Chapter 8. Setting up a WireGuard VPN
WireGuard is a high-performance VPN that runs in the Linux kernel. It uses modern cryptography and is easier to configure than other VPN solutions. Its small codebase improves security, and for authentication and encryption, it uses keys similar to SSH.
WireGuard is provided as a Technology Preview only. Technology Preview features are not supported with Red Hat production Service Level Agreements (SLAs), might not be functionally complete, and Red Hat does not recommend using them for production. These previews provide early access to upcoming product features, enabling customers to test functionality and provide feedback during the development process.
Note that all hosts that participate in a WireGuard VPN are peers. This documentation uses the terms client to describe hosts that establish a connection and server to describe the host with the fixed hostname or IP address that the clients connect to and, optionally, route all traffic through this server.
To set up a WireGuard VPN, you must complete the following steps:
- Configure the server.
- Open the WireGuard port in the local firewall.
- Configure the clients.
WireGuard operates on the network layer (layer 3). Therefore, you cannot use DHCP and must assign static IP addresses or IPv6 global addresses to the tunnel devices on both the server and clients.
You can use WireGuard only if the Federal Information Processing Standard (FIPS) mode in RHEL is disabled.
8.1. Protocols and primitives used by WireGuard
Understanding the protocols and primitives used by WireGuard is important for evaluating its security and trustworthiness. Knowing these components enables a user to verify that the system uses modern and secure cryptographic standards.
WireGuard uses the following protocols and primitives:
- ChaCha20 for symmetric encryption, authenticated with Poly1305, using Authenticated Encryption with Associated Data (AEAD) construction
- Curve25519 for Elliptic-curve Diffie-Hellman (ECDH) key exchange
- BLAKE2s for hashing and keyed hashing
- SipHash24 for hash table keys
- HKDF for key derivation
8.2. How WireGuard uses tunnel IP addresses, public keys, and remote endpoints
WireGuard’s design tightly couples network routing with cryptographic identity, creating a Cryptokey Routing Table. This system enables the protocol to function as both a routing mechanism for outgoing traffic and an access control list for incoming packets, ensuring that only authenticated and authorized traffic is processed.
When WireGuard sends a network packet to a peer:
- WireGuard reads the destination IP from the packet and compares it to the list of allowed IP addresses in the local configuration. If the peer is not found, WireGuard drops the packet.
- If the peer is valid, WireGuard encrypts the packet using the peer’s public key.
- The sending host looks up the most recent Internet IP address of the host and sends the encrypted packet to it.
When WireGuard receives a packet:
- WireGuard decrypts the packet using the private key of the remote host.
- WireGuard reads the internal source address from the packet and looks up whether the IP is configured in the list of allowed IP addresses in the settings for the peer on the local host. If the source IP is on the allowlist, WireGuard accepts the packet. If the IP address is not on the list, WireGuard drops the packet.
8.3. Using a WireGuard client behind NAT and firewalls
WireGuard uses the UDP protocol and transmits data only when a peer sends packets. Stateful firewalls and network address translation (NAT) on routers track connections to enable a peer behind NAT or a firewall to receive packets.
To keep the connection active, WireGuard supports persistent keepalives. This means you can set an interval at which WireGuard sends keepalive packets. By default, the persistent keep-alive feature is disabled to reduce network traffic. Enable this feature on the client if you use the client in a network with NAT or if a firewall closes the connection after some time of inactivity.
Note that you cannot configure keepalive packets in WireGuard connections by using the RHEL web console. To configure this feature, edit the connection profile by using the nmcli utility.
8.4. Creating private and public keys to be used in WireGuard connections
WireGuard uses base64-encoded private and public keys to authenticate hosts to each other. Therefore, you must create the keys on each host that participates in the WireGuard VPN.
For secure connections, create different keys for each host, and ensure that you only share the public key with the remote WireGuard host. Do not use the example keys used in this documentation.
If you plan to use the RHEL web console to create a WireGuard VPN connection, you can, alternatively, generate the public and private key pairs in the web console.
Procedure
Install the
wireguard-toolspackage:# dnf install wireguard-toolsCreate a private key and a corresponding public key for the host:
# wg genkey | tee /etc/wireguard/$HOSTNAME.private.key | wg pubkey > /etc/wireguard/$HOSTNAME.public.keyYou will need the content of the key files, but not the files themselves. However, Red Hat recommends keeping the files in case that you need to remember the keys in future.
Set secure permissions on the key files:
# chmod 600 /etc/wireguard/$HOSTNAME.private.key /etc/wireguard/$HOSTNAME.public.keyDisplay the private key:
# cat /etc/wireguard/$HOSTNAME.private.key YFAnE0psgIdiAF7XR4abxiwVRnlMfeltxu10s/c4JXg=You will need the private key to configure the WireGuard connection on the local host. Do not share the private key.
Display the public key:
# cat /etc/wireguard/$HOSTNAME.public.key UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE=You will need the public key to configure the WireGuard connection on the remote host.
8.5. Configuring a WireGuard server by using nmcli
You can configure the WireGuard server by creating a connection profile in NetworkManager. Use this method to let NetworkManager manage the WireGuard connection.
This procedure assumes the following settings:
Server:
-
Private key:
YFAnE0psgIdiAF7XR4abxiwVRnlMfeltxu10s/c4JXg= -
Tunnel IPv4 address:
192.0.2.1/24 -
Tunnel IPv6 address:
2001:db8:1::1/64
-
Private key:
Client:
-
Public key:
bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= -
Tunnel IPv4 address:
192.0.2.2/24 -
Tunnel IPv6 address:
2001:db8:1::2/64
-
Public key:
Prerequisites
- You have generated the public and private key for both the server and client.
