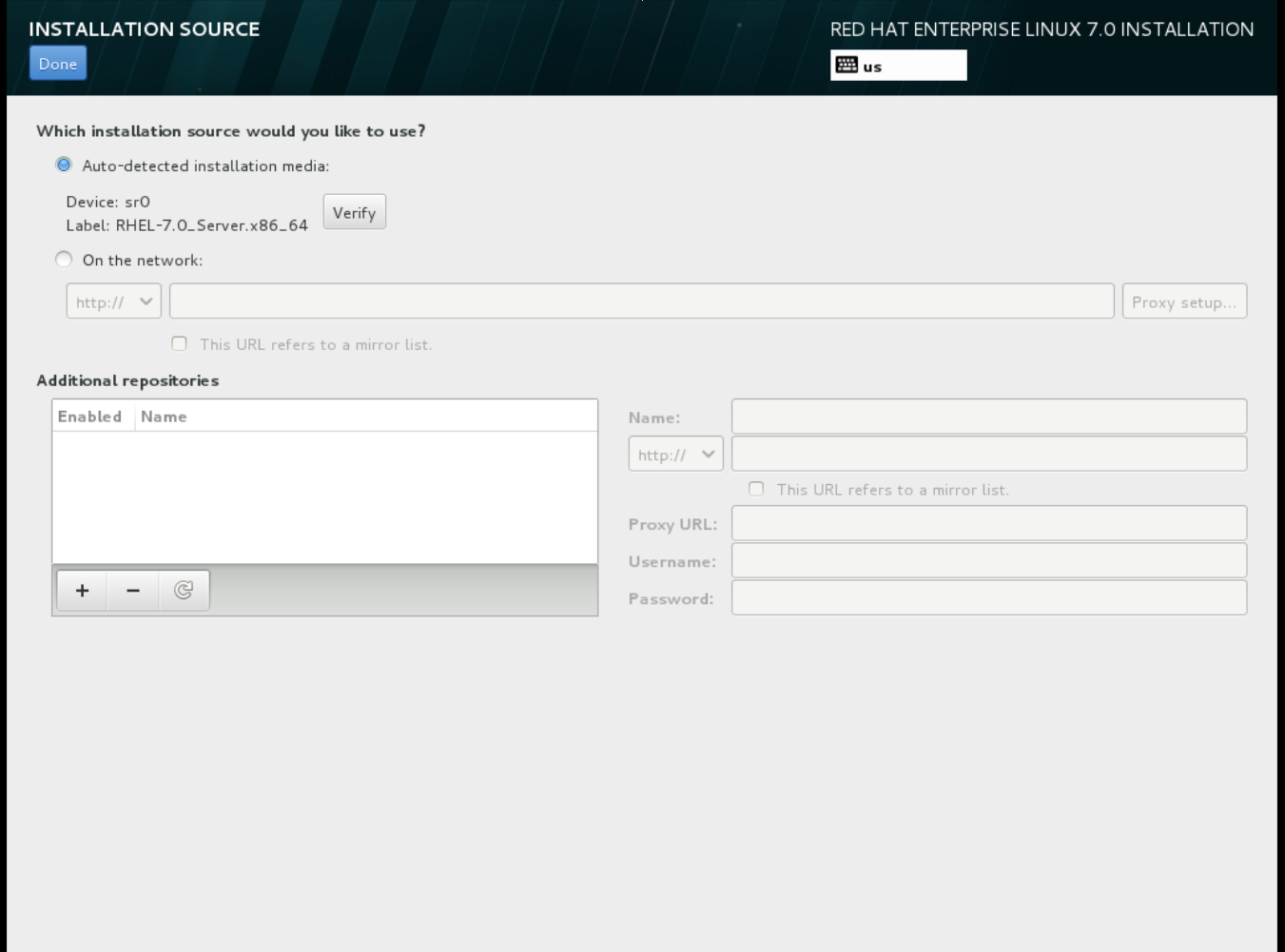
-
When prompted about which type of devices your installation uses, choose Auto-detected installation media.
-
When prompted about which type of installation destination, choose Local Standard Disks.
