ネットワーク
クラスターネットワークの設定および管理
概要
第1章 ネットワークについて
クラスター管理者は、クラスターで実行されるアプリケーションを外部トラフィックに公開し、ネットワーク接続のセキュリティーを保護するための複数のオプションがあります。
- ノードポートやロードバランサーなどのサービスタイプ
-
IngressやRouteなどの API リソース
デフォルトで、Kubernetes は各 Pod に、Pod 内で実行しているアプリケーションの内部 IP アドレスを割り当てます。Pod とそのコンテナーはネットワークネットワーク接続が可能ですが、クラスター外のクライアントにはネットワークアクセスがありません。アプリケーションを外部トラフィックに公開する場合、各 Pod に IP アドレスを割り当てると、ポートの割り当て、ネットワーク、名前の指定、サービス検出、負荷分散、アプリケーション設定、移行などの点で、Pod を物理ホストや仮想マシンのように扱うことができます。
一部のクラウドプラットフォームでは、169.254.169.254 IP アドレスでリッスンするメタデータ API があります。これは、IPv4 169.254.0.0/16 CIDR ブロックのリンクローカル IP アドレスです。
この CIDR ブロックは Pod ネットワークから到達できません。これらの IP アドレスへのアクセスを必要とする Pod には、Pod 仕様の spec.hostNetwork フィールドを true に設定して、ホストのネットワークアクセスが付与される必要があります。
Pod ホストのネットワークアクセスを許可する場合、Pod に基礎となるネットワークインフラストラクチャーへの特権アクセスを付与します。
1.1. OpenShift Container Platform DNS
フロントエンドサービスやバックエンドサービスなど、複数のサービスを実行して複数の Pod で使用している場合、フロントエンド Pod がバックエンドサービスと通信できるように、ユーザー名、サービス IP などの環境変数を作成します。サービスが削除され、再作成される場合には、新規の IP アドレスがそのサービスに割り当てられるので、フロントエンド Pod がサービス IP の環境変数の更新された値を取得するには、これを再作成する必要があります。さらに、バックエンドサービスは、フロントエンド Pod を作成する前に作成し、サービス IP が正しく生成され、フロントエンド Pod に環境変数として提供できるようにする必要があります。
そのため、OpenShift Container Platform には DNS が組み込まれており、これにより、サービスは、サービス IP/ポートと共にサービス DNS によって到達可能になります。
1.2. OpenShift Container Platform Ingress Operator
OpenShift Container Platform クラスターを作成すると、クラスターで実行している Pod およびサービスにはそれぞれ独自の IP アドレスが割り当てられます。IP アドレスは、近くで実行されている他の Pod やサービスからアクセスできますが、外部クライアントの外部からはアクセスできません。Ingress Operator は IngressController API を実装し、OpenShift Container Platform クラスターサービスへの外部アクセスを可能にするコンポーネントです。
Ingress Operator を使用すると、ルーティングを処理する 1 つ以上の HAProxy ベースの Ingress コントローラー をデプロイおよび管理することにより、外部クライアントがサービスにアクセスできるようになります。OpenShift Container Platform Route および Kubernetes Ingress リソースを指定して、トラフィックをルーティングするために Ingress Operator を使用します。endpointPublishingStrategy タイプおよび内部負荷分散を定義する機能などの Ingress コントローラー内の設定は、Ingress コントローラーエンドポイントを公開する方法を提供します。
1.2.1. ルートと Ingress の比較
OpenShift Container Platform の Kubernetes Ingress リソースは、クラスター内で Pod として実行される共有ルーターサービスと共に Ingress コントローラーを実装します。Ingress トラフィックを管理する最も一般的な方法は Ingress コントローラーを使用することです。他の通常の Pod と同様にこの Pod をスケーリングし、複製できます。このルーターサービスは、オープンソースのロードバランサーソリューションである HAProxy をベースとしています。
OpenShift Container Platform ルートは、クラスターのサービスに Ingress トラフィックを提供します。ルートは、Blue-Green デプロイメント向けに TLS 再暗号化、TLS パススルー、分割トラフィックなどの標準の Kubernetes Ingress コントローラーでサポートされない可能性のある高度な機能を提供します。
Ingress トラフィックは、ルートを介してクラスターのサービスにアクセスします。ルートおよび Ingress は、Ingress トラフィックを処理する主要なリソースです。Ingress は、外部要求を受け入れ、ルートに基づいてそれらを委譲するなどのルートと同様の機能を提供します。ただし、Ingress では、特定タイプの接続 (HTTP/2、HTTPS およびサーバー名 ID(SNI)、ならび証明書を使用した TLS のみを許可できます。OpenShift Container Platform では、ルートは、Ingress リソースで指定される各種の条件を満たすために生成されます。
第2章 ホストへのアクセス
OpenShift Container Platform インスタンスにアクセスして、セキュアなシェル (SSH) アクセスでコントロールプレーンノード (別名マスターノード) にアクセスするために bastion ホストを作成する方法を学びます。
2.1. インストーラーでプロビジョニングされるインフラストラクチャークラスターでの Amazon Web Services のホストへのアクセス
OpenShift Container Platform インストーラーは、OpenShift Container Platform クラスターにプロビジョニングされる Amazon Elastic Compute Cloud (Amazon EC2) インスタンスのパブリック IP アドレスを作成しません。OpenShift Container Platform ホストに対して SSH を実行できるようにするには、以下の手順を実行する必要があります。
手順
-
openshift-installコマンドで作成される仮想プライベートクラウド (VPC) に対する SSH アクセスを可能にするセキュリティーグループを作成します。 - インストーラーが作成したパブリックサブネットのいずれかに Amazon EC2 インスタンスを作成します。
パブリック IP アドレスを、作成した Amazon EC2 インスタンスに関連付けます。
OpenShift Container Platform のインストールとは異なり、作成した Amazon EC2 インスタンスを SSH キーペアに関連付ける必要があります。これにはインターネットを OpenShift Container Platform クラスターの VPC にブリッジ接続するための SSH bastion としてのみの単純な機能しかないため、このインスタンスにどのオペレーティングシステムを選択しても問題ありません。どの Amazon Machine Image (AMI) を使用するかについては、注意が必要です。たとえば、Red Hat Enterprise Linux CoreOS (RHCOS) では、インストーラーと同様に、Ignition でキーを指定することができます。
Amazon EC2 インスタンスをプロビジョニングし、これに対して SSH を実行した後に、OpenShift Container Platform インストールに関連付けた SSH キーを追加する必要があります。このキーは bastion インスタンスのキーとは異なる場合がありますが、異なるキーにしなければならない訳ではありません。
注記直接の SSH アクセスは、障害復旧を目的とする場合にのみ推奨されます。Kubernetes API が応答する場合、特権付き Pod を代わりに実行します。
-
oc get nodesを実行し、出力を検査し、マスターであるノードのいずれかを選択します。ホスト名はip-10-0-1-163.ec2.internalに類似したものになります。 Amazon EC2 に手動でデプロイした bastion SSH ホストから、そのコントロールプレーンホスト (別名マスターホスト) に対して SSH を実行します。インストール時に指定したものと同じ SSH キーを使用するようにします。
$ ssh -i <ssh-key-path> core@<master-hostname>
第3章 ネットワーキング Operator の概要
OpenShift Container Platform は、複数のタイプのネットワーキング Operator をサポートします。これらのネットワーク Operator を使用して、クラスターネットワークを管理できます。
3.1. Cluster Network Operator
Cluster Network Operator (CNO) は、OpenShift Container Platform クラスター内のクラスターネットワークコンポーネントをデプロイおよび管理します。これには、インストール中にクラスター用に選択された Container Network Interface (CNI) のデフォルトネットワークプロバイダープラグインのデプロイメントが含まれます。詳細は、OpenShift Container Platform における Cluster Network Operator を参照してください。
3.2. DNS Operator
DNS Operator は、CoreDNS をデプロイして管理し、Pod に名前解決サービスを提供します。これにより、OpenShift Container Platform で DNS ベースの Kubernetes サービス検出が可能になります。詳細は、OpenShift Container Platform の DNS Operator を参照してください。
3.3. Ingress Operator
OpenShift Container Platform クラスターを作成すると、クラスターで実行している Pod およびサービスにはそれぞれの IP アドレスが割り当てられます。IP アドレスは、近くで実行されている他の Pod やサービスからアクセスできますが、外部クライアントの外部からはアクセスできません。Ingress Operator は IngressController API を実装し、OpenShift Container Platform クラスターサービスへの外部アクセスを可能にします。詳細は、OpenShift Container Platform の Ingress Operator を参照してください。
第4章 OpenShift Container Platform における Cluster Network Operator
Cluster Network Operator (CNO) は、インストール時にクラスター用に選択される Container Network Interface (CNI) デフォルトネットワークプロバイダープラグインを含む、OpenShift Container Platform クラスターの各種のクラスターネットワークコンポーネントをデプロイし、これらを管理します。
4.1. Cluster Network Operator
Cluster Network Operator は、operator.openshift.io API グループから network API を実装します。Operator は、デーモンセットを使用して OpenShift SDN デフォルト Container Network Interface (CNI) ネットワークプロバイダープラグイン、またはクラスターのインストール時に選択したデフォルトネットワークプロバイダープラグインをデプロイします。
手順
Cluster Network Operator は、インストール時に Kubernetes Deployment としてデプロイされます。
以下のコマンドを実行して Deployment のステータスを表示します。
$ oc get -n openshift-network-operator deployment/network-operator出力例
NAME READY UP-TO-DATE AVAILABLE AGE network-operator 1/1 1 1 56m以下のコマンドを実行して、Cluster Network Operator の状態を表示します。
$ oc get clusteroperator/network出力例
NAME VERSION AVAILABLE PROGRESSING DEGRADED SINCE network 4.5.4 True False False 50m以下のフィールドは、Operator のステータス (
AVAILABLE、PROGRESSING、およびDEGRADED) についての情報を提供します。AVAILABLEフィールドは、Cluster Network Operator が Available ステータス条件を報告する場合にTrueになります。
4.2. クラスターネットワーク設定の表示
すべての新規 OpenShift Container Platform インストールには、cluster という名前の network.config オブジェクトがあります。
手順
oc describeコマンドを使用して、クラスターネットワーク設定を表示します。$ oc describe network.config/cluster出力例
Name: cluster Namespace: Labels: <none> Annotations: <none> API Version: config.openshift.io/v1 Kind: Network Metadata: Self Link: /apis/config.openshift.io/v1/networks/cluster Spec:1 Cluster Network: Cidr: 10.128.0.0/14 Host Prefix: 23 Network Type: OpenShiftSDN Service Network: 172.30.0.0/16 Status:2 Cluster Network: Cidr: 10.128.0.0/14 Host Prefix: 23 Cluster Network MTU: 8951 Network Type: OpenShiftSDN Service Network: 172.30.0.0/16 Events: <none>
4.3. Cluster Network Operator のステータス表示
oc describe コマンドを使用して、Cluster Network Operator のステータスを検査し、その詳細を表示することができます。
手順
以下のコマンドを実行して、Cluster Network Operator のステータスを表示します。
$ oc describe clusteroperators/network
4.4. Cluster Network Operator ログの表示
oc logs コマンドを使用して、Cluster Network Operator ログを表示できます。
手順
以下のコマンドを実行して、Cluster Network Operator のログを表示します。
$ oc logs --namespace=openshift-network-operator deployment/network-operator
4.5. Cluster Network Operator (CNO) の設定
クラスターネットワークの設定は、Cluster Network Operator (CNO) 設定の一部として指定され、cluster という名前のカスタムリソース (CR) オブジェクトに保存されます。CR は operator.openshift.io API グループの Network API のフィールドを指定します。
CNO 設定は、Network.config.openshift.io API グループの Network API からクラスターのインストール時に以下のフィールドを継承し、これらのフィールドは変更できません。
clusterNetwork- Pod IP アドレスの割り当てに使用する IP アドレスプール。
serviceNetwork- サービスの IP アドレスプール。
defaultNetwork.type- OpenShift SDN または OVN-Kubernetes などのクラスターネットワークプロバイダー。
クラスターのインストール後に、直前のセクションで一覧表示されているフィールドを変更することはできません。
defaultNetwork オブジェクトのフィールドを cluster という名前の CNO オブジェクトに設定することにより、クラスターのクラスターネットワークプロバイダー設定を指定できます。
4.5.1. Cluster Network Operator 設定オブジェクト
Cluster Network Operator (CNO) のフィールドは以下の表で説明されています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
CNO オブジェクトの名前。この名前は常に |
|
|
| Pod ID アドレスの割り当て、サブネット接頭辞の長さのクラスター内の個別ノードへの割り当てに使用される IP アドレスのブロックを指定する一覧です。以下に例を示します。
この値は読み取り専用であり、クラスターのインストール時に |
|
|
| サービスの IP アドレスのブロック。OpenShift SDN および OVN-Kubernetes Container Network Interface (CNI) ネットワークプロバイダーは、サービスネットワークの単一 IP アドレスブロックのみをサポートします。以下に例を示します。
この値は読み取り専用であり、クラスターのインストール時に |
|
|
| クラスターネットワークの Container Network Interface (CNI) ネットワークプロバイダーを設定します。 |
|
|
| このオブジェクトのフィールドは、kube-proxy 設定を指定します。OVN-Kubernetes クラスターネットワークプロバイダーを使用している場合、kube-proxy 設定は機能しません。 |
defaultNetwork オブジェクト設定
defaultNetwork オブジェクトの値は、以下の表で定義されます。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
注記 OpenShift Container Platform はデフォルトで、OpenShift SDN Container Network Interface (CNI) クラスターネットワークプロバイダーを使用します。 |
|
|
| このオブジェクトは OpenShift SDN クラスターネットワークプロバイダーにのみ有効です。 |
|
|
| このオブジェクトは OVN-Kubernetes クラスターネットワークプロバイダーにのみ有効です。 |
OpenShift SDN CNI クラスターネットワークプロバイダーの設定
以下の表は、OpenShift SDN Container Network Interface (CNI) クラスターネットワークプロバイダーの設定フィールドについて説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
| OpenShiftSDN のネットワーク分離モード。 |
|
|
| VXLAN オーバーレイネットワークの最大転送単位 (MTU)。通常、この値は自動的に設定されます。 |
|
|
|
すべての VXLAN パケットに使用するポート。デフォルト値は |
クラスターのインストール時にのみクラスターネットワークプロバイダーの設定を変更することができます。
OpenShift SDN 設定の例
defaultNetwork:
type: OpenShiftSDN
openshiftSDNConfig:
mode: NetworkPolicy
mtu: 1450
vxlanPort: 4789OVN-Kubernetes CNI クラスターネットワークプロバイダーの設定
以下の表は OVN-Kubernetes CNI クラスターネットワークプロバイダーの設定フィールドについて説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
| Geneve (Generic Network Virtualization Encapsulation) オーバーレイネットワークの MTU (maximum transmission unit)。通常、この値は自動的に設定されます。 |
|
|
| Geneve オーバーレイネットワークの UDP ポート。 |
|
|
| フィールドがある場合、IPsec はクラスターに対して有効にされます。 |
クラスターのインストール時にのみクラスターネットワークプロバイダーの設定を変更することができます。
OVN-Kubernetes 設定の例
defaultNetwork:
type: OVNKubernetes
ovnKubernetesConfig:
mtu: 1400
genevePort: 6081
ipsecConfig: {}kubeProxyConfig オブジェクト設定
kubeProxyConfig オブジェクトの値は以下の表で定義されます。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
注記
OpenShift Container Platform 4.3 以降で強化されたパフォーマンスの向上により、 |
|
|
|
|
4.5.2. Cluster Network Operator の設定例
以下の例では、詳細な CNO 設定が指定されています。
Cluster Network Operator オブジェクトのサンプル
apiVersion: operator.openshift.io/v1
kind: Network
metadata:
name: cluster
spec:
clusterNetwork:
- cidr: 10.128.0.0/14
hostPrefix: 23
serviceNetwork:
- 172.30.0.0/16
defaultNetwork:
type: OpenShiftSDN
openshiftSDNConfig:
mode: NetworkPolicy
mtu: 1450
vxlanPort: 4789
kubeProxyConfig:
iptablesSyncPeriod: 30s
proxyArguments:
iptables-min-sync-period:
- 0s第5章 OpenShift Container Platform の DNS Operator
DNS Operator は、Pod に対して名前解決サービスを提供するために CoreDNS をデプロイし、これを管理し、OpenShift 内での DNS ベースの Kubernetes サービス検出を可能にします。
5.1. DNS Operator
DNS Operator は、operator.openshift.io API グループから dns API を実装します。この Operator は、デーモンセットを使用して CoreDNS をデプロイし、デーモンセットのサービスを作成し、 kubelet を Pod に対して名前解決に CoreDNS サービス IP を使用するように指示するように設定します。
手順
DNS Operator は、インストール時に Deployment オブジェクトを使用してデプロイされます。
oc getコマンドを使用してデプロイメントのステータスを表示します。$ oc get -n openshift-dns-operator deployment/dns-operator出力例
NAME READY UP-TO-DATE AVAILABLE AGE dns-operator 1/1 1 1 23hoc getコマンドを使用して DNS Operator の状態を表示します。$ oc get clusteroperator/dns出力例
NAME VERSION AVAILABLE PROGRESSING DEGRADED SINCE dns 4.1.0-0.11 True False False 92mAVAILABLE、PROGRESSINGおよびDEGRADEDは、Operator のステータスについての情報を提供します。AVAILABLEは、CoreDNS デーモンセットからの 1 つ以上の Pod がAvailableステータス条件を報告する場合はTrueになります。
5.2. デフォルト DNS の表示
すべての新規 OpenShift Container Platform インストールには、default という名前の dns.operator があります。
手順
oc describeコマンドを使用してデフォルトのdnsを表示します。$ oc describe dns.operator/default出力例
Name: default Namespace: Labels: <none> Annotations: <none> API Version: operator.openshift.io/v1 Kind: DNS ... Status: Cluster Domain: cluster.local1 Cluster IP: 172.30.0.102 ...クラスターのサービス CIDR を見つけるには、
oc getコマンドを使用します。$ oc get networks.config/cluster -o jsonpath='{$.status.serviceNetwork}'
出力例
[172.30.0.0/16]5.3. DNS 転送の使用
DNS 転送を使用すると、指定のゾーンにどのネームサーバーを使用するかを指定することで、ゾーンごとに /etc/resolv.conf で特定される転送設定をオーバーライドできます。転送されるゾーンが OpenShift Container Platform によって管理される Ingress ドメインである場合、アップストリームネームサーバーがドメインについて認証される必要があります。
手順
defaultという名前の DNS Operator オブジェクトを変更します。$ oc edit dns.operator/defaultこれにより、
Serverに基づく追加のサーバー設定ブロックを使用してdns-defaultという名前の ConfigMap を作成し、更新できます。クエリーに一致するゾーンを持つサーバーがない場合、名前解決は/etc/resolv.confで指定されたネームサーバーにフォールバックします。DNS の例
apiVersion: operator.openshift.io/v1 kind: DNS metadata: name: default spec: servers: - name: foo-server1 zones:2 - example.com forwardPlugin: upstreams:3 - 1.1.1.1 - 2.2.2.2:5353 - name: bar-server zones: - bar.com - example.com forwardPlugin: upstreams: - 3.3.3.3 - 4.4.4.4:5454注記serversが定義されていないか、または無効な場合、ConfigMap にはデフォルトサーバーのみが含まれます。ConfigMap を表示します。
$ oc get configmap/dns-default -n openshift-dns -o yaml以前のサンプル DNS に基づく DNS ConfigMap の例
apiVersion: v1 data: Corefile: | example.com:5353 { forward . 1.1.1.1 2.2.2.2:5353 } bar.com:5353 example.com:5353 { forward . 3.3.3.3 4.4.4.4:54541 } .:5353 { errors health kubernetes cluster.local in-addr.arpa ip6.arpa { pods insecure upstream fallthrough in-addr.arpa ip6.arpa } prometheus :9153 forward . /etc/resolv.conf { policy sequential } cache 30 reload } kind: ConfigMap metadata: labels: dns.operator.openshift.io/owning-dns: default name: dns-default namespace: openshift-dns- 1
forwardPluginへの変更により、CoreDNS デーモンセットのローリング更新がトリガーされます。
5.4. DNS Operator のステータス
oc describe コマンドを使用して、DNS Operator のステータスを検査し、その詳細を表示することができます。
手順
DNS Operator のステータスを表示します。
$ oc describe clusteroperators/dns5.5. DNS Operator ログ
oc logs コマンドを使用して、DNS Operator ログを表示できます。
手順
DNS Operator のログを表示します。
$ oc logs -n openshift-dns-operator deployment/dns-operator -c dns-operator第6章 OpenShift Container Platform の Ingress Operator
6.1. OpenShift Container Platform Ingress Operator
OpenShift Container Platform クラスターを作成すると、クラスターで実行している Pod およびサービスにはそれぞれ独自の IP アドレスが割り当てられます。IP アドレスは、近くで実行されている他の Pod やサービスからアクセスできますが、外部クライアントの外部からはアクセスできません。Ingress Operator は IngressController API を実装し、OpenShift Container Platform クラスターサービスへの外部アクセスを可能にするコンポーネントです。
Ingress Operator を使用すると、ルーティングを処理する 1 つ以上の HAProxy ベースの Ingress コントローラー をデプロイおよび管理することにより、外部クライアントがサービスにアクセスできるようになります。OpenShift Container Platform Route および Kubernetes Ingress リソースを指定して、トラフィックをルーティングするために Ingress Operator を使用します。endpointPublishingStrategy タイプおよび内部負荷分散を定義する機能などの Ingress コントローラー内の設定は、Ingress コントローラーエンドポイントを公開する方法を提供します。
6.2. Ingress 設定アセット
インストールプログラムでは、config.openshift.io API グループの Ingress リソースでアセットを生成します (cluster-ingress-02-config.yml)。
Ingress リソースの YAML 定義
apiVersion: config.openshift.io/v1
kind: Ingress
metadata:
name: cluster
spec:
domain: apps.openshiftdemos.com
インストールプログラムは、このアセットを manifests/ ディレクトリーの cluster-ingress-02-config.yml ファイルに保存します。この Ingress リソースは、Ingress のクラスター全体の設定を定義します。この Ingress 設定は、以下のように使用されます。
- Ingress Operator は、クラスター Ingress 設定のドメインを、デフォルト Ingress コントローラーのドメインとして使用します。
-
OpenShift API Server Operator は、クラスター Ingress 設定からのドメインを使用します。このドメインは、明示的なホストを指定しない
Routeリソースのデフォルトホストを生成する際にも使用されます。
6.3. イメージコントローラー設定パラメーター
ingresscontrollers.operator.openshift.io リソースは以下の設定パラメーターを提供します。
| パラメーター | 説明 |
|---|---|
|
|
空の場合、デフォルト値は |
|
|
|
|
|
設定されていない場合、デフォルト値は
|
|
|
シークレットには以下のキーおよびデータが含まれる必要があります: *
設定されていない場合、ワイルドカード証明書は自動的に生成され、使用されます。証明書は Ingress コントーラーの 使用中の証明書 (生成されるか、ユーザー指定の場合かを問わない) は OpenShift Container Platform のビルトイン OAuth サーバーに自動的に統合されます。 |
|
|
|
|
|
|
|
|
設定されていない場合は、デフォルト値が使用されます。 注記
|
|
|
これが設定されていない場合、デフォルト値は
Ingress コントローラーの最小の TLS バージョンは 重要
HAProxy Ingress コントローラーイメージは TLS
また、Ingress Operator は TLS
OpenShift Container Platform ルーターは、TLS_AES_128_CCM_SHA256、TLS_CHACHA20_POLY1305_SHA256、TLS_AES_256_GCM_SHA384、および TLS_AES_128_GCM_SHA256 を使用する TLS 注記
設定されたセキュリティープロファイルの暗号および最小 TLS バージョンが |
|
|
|
|
|
|
|
|
デフォルトでは、ポリシーは
|
すべてのパラメーターはオプションです。
6.3.1. Ingress コントローラーの TLS セキュリティープロファイル
TLS セキュリティープロファイルは、サーバーに接続する際に接続クライアントが使用できる暗号を規制する方法をサーバーに提供します。
6.3.1.1. TLS セキュリティープロファイルについて
TLS (Transport Layer Security) セキュリティープロファイルを使用して、さまざまな OpenShift Container Platform コンポーネントに必要な TLS 暗号を定義できます。OpenShift Container Platform の TLS セキュリティープロファイルは、Mozilla が推奨する設定 に基づいています。
コンポーネントごとに、以下の TLS セキュリティープロファイルのいずれかを指定できます。
| プロファイル | 説明 |
|---|---|
|
| このプロファイルは、レガシークライアントまたはライブラリーでの使用を目的としています。このプロファイルは、Old 後方互換性 の推奨設定に基づいています。
注記 Ingress コントローラーの場合、TLS の最小バージョンは 1.0 から 1.1 に変換されます。 |
|
| このプロファイルは、大多数のクライアントに推奨される設定です。これは、Ingress コントローラーおよびコントロールプレーンのデフォルトの TLS セキュリティープロファイルです。このプロファイルは、Intermediate 互換性 の推奨設定に基づいています。
|
|
| このプロファイルは、後方互換性を必要としない Modern のクライアントでの使用を目的としています。このプロファイルは、Modern 互換性 の推奨設定に基づいています。
注記
OpenShift Container Platform 4.6、4.7、および 4.8 では、 重要
|
|
| このプロファイルを使用すると、使用する TLS バージョンと暗号を定義できます。 警告
無効な設定により問題が発生する可能性があるため、 注記
OpenShift Container Platform ルーターは、Red Hat 分散の OpenSSL デフォルトセットの TLS |
事前定義されたプロファイルタイプのいずれかを使用する場合、有効なプロファイル設定はリリース間で変更される可能性があります。たとえば、リリース X.Y.Z にデプロイされた Intermediate プロファイルを使用する仕様がある場合、リリース X.Y.Z+1 へのアップグレードにより、新規のプロファイル設定が適用され、ロールアウトが生じる可能性があります。
6.3.1.2. Ingress コントローラーの TLS セキュリティープロファイルの設定
Ingress コントローラーの TLS セキュリティープロファイルを設定するには、IngressController カスタムリソース (CR) を編集して、事前定義済みまたはカスタムの TLS セキュリティープロファイルを指定します。TLS セキュリティープロファイルが設定されていない場合、デフォルト値は API サーバーに設定された TLS セキュリティープロファイルに基づいています。
Old TLS のセキュリティープロファイルを設定するサンプル IngressController CR
apiVersion: operator.openshift.io/v1
kind: IngressController
...