You know the following information:
- The private key of the server
- The static tunnel IP addresses and subnet masks of the client
- The public key of the client
- The static tunnel IP addresses and subnet masks of the server
Procedure
Add a NetworkManager WireGuard connection profile:
# nmcli connection add type wireguard con-name server-wg0 ifname wg0 autoconnect noThis command creates a profile named
server-wg0and assigns the virtual interfacewg0to it. To prevent the connection from starting automatically after you add it without finalizing the configuration, disable theautoconnectparameter.Set the tunnel IPv4 address and subnet mask of the server:
# nmcli connection modify server-wg0 ipv4.method manual ipv4.addresses 192.0.2.1/24Set the tunnel IPv6 address and subnet mask of the server:
# nmcli connection modify server-wg0 ipv6.method manual ipv6.addresses 2001:db8:1::1/64Add the server’s private key to the connection profile:
# nmcli connection modify server-wg0 wireguard.private-key "YFAnE0psgIdiAF7XR4abxiwVRnlMfeltxu10s/c4JXg="Set the port for incoming WireGuard connections:
# nmcli connection modify server-wg0 wireguard.listen-port 51820Always set a fixed port number on hosts that receive incoming WireGuard connections. If you do not set a port, WireGuard uses a random free port each time you activate the
wg0interface.Add peer connection configurations for each client that you want to allow to communicate with this server:
nmcli connection modify client-wg0 wireguard.peers 'bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= allowed-ips=192.0.2.2;2001:db8:1::2'The
wireguard.peersparameter defines the peer section of the client in the NetworkManager connection profile.Optional: Configure the connection to start automatically, enter:
# nmcli connection modify server-wg0 autoconnect yesReactivate the
server-wg0connection:# nmcli connection up server-wg0- If you use this host in a network with DHCP or Stateless Address Autoconfiguration (SLAAC), the connection can be vulnerable to being redirected. For details and mitigation steps, see Assigning a VPN connection to a dedicated routing table to prevent the connection from bypassing the tunnel.
Verification
Display the interface configuration of the
wg0device:# wg show wg0 interface: wg0 public key: UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= private key: (hidden) listening port: 51820 peer: bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= allowed ips: 192.0.2.2/32, 2001:db8:1::2/128To display the private key in the output, use the
WG_HIDE_KEYS=never wg show wg0command.Display the IP configuration of the
wg0device:# ip address show wg0 20: wg0: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000 link/none inet 192.0.2.1/24 brd 192.0.2.255 scope global noprefixroute wg0 valid_lft forever preferred_lft forever inet6 2001:db8:1::1/64 scope global noprefixroute valid_lft forever preferred_lft forever inet6 fe80::3ef:8863:1ce2:844/64 scope link noprefixroute valid_lft forever preferred_lft forever
8.6. Configuring a WireGuard server by using nmtui
You can configure the WireGuard server by creating a connection profile in NetworkManager. Use this method to let NetworkManager manage the WireGuard connection.
This procedure assumes the following settings:
Server:
-
Private key:
YFAnE0psgIdiAF7XR4abxiwVRnlMfeltxu10s/c4JXg= -
Tunnel IPv4 address:
192.0.2.1/24 -
Tunnel IPv6 address:
2001:db8:1::1/64
-
Private key:
Client:
-
Public key:
bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= -
Tunnel IPv4 address:
192.0.2.2/24 -
Tunnel IPv6 address:
2001:db8:1::2/64
-
Public key:
Prerequisites
- You have generated the public and private key for both the server and client.
You know the following information:
- The private key of the server
- The static tunnel IP addresses and subnet masks of the client
- The public key of the client
- The static tunnel IP addresses and subnet masks of the server
-
You installed the
NetworkManager-tuipackage.
Procedure
Start the
nmtuiapplication:# nmtui- Select Edit a connection, and press Enter.
- Select , and press Enter.
- Select the WireGuard connection type in the list, and press Enter.
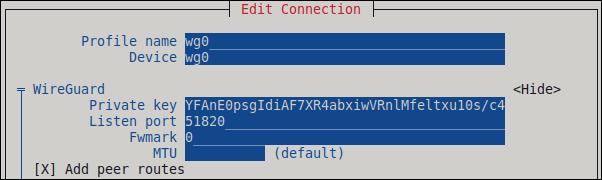
In the Edit connection window:
-
Enter the name of the connection and the virtual interface, such as
wg0, that NetworkManager should assign to the connection. - Enter the private key of the server.
Set the listen port number, such as
51820, for incoming WireGuard connections.Always set a fixed port number on hosts that receive incoming WireGuard connections. If you do not set a port, WireGuard uses a random free port each time you activate the interface.
Click next to the Peers pane:
- Enter the public key of the client.
- Set the Allowed IPs field to the tunnel IP addresses of the client that are allowed to send data to this server.
Select , and press Enter.

Select next to *IPv4 Configuration, and press Enter.
- Select the IPv4 configuration method Manual.
- Enter the tunnel IPv4 address and the subnet mask. Leave the Gateway field empty.
Select next to IPv6 Configuration, and press Enter.
- Select the IPv6 configuration method Manual.
-
Enter the tunnel IPv6 address and the subnet mask. Leave the
Gatewayfield empty.
Select , and press Enter

-
Enter the name of the connection and the virtual interface, such as
- In the window with the list of connections, select , and press Enter.
- In the NetworkManager TUI main window, select , and press Enter.
- If you use this host in a network with DHCP or Stateless Address Autoconfiguration (SLAAC), the connection can be vulnerable to being redirected. For details and mitigation steps, see Assigning a VPN connection to a dedicated routing table to prevent the connection from bypassing the tunnel.
Verification
Display the interface configuration of the
wg0device:# wg show wg0 interface: wg0 public key: UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= private key: (hidden) listening port: 51820 peer: bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= allowed ips: 192.0.2.2/32, 2001:db8:1::2/128To display the private key in the output, use the
WG_HIDE_KEYS=never wg show wg0command.Display the IP configuration of the
wg0device:# ip address show wg0 20: wg0: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000 link/none inet 192.0.2.1/24 brd 192.0.2.255 scope global noprefixroute wg0 valid_lft forever preferred_lft forever inet6 _2001:db8:1::1/64 scope global noprefixroute valid_lft forever preferred_lft forever inet6 fe80::3ef:8863:1ce2:844/64 scope link noprefixroute valid_lft forever preferred_lft forever
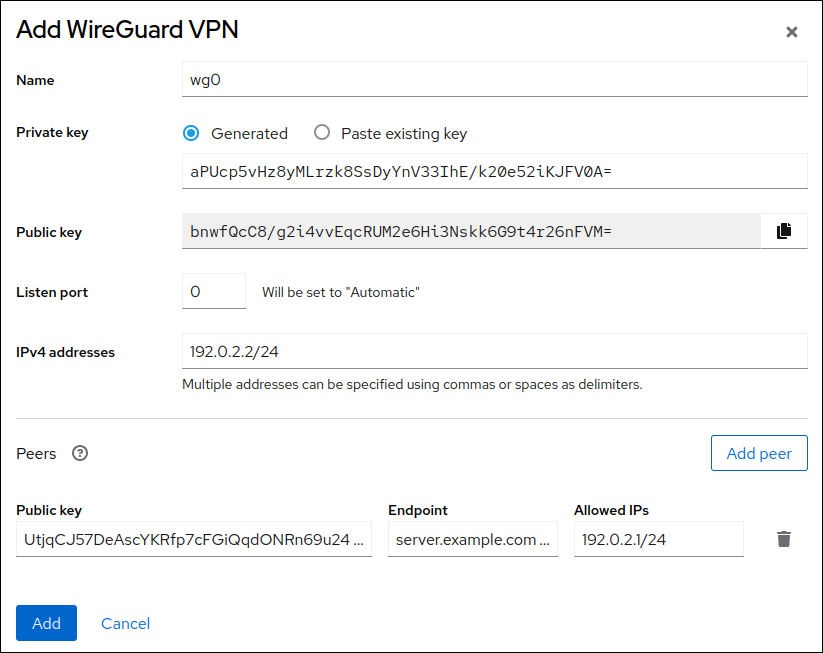
8.7. Configuring a WireGuard server by using the RHEL web console
You can configure a WireGuard server by using the browser-based RHEL web console. Use this method to let NetworkManager manage the WireGuard connection.
