Chapter 8. Monitoring server and database activity
You can monitor Directory Server and replication topology by using the web console and the dsconf utility. You can configure Directory Server to record events to log files that you can then use to troubleshoot, monitor, and analyze the directory activity.
8.1. Monitoring Directory Server activity
The Red Hat Directory Server tracks and records performance data by using performance counters and logs.
- Performance counters provide a measurement of the Directory Server performance. Performance counters focus on the operations and information of Directory Server, configured databases, and database links (chaining databases).
Log files record events that happen during server activity. To monitor the performance, you can use the following logs:
- Access log
- Error log
- Audit log
- Audit fail log
Security log
For more details about log files, see Types of log files in Directory Server.
The information on the current Directory Server activities is available through the web console or by using the command line. You can also monitor the cache activity of all databases.
The access log is buffered and it enables full access logging even with highly loaded servers. However, there is a discrepancy between when the event occurs on the server and the time the event is recorded in the log.
8.1.1. Monitoring Directory Server using the command line
With the dsconf command, you can monitor the disk usage, query server statistics that are stored in the directory, and other metrics to track the performance.
Prerequisite
-
Ensure the server is running to use the
dconfutility.
Procedure
To monitor the server performance using the command-line, run:
# dsconf <instance_name> monitor server
8.1.2. Monitoring Directory Server using the web console
The web console is a browser-based graphical user interface (GUI) that enables users to perform administrative tasks. The Directory Server packages automatically install the Directory Server user interface for the web console.
Procedure
To open Directory Server in the web console, connect to the web console running on port 9090 on the Directory Server host.
https://server.example.com:9090-
Log in as the
rootuser or withsudoprivileges. Under the Monitoring tab, select
. 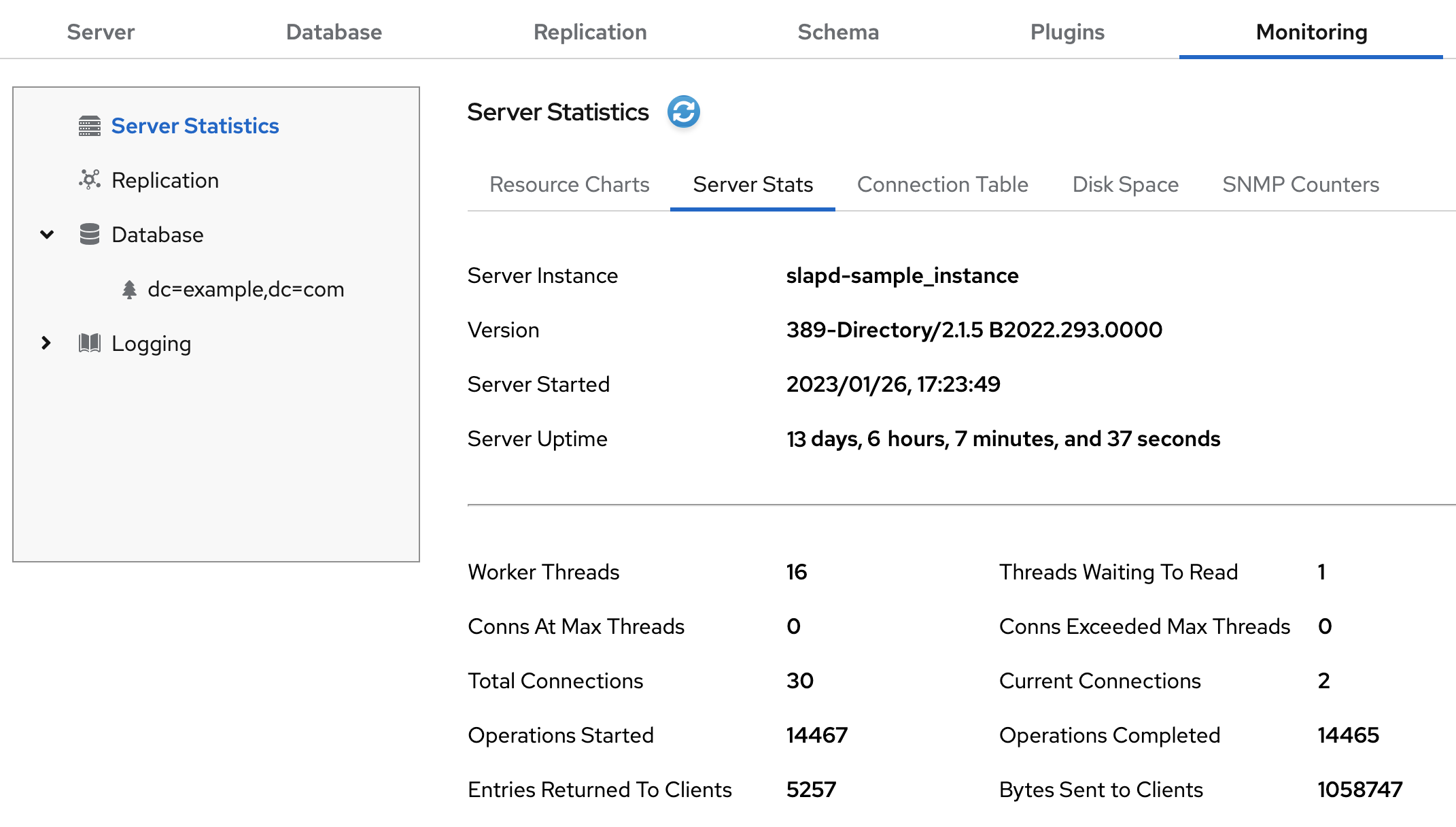
8.1.3. Server monitoring attributes
The dsconf command returns the following attributes when monitoring Directory Server.
| Attribute | Description |
|---|---|
|
| Identifies the current directory version number. |
|
| The current number of active threads handling requests. The internal server tasks, such as replication or chaining, can create additional threads when required. |
|
| Provides the following summary information for each open connection when you bind to the directory as the Directory Manager:
By default, this information is available to the Directory Manager. However, you can edit the Access Control Instruction (ACI) attribute in directory entries and configure additional users on access privileges to the information. |
|
| Identifies the number of connections currently in service by the directory. |
|
| Identifies the number of connections the server handles after it starts. |
|
|
Displays the connections currently in a |
|
|
Displays the number of times a connection hits the |
|
|
Shows the number of file descriptors available for the directory. Each connection requires one file descriptor for every open index, log file management, and for |
|
| Identifies the number of threads waiting to read data from a client. |
|
| Identifies the number of operations the server initiates after it starts. |
|
| Identifies the number of operations the server completes. |
|
| Identifies the number of entries sent to clients after the server starts. |
|
| Identifies the number of bytes sent to clients after the server starts. |
|
| Identifies the server snapshot time. The time display is Greenwich Mean Time (GMT) in UTC format. |
|
| Identifies the time when the server starts. The time display is Greenwich Mean Time (GMT) in UTC format. |
|
| Identifies the number of back ends (databases) the server services. |
8.1.4. Server information
The Directory Server displays the following fields under the Server Information menu.
| Field | Description |
|---|---|
|
| Displays the name of the Directory Server instance. |
|
| Identifies the current server version. |
|
| The date and time the server is up and running. |
|
| The measure of time the instance is up and running. |
|
| The current number of active threads that handle requests. The internal server tasks, such as replication or chaining, can create additional threads when required. |
|
| The total number of threads waiting to be read from the client. Threads may not be immediately read if the server receives new request from the client and halts the request transmission. Generally, waiting threads indicate a slow network or a slow client. |
|
|
Displays all connections that are currently in a |
|
|
Displays the number of times a connection hits |
|
| The total number of connections established to a Directory Server instance. |
|
| The total number of open connections. Each connection can start multiple operations and therefore multiple threads. |
|
| The number of operations initiated by a connection. |
|
| The number of operations completed by the server for all connections. |
|
| The number of entries sent to clients after the server starts. |
8.2. Using the health check to identify problems
You can perform a health check to analyze the Directory Server instance for potential issues and to get recommended solutions.
8.2.1. Running the Directory Server health check
Use the dsctl healthcheck command to run a health check.
