Chapitre 12. Troubleshooting authentication with SSSD in IdM
Authentication in an Identity Management (IdM) environment involves many components:
On the IdM client:
- The SSSD service.
- The Name Services Switch (NSS).
- Pluggable Authentication Modules (PAM).
On the IdM server:
- The SSSD service.
- The IdM Directory Server.
- The IdM Kerberos Key Distribution Center (KDC).
If you are authenticating as an Active Directory (AD) user:
- The Directory Server on an AD Domain Controller.
- The Kerberos server on an AD Domain Controller.
To authenticate users, you must be able to perform the following functions with the SSSD service:
- Retrieve user information from the authentication server.
- Prompt the user for their credentials, pass those credentials to the authentication server, and process the outcome.
The following sections discuss how information flows between the SSSD service and servers that store user information, so you can troubleshoot failing authentication attempts in your environment:
- Data flow when retrieving IdM user information with SSSD
- Data flow when retrieving AD user information with SSSD
- Data flow when authenticating as a user with SSSD in IdM
- Narrowing the scope of authentication issues
- SSSD log files and logging levels
- Enabling detailed logging for SSSD in the sssd.conf file
- Enabling detailed logging for SSSD with the sssctl command
- Gathering debugging logs from the SSSD service to troubleshoot authentication issues with an IdM server
- Gathering debugging logs from the SSSD service to troubleshoot authentication issues with an IdM client
- Tracking client requests in the SSSD backend
- Tracking client requests using the log analyzer tool
12.1. Data flow when retrieving IdM user information with SSSD
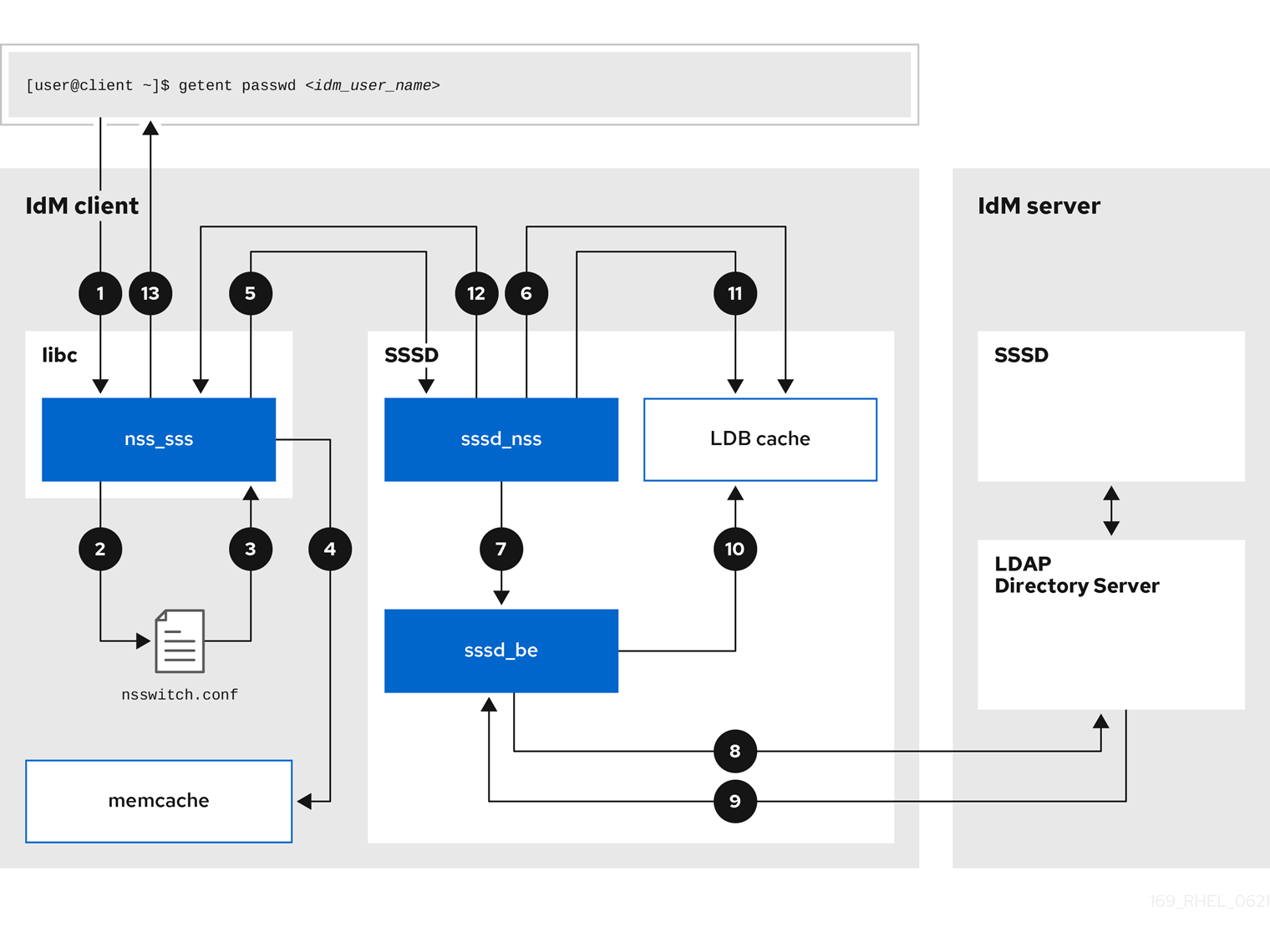
The following diagram is a simplification of the information flow between an IdM client and an IdM server during a request for IdM user information with the command getent passwd <idm_user_name>.
-
The
getentcommand triggers thegetpwnamcall from thelibclibrary. -
The
libclibrary references the/etc/nsswitch.confconfiguration file to check which service is responsible for providing user information, and discovers the entrysssfor the SSSD service. -
The
libclibrary opens thenss_sssmodule. -
The nss_sss module checks the memory-mapped cache for the user information. If the data is present in the cache, the
nss_sssmodule returns it. -
If the user information is not in the memory-mapped cache, the request is passed to the SSSD
sssd_nssresponder process. -
The SSSD service checks its cache. If the data is present in the cache and valid, the
sssd_nssresponder reads the data from the cache and returns it to the application. -
If the data is not present in the cache or it is expired, the
sssd_nssresponder queries the appropriate back-end process and waits for a reply. The SSSD service uses the IPA backend in an IdM environment, enabled by the settingid_provider=ipain thesssd.confconfiguration file. -
The
sssd_beback-end process connects to the IdM server and requests the information from the IdM LDAP Directory Server. - The SSSD back-end on the IdM server responds to the SSSD back-end process on the IdM client.
- The SSSD back-end on the client stores the resulting data in the SSSD cache and alerts the responder process that the cache has been updated.
-
The
sssd_nssfront-end responder process retrieves the information from the SSSD cache. -
The
sssd_nssresponder sends the user information to thenss_sssresponder, completing the request. -
The
libclibrary returns the user information to the application that requested it.