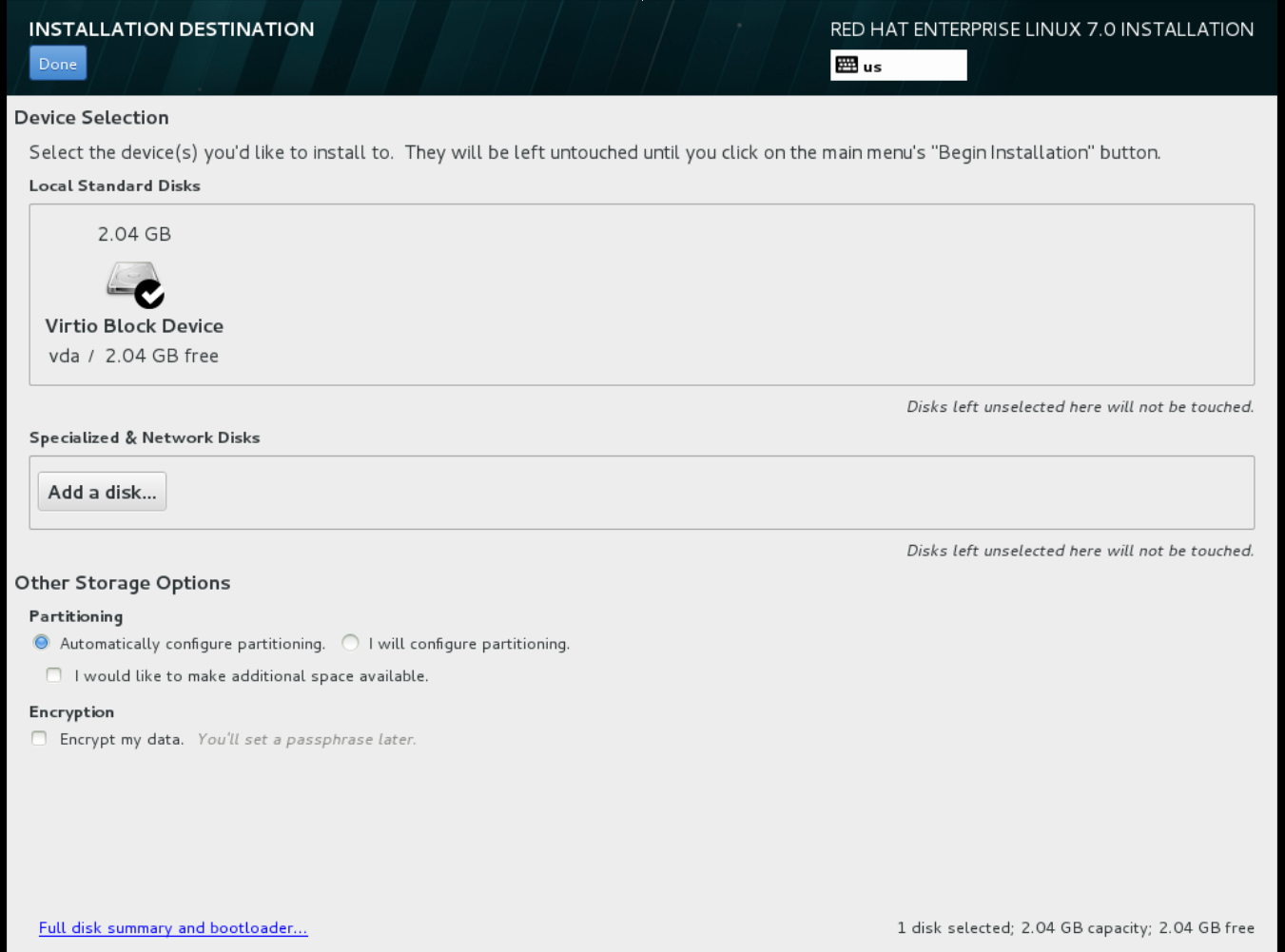 For other storage options, choose Automatically configure partitioning.
For other storage options, choose Automatically configure partitioning.
- For software selection, choose Minimal Install.
-
For network and host name, choose
eth0for network and choose ahostnamefor your device. The default host name islocalhost.localdomain. -
Choose the
rootpassword.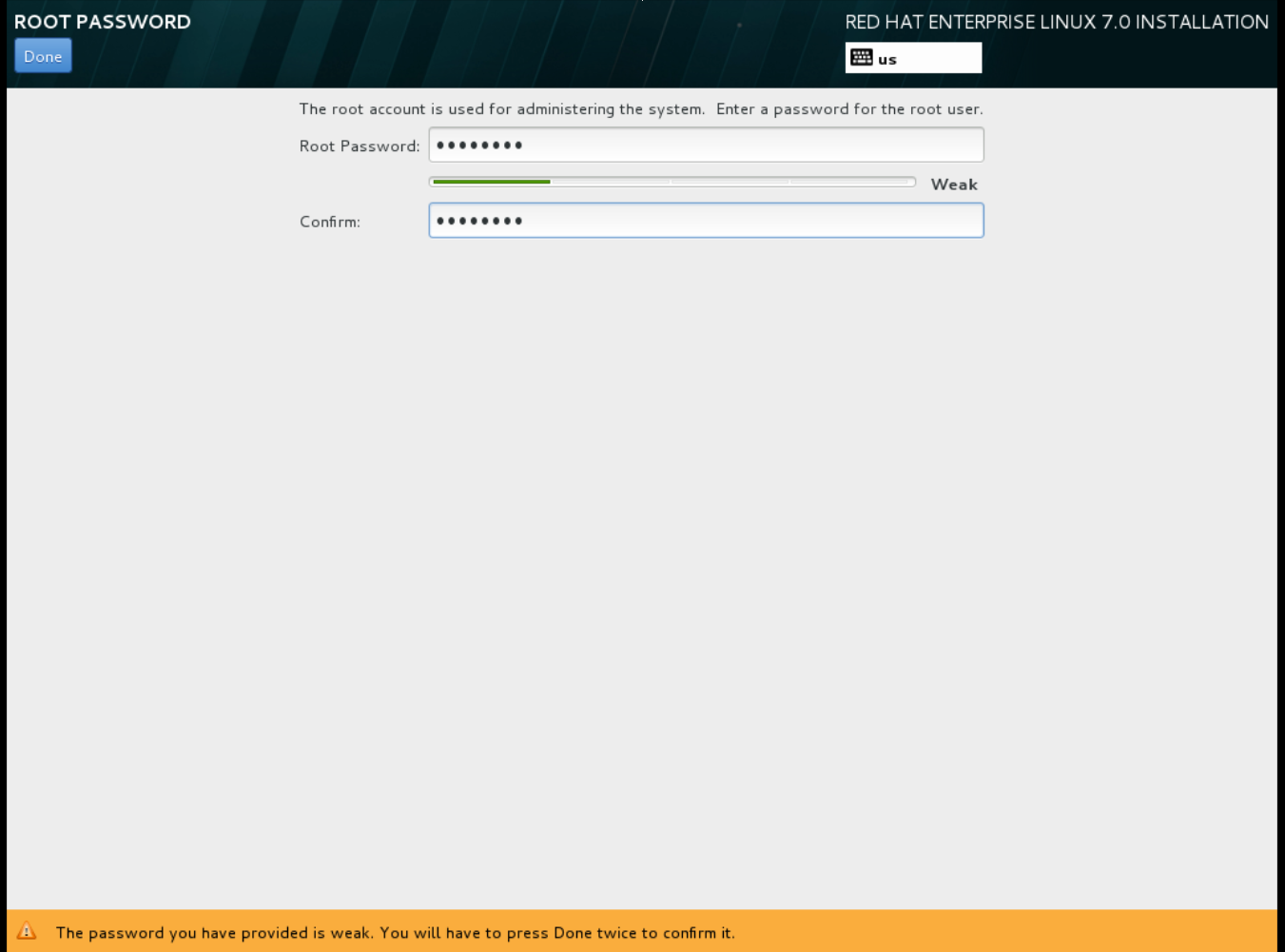 The installation process completes and the Complete! screen appears.