Procedure
To run a health check, enter:
# dsctl <instance_name> healthcheck Beginning lint report, this could take a while ... Checking Backends ... Checking Config ... Checking Encryption ... Checking FSChecks ... Checking ReferentialIntegrityPlugin ... Checking MonitorDiskSpace ... Checking Replica ... Checking Changelog ... Checking NssSsl ... Healthcheck complete. 1 Issue found! Generating report ...To display the output in JSON format, pass the
--jsonparameter to the command:# dsctl --json <instance_name> healthcheckPossible report of the health check
[1] DS Lint Error: DSELE0001 -------------------------------------------------------------------------------- Severity: MEDIUM Affects: -- cn=encryption,cn=config Details: ----------- This Directory Server may not be using strong TLS protocol versions. TLS1.0 is known to have a number of issues with the protocol. Please see: https://tools.ietf.org/html/rfc7457 It is advised you set this value to the maximum possible. Resolution: ----------- There are two options for setting the TLS minimum version allowed. You, can set "sslVersionMin" in "cn=encryption,cn=config" to a version greater than "TLS1.0" You can also use 'dsconf' to set this value. Here is an example: # dsconf slapd-instance_name security set --tls-protocol-min=TLS1.2 You must restart the Directory Server for this change to take effect. Or, you can set the system wide crypto policy to FUTURE which will use a higher TLS minimum version, but doing this affects the entire system: # update-crypto-policies --set FUTURE \===== End Of Report (1 Issue found) =====Possible report of the health check in JSON format
[ { "dsle": "DSELE0001", "severity": "MEDIUM", "items": [ "cn=encryption,cn=config" ], "detail": "This Directory Server may not be using strong TLS protocol versions. TLS1.0 is known to\nhave a number of issues with the protocol. Please see:\n\nhttps://tools.ietf.org/html/rfc7457\n\nIt is advised you set this value to the maximum possible.", "fix": "There are two options for setting the TLS minimum version allowed. You,\ncan set \"sslVersionMin\" in \"cn=encryption,cn=config\" to a version greater than \"TLS1.0\"\nYou can also use 'dsconf' to set this value. Here is an example:\n\n # dsconf slapd-instance_name security set --tls-protocol-min=TLS1.2\n\nYou must restart the Directory Server for this change to take effect.\n\nOr, you can set the system wide crypto policy to FUTURE which will use a higher TLS\nminimum version, but doing this affects the entire system:\n\n # update-crypto-policies --set FUTURE" } ]
8.2.2. Overview of health checks
The dsctl healthcheck command performs the following checks:
| Component | Severity | Result code | Description |
|---|---|---|---|
| Back end | Medium | DSBLE0006 | Berkeley database (BDB) is still used as a backend. BDB is deprecated and should not be used as a backend. |
| Back end | Low | DSBLE0005 | Backend configuration attributes mismatch. Found configuration attributes that are not applicable for the configured backend type. |
| Back end | Low | DSBLE0003 | The database was not initialized. The database was created, but it is empty. |
| Back end | Medium | DSBLE0001 | The mapping tree entry for a back end is missing in the configuration. |
| Config | Low | DSCLE0001 | High-resolution time stamps are disabled. |
| Config | High | DSVIRTLE0001 | A virtual attribute is incorrectly indexed. Indexed attributes used by roles or Class of Service (CoS) definitions can corrupt search results. |
| Operating System | Medium | DSPERMLE0001 |
The permissions set on the |
| Operating System | High | DSDSLE0001 | Low disk space. |
| Operating System | High | DSPERMLE0002 |
The permissions set on the |
| Plug-ins | Low | DSRILE0001 | An update delay is set for the Referential Integrity plug-in. This can cause replication issues. |
| Plug-ins | High | DSRILE0002 | The Referential Integrity plug-in misses indexes. The plug-in queries certain attributes for every delete operation if they are not indexed. This can cause hard-to-detect unindexed searches and high CPU usage. |
| Replication | Low | DSREPLLE0002 | Conflict entries exist in the database. |
| Replication | Low | DSSKEWLE0001 | The replication time skew is larger than 6 hours and lower than 12 hours. |
| Replication | Medium | DSCLLE0001 | Changelog trimming is disabled. In this case, the changelog grows without limits. |
| Replication | Medium | DSREPLLE0004 | The health check failed to retrieve the replication status. |
| Replication | Medium | DSREPLLE0003 | The topology is out of synchronization, but the replication is working. |
| Replication | Medium | DSREPLLE0005 | A remote replica is not reachable. |
| Replication | Medium | DSSKEWLE0002 | The replication time skew is larger than 12 hours and lower than 24 hours. |
| Replication | High | DSREPLLE0001 | The topology is out of synchronization, and the replication is not working. |
| Replication | High | DSSKEWLE0003 | The replication time skew is larger than 24 hours. Replication sessions could break. |
| Security | Medium | DSELE0001 | The minimum TLS version is set to a value lower than TLS 1.2. |
| Security | High | DSCLE0002 | A password storage scheme is weak. |
| Server | High | DSBLE0002 | The health check failed to query the back end. |
| Transparent Huge Pages (THP) | Medium | DSTHPLE0001 | THP are enabled and might have an impact on the Directory Server performance. |
| TLS certificates | Medium | DSCERTLE0001 | The server certificate expires within the next 30 days. |
| TLS certificates | High | DSCERTLE0002 | The server certificate has expired. |
| Indexes | Low | DSMOLE0002 | If the substring index is configured for a membership attribute. The removal of a member from a large group can be slow. |
8.3. Configuring log files in Directory Server
Directory Server records events to log files. Use these files to troubleshoot, monitor, and analyze the directory activity.
In Directory Server, you can enable or disable logging, configure the log level, define logging policies, compress log files, and perform other operations.
8.3.1. Types of log files in Directory Server
Directory Server has the following log file types that are stored the /var/log/dirsrv/slapd-<instance_name>/ directory:
- Access log (access). Enabled by default
- Contains information on client connections and connection attempts to the Directory Server instance. Note that because the access log is buffered, you can notice a discrepancy between when the event occurs on the server and the time the event is recorded in the log.
- Error log (error). Enabled by default
- Contains detailed messages of errors and events that the directory experiences during normal operations.
If Directory Server fails to write messages to the error log file, the server sends an error message to the syslog service and exits.
- Audit log (audit). Disabled by default
-
Records changes made to each database and to the server configuration. If you enable audit logging, Directory Server records only successful operations to the
auditlog file. - Audit fail log (auditfail). Disabled by default
-
Records failed change operations. With the default settings, Directory Server writes failed operations to the same file as the audit log. To write failed operations to a separate file, set a path to this file in the
nsslapd-auditfaillogconfiguration attribute. For details, see nsslapd-auditfaillog section. - Security log (security). Enabled by default
- Records authentication events, authorization issues, DoS/TCP attacks, and other security events.
For more detailed information about Directory Server log files, see Log files reference.
8.3.2. Displaying log files
You can display Directory Server log files using the command line or the web console.
8.3.2.1. Displaying log files using the command line
Use the utilities included in Red Hat Enterprise Linux, such as less, more, and cat, to view the log files.
Prerequisites
- You enabled logging as described in Enabling or disabling logging using the command line.
Procedure
To display the log files, use the following commands:
# less /var/log/dirsrv/slapd-<instance_name>/access # less /var/log/dirsrv/slapd-<instance_name>/errors # less /var/log/dirsrv/slapd-<instance_name>/audit # less /var/log/dirsrv/slapd-<instance_name>/access # less /var/log/dirsrv/slapd-<instance_name>/securityNote that by default the audit log and the audit fail log write operations to the same file.
To display the locations of log files, use the command:
# dsconf <instance_name> config get nsslapd-accesslog nsslapd-errorlog nsslapd-auditlog nsslapd-auditfaillog nsslapd-securitylog nsslapd-accesslog: /var/log/dirsrv/slapd-<instance_name>/access nsslapd-errorlog: /var/log/dirsrv/slapd-<instance_name>/errors nsslapd-auditlog: /var/log/dirsrv/slapd-<instance_name>/audit nsslapd-auditfaillog: /var/log/dirsrv/slapd-<instance_name>/auditfail nsslapd-securitylog: /var/log/dirsrv/slapd-<instance_name>/securityNoteIf you have not enabled logging for a specified log type, Directory Server does not create the corresponding log file.
8.3.2.2. Displaying log files using the web console
To view Directory Server log files use the tab of the web console.
Prerequisites
- You are logged in to the web console.
Procedure
- Select the instance.
-
Navigate to
. In the list of log types, select the log you want to display:

Optional: Apply the following settings to the log viewer:
- Set the number of records to display.
- Enable automatic display of new log entries by selecting Continuously Refresh.
- Click the button to apply the changes.
8.3.3. Enabling or disabling logging
By default, Directory Server enables only access, error, and security logging.
- IMPORTANT
- Every 2000 accesses to the directory increases the access log file by approximately 1 MB. However, before disabling the access logging, consider that this information can help to troubleshoot problems.
8.3.3.1. Enabling or disabling logging using the command line
To enable or disable logging for an instance, use the dsconf utility.