spec:
tlsSecurityProfile:
old: {}
type: Old
...TLS セキュリティープロファイルは、Ingress コントローラーの TLS 接続の最小 TLS バージョンと TLS 暗号を定義します。
設定された TLS セキュリティープロファイルの暗号と最小 TLS バージョンは、Status.Tls Profile 配下の IngressController カスタムリソース (CR) と Spec.Tls Security Profile 配下の設定された TLS セキュリティープロファイルで確認できます。Custom TLS セキュリティープロファイルの場合、特定の暗号と最小 TLS バージョンは両方のパラメーターの下に一覧表示されます。
HAProxy Ingress コントローラーイメージは TLS 1.3 をサポートしません。Modern プロファイルには TLS 1.3 が必要であることから、これはサポートされません。Ingress Operator は Modern プロファイルを Intermediate に変換します。また、Ingress Operator は TLS 1.0 の Old または Custom プロファイルを 1.1 に変換し、TLS 1.3 の Custom プロファイルを 1.2 に変換します。
前提条件
-
cluster-adminロールを持つユーザーとしてクラスターにアクセスできる。
手順
openshift-ingress-operatorプロジェクトのIngressControllerCR を編集して、TLS セキュリティープロファイルを設定します。$ oc edit IngressController default -n openshift-ingress-operatorspec.tlsSecurityProfileフィールドを追加します。CustomプロファイルのサンプルIngressControllerCRapiVersion: operator.openshift.io/v1 kind: IngressController ... spec: tlsSecurityProfile: type: Custom1 custom:2 ciphers:3 - ECDHE-ECDSA-CHACHA20-POLY1305 - ECDHE-RSA-CHACHA20-POLY1305 - ECDHE-RSA-AES128-GCM-SHA256 - ECDHE-ECDSA-AES128-GCM-SHA256 minTLSVersion: VersionTLS11 ...- 変更を適用するためにファイルを保存します。
検証
IngressControllerCR にプロファイルが設定されていることを確認します。$ oc describe IngressController default -n openshift-ingress-operator出力例
Name: default Namespace: openshift-ingress-operator Labels: <none> Annotations: <none> API Version: operator.openshift.io/v1 Kind: IngressController ... Spec: ... Tls Security Profile: Custom: Ciphers: ECDHE-ECDSA-CHACHA20-POLY1305 ECDHE-RSA-CHACHA20-POLY1305 ECDHE-RSA-AES128-GCM-SHA256 ECDHE-ECDSA-AES128-GCM-SHA256 Min TLS Version: VersionTLS11 Type: Custom ...
6.3.2. Ingress コントローラーエンドポイントの公開ストラテジー
NodePortService エンドポイントの公開ストラテジー
NodePortService エンドポイントの公開ストラテジーは、Kubernetes NodePort サービスを使用して Ingress コントローラーを公開します。
この設定では、Ingress コントローラーのデプロイメントはコンテナーのネットワークを使用します。NodePortService はデプロイメントを公開するために作成されます。特定のノードポートは OpenShift Container Platform によって動的に割り当てられますが、静的ポートの割り当てをサポートするために、管理される NodePortService のノードポートフィールドへの変更が保持されます。
図6.1 NodePortService の図
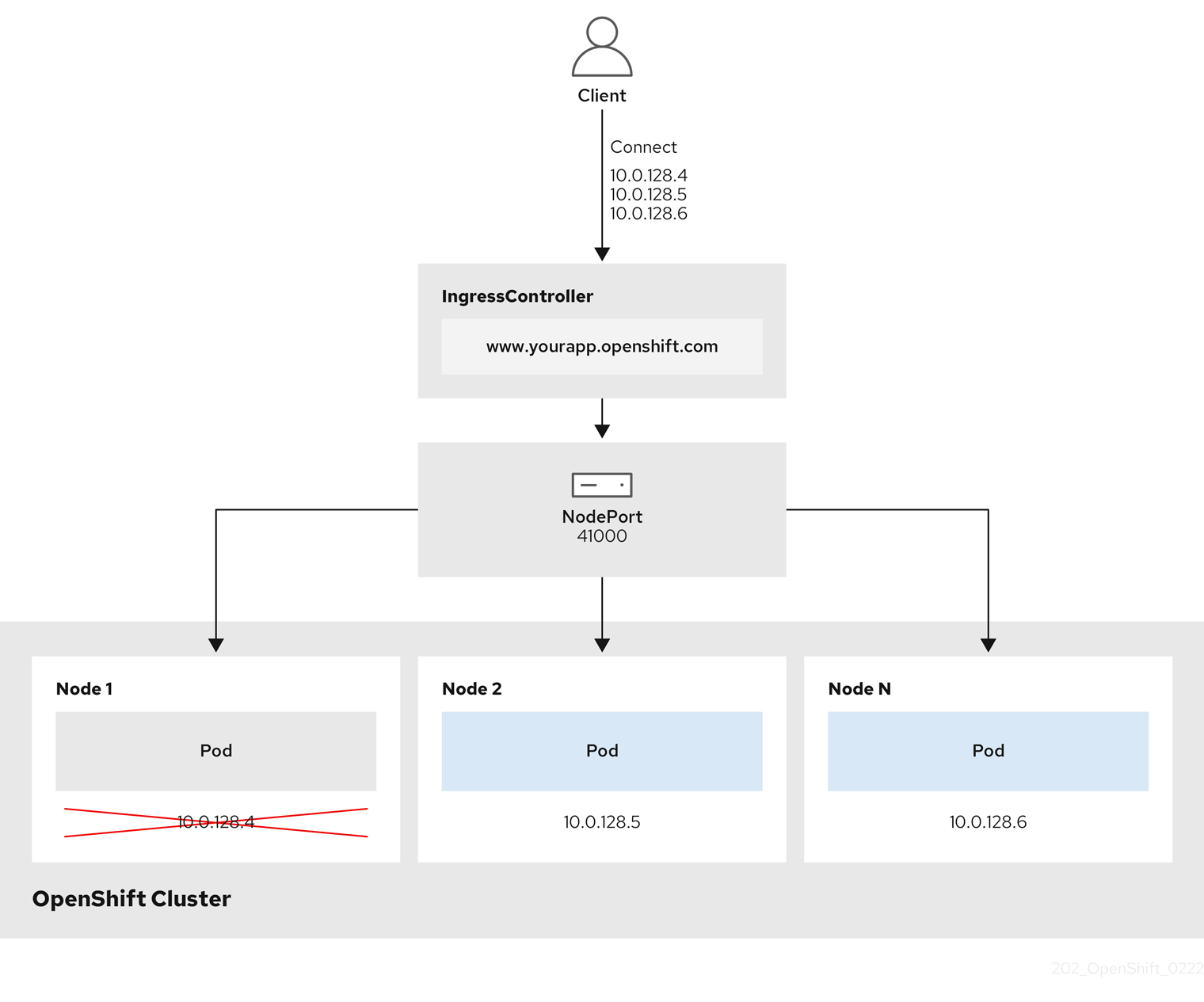
前述の図では、OpenShift Container Platform Ingress NodePort エンドポイントの公開戦略に関する以下のような概念を示しています。
- クラスターで利用可能なノードにはすべて、外部からアクセス可能な独自の IP アドレスが割り当てられています。クラスター内で動作するサービスは、全ノードに固有の NodePort にバインドされます。
-
たとえば、クライアントが図中の IP アドレス
10.0.128.4に接続してダウンしているノードに接続した場合に、ノードポートは、サービスを実行中で利用可能なノードにクライアントを直接接続します。このシナリオでは、ロードバランシングは必要ありません。イメージが示すように、10.0.128.4アドレスがダウンしており、代わりに別の IP アドレスを使用する必要があります。
Ingress Operator は、サービスの .spec.ports[].nodePort フィールドへの更新を無視します。
デフォルトで、ポートは自動的に割り当てられ、各種の統合用のポート割り当てにアクセスできます。ただし、既存のインフラストラクチャーと統合するために静的ポートの割り当てが必要になることがありますが、これは動的ポートに対応して簡単に再設定できない場合があります。静的ノードポートとの統合を実行するには、管理対象のサービスリソースを直接更新できます。
詳細は、NodePort についての Kubernetes サービスについてのドキュメント を参照してください。
HostNetwork エンドポイントの公開ストラテジー
HostNetwork エンドポイントの公開ストラテジーは、Ingress コントローラーがデプロイされるノードポートで Ingress コントローラーを公開します。
HostNetwork エンドポイント公開ストラテジーを持つ Ingress コントローラーには、ノードごとに単一の Pod レプリカのみを設定できます。n のレプリカを使用する場合、それらのレプリカをスケジュールできる n 以上のノードを使用する必要があります。各 Pod はスケジュールされるノードホストでポート 80 および 443 を要求するので、同じノードで別の Pod がそれらのポートを使用している場合、レプリカをノードにスケジュールすることはできません。
6.4. デフォルト Ingress コントローラーの表示
Ingress Operator は、OpenShift Container Platform の中核となる機能であり、追加の設定なしに有効にできます。
すべての新規 OpenShift Container Platform インストールには、ingresscontroller の名前付きのデフォルトがあります。これは、追加の Ingress コントローラーで補足できます。デフォルトの ingresscontroller が削除される場合、Ingress Operator は 1 分以内にこれを自動的に再作成します。
手順
デフォルト Ingress コントローラーを表示します。
$ oc describe --namespace=openshift-ingress-operator ingresscontroller/default
6.5. Ingress Operator ステータスの表示
Ingress Operator のステータスを表示し、検査することができます。
手順
Ingress Operator ステータスを表示します。
$ oc describe clusteroperators/ingress
6.6. Ingress コントローラーログの表示
Ingress コントローラーログを表示できます。
手順
Ingress コントローラーログを表示します。
$ oc logs --namespace=openshift-ingress-operator deployments/ingress-operator
6.7. Ingress コントローラーステータスの表示
特定の Ingress コントローラーのステータスを表示できます。
手順
Ingress コントローラーのステータスを表示します。
$ oc describe --namespace=openshift-ingress-operator ingresscontroller/<name>
6.8. Ingress コントローラーの設定
6.8.1. カスタムデフォルト証明書の設定
管理者として、 Secret リソースを作成し、IngressController カスタムリソース (CR) を編集して Ingress コントローラーがカスタム証明書を使用するように設定できます。
前提条件
- PEM エンコードされたファイルに証明書/キーのペアがなければなりません。ここで、証明書は信頼される認証局またはカスタム PKI で設定されたプライベートの信頼される認証局で署名されます。
証明書が以下の要件を満たしている必要があります。
- 証明書が Ingress ドメインに対して有効化されている必要があります。
-
証明書は拡張を使用して、
subjectAltName拡張を使用して、*.apps.ocp4.example.comなどのワイルドカードドメインを指定します。
IngressControllerCR がなければなりません。デフォルトの CR を使用できます。$ oc --namespace openshift-ingress-operator get ingresscontrollers出力例
NAME AGE default 10m
Intermediate 証明書がある場合、それらはカスタムデフォルト証明書が含まれるシークレットの tls.crt ファイルに組み込まれる必要があります。証明書を指定する際の順序は重要になります。サーバー証明書の後に Intermediate 証明書を一覧表示します。
手順
以下では、カスタム証明書とキーのペアが、現在の作業ディレクトリーの tls.crt および tls.key ファイルにあることを前提とします。tls.crt および tls.key を実際のパス名に置き換えます。さらに、 Secret リソースを作成し、これを IngressController CR で参照する際に、custom-certs-default を別の名前に置き換えます。
このアクションにより、Ingress コントローラーはデプロイメントストラテジーを使用して再デプロイされます。
tls.crtおよびtls.keyファイルを使用して、カスタム証明書を含む Secret リソースをopenshift-ingressnamespace に作成します。$ oc --namespace openshift-ingress create secret tls custom-certs-default --cert=tls.crt --key=tls.keyIngressController CR を、新規証明書シークレットを参照するように更新します。
$ oc patch --type=merge --namespace openshift-ingress-operator ingresscontrollers/default \ --patch '{"spec":{"defaultCertificate":{"name":"custom-certs-default"}}}'更新が正常に行われていることを確認します。
$ echo Q |\ openssl s_client -connect console-openshift-console.apps.<domain>:443 -showcerts 2>/dev/null |\ openssl x509 -noout -subject -issuer -enddateここでは、以下のようになります。
<domain>- クラスターのベースドメイン名を指定します。
出力例
subject=C = US, ST = NC, L = Raleigh, O = RH, OU = OCP4, CN = *.apps.example.com issuer=C = US, ST = NC, L = Raleigh, O = RH, OU = OCP4, CN = example.com notAfter=May 10 08:32:45 2022 GM証明書シークレットの名前は、CR を更新するために使用された値に一致する必要があります。
IngressController CR が変更された後に、Ingress Operator はカスタム証明書を使用できるように Ingress コントローラーのデプロイメントを更新します。
6.8.2. カスタムデフォルト証明書の削除
管理者は、使用する Ingress Controller を設定したカスタム証明書を削除できます。
前提条件
-
cluster-adminロールを持つユーザーとしてクラスターにアクセスできる。 -
OpenShift CLI (
oc) がインストールされている。 - Ingress Controller のカスタムデフォルト証明書を設定している。
手順
カスタム証明書を削除し、OpenShift Container Platform に同梱されている証明書を復元するには、以下のコマンドを入力します。
$ oc patch -n openshift-ingress-operator ingresscontrollers/default \ --type json -p $'- op: remove\n path: /spec/defaultCertificate'クラスターが新しい証明書設定を調整している間、遅延が発生する可能性があります。
検証
元のクラスター証明書が復元されたことを確認するには、次のコマンドを入力します。
$ echo Q | \ openssl s_client -connect console-openshift-console.apps.<domain>:443 -showcerts 2>/dev/null | \ openssl x509 -noout -subject -issuer -enddateここでは、以下のようになります。
<domain>- クラスターのベースドメイン名を指定します。
出力例
subject=CN = *.apps.<domain> issuer=CN = ingress-operator@1620633373 notAfter=May 10 10:44:36 2023 GMT
6.8.3. Ingress コントローラーのスケーリング
Ingress コントローラーは、スループットを増大させるための要件を含む、ルーティングのパフォーマンスや可用性に関する各種要件に対応するために手動でスケーリングできます。oc コマンドは、IngressController リソースのスケーリングに使用されます。以下の手順では、デフォルトの IngressController をスケールアップする例を示します。
手順
デフォルト
IngressControllerの現在の利用可能なレプリカ数を表示します。$ oc get -n openshift-ingress-operator ingresscontrollers/default -o jsonpath='{$.status.availableReplicas}'出力例
2oc patchコマンドを使用して、デフォルトのIngressControllerを必要なレプリカ数にスケーリングします。以下の例では、デフォルトのIngressControllerを 3 つのレプリカにスケーリングしています。$ oc patch -n openshift-ingress-operator ingresscontroller/default --patch '{"spec":{"replicas": 3}}' --type=merge出力例
ingresscontroller.operator.openshift.io/default patchedデフォルトの
IngressControllerが指定したレプリカ数にスケーリングされていることを確認します。$ oc get -n openshift-ingress-operator ingresscontrollers/default -o jsonpath='{$.status.availableReplicas}'出力例
3
スケーリングは、必要な数のレプリカを作成するのに時間がかかるため、すぐに実行できるアクションではありません。
6.8.4. Ingress アクセスロギングの設定
アクセスログを有効にするように Ingress コントローラーを設定できます。大量のトラフィックを受信しないクラスターがある場合、サイドカーにログインできます。クラスターのトラフィックが多い場合、ロギングスタックの容量を超えないようにしたり、OpenShift Container Platform 外のロギングインフラストラクチャーと統合したりするために、ログをカスタム syslog エンドポイントに転送することができます。アクセスログの形式を指定することもできます。
コンテナーロギングは、既存の Syslog ロギングインフラストラクチャーがない場合や、Ingress コントローラーで問題を診断する際に短期間使用する場合に、低トラフィックのクラスターのアクセスログを有効にするのに役立ちます。
アクセスログが OpenShift Logging スタックの容量を超える可能性があるトラフィックの多いクラスターや、ロギングソリューションが既存の Syslog ロギングインフラストラクチャーと統合する必要のある環境では、syslog が必要です。Syslog のユースケースは重複する可能性があります。
前提条件
-
cluster-admin権限を持つユーザーとしてログインしている。
手順
サイドカーへの Ingress アクセスロギングを設定します。
Ingress アクセスロギングを設定するには、
spec.logging.access.destinationを使用して宛先を指定する必要があります。サイドカーコンテナーへのロギングを指定するには、Containerspec.logging.access.destination.typeを指定する必要があります。以下の例は、コンテナーContainerの宛先に対してログ記録する Ingress コントローラー定義です。apiVersion: operator.openshift.io/v1 kind: IngressController metadata: name: default namespace: openshift-ingress-operator spec: replicas: 2 logging: access: destination: type: ContainerIngress コントローラーをサイドカーに対してログを記録するように設定すると、Operator は Ingress コントローラー Pod 内に
logsという名前のコンテナーを作成します。$ oc -n openshift-ingress logs deployment.apps/router-default -c logs出力例
2020-05-11T19:11:50.135710+00:00 router-default-57dfc6cd95-bpmk6 router-default-57dfc6cd95-bpmk6 haproxy[108]: 174.19.21.82:39654 [11/May/2020:19:11:50.133] public be_http:hello-openshift:hello-openshift/pod:hello-openshift:hello-openshift:10.128.2.12:8080 0/0/1/0/1 200 142 - - --NI 1/1/0/0/0 0/0 "GET / HTTP/1.1"
Syslog エンドポイントへの Ingress アクセスロギングを設定します。
Ingress アクセスロギングを設定するには、
spec.logging.access.destinationを使用して宛先を指定する必要があります。Syslog エンドポイント宛先へのロギングを指定するには、spec.logging.access.destination.typeにSyslogを指定する必要があります。宛先タイプがSyslogの場合、spec.logging.access.destination.syslog.endpointを使用して宛先エンドポイントも指定する必要があります。また、spec.logging.access.destination.syslog.facilityを使用してファシリティーを指定できます。以下の例は、Syslog宛先に対してログを記録する Ingress コントローラーの定義です。apiVersion: operator.openshift.io/v1 kind: IngressController metadata: name: default namespace: openshift-ingress-operator spec: replicas: 2 logging: access: destination: type: Syslog syslog: address: 1.2.3.4 port: 10514注記syslog宛先ポートは UDP である必要があります。
特定のログ形式で Ingress アクセスロギングを設定します。
spec.logging.access.httpLogFormatを指定して、ログ形式をカスタマイズできます。以下の例は、IP アドレスが 1.2.3.4 およびポート 10514 のsyslogエンドポイントに対してログを記録する Ingress コントローラーの定義です。apiVersion: operator.openshift.io/v1 kind: IngressController metadata: name: default namespace: openshift-ingress-operator spec: replicas: 2 logging: access: destination: type: Syslog syslog: address: 1.2.3.4 port: 10514 httpLogFormat: '%ci:%cp [%t] %ft %b/%s %B %bq %HM %HU %HV'
Ingress アクセスロギングを無効にします。
Ingress アクセスロギングを無効にするには、
spec.loggingまたはspec.logging.accessを空のままにします。apiVersion: operator.openshift.io/v1 kind: IngressController metadata: name: default namespace: openshift-ingress-operator spec: replicas: 2 logging: access: null
6.8.5. Ingress コントローラーのシャード化
トラフィックがクラスターに送信される主要なメカニズムとして、Ingress コントローラーまたはルーターへの要求が大きくなる可能性があります。クラスター管理者は、以下を実行するためにルートをシャード化できます。
- Ingress コントローラーまたはルーターを複数のルートに分散し、変更に対する応答を加速します。
- 特定のルートを他のルートとは異なる信頼性の保証を持つように割り当てます。
- 特定の Ingress コントローラーに異なるポリシーを定義することを許可します。
- 特定のルートのみが追加機能を使用することを許可します。
- たとえば、異なるアドレスで異なるルートを公開し、内部ユーザーおよび外部ユーザーが異なるルートを認識できるようにします。
Ingress コントローラーは、ルートラベルまたは namespace ラベルのいずれかをシャード化の方法として使用できます。
6.8.5.1. ルートラベルを使用した Ingress コントローラーのシャード化の設定
ルートラベルを使用した Ingress コントローラーのシャード化とは、Ingress コントローラーがルートセレクターによって選択される任意 namespace の任意のルートを提供することを意味します。
Ingress コントローラーのシャード化は、一連の Ingress コントローラー間で着信トラフィックの負荷を分散し、トラフィックを特定の Ingress コントローラーに分離する際に役立ちます。たとえば、Company A のトラフィックをある Ingress コントローラーに指定し、Company B を別の Ingress コントローラーに指定できます。
手順
router-internal.yamlファイルを編集します。# cat router-internal.yaml apiVersion: v1 items: - apiVersion: operator.openshift.io/v1 kind: IngressController metadata: name: sharded namespace: openshift-ingress-operator spec: domain: <apps-sharded.basedomain.example.net> nodePlacement: nodeSelector: matchLabels: node-role.kubernetes.io/worker: "" routeSelector: matchLabels: type: sharded status: {} kind: List metadata: resourceVersion: "" selfLink: ""Ingress コントローラーの
router-internal.yamlファイルを適用します。# oc apply -f router-internal.yamlIngress コントローラーは、
type: shardedというラベルのある namespace のルートを選択します。
6.8.5.2. namespace ラベルを使用した Ingress コントローラーのシャード化の設定
namespace ラベルを使用した Ingress コントローラーのシャード化とは、Ingress コントローラーが namespace セレクターによって選択される任意の namespace の任意のルートを提供することを意味します。
Ingress コントローラーのシャード化は、一連の Ingress コントローラー間で着信トラフィックの負荷を分散し、トラフィックを特定の Ingress コントローラーに分離する際に役立ちます。たとえば、Company A のトラフィックをある Ingress コントローラーに指定し、Company B を別の Ingress コントローラーに指定できます。
Keepalived Ingress VIP をデプロイする場合は、endpoint Publishing Strategy パラメーターに Host Network の値が割り当てられた、デフォルト以外の Ingress Controller をデプロイしないでください。デプロイしてしまうと、問題が発生する可能性があります。endpoint Publishing Strategy に Host Network ではなく、Node Port という値を使用してください。
手順
router-internal.yamlファイルを編集します。# cat router-internal.yaml出力例
apiVersion: v1 items: - apiVersion: operator.openshift.io/v1 kind: IngressController metadata: name: sharded namespace: openshift-ingress-operator spec: domain: <apps-sharded.basedomain.example.net> nodePlacement: nodeSelector: matchLabels: node-role.kubernetes.io/worker: "" namespaceSelector: matchLabels: type: sharded status: {} kind: List metadata: resourceVersion: "" selfLink: ""Ingress コントローラーの
router-internal.yamlファイルを適用します。# oc apply -f router-internal.yamlIngress コントローラーは、
type: shardedというラベルのある namespace セレクターによって選択される namespace のルートを選択します。
6.8.6. 内部ロードバランサーを使用するように Ingress コントローラーを設定する
クラウドプラットフォームで Ingress コントローラーを作成する場合、Ingress コントローラーはデフォルトでパブリッククラウドロードバランサーによって公開されます。管理者は、内部クラウドロードバランサーを使用する Ingress コントローラーを作成できます。
クラウドプロバイダーが Microsoft Azure の場合、ノードを参照するパブリックロードバランサーが少なくとも 1 つ必要です。これがない場合、すべてのノードがインターネットへの egress 接続を失います。
IngressController オブジェクトの スコープ を変更する必要がある場合、IngressController オブジェクトを削除してから、これを再作成する必要があります。カスタムリソース (CR) の作成後に .spec.endpointPublishingStrategy.loadBalancer.scope パラメーターを変更することはできません。
図6.2 ロードバランサーの図
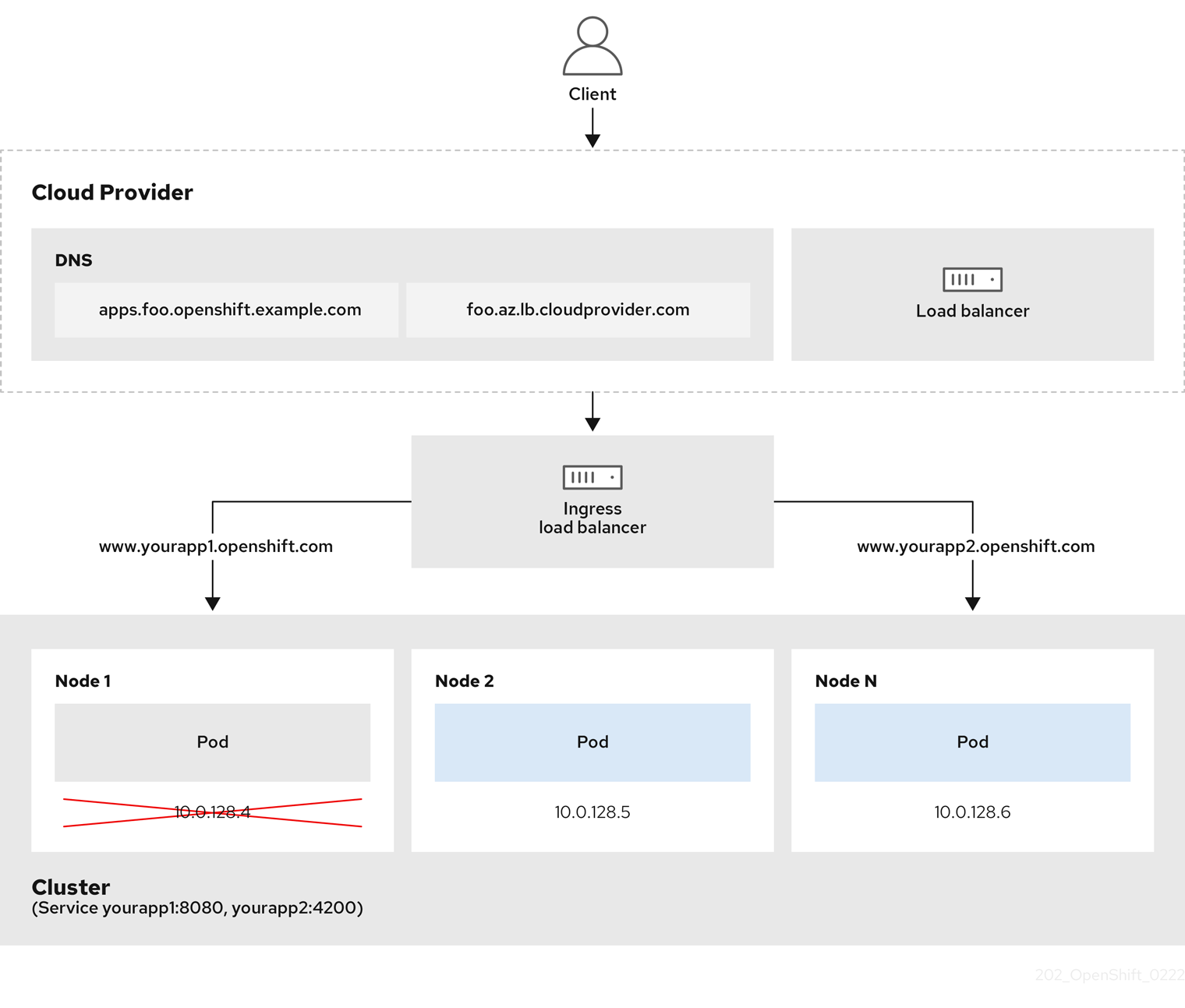
前述の図では、OpenShift Container Platform Ingress LoadBalancerService エンドポイントの公開戦略に関する以下のような概念を示しています。
- 負荷は、外部からクラウドプロバイダーのロードバランサーを使用するか、内部から OpenShift Ingress Controller Load Balancer を使用して、分散できます。
- ロードバランサーのシングル IP アドレスと、図にあるクラスターのように、8080 や 4200 といった馴染みのあるポートを使用することができます。
- 外部のロードバランサーからのトラフィックは、ダウンしたノードのインスタンスで記載されているように、Pod の方向に進められ、ロードバランサーが管理します。実装の詳細については、Kubernetes サービスドキュメント を参照してください。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
以下の例のように、
<name>-ingress-controller.yamlという名前のファイルにIngressControllerカスタムリソース (CR) を作成します。apiVersion: operator.openshift.io/v1 kind: IngressController metadata: namespace: openshift-ingress-operator name: <name>1 spec: domain: <domain>2 endpointPublishingStrategy: type: LoadBalancerService loadBalancer: scope: Internal3 以下のコマンドを実行して、直前の手順で定義された Ingress コントローラーを作成します。
$ oc create -f <name>-ingress-controller.yaml1 - 1
<name>をIngressControllerオブジェクトの名前に置き換えます。
オプション: 以下のコマンドを実行して Ingress コントローラーが作成されていることを確認します。
$ oc --all-namespaces=true get ingresscontrollers