Prerequisites
- You are logged in to the RHEL web console.
You know the following information:
- The static tunnel IP addresses and subnet masks of both the server and client
- The public key of the client
Procedure
- Select the Networking tab in the navigation on the left side of the screen.
- Click Add VPN in the Interfaces section.
-
If the
wireguard-toolsandsystemd-resolvedpackages are not already installed, the web console displays a corresponding notification. Click Install to install these packages. - Enter the name of the WireGuard device that you want to create.
Configure the key pair of this host:
If you want use the keys that the web console has created:
- Keep the pre-selected Generated option in the Private key area.
- Note the Public key value. You require this information when you configure the client.
If you want to use an existing private key:
- Select Paste existing key in the Private key area.
- Paste the private key into the text field. The web console automatically calculates the corresponding public key.
Set a listen port number, such as
51820, for incoming WireGuard connections.Always set a fixed port number on hosts that receive incoming WireGuard connections. If you do not set a port, WireGuard uses a random free port each time you activate the interface.
Set the tunnel IPv4 address and subnet mask of the server.
To also set an IPv6 address, you must edit the connection after you have created it.
Add peer configurations for each client that you want to allow to communicate with this server:
- Click Add peer.
- Enter the public key of the client.
- Leave the Endpoint field empty.
- Set the Allowed IPs field to the tunnel IP addresses of the clients that are allowed to send data to this server.
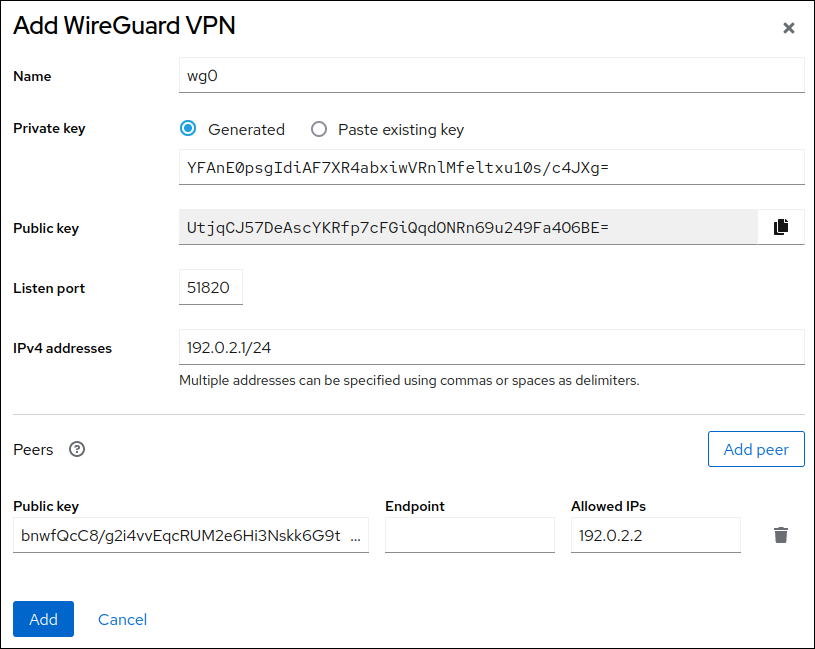
- Click Add to create the WireGuard connection.
If you want to also set a tunnel IPv6 address:
- Click on the WireGuard connection’s name in the Interfaces section.
- Click edit next to IPv6.
-
Set the Addresses field to
Manual, and enter the tunnel IPv6 address and prefix of the server. - Click Save.
- If you use this host in a network with DHCP or Stateless Address Autoconfiguration (SLAAC), the connection can be vulnerable to being redirected. For details and mitigation steps, see Assigning a VPN connection to a dedicated routing table to prevent the connection from bypassing the tunnel.
Verification
Display the interface configuration of the
wg0device:# wg show wg0 interface: wg0 public key: UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= private key: (hidden) listening port: 51820 peer: bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= allowed ips: 192.0.2.2/32, 2001:db8:1::2/128To display the private key in the output, use the
WG_HIDE_KEYS=never wg show wg0command.Display the IP configuration of the
wg0device:# ip address show wg0 20: wg0: <POINTOPOINT,NOARP,UP,LOWERUP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000 link/none inet 192.0.2.1/24 brd 192.0.2.255 scope global noprefixroute wg0 valid_lft forever preferred_lft forever inet6 2001:db8:1::1/32 scope global noprefixroute valid_lft forever preferred_lft forever inet6 fe80::3ef:8863:1ce2:844/64 scope link noprefixroute valid_lft forever preferred_lft forever
8.8. Configuring a WireGuard server by using nm-connection-editor
You can configure the WireGuard server by creating a connection profile in NetworkManager. Use this method to let NetworkManager manage the WireGuard connection.
Prerequisites
- You have generated the public and private key for both the server and client.
You know the following information:
- The private key of the server
- The static tunnel IP addresses and subnet masks of the client
- The public key of the client
- The static tunnel IP addresses and subnet masks of the server
Procedure
Open a console, and enter:
# nm-connection-editor- Add a new connection by clicking the button.
-
Select the
WireGuardconnection type, and click . - Optional: Update the connection name.