The installation process completes and the Complete! screen appears.
-
At the initial Installer boot menu, choose the
- After the installation is complete, reboot the instance and log in as the root user.
Update the
/etc/sysconfig/network-scripts/ifcfg-eth0file so it only contains the following values:TYPE=Ethernet DEVICE=eth0 ONBOOT=yes BOOTPROTO=dhcp NM_CONTROLLED=no- Reboot the machine.
Register the machine with the Content Delivery Network.
# sudo subscription-manager register # sudo subscription-manager attach --pool=Valid-Pool-Number-123456 # sudo subscription-manager repos --enable=rhel-7-server-rpmsUpdate the system:
# dnf -y updateInstall the
cloud-initpackages:# dnf install -y cloud-utils-growpart cloud-initEdit the
/etc/cloud/cloud.cfgconfiguration file and undercloud_init_modulesadd:- resolv-confThe
resolv-confoption automatically configures theresolv.confwhen an instance boots for the first time. This file contains information related to the instance such asnameservers,domainand other options.Add the following line to
/etc/sysconfig/networkto avoid problems accessing the EC2 metadata service:NOZEROCONF=yesTo ensure the console messages appear in the
Logtab on the dashboard and thenova console-logoutput, add the following boot option to the/etc/default/grubfile:GRUB_CMDLINE_LINUX_DEFAULT="console=tty0 console=ttyS0,115200n8"Run the
grub2-mkconfigcommand:# grub2-mkconfig -o /boot/grub2/grub.cfgThe output is as follows:
Generating grub configuration file ... Found linux image: /boot/vmlinuz-3.10.0-229.7.2.el7.x86_64 Found initrd image: /boot/initramfs-3.10.0-229.7.2.el7.x86_64.img Found linux image: /boot/vmlinuz-3.10.0-121.el7.x86_64 Found initrd image: /boot/initramfs-3.10.0-121.el7.x86_64.img Found linux image: /boot/vmlinuz-0-rescue-b82a3044fb384a3f9aeacf883474428b Found initrd image: /boot/initramfs-0-rescue-b82a3044fb384a3f9aeacf883474428b.img doneUn-register the virtual machine so that the resulting image does not contain the same subscription details for every instance cloned based on it:
# subscription-manager repos --disable=* # subscription-manager unregister # dnf clean allPower off the instance:
# poweroffReset and clean the image using the
virt-sysprepcommand so it can be used to create instances without issues:[root@host]# virt-sysprep -d rhel7Reduce image size using the
virt-sparsifycommand. This command converts any free space within the disk image back to free space within the host:[root@host]# virt-sparsify --compress /tmp/rhel7.qcow2 rhel7-cloud.qcow2This creates a new
rhel7-cloud.qcow2file in the location from where the command is run.
The rhel7-cloud.qcow2 image file is ready to be uploaded to the Image service. For more information on uploading this image to your OpenStack deployment using the dashboard, see Upload an Image.
1.2.1.2.2. Create a Red Hat Enterprise Linux 6 Image
This section provides you with the steps to manually create an OpenStack-compatible image in the QCOW2 format using a Red Hat Enterprise Linux 6 ISO file.
Start the installation using
virt-install:[root@host]# qemu-img create -f qcow2 rhel6.qcow2 4G [root@host]# virt-install --connect=qemu:///system --network=bridge:virbr0 \ --name=rhel6 --os-type linux --os-variant rhel6 \ --disk path=rhel6.qcow2,format=qcow2,size=10,cache=none \ --ram 4096 --vcpus=2 --check-cpu --accelerate \ --hvm --cdrom=rhel-server-6.8-x86_64-dvd.isoThis launches an instance and starts the installation process.