6.8.7. クラスターを内部に配置するようにのデフォルト Ingress コントローラーを設定する
削除や再作成を実行して、クラスターを内部に配置するように default Ingress コントローラーを設定できます。
クラウドプロバイダーが Microsoft Azure の場合、ノードを参照するパブリックロードバランサーが少なくとも 1 つ必要です。これがない場合、すべてのノードがインターネットへの egress 接続を失います。
IngressController オブジェクトの スコープ を変更する必要がある場合、IngressController オブジェクトを削除してから、これを再作成する必要があります。カスタムリソース (CR) の作成後に .spec.endpointPublishingStrategy.loadBalancer.scope パラメーターを変更することはできません。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
削除や再作成を実行して、クラスターを内部に配置するように
defaultIngress コントローラーを設定します。$ oc replace --force --wait --filename - <<EOF apiVersion: operator.openshift.io/v1 kind: IngressController metadata: namespace: openshift-ingress-operator name: default spec: endpointPublishingStrategy: type: LoadBalancerService loadBalancer: scope: Internal EOF
6.8.8. ルートの受付ポリシーの設定
管理者およびアプリケーション開発者は、同じドメイン名を持つ複数の namespace でアプリケーションを実行できます。これは、複数のチームが同じホスト名で公開されるマイクロサービスを開発する組織を対象としています。
複数の namespace での要求の許可は、namespace 間の信頼のあるクラスターに対してのみ有効にする必要があります。有効にしないと、悪意のあるユーザーがホスト名を乗っ取る可能性があります。このため、デフォルトの受付ポリシーは複数の namespace 間でのホスト名の要求を許可しません。
前提条件
- クラスター管理者の権限。
手順
以下のコマンドを使用して、
ingresscontrollerリソース変数の.spec.routeAdmissionフィールドを編集します。$ oc -n openshift-ingress-operator patch ingresscontroller/default --patch '{"spec":{"routeAdmission":{"namespaceOwnership":"InterNamespaceAllowed"}}}' --type=mergeイメージコントローラー設定例
spec: routeAdmission: namespaceOwnership: InterNamespaceAllowed ...
6.8.9. ワイルドカードルートの使用
HAProxy Ingress コントローラーにはワイルドカードルートのサポートがあります。Ingress Operator は wildcardPolicy を使用して、Ingress コントローラーの ROUTER_ALLOW_WILDCARD_ROUTES 環境変数を設定します。
Ingress コントローラーのデフォルトの動作では、ワイルドカードポリシーの None (既存の IngressController リソースとの後方互換性がある) を持つルートを許可します。
手順
ワイルドカードポリシーを設定します。
以下のコマンドを使用して
IngressControllerリソースを編集します。$ oc edit IngressControllerspecの下で、wildcardPolicyフィールドをWildcardsDisallowedまたはWildcardsAllowedに設定します。spec: routeAdmission: wildcardPolicy: WildcardsDisallowed # or WildcardsAllowed
6.8.10. X-Forwarded ヘッダーの使用
Forwarded および X-Forwarded-For を含む HTTP ヘッダーの処理方法についてのポリシーを指定するように HAProxy Ingress コントローラーを設定します。Ingress Operator は HTTPHeaders フィールドを使用して、Ingress コントローラーの ROUTER_SET_FORWARDED_HEADERS 環境変数を設定します。
手順
Ingress コントローラー用に
HTTPHeadersフィールドを設定します。以下のコマンドを使用して
IngressControllerリソースを編集します。$ oc edit IngressControllerspecの下で、HTTPHeadersポリシーフィールドをAppend、Replace、IfNone、またはNeverに設定します。apiVersion: operator.openshift.io/v1 kind: IngressController metadata: name: default namespace: openshift-ingress-operator spec: httpHeaders: forwardedHeaderPolicy: Append
使用例
クラスター管理者として、以下を実行できます。
Ingress コントローラーに転送する前に、
X-Forwarded-Forヘッダーを各リクエストに挿入する外部プロキシーを設定します。ヘッダーを変更せずに渡すように Ingress コントローラーを設定するには、
neverポリシーを指定します。これにより、Ingress コントローラーはヘッダーを設定しなくなり、アプリケーションは外部プロキシーが提供するヘッダーのみを受信します。外部プロキシーが外部クラスター要求を設定する
X-Forwarded-Forヘッダーを変更せずに渡すように Ingress コントローラーを設定します。外部プロキシーを通過しない内部クラスター要求に
X-Forwarded-Forヘッダーを設定するように Ingress コントローラーを設定するには、if-noneポリシーを指定します。外部プロキシー経由で HTTP 要求にヘッダーがすでに設定されている場合、Ingress コントローラーはこれを保持します。要求がプロキシーを通過していないためにヘッダーがない場合、Ingress コントローラーはヘッダーを追加します。
アプリケーション開発者として、以下を実行できます。
X-Forwarded-Forヘッダーを挿入するアプリケーション固有の外部プロキシーを設定します。他の Route のポリシーに影響を与えずに、アプリケーションの Route 用にヘッダーを変更せずに渡すように Ingress コントローラーを設定するには、アプリケーションの Route に アノテーション
haproxy.router.openshift.io/set-forwarded-headers: if-noneまたはhaproxy.router.openshift.io/set-forwarded-headers: neverを追加します。注記Ingress コントローラーのグローバルに設定された値とは別に、
haproxy.router.openshift.io/set-forwarded-headersアノテーションをルートごとに設定できます。
6.8.11. HTTP/2 Ingress 接続の有効化
HAProxy で透過的なエンドツーエンド HTTP/2 接続を有効にすることができます。これにより、アプリケーションの所有者は、単一接続、ヘッダー圧縮、バイナリーストリームなど、HTTP/2 プロトコル機能を使用できます。
個別の Ingress コントローラーまたはクラスター全体について、HTTP/2 接続を有効にすることができます。
クライアントから HAProxy への接続について HTTP/2 の使用を有効にするために、ルートはカスタム証明書を指定する必要があります。デフォルトの証明書を使用するルートは HTTP/2 を使用することができません。この制限は、クライアントが同じ証明書を使用する複数の異なるルートに接続を再使用するなどの、接続の結合 (coalescing) の問題を回避するために必要です。
HAProxy からアプリケーション Pod への接続は、re-encrypt ルートのみに HTTP/2 を使用でき、edge termination ルートまたは非セキュアなルートには使用しません。この制限は、HAProxy が TLS 拡張である Application-Level Protocol Negotiation (ALPN) を使用してバックエンドで HTTP/2 の使用をネゴシエートするためにあります。そのため、エンドツーエンドの HTTP/2 はパススルーおよび re-encrypt 使用できますが、非セキュアなルートまたは edge termination ルートでは使用できません。
再暗号化ルートで WebSocket を使用し、Ingress Controller で HTTP/2 を有効にするには、HTTP/2 を介した WebSocket のサポートが必要です。HTTP/2 上の WebSockets は HAProxy 2.4 の機能であり、現時点では OpenShift Container Platform ではサポートされていません。
パススルー以外のルートの場合、Ingress コントローラーはクライアントからの接続とは独立してアプリケーションへの接続をネゴシエートします。つまり、クライアントが Ingress コントローラーに接続して HTTP/1.1 をネゴシエートし、Ingress コントローラーは次にアプリケーションに接続して HTTP/2 をネゴシエートし、アプリケーションへの HTTP/2 接続を使用してクライアント HTTP/1.1 接続からの要求の転送を実行できます。Ingress コントローラーは WebSocket を HTTP/2 に転送できず、その HTTP/2 接続を WebSocket に対してアップグレードできないため、クライアントが後に HTTP/1.1 から WebSocket プロトコルに接続をアップグレードしようとすると問題が発生します。そのため、WebSocket 接続を受け入れることが意図されたアプリケーションがある場合、これは HTTP/2 プロトコルのネゴシエートを許可できないようにする必要があります。そうしないと、クライアントは WebSocket プロトコルへのアップグレードに失敗します。
手順
単一 Ingress コントローラーで HTTP/2 を有効にします。
Ingress コントローラーで HTTP/2 を有効にするには、
oc annotateコマンドを入力します。$ oc -n openshift-ingress-operator annotate ingresscontrollers/<ingresscontroller_name> ingress.operator.openshift.io/default-enable-http2=true<ingresscontroller_name>をアノテーションを付ける Ingress コントローラーの名前に置き換えます。
クラスター全体で HTTP/2 を有効にします。
クラスター全体で HTTP/2 を有効にするには、
oc annotateコマンドを入力します。$ oc annotate ingresses.config/cluster ingress.operator.openshift.io/default-enable-http2=true
6.8.12. appsDomain オプションを使用した代替クラスタードメインの指定
クラスター管理者は、appsDomain フィールドを設定して、ユーザーが作成したルートのデフォルトのクラスタードメインの代わりとなるものを指定できます。appsDomain フィールドは、domain フィールドで指定されているデフォルトの代わりに使用する OpenShift Container Platform のオプションのドメインです。代替ドメインを指定する場合、これは新規ルートのデフォルトホストを判別できるようにする目的でデフォルトのクラスタードメインを上書きします。
たとえば、所属企業の DNS ドメインを、クラスター上で実行されるアプリケーションのルートおよび ingress のデフォルトドメインとして使用できます。
前提条件
- OpenShift Container Platform クラスターをデプロイしていること。
-
ocコマンドラインインターフェイスをインストールしている。
手順
ユーザーが作成するルートに代替のデフォルトドメインを指定して
appsDomainフィールドを設定します。Ingress
clusterリソースを編集します。$ oc edit ingresses.config/cluster -o yamlYAML ファイルを編集します。
test.example.comへのapps Domainの設定例apiVersion: config.openshift.io/v1 kind: Ingress metadata: name: cluster spec: domain: apps.example.com1 appsDomain: <test.example.com>2
ルートを公開し、ルートドメインの変更を確認して、既存のルートに、
appsDomainフィールドで指定したドメイン名が含まれていることを確認します。注記ルートを公開する前に
openshift-apiserverがローリング更新を終了するのを待機します。ルートを公開します。
$ oc expose service hello-openshift route.route.openshift.io/hello-openshift exposed出力例:
$ oc get routes NAME HOST/PORT PATH SERVICES PORT TERMINATION WILDCARD hello-openshift hello_openshift-<my_project>.test.example.com hello-openshift 8080-tcp None
第7章 エンドポイントへの接続の確認
Cluster Network Operator (CNO) は、クラスター内のリソース間の接続ヘルスチェックを実行するコントローラーである接続性チェックコントローラーを実行します。ヘルスチェックの結果を確認して、調査している問題が原因で生じる接続の問題を診断したり、ネットワーク接続を削除したりできます。
7.1. 実行する接続ヘルスチェック
クラスターリソースにアクセスできることを確認するには、以下のクラスター API サービスのそれぞれに対して TCP 接続が行われます。
- Kubernetes API サーバーサービス
- Kubernetes API サーバーエンドポイント
- OpenShift API サーバーサービス
- OpenShift API サーバーエンドポイント
- ロードバランサー
サービスおよびサービスエンドポイントがクラスター内のすべてのノードで到達可能であることを確認するには、以下の各ターゲットに対して TCP 接続が行われます。
- ヘルスチェックターゲットサービス
- ヘルスチェックターゲットエンドポイント
7.2. 接続ヘルスチェックの実装
接続チェックコントローラーは、クラスター内の接続検証チェックをオーケストレーションします。接続テストの結果は、openshift-network-diagnostics namespace の PodNetworkConnectivity オブジェクトに保存されます。接続テストは、1 分ごとに並行して実行されます。
Cluster Network Operator (CNO) は、接続性ヘルスチェックを送受信するためにいくつかのリソースをクラスターにデプロイします。
- ヘルスチェックのソース
-
このプログラムは、
Deploymentオブジェクトで管理される単一の Pod レプリカセットにデプロイします。このプログラムはPodNetworkConnectivityオブジェクトを消費し、各オブジェクトで指定されるspec.targetEndpointに接続されます。 - ヘルスチェックのターゲット
- クラスターのすべてのノードにデーモンセットの一部としてデプロイされた Pod。Pod はインバウンドのヘルスチェックをリッスンします。すべてのノードにこの Pod が存在すると、各ノードへの接続をテストすることができます。
7.3. PodNetworkConnectivityCheck オブジェクトフィールド
PodNetworkConnectivityCheck オブジェクトフィールドについては、以下の表で説明されています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
以下の形式のオブジェクトの名前:
|
|
|
|
オブジェクトが関連付けられる namespace。この値は、常に |
|
|
|
接続チェックの起点となる Pod の名前 (例: |
|
|
|
|
|
|
| 使用する TLS 証明書の設定。 |
|
|
| 使用される TLS 証明書の名前 (ある場合)。デフォルト値は空の文字列です。 |
|
|
| 接続テストの状態を表す、および最近の接続の成功および失敗についてのログ。 |
|
|
| 接続チェックと最新のステータスと以前のステータス。 |
|
|
| 試行に失敗した接続テストのログ。 |
|
|
| 停止が生じた期間が含まれる接続テストのログ。 |
|
|
| 試行に成功した接続テストのログ。 |
以下の表は、status.conditions 配列内のオブジェクトのフィールドについて説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
| 接続の条件がある状態から別の状態に移行した時間。 |
|
|
| 人が判読できる形式の最後の移行についての詳細。 |
|
|
| マシンの読み取り可能な形式での移行の最後のステータス。 |
|
|
| 状態のテータス。 |
|
|
| 状態のタイプ。 |
以下の表は、status.conditions 配列内のオブジェクトのフィールドについて説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
| 接続の障害が解決された時点からのタイムスタンプ。 |
|
|
| 接続ログエントリー (停止の正常な終了に関連するログエントリーを含む)。 |
|
|
| 人が判読できる形式の停止について詳細情報の要約。 |
|
|
| 接続の障害が最初に検知された時点からのタイムスタンプ。 |
|
|
| 元の障害を含む接続ログのエントリー。 |
接続ログフィールド
接続ログエントリーのフィールドの説明は以下の表で説明されています。オブジェクトは以下のフィールドで使用されます。
-
status.failures[] -
status.successes[] -
status.outages[].startLogs[] -
status.outages[].endLogs[]
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
| アクションの期間を記録します。 |
|
|
| ステータスを人が判読できる形式で提供します。 |
|
|
|
ステータスの理由をマシンが判読できる形式で提供します。値は |
|
|
| ログエントリーが成功または失敗であるかを示します。 |
|
|
| 接続チェックの開始時間。 |
7.4. エンドポイントのネットワーク接続の確認
クラスター管理者は、API サーバー、ロードバランサー、サービス、または Pod などのエンドポイントの接続を確認できます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-adminロールを持つユーザーとしてクラスターにアクセスできる。
手順
現在の
PodNetworkConnectivityCheckオブジェクトを一覧表示するには、以下のコマンドを入力します。$ oc get podnetworkconnectivitycheck -n openshift-network-diagnostics出力例
NAME AGE network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0 75m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-1 73m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-2 75m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-kubernetes-apiserver-service-cluster 75m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-kubernetes-default-service-cluster 75m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-load-balancer-api-external 75m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-load-balancer-api-internal 75m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-network-check-target-ci-ln-x5sv9rb-f76d1-4rzrp-master-0 75m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-network-check-target-ci-ln-x5sv9rb-f76d1-4rzrp-master-1 75m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-network-check-target-ci-ln-x5sv9rb-f76d1-4rzrp-master-2 75m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-network-check-target-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh 74m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-network-check-target-ci-ln-x5sv9rb-f76d1-4rzrp-worker-c-n8mbf 74m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-network-check-target-ci-ln-x5sv9rb-f76d1-4rzrp-worker-d-4hnrz 74m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-network-check-target-service-cluster 75m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-openshift-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0 75m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-openshift-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-1 75m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-openshift-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-2 74m network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-openshift-apiserver-service-cluster 75m接続テストログを表示します。
- 直前のコマンドの出力から、接続ログを確認するエンドポイントを特定します。
オブジェクトを表示するには、以下のコマンドを入力します。
$ oc get podnetworkconnectivitycheck <name> \ -n openshift-network-diagnostics -o yamlここで、
<name>はPodNetworkConnectivityCheckオブジェクトの名前を指定します。出力例
apiVersion: controlplane.operator.openshift.io/v1alpha1 kind: PodNetworkConnectivityCheck metadata: name: network-check-source-ci-ln-x5sv9rb-f76d1-4rzrp-worker-b-6xdmh-to-kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0 namespace: openshift-network-diagnostics ... spec: sourcePod: network-check-source-7c88f6d9f-hmg2f targetEndpoint: 10.0.0.4:6443 tlsClientCert: name: "" status: conditions: - lastTransitionTime: "2021-01-13T20:11:34Z" message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: tcp connection to 10.0.0.4:6443 succeeded' reason: TCPConnectSuccess status: "True" type: Reachable failures: - latency: 2.241775ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: failed to establish a TCP connection to 10.0.0.4:6443: dial tcp 10.0.0.4:6443: connect: connection refused' reason: TCPConnectError success: false time: "2021-01-13T20:10:34Z" - latency: 2.582129ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: failed to establish a TCP connection to 10.0.0.4:6443: dial tcp 10.0.0.4:6443: connect: connection refused' reason: TCPConnectError success: false time: "2021-01-13T20:09:34Z" - latency: 3.483578ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: failed to establish a TCP connection to 10.0.0.4:6443: dial tcp 10.0.0.4:6443: connect: connection refused' reason: TCPConnectError success: false time: "2021-01-13T20:08:34Z" outages: - end: "2021-01-13T20:11:34Z" endLogs: - latency: 2.032018ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: tcp connection to 10.0.0.4:6443 succeeded' reason: TCPConnect success: true time: "2021-01-13T20:11:34Z" - latency: 2.241775ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: failed to establish a TCP connection to 10.0.0.4:6443: dial tcp 10.0.0.4:6443: connect: connection refused' reason: TCPConnectError success: false time: "2021-01-13T20:10:34Z" - latency: 2.582129ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: failed to establish a TCP connection to 10.0.0.4:6443: dial tcp 10.0.0.4:6443: connect: connection refused' reason: TCPConnectError success: false time: "2021-01-13T20:09:34Z" - latency: 3.483578ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: failed to establish a TCP connection to 10.0.0.4:6443: dial tcp 10.0.0.4:6443: connect: connection refused' reason: TCPConnectError success: false time: "2021-01-13T20:08:34Z" message: Connectivity restored after 2m59.999789186s start: "2021-01-13T20:08:34Z" startLogs: - latency: 3.483578ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: failed to establish a TCP connection to 10.0.0.4:6443: dial tcp 10.0.0.4:6443: connect: connection refused' reason: TCPConnectError success: false time: "2021-01-13T20:08:34Z" successes: - latency: 2.845865ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: tcp connection to 10.0.0.4:6443 succeeded' reason: TCPConnect success: true time: "2021-01-13T21:14:34Z" - latency: 2.926345ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: tcp connection to 10.0.0.4:6443 succeeded' reason: TCPConnect success: true time: "2021-01-13T21:13:34Z" - latency: 2.895796ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: tcp connection to 10.0.0.4:6443 succeeded' reason: TCPConnect success: true time: "2021-01-13T21:12:34Z" - latency: 2.696844ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: tcp connection to 10.0.0.4:6443 succeeded' reason: TCPConnect success: true time: "2021-01-13T21:11:34Z" - latency: 1.502064ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: tcp connection to 10.0.0.4:6443 succeeded' reason: TCPConnect success: true time: "2021-01-13T21:10:34Z" - latency: 1.388857ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: tcp connection to 10.0.0.4:6443 succeeded' reason: TCPConnect success: true time: "2021-01-13T21:09:34Z" - latency: 1.906383ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: tcp connection to 10.0.0.4:6443 succeeded' reason: TCPConnect success: true time: "2021-01-13T21:08:34Z" - latency: 2.089073ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: tcp connection to 10.0.0.4:6443 succeeded' reason: TCPConnect success: true time: "2021-01-13T21:07:34Z" - latency: 2.156994ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: tcp connection to 10.0.0.4:6443 succeeded' reason: TCPConnect success: true time: "2021-01-13T21:06:34Z" - latency: 1.777043ms message: 'kubernetes-apiserver-endpoint-ci-ln-x5sv9rb-f76d1-4rzrp-master-0: tcp connection to 10.0.0.4:6443 succeeded' reason: TCPConnect success: true time: "2021-01-13T21:05:34Z"