-
On the
Generaltab, selectConnect automatically with priority. Optionally, set a priority value. On the
WireGuardtab:-
Enter the name of the virtual interface, such as
wg0, that NetworkManager should assign to the connection. - Enter the private key of the server.
Set the listen port number, such as
51820, for incoming WireGuard connections.Always set a fixed port number on hosts that receive incoming WireGuard connections. If you do not set a port, WireGuard uses a random free port each time you activate the interface.
Click to add peers:
- Enter the public key of the client.
-
Set the
Allowed IPsfield to the tunnel IP addresses of the client that are allowed to send data to this server. - Click .
-
Enter the name of the virtual interface, such as
On the
IPv4 Settingstab:-
Select
Manualin theMethodlist. -
Click to enter the tunnel IPv4 address and the subnet mask. Leave the
Gatewayfield empty.
-
Select
On the
IPv6 Settingstab:-
Select
Manualin theMethodlist. -
Click to enter the tunnel IPv6 address and the subnet mask. Leave the
Gatewayfield empty.
-
Select
- Click to store the connection profile.
- If you use this host in a network with DHCP or Stateless Address Autoconfiguration (SLAAC), the connection can be vulnerable to being redirected. For details and mitigation steps, see Assigning a VPN connection to a dedicated routing table to prevent the connection from bypassing the tunnel.
Verification
Display the interface configuration of the
wg0device:# wg show wg0 interface: wg0 public key: UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= private key: (hidden) listening port: 51820 peer: bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= allowed ips: 192.0.2.2/32, 2001:db8:1::2/128To display the private key in the output, use the
WG_HIDE_KEYS=never wg show wg0command.Display the IP configuration of the
wg0device:# ip address show wg0 20: wg0: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000 link/none inet 192.0.2.1/24 brd 192.0.2.255 scope global noprefixroute wg0 valid_lft forever preferred_lft forever inet6 2001:db8:1::1/64 scope global noprefixroute valid_lft forever preferred_lft forever inet6 fe80::3ef:8863:1ce2:844/64 scope link noprefixroute valid_lft forever preferred_lft forever
8.9. Configuring a WireGuard server by using the wg-quick service
You can configure the WireGuard server by creating a configuration file in the /etc/wireguard/ directory. Use this method to configure the service independently from NetworkManager.
This procedure assumes the following settings:
Server:
-
Private key:
YFAnE0psgIdiAF7XR4abxiwVRnlMfeltxu10s/c4JXg= -
Tunnel IPv4 address:
192.0.2.1/24 -
Tunnel IPv6 address:
2001:db8:1::1/64
-
Private key:
Client:
-
Public key:
bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= -
Tunnel IPv4 address:
192.0.2.2/24 -
Tunnel IPv6 address:
2001:db8:1::2/64
-
Public key:
Prerequisites
- You have generated the public and private key for both the server and client.
You know the following information:
- The private key of the server
- The static tunnel IP addresses and subnet masks of the client
- The public key of the client
- The static tunnel IP addresses and subnet masks of the server
Procedure
Install the
wireguard-toolspackage:# dnf install wireguard-toolsCreate the
/etc/wireguard/wg0.conffile with the following content:[Interface] Address = 192.0.2.1/24, 2001:db8:1::1/64 ListenPort = 51820 PrivateKey = YFAnE0psgIdiAF7XR4abxiwVRnlMfeltxu10s/c4JXg= [Peer] PublicKey = bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= AllowedIPs = 192.0.2.2, 2001:db8:1::2The
[Interface]section describes the WireGuard settings of the interface on the server:-
Address: A comma-separated list of the server’s tunnel IP addresses. -
PrivateKey: The private key of the server. ListenPort: The port on which WireGuard listens for incoming UDP connections.Always set a fixed port number on hosts that receive incoming WireGuard connections. If you do not set a port, WireGuard uses a random free port each time you activate the
wg0interface.
-
Each
[Peer]section describes the settings of one client:-
PublicKey: The public key of the client. -
AllowedIPs: The tunnel IP addresses of the client that are allowed to send data to this server.
-
Enable and start the WireGuard connection:
# systemctl enable --now wg-quick@wg0The systemd instance name must match the name of the configuration file in the
/etc/wireguard/directory without the.confsuffix. The service also uses this name for the virtual network interface.- If you use this host in a network with DHCP or Stateless Address Autoconfiguration (SLAAC), the connection can be vulnerable to being redirected. For details and mitigation steps, see Assigning a VPN connection to a dedicated routing table to prevent the connection from bypassing the tunnel.
Verification
Display the interface configuration of the
wg0device:# wg show wg0 interface: wg0 public key: UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= private key: (hidden) listening port: 51820 peer: bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= allowed ips: 192.0.2.2/32, 2001:db8:1::2/128To display the private key in the output, use the
WG_HIDE_KEYS=never wg show wg0command.Display the IP configuration of the
wg0device:# ip address show wg0 20: wg0: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000 link/none inet 192.0.2.1/24 scope global wg0 valid_lft forever preferred_lft forever inet6 2001:db8:1::1/64 scope global valid_lft forever preferred_lft forever
8.10. Configuring firewalld on a WireGuard server by using the command line
Configure the firewalld service on the WireGuard server, allowing incoming connections from clients. If clients need to use the server as their default gateway and route all traffic through the tunnel, enable also masquerading.
Procedure
Open the WireGuard port for incoming connections in the
firewalldservice:# firewall-cmd --permanent --add-port=51820/udp --zone=publicIf you want clients to route all traffic through the tunnel and use the WireGuard server as the default gateway, enable masquerading for the
publiczone:# firewall-cmd --permanent --zone=public --add-masqueradeReload the
firewalldrules.# firewall-cmd --reload
Verification
Display the configuration of the
publiczone:# firewall-cmd --list-all public (active) ... ports: 51820/udp masquerade: yes ...
8.11. Configuring firewalld on a WireGuard server by using the RHEL web console
Configure the firewalld service on the WireGuard server, allowing incoming connections from clients. If clients need to use the server as their default gateway and route all traffic through the tunnel, enable also masquerading.
Prerequisites
- You are logged in to the RHEL web console.
Procedure
- Select the Networking tab in the navigation on the left side of the screen.
- Click Edit rules and zones in the Firewall section.
- Click Add services.
