此内容没有您所选择的语言版本。
5.4. Configuring Fence Devices
Configuring fence devices for the cluster consists of selecting one or more fence devices and specifying fence-device-dependent parameters (for example, name, IP address, login, and password).
To configure fence devices, follow these steps:
- Click . At the bottom of the right frame (labeled ), click the button. Clicking causes the Fence Device Configuration dialog box to be displayed (refer to Figure 5.4, “Fence Device Configuration”).
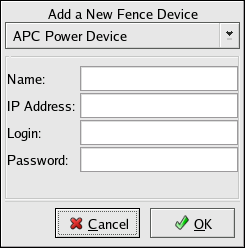
Figure 5.4. Fence Device Configuration
- At the Fence Device Configuration dialog box, click the drop-down box under and select the type of fence device to configure.
- Specify the information in the Fence Device Configuration dialog box according to the type of fence device. Refer to Appendix B, Fence Device Parameters for more information about fence device parameters.
- Click .
- Choose => to save the changes to the cluster configuration.