第8章 ノードポートサービス範囲の設定
クラスター管理者は、利用可能なノードのポート範囲を拡張できます。クラスターで多数のノードポートが使用される場合、利用可能なポートの数を増やす必要がある場合があります。
デフォルトのポート範囲は 30000-32767 です。最初にデフォルト範囲を超えて拡張した場合でも、ポート範囲を縮小することはできません。
8.1. 前提条件
-
クラスターインフラストラクチャーは、拡張された範囲内で指定するポートへのアクセスを許可する必要があります。たとえば、ノードのポート範囲を
30000-32900に拡張する場合、ファイアウォールまたはパケットフィルターリングの設定によりこれに含まれるポート範囲32768-32900を許可する必要があります。
8.2. ノードのポート範囲の拡張
クラスターのノードポート範囲を拡張できます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてクラスターにログインすること。
手順
ノードのポート範囲を拡張するには、以下のコマンドを入力します。
<port>を、新規の範囲内で最大のポート番号に置き換えます。$ oc patch network.config.openshift.io cluster --type=merge -p \ '{ "spec": { "serviceNodePortRange": "30000-<port>" } }'出力例
network.config.openshift.io/cluster patched設定がアクティブであることを確認するには、以下のコマンドを入力します。更新が適用されるまでに数分の時間がかかることがあります。
$ oc get configmaps -n openshift-kube-apiserver config \ -o jsonpath="{.data['config\.yaml']}" | \ grep -Eo '"service-node-port-range":["[[:digit:]]+-[[:digit:]]+"]'出力例
"service-node-port-range":["30000-33000"]
第9章 ベアメタルクラスターでの SCTP (Stream Control Transmission Protocol) の使用
クラスター管理者は、クラスターで SCTP (Stream Control Transmission Protocol) を使用できます。
9.1. OpenShift Container Platform での SCTP (Stream Control Transmission Protocol) のサポート
クラスター管理者は、クラスターのホストで SCTP を有効にできます。Red Hat Enterprise Linux CoreOS (RHCOS) で、SCTP モジュールはデフォルトで無効にされています。
SCTP は、IP ネットワークの上部で実行される信頼できるメッセージベースのプロトコルです。
これを有効にすると、SCTP を Pod、サービス、およびネットワークポリシーでプロトコルとして使用できます。Service オブジェクトは、type パラメーターを ClusterIP または NodePort のいずれかの値に設定して定義する必要があります。
9.1.1. SCTP プロトコルを使用した設定例
protocol パラメーターを Pod またはサービスリソース定義の SCTP 値に設定して、Pod またはサービスを SCTP を使用するように設定できます。
以下の例では、Pod は SCTP を使用するように設定されています。
apiVersion: v1
kind: Pod
metadata:
namespace: project1
name: example-pod
spec:
containers:
- name: example-pod
...
ports:
- containerPort: 30100
name: sctpserver
protocol: SCTP以下の例では、サービスは SCTP を使用するように設定されています。
apiVersion: v1
kind: Service
metadata:
namespace: project1
name: sctpserver
spec:
...
ports:
- name: sctpserver
protocol: SCTP
port: 30100
targetPort: 30100
type: ClusterIP
以下の例では、NetworkPolicy オブジェクトは、特定のラベルの付いた Pod からポート 80 の SCTP ネットワークトラフィックに適用するように設定されます。
kind: NetworkPolicy
apiVersion: networking.k8s.io/v1
metadata:
name: allow-sctp-on-http
spec:
podSelector:
matchLabels:
role: web
ingress:
- ports:
- protocol: SCTP
port: 809.2. SCTP (Stream Control Transmission Protocol) の有効化
クラスター管理者は、クラスターのワーカーノードでブラックリストに指定した SCTP カーネルモジュールを読み込み、有効にできます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-adminロールを持つユーザーとしてクラスターにアクセスできる。
手順
以下の YAML 定義が含まれる
load-sctp-module.yamlという名前のファイルを作成します。apiVersion: machineconfiguration.openshift.io/v1 kind: MachineConfig metadata: name: load-sctp-module labels: machineconfiguration.openshift.io/role: worker spec: config: ignition: version: 3.2.0 storage: files: - path: /etc/modprobe.d/sctp-blacklist.conf mode: 0644 overwrite: true contents: source: data:, - path: /etc/modules-load.d/sctp-load.conf mode: 0644 overwrite: true contents: source: data:,sctpMachineConfigオブジェクトを作成するには、以下のコマンドを入力します。$ oc create -f load-sctp-module.yamlオプション: MachineConfig Operator が設定変更を適用している間にノードのステータスを確認するには、以下のコマンドを入力します。ノードのステータスが
Readyに移行すると、設定の更新が適用されます。$ oc get nodes
9.3. SCTP (Stream Control Transmission Protocol) が有効になっていることの確認
SCTP がクラスターで機能することを確認するには、SCTP トラフィックをリッスンするアプリケーションで Pod を作成し、これをサービスに関連付け、公開されたサービスに接続します。
前提条件
-
クラスターからインターネットにアクセスし、
ncパッケージをインストールすること。 -
OpenShift CLI (
oc) をインストールします。 -
cluster-adminロールを持つユーザーとしてクラスターにアクセスできる。
手順
SCTP リスナーを起動する Pod を作成します。
以下の YAML で Pod を定義する
sctp-server.yamlという名前のファイルを作成します。apiVersion: v1 kind: Pod metadata: name: sctpserver labels: app: sctpserver spec: containers: - name: sctpserver image: registry.access.redhat.com/ubi8/ubi command: ["/bin/sh", "-c"] args: ["dnf install -y nc && sleep inf"] ports: - containerPort: 30102 name: sctpserver protocol: SCTP以下のコマンドを入力して Pod を作成します。
$ oc create -f sctp-server.yaml
SCTP リスナー Pod のサービスを作成します。
以下の YAML でサービスを定義する
sctp-service.yamlという名前のファイルを作成します。apiVersion: v1 kind: Service metadata: name: sctpservice labels: app: sctpserver spec: type: NodePort selector: app: sctpserver ports: - name: sctpserver protocol: SCTP port: 30102 targetPort: 30102サービスを作成するには、以下のコマンドを入力します。
$ oc create -f sctp-service.yaml
SCTP クライアントの Pod を作成します。
以下の YAML で
sctp-client.yamlという名前のファイルを作成します。apiVersion: v1 kind: Pod metadata: name: sctpclient labels: app: sctpclient spec: containers: - name: sctpclient image: registry.access.redhat.com/ubi8/ubi command: ["/bin/sh", "-c"] args: ["dnf install -y nc && sleep inf"]Podオブジェクトを作成するには、以下のコマンドを入力します。$ oc apply -f sctp-client.yaml
サーバーで SCTP リスナーを実行します。
サーバー Pod に接続するには、以下のコマンドを入力します。
$ oc rsh sctpserverSCTP リスナーを起動するには、以下のコマンドを入力します。
$ nc -l 30102 --sctp
サーバーの SCTP リスナーに接続します。
- ターミナルプログラムで新規のターミナルウィンドウまたはタブを開きます。
sctpserviceサービスの IP アドレスを取得します。以下のコマンドを入力します。$ oc get services sctpservice -o go-template='{{.spec.clusterIP}}{{"\n"}}'クライアント Pod に接続するには、以下のコマンドを入力します。
$ oc rsh sctpclientSCTP クライアントを起動するには、以下のコマンドを入力します。
<cluster_IP>をsctpserviceサービスのクラスター IP アドレスに置き換えます。# nc <cluster_IP> 30102 --sctp
第10章 PTP ハードウェアの設定
Precision Time Protocol (PTP) ハードウェアはテクノロジープレビュー機能です。テクノロジープレビュー機能は Red Hat の実稼働環境でのサービスレベルアグリーメント (SLA) ではサポートされていないため、Red Hat では実稼働環境での使用を推奨していません。Red Hat は実稼働環境でこれらを使用することを推奨していません。テクノロジープレビューの機能は、最新の製品機能をいち早く提供して、開発段階で機能のテストを行いフィードバックを提供していただくことを目的としています。
Red Hat のテクノロジープレビュー機能のサポート範囲に関する詳細は、テクノロジープレビュー機能のサポート範囲 を参照してください。
10.1. PTP ハードウェアについて
OpenShift Container Platform には、ノード上で Precision Time Protocol (PTP) ハードウェアを使用する機能が含まれます。linuxptp サービスは、PTP 対応ハードウェアを搭載したクラスターで設定できます。
PTP Operator は、ベアメタルインフラストラクチャーでのみプロビジョニングされるクラスターの PTP 対応デバイスと連携します。
PTP Operator をデプロイし、OpenShift Container Platform コンソールを使用して PTP をインストールできます。PTP Operator は、linuxptp サービスを作成し、管理します。Operator は以下の機能を提供します。
- クラスター内の PTP 対応デバイスの検出。
- linuxptp サービスの設定の管理。
10.2. PTP ネットワークデバイスの自動検出
PTP Operator は NodePtpDevice.ptp.openshift.io カスタムリソース定義 (CRD) を OpenShift Container Platform に追加します。PTP Operator はクラスターで、各ノードの PTP 対応ネットワークデバイスを検索します。Operator は、互換性のある PTP デバイスを提供する各ノードの NodePtpDevice カスタムリソース (CR) オブジェクトを作成し、更新します。
1 つの CR がノードごとに作成され、ノードと同じ名前を共有します。.status.devices 一覧は、ノード上の PTP デバイスについての情報を提供します。
以下は、PTP Operator によって作成される NodePtpDevice CR の例です。
apiVersion: ptp.openshift.io/v1
kind: NodePtpDevice
metadata:
creationTimestamp: "2019-11-15T08:57:11Z"
generation: 1
name: dev-worker-0
namespace: openshift-ptp
resourceVersion: "487462"
selfLink: /apis/ptp.openshift.io/v1/namespaces/openshift-ptp/nodeptpdevices/dev-worker-0
uid: 08d133f7-aae2-403f-84ad-1fe624e5ab3f
spec: {}
status:
devices:
- name: eno1
- name: eno2
- name: ens787f0
- name: ens787f1
- name: ens801f0
- name: ens801f1
- name: ens802f0
- name: ens802f1
- name: ens80310.3. PTP Operator のインストール
クラスター管理者は、OpenShift Container Platform CLI または Web コンソールを使用して PTP Operator をインストールできます。
10.3.1. CLI: PTP Operator のインストール
クラスター管理者は、CLI を使用して Operator をインストールできます。
前提条件
- PTP に対応するハードウェアを持つノードでベアメタルハードウェアにインストールされたクラスター。
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
PTP Operator の namespace を作成するには、以下のコマンドを入力します。
$ cat << EOF| oc create -f - apiVersion: v1 kind: Namespace metadata: name: openshift-ptp labels: name: openshift-ptp openshift.io/cluster-monitoring: "true" EOFOperator の Operator グループを作成するには、以下のコマンドを入力します。
$ cat << EOF| oc create -f - apiVersion: operators.coreos.com/v1 kind: OperatorGroup metadata: name: ptp-operators namespace: openshift-ptp spec: targetNamespaces: - openshift-ptp EOFPTP Operator にサブスクライブします。
以下のコマンドを実行して、OpenShift Container Platform のメジャーおよびマイナーバージョンを環境変数として設定します。これは次の手順で
channelの値として使用されます。$ OC_VERSION=$(oc version -o yaml | grep openshiftVersion | \ grep -o '[0-9]*[.][0-9]*' | head -1)PTP Operator のサブスクリプションを作成するには、以下のコマンドを入力します。
$ cat << EOF| oc create -f - apiVersion: operators.coreos.com/v1alpha1 kind: Subscription metadata: name: ptp-operator-subscription namespace: openshift-ptp spec: channel: "${OC_VERSION}" name: ptp-operator source: redhat-operators sourceNamespace: openshift-marketplace EOF
Operator がインストールされていることを確認するには、以下のコマンドを入力します。
$ oc get csv -n openshift-ptp \ -o custom-columns=Name:.metadata.name,Phase:.status.phase出力例
Name Phase ptp-operator.4.4.0-202006160135 Succeeded
10.3.2. Web コンソール: PTP Operator のインストール
クラスター管理者は、Web コンソールを使用して Operator をインストールできます。
先のセクションで説明されているように namespace および Operator グループを作成する必要があります。
手順
OpenShift Container Platform Web コンソールを使用して PTP Operator をインストールします。
- OpenShift Container Platform Web コンソールで、Operators → OperatorHub をクリックします。
- 利用可能な Operator の一覧から PTP Operator を選択してから Install をクリックします。
- Install Operator ページの A specific namespace on the cluster の下で openshift-ptp を選択します。次に、Install をクリックします。
オプション: PTP Operator が正常にインストールされていることを確認します。
- Operators → Installed Operators ページに切り替えます。
PTP Operator が Status が InstallSucceeded の状態で openshift-ptp プロジェクトに一覧表示されていることを確認します。
注記インストール時に、 Operator は Failed ステータスを表示する可能性があります。インストールが後に InstallSucceeded メッセージを出して正常に実行される場合は、Failed メッセージを無視できます。
Operator がインストール済みとして表示されない場合に、さらにトラブルシューティングを実行します。
- Operators → Installed Operators ページに移動し、Operator Subscriptions および Install Plans タブで Status にエラーがあるかどうかを検査します。
-
Workloads → Pods ページに移動し、
openshift-ptpプロジェクトで Pod のログを確認します。
10.4. Linuxptp サービスの設定
PTP Operator は PtpConfig.ptp.openshift.io カスタムリソース定義 (CRD) を OpenShift Container Platform に追加します。PtpConfig カスタムリソース (CR) オブジェクトを作成して、Linuxptp サービス (ptp4l、phc2sys) を設定できます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。 - PTP Operator がインストールされていること。
手順
以下の
PtpConfigCR を作成してから、YAML を<name>-ptp-config.yamlファイルに保存します。<name>をこの設定の名前に置き換えます。apiVersion: ptp.openshift.io/v1 kind: PtpConfig metadata: name: <name>1 namespace: openshift-ptp2 spec: profile:3 - name: "profile1"4 interface: "ens787f1"5 ptp4lOpts: "-s -2"6 phc2sysOpts: "-a -r"7 recommend:8 - profile: "profile1"9 priority: 1010 match:11 - nodeLabel: "node-role.kubernetes.io/worker"12 nodeName: "dev-worker-0"13 - 1
PtpConfigCR の名前を指定します。- 2
- PTP Operator がインストールされている namespace を指定します。
- 3
- 1 つ以上の
profileオブジェクトの配列を指定します。 - 4
- プロファイルオブジェクトを一意に識別するために使用されるプロファイルオブジェクトの名前を指定します。
- 5
ptp4lサービスで使用するネットワークインターフェイス名を指定します (例:ens787f1)。- 6
ptp4lサービスのシステム設定オプション (例:-s -2) を指定します。これには、インターフェイス名-i <interface>およびサービス設定ファイル-f /etc/ptp4l.confを含めないでください。これらは自動的に追加されます。- 7
phc2sysサービスのシステム設定オプション (例:-a -r) を指定します。- 8
profileがノードに適用される方法を定義する 1 つ以上のrecommendオブジェクトの配列を指定します。- 9
profileセクションに定義されるprofileオブジェクト名を指定します。- 10
0から99までの整数値でpriorityを指定します。数値が大きいほど優先度が低くなるため、99の優先度は10よりも低くなります。ノードがmatchフィールドで定義されるルールに基づいて複数のプロファイルに一致する場合、優先順位の高い プロファイルがそのノードに適用されます。- 11
matchルールを、nodeLabelまたはnodeNameで指定します。- 12
nodeLabelを、ノードオブジェクトのnode.Labelsのkeyで指定します。- 13
nodeNameをノードオブジェクトのnode.Nameで指定します。
以下のコマンドを実行して CR を作成します。
$ oc create -f <filename>1 - 1
<filename>を、先の手順で作成したファイルの名前に置き換えます。
オプション:
PtpConfigプロファイルが、nodeLabelまたはnodeNameに一致するノードに適用されることを確認します。$ oc get pods -n openshift-ptp -o wide出力例
NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES linuxptp-daemon-4xkbb 1/1 Running 0 43m 192.168.111.15 dev-worker-0 <none> <none> linuxptp-daemon-tdspf 1/1 Running 0 43m 192.168.111.11 dev-master-0 <none> <none> ptp-operator-657bbb64c8-2f8sj 1/1 Running 0 43m 10.128.0.116 dev-master-0 <none> <none> $ oc logs linuxptp-daemon-4xkbb -n openshift-ptp I1115 09:41:17.117596 4143292 daemon.go:107] in applyNodePTPProfile I1115 09:41:17.117604 4143292 daemon.go:109] updating NodePTPProfile to: I1115 09:41:17.117607 4143292 daemon.go:110] ------------------------------------ I1115 09:41:17.117612 4143292 daemon.go:102] Profile Name: profile11 I1115 09:41:17.117616 4143292 daemon.go:102] Interface: ens787f12 I1115 09:41:17.117620 4143292 daemon.go:102] Ptp4lOpts: -s -23 I1115 09:41:17.117623 4143292 daemon.go:102] Phc2sysOpts: -a -r4 I1115 09:41:17.117626 4143292 daemon.go:116] ------------------------------------ I1115 09:41:18.117934 4143292 daemon.go:186] Starting phc2sys... I1115 09:41:18.117985 4143292 daemon.go:187] phc2sys cmd: &{Path:/usr/sbin/phc2sys Args:[/usr/sbin/phc2sys -a -r] Env:[] Dir: Stdin:<nil> Stdout:<nil> Stderr:<nil> ExtraFiles:[] SysProcAttr:<nil> Process:<nil> ProcessState:<nil> ctx:<nil> lookPathErr:<nil> finished:false childFiles:[] closeAfterStart:[] closeAfterWait:[] goroutine:[] errch:<nil> waitDone:<nil>} I1115 09:41:19.118175 4143292 daemon.go:186] Starting ptp4l... I1115 09:41:19.118209 4143292 daemon.go:187] ptp4l cmd: &{Path:/usr/sbin/ptp4l Args:[/usr/sbin/ptp4l -m -f /etc/ptp4l.conf -i ens787f1 -s -2] Env:[] Dir: Stdin:<nil> Stdout:<nil> Stderr:<nil> ExtraFiles:[] SysProcAttr:<nil> Process:<nil> ProcessState:<nil> ctx:<nil> lookPathErr:<nil> finished:false childFiles:[] closeAfterStart:[] closeAfterWait:[] goroutine:[] errch:<nil> waitDone:<nil>} ptp4l[102189.864]: selected /dev/ptp5 as PTP clock ptp4l[102189.886]: port 1: INITIALIZING to LISTENING on INIT_COMPLETE ptp4l[102189.886]: port 0: INITIALIZING to LISTENING on INIT_COMPLETE
第11章 ネットワークポリシー
11.1. ネットワークポリシーについて
クラスター管理者は、トラフィックをクラスター内の Pod に制限するネットワークポリシーを定義できます。
11.1.1. ネットワークポリシーについて
Kubernetes ネットワークポリシーをサポートする Kubernetes Container Network Interface (CNI) プラグインを使用するクラスターでは、ネットワークの分離は NetworkPolicy オブジェクトによって完全に制御されます。OpenShift Container Platform 4.7 では、OpenShift SDN はデフォルトのネットワーク分離モードでのネットワークポリシーの使用をサポートしています。
OpenShift SDN クラスターネットワークプロバイダーを使用する場合、ネットワークポリシーについて、以下の制限が適用されます。
-
egressフィールドで指定される egress ネットワークポリシーはサポートされていません。 -
IPBlock はネットワークポリシーでサポートされますが、
except句はサポートしません。except句を含む IPBlock セクションのあるポリシーを作成する場合、SDN Pod は警告をログに記録し、そのポリシーの IPBlock セクション全体は無視されます。