Procedure
To enable, for example, audit logging, do the following steps:
Ensure that the logging you want to enable has the correctly configured path and filename:
# dsconf <instance_name> logging audit getAudit Log Configuration ------------------------------------------------------- ... Log name and location = /var/log/dirsrv/slapd-instance_name/audit ...The command displays the audit logging configuration. The
nsslapd-auditlogattribute in thecn=configentry is responsible for storing the path and filename value.Enable the audit logging:
# dsconf <instance_name> logging audit set logging-enabledThe command sets the
nsslapd-audit-logging-enabledattribute toonin thecn=configentry.
To disable, for example, the error logging:
# dsconf <instance_name> logging error set logging-disabledThe command sets the
nsslapd-errorlog-logging-enabledattribute tooffin thecn=configentry.When you disable logging, Directory Server stops to record new events to a log file. However, the log file remains in the
/var/log/dirsrv/slapd-<instance_name>/directory.
Verification
Check the audit logging settings:
# dsconf <instance_name> logging audit getAudit Log Configuration ------------------------------------------------------- ... Log name and location = /var/log/dirsrv/slapd-instance_name/audit Logging enabled = on ...Check the error logging settings:
# dsconf <instance_name> logging error getError Log Configuration ------------------------------------------------------- ... Log name and location = /var/log/dirsrv/slapd-instance_name/errors Logging enabled = off ...
8.3.3.2. Enabling or disabling logging using the web console
To enable or disable logging for an instance use the tab in the web console.
Prerequisites
- You are logged in to the web console.
Procedure
- Select the instance.
-
Navigate to
. - Select the log type you want to configure, for example, Access Log.
- Enable or disable the logging for the selected log type.
- Optional: Configure additional settings, such as the log level, the log rotation policy, the log format, and the log buffering.
- Click the button to apply the changes.
Verification
-
Navigate to
and see if Directory Server now logs the events.
8.3.4. Defining a log rotation policy
Directory Server periodically rotates the current log file and creates a new one. However, you can change the default behavior by setting a rotation policy using the command line or the web console.
You can manage the following rotation settings:
- Maximum number of logs
Sets the maximum number of log files to keep. When the number of files is reached, Directory Server deletes the oldest log file before creating the new one. By default, it is
10for the access log, and1for other logs. Use themax-logsoption of thedsconfutility or the web console to configure the corresponding setting.-
access log:
nsslapd-accesslog-maxlogsperdir -
error log:
nsslapd-errorlog-maxlogsperdir -
audit log:
nsslapd-auditlog-maxlogsperdir -
auditfail log:
nsslapd-auditfaillog-maxlogsperdir -
security log:
nsslapd-securitylog-maxlogsperdir
-
access log:
- Maximum log size (in MB)
Sets the maximum size of a log file in megabytes before it is rotated. By default, it is
100MB for all logs. Use themax-logsizeoption of thedsconfutility or the web console to configure the corresponding setting.-
access log:
nsslapd-accesslog-maxlogsize -
error log:
nsslapd-errorlog-maxlogsize -
audit log:
nsslapd-auditlog-maxlogsize -
auditfail log:
nsslapd-auditfaillog-maxlogsize -
security log:
nsslapd-securitylog-maxlogsize
-
access log:
- Create new log every
Sets the maximum age of a log file. By default, Directory Server rotates all logs every week. Use the
rotation-intervalandrotation-interval-unitoptions of thedsconfutility or the web console to configure the corresponding setting.-
access log:
nsslapd-accesslog-logrotationtimeandnsslapd-accesslog-logrotationtimeunit -
error log:
nsslapd-errorlog-logrotationtimeandnsslapd-errorlog-logrotationtimeunit -
audit log:
nsslapd-auditlog-logrotationtimeandnsslapd-auditlog-logrotationtimeunit -
auditfail log:
nsslapd-auditfaillog-logrotationtimeandnsslapd-auditfaillog-logrotationtimeunit -
security log:
nsslapd-securitylog-logrotationtimeandnsslapd-securitylog-logrotationtimeunit
-
access log:
- Time of day
Set the time when the log file is rotated. This setting is not enabled by default for all logs. Use the
rotation-tod-hourandrotation-tod-minuteoptions of thedsconfutility or the web console to configure the corresponding setting.-
access log:
nsslapd-accesslog-logrotationsynchourandnsslapd-accesslog-logrotationsyncmin -
error log:
nsslapd-errorlog-logrotationsynchourandnsslapd-errorlog-logrotationsyncmin -
audit log:
nsslapd-auditlog-logrotationsynchourandnsslapd-auditlog-logrotationsyncmin -
auditfail log:
nsslapd-auditfaillog-logrotationsynchourandnsslapd-auditfaillog-logrotationsyncmin -
security log:
nsslapd-securitylog-logrotationsynchourandnsslapd-securitylog-logrotationsyncmin
-
access log:
- Access mode
The access mode sets the file permissions on newly created log files. By default, it is
600for all logs. Use themodeoption of thedsconfutility or the web console to configure the corresponding setting.-
access log:
nsslapd-accesslog-mode -
error log:
nsslapd-errorlog-mode -
audit log:
nsslapd-auditlog-mode -
auditfail log:
nsslapd-auditfaillog-mode -
security log:
nsslapd-securitylog-mode
-
access log:
For details about the log configuration settings, see Core server configuration attributes description.
8.3.4.1. Configuring a log rotation policy using the command line
You can change the default log rotation settings.
For example, you want the error log to keep maximum 3 logs, to rotate a log file when it exceeds 90 MB size or every 5 days.
Procedure
Set the maximum number of log files to keep:
# dsconf <instance_name> logging error set max-logs 3The command sets the
nsslapd-errorlog-maxlogsperdirattribute.Sets the maximum size of a log file in megabytes before it is rotated:
# dsconf <instance_name> logging error set max-logsize 90The command sets the
nsslapd-errorlog-maxlogsizeattribute.Set the maximum age of a log file.
Provide the period of time between error log file rotations:
# dsconf <instance_name> logging error set rotation-interval 5The command modifies the
nsslapd-errorlog-logrotationtimeattribute.Provide the units for the rotation period (
month,week,day,hour,minute):# dsconf <instance_name> logging error set rotation-interval-unit dayThe command modifies the
nsslapd-errorlog-logrotationtimeunitattribute.
Optional: To make analysis of the log files easier, configure the hour of the day and minutes for the error logs rotation.
Enable synchronization with a particular time of the day:
# dsconf <instance_name> logging error set rotation-tod-enabledThe command sets the
nsslapd-errorlog-logrotationsync-enabledattribute toon.Set the hour for the log rotation:
# dsconf <instance_name> logging error set rotation-tod-hour 22The command modifies the
nsslapd-errorlog-logrotationsynchourattribute.Set the minutes for the log rotation:
# dsconf <instance_name> logging error set rotation-tod-minute 55The command modifies the
nsslapd-errorlog-logrotationsyncminattribute.
Verification
Display the error logging settings:
# dsconf <instance_name> logging error getError Log Configuration ---------------------------------------------- ... Max log size = 90 Max logs = 3 Rotation interval = 5 Rotation interval unit = day TOD rotation enabled = on TOD rotation hour = 22 TOD rotation minute = 55 ...
8.3.4.2. Configuring a log rotation policy using the web console
To periodically archive the current log file and create a new one, set a log file rotation policy by using the web console.
Prerequisites
- You are logged in to the web console.
Procedure
- Select the instance.
Navigate to
and select the log type, for example, Error Log.The Error Log Settings page opens.
- Click the Rotation Policy tab.
Configure rotation policy parameters. For example, set maximum 3 log files, the log size maximum 110 MB, and creation of a new log file every 3 days.