NoteIf the instance does not launch automatically, run the
virt-viewercommand to view the console:[root@host]# virt-viewer rhel6Set up the virtual machines as follows:
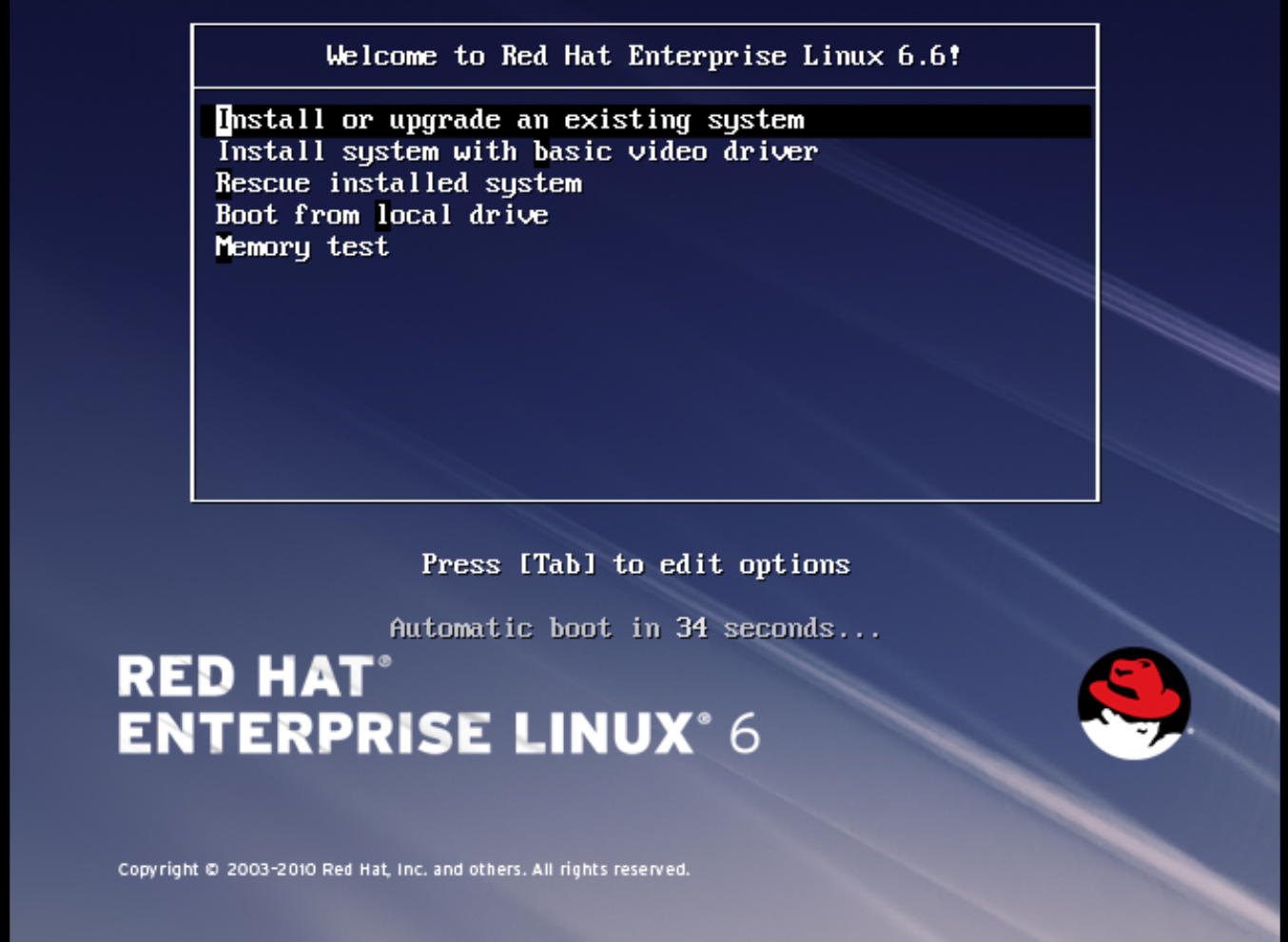
At the initial Installer boot menu, choose the Install or upgrade an existing system option.
 Step through the installation prompts. Accept the defaults.
Step through the installation prompts. Accept the defaults.
The installer checks for the disc and lets you decide whether you want to test your installation media before installation. Select OK to run the test or Skip to proceed without testing.
- Choose the appropriate Language and Keyboard options.
-
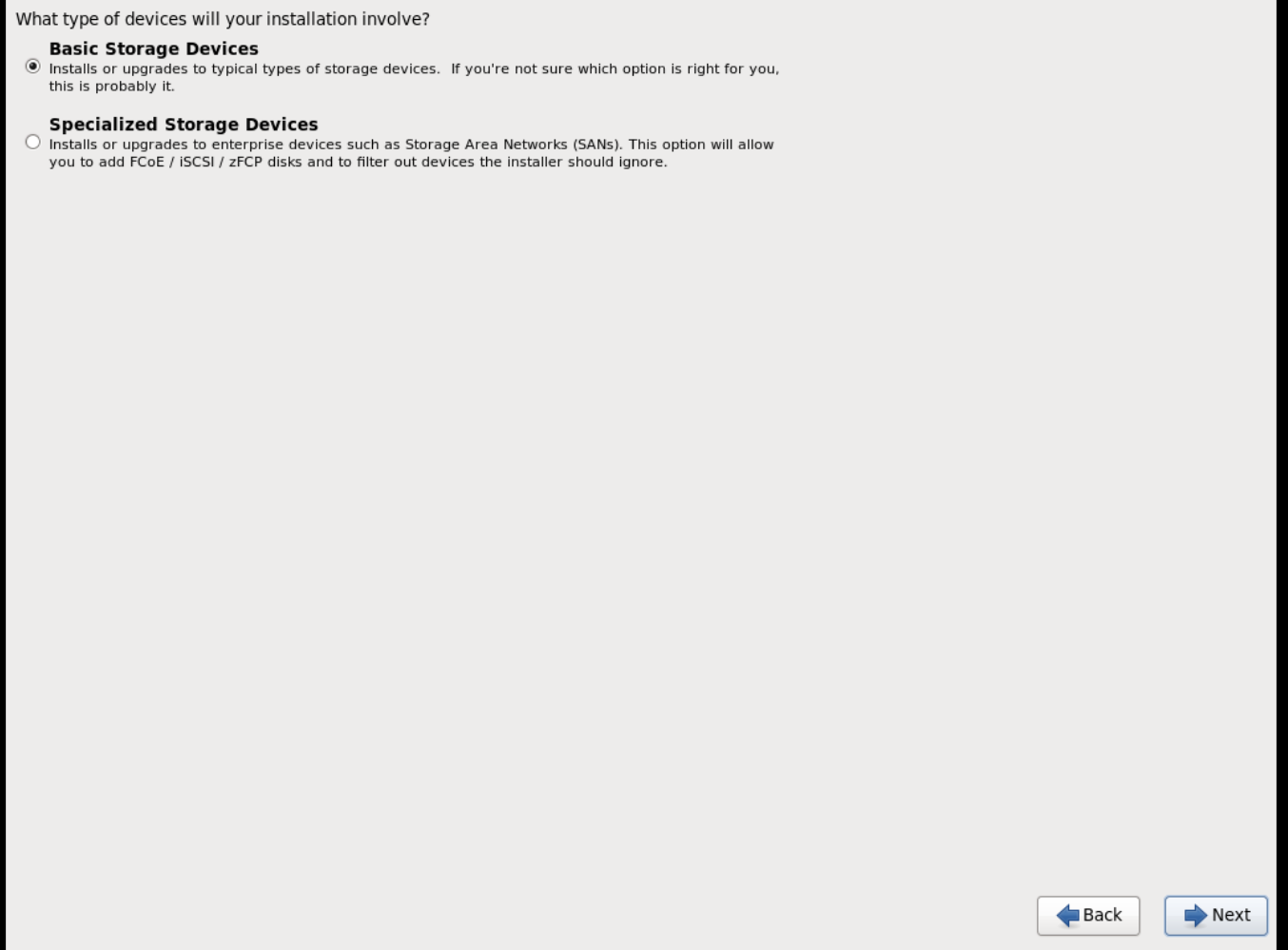
When prompted about which type of devices your installation uses, choose Basic Storage Devices.