ネットワークポリシーは、ホストのネットワーク namespace には適用されません。ホストネットワークが有効にされている Pod はネットワークポリシールールによる影響を受けません。
デフォルトで、プロジェクトのすべての Pod は他の Pod およびネットワークのエンドポイントからアクセスできます。プロジェクトで 1 つ以上の Pod を分離するには、そのプロジェクトで NetworkPolicy オブジェクトを作成し、許可する着信接続を指定します。プロジェクト管理者は独自のプロジェクト内で NetworkPolicy オブジェクトの作成および削除を実行できます。
Pod が 1 つ以上の NetworkPolicy オブジェクトのセレクターで一致する場合、Pod はそれらの 1 つ以上の NetworkPolicy オブジェクトで許可される接続のみを受け入れます。NetworkPolicy オブジェクトによって選択されていない Pod は完全にアクセス可能です。
以下のサンプル NetworkPolicy オブジェクトは、複数の異なるシナリオをサポートすることを示しています。
すべてのトラフィックを拒否します。
プロジェクトに deny by default (デフォルトで拒否) を実行させるには、すべての Pod に一致するが、トラフィックを一切許可しない
NetworkPolicyオブジェクトを追加します。kind: NetworkPolicy apiVersion: networking.k8s.io/v1 metadata: name: deny-by-default spec: podSelector: {} ingress: []OpenShift Container Platform Ingress コントローラーからの接続のみを許可します。
プロジェクトで OpenShift Container Platform Ingress コントローラーからの接続のみを許可するには、以下の
NetworkPolicyオブジェクトを追加します。apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: allow-from-openshift-ingress spec: ingress: - from: - namespaceSelector: matchLabels: network.openshift.io/policy-group: ingress podSelector: {} policyTypes: - Ingressプロジェクト内の Pod からの接続のみを受け入れます。
Pod が同じプロジェクト内の他の Pod からの接続を受け入れるが、他のプロジェクトの Pod からの接続を拒否するように設定するには、以下の
NetworkPolicyオブジェクトを追加します。kind: NetworkPolicy apiVersion: networking.k8s.io/v1 metadata: name: allow-same-namespace spec: podSelector: {} ingress: - from: - podSelector: {}Pod ラベルに基づいて HTTP および HTTPS トラフィックのみを許可します。
特定のラベル (以下の例の
role=frontend) の付いた Pod への HTTP および HTTPS アクセスのみを有効にするには、以下と同様のNetworkPolicyオブジェクトを追加します。kind: NetworkPolicy apiVersion: networking.k8s.io/v1 metadata: name: allow-http-and-https spec: podSelector: matchLabels: role: frontend ingress: - ports: - protocol: TCP port: 80 - protocol: TCP port: 443namespace および Pod セレクターの両方を使用して接続を受け入れます。
namespace と Pod セレクターを組み合わせてネットワークトラフィックのマッチングをするには、以下と同様の
NetworkPolicyオブジェクトを使用できます。kind: NetworkPolicy apiVersion: networking.k8s.io/v1 metadata: name: allow-pod-and-namespace-both spec: podSelector: matchLabels: name: test-pods ingress: - from: - namespaceSelector: matchLabels: project: project_name podSelector: matchLabels: name: test-pods
NetworkPolicy オブジェクトは加算されるものです。 つまり、複数の NetworkPolicy オブジェクトを組み合わせて複雑なネットワーク要件を満すことができます。
たとえば、先の例で定義された NetworkPolicy オブジェクトの場合、同じプロジェト内に allow-same-namespace と allow-http-and-https ポリシーの両方を定義することができます。これにより、ラベル role=frontend の付いた Pod は各ポリシーで許可されるすべての接続を受け入れます。つまり、同じ namespace の Pod からのすべてのポート、およびすべての namespace の Pod からのポート 80 および 443 での接続を受け入れます。
11.1.2. ネットワークポリシーの最適化
ネットワークポリシーを使用して、namespace 内でラベルで相互に区別される Pod を分離します。
ネットワークポリシールールを効果的に使用するためのガイドラインは、OpenShift SDN クラスターネットワークプロバイダーのみに適用されます。
NetworkPolicy オブジェクトを単一 namespace 内の多数の個別 Pod に適用することは効率的ではありません。Pod ラベルは IP レベルには存在しないため、ネットワークポリシーは、podSelector で選択されるすべての Pod 間のすべてのリンクについての別個の Open vSwitch (OVS) フロールールを生成します。
たとえば、仕様の podSelector および NetworkPolicy オブジェクト内の ingress podSelector のそれぞれが 200 Pod に一致する場合、40,000 (200*200) OVS フロールールが生成されます。これにより、ノードの速度が低下する可能性があります。
ネットワークポリシーを設計する場合は、以下のガイドラインを参照してください。
namespace を使用して分離する必要のある Pod のグループを組み込み、OVS フロールールの数を減らします。
namespace 全体を選択する
NetworkPolicyオブジェクトは、namespaceSelectorsまたは空のpodSelectorsを使用して、namespace の VXLAN 仮想ネットワーク ID に一致する単一の OVS フロールールのみを生成します。- 分離する必要のない Pod は元の namespace に維持し、分離する必要のある Pod は 1 つ以上の異なる namespace に移します。
- 追加のターゲット設定された namespace 間のネットワークポリシーを作成し、分離された Pod から許可する必要のある特定のトラフィックを可能にします。
11.1.3. 次のステップ
- ネットワークポリシーの作成
- オプション: デフォルトネットワークポリシーの定義
11.2. ネットワークポリシーの作成
admin ロールを持つユーザーは、namespace のネットワークポリシーを作成できます。
11.2.1. ネットワークポリシーの作成
クラスターの namespace に許可される Ingress または egress ネットワークトラフィックを記述する詳細なルールを定義するには、ネットワークポリシーを作成できます。
cluster-admin ロールを持つユーザーでログインしている場合、クラスター内の namespace でネットワークポリシーを作成できます。
前提条件
-
クラスターは、
NetworkPolicyオブジェクトをサポートするクラスターネットワークプロバイダーを使用する (例: OVN-Kubernetes ネットワークプロバイダー、またはmode: NetworkPolicyが設定された OpenShift SDN ネットワークプロバイダー)。このモードは OpenShiftSDN のデフォルトです。 -
OpenShift CLI (
oc) がインストールされている。 -
admin権限を持つユーザーとしてクラスターにログインしている。 - ネットワークポリシーが適用される namespace で作業している。
手順
ポリシールールを作成します。
<policy_name>.yamlファイルを作成します。$ touch <policy_name>.yamlここでは、以下のようになります。
<policy_name>- ネットワークポリシーファイル名を指定します。
作成したばかりのファイルで、以下の例のようなネットワークポリシーを定義します。
すべての namespace のすべての Pod から ingress を拒否します。
kind: NetworkPolicy apiVersion: networking.k8s.io/v1 metadata: name: deny-by-default spec: podSelector: ingress: []同じ namespace のすべての Pod から ingress を許可します。
kind: NetworkPolicy apiVersion: networking.k8s.io/v1 metadata: name: allow-same-namespace spec: podSelector: ingress: - from: - podSelector: {}
ネットワークポリシーオブジェクトを作成するには、以下のコマンドを入力します。
$ oc apply -f <policy_name>.yaml -n <namespace>ここでは、以下のようになります。
<policy_name>- ネットワークポリシーファイル名を指定します。
<namespace>- オプション: オブジェクトが現在の namespace 以外の namespace に定義されている場合は namespace を指定します。
出力例
networkpolicy "default-deny" created
11.2.2. サンプル NetworkPolicy オブジェクト
以下は、サンプル NetworkPolicy オブジェクトにアノテーションを付けます。
kind: NetworkPolicy
apiVersion: networking.k8s.io/v1
metadata:
name: allow-27107
spec:
podSelector:
matchLabels:
app: mongodb
ingress:
- from:
- podSelector:
matchLabels:
app: app
ports:
- protocol: TCP
port: 2701711.3. ネットワークポリシーの表示
admin ロールを持つユーザーは、namespace のネットワークポリシーを表示できます。
11.3.1. ネットワークポリシーの表示
namespace のネットワークポリシーを検査できます。
cluster-admin ロールを持つユーザーでログインしている場合、クラスター内のネットワークポリシーを表示できます。
前提条件
-
OpenShift CLI (
oc) がインストールされている。 -
admin権限を持つユーザーとしてクラスターにログインしている。 - ネットワークポリシーが存在する namespace で作業している。
手順
namespace のネットワークポリシーを一覧表示します。
namespace で定義された
NetworkPolicyオブジェクトを表示するには、以下のコマンドを実行します。$ oc get networkpolicyオプション: 特定のネットワークポリシーを検査するには、以下のコマンドを入力します。
$ oc describe networkpolicy <policy_name> -n <namespace>ここでは、以下のようになります。
<policy_name>- 検査するネットワークポリシーの名前を指定します。
<namespace>- オプション: オブジェクトが現在の namespace 以外の namespace に定義されている場合は namespace を指定します。
以下に例を示します。
$ oc describe networkpolicy allow-same-namespaceoc describeコマンドの出力Name: allow-same-namespace Namespace: ns1 Created on: 2021-05-24 22:28:56 -0400 EDT Labels: <none> Annotations: <none> Spec: PodSelector: <none> (Allowing the specific traffic to all pods in this namespace) Allowing ingress traffic: To Port: <any> (traffic allowed to all ports) From: PodSelector: <none> Not affecting egress traffic Policy Types: Ingress
11.3.2. サンプル NetworkPolicy オブジェクト
以下は、サンプル NetworkPolicy オブジェクトにアノテーションを付けます。
kind: NetworkPolicy
apiVersion: networking.k8s.io/v1
metadata:
name: allow-27107
spec:
podSelector:
matchLabels:
app: mongodb
ingress:
- from:
- podSelector:
matchLabels:
app: app
ports:
- protocol: TCP
port: 2701711.4. ネットワークポリシーの編集
admin ロールを持つユーザーは、namespace の既存のネットワークポリシーを編集できます。
11.4.1. ネットワークポリシーの編集
namespace のネットワークポリシーを編集できます。
cluster-admin ロールを持つユーザーでログインしている場合、クラスター内の namespace でネットワークポリシーを編集できます。
前提条件
-
クラスターは、
NetworkPolicyオブジェクトをサポートするクラスターネットワークプロバイダーを使用する (例: OVN-Kubernetes ネットワークプロバイダー、またはmode: NetworkPolicyが設定された OpenShift SDN ネットワークプロバイダー)。このモードは OpenShiftSDN のデフォルトです。 -
OpenShift CLI (
oc) がインストールされている。 -
admin権限を持つユーザーとしてクラスターにログインしている。 - ネットワークポリシーが存在する namespace で作業している。
手順
オプション: namespace のネットワークポリシーオブジェクトを一覧表示するには、以下のコマンドを入力します。
$ oc get networkpolicy -n <namespace>ここでは、以下のようになります。
<namespace>- オプション: オブジェクトが現在の namespace 以外の namespace に定義されている場合は namespace を指定します。
NetworkPolicyオブジェクトを編集します。ネットワークポリシーの定義をファイルに保存した場合は、ファイルを編集して必要な変更を加えてから、以下のコマンドを入力します。
$ oc apply -n <namespace> -f <policy_file>.yamlここでは、以下のようになります。
<namespace>- オプション: オブジェクトが現在の namespace 以外の namespace に定義されている場合は namespace を指定します。
<policy_file>- ネットワークポリシーを含むファイルの名前を指定します。
NetworkPolicyオブジェクトを直接更新する必要がある場合、以下のコマンドを入力できます。$ oc edit networkpolicy <policy_name> -n <namespace>ここでは、以下のようになります。
<policy_name>- ネットワークポリシーの名前を指定します。
<namespace>- オプション: オブジェクトが現在の namespace 以外の namespace に定義されている場合は namespace を指定します。
NetworkPolicyオブジェクトが更新されていることを確認します。$ oc describe networkpolicy <policy_name> -n <namespace>ここでは、以下のようになります。
<policy_name>- ネットワークポリシーの名前を指定します。
<namespace>- オプション: オブジェクトが現在の namespace 以外の namespace に定義されている場合は namespace を指定します。
11.4.2. サンプル NetworkPolicy オブジェクト
以下は、サンプル NetworkPolicy オブジェクトにアノテーションを付けます。
kind: NetworkPolicy
apiVersion: networking.k8s.io/v1
metadata:
name: allow-27107
spec:
podSelector:
matchLabels:
app: mongodb
ingress:
- from:
- podSelector:
matchLabels:
app: app
ports:
- protocol: TCP
port: 2701711.5. ネットワークポリシーの削除
admin ロールを持つユーザーは、namespace からネットワークポリシーを削除できます。
11.5.1. ネットワークポリシーの削除
namespace のネットワークポリシーを削除できます。
cluster-admin ロールを持つユーザーでログインしている場合、クラスター内のネットワークポリシーを削除できます。
前提条件
-
クラスターは、
NetworkPolicyオブジェクトをサポートするクラスターネットワークプロバイダーを使用する (例: OVN-Kubernetes ネットワークプロバイダー、またはmode: NetworkPolicyが設定された OpenShift SDN ネットワークプロバイダー)。このモードは OpenShiftSDN のデフォルトです。 -
OpenShift CLI (
oc) がインストールされている。 -
admin権限を持つユーザーとしてクラスターにログインしている。 - ネットワークポリシーが存在する namespace で作業している。
手順
NetworkPolicyオブジェクトを削除するには、以下のコマンドを入力します。$ oc delete networkpolicy <policy_name> -n <namespace>ここでは、以下のようになります。
<policy_name>- ネットワークポリシーの名前を指定します。
<namespace>- オプション: オブジェクトが現在の namespace 以外の namespace に定義されている場合は namespace を指定します。
出力例
networkpolicy.networking.k8s.io/allow-same-namespace deleted
11.6. プロジェクトのデフォルトネットワークポリシーの定義
クラスター管理者は、新規プロジェクトの作成時にネットワークポリシーを自動的に含めるように新規プロジェクトテンプレートを変更できます。新規プロジェクトのカスタマイズされたテンプレートがまだない場合には、まずテンプレートを作成する必要があります。
11.6.1. 新規プロジェクトのテンプレートの変更
クラスター管理者は、デフォルトのプロジェクトテンプレートを変更し、新規プロジェクトをカスタム要件に基づいて作成することができます。
独自のカスタムプロジェクトテンプレートを作成するには、以下を実行します。
手順
-
cluster-admin権限を持つユーザーとしてログインしている。 デフォルトのプロジェクトテンプレートを生成します。
$ oc adm create-bootstrap-project-template -o yaml > template.yaml-
オブジェクトを追加するか、または既存オブジェクトを変更することにより、テキストエディターで生成される
template.yamlファイルを変更します。 プロジェクトテンプレートは、
openshift-confignamespace に作成される必要があります。変更したテンプレートを読み込みます。$ oc create -f template.yaml -n openshift-configWeb コンソールまたは CLI を使用し、プロジェクト設定リソースを編集します。
Web コンソールの使用
- Administration → Cluster Settings ページに移動します。
- Global Configuration をクリックし、すべての設定リソースを表示します。
- Project のエントリーを見つけ、Edit YAML をクリックします。
CLI の使用
project.config.openshift.io/clusterリソースを編集します。$ oc edit project.config.openshift.io/cluster
specセクションを、projectRequestTemplateおよびnameパラメーターを組み込むように更新し、アップロードされたプロジェクトテンプレートの名前を設定します。デフォルト名はproject-requestです。カスタムプロジェクトテンプレートを含むプロジェクト設定リソース
apiVersion: config.openshift.io/v1 kind: Project metadata: ... spec: projectRequestTemplate: name: <template_name>- 変更を保存した後、変更が正常に適用されたことを確認するために、新しいプロジェクトを作成します。
11.6.2. 新規プロジェクトへのネットワークポリシーの追加
クラスター管理者は、ネットワークポリシーを新規プロジェクトのデフォルトテンプレートに追加できます。OpenShift Container Platform は、プロジェクトのテンプレートに指定されたすべての NetworkPolicy オブジェクトを自動的に作成します。
前提条件
-
クラスターは、
NetworkPolicyオブジェクトをサポートするデフォルトの CNI ネットワークプロバイダーを使用する (例:mode: NetworkPolicyが設定された OpenShift SDN ネットワークプロバイダー)。このモードは OpenShiftSDN のデフォルトです。 -
OpenShift CLI (
oc) がインストールされている。 -
cluster-admin権限を持つユーザーとしてクラスターにログインすること。 - 新規プロジェクトのカスタムデフォルトプロジェクトテンプレートを作成していること。
手順
以下のコマンドを実行して、新規プロジェクトのデフォルトテンプレートを編集します。
$ oc edit template <project_template> -n openshift-config<project_template>を、クラスターに設定したデフォルトテンプレートの名前に置き換えます。デフォルトのテンプレート名はproject-requestです。テンプレートでは、各
NetworkPolicyオブジェクトを要素としてobjectsパラメーターに追加します。objectsパラメーターは、1 つ以上のオブジェクトのコレクションを受け入れます。以下の例では、
objectsパラメーターのコレクションにいくつかのNetworkPolicyオブジェクトが含まれます。重要OVN-Kubernetes ネットワークプロバイダープラグインの場合、Ingress コントローラーが
HostNetworkエンドポイント公開ストラテジーを使用するように設定されている場合、Ingress トラフィックが許可され、他のすべてのトラフィックが拒否されるようにネットワークポリシーを適用するための方法はサポートされていません。objects: - apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: allow-from-same-namespace spec: podSelector: {} ingress: - from: - podSelector: {} - apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: allow-from-openshift-ingress spec: ingress: - from: - namespaceSelector: matchLabels: network.openshift.io/policy-group: ingress podSelector: {} policyTypes: - Ingress ...オプション: 以下のコマンドを実行して、新規プロジェクトを作成し、ネットワークポリシーオブジェクトが正常に作成されることを確認します。
新規プロジェクトを作成します。
$ oc new-project <project>1 - 1
<project>を、作成しているプロジェクトの名前に置き換えます。
新規プロジェクトテンプレートのネットワークポリシーオブジェクトが新規プロジェクトに存在することを確認します。
$ oc get networkpolicy NAME POD-SELECTOR AGE allow-from-openshift-ingress <none> 7s allow-from-same-namespace <none> 7s
11.7. ネットワークポリシーを使用したマルチテナント分離の設定
クラスター管理者は、マルチテナントネットワークの分離を実行するようにネットワークポリシーを設定できます。
OpenShift SDN クラスターネットワークプロバイダーを使用している場合、本セクションで説明されているようにネットワークポリシーを設定すると、マルチテナントモードと同様のネットワーク分離が行われますが、ネットワークポリシーモードが設定されます。
11.7.1. ネットワークポリシーを使用したマルチテナント分離の設定
他のプロジェクト namespace の Pod およびサービスから分離できるようにプロジェクトを設定できます。
前提条件
-
クラスターは、
NetworkPolicyオブジェクトをサポートするクラスターネットワークプロバイダーを使用する (例: OVN-Kubernetes ネットワークプロバイダー、またはmode: NetworkPolicyが設定された OpenShift SDN ネットワークプロバイダー)。このモードは OpenShiftSDN のデフォルトです。 -
OpenShift CLI (
oc) がインストールされている。 -
admin権限を持つユーザーとしてクラスターにログインしている。
手順
以下の
NetworkPolicyオブジェクトを作成します。allow-from-openshift-ingressという名前のポリシー:$ cat << EOF| oc create -f - apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: allow-from-openshift-ingress spec: ingress: - from: - namespaceSelector: matchLabels: policy-group.network.openshift.io/ingress: "" podSelector: {} policyTypes: - Ingress EOF注記policy-group.network.openshift.io/ingress: ""は、OpenShift SDN の推奨の namespace セレクターラベルです。network.openshift.io/policy-group: ingressnamespace セレクターラベルを使用できますが、これはレガシーラベルです。allow-from-openshift-monitoringという名前のポリシー。$ cat << EOF| oc create -f - apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: allow-from-openshift-monitoring spec: ingress: - from: - namespaceSelector: matchLabels: network.openshift.io/policy-group: monitoring podSelector: {} policyTypes: - Ingress EOFallow-same-namespaceという名前のポリシー:$ cat << EOF| oc create -f - kind: NetworkPolicy apiVersion: networking.k8s.io/v1 metadata: name: allow-same-namespace spec: podSelector: ingress: - from: - podSelector: {} EOF
オプション: 以下のコマンドを実行し、ネットワークポリシーオブジェクトが現在のプロジェクトに存在することを確認します。
$ oc describe networkpolicy出力例
Name: allow-from-openshift-ingress Namespace: example1 Created on: 2020-06-09 00:28:17 -0400 EDT Labels: <none> Annotations: <none> Spec: PodSelector: <none> (Allowing the specific traffic to all pods in this namespace) Allowing ingress traffic: To Port: <any> (traffic allowed to all ports) From: NamespaceSelector: network.openshift.io/policy-group: ingress Not affecting egress traffic Policy Types: Ingress Name: allow-from-openshift-monitoring Namespace: example1 Created on: 2020-06-09 00:29:57 -0400 EDT Labels: <none> Annotations: <none> Spec: PodSelector: <none> (Allowing the specific traffic to all pods in this namespace) Allowing ingress traffic: To Port: <any> (traffic allowed to all ports) From: NamespaceSelector: network.openshift.io/policy-group: monitoring Not affecting egress traffic Policy Types: Ingress
11.7.2. 次のステップ
第12章 複数ネットワーク
12.1. 複数ネットワークについて
Kubernetes では、コンテナーネットワークは Container Network Interface (CNI) を実装するネットワークプラグインに委任されます。