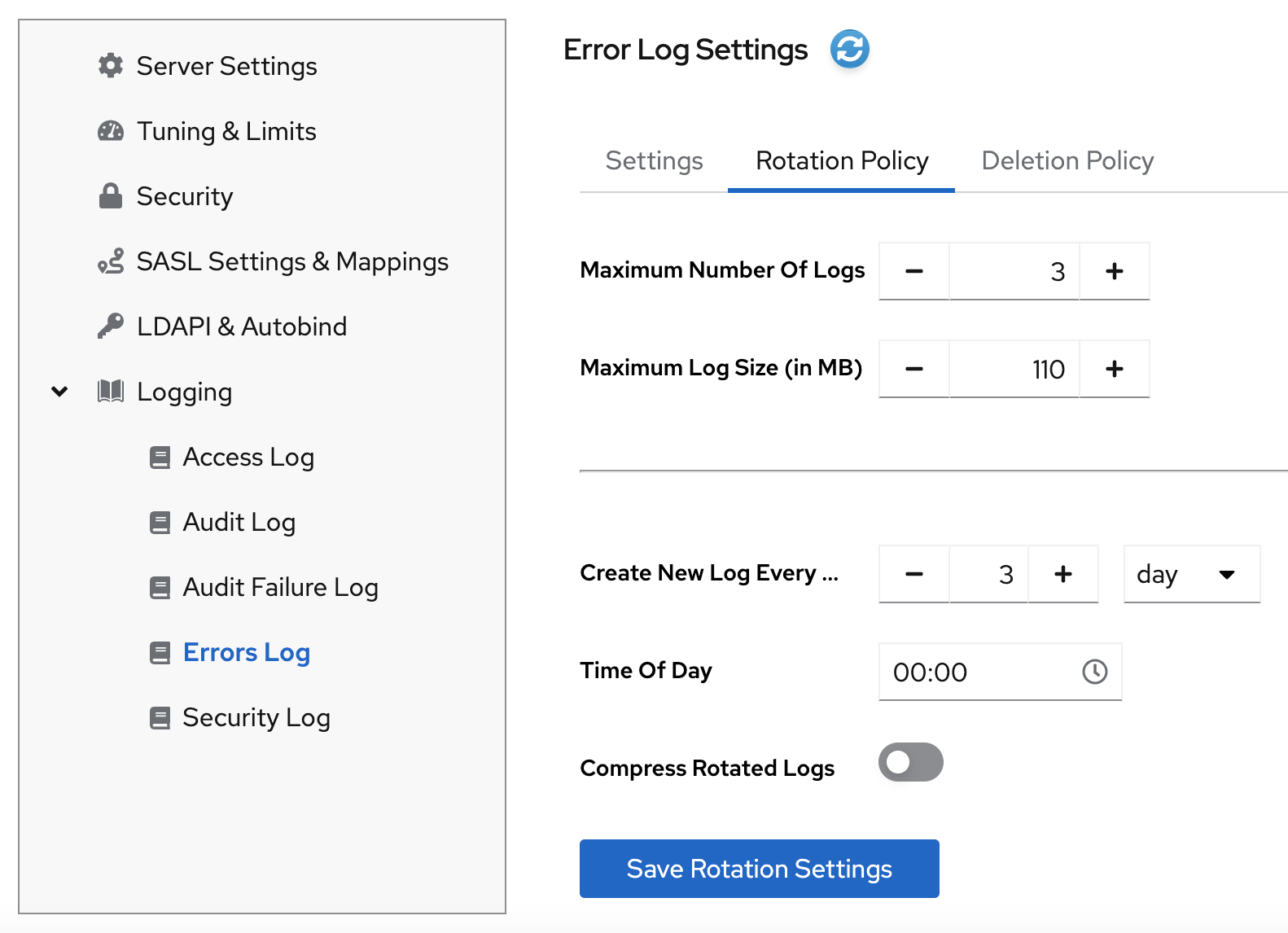
- Click the button to apply changes.
8.3.5. Defining a log deletion policy
Directory Server automatically deletes old archived log files if you set a deletion policy.
You can only set a log file deletion policy if you have a log file rotation policy set. Directory Server applies the deletion policy at the time of log rotation.
You can set the following configuration attributes to manage the log file deletion policy:
- Log archive exceeds (in MB)
If the size of a log file of one type exceeds the configured value, the oldest log file of this type is automatically deleted. Use the
max-disk-spaceoption of thedsconfutility or the web console to configure the corresponding setting.-
access log:
nsslapd-accesslog-logmaxdiskspace -
error log:
nsslapd-errorlog-logmaxdiskspace -
audit log:
nsslapd-auditlog-logmaxdiskspace -
auditfail log:
nsslapd-auditfaillog-logmaxdiskspace -
security log:
nsslapd-securitylog-logmaxdiskspace
-
access log:
- Free disk space (in MB)
When the free disk space reaches this value, the oldest archived log file is automatically deleted. Use the
free-disk-spaceoption of thedsconfutility or the web console to configure the corresponding setting.-
access log:
nsslapd-accesslog-logminfreediskspace -
error log:
nsslapd-errorlog-logminfreediskspace -
audit log:
nsslapd-auditlog-logminfreediskspace -
auditfail log:
nsslapd-auditfaillog-logminfreediskspace -
security log:
nsslapd-securitylog-logminfreediskspace
-
access log:
- Log file is older than
When a log file is older than the configured time, it is automatically deleted. Use the
deletion-intervalanddeletion-interval-unitoptions of thedsconfutility or the web console to configure the corresponding setting.-
access log:
nsslapd-accesslog-logexpirationtimeandnsslapd-accesslog-logexpirationtimeunit -
error log:
nsslapd-errorlog-logexpirationtimeandnsslapd-errorlog-logexpirationtimeunit -
audit log:
nsslapd-auditlog-logexpirationtimeandnsslapd-auditlog-logexpirationtimeunit -
audit log:
nsslapd-auditfaillog-logexpirationtimeandnsslapd-auditfaillog-logexpirationtimeunit -
security log:
nsslapd-securitylog-logexpirationtimeandnsslapd-securitylog-logexpirationtimeunit
-
access log:
For details about the log configuration settings, see Core server configuration attributes description.
8.3.5.1. Configuring a log deletion policy using the command line
You can change the default log deletion settings.
For example, you want Directory Server to delete old access logs in the following situations:
- The total size of all access log files exceeds 500 MB.
- An access log file is older that 3 weeks.
Procedure
Set the maximum amount of disk space in megabytes that the access logs are allowed to consume:
# dsconf <instance_name> logging access set max-logsize 500The command updates the
nsslapd-accesslog-logmaxdiskspaceattribute in thecn=configconfiguration entry.Set the required deletion interval:
Provide the maximum age that a log file is allowed to reach before Directory Server deletes it:
# dsconf <instance_name> logging access set deletion-interval 3The command modifies the
nsslapd-accesslog-logexpirationtimeattribute.Provide the units for the log maximum age (
month,week,day):# dsconf <instance_name> logging access set deletion-interval-unit weekThe command modifies the
nsslapd-accesslog-logexpirationtimeunitattribute.
Verification
Display the access logging settings:
# dsconf <instance_name> logging access getAccess Log Configuration -------------------------------------- ... Deletion interval = 3 Deletion interval unit = week ... Max log size = 500 ...
8.3.5.2. Configuring a log deletion policy using the web console
To automatically delete old archived log files, set a log deletion policy by using the web console.
Prerequisites
- You are logged in to the web console.
Procedure
- Select the instance.
-
Navigate to
and select the log type, for example, Access Log. The Access Log Settings page opens. - Click the Deletion Policy tab.
Configure deletion policy parameters. For example, set maximum archive size to 600 MB and the log file age to 3 weeks.
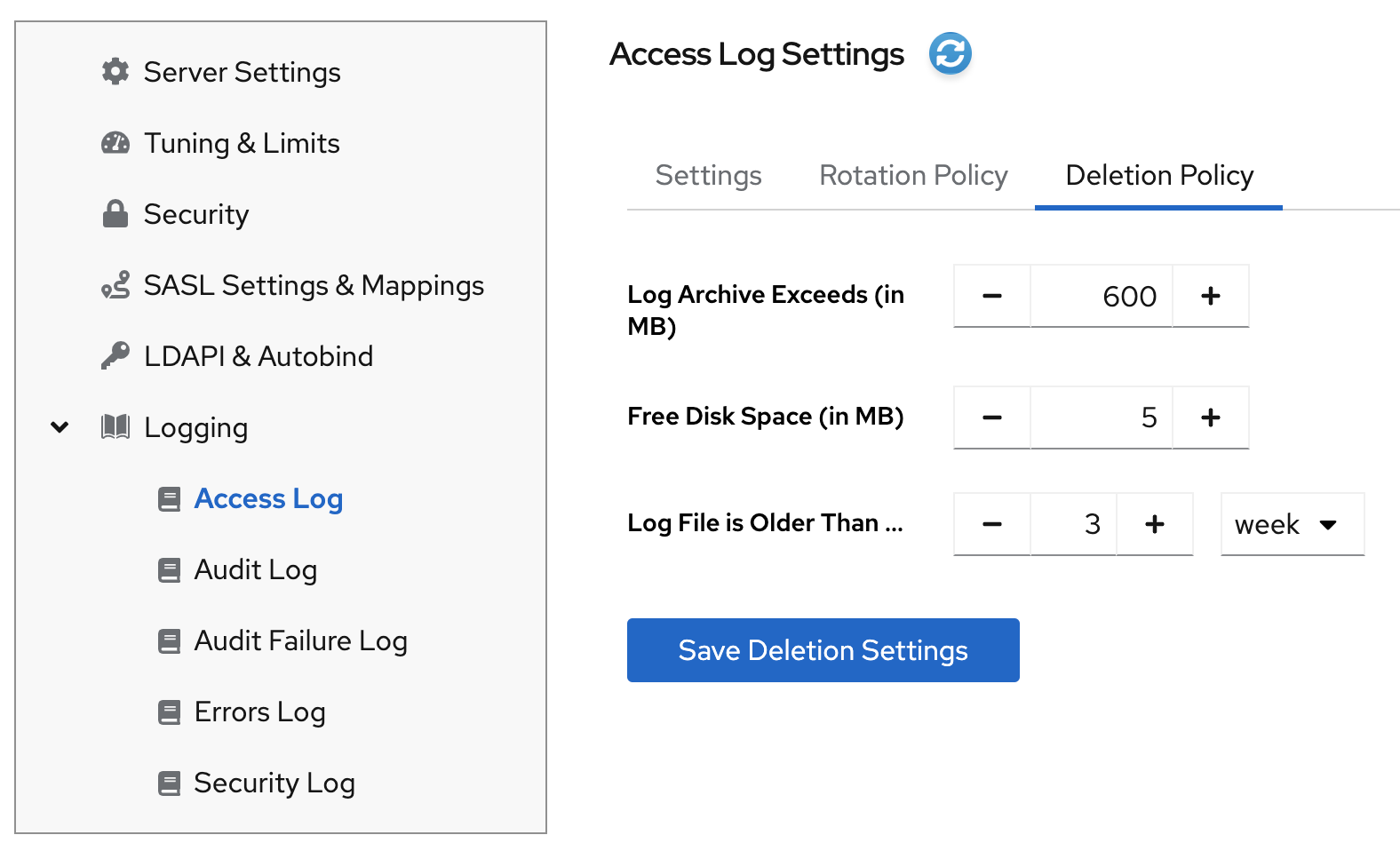
- Click the button to apply changes.