-
Enter
wireguardinto the Filter services field. Select the
wireguardentry from the list.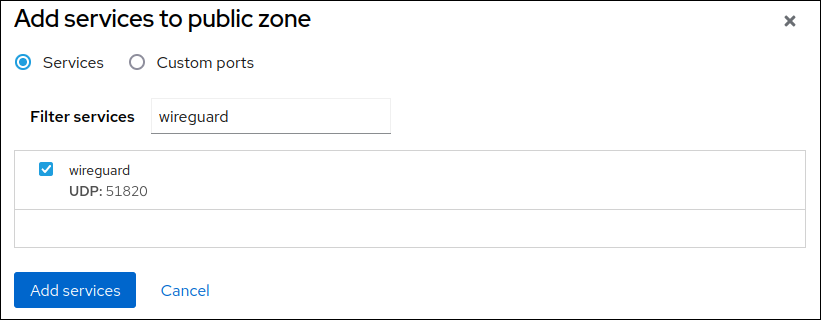
- Click Add services.
If you want clients to route all traffic through the tunnel and use the WireGuard server as the default gateway, enable masquerading for the
publiczone:# firewall-cmd --permanent --zone=public --add-masquerade # firewall-cmd --reloadNote that you cannot enable masquerading in
firewalldzones in the web console.
Verification
- Select the Networking tab in the navigation on the left side of the screen.
- Click Edit rules and zones in the Firewall section.
-
The list contains an entry for the
wireguardservice and displays the UDP port that you configured in the WireGuard connection profile. To verify that masquerading is enabled in the
publiczone offirewalld, enter:# firewall-cmd --list-all --zone=public public (active) ... services: ... wireguard ports: forward: yes masquerade: yes ...
8.12. Configuring firewalld on a WireGuard server by using the graphical interface
Configure the firewalld service on the WireGuard server, allowing incoming connections from clients. If clients need to use the server as their default gateway and route all traffic through the tunnel, enable also masquerading.
Procedure
-
Press the Super key, enter
firewall, and select the Firewall application from the results. -
Select
Permanentin the Configuration list. -
Select the
publiczone. Allow incoming connections to the WireGuard port:
- On the Ports tab, click .
- Enter the port number you set for incoming WireGuard connections:
-
Select
udpfrom theProtocollist. - Click .
If clients should route all traffic through the tunnel and use the WireGuard server as the default gateway:
- Navigate to the Masquerading tab of the public zone.
-
Select
Masquerade zone.
-
Select
.
Verification
Display the configuration of the
publiczone:# firewall-cmd --list-all public (active) ... ports: 51820/udp masquerade: yes ...
8.13. Configuring a WireGuard client by using nmcli
You can configure a WireGuard client by creating a connection profile in NetworkManager. Use this method to let NetworkManager manage the WireGuard connection.
This procedure assumes the following settings:
Client:
-
Private key:
aPUcp5vHz8yMLrzk8SsDyYnV33IhE/k20e52iKJFV0A= -
Tunnel IPv4 address:
192.0.2.2/24 -
Tunnel IPv6 address:
2001:db8:1::2/64
-
Private key:
Server:
-
Public key:
UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= -
Tunnel IPv4 address:
192.0.2.1/24 -
Tunnel IPv6 address:
2001:db8:1::1/64
-
Public key:
Prerequisites
- You have generated the public and private key for both the server and client.
You know the following information:
- The private key of the client
- The static tunnel IP addresses and subnet masks of the client
- The public key of the server
- The static tunnel IP addresses and subnet masks of the server
Procedure
Add a NetworkManager WireGuard connection profile:
# nmcli connection add type wireguard con-name client-wg0 ifname wg0This command creates a profile named
client-wg0and assigns the virtual interfacewg0to it.Optional: Configure NetworkManager so that it does not automatically start the
client-wgconnection:# nmcli connection modify client-wg0 autoconnect noSet the tunnel IPv4 address and subnet mask of the client:
# nmcli connection modify client-wg0 ipv4.method manual ipv4.addresses 192.0.2.2/24Set the tunnel IPv6 address and subnet mask of the client:
# nmcli connection modify client-wg0 ipv6.method manual ipv6.addresses 2001:db8:1::2/64If you want to route all traffic through the tunnel, set the tunnel IP addresses of the server as the default gateway:
# nmcli connection modify client-wg0 ipv4.gateway 192.0.2.1 ipv6.gateway 2001:db8:1::1Routing all traffic through the tunnel requires that you set, in a later step, the
allowed-ipson this client to0.0.0.0/0;::/0.Note that routing all traffic through the tunnel can impact the connectivity to other hosts based on the server routing and firewall configuration.
Add the client’s private key to the connection profile:
# nmcli connection modify client-wg0 wireguard.private-key "aPUcp5vHz8yMLrzk8SsDyYnV33IhE/k20e52iKJFV0A="Add peer connection configurations for each server that you want to allow to communicate with this client:
# nmcli connection modify client-wg0 wireguard.peers 'kEyMNyYhpmn9zPQ4m7iGmU9G7nooS9eeUBe0Y0wO0gM= endpoint=server.example.com:51820 allowed-ips=0.0.0.0/0 ;::/0'The
wireguard.peersparameter defines the peer section of the client in the NetworkManager connection profile. Use0.0.0.0/0;::/0;inallowed-ipsto allow any remote IPv4 and IPv6 address to communicate with this client. Use this setting to route all traffic through the tunnel and use the WireGuard server as default gateway.Reactivate the
client-wg0connection:# nmcli connection up client-wg0- If you use this host in a network with DHCP or Stateless Address Autoconfiguration (SLAAC), the connection can be vulnerable to being redirected. For details and mitigation steps, see Assigning a VPN connection to a dedicated routing table to prevent the connection from bypassing the tunnel.