OpenShift Container Platform は、Multus CNI プラグインを使用して CNI プラグインのチェーンを許可します。クラスターのインストール時に、デフォルト の Pod ネットワークを設定します。デフォルトのネットワークは、クラスターのすべての通常のネットワークトラフィックを処理します。利用可能な CNI プラグインに基づいて 追加のネットワーク を定義し、1 つまたは複数のネットワークを Pod に割り当てることができます。必要に応じて、クラスターの複数のネットワークを追加で定義することができます。これは、スイッチまたはルーティングなどのネットワーク機能を提供する Pod を設定する場合に柔軟性を実現します。
12.1.1. 追加ネットワークの使用シナリオ
データプレーンとコントロールプレーンの分離など、ネットワークの分離が必要な状況で追加のネットワークを使用することができます。トラフィックの分離は、以下のようなパフォーマンスおよびセキュリティー関連の理由で必要になります。
- パフォーマンス
- 各プレーンのトラフィック量を管理するために、2 つの異なるプレーンにトラフィックを送信できます。
- セキュリティー
- 機密トラフィックは、セキュリティー上の考慮に基づいて管理されているネットワークに送信でき、テナントまたはカスタマー間で共有できないプライベートを分離することができます。
クラスターのすべての Pod はクラスター全体のデフォルトネットワークを依然として使用し、クラスター全体での接続性を維持します。すべての Pod には、クラスター全体の Pod ネットワークに割り当てられる eth0 インターフェイスがあります。Pod のインターフェイスは、oc exec -it <pod_name> -- ip a コマンドを使用して表示できます。Multus CNI を使用するネットワークを追加する場合、それらの名前は net1、net2、…、 netN になります。
追加のネットワークを Pod に割り当てるには、インターフェイスの割り当て方法を定義する設定を作成する必要があります。それぞれのインターフェイスは、NetworkAttachmentDefinition カスタムリソース (CR) を使用して指定します。これらの CR のそれぞれにある CNI 設定は、インターフェイスの作成方法を定義します。
12.1.2. OpenShift Container Platform の追加ネットワーク
OpenShift Container Platform は、クラスターに追加のネットワークを作成するために使用する以下の CNI プラグインを提供します。
- bridge: ブリッジベースの追加ネットワークを設定する ことで、同じホストにある Pod が相互に、かつホストと通信できます。
- host-device: ホストデバイスの追加ネットワークを設定する ことで、Pod がホストシステム上の物理イーサネットネットワークデバイスにアクセスすることができます。
- ipvlan: ipvlan ベースの追加ネットワークを設定する ことで、macvlan ベースの追加ネットワークと同様に、ホスト上の Pod が他のホストやそれらのホストの Pod と通信できます。macvlan ベースの追加のネットワークとは異なり、各 Pod は親の物理ネットワークインターフェイスと同じ MAC アドレスを共有します。
- macvlan: macvlan ベースの追加ネットワークを作成 することで、ホスト上の Pod が物理ネットワークインターフェイスを使用して他のホストやそれらのホストの Pod と通信できます。macvlan ベースの追加ネットワークに割り当てられる各 Pod には固有の MAC アドレスが割り当てられます。
- SR-IOV: SR-IOV ベースの追加ネットワークを設定する ことで、Pod を ホストシステム上の SR-IOV 対応ハードウェアの Virtual Function (VF) インターフェイスに割り当てることができます。
12.2. 追加のネットワークの設定
クラスター管理者は、クラスターの追加のネットワークを設定できます。以下のネットワークタイプに対応しています。
12.2.1. 追加のネットワークを管理するためのアプローチ
追加したネットワークのライフサイクルを管理するには、2 つのアプローチがあります。各アプローチは同時に使用できず、追加のネットワークを管理する場合に 1 つのアプローチしか使用できません。いずれの方法でも、追加のネットワークは、お客様が設定した Container Network Interface (CNI) プラグインで管理します。
追加ネットワークの場合には、IP アドレスは、追加ネットワークの一部として設定する IPAM(IP Address Management)CNI プラグインでプロビジョニングされます。IPAM プラグインは、DHCP や静的割り当てなど、さまざまな IP アドレス割り当ての方法をサポートしています。
-
Cluster Network Operator (CNO) の設定を変更する: CNO は自動的に
Network Attachment Definitionオブジェクトを作成し、管理します。CNO は、オブジェクトのライフサイクル管理に加えて、DHCP で割り当てられた IP アドレスを使用する追加のネットワークで確実に DHCP が利用できるようにします。 -
YAML マニフェストを適用する:
Network Attachment Definitionオブジェクトを作成することで、追加のネットワークを直接管理できます。この方法では、CNI プラグインを連鎖させることができます。
12.2.2. ネットワーク追加割り当ての設定
追加のネットワークは、k8s.cni.cncf.ioAPI グループの Network Attachment DefinitionAPI で設定されます。API の設定については、以下の表で説明されています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
| 追加のネットワークの名前です。 |
|
|
| オブジェクトが関連付けられる namespace。 |
|
|
| JSON 形式の CNI プラグイン設定です。 |
12.2.2.1. Cluster Network Operator による追加ネットワークの設定
追加のネットワーク割り当ての設定は、Cluster Network Operator (CNO) の設定の一部として指定します。
以下の YAML は、CNO で追加のネットワークを管理するための設定パラメーターを記述しています。
Cluster Network Operator (CNO) の設定
apiVersion: operator.openshift.io/v1
kind: Network
metadata:
name: cluster
spec:
# ...
additionalNetworks:
- name: <name>
namespace: <namespace>
rawCNIConfig: |-
{
...
}
type: Raw12.2.2.2. YAML マニフェストからの追加ネットワークの設定
追加ネットワークの設定は、以下の例のように YAML 設定ファイルから指定します。
apiVersion: k8s.cni.cncf.io/v1
kind: NetworkAttachmentDefinition
metadata:
name: <name>
spec:
config: |-
{
...
}12.2.3. 追加のネットワークタイプの設定
次のセクションでは、追加のネットワークの具体的な設定フィールドについて説明します。
12.2.3.1. ブリッジネットワークの追加設定
以下のオブジェクトは、ブリッジ CNI プラグインの設定パラメーターについて説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
CNI 仕様のバージョン。値 |
|
|
|
CNO 設定に以前に指定した |
|
|
| |
|
|
|
使用する仮想ブリッジの名前を指定します。ブリッジインターフェイスがホストに存在しない場合は、これが作成されます。デフォルト値は |
|
|
| IPAM CNI プラグインの設定オブジェクト。プラグインは、割り当て定義についての IP アドレスの割り当てを管理します。 |
|
|
|
仮想ネットワークから外すトラフィックについて IP マスカレードを有効にするには、 |
|
|
|
IP アドレスをブリッジに割り当てるには |
|
|
|
ブリッジを仮想ネットワークのデフォルトゲートウェイとして設定するには、 |
|
|
|
仮想ブリッジの事前に割り当てられた IP アドレスの割り当てを許可するには、 |
|
|
|
仮想ブリッジが受信時に使用した仮想ポートでイーサネットフレームを送信できるようにするには、 |
|
|
|
ブリッジで無作為検出モード (Promiscuous Mode) を有効にするには、 |
|
|
| 仮想 LAN (VLAN) タグを整数値として指定します。デフォルトで、VLAN タグは割り当てません。 |
|
|
| 最大転送単位 (MTU) を指定された値に設定します。デフォルト値はカーネルによって自動的に設定されます。 |
12.2.3.1.1. ブリッジ設定の例
以下の例では、bridge-net という名前の追加のネットワークを設定します。
{
"cniVersion": "0.3.1",
"name": "work-network",
"type": "bridge",
"isGateway": true,
"vlan": 2,
"ipam": {
"type": "dhcp"
}
}12.2.3.2. ホストデバイスの追加ネットワークの設定
device、hwaddr、 kernelpath、または pciBusID のいずれかのパラメーターを設定してネットワークデバイスを指定します。
以下のオブジェクトは、ホストデバイス CNI プラグインの設定パラメーターについて説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
CNI 仕様のバージョン。値 |
|
|
|
CNO 設定に以前に指定した |
|
|
|
設定する CNI プラグインの名前: |
|
|
|
オプション: |
|
|
| オプション: デバイスハードウェアの MAC アドレス。 |
|
|
|
オプション: |
|
|
|
オプション: |
|
|
| IPAM CNI プラグインの設定オブジェクト。プラグインは、割り当て定義についての IP アドレスの割り当てを管理します。 |
12.2.3.2.1. ホストデバイス設定例
以下の例では、hostdev-net という名前の追加のネットワークを設定します。
{
"cniVersion": "0.3.1",
"name": "work-network",
"type": "host-device",
"device": "eth1",
"ipam": {
"type": "dhcp"
}
}12.2.3.3. IPVLAN 追加ネットワークの設定
以下のオブジェクトは、IPVLAN CNI プラグインの設定パラメーターについて説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
CNI 仕様のバージョン。値 |
|
|
|
CNO 設定に以前に指定した |
|
|
|
設定する CNI プラグインの名前: |
|
|
|
仮想ネットワークの操作モード。この値は、 |
|
|
|
ネットワーク割り当てに関連付けるイーサネットインターフェイス。 |
|
|
| 最大転送単位 (MTU) を指定された値に設定します。デフォルト値はカーネルによって自動的に設定されます。 |
|
|
| IPAM CNI プラグインの設定オブジェクト。プラグインは、割り当て定義についての IP アドレスの割り当てを管理します。
|
12.2.3.3.1. IPVLAN 設定例
以下の例では、ipvlan-net という名前の追加のネットワークを設定します。
{
"cniVersion": "0.3.1",
"name": "work-network",
"type": "ipvlan",
"master": "eth1",
"mode": "l3",
"ipam": {
"type": "static",
"addresses": [
{
"address": "192.168.10.10/24"
}
]
}
}12.2.3.4. MACVLAN 追加ネットワークの設定
以下のオブジェクトは、macvlan CNI プラグインの設定パラメーターについて説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
CNI 仕様のバージョン。値 |
|
|
|
CNO 設定に以前に指定した |
|
|
|
設定する CNI プラグインの名前: |
|
|
|
仮想ネットワークのトラフィックの可視性を設定します。 |
|
|
| 仮想インターフェイスに関連付けるイーサネット、ボンディング、または VLAN インターフェイス。値が指定されない場合、ホストシステムのプライマリーイーサネットインターフェイスが使用されます。 |
|
|
| 最大転送単位 (MTU) を指定された値。デフォルト値はカーネルによって自動的に設定されます。 |
|
|
| IPAM CNI プラグインの設定オブジェクト。プラグインは、割り当て定義についての IP アドレスの割り当てを管理します。 |
12.2.3.4.1. macvlan 設定の例
以下の例では、macvlan-net という名前の追加のネットワークを設定します。
{
"cniVersion": "0.3.1",
"name": "macvlan-net",
"type": "macvlan",
"master": "eth1",
"mode": "bridge",
"ipam": {
"type": "dhcp"
}
}12.2.4. 追加ネットワークの IP アドレス割り当ての設定
IPAM (IP アドレス管理) Container Network Interface (CNI) プラグインは、他の CNI プラグインの IP アドレスを提供します。
以下の IP アドレスの割り当てタイプを使用できます。
- 静的割り当て。
- DHCP サーバーを使用した動的割り当て。指定する DHCP サーバーは、追加のネットワークから到達可能である必要があります。
- Whereabouts IPAM CNI プラグインを使用した動的割り当て。
12.2.4.1. 静的 IP アドレス割り当ての設定
以下の表は、静的 IP アドレスの割り当ての設定について説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
IPAM のアドレスタイプ。値 |
|
|
| 仮想インターフェイスに割り当てる IP アドレスを指定するオブジェクトの配列。IPv4 と IPv6 の IP アドレスの両方がサポートされます。 |
|
|
| Pod 内で設定するルートを指定するオブジェクトの配列です。 |
|
|
| オプション: DNS の設定を指定するオブジェクトの配列です。 |
addressesの配列には、以下のフィールドのあるオブジェクトが必要です。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
指定する IP アドレスおよびネットワーク接頭辞。たとえば、 |
|
|
| egress ネットワークトラフィックをルーティングするデフォルトのゲートウェイ。 |
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
CIDR 形式の IP アドレス範囲 ( |
|
|
| ネットワークトラフィックがルーティングされるゲートウェイ。 |
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
| DNS クエリーの送信先となる 1 つ以上の IP アドレスの配列。 |
|
|
|
ホスト名に追加するデフォルトのドメイン。たとえば、ドメインが |
|
|
|
DNS ルックアップのクエリー時に非修飾ホスト名に追加されるドメイン名の配列 (例: |
静的 IP アドレス割り当ての設定例
{
"ipam": {
"type": "static",
"addresses": [
{
"address": "191.168.1.7/24"
}
]
}
}12.2.4.2. 動的 IP アドレス (DHCP) 割り当ての設定
以下の JSON は、DHCP を使用した動的 IP アドレスの割り当ての設定について説明しています。
Pod は、作成時に元の DHCP リースを取得します。リースは、クラスターで実行している最小限の DHCP サーバーデプロイメントで定期的に更新する必要があります。
DHCP サーバーのデプロイメントをトリガーするには、以下の例にあるように Cluster Network Operator 設定を編集して shim ネットワーク割り当てを作成する必要があります。
shim ネットワーク割り当ての定義例
apiVersion: operator.openshift.io/v1
kind: Network
metadata:
name: cluster
spec:
additionalNetworks:
- name: dhcp-shim
namespace: default
type: Raw
rawCNIConfig: |-
{
"name": "dhcp-shim",
"cniVersion": "0.3.1",
"type": "bridge",
"ipam": {
"type": "dhcp"
}
}
# ...| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
IPAM のアドレスタイプ。値 |
動的 IP アドレス (DHCP) 割り当ての設定例
{
"ipam": {
"type": "dhcp"
}
}12.2.4.3. Whereabouts を使用した動的 IP アドレス割り当ての設定
Whereabouts CNI プラグインにより、DHCP サーバーを使用せずに IP アドレスを追加のネットワークに動的に割り当てることができます。
以下の表は、Whereabouts を使用した動的 IP アドレス割り当ての設定について説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
IPAM のアドレスタイプ。値 |
|
|
| IP アドレスと範囲を CIDR 表記。IP アドレスは、この範囲内のアドレスから割り当てられます。 |
|
|
| オプション: CIDR 表記の IP アドレスと範囲 (0 個以上) の一覧。除外されたアドレス範囲内の IP アドレスは割り当てられません。 |
Whereabouts を使用する動的 IP アドレス割り当ての設定例
{
"ipam": {
"type": "whereabouts",
"range": "192.0.2.192/27",
"exclude": [
"192.0.2.192/30",
"192.0.2.196/32"
]
}
}12.2.5. Cluster Network Operator による追加ネットワーク割り当ての作成
Cluster Network Operator (CNO) は追加ネットワークの定義を管理します。作成する追加ネットワークを指定する場合、CNO は NetworkAttachmentDefinition オブジェクトを自動的に作成します。
Cluster Network Operator が管理する NetworkAttachmentDefinition オブジェクトは編集しないでください。これを実行すると、追加ネットワークのネットワークトラフィックが中断する可能性があります。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
CNO 設定を編集するには、以下のコマンドを入力します。
$ oc edit networks.operator.openshift.io cluster以下のサンプル CR のように、作成される追加ネットワークの設定を追加して、作成している CR を変更します。
apiVersion: operator.openshift.io/v1 kind: Network metadata: name: cluster spec: # ... additionalNetworks: - name: tertiary-net namespace: project2 type: Raw rawCNIConfig: |- { "cniVersion": "0.3.1", "name": "tertiary-net", "type": "ipvlan", "master": "eth1", "mode": "l2", "ipam": { "type": "static", "addresses": [ { "address": "192.168.1.23/24" } ] } }- 変更を保存し、テキストエディターを終了して、変更をコミットします。
検証
以下のコマンドを実行して、CNO が NetworkAttachmentDefinition オブジェクトを作成していることを確認します。CNO がオブジェクトを作成するまでに遅延が生じる可能性があります。
$ oc get network-attachment-definitions -n <namespace>ここでは、以下のようになります。
<namespace>- CNO の設定に追加したネットワーク割り当ての namespace を指定します。
出力例
NAME AGE test-network-1 14m
12.2.6. YAML マニフェストを適用した追加のネットワーク割り当ての作成
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
以下の例のように、追加のネットワーク設定を含む YAML ファイルを作成します。
apiVersion: k8s.cni.cncf.io/v1 kind: NetworkAttachmentDefinition metadata: name: next-net spec: config: |- { "cniVersion": "0.3.1", "name": "work-network", "type": "host-device", "device": "eth1", "ipam": { "type": "dhcp" } }追加のネットワークを作成するには、次のコマンドを入力します。
$ oc apply -f <file>.yamlここでは、以下のようになります。
<file>- YAML マニフェストを含むファイルの名前を指定します。
12.3. 仮想ルーティングおよび転送について
12.3.1. 仮想ルーティングおよび転送について
VRF (Virtual Routing and Forwarding) デバイスは IP ルールとの組み合わせにより、仮想ルーティングと転送ドメインを作成する機能を提供します。VRF は、CNF で必要なパーミッションの数を減らし、セカンダリーネットワークのネットワークトポロジーの可視性を強化します。VRF はマルチテナンシー機能を提供するために使用されます。たとえば、この場合、各テナントには固有のルーティングテーブルがあり、異なるデフォルトゲートウェイが必要です。
プロセスは、ソケットを VRF デバイスにバインドできます。バインドされたソケット経由のパケットは、VRF デバイスに関連付けられたルーティングテーブルを使用します。VRF の重要な機能として、これは OSI モデルレイヤー 3 以上にのみ影響を与えるため、LLDP などの L2 ツールは影響を受けません。これにより、ポリシーベースのルーティングなどの優先度の高い IP ルールが、特定のトラフィックを転送する VRF デバイスルールよりも優先されます。
12.3.1.1. Telecommunications Operator についての Pod のセカンダリーネットワークの利点
通信のユースケースでは、各 CNF が同じアドレス空間を共有する複数の異なるネットワークに接続される可能性があります。これらのセカンダリーネットワークは、クラスターのメインネットワーク CIDR と競合する可能性があります。CNI VRF プラグインを使用すると、ネットワーク機能は、同じ IP アドレスを使用して異なるユーザーのインフラストラクチャーに接続でき、複数の異なるお客様の分離された状態を維持します。IP アドレスは OpenShift Container Platform の IP スペースと重複します。CNI VRF プラグインは、CNF で必要なパーミッションの数も減らし、セカンダリーネットワークのネットワークトポロジーの可視性を高めます。
12.4. Pod の追加のネットワークへの割り当て
クラスターユーザーとして、Pod を追加のネットワークに割り当てることができます。
12.4.1. Pod の追加ネットワークへの追加
Pod を追加のネットワークに追加できます。Pod は、デフォルトネットワークで通常のクラスター関連のネットワークトラフィックを継続的に送信します。
Pod が作成されると、追加のネットワークが割り当てられます。ただし、Pod がすでに存在する場合は、追加のネットワークをこれに割り当てることはできません。
Pod が追加ネットワークと同じ namespace にあること。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 - クラスターにログインする。
手順
アノテーションを
Podオブジェクトに追加します。以下のアノテーション形式のいずれかのみを使用できます。カスタマイズせずに追加ネットワークを割り当てるには、以下の形式でアノテーションを追加します。
<network>を、Pod に関連付ける追加ネットワークの名前に置き換えます。metadata: annotations: k8s.v1.cni.cncf.io/networks: <network>[,<network>,...]1 - 1
- 複数の追加ネットワークを指定するには、各ネットワークをコンマで区切ります。コンマの間にはスペースを入れないでください。同じ追加ネットワークを複数回指定した場合、Pod は複数のネットワークインターフェイスをそのネットワークに割り当てます。
カスタマイズして追加のネットワークを割り当てるには、以下の形式でアノテーションを追加します。
metadata: annotations: k8s.v1.cni.cncf.io/networks: |- [ { "name": "<network>",1 "namespace": "<namespace>",2 "default-route": ["<default-route>"]3 } ]
Pod を作成するには、以下のコマンドを入力します。
<name>を Pod の名前に置き換えます。$ oc create -f <name>.yamlオプション: アノテーションが
PodCR に存在することを確認するには、<name>を Pod の名前に置き換えて、以下のコマンドを入力します。$ oc get pod <name> -o yaml以下の例では、
example-podPod が追加ネットワークのnet1に割り当てられています。$ oc get pod example-pod -o yaml apiVersion: v1 kind: Pod metadata: annotations: k8s.v1.cni.cncf.io/networks: macvlan-bridge k8s.v1.cni.cncf.io/networks-status: |-1 [{ "name": "openshift-sdn", "interface": "eth0", "ips": [ "10.128.2.14" ], "default": true, "dns": {} },{ "name": "macvlan-bridge", "interface": "net1", "ips": [ "20.2.2.100" ], "mac": "22:2f:60:a5:f8:00", "dns": {} }] name: example-pod namespace: default spec: ... status: ...- 1
k8s.v1.cni.cncf.io/networks-statusパラメーターは、オブジェクトの JSON 配列です。各オブジェクトは、Pod に割り当てられる追加のネットワークのステータスについて説明します。アノテーションの値はプレーンテキストの値として保存されます。
12.4.1.1. Pod 固有のアドレスおよびルーティングオプションの指定
Pod を追加のネットワークに割り当てる場合、特定の Pod でそのネットワークに関するその他のプロパティーを指定する必要がある場合があります。これにより、ルーティングの一部を変更することができ、静的 IP アドレスおよび MAC アドレスを指定できます。これを実行するには、JSON 形式のアノテーションを使用できます。
前提条件
- Pod が追加ネットワークと同じ namespace にあること。
-
OpenShift コマンドラインインターフェイス (
oc) のインストール。 - クラスターにログインすること。
手順
アドレスおよび/またはルーティングオプションを指定する間に Pod を追加のネットワークに追加するには、以下の手順を実行します。
Podリソース定義を編集します。既存のPodリソースを編集する場合は、以下のコマンドを実行してデフォルトエディターでその定義を編集します。<name>を、編集するPodリソースの名前に置き換えます。$ oc edit pod <name>Podリソース定義で、k8s.v1.cni.cncf.io/networksパラメーターを Pod のmetadataマッピングに追加します。k8s.v1.cni.cncf.io/networksは、追加のプロパティーを指定するだけでなく、NetworkAttachmentDefinitionカスタムリソース (CR) 名を参照するオブジェクト一覧の JSON 文字列を受け入れます。metadata: annotations: k8s.v1.cni.cncf.io/networks: '[<network>[,<network>,...]]'1 - 1
<network>を、以下の例にあるように JSON オブジェクトに置き換えます。一重引用符が必要です。
以下の例では、アノテーションで
default-routeパラメーターを使用して、デフォルトルートを持つネットワーク割り当てを指定します。apiVersion: v1 kind: Pod metadata: name: example-pod annotations: k8s.v1.cni.cncf.io/networks: ' { "name": "net1" }, { "name": "net2",1 "default-route": ["192.0.2.1"]2 }' spec: containers: - name: example-pod command: ["/bin/bash", "-c", "sleep 2000000000000"] image: centos/tools
デフォルトのルートにより、他のルートに指定されていないトラフィックがゲートウェイにルーティングされます。
OpenShift Container Platform のデフォルトのネットワークインターフェイス以外のインターフェイスへのデフォルトのルートを設定すると、Pod 間のトラフィックについて予想されるトラフィックが別のインターフェイスでルーティングされる可能性があります。
Pod のルーティングプロパティーを確認する場合、oc コマンドを Pod 内で ip コマンドを実行するために使用できます。
$ oc exec -it <pod_name> -- ip route
また、Pod の k8s.v1.cni.cncf.io/networks-status を参照して、JSON 形式の一覧のオブジェクトで default-route キーの有無を確認し、デフォルトルートが割り当てられている追加ネットワークを確認することができます。
Pod に静的 IP アドレスまたは MAC アドレスを設定するには、JSON 形式のアノテーションを使用できます。これには、この機能をとくに許可するネットワークを作成する必要があります。これは、CNO の rawCNIConfig で指定できます。
以下のコマンドを実行して CNO CR を編集します。
$ oc edit networks.operator.openshift.io cluster
以下の YAML は、CNO の設定パラメーターについて説明しています。
Cluster Network Operator YAML の設定
name: <name>
namespace: <namespace>
rawCNIConfig: '{
...