8.3.6. Manual log file rotation
You can rotate log files manually only if you did not configure an automatic log file rotation or deletion policies.
Procedure
Stop the instance:
# dsctl <instance_name> stop-
Go to the log files directory. By default, Directory Server stores access, error, audit, audit fail log, and security files in the
/var/log/dirsrv/slapd-<instance_name>/directory. - Move or rename the log file you want to rotate to make it available for future reference.
Start the instance:
# dsctl <instance_name> restart
8.3.7. Configuring format of Directory Server log files
Use the command line to customize the access, error, audit, and audit fail logging format. Directory Server supports the following logging format:
- Default (original plain text)
- JSON
- JSON (pretty)
Note that when you switch to a new logging format, Directory Server rotates the current log.
The security logs are only available in the JSON format.
Prerequisites
- You have root permissions.
Procedure
Configure the desired format of Directory Server log files. For example, to make logging more consumable by standard parsing tools, set the log format to JSON:
To set the format for the access logging, run:
# dsconf <instance_name> logging access set log-format jsonThe command sets the
nsslapd-accesslog-log-formatattribute tojson. For details about the attribute, see the nsslapd-accesslog-log-format description in the reference documentation.To set the format for the error logging, run:
# dsconf <instance_name> logging error set log-format jsonThe command sets the
nsslapd-errorlog-json-formatattribute tojson. For details about the attribute, see the nsslapd-errorlog-json-format description in the reference documentation.To set the format for the audit and audit fail logging, run:
# dsconf <instance_name> logging audit set log-format jsonThe command sets the
nsslapd-auditlog-log-formatattribute tojson. For details about the attribute, see the nsslapd-auditlog-log-format description in the reference documentation.
Optional: If you do not want the default
%FT%Tformat (2025-11-31T17:25:01), customize the timestamps format in a log. For example, you want the%DT%T(11/31/25T17:25:01) format for the timestamps in the access logs:# dsconf <instance_name> logging access set time-format %DT%TThe command sets the
nsslapd-accesslog-time-formatattributes to%DT%T.
Verification
Display logging details by using the
dsconf logging <log_file_type> getcommand. For example, display the access logging details:# dsconf <instance_name> logging access getAccess Log Configuration ------------------------------------------------ ... Logging format = json ... Time format for JSON logging (strftime) = %FT%T
8.3.8. Configuring log levels
To manage how detailed logs are, and therefore the amount of information that is logged, you can specify log levels for access and error logging.
Changing the default log level can lead to very large log files. Red Hat recommends that you do not change the default logging values without being asked to do so by Red Hat technical support.
8.3.8.1. Configuring log levels using the command line
You can adjust access and error log levels for debugging purposes.
Prerequisites
- You enabled access and error logging.
Procedure
To modify log levels for the access logs:
Optional: List available access log levels:
# dsconf <instance_name> logging access list-levelsLevel Description ------------------------------------------ entry Log entry and referral stats default Standard access logging internal Log internal operationsSet the required logging level. For example, you want the access log to contain internal access operations and the default logging:
# dsconf <instance_name> logging access set level default internalThe command modifies the
nsslapd-accesslog-levelattribute in thecn=configconfiguration entry.
To modify log levels for the error logs:
Optional: List available error log levels:
# dsconf <instance_name> logging error list-levelsLevel Description ---------------------------------------------- acl Provides very detailed access control list processing information aclsumary Summarizes information about access to the server, much less verbose than level 'acl' backend Backend debug logging ber Logs the number of packets sent and received by the server cache Database entry cache logging config Prints any .conf configuration files used with the server, line by line, when the server is started connection Logs the current connection status, including the connection methods used for a SASL bind default Default logging level filter Logs all of the functions called by a search operation heavytrace Logs when the server enters and exits a function, with additional debugging messages house Logging for housekeeping thread packet Network packet logging parse Logs schema parsing debugging information plugin Plugin logging pwpolicy Debug information about password policy behavior replication Debug replication logging shell Special authentication/connection tracking trace Logs a message when the server enters and exits a functionSet the required logging level. For example, you want the error log to contain search filter logging, the default logging, and config file processing:
# dsconf <instance_name> logging error set level default filter configThe command modifies the
nsslapd-errorlog-levelattribute in thecn=configconfiguration entry.
Verification
When you set the access log level to internal, do the following steps to see if Directory Server started to log internal access events:
Optional: Display the access log configuration:
# dsconf <instance_name> logging access getAccess Log Configuration --------------------------------- ... Log level = default,internal ...Restart the instance to trigger internal events by command:
# dsctl <instance_name> restartView the access log file and find internal operation records:
# cat /var/log/dirsrv/slapd-<instance_name>/access ... [time_stamp] conn=2 (Internal) op=1(1)(1) SRCH base="cn=config,cn=WritersData,cn=ldbm database,cn=plugins,cn=config" scope=1 filter="objectclass=vlvsearch" attrs=ALL [time_stamp] conn=2 (Internal) op=1(1)(1) RESULT err=0 tag=48 nentries=0 wtime=0.000016828 optime=0.000274854 etime=0.000288952 ...
8.3.8.2. Configuring log levels using the web console
To manage how detailed logs are, specify log levels for access logging and error logging.
Prerequisites
- You are logged in to the web console.
- You enabled access and error logging.
Procedure
- Select the instance.
-
Navigate to
. -
Select the log type, for example,
Access Log. Click the button to see all available log levels for the log type.
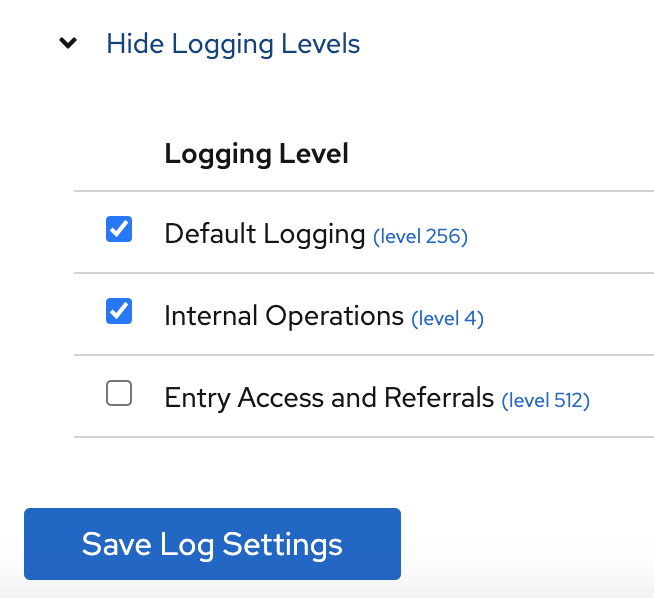
-
Select log levels, for example,
Default LoggingandInternal Operationslevels. - Click the button to apply changes.
Verification
To see if Directory Server started to log internal access events, do the following:
- Restart the instance by clicking button and then selecting . Directory Server restarts the instance and generates internal events.