-
Choose a
hostnamefor your device. The default host name islocalhost.localdomain. -
Set timezone and
rootpassword. -
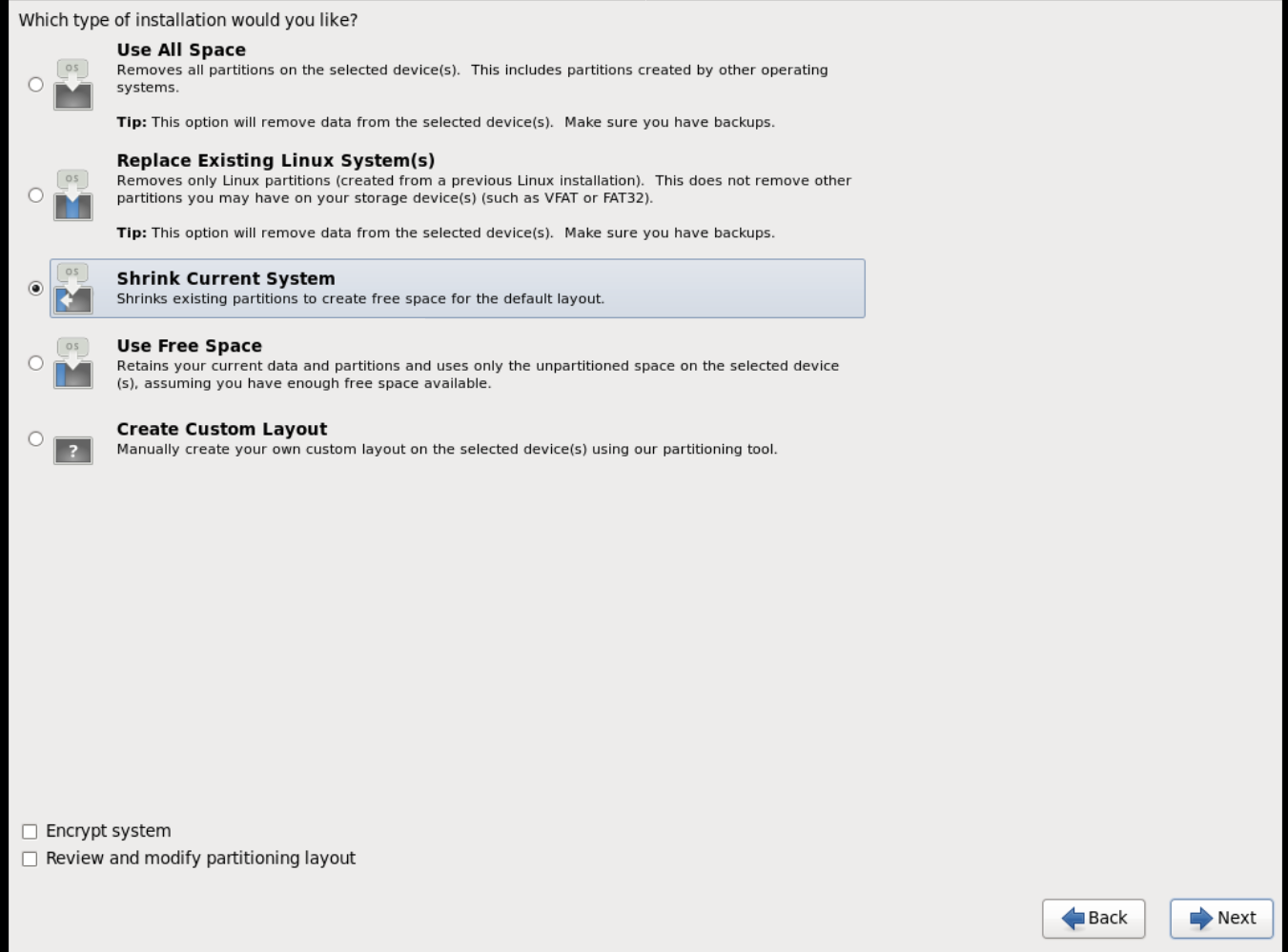
Based on the space on the disk, choose the type of installation.