}'
type: Raw以下のオブジェクトは、macvlan CNI プラグインを使用して静的 MAC アドレスと IP アドレスを使用するための設定パラメーターについて説明しています。
静的 IP および MAC アドレスを使用した macvlan CNI プラグイン JSON 設定オブジェクト
{
"cniVersion": "0.3.1",
"name": "<name>",
"plugins": [{
"type": "macvlan",
"capabilities": { "ips": true },
"master": "eth0",
"mode": "bridge",
"ipam": {
"type": "static"
}
}, {
"capabilities": { "mac": true },
"type": "tuning"
}]
}上記のネットワーク割り当ては、特定の Pod に割り当てられる静的 IP アドレスと MAC アドレスを指定するキーと共に、JSON 形式のアノテーションで参照できます。
以下を使用して Pod を編集します。
$ oc edit pod <name>静的 IP および MAC アドレスを使用した macvlan CNI プラグイン JSON 設定オブジェクト
apiVersion: v1
kind: Pod
metadata:
name: example-pod
annotations:
k8s.v1.cni.cncf.io/networks: '[
{
"name": "<name>",
"ips": [ "192.0.2.205/24" ],
"mac": "CA:FE:C0:FF:EE:00"
}
]'静的 IP アドレスおよび MAC アドレスを同時に使用することはできません。これらは個別に使用することも、一緒に使用することもできます。
追加のネットワークを持つ Pod の IP アドレスと MAC プロパティーを検証するには、oc コマンドを使用して Pod 内で ip コマンドを実行します。
$ oc exec -it <pod_name> -- ip a12.5. 追加ネットワークからの Pod の削除
クラスターユーザーとして、追加のネットワークから Pod を削除できます。
12.5.1. 追加ネットワークからの Pod の削除
Pod を削除するだけで、追加のネットワークから Pod を削除できます。
前提条件
- 追加のネットワークが Pod に割り当てられている。
-
OpenShift CLI (
oc) をインストールしている。 - クラスターにログインする。
手順
Pod を削除するには、以下のコマンドを入力します。
$ oc delete pod <name> -n <namespace>-
<name>は Pod の名前です。 -
<namespace>は Pod が含まれる namespace です。
-
12.6. 追加ネットワークの編集
クラスター管理者は、既存の追加ネットワークの設定を変更することができます。
12.6.1. 追加ネットワーク割り当て定義の変更
クラスター管理者は、既存の追加ネットワークに変更を加えることができます。追加ネットワークに割り当てられる既存の Pod は更新されません。
前提条件
- クラスター用に追加のネットワークを設定している。
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
クラスターの追加ネットワークを編集するには、以下の手順を実行します。
以下のコマンドを実行し、デフォルトのテキストエディターで Cluster Network Operator (CNO) CR を編集します。
$ oc edit networks.operator.openshift.io cluster-
additionalNetworksコレクションで、追加ネットワークを変更内容で更新します。 - 変更を保存し、テキストエディターを終了して、変更をコミットします。
オプション: 以下のコマンドを実行して、CNO が
NetworkAttachmentDefinitionオブジェクトを更新していることを確認します。<network-name>を表示する追加ネットワークの名前に置き換えます。CNO がNetworkAttachmentDefinitionオブジェクトを更新して変更内容が反映されるまでに遅延が生じる可能性があります。$ oc get network-attachment-definitions <network-name> -o yamlたとえば、以下のコンソールの出力は
net1という名前のNetworkAttachmentDefinitionオブジェクトを表示します。$ oc get network-attachment-definitions net1 -o go-template='{{printf "%s\n" .spec.config}}' { "cniVersion": "0.3.1", "type": "macvlan", "master": "ens5", "mode": "bridge", "ipam": {"type":"static","routes":[{"dst":"0.0.0.0/0","gw":"10.128.2.1"}],"addresses":[{"address":"10.128.2.100/23","gateway":"10.128.2.1"}],"dns":{"nameservers":["172.30.0.10"],"domain":"us-west-2.compute.internal","search":["us-west-2.compute.internal"]}} }
12.7. 追加ネットワークの削除
クラスター管理者は、追加のネットワーク割り当てを削除できます。
12.7.1. 追加ネットワーク割り当て定義の削除
クラスター管理者は、追加ネットワークを OpenShift Container Platform クラスターから削除できます。追加ネットワークは、割り当てられている Pod から削除されません。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
クラスターから追加ネットワークを削除するには、以下の手順を実行します。
以下のコマンドを実行して、デフォルトのテキストエディターで Cluster Network Operator (CNO) を編集します。
$ oc edit networks.operator.openshift.io cluster削除しているネットワーク割り当て定義の
additionalNetworksコレクションから設定を削除し、CR を変更します。apiVersion: operator.openshift.io/v1 kind: Network metadata: name: cluster spec: additionalNetworks: []1 - 1
additionalNetworksコレクションの追加ネットワーク割り当てのみの設定マッピングを削除する場合、空のコレクションを指定する必要があります。
- 変更を保存し、テキストエディターを終了して、変更をコミットします。
オプション: 以下のコマンドを実行して、追加ネットワーク CR が削除されていることを確認します。
$ oc get network-attachment-definition --all-namespaces
12.8. VRF へのセカンダリーネットワークの割り当て
CNI VRF プラグインはテクノロジープレビュー機能としてのみご利用いただけます。テクノロジープレビュー機能は Red Hat の実稼働環境でのサービスレベルアグリーメント (SLA) ではサポートされていないため、Red Hat では実稼働環境での使用を推奨していません。Red Hat は実稼働環境でこれらを使用することを推奨していません。テクノロジープレビューの機能は、最新の製品機能をいち早く提供して、開発段階で機能のテストを行いフィードバックを提供していただくことを目的としています。
Red Hat のテクノロジープレビュー機能のサポート範囲についての詳細は、https://access.redhat.com/ja/support/offerings/techpreview/ を参照してください。
12.8.1. VRF へのセカンダリーネットワークの割り当て
クラスター管理者は、CNI VRF プラグインを使用して、VRF ドメインの追加のネットワークを設定できます。このプラグインにより作成される仮想ネットワークは、指定する物理インターフェイスに関連付けられます。
VRF を使用するアプリケーションを特定のデバイスにバインドする必要があります。一般的な使用方法として、ソケットに SO_BINDTODEVICE オプションを使用できます。SO_BINDTODEVICE は、渡されるインターフェイス名で指定されているデバイスにソケットをバインドします (例: eth1)。SO_BINDTODEVICE を使用するには、アプリケーションに CAP_NET_RAW 機能がある必要があります。
12.8.1.1. CNI VRF プラグインを使用した追加のネットワーク割り当ての作成
Cluster Network Operator (CNO) は追加ネットワークの定義を管理します。作成する追加ネットワークを指定する場合、CNO は NetworkAttachmentDefinition カスタムリソース (CR) を自動的に作成します。
Cluster Network Operator が管理する NetworkAttachmentDefinition CR は編集しないでください。これを実行すると、追加ネットワークのネットワークトラフィックが中断する可能性があります。
CNI VRF プラグインで追加のネットワーク割り当てを作成するには、以下の手順を実行します。
前提条件
- OpenShift Container Platform CLI (oc) をインストールします。
- cluster-admin 権限を持つユーザーとして OpenShift クラスターにログインします。
手順
以下のサンプル CR のように、追加のネットワーク割り当て用の
Networkカスタムリソース (CR) を作成し、追加ネットワークのrawCNIConfig設定を挿入します。YAML をadditional-network-attachment.yamlファイルとして保存します。apiVersion: operator.openshift.io/v1 kind: Network metadata: name: cluster spec: additionalNetworks: - name: test-network-1 namespace: additional-network-1 type: Raw rawCNIConfig: '{ "cniVersion": "0.3.1", "name": "macvlan-vrf", "plugins": [1 { "type": "macvlan",2 "master": "eth1", "ipam": { "type": "static", "addresses": [ { "address": "191.168.1.23/24" } ] } }, { "type": "vrf", "vrfname": "example-vrf-name",3 "table": 10014 }] }'- 1
pluginsは一覧である必要があります。一覧の最初の項目は、VRF ネットワークのベースとなるセカンダリーネットワークである必要があります。一覧の 2 つ目の項目は、VRF プラグイン設定です。- 2
typeはvrfに設定する必要があります。- 3
vrfnameは、インターフェイスが割り当てられた VRF の名前です。これが Pod に存在しない場合は作成されます。- 4
- オプション:
tableはルーティングテーブル ID です。デフォルトで、tableidパラメーターが使用されます。これが指定されていない場合、CNI は空のルーティングテーブル ID を VRF に割り当てます。
注記VRF は、リソースが
netdeviceタイプの場合にのみ正常に機能します。Networkリソースを作成します。$ oc create -f additional-network-attachment.yaml以下のコマンドを実行して、CNO が
NetworkAttachmentDefinitionCR を作成していることを確認します。<namespace>を、ネットワーク割り当ての設定時に指定した namespace に置き換えます (例:additional-network-1)。$ oc get network-attachment-definitions -n <namespace>出力例
NAME AGE additional-network-1 14m注記CNO が CR を作成するまでに遅延が生じる可能性があります。
追加の VRF ネットワーク割り当てが正常であることの確認
VRF CNI が正しく設定され、追加のネットワーク割り当てが接続されていることを確認するには、以下を実行します。
- VRF CNI を使用するネットワークを作成します。
- ネットワークを Pod に割り当てます。
Pod のネットワーク割り当てが VRF の追加ネットワークに接続されていることを確認します。Pod にリモートシェルを実行し、以下のコマンドを実行します。
$ ip vrf show出力例
Name Table ----------------------- red 10VRF インターフェイスがセカンダリーインターフェイスのマスターであることを確認します。
$ ip link出力例
5: net1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master red state UP mode
第13章 ハードウェアネットワーク
13.1. Single Root I/O Virtualization (SR-IOV) ハードウェアネットワークについて
Single Root I/O Virtualization (SR-IOV) 仕様は、単一デバイスを複数の Pod で共有できる PCI デバイス割り当てタイプの標準です。
SR-IOV を使用すると、準拠したネットワークデバイス (ホストノードで物理機能 (PF) として認識される) を複数の仮想機能 (VF) にセグメント化することができます。VF は他のネットワークデバイスと同様に使用されます。デバイスの SR-IOV デバイスドライバーは、VF がコンテナーで公開される方法を判別します。
-
netdeviceドライバー: コンテナーのnetns内の通常のカーネルネットワークデバイス -
vfio-pciドライバー: コンテナーにマウントされるキャラクターデバイス
SR-IOV ネットワークデバイスは、ベアメタルまたは Red Hat Open Stack Platform (RHOSP) インフラ上にインストールされた OpenShift Container Platform クラスターにネットワークを追加して、高帯域または低遅延を確保する必要のあるアプリケーションに使用できます。
次のコマンドを使用して、ノードで SR-IOV を有効にできます。
$ oc label node <node_name> feature.node.kubernetes.io/network-sriov.capable="true"13.1.1. SR-IOV ネットワークデバイスを管理するコンポーネント
SR-IOV Network Operator は SR-IOV スタックのコンポーネントを作成し、管理します。以下の機能を実行します。
- SR-IOV ネットワークデバイスの検出および管理のオーケストレーション
-
SR-IOV Container Network Interface (CNI) の
NetworkAttachmentDefinitionカスタムリソースの生成 - SR-IOV ネットワークデバイスプラグインの設定の作成および更新
-
ノード固有の
SriovNetworkNodeStateカスタムリソースの作成 -
各
SriovNetworkNodeStateカスタムリソースのspec.interfacesフィールドの更新
Operator は以下のコンポーネントをプロビジョニングします。
- SR-IOV ネットワーク設定デーモン
- SR-IOV Operator の起動時にワーカーノードにデプロイされる DaemonSet。デーモンは、クラスターで SR-IOV ネットワークデバイスを検出し、初期化します。
- SR-IOV Operator Webhook
- Operator カスタムリソースを検証し、未設定フィールドに適切なデフォルト値を設定する動的受付コントローラー Webhook。
- SR-IOV Network Resources Injector
-
SR-IOV VF などのカスタムネットワークリソースの要求および制限のある Kubernetes Pod 仕様のパッチを適用するための機能を提供する動的受付コントローラー Webhook。SR-IOV ネットワークリソースインジェクターは、 Pod 内の最初のコンテナーのみに
resourceフィールドを自動的に追加します。 - SR-IOV ネットワークデバイスプラグイン
- SR-IOV ネットワーク Virtual Function (VF) リソースの検出、公開、割り当てを実行するデバイスプラグイン。デバイスプラグインは、とりわけ物理デバイスでの制限されたリソースの使用を有効にするために Kubernetes で使用されます。デバイスプラグインは Kubernetes スケジューラーにリソースの可用性を認識させるため、スケジューラーはリソースが十分にあるノードで Pod をスケジュールできます。
- SR-IOV CNI プラグイン
- SR-IOV デバイスプラグインから割り当てられる VF インターフェイスを直接 Pod に割り当てる CNI プラグイン。
- SR-IOV InfiniBand CNI プラグイン
- SR-IOV デバイスプラグインから割り当てられる InfiniBand (IB) VF インターフェイスを直接 Pod に割り当てる CNI プラグイン。
SR-IOV Network Resources Injector および SR-IOV Network Operator Webhook は、デフォルトで有効にされ、default の SriovOperatorConfig CR を編集して無効にできます。
13.1.1.1. サポートされるプラットフォーム
SR-IOV Network Operator は、以下のプラットフォームに対応しています。
- ベアメタル
- Red Hat OpenStack Platform (RHOSP)
13.1.1.2. サポートされるデバイス
以下のネットワークインターフェイスコントローラーは、OpenShift Container Platform でサポートされています。
| 製造元 | モデル | ベンダー ID | デバイス ID |
|---|---|---|---|
| Intel | X710 | 8086 | 1572 |
| Intel | XXV710 | 8086 | 158b |
| Mellanox | MT27700 Family [ConnectX‑4] | 15b3 | 1013 |
| Mellanox | MT27710 Family [ConnectX‑4 Lx] | 15b3 | 1015 |
| Mellanox | MT27800 Family [ConnectX‑5] | 15b3 | 1017 |
| Mellanox | MT28908 Family [ConnectX‑6] | 15b3 | 101b |
13.1.1.3. SR-IOV ネットワークデバイスの自動検出
SR-IOV Network Operator は、クラスターでワーカーノード上の SR-IOV 対応ネットワークデバイスを検索します。Operator は、互換性のある SR-IOV ネットワークデバイスを提供する各ワーカーノードの SriovNetworkNodeState カスタムリソース (CR) を作成し、更新します。
CR にはワーカーノードと同じ名前が割り当てられます。status.interfaces 一覧は、ノード上のネットワークデバイスについての情報を提供します。
SriovNetworkNodeState オブジェクトは変更しないでください。Operator はこれらのリソースを自動的に作成し、管理します。
13.1.1.3.1. SriovNetworkNodeState オブジェクトの例
以下の YAML は、SR-IOV Network Operator によって作成される SriovNetworkNodeState オブジェクトの例です。
SriovNetworkNodeState オブジェクト
apiVersion: sriovnetwork.openshift.io/v1
kind: SriovNetworkNodeState
metadata:
name: node-25
namespace: openshift-sriov-network-operator
ownerReferences:
- apiVersion: sriovnetwork.openshift.io/v1
blockOwnerDeletion: true
controller: true
kind: SriovNetworkNodePolicy
name: default
spec:
dpConfigVersion: "39824"
status:
interfaces:
- deviceID: "1017"
driver: mlx5_core
mtu: 1500
name: ens785f0
pciAddress: "0000:18:00.0"
totalvfs: 8
vendor: 15b3
- deviceID: "1017"
driver: mlx5_core
mtu: 1500
name: ens785f1
pciAddress: "0000:18:00.1"
totalvfs: 8
vendor: 15b3
- deviceID: 158b
driver: i40e
mtu: 1500
name: ens817f0
pciAddress: 0000:81:00.0
totalvfs: 64
vendor: "8086"
- deviceID: 158b
driver: i40e
mtu: 1500
name: ens817f1
pciAddress: 0000:81:00.1
totalvfs: 64
vendor: "8086"
- deviceID: 158b
driver: i40e
mtu: 1500
name: ens803f0
pciAddress: 0000:86:00.0
totalvfs: 64
vendor: "8086"
syncStatus: Succeeded13.1.1.4. Pod での Virtual Function (VF) の使用例
SR-IOV VF が割り当てられている Pod で、Remote Direct Memory Access (RDMA) または Data Plane Development Kit (DPDK) アプリケーションを実行できます。
以下の例では、RDMA モードで Virtual Function (VF) を使用する Pod を示しています。
RDMA モードを使用する Pod 仕様
apiVersion: v1
kind: Pod
metadata:
name: rdma-app
annotations:
k8s.v1.cni.cncf.io/networks: sriov-rdma-mlnx
spec:
containers:
- name: testpmd
image: <RDMA_image>
imagePullPolicy: IfNotPresent
securityContext:
runAsUser: 0
capabilities:
add: ["IPC_LOCK","SYS_RESOURCE","NET_RAW"]
command: ["sleep", "infinity"]以下の例は、DPDK モードの VF のある Pod を示しています。
DPDK モードを使用する Pod 仕様
apiVersion: v1
kind: Pod
metadata:
name: dpdk-app
annotations:
k8s.v1.cni.cncf.io/networks: sriov-dpdk-net
spec:
containers:
- name: testpmd
image: <DPDK_image>
securityContext:
runAsUser: 0
capabilities:
add: ["IPC_LOCK","SYS_RESOURCE","NET_RAW"]
volumeMounts:
- mountPath: /dev/hugepages
name: hugepage
resources:
limits:
memory: "1Gi"
cpu: "2"
hugepages-1Gi: "4Gi"
requests:
memory: "1Gi"
cpu: "2"
hugepages-1Gi: "4Gi"
command: ["sleep", "infinity"]
volumes:
- name: hugepage
emptyDir:
medium: HugePages13.1.1.5. コンテナーアプリケーションで使用する DPDK ライブラリー
オプションライブラリー の app-netutil は、その Pod 内で実行されるコンテナーから Pod についてのネットワーク情報を収集するための複数の API メソッドを提供します。
このライブラリーは、DPDK (Data Plane Development Kit) モードの SR-IOV 仮想機能 (VF) のコンテナーへの統合を支援することを目的としています。このライブラリーは Golang API と C API の両方を提供します。
現時点で 3 つの API メソッドが実装されています。
GetCPUInfo()- この機能は、コンテナーで利用可能な CPU を判別し、一覧を呼び出し元に返します。
GetHugepages()この機能は、各コンテナーの
Pod仕様で要求される hugepage メモリーの量を判別し、値を呼び出し元に返します。注記Kubernetes Downward API 経由で hugepage を公開することは、Kubernetes 1.20 のアルファ機能であり、OpenShift Container Platform では有効にされません。Kubernetes 1.20 以降で機能ゲートの
FEATURE_GATES="DownwardAPIHugePages=true" を有効にするを有効にして API をテストすることができます。GetInterfaces()- この機能は、コンテナーのインターフェイスセットを判別し、インターフェイスタイプとタイプ固有のデータと共に一覧を返します。
また、サンプルの Docker イメージ dpdk-app-centos も用意されています。このイメージは、Pod 仕様の l2fwd、l3wd または testpmd の環境変数に基づいて、以下の DPDK サンプルアプリケーションのいずれかを実行できます。この Docker イメージは、app-netutil をコンテナーイメージ自体に統合するサンプルを提供します。ライブラリーも、必要なデータを収集し、データを既存の DPDK ワークロードに渡す init-container に統合できます。
13.1.2. 次のステップ
- SR-IOV Network Operator のインストール
- オプション: SR-IOV ネットワーク Operator の設定
- SR-IOV ネットワークデバイスの設定
- OpenShift Virtualization を使用する場合: 仮想マシンの SR-IOV ネットワークデバイスの設定
- SR-IOV ネットワーク割り当ての設定
- Pod の SR-IOV の追加ネットワークへの追加
13.2. SR-IOV Network Operator のインストール
Single Root I/O Virtualization (SR-IOV) ネットワーク Operator をクラスターにインストールし、SR-IOV ネットワークデバイスとネットワークの割り当てを管理できます。
13.2.1. SR-IOV Network Operator のインストール
クラスター管理者は、OpenShift Container Platform CLI または Web コンソールを使用して SR-IOV Network Operator をインストールできます。