-
Navigate to
. Refresh access log and view recorded internal events:
[time_stamp] conn=6 (Internal) op=1(2)(1) SRCH base="cn=config,cn=Example database,cn=ldbm database,cn=plugins,cn=config" scope=1 filter="objectclass=vlvsearch" attrs=ALL [time_stamp] conn=6 (Internal) op=1(2)(1) RESULT err=0 tag=48 nentries=0 wtime=0.000004563 optime=0.000078000 etime=0.000081911
8.3.9. Configuring logging for plug-ins
By default, Directory Server does not log internal events which plug-ins initiate. To debug plug-in operations, you can enable access and audit logging for all plug-ins, or for specific plug-ins.
8.3.9.1. Configuring logging for all plug-ins
Use nsslapd-plugin-logging attribute to configure logging for all plug-ins.
Procedure
To enable access and audit logging for all plug-ins, use the following command:
# dsconf <instance_name> config replace nsslapd-plugin-logging=on
8.3.9.2. Configuring logging for a specific plugin
Use nsslapd-logAccess and nsslapd-logAudit attributes to configure logging for a plug-in.
Prerequisites
-
The
nsslapd-accesslogattribute contains valid path and the filename for the access log file. -
The
nsslapd-auditlogattribute contains valid path and the filename for the audit log file.
Procedure
To enable access and audit logging for a specific plug-in, modify
nsslapd-logAccessandnsslapd-logAuditattributes using the LDAP interface:# ldapmodify -D "cn=Directory Manager" -W -x -H ldap://server.example.com dn: cn=MemberOf Plugin,cn=plugins,cn=config changetype: modify replace: nsslapd-logAccess nsslapd-logAccess: on dn: cn=MemberOf Plugin,cn=plugins,cn=config changetype: modify replace: nsslapd-logAudit nsslapd-logAudit: on
8.3.10. Logging statistics per search operation
During some search operations, especially with filters such as (cn=user*), the time the server spends for receiving the tasks and then sending the result back (etime) can be very long.
Expanding the access log with information related to indexes used during search operation helps to diagnose why etime value is resource expensive.
Use the nsslapd-statlog-level attribute to enable collecting statistics, such as a number of index lookups (database read operations) and overall duration of index lookups for each search operation, with minimal impact on the server.
Prerequisites
- You enabled access logging.
Procedure
Enable search operation metrics:
# dsconf <instance_name> config replace nsslapd-statlog-level=1Restart the instance:
# dsctl <instance_name> restart
Verification
Perform a search operation:
# ldapsearch -D "cn=Directory Manager" -H ldap://server.example.com -b "dc=example,dc=com" -s sub -x "cn=user*"View the access log file and find the search statistics records:
# cat /var/log/dirsrv/slapd-<instance_name>/access ... [16/Nov/2022:11:34:11.834135997 +0100] conn=1 op=73 SRCH base="dc=example,dc=com" scope=2 filter="(cn=user)"* attrs=ALL [16/Nov/2022:11:34:11.835750508 +0100] conn=1 op=73 STAT read index: attribute=objectclass key(eq)=referral --> count 0 [16/Nov/2022:11:34:11.836648697 +0100] conn=1 op=73 STAT read index: attribute=cn key(sub)=er_ --> count 25 [16/Nov/2022:11:34:11.837538489 +0100] conn=1 op=73 STAT read index: attribute=cn key(sub)=ser --> count 25 [16/Nov/2022:11:34:11.838814948 +0100] conn=1 op=73 STAT read index: attribute=cn key(sub)=use --> count 25 [16/Nov/2022:11:34:11.841241531 +0100] conn=1 op=73 STAT read index: attribute=cn key(sub)=^us --> count 25 [16/Nov/2022:11:34:11.842230318 +0100] conn=1 op=73 STAT read index: duration 0.000010276 [16/Nov/2022:11:34:11.843185322 +0100] conn=1 op=73 RESULT err=0 tag=101 nentries=24 wtime=0.000078414 optime=0.001614101 etime=0.001690742 ...
8.3.11. Compressing log files
To save disc space, you can enable log file compression that compresses archived logs into .gzip files.
By default, Directory Server compresses only archived security log files.
Procedure
To enable log file compression, for example, for the access logs, run:
# dsconf <instance_name> logging access set compress-enabledThe command sets the
nsslapd-accesslog-compressattribute toon.To disable log file compression, for example, for the error logs, run:
# dsconf <instance_name> logging error set compress-disabledThe command sets the
nsslapd-errorlog-compressattribute tooff.
Verification
Display the access logging settings:
# dsconf <instance_name> logging access getAccess Log Configuration --------------------------------- ... Compression enabled = on ...Check that the log file directory contains compressed logs files:
# ls /var/log/dirsrv/slapd-instance_name/*
8.3.12. Disabling log buffering for debugging purposes
For debugging purposes, you can disable log buffering, which is enabled by default for the access, audit, and audit fail logs. With log buffering disabled, Directory Server writes log entries directly to the disk.
Do not disable access logging in a normal operating environment. When you disable the buffering of an active log, Directory Server performance decreases, especially under heavy load.
8.3.12.1. Disabling log buffering using the command line
Use the dsconf utility to disable Directory Server log buffering. When log buffering is disabled, Directory Server writes log entries directly to the disk.
The following procedure disables the access and audit log buffering.
Procedure
To disable the access log buffering, enter:
# dsconf <instance_name> logging access set buffering-disabledThe command sets the
nsslapd-accesslog-logbufferingattribute tooff.To disable the audit log buffering, enter:
# dsconf <instance_name> logging audit set buffering-disabledThe command sets the
nsslapd-auditlog-logbufferingattribute tooff.NoteBoth the audit and audit fail logs use the
nsslapd-auditlog-logbufferingattribute for the buffering configuration. Therefore, when you disable buffering for the audit logging, Directory Server also disables the audit fail logs buffering.
Verification
Display the access logging settings:
# dsconf <instance_name> logging access getAccess Log Configuration --------------------------------- ... Buffering enabled = off ...Display the access log in continuous mode:
# tail -f /var/log/dirsrv/slapd-<instance_name>/access- Perform actions in the directory, such as searches.
- Monitor the access log. Log entries appear without delay at the moment when users perform actions in the directory.
8.3.12.2. Disabling log buffering using the web console
Use the web console to disable Directory Server log buffering. When log buffering is disabled, Directory Server writes log entries directly to the disk.
The following procedure disables the access log buffering.
Procedure
-
Navigate to
. -
Deselect
Access Log Buffering Enabled. Click .
NoteTo disable the audit fail log buffering, disable buffering for the the audit log on the
tab.
Verification
-
Navigate to
. -
Select
Continuously Refresh. - Perform actions in the directory, such as searches.
- Monitor the access log. Log entries appear without delay at the moment when users perform actions in the directory.
8.4. Monitoring the replication topology
Use the command line of the web console to monitor the replication topology.
8.4.1. Monitoring the replication topology using the command line
To monitor the state of the directory data replication between suppliers, consumers, and hubs, you can use replication topology report that provides information on the replication progress, replica IDs, number of changes, and other parameters. To generate the report faster and make it more readable, you can configure your own credentials and aliases.
8.4.1.1. Displaying a replication topology report using the command line
To view overall information about the replication status for each agreement in your replication topology, you can display the replication topology report. To do so, use the dsconf replication monitor command.
Prerequisites
- The host is a member of replication topology.
- You initialized the consumers.
Procedure
To view a replication topology report, enter:
# dsconf <instance_name> replication monitorThe
dsconfutility will request authentication credentials for each instance in the topology:Enter password for cn=Directory Manager on ldap://supplier.example.com: password Enter a bind DN for consumer.example.com:389: cn=Directory Manager Enter a password for cn=Directory Manager on consumer.example.com:389: password Supplier: server.example.com:389 -------------------------------- Replica Root: dc=example,dc=com Replica ID: 1 Replica Status: Online Max CSN: 5e3acb77001d00010000 Status For Agreement: "example-agreement" (consumer.example.com:1389) Replica Enabled: on Update In Progress: FALSE Last Update Start: 20211209122116Z Last Update End: 20211209122116Z Number Of Changes Sent: 1:21/0 Number Of Changes Skipped: None Last Update Status: Error (0) Replica acquired successfully: Incremental update succeeded Last Init Start: 20211209122111Z Last Init End: 20211209122114Z Last Init Status: Error (0) Total update succeeded Reap Active: 0 Replication Status: In Synchronization Replication Lag Time: 00:00:00 Supplier: consumer.example.com:1389 ----------------------------------- Replica Root: dc=example,dc=com Replica ID: 65535 Replica Status: Online Max CSN: 00000000000000000000
8.4.1.2. Setting credentials for replication monitoring in the .dsrc file
By default, the dsconf replication monitor command asks for bind DNs and passwords when authenticating to remote instances. To generate the report faster and easier in the future, you can set the bind DNs, and optionally passwords, for each server in the topology in the user’s ~/.dsrc file.
Prerequisites
- The host is a member of replication topology.