-
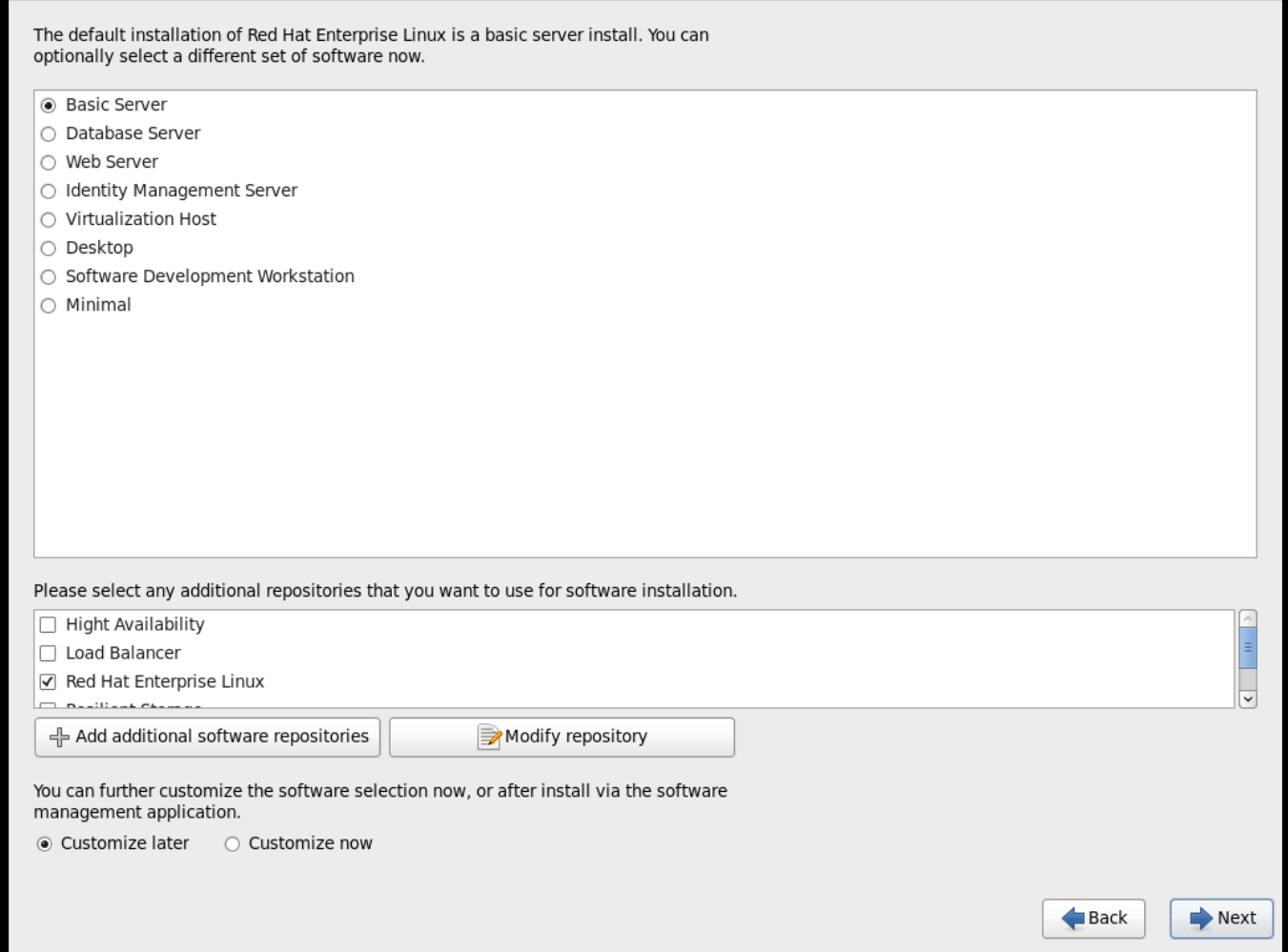
Choose the Basic Server install, which installs an SSH server.
- The installation process completes and Congratulations, your Red Hat Enterprise Linux installation is complete screen appears.
-
Reboot the instance and log in as the
rootuser. Update the
/etc/sysconfig/network-scripts/ifcfg-eth0file so it only contains the following values:TYPE=Ethernet DEVICE=eth0 ONBOOT=yes BOOTPROTO=dhcp NM_CONTROLLED=no- Reboot the machine.
Register the machine with the Content Delivery Network:
# sudo subscription-manager register # sudo subscription-manager attach --pool=Valid-Pool-Number-123456 # sudo subscription-manager repos --enable=rhel-6-server-rpmsUpdate the system:
# dnf -y updateInstall the
cloud-initpackages:# dnf install -y cloud-utils-growpart cloud-initEdit the
/etc/cloud/cloud.cfgconfiguration file and undercloud_init_modulesadd:- resolv-confThe
resolv-confoption automatically configures theresolv.confconfiguration file when an instance boots for the first time. This file contains information related to the instance such asnameservers,domain, and other options.To prevent network issues, create the
/etc/udev/rules.d/75-persistent-net-generator.rulesfile as follows:# echo "#" > /etc/udev/rules.d/75-persistent-net-generator.rulesThis prevents
/etc/udev/rules.d/70-persistent-net.rulesfile from being created. If/etc/udev/rules.d/70-persistent-net.rulesis created, networking may not function properly when booting from snapshots (the network interface is created as "eth1" rather than "eth0" and IP address is not assigned).Add the following line to
/etc/sysconfig/networkto avoid problems accessing the EC2 metadata service:NOZEROCONF=yesTo ensure the console messages appear in the
Logtab on the dashboard and thenova console-logoutput, add the following boot option to the/etc/grub.conf:console=tty0 console=ttyS0,115200n8Un-register the virtual machine so that the resulting image does not contain the same subscription details for every instance cloned based on it:
# subscription-manager repos --disable=* # subscription-manager unregister # dnf clean allPower off the instance:
# poweroffReset and clean the image using the
virt-sysprepcommand so it can be used to create instances without issues:[root@host]# virt-sysprep -d rhel6Reduce image size using the
virt-sparsifycommand. This command converts any free space within the disk image back to free space within the host:[root@host]# virt-sparsify --compress rhel6.qcow2 rhel6-cloud.qcow2This creates a new
rhel6-cloud.qcow2file in the location from where the command is run.NoteYou will need to manually resize the partitions of instances based on the image in accordance with the disk space in the flavor that is applied to the instance.