Verification
Ping the IP addresses of the server:
# ping 192.0.2.1 # ping6 2001:db8:1::1Display the interface configuration of the
wg0device:# wg show wg0 interface: wg0 public key: bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= private key: (hidden) listening port: 51820 peer: UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= endpoint: server.example.com:51820 allowed ips: 192.0.2.1/32, 2001:db8:1::1/128 latest handshake: 1 minute, 41 seconds ago transfer: 824 B received, 1.01 KiB sent persistent keepalive: every 20 secondsTo display the private key in the output, use the
WG_HIDE_KEYS=never wg show wg0command.Note that the output has only the
latest handshakeandtransferentries if you have already sent traffic through the VPN tunnel.Display the IP configuration of the
wg0device:# ip address show wg0 10: wg0: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000 link/none inet 192.0.2.2/24 brd 192.0.2.255 scope global noprefixroute wg0 valid_lft forever preferred_lft forever inet6 2001:db8:1::2/64 scope global noprefixroute valid_lft forever preferred_lft forever inet6 fe80::73d9:6f51:ea6f:863e/64 scope link noprefixroute valid_lft forever preferred_lft forever
8.14. Configuring a WireGuard client by using nmtui
You can configure a WireGuard client by creating a connection profile in NetworkManager. Use this method to let NetworkManager manage the WireGuard connection.
This procedure assumes the following settings:
Client:
-
Private key:
aPUcp5vHz8yMLrzk8SsDyYnV33IhE/k20e52iKJFV0A= -
Tunnel IPv4 address:
192.0.2.2/24 -
Tunnel IPv6 address:
2001:db8:1::2/64
-
Private key:
Server:
-
Public key:
UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= -
Tunnel IPv4 address:
192.0.2.1/24 -
Tunnel IPv6 address:
2001:db8:1::1/64
-
Public key:
Prerequisites
- You have generated the public and private key for both the server and client.
You know the following information:
- The private key of the client
- The static tunnel IP addresses and subnet masks of the client
- The public key of the server
- The static tunnel IP addresses and subnet masks of the server
-
You installed the
NetworkManager-tuipackage
Procedure
Start the
nmtuiapplication:# nmtui- Select Edit a connection, and press Enter.
- Select , and press Enter.
- Select the WireGuard connection type in the list, and press Enter.
In the Edit connection window:
-
Enter the name of the connection and the virtual interface, such as
wg0, that NetworkManager should assign to the connection. Enter the private key of the client.
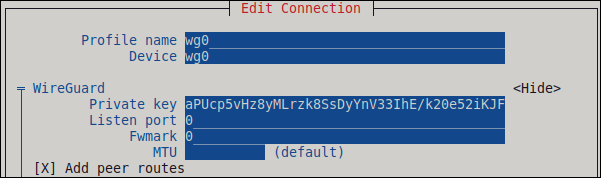
Click next to the Peers pane:
- Enter the public key of the server.
Set the Allowed IPs field. For example, set it to:
- The tunnel IP addresses of the server to allow only the server to communicate with this client.
-
0.0.0.0/0,::/0to allow any remote IPv4 and IPv6 address to communicate with this client. Use this setting to route all traffic through the tunnel and use the WireGuard server as default gateway.
-
Enter the host name or IP address and port of the WireGuard server into the Endpoint field. Use the following format:
<hostname_or_IP>:<port_number> - Optional: If you use the client in a network with network address translation (NAT) or if a firewall closes the UDP connection after some time of inactivity, set a persistent keep alive interval in seconds. In this interval, the client sends a keepalive packet to the server.
Select , and press Enter.

Select next to IPv4 Configuration, and press Enter.
- Select the IPv4 configuration method Manual.
- Enter the tunnel IPv4 address and the subnet mask. Leave the Gateway field empty.
Select next to IPv6 Configuration, and press Enter.
- Select the IPv6 configuration method Manual.
- Enter the tunnel IPv6 address and the subnet mask. Leave the Gateway field empty.
- Optional: Select Automatically connect.
Select , and press Enter

-
Enter the name of the connection and the virtual interface, such as
- In the window with the list of connections, select , and press Enter.
- In the NetworkManager TUI main window, select , and press Enter.
- If you use this host in a network with DHCP or Stateless Address Autoconfiguration (SLAAC), the connection can be vulnerable to being redirected. For details and mitigation steps, see Assigning a VPN connection to a dedicated routing table to prevent the connection from bypassing the tunnel.
Verification
Ping the IP addresses of the server:
# ping 192.0.2.1 # ping6 2001:db8:1::1Display the interface configuration of the
wg0device:# wg show wg0 interface: wg0 public key: bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= private key: (hidden) listening port: 51820 peer: UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= endpoint: server.example.com:51820_ allowed ips: 192.0.2.1/32, 2001:db8:1::1/128 latest handshake: 1 minute, 41 seconds ago transfer: 824 B received, 1.01 KiB sent persistent keepalive: every 20 secondsTo display the private key in the output, use the
WG_HIDE_KEYS=never wg show wg0command.Note that the output contains only the
latest handshakeandtransferentries if you have already sent traffic through the VPN tunnel.Display the IP configuration of the
wg0device:# ip address show wg0 10: wg0: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000 link/none inet 192.0.2.2/24 brd 192.0.2.255 scope global noprefixroute wg0 valid_lft forever preferred_lft forever inet6 2001:db8:1::2/64 scope global noprefixroute valid_lft forever preferred_lft forever inet6 fe80::73d9:6f51:ea6f:863e/64 scope link noprefixroute valid_lft forever preferred_lft forever
8.15. Configuring a WireGuard client by using the RHEL web console
You can configure a WireGuard client by using the browser-based RHEL web console. Use this method to let NetworkManager manage the WireGuard connection.
Prerequisites
- You are logged in to the RHEL web console.
You know the following information:
- The static tunnel IP addresses and subnet masks of both the server and client
- The public key of the server
Procedure
- Select the Networking tab in the navigation on the left side of the screen.
- Click Add VPN in the Interfaces section.
-
If the
wireguard-toolsandsystemd-resolvedpackages are not already installed, the web console displays a corresponding notification. Click Install to install these packages. - Enter the name of the WireGuard device that you want to create.
Configure the key pair of this host:
If you want use the keys that the web console has created:
- Keep the pre-selected Generated option in the Private key area.
- Note the Public key value. You require this information when you configure the client.
If you want to use an existing private key:
- Select Paste existing key in the Private key area.
- Paste the private key into the text field. The web console automatically calculates the corresponding public key.
-
Preserve the
0value in the Listen port field. Set the tunnel IPv4 address and subnet mask of the client.
To also set an IPv6 address, you must edit the connection after you have created it.
Add a peer configuration for the server that you want to allow to communicate with this client:
- Click Add peer.
- Enter the public key of the server.
-
Set the Endpoint field to the hostname or IP address and the port of the server, for example
server.example.com:51820. The client uses this information to establish the connection. Set the Allowed IPs field to the tunnel IP addresses of the clients that are allowed to send data to this server. For example, set the field to one of the following:
- The tunnel IP addresses of the server to allow only the server to communicate with this client. The value in the screen capture below configures this scenario.
