Este conteúdo não está disponível no idioma selecionado.
Chapter 22. User Authentication
This chapter describes managing user authentication mechanisms, including information on how to manage users' passwords, SSH keys, and certificates, or how to configure one-time password (OTP) and smart-card authentication.
Note
For documentation on how to log in to Identity Management (IdM) using Kerberos, see Chapter 5, The Basics of Managing the IdM Server and Services.
22.1. User Passwords
Copiar o linkLink copiado para a área de transferência!
22.1.1. Changing and Resetting User Passwords
Copiar o linkLink copiado para a área de transferência!
Regular users without the permission to change other users' passwords can change only their own personal password. Personal passwords changed in this way:
- Must meet the IdM password policies. For details on configuring password policies, see Chapter 28, Defining Password Policies.
Administrators and users with password change rights can set initial passwords for new users and reset passwords for existing users. Passwords changed in this way:
- Do not have to meet the IdM password policies
- Expire after the first successful login. When this happens, IdM prompts the user to change the expired password immediately. To disable this behavior, see Section 22.1.2, “Enabling Password Reset Without Prompting for a Password Change at the Next Login”.
Note
The LDAP Directory Manager (DM) user can change user passwords using LDAP tools. The new password can override any IdM password policies. Passwords set by DM do not expire after the first login.
22.1.1.1. Web UI: Changing Your Own Personal Password
Copiar o linkLink copiado para a área de transferência!
- In the top right corner, click
. Figure 22.1. Resetting Password

- Enter the new password.
22.1.1.2. Web UI: Resetting Another User's Password
Copiar o linkLink copiado para a área de transferência!
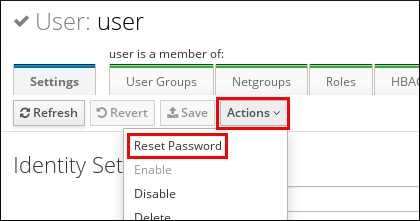
- Select
. - Click the name of the user to edit.
- Click
. Figure 22.2. Resetting Password
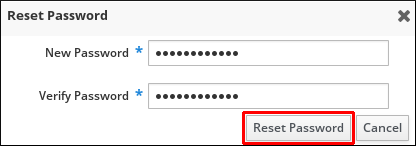
- Enter the new password, and click .
Figure 22.3. Confirming New Password
22.1.1.3. Command Line: Changing or Resetting Another User's Password
Copiar o linkLink copiado para a área de transferência!
To change your own personal password or to change or reset another user's password, add the
--password option to the ipa user-mod command. The command will prompt you for the new password.
$ ipa user-mod user --password
Password:
Enter Password again to verify:
--------------------
Modified user "user"
--------------------
...
22.1.2. Enabling Password Reset Without Prompting for a Password Change at the Next Login
Copiar o linkLink copiado para a área de transferência!
By default, when an administrator resets another user's password, the password expires after the first successful login. See Section 22.1.1, “Changing and Resetting User Passwords” for details.
To ensure that passwords set by administrators do not expire when used for the first time, make these changes on every Identity Management server in the domain:
- Edit the password synchronization entry:
cn=ipa_pwd_extop,cn=plugins,cn=config. - Specify the administrative user accounts in the
passSyncManagersDNsattribute. The attribute is multi-valued.
For example, to specify the
admin user by using the ldapmodify utility:
$ ldapmodify -x -D "cn=Directory Manager" -W -h ldap.example.com -p 389
dn: cn=ipa_pwd_extop,cn=plugins,cn=config
changetype: modify
add: passSyncManagersDNs
passSyncManagersDNs: uid=admin,cn=users,cn=accounts,dc=example,dc=comWarning
Specify only the users who require these additional privileges. All users listed under
passSyncManagerDNs can:
- Perform password change operations without requiring a subsequent password reset
- Bypass the password policy so that no strength or history enforcement is applied
22.1.3. Unlocking User Accounts After Password Failures
Copiar o linkLink copiado para a área de transferência!
If a user attempts to log in using an incorrect password a certain number of times, IdM will lock the user account, which prevents the user from logging in. Note that IdM does not display any warning message that the user account has been locked.
Note
For information on setting the exact number of allowed failed attempts and the duration of the lockout, see Chapter 28, Defining Password Policies.
IdM automatically unlocks the user account after a specified amount of time has passed. Alternatively, the administrator can unlock the user account manually.
Unlocking a User Account Manually
To unlock a user account, use the ipa user-unlock command.
$ ipa user-unlock user
-----------------------
Unlocked account "user"
-----------------------
After this, the user is able to log in again.
22.1.3.1. Checking the Status of a User Account
Copiar o linkLink copiado para a área de transferência!
To display the number of failed login attempts for a user, use the ipa user-status command. If the displayed number exceeds the number of allowed failed login attempts, the user account is locked.
$ ipa user-status user
-----------------------
Account disabled: False
-----------------------
Server: example.com
Failed logins: 8
Last successful authentication: 20160229080309Z
Last failed authentication: 20160229080317Z
Time now: 2016-02-29T08:04:46Z
----------------------------
Number of entries returned 1
----------------------------
By default, IdM unning on Red Hat Enterprise Linux 7.4 and later does not store the time stamp of the last successful Kerberos authentication of a user. To enable this feature, see Section 22.2, “Enabling Tracking of Last Successful Kerberos Authentication”.