The rhel6-cloud.qcow2 image file is ready to be uploaded to the Image service. For more information on uploading this image to your OpenStack deployment using the dashboard, see Upload an Image
1.2.1.2.3. Create a Windows Image
This section provides you with the steps to manually create an OpenStack-compatible image in the QCOW2 format using a Windows ISO file.
Start the installation using
virt-installas shown below:[root@host]# virt-install --name=name \ --disk size=size \ --cdrom=path \ --os-type=windows \ --network=bridge:virbr0 \ --graphics spice \ --ram=RAMReplace the values of the
virt-installparameters as follows:- name — the name that the Windows guest should have.
- size — disk size in GB.
- path — the path to the Windows installation ISO file.
RAM — the requested amount of RAM in MB.
NoteThe
--os-type=windowsparameter ensures that the clock is set up correctly for the Windows guest, and enables its Hyper-V enlightenment features.Note that
virt-installsaves the guest image as/var/lib/libvirt/images/name.qcow2by default. If you want to keep the guest image elsewhere, change the parameter of the--diskoption as follows:--disk path=filename,size=sizeReplace filename with the name of the file which should store the guest image (and optionally its path); for example
path=win8.qcow2,size=8creates an 8 GB file namedwin8.qcow2in the current working directory.TipIf the guest does not launch automatically, run the
virt-viewercommand to view the console:[root@host]# virt-viewer name
- Installation of Windows systems is beyond the scope of this document. For instructions on how to install Windows, see the relevant Microsoft documentation.
-
To allow the newly-installed Windows system to use the virtualized hardware, you might need to install virtio drivers. To so do, first install the
virtio-winpackage on the host system. This package contains the virtio ISO image, which you must attach as a CD-ROM drive to the Windows guest. To install thevirtio-winpackage you must add the virtio ISO image to the guest, and install the virtio drivers. See Installing KVM paravirtualized drivers for Windows virtual machines in the Configuring and managing virtualization guide. To complete the setup, download and execute Cloudbase-Init on the Windows system. At the end of the installation of Cloudbase-Init, select the
Run SysprepandShutdowncheck boxes. TheSyspreptool makes the guest unique by generating an OS ID, which is used by certain Microsoft services.ImportantRed Hat does not provide technical support for Cloudbase-Init. If you encounter an issue, contact Cloudbase Solutions.
When the Windows system shuts down, the name.qcow2 image file is ready to be uploaded to the Image service. For more information on uploading this image to your OpenStack deployment using the dashboard or the command line, see Upload an Image.
1.2.1.3. Use libosinfo
Image Service (glance) can process libosinfo data for images, making it easier to configure the optimal virtual hardware for an instance. This can be done by adding the libosinfo-formatted operating system name to the glance image.
This example specifies that the image with ID
654dbfd5-5c01-411f-8599-a27bd344d79buses the libosinfo value ofrhel7.2:$ openstack image set 654dbfd5-5c01-411f-8599-a27bd344d79b --property os_name=rhel7.2As a result, Compute will supply virtual hardware optimized for
rhel7.2whenever an instance is built using the654dbfd5-5c01-411f-8599-a27bd344d79bimage.NoteFor a complete list of
libosinfovalues, refer to the libosinfo project: https://gitlab.com/libosinfo/osinfo-db/tree/master/data/os
1.2.2. Upload an Image
- In the dashboard, select Project > Compute > Images.
- Click Create Image.
- Fill out the values, and click Create Image when finished.
| Field | Notes |
|---|---|
| Name | Name for the image. The name must be unique within the project. |
| Description | Brief description to identify the image. |
| Image Source | Image source: Image Location or Image File. Based on your selection, the next field is displayed. |
| Image Location or Image File |
|
| Format | Image format (for example, qcow2). |
| Architecture | Image architecture. For example, use i686 for a 32-bit architecture or x86_64 for a 64-bit architecture. |
| Minimum Disk (GB) | Minimum disk size required to boot the image. If this field is not specified, the default value is 0 (no minimum). |
| Minimum RAM (MB) | Minimum memory size required to boot the image. If this field is not specified, the default value is 0 (no minimum). |
| Public | If selected, makes the image public to all users with access to the project. |
| Protected | If selected, ensures only users with specific permissions can delete this image. |
When the image has been successfully uploaded, its status is changed to active, which indicates that the image is available for use. Note that the Image service can handle even large images that take a long time to upload — longer than the lifetime of the Identity service token which was used when the upload was initiated. This is due to the fact that the Image service first creates a trust with the Identity service so that a new token can be obtained and used when the upload is complete and the status of the image is to be updated.
You can also use the glance image-create command with the property option to upload an image. More values are available on the command line. For a complete listing, see Image Configuration Parameters.
1.2.3. Update an Image
- In the dashboard, select Project > Compute > Images.
Click Edit Image from the dropdown list.