-
0.0.0.0/0to allow any remote IPv4 address to communicate with this client. Use this setting to route all traffic through the tunnel and use the WireGuard server as default gateway.
- Click Add to create the WireGuard connection.
If you want to also set a tunnel IPv6 address:
- Click on the WireGuard connection’s name in the Interfaces section.
- Click Edit next to IPv6.
-
Set the Addresses field to
Manual, and enter the tunnel IPv6 address and prefix of the client. - Click Save.
- If you use this host in a network with DHCP or Stateless Address Autoconfiguration (SLAAC), the connection can be vulnerable to being redirected. For details and mitigation steps, see Assigning a VPN connection to a dedicated routing table to prevent the connection from bypassing the tunnel.
Verification
Ping the IP addresses of the server:
# ping 192.0.2.1WireGuard establishes the connection when you try to send traffic through the tunnel.
Display the interface configuration of the
wg0device:# wg show wg0 interface: wg0 public key: bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= private key: (hidden) listening port: 45513 peer: UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= endpoint: server.example.com:51820 allowed ips: 192.0.2.1/32, 2001:db8:1::1/128 latest handshake: 1 minute, 41 seconds ago transfer: 824 B received, 1.01 KiB sent persistent keepalive: every 20 secondsTo display the private key in the output, use the
WG_HIDE_KEYS=never wg show wg0command.Note that the output has only the
latest handshakeandtransferentries if you have already sent traffic through the VPN tunnel.Display the IP configuration of the
wg0device:# ip address show wg0 10: wg0: <POINTOPOINT,NOARP,UP,LOWERUP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000 link/none inet 192.0.2.2/24 brd 192.0.2.255 scope global noprefixroute wg0 valid_lft forever preferred_lft forever inet6 2001:db8:1::2/32 scope global noprefixroute valid_lft forever preferred_lft forever inet6 fe80::73d9:6f51:ea6f:863e/64 scope link noprefixroute valid_lft forever preferred_lft forever
8.16. Configuring a WireGuard client by using nm-connection-editor
You can configure a WireGuard client by creating a connection profile in NetworkManager. Use this method to let NetworkManager manage the WireGuard connection.
Prerequisites
- You have generated the public and private key for both the server and client.
You know the following information:
- The private key of the client
- The static tunnel IP addresses and subnet masks of the client
- The public key of the server
- The static tunnel IP addresses and subnet masks of the server
Procedure
Open a console, and enter:
# nm-connection-editor- Add a new connection by clicking the button.
- Select the WireGuard connection type, and click .
- Optional: Update the connection name.
- Optional: On the General tab, select Connect automatically with priority.
On the WireGuard tab:
-
Enter the name of the virtual interface, such as
wg0, that NetworkManager should assign to the connection. - Enter client’s private key.
Click to add peers:
- Enter the public key of the server.
Set the Allowed IPs field. For example, set it to:
- The tunnel IP addresses of the server to allow only the server to communicate with this client.
0.0.0.0/0;::/0;to allow any remote IPv4 and IPv6 address to communicate with this client. Use this setting to route all traffic through the tunnel and use the WireGuard server as default gateway.Note that routing all traffic through the tunnel can impact the connectivity to other hosts based on the server routing and firewall configuration.
-
Enter the hostname or IP address and port of the WireGuard server into the Endpoint field. Use the following format:
<hostname_or_IP<:<port_number> - Optional: If you use the client in a network with network address translation (NAT) or if a firewall closes the UDP connection after some time of inactivity, set a persistent keep alive interval in seconds. In this interval, the client sends a keep alive packet to the server.
- Click .
-
Enter the name of the virtual interface, such as
On the IPv4 Settings tab:
- Select Manual in the Method list.
- Click to enter the tunnel IPv4 address and the subnet mask.
If you want to route all traffic through the tunnel, set the tunnel IPv4 address of the server in the Gateway field. Otherwise, leave the field empty.
Routing all IPv4 traffic through the tunnel requires that you included
0.0.0.0/0in the Allowed IPs field on this client.
On the IPv6 Settings tab:
- Select Manual in the Method list.
- Click to enter the tunnel IPv6 address and the subnet mask.
If you want to route all traffic through the tunnel, set the tunnel IPv6 address of the server in the Gateway field. Otherwise, leave the field empty.
Routing all IPv4 traffic through the tunnel requires that you included
::/0in the Allowed IPs field on this client.
- Click to store the connection profile.
- If you use this host in a network with DHCP or Stateless Address Autoconfiguration (SLAAC), the connection can be vulnerable to being redirected. For details and mitigation steps, see Assigning a VPN connection to a dedicated routing table to prevent the connection from bypassing the tunnel.
Verification
Ping the IP addresses of the server:
# ping 192.0.2.1 # ping6 2001:db8:1::1Display the interface configuration of the
wg0device:# wg show wg0 interface: wg0 public key: bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= private key: (hidden) listening port: 51820 peer: UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= endpoint: server.example.com:51820 allowed ips: 192.0.2.1/32, 2001:db8:1::1/128 latest handshake: 1 minute, 41 seconds ago transfer: 824 B received, 1.01 KiB sent persistent keepalive: every 20 secondsTo display the private key in the output, use the
WG_HIDE_KEYS=never wg show wg0command.Note that the output only has the
latest handshakeandtransferentries if you have already sent traffic through the VPN tunnel.Display the IP configuration of the
wg0device:# ip address show wg0 10: wg0: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000 link/none inet 192.0.2.2/24 brd 192.0.2.255 scope global noprefixroute wg0 valid_lft forever preferred_lft forever inet6 2001:db8:1::2/64 scope global noprefixroute valid_lft forever preferred_lft forever inet6 fe80::73d9:6f51:ea6f:863e/64 scope link noprefixroute valid_lft forever preferred_lft forever
8.17. Configuring a WireGuard client by using the wg-quick service
You can configure a WireGuard client by creating a configuration file in the /etc/wireguard/ directory. Use this method to configure the service independently from NetworkManager.