- You initialized the consumers.
Procedure
-
Optional: Create the
~/.dsrcfile. In the
~/.dsrcfile, set the bind DNs, and passwords. For example:[repl-monitor-connections] connection1 = server1.example.com:389:cn=Directory Manager:* connection2 = server2.example.com:389:cn=Directory Manager:[~/pwd.txt] connection3 = hub1.example.com:389:cn=Directory Manager:S3cretThis example uses connection1 to connection3 as keys for each entry. However, you can use any unique key.
When you run the
dsconf replication monitorcommand, thedsconfutility connects to all servers configured in replication agreements of the instance. If the utility finds the hostname in~/.dsrc, it uses the defined credentials to authenticate to the remote server. In the example above,dsconfuses the following credentials when connecting to a server:Expand Hostname Bind DN Password setup method server1.example.com
cn=Directory Manager
Requests the password
server2.example.com
cn=Directory Manager
Reads the password from
~/pwd.txthub1.example.com
cn=Directory Manager
S3cret
Verification
-
Run the
dsconf replication monitorcommand to see Ifdsconfutility uses credentials configured in the~/.dsrcfile. For more information, see Displaying a replication topology report using the command.
8.4.1.3. Using aliases in the replication topology monitoring output
To make the report more readable, you can set your own aliases that will be displayed in the report output. By default, the replication monitoring report contains the hostnames of remote servers.
Prerequisites
- The host is a member of replication topology.
- You initialized the consumers.
Procedure
If you want to see aliases in the report, use one of the following methods:
Define the aliases in the
~/.dsrcfile:[repl-monitor-aliases] M1 = server1.example.com:389 M2 = server2.example.com:389Define the aliases by passing the
-a alias=host_name:portparameter to thedsconf replication monitorcommand:# dsconf <instance_name> replication monitor -a M1=server1.example.com:389 M2=server2.example.com:389In both cases, the
dsconf replication monitorcommand displays the alias in the output:... Supplier: M1 (server1.example.com:389) -------------------------------- Replica Root: dc=example,dc=com ... Supplier: M2 (server2.example.com:389) -------------------------------- Replica Root: dc=example,dc=com
8.4.2. Monitoring the replication topology using the web console
To monitor the state of the directory data replication between suppliers, consumers, and hubs, you can use replication topology report that provides information on the replication progress, replica IDs, number of changes, and other parameters. To generate the report faster and make it more readable, you can configure your own credentials and aliases.
8.4.2.1. Displaying a replication topology report using the web console
To view overall information about the replication status for each agreement in your replication topology, you can display the replication topology report.
Prerequisites
- The host is a member of replication topology.
- You initialized the consumers.
- You are logged in to the web console.
Procedure
-
Navigate to
. The page opens. - Click .
Enter the passwords for login to remote instances and click . Directory Server uses bind DNs values from existing replication agreements.
The replication topology report will be generated on the tab.
NoteTo generate another replication topology report, go to the tab.
8.4.2.2. Setting credentials for replication monitoring using the web console
To generate the replication topology report faster and easier, you can set your own bind DNs, and optionally passwords, for each server in the topology for authentication. In this case, you do not need to confirm replication credentials each time you want to generate a replication topology report. By default, Directory Server takes these credentials from existing replication agreements.
Prerequisites
- The host is a member of replication topology.
- You initialized the consumer.
- You are logged in to the web console.
Procedure
-
Navigate to
. The page opens. - Click .
Enter replication login credentials you want to use for authentication to remote instances:
-
Hostname. A remote instance hostname you want the server to authenticate to. -
Port. A remote instance port. -
Bind DN. Bind DN used for authentication to the remote instance. -
Password. A password used for authentication. -
Interactive Input. If checked, Directory Server will ask for a password every time you generate a replication topology report.
-
- Click .
Verification
- Generate the replication topology report to see If the report asks for the credentials. For more information, see Displaying a replication topology report using the web console.
8.4.2.3. Configuring replication naming aliases using the web console
To make the report more readable, you can set your own aliases that will be displayed in the report output. By default, the replication monitoring report contains the hostnames of servers.
Prerequisites
- The host is a member of replication topology.
- You initialized the consumers.
- You are logged in to the web console.
Procedure
-
Navigate to
. - Click .
Enter alias details:
-
Alias. An alias that will be displayed in the replication topology report. -
Hostname. An instance hostname. -
Port. An instance port.
-
- Click .
Verification
- Generate the replication topology report to see If the report uses new aliases. For more information, see Displaying a replication topology report using the web console.
8.5. Tracking the bind DN for plug-in-initiated updates
In Directory Server, you can track which user performed an action that caused a plug-in to update an entry. If the tracking is enabled and a plug-in changes an entry as a consequence of an action performed by a user, you can see the user’s name in the modifiersname attribute of updated entry.
8.5.1. Tracking user information for entry modifications performed by a plug-in
When the user performs an action that changes an entry, it can trigger other, automatic changes across the directory tree. By default, Directory Server is not tracking the name of the user who performed the action that has initiated the data modification. To track the user information, you can use the nsslapd-plugin-binddn-tracking parameter.
For example, when the administrator deletes a user, the Referential Integrity Postoperation plug-in automatically removes the user from all groups. You can see the initial action in the entry as being performed by the user account bound to the server. But all related updates are, by default, shown as being performed by the plug-in, with no information about which user initiated the update.
A second example might be using the MemberOf plug-in to update user entries with group membership. The update to the group account is shown as being performed by the bound user, while the edit to the user entry is shown as being performed by the MemberOf plug-in:
dn: cn=example_group,ou=groups,dc=example,dc=com
modifiersname: uid=example,ou=people,dc=example,dc=com
dn: uid=example,ou=people,dc=example,dc=com
modifiersname: cn=MemberOf Plugin,cn=plugins,cn=config
The nsslapd-plugin-binddn-tracking parameter enables the server to track which user originated an update operation, as well as the internal plug-in which actually performed the operation. The bound user is shown in the modifiersname and creatorsname operational attributes, while the plug-in which performed the update is shown in the internalModifiersname and internalCreatorsname operational attributes. For example:
dn: uid=example,ou=people,dc=example,dc=com
modifiersname: uid=admin,ou=people,dc=example,dc=com
internalModifiersname: cn=MemberOf Plugin,cn=plugins,cn=config
The nsslapd-plugin-binddn-tracking parameter tracks and maintains the relationship between the bound user and all updates performed for that connection.
The internalModifiersname and internalCreatorsname attributes always show a plug-in as the identity. The value of the attribute is:
-
cn=ldbm database,cn=plugins,cn=configwhen the core Directory Server performs the change -
cn=the DN of the plug-in,cn=plugins,cn=configwhen a plug-in changed the entry
8.5.2. Enabling tracking the bind DN for plug-in-initiated updates using the command line
For data updates initiated by a plug-in, you often need to know which user has performed the action that led to the update. In the command line, set up the nsslapd-plugin-binddn-tracking parameter to track such user information.
Procedure
Set the
nsslapd-plugin-binddn-trackingparameter toon:# dsconf <instance_name> config replace nsslapd-plugin-binddn-tracking=on
Verification
-
Display the
modifiersnameandinternalModifiersnameattributes of an entry that was changed by a plug-in. For example, if thememberOfattribute is enabled, display the attributes of a user after you added the user to a group:
# ldapsearch -D "cn=Directory Manager" -W -H ldap://server.example.com -x -b "uid=example-user,ou=People,dc=example,dc=com" -s base -x internalModifiersname -x modifiersname
dn: uid=example-user,ou=people,dc=example,dc=com
modifiersname: uid=admin,ou=people,dc=example,dc=com
internalModifiersname: cn=MemberOf Plugin,cn=plugins,cn=config8.5.3. Enabling tracking the bind DN for plug-in-initiated updates using the web console
For data updates initiated by a plug-in, you often need to know which user has performed the action that led to the update. Using the web console, you can enable tracking of the user information.
Prerequisites
- You are logged in to the Directory Server instance in the web console.
Procedure
-
Open the
menu. -
On the Advanced Settings tab, select
Enable Plugin Bind DN Tracking. - Click .
Verification
-
Display the
modifiersnameandinternalModifiersnameattributes of an entry that was changed by a plug-in. For example, if thememberOfattribute is enabled, display the attributes of a user after you added the user to a group:
# ldapsearch -D "cn=Directory Manager" -W -H ldap://server.example.com -x -b "uid=example-user,ou=People,dc=example,dc=com" -s base -x internalModifiersname -x modifiersname
dn: uid=example-user,ou=people,dc=example,dc=com
modifiersname: uid=admin,ou=people,dc=example,dc=com
internalModifiersname: cn=MemberOf Plugin,cn=plugins,cn=config8.6. Monitoring the database activity
Administrators should monitor the database activity to ensure that tuning settings, such as caches, are properly configured.