NoteThe Edit Image option is available only when you log in as an
adminuser. When you log in as ademouser, you have the option to Launch an instance or Create Volume.- Update the fields and click Update Image when finished. You can update the following values - name, description, kernel ID, ramdisk ID, architecture, format, minimum disk, minimum RAM, public, protected.
- Click the drop-down menu and select Update Metadata option.
- Specify metadata by adding items from the left column to the right one. In the left column, there are metadata definitions from the Image Service Metadata Catalog. Select Other to add metadata with the key of your choice and click Save when finished.
You can also use the glance image-update command with the property option to update an image. More values are available on the command line; for a complete listing, see Image Configuration Parameters.
1.2.4. Import an Image
You can import images into the Image service (glance) using web-download to import an image from a URI and glance-direct to import an image from a local file system. Both options are enabled by default.
Import methods are configured by the cloud administrator. Run the glance import-info command to list available import options.
1.2.4.1. Import from a Remote URI
You can use the web-download method to copy an image from a remote URI.
Create an image and specify the URI of the image to import.
glance image-create --uri <URI>-
You can monitor the image’s availability using the
glance image-show <image-ID>command where the ID is the one provided during image creation.
The Image service web-download method uses a two-stage process to perform the import. First, it creates an image record. Second, it retrieves the image the specified URI. This method provides a more secure way to import images than the deprecated copy-from method used in Image API v1.
The URI is subject to optional blacklist and whitelist filtering as described in the Advanced Overcloud Customization Guide.
The Image Property Injection plugin may inject metadata properties to the image as described in the Advanced Overcloud Customization Guide. These injected properties determine which compute nodes the image instances are launched on.
1.2.4.2. Import from a Local Volume
The glance-direct method creates an image record, which generates an image ID. Once the image is uploaded to the service from a local volume, it is stored in a staging area and is made active after it passes any configured checks. The glance-direct method requires a shared staging area when used in a highly available (HA) configuration.
Image uploads using the glance-direct method fail in an HA environment if a common staging area is not present. In an HA active-active environment, API calls are distributed to the glance controllers. The download API call could be sent to a different controller than the API call to upload the image. For more information about configuring the staging area, refer to the Storage Configuration section in the Advanced Overcloud Customization Guide.
The glance-direct method uses three different calls to import an image:
-
glance image-create -
glance image-stage -
glance image-import
You can use the glance image-create-via-import command to perform all three of these calls in one command. In the example below, uppercase words should be replaced with the appropriate options.
glance image-create-via-import --container-format FORMAT --disk-format DISKFORMAT --name NAME --file /PATH/TO/IMAGEOnce the image moves from the staging area to the back end location, the image is listed. However, it may take some time for the image to become active.
You can monitor the image’s availability using the glance image-show <image-ID> command where the ID is the one provided during image creation.
1.2.5. Delete an Image
- In the dashboard, select Project > Compute > Images.
- Select the image you want to delete and click Delete Images.
1.2.6. Hide or Unhide an Image
You can hide public images from normal listings presented to users. For instance, you can hide obsolete CentOS 7 images and show only the latest version to simplify the user experience. Users can discover and use hidden images.
To hide an image:
glance image-update <image-id> --hidden 'true'
To create a hidden image, add the --hidden argument to the glance image-create command.
To unhide an image:
glance image-update <image-id> --hidden 'false'1.2.8. Enabling image conversion
With the GlanceImageImportPlugins parameter enabled, you can upload a QCOW2 image, and the Image service will convert it to RAW.
Image conversion is automatically enabled when you use Red Hat Ceph Storage RBD to store images and boot Nova instances.
To enable image conversion, create an environment file that contains the following parameter value and include the new environment file with the -e option in the openstack overcloud deploy command:
parameter_defaults:
GlanceImageImportPlugins:'image_conversion'1.2.9. Converting an image to RAW format
Red Hat Ceph Storage can store, but does not support using, QCOW2 images to host virtual machine (VM) disks.
When you upload a QCOW2 image and create a VM from it, the compute node downloads the image, converts the image to RAW, and uploads it back into Ceph, which can then use it. This process affects the time it takes to create VMs, especially during parallel VM creation.
For example, when you create multiple VMs simultaneously, uploading the converted image to the Ceph cluster may impact already running workloads. The upload process can starve those workloads of IOPS and impede storage responsiveness.
To boot VMs in Ceph more efficiently (ephemeral back end or boot from volume), the glance image format must be RAW.
Converting an image to RAW may yield an image that is larger in size than the original QCOW2 image file. Run the following command before the conversion to determine the final RAW image size:
qemu-img info <image>.qcow2To convert an image from QCOW2 to RAW format, do the following:
qemu-img convert -p -f qcow2 -O raw <original qcow2 image>.qcow2 <new raw image>.raw1.2.9.1. Configuring Image Service to accept RAW and ISO only
Optionally, to configure the Image Service to accept only RAW and ISO image formats, deploy using an additional environment file that contains the following:
parameter_defaults:
ExtraConfig:
glance::config::api_config:
image_format/disk_formats:
value: "raw,iso"1.2.10. Storing an image in RAW format
With the GlanceImageImportPlugins parameter enabled, run the following command to store a previously created image in RAW format:
$ glance image-create-via-import \
--disk-format qcow2 \
--container-format bare \
--name NAME \
--visibility public \
--import-method web-download \
--uri http://server/image.qcow2-
For
--name, replaceNAMEwith the name of the image; this is the name that will appear inglance image-list. -
For
--uri, replacehttp://server/image.qcow2with the location and file name of the QCOW2 image.
This command example creates the image record and imports it by using the web-download method. The glance-api downloads the image from the --uri location during the import process. If web-download is not available, glanceclient cannot automatically download the image data. Run the glance import-info command to list the available image import methods.