This procedure assumes the following settings:
Client:
-
Private key:
aPUcp5vHz8yMLrzk8SsDyYnV33IhE/k20e52iKJFV0A= -
Tunnel IPv4 address:
192.0.2.2/24 -
Tunnel IPv6 address:
2001:db8:1::2/64
-
Private key:
Server:
-
Public key:
UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= -
Tunnel IPv4 address:
192.0.2.1/24 -
Tunnel IPv6 address:
2001:db8:1::1/64
-
Public key:
Prerequisites
- You have generated the public and private key for both the server and client.
You know the following information:
- The private key of the client
- The static tunnel IP addresses and subnet masks of the client
- The public key of the server
- The static tunnel IP addresses and subnet masks of the server
Procedure
Install the
wireguard-toolspackage:# dnf install wireguard-toolsCreate the
/etc/wireguard/wg0.conffile with the following content:[Interface] Address = 192.0.2.2/24, 2001:db8:1::2/64 PrivateKey = aPUcp5vHz8yMLrzk8SsDyYnV33IhE/k20e52iKJFV0A= [Peer] PublicKey = UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= AllowedIPs = 192.0.2.1, 2001:db8:1::1 Endpoint = server.example.com:51820 PersistentKeepalive = 20The
[Interface]section describes the WireGuard settings of the interface on the client:-
Address: A comma-separated list of the client’s tunnel IP addresses. -
PrivateKey: The private key of the client.
-
The
[Peer]section describes the settings of the server:-
PublicKey: The public key of the server. AllowedIPs: The IP addresses that are allowed to send data to this client. For example, set the parameter to:- The tunnel IP addresses of the server to allow only the server to communicate with this client. The value in the example above configures this scenario.
-
0.0.0.0/0, ::/0to allow any remote IPv4 and IPv6 address to communicate with this client. Use this setting to route all traffic through the tunnel and use the WireGuard server as default gateway.
-
Endpoint: Sets the hostname or IP address and the port of the server. The client uses this information to establish the connection. -
The optional
persistent-keepaliveparameter defines an interval in seconds in which WireGuard sends a keepalive packet to the server. Set this parameter if you use the client in a network with network address translation (NAT) or if a firewall closes the UDP connection after some time of inactivity.
-
Enable and start the WireGuard connection:
# systemctl enable --now wg-quick@wg0The systemd instance name must match the name of the configuration file in the
/etc/wireguard/directory without the.confsuffix. The service also uses this name for the virtual network interface.- If you use this host in a network with DHCP or Stateless Address Autoconfiguration (SLAAC), the connection can be vulnerable to being redirected. For details and mitigation steps, see Assigning a VPN connection to a dedicated routing table to prevent the connection from bypassing the tunnel.
Verification
Ping the IP addresses of the server:
# ping 192.0.2.1 # ping6 2001:db8:1::1Display the interface configuration of the
wg0device:# wg show wg0 interface: wg0 public key: bnwfQcC8/g2i4vvEqcRUM2e6Hi3Nskk6G9t4r26nFVM= private key: (hidden) listening port: 51820 peer: UtjqCJ57DeAscYKRfp7cFGiQqdONRn69u249Fa4O6BE= endpoint: server.example.com:51820 allowed ips: 192.0.2.1/32, 2001:db8:1::1/128 latest handshake: 1 minute, 41 seconds ago transfer: 824 B received, 1.01 KiB sent persistent keepalive: every 20 secondsTo display the private key in the output, use the
WG_HIDE_KEYS=never wg show wg0command.Note that the output contains only the
latest handshakeandtransferentries if you have already sent traffic through the VPN tunnel.Display the IP configuration of the
wg0device:# ip address show wg0 10: wg0: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000 link/none inet 192.0.2.2/24 scope global wg0 valid_lft forever preferred_lft forever inet6 2001:db8:1::2/64 scope global valid_lft forever preferred_lft forever
8.18. Assigning a VPN connection to a dedicated routing table to prevent the connection from bypassing the tunnel
To protect your VPN connection from traffic redirection attacks, assign it to a dedicated routing table. This prevents malicious network servers from bypassing the secure tunnel and compromising data integrity.
Both a DHCP server and Stateless Address Autoconfiguration (SLAAC) can add routes to a client’s routing table. For example, a malicious DHCP server can use this feature to force a host with VPN connection to redirect traffic through a physical interface instead of the VPN tunnel. This vulnerability is also known as TunnelVision and described in the CVE-2024-3661 vulnerability article.
To mitigate this vulnerability, you can assign the VPN connection to a dedicated routing table. This prevents the DHCP configuration or SLAAC from manipulating routing decisions for network packets intended for the VPN tunnel.
Follow the steps if at least one of the conditions applies to your environment:
- At least one network interface uses DHCP or SLAAC.
- Your network does not use mechanisms, such as DHCP snooping, that prevent a rogue DHCP server.
Routing the entire traffic through the VPN prevents the host from accessing local network resources.
Prerequisites
- You use NetworkManager 1.48.10-5 or later.
Procedure
- Decide which routing table you want to use. The following steps use table 75. By default, RHEL does not use the tables 1-254, and you can use any of them.
Configure the VPN connection profile to place the VPN routes in a dedicated routing table:
# nmcli connection modify <vpn_connection_profile> ipv4.route-table 75 ipv6.route-table 75Set a low priority value for the table you used in the previous command:
# nmcli connection modify <vpn_connection_profile> ipv4.routing-rules "priority 32345 from all table 75" ipv6.routing-rules "priority 32345 from all table 75"The priority value can be any value between 1 and 32766. The lower the value, the higher the priority.
Reconnect the VPN connection:
# nmcli connection down <vpn_connection_profile> # nmcli connection up <vpn_connection_profile>
Verification
Display the IPv4 routes in table 75:
# ip route show table 75 ... 192.0.2.0/24 via 192.0.2.254 dev vpn_device proto static metric 50 default dev vpn_device proto static scope link metric 50The output confirms that both the route to the remote network and the default gateway are assigned to routing table 75 and, therefore, all traffic is routed through the tunnel. If you set
ipv4.never-default truein the VPN connection profile, a default route is not created and, therefore, not visible in this output.Display the IPv6 routes in table 75:
# ip -6 route show table 75 ... 2001:db8:1::/64 dev vpn_device proto kernel metric 50 pref medium default dev vpn_device proto static metric 50 pref mediumThe output confirms that both the route to the remote network and the default gateway are assigned to routing table 75 and, therefore, all traffic is routed through the tunnel. If you set
ipv6.never-default truein the VPN connection profile, a default route is not created and, therefore, not visible in this output.