8.6.1. Monitoring the database activity using the command line
To display the monitoring activity using the command line, display the dynamically-updated read-only attributes stored in the cn=monitor,cn=database_name,cn=ldbm database,cn=plugins,cn=config.
Procedure
To display the current activity of a database, enter:
# dsconf <instance_name> monitor backend userRootThis command displays the activity of the
userRootdatabase.
8.6.2. Monitoring the database activity using the web console
In the web console, Directory Server displays the values of the dynamically-updated read-only monitoring attributes from the cn=monitor,cn=database_name,cn=ldbm database,cn=plugins,cn=config in the `Monitoring´ tab.
Procedure
-
Navigate to
. - Display the cache values on the Entry Cache and DN Cache tabs.
8.6.3. Database monitoring attributes
| Attribute | Description |
|---|---|
|
|
Indicates whether the database is in read-only mode ( |
|
| The total number of successful entry cache lookups. The value is the total number of times the server could retrieve an entry from the entry cache without reloading it from the database. |
|
| The total number of entry cache lookups since you started the instance. The value is the total number, since the instance has been started, Directory Server tried to retrieve entry from the entry cache. |
|
| The number of entry cache tries to successful entry cache lookups. This number is based on the total lookups and hits since you last started the instance. The closer the entry cache hit ratio is to 100%, the better. Whenever an operation attempts to find an entry that is not present in the entry cache, the server needs to access the database to obtain the entry. Thus, as this ratio drops towards zero, the number of disk accesses increases, and directory search performance decreases. To improve this ratio, increase the size of the entry cache of the database.
To improve this ratio, increase the size of the entry cache by increasing the value of the |
|
| The total size, in bytes, of directory entries currently present in the entry cache.
To increase the size of the entries which can be present in the cache, increase the value of the |
|
| The maximum size, in bytes, of directory entries that Directory Server can maintain in the entry cache.
To increase the size of the entries which can be present in the cache, increase the value of the |
|
| The current number of entries stored in the entry cache of a given backend. |
|
| The maximum number of entries stored in the entry cache of a database.
To tune this value, increase the value of the |
|
| The number of times the server could process a request by obtaining a normalized distinguished name (DN) from the DN cache rather than normalizing it again. |
|
| The total number of DN cache accesses since you started the instance. |
|
| The ratio of cache tries to successful DN cache hits. The closer this value is to 100%, the better. |
|
| The total size, in bytes, of DN currently present in the DN cache.
To increase the size of the entries which can be present in the DN cache, increase the value of the |
|
| The maximum size, in bytes, of DNs that Directory Server can maintain in the DN cache.
To increase the size of the entries which can be present in the cache, increase the value of the |
|
| The number of DNs currently present in the DN cache. |
|
| The maximum number of DNs allowed in the DN cache. |
8.7. Getting Directory Server access log using the command line
The logconv.pl command analyzes Directory Server access logs, extracts usage statistics, and counts occurrences of significant events specified on the command line. The logconv.pl command prints a list of total operations, total number of connections, counts per each operation type, counts for some extended operations like persistent searches, and bind information.
The logconv.pl command has the following syntax:
# logconv.pl /path/to/accesslogTo analyze multiple access log files, you can use the following format with an asterisk (*):
# logconv.pl /var/log/dirsrv/slapd-<instance_name>/access*
The logconv.pl command generates following three types of statistics that are useful for monitoring the Directory Server and optimizing Directory Server configuration:
- Counts of events, such as total binds and total searches performed.
-
Lists of the most frequently occurring parameters in LDAP requests. For example, the
logconv.plcommand generates lists of the top ten bind DNs, base DNs, filter strings, and attributes returned. -
Counts of occurrences for error codes such as those defined in
ldap.h.
8.7.1. Analyzing Directory Server access logs using the command line
The logconv.pl command analyzes Directory Server access logs and extracts usage statistics and counts occurrences of significant events.
The logconv.pl takes following options:
-
-S: specifies the time to begin the log file analysis. -
-E: specifies the time to stop the log files analysis. -
-bc: generates a report based on the number of DNs used to connect to the server and the total connection codes the server returns. -
-m: generates output data per second (-m) to a specified CSV output file. -
-M: generates output data with counts per minute (-M) to a specified CSV output file.
Procedure
To generate a simple access log summary, run the following command:
# logconv.pl /var/log/dirsrv/slapd-<instance_name>/access Access Log Analyzer 8.2 Command: logconv.pl /var/log/dirsrv/slapd-<instance_name>/access Processing 1 Access Log(s)... [001] /var/log/dirsrv/slapd-<instance_name>/access size(bytes):77532 Total Log Lines Analysed: 527 Start of Logs: 14/Oct/2017:16:15:22.452909568 End of Logs: 14/Oct/2017:16:39:50.157790196 Processed Log Time: 0 Hours, 24 Minutes, 27.704877056 Seconds Restarts: 10 Secure Protocol Versions: - TLS1.2 client bound as uid=user_name,ou=people,o=example.com (11 connections) - TLS1.2 128-bit AES; client CN=CA Subsystem,O=example.com; issuer CN=Certificate Authority,O=example.com (11 connections) - TLS1.2 128-bit AES-GCM (2 connections) - TLS1.2 128-bit AES (3 connections) Peak Concurrent Connections: 38 Total Operations: 4771 Total Results: 4653 Overall Performance: 97.5% Total Connections: 249 (0.17/sec) (10.18/min) - LDAP Connections: 107 (0.07/sec) (4.37/min) - LDAPI Connections: 128 (0.09/sec) (5.23/min) - LDAPS Connections: 14 (0.01/sec) (0.57/min) - StartTLS Extended Ops: 2 (0.00/sec) (0.08/min) Searches: 2963 (2.02/sec) (121.13/min) Modifications: 649 (0.44/sec) (26.53/min) Adds: 785 (0.53/sec) (32.09/min) Deletes: 10 (0.01/sec) (0.41/min) Mod RDNs: 6 (0.00/sec) (0.25/min) Compares: 0 (0.00/sec) (0.00/min) Binds: 324 (0.22/sec) (13.25/min) Proxied Auth Operations: 0 Persistent Searches: 17 Internal Operations: 0 Entry Operations: 0 Extended Operations: 4 Abandoned Requests: 0 Smart Referrals Received: 0 VLV Operations: 30 VLV Unindexed Searches: 0 VLV Unindexed Components: 20 SORT Operations: 22 Entire Search Base Queries: 12 Paged Searches: 2 Unindexed Searches: 0 Unindexed Components: 149 FDs Taken: 249 FDs Returned: 212 Highest FD Taken: 107 Broken Pipes: 0 Connections Reset By Peer: 0 Resource Unavailable: 0 Max BER Size Exceeded: 0 Binds: 324 Unbinds: 155 --------------------------------- - LDAP v2 Binds: 41 - LDAP v3 Binds: 180 - AUTOBINDs(LDAPI): 103 - SSL Client Binds: 0 - Failed SSL Client Binds: 0 - SASL Binds: 134 - EXTERNAL: 114 - GSSAPI: 20 - Directory Manager Binds: 10 - Anonymous Binds: 1 Cleaning up temp files... Done.The
logconv.plscript prints a list of total operations, total number of connections, counts per each operation type, counts for some extended operations like persistent searches, and bind information.Optional: If you must enable additional connection summaries passed as a single option, such as the number of DNs used to connect to the server (
b) and the total connection codes the server (c) returns, specify the-bcoption as follows:# lotgconv.pl -bc /var/log/dirsrv/slapd-<instance_name>/access ----- Total Connection Codes ----- U1 3 Cleanly Closed Connections B1 1 Bad Ber Tag Encountered ----- Top 20 Bind DN's ----- Number of Unique Bind DN's: 212 1801 cn=Directory Manager 1297 Anonymous Binds 311 uid=jsmith,ou=people... 87 uid=bjensen,ou=peopl... 85 uid=mreynolds,ou=peo... 69 uid=jrockford,ou=peo... 55 uid=sspencer,ou=peop...Optional: If you must enable data output for a certain start (
-S) and end time (-E) or within a specific range, run the following command# logconv.pl -S "[01/Jul/2022:16:11:47.000000000 -0400]" -E "[01/Jul/2022:17:23:08.999999999 -0400]" /var/log/dirsrv/slapd-<instance_name>/access ... ----------- Access Log Output ------------ Start of Logs: 01/Jul/2022:16:11:47 End of Logs: 01/Jul/2022:17:23:08When start and end times are set, the
logconv.plcommand first prints the time range given, then the summary for that period.Optional: If you must enable data output with counts per minute (
-M) or per second (-m), run the following command:# logconv.pl -m|-M outputFile accessLogFile