13.2.1.1. CLI: SR-IOV Network Operator のインストール
クラスター管理者は、CLI を使用して Operator をインストールできます。
前提条件
- SR-IOV に対応するハードウェアを持つノードでベアメタルハードウェアにインストールされたクラスター。
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つアカウント。
手順
openshift-sriov-network-operatornamespace を作成するには、以下のコマンドを入力します。$ cat << EOF| oc create -f - apiVersion: v1 kind: Namespace metadata: name: openshift-sriov-network-operator EOFOperatorGroup CR を作成するには、以下のコマンドを実行します。
$ cat << EOF| oc create -f - apiVersion: operators.coreos.com/v1 kind: OperatorGroup metadata: name: sriov-network-operators namespace: openshift-sriov-network-operator spec: targetNamespaces: - openshift-sriov-network-operator EOFSR-IOV Network Operator にサブスクライブします。
以下のコマンドを実行して OpenShift Container Platform のメジャーおよびマイナーバージョンを取得します。これは、次の手順の
channelの値に必要です。$ OC_VERSION=$(oc version -o yaml | grep openshiftVersion | \ grep -o '[0-9]*[.][0-9]*' | head -1)SR-IOV Network Operator の Subscription CR を作成するには、以下のコマンドを入力します。
$ cat << EOF| oc create -f - apiVersion: operators.coreos.com/v1alpha1 kind: Subscription metadata: name: sriov-network-operator-subscription namespace: openshift-sriov-network-operator spec: channel: "${OC_VERSION}" name: sriov-network-operator source: redhat-operators sourceNamespace: openshift-marketplace EOF
Operator がインストールされていることを確認するには、以下のコマンドを入力します。
$ oc get csv -n openshift-sriov-network-operator \ -o custom-columns=Name:.metadata.name,Phase:.status.phase出力例
Name Phase sriov-network-operator.4.4.0-202006160135 Succeeded
13.2.1.2. Web コンソール: SR-IOV Network Operator のインストール
クラスター管理者は、Web コンソールを使用して Operator をインストールできます。
CLI を使用して Operator グループを作成する必要があります。
前提条件
- SR-IOV に対応するハードウェアを持つノードでベアメタルハードウェアにインストールされたクラスター。
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つアカウント。
手順
SR-IOV Network Operator の namespace を作成します。
- OpenShift Container Platform Web コンソールで、Administration → Namespaces をクリックします。
- Create Namespace をクリックします。
-
Name フィールドに
openshift-sriov-network-operatorを入力し、Create をクリックします。
SR-IOV Network Operator をインストールします。
- OpenShift Container Platform Web コンソールで、Operators → OperatorHub をクリックします。
- 利用可能な Operator の一覧から SR-IOV Network Operator を選択してから Install をクリックします。
- Install Operator ページの A specific namespace on the cluster の下で、openshift-sriov-network-operator を選択します。
- Install をクリックします。
SR-IOV Network Operator が正常にインストールされていることを確認します。
- Operators → Installed Operators ページに移動します。
Status が InstallSucceeded の状態で、SR-IOV Network Operator が openshift-sriov-network-operator プロジェクトに一覧表示されていることを確認します。
注記インストール時に、 Operator は Failed ステータスを表示する可能性があります。インストールが後に InstallSucceeded メッセージを出して正常に実行される場合は、Failed メッセージを無視できます。
Operator がインストール済みとして表示されない場合に、さらにトラブルシューティングを実行します。
- Operator Subscriptions および Install Plans タブで、Status の下の失敗またはエラーの有無を確認します。
-
Workloads → Pods ページに移動し、
openshift-sriov-network-operatorプロジェクトで Pod のログを確認します。
13.2.2. 次のステップ
- オプション: SR-IOV ネットワーク Operator の設定
13.3. SR-IOV Network Operator の設定
Single Root I/O Virtualization (SR-IOV) ネットワーク Operator は、クラスターで SR-IOV ネットワークデバイスおよびネットワーク割り当てを管理します。
13.3.1. SR-IOV Network Operator の設定
通常、SR-IOV Network Operator 設定を変更する必要はありません。デフォルト設定は、ほとんどのユースケースで推奨されます。Operator のデフォルト動作がユースケースと互換性がない場合にのみ、関連する設定を変更する手順を実行します。
SR-IOV Network Operator は SriovOperatorConfig.sriovnetwork.openshift.io CustomResourceDefinition リソースを追加します。Operator は、openshift-sriov-network-operator namespace に default という名前の SriovOperatorConfig カスタムリソース (CR) を自動的に作成します。
default CR には、クラスターの SR-IOV Network Operator 設定が含まれます。Operator 設定を変更するには、この CR を変更する必要があります。
SriovOperatorConfig オブジェクトは、Operator を設定するための複数のフィールドを提供します。
-
enableInjectorを使用すると、プロジェクト管理者は Network Resources Injector デーモンセットを有効または無効にすることができます。 -
enableOperatorWebhookを使用すると、プロジェクト管理者は Operator Admission Controller webhook デーモンセットを有効または無効にすることができます。 -
configDaemonNodeSelectorを使用すると、プロジェクト管理者は選択したノードで SR-IOV Network Config Daemon をスケジュールできます。
13.3.1.1. Network Resources Injector について
Network Resources Injector は Kubernetes Dynamic Admission Controller アプリケーションです。これは、以下の機能を提供します。
-
SR-IOV リソース名を SR-IOV ネットワーク割り当て定義アノテーションに従って追加するための、
Pod仕様でのリソース要求および制限の変更。 -
Pod のアノテーションおよびラベルを
/etc/podnetinfoパスの下にあるファイルとして公開するための、Downward API ボリュームでのPod仕様の変更。
デフォルトで、Network Resources Injector は SR-IOV Operator によって有効にされ、すべてのコントロールプレーンノード (別名マスターノード) でデーモンセットとして実行されます。以下は、3 つのコントロールプレーンノードを持つクラスターで実行される Network Resources Injector Pod の例です。
$ oc get pods -n openshift-sriov-network-operator出力例
NAME READY STATUS RESTARTS AGE
network-resources-injector-5cz5p 1/1 Running 0 10m
network-resources-injector-dwqpx 1/1 Running 0 10m
network-resources-injector-lktz5 1/1 Running 0 10m13.3.1.2. SR-IOV Operator Admission Controller Webhook について
SR-IOV Operator Admission Controller Webbook は Kubernetes Dynamic Admission Controller アプリケーションです。これは、以下の機能を提供します。
-
作成時または更新時の
SriovNetworkNodePolicyCR の検証 -
CR の作成または更新時の
priorityおよびdeviceTypeフィールドのデフォルト値の設定によるSriovNetworkNodePolicyCR の変更
デフォルトで、SR-IOV Operator Admission Controller Webhook は Operator によって有効にされ、すべてのコントロールプレーンノードでデーモンセットとして実行されます。以下は、3 つのコントロールプレーンノードを持つクラスターで実行される Operator Admission Controller Webhook Pod の例です。
$ oc get pods -n openshift-sriov-network-operator出力例
NAME READY STATUS RESTARTS AGE
operator-webhook-9jkw6 1/1 Running 0 16m
operator-webhook-kbr5p 1/1 Running 0 16m
operator-webhook-rpfrl 1/1 Running 0 16m13.3.1.3. カスタムノードセレクターについて
SR-IOV Network Config デーモンは、クラスターノード上の SR-IOV ネットワークデバイスを検出し、設定します。デフォルトで、これはクラスター内のすべての worker ノードにデプロイされます。ノードラベルを使用して、SR-IOV Network Config デーモンが実行するノードを指定できます。
13.3.1.4. Network Resources Injector の無効化または有効化
デフォルトで有効にされている Network Resources Injector を無効にするか、または有効にするには、以下の手順を実行します。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。 - SR-IOV Operator がインストールされていること。
手順
enableInjectorフィールドを設定します。<value>をfalseに置き換えて機能を無効にするか、またはtrueに置き換えて機能を有効にします。$ oc patch sriovoperatorconfig default \ --type=merge -n openshift-sriov-network-operator \ --patch '{ "spec": { "enableInjector": <value> } }'
13.3.1.5. SR-IOV Operator Admission Controller Webhook の無効化または有効化
デフォルトで有効にされている なっている受付コントローラー Webhook を無効にするか、または有効にするには、以下の手順を実行します。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。 - SR-IOV Operator がインストールされていること。
手順
enableOperatorWebhookフィールドを設定します。<value>をfalseに置き換えて機能を無効するか、trueに置き換えて機能を有効にします。$ oc patch sriovoperatorconfig default --type=merge \ -n openshift-sriov-network-operator \ --patch '{ "spec": { "enableOperatorWebhook": <value> } }'
13.3.1.6. SRIOV Network Config Daemon のカスタム NodeSelector の設定
SR-IOV Network Config デーモンは、クラスターノード上の SR-IOV ネットワークデバイスを検出し、設定します。デフォルトで、これはクラスター内のすべての worker ノードにデプロイされます。ノードラベルを使用して、SR-IOV Network Config デーモンが実行するノードを指定できます。
SR-IOV Network Config デーモンがデプロイされるノードを指定するには、以下の手順を実行します。
configDaemonNodeSelector フィールドを更新する際に、SR-IOV Network Config デーモンがそれぞれの選択されたノードに再作成されます。デーモンが再作成されている間、クラスターのユーザーは新規の SR-IOV Network ノードポリシーを適用したり、新規の SR-IOV Pod を作成したりできません。
手順
Operator のノードセレクターを更新するには、以下のコマンドを入力します。
$ oc patch sriovoperatorconfig default --type=json \ -n openshift-sriov-network-operator \ --patch '[{ "op": "replace", "path": "/spec/configDaemonNodeSelector", "value": {<node-label>} }]'以下の例のように、
<node-label>を適用するラベルに置き換えます:"node-role.kubernetes.io/worker": ""
13.3.2. 次のステップ
13.4. SR-IOV ネットワークデバイスの設定
クラスターで Single Root I/O Virtualization (SR-IOV) デバイスを設定できます。
13.4.1. SR-IOV ネットワークノード設定オブジェクト
SR-IOV ネットワークノードポリシーを作成して、ノードの SR-IOV ネットワークデバイス設定を指定します。ポリシーの API オブジェクトは sriovnetwork.openshift.io API グループの一部です。
以下の YAML は SR-IOV ネットワークノードポリシーについて説明しています。
apiVersion: sriovnetwork.openshift.io/v1
kind: SriovNetworkNodePolicy
metadata:
name: <name>
namespace: openshift-sriov-network-operator
spec:
resourceName: <sriov_resource_name>
nodeSelector:
feature.node.kubernetes.io/network-sriov.capable: "true"
priority: <priority>
mtu: <mtu>
numVfs: <num>
nicSelector:
vendor: "<vendor_code>"
deviceID: "<device_id>"
pfNames: ["<pf_name>", ...]
rootDevices: ["<pci_bus_id>", ...]
netFilter: "<filter_string>"
deviceType: <device_type>
isRdma: false
linkType: <link_type> - 1
- カスタムリソースオブジェクトの名前。
- 2
- SR-IOV Operator がインストールされている namespace。
- 3
- SR-IOV デバイスプラグインのリソース名。1 つのリソース名に複数の SR-IOV ネットワークポリシーを作成できます。
- 4
- ノードセレクターは設定するノードを指定します。選択したノード上の SR-IOV ネットワークデバイスのみが設定されます。SR-IOV Container Network Interface (CNI) プラグインおよびデバイスプラグインは、選択したノードにのみデプロイされます。
- 5
- オプション: 優先度は
0から99までの整数値で指定されます。値が小さいほど優先度が高くなります。たとえば、10の優先度は99よりも高くなります。デフォルト値は99です。 - 6
- オプション: Virtual Function (VF) の最大転送単位 (MTU)。MTU の最大値は、複数の異なるネットワークインターフェイスコントローラー (NIC) に応じて異なります。
- 7
- SR-IOV 物理ネットワークデバイス用に作成する仮想機能 (VF) の数。Intel ネットワークインターフェイスコントローラー (NIC) の場合、VF の数はデバイスがサポートする VF の合計よりも大きくすることはできません。Mellanox NIC の場合、VF の数は
128よりも大きくすることはできません。 - 8
- NIC セレクターは、Operator が設定するデバイスを特定します。すべてのパラメーターの値を指定する必要はありません。意図せずにデバイスを選択しないように、ネットワークデバイスを極めて正確に特定することが推奨されます。
rootDevicesを指定する場合、vendor、deviceID、またはpfNameの値も指定する必要があります。pfNamesおよびrootDevicesの両方を同時に指定する場合、それらが同一のデバイスを参照していることを確認します。netFilterの値を指定する場合、ネットワーク ID は一意の ID であるためにその他のパラメーターを指定する必要はありません。 - 9
- オプション: SR-IOV ネットワークデバイスのベンダーの 16 進数コード。許可される値は
8086および15b3のみになります。 - 10
- オプション: SR-IOV ネットワークデバイスのデバイスの 16 進数コード。許可される値は
158b、1015、および1017のみになります。 - 11
- オプション: 1 つ以上のデバイスの物理機能 (PF) 名の配列。
- 12
- オプション: デバイスの PF 用の 1 つ以上の PCI バスアドレスの配列。以下の形式でアドレスを指定します:
0000:02:00.1 - 13
- オプション: プラットフォーム固有のネットワークフィルター。サポートされるプラットフォームは Red Hat OpenStack Platform (RHOSP) のみです。許可される値は、
openstack/NetworkID:xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxxの形式を使用します。xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxxを、/var/config/openstack/latest/network_data.jsonメタデータファイルの値に置き換えます。 - 14
- オプション: Virtual Function (VF) のドライバータイプ。許可される値は
netdeviceおよびvfio-pciのみです。デフォルト値はnetdeviceです。Mellanox NIC をベアメタルノードの Data Plane Development Kit (DPDK) モードで機能させるには、
netdeviceドライバータイプを使用し、isRdmaをtrueに設定します。 - 15
- オプション: Remote Direct Memory Access (RDMA) モードを有効にするかどうか。デフォルト値は
falseです。isRDMAパラメーターがtrueに設定される場合、引き続き RDMA 対応の VF を通常のネットワークデバイスとして使用できます。デバイスはどちらのモードでも使用できます。 - 16
- オプション: VF のリンクタイプ。
ethまたはibのいずれかの値を指定できます。イーサネットにはethを、または InfiniBand にはibを指定します。デフォルト値はethです。linkTypeがibに設定されている場合、SR-IOV Network Operator Webhook によってisRdmaはtrueに自動的に設定されます。linkTypeがibに設定されている場合、deviceTypeはvfio-pciに設定できません。
13.4.1.1. SR-IOV ネットワークノードの設定例
以下の例では、InfiniBand デバイスの設定について説明します。
InfiniBand デバイスの設定例
apiVersion: sriovnetwork.openshift.io/v1
kind: SriovNetworkNodePolicy
metadata:
name: policy-ib-net-1
namespace: openshift-sriov-network-operator
spec:
resourceName: ibnic1
nodeSelector:
feature.node.kubernetes.io/network-sriov.capable: "true"
numVfs: 4
nicSelector:
vendor: "15b3"
deviceID: "101b"
rootDevices:
- "0000:19:00.0"
linkType: ib
isRdma: true以下の例では、RHOSP 仮想マシンの SR-IOV ネットワークデバイスの設定について説明します。
仮想マシンの SR-IOV デバイスの設定例
apiVersion: sriovnetwork.openshift.io/v1
kind: SriovNetworkNodePolicy
metadata:
name: policy-sriov-net-openstack-1
namespace: openshift-sriov-network-operator
spec:
resourceName: sriovnic1
nodeSelector:
feature.node.kubernetes.io/network-sriov.capable: "true"
numVfs: 1
nicSelector:
vendor: "15b3"
deviceID: "101b"
netFilter: "openstack/NetworkID:ea24bd04-8674-4f69-b0ee-fa0b3bd20509" 13.4.1.2. SR-IOV デバイスの Virtual Function (VF) パーティション設定
Virtual Function (VF) を同じ物理機能 (PF) から複数のリソースプールに分割する必要がある場合があります。たとえば、VF の一部をデフォルトドライバーで読み込み、残りの VF を vfio-pci ドライバーで読み込む必要がある場合などです。このようなデプロイメントでは、SriovNetworkNodePolicy カスタムリソース (CR) の pfNames セレクターは、以下の形式を使用してプールの VF の範囲を指定するために使用できます: <pfname>#<first_vf>-<last_vf>
たとえば、以下の YAML は、VF が 2 から 7 まである netpf0 という名前のインターフェイスのセレクターを示します。
pfNames: ["netpf0#2-7"]-
netpf0は PF インターフェイス名です。 -
2は、範囲に含まれる最初の VF インデックス (0 ベース) です。 -
7は、範囲に含まれる最後の VF インデックス (0 ベース) です。
以下の要件を満たす場合、異なるポリシー CR を使用して同じ PF から VF を選択できます。
-
numVfsの値は、同じ PF を選択するポリシーで同一である必要があります。 -
VF インデックスは、
0から<numVfs>-1の範囲にある必要があります。たとえば、numVfsが8に設定されているポリシーがある場合、<first_vf>の値は0よりも小さくすることはできず、<last_vf>は7よりも大きくすることはできません。 - 異なるポリシーの VF の範囲は重複しないようにしてください。
-
<first_vf>は<last_vf>よりも大きくすることはできません。
以下の例は、SR-IOV デバイスの NIC パーティション設定を示しています。
ポリシー policy-net-1 は、デフォルトの VF ドライバーと共に PF netpf0 の VF 0 が含まれるリソースプール net-1 を定義します。ポリシー policy-net-1-dpdk は、vfio VF ドライバーと共に PF netpf0 の VF 8 から 15 までが含まれるリソースプール net-1-dpdk を定義します。
ポリシー policy-net-1:
apiVersion: sriovnetwork.openshift.io/v1
kind: SriovNetworkNodePolicy
metadata:
name: policy-net-1
namespace: openshift-sriov-network-operator
spec:
resourceName: net1
nodeSelector:
feature.node.kubernetes.io/network-sriov.capable: "true"
numVfs: 16
nicSelector:
pfNames: ["netpf0#0-0"]
deviceType: netdevice
ポリシー policy-net-1-dpdk:
apiVersion: sriovnetwork.openshift.io/v1
kind: SriovNetworkNodePolicy
metadata:
name: policy-net-1-dpdk
namespace: openshift-sriov-network-operator
spec:
resourceName: net1dpdk
nodeSelector:
feature.node.kubernetes.io/network-sriov.capable: "true"
numVfs: 16
nicSelector:
pfNames: ["netpf0#8-15"]
deviceType: vfio-pci13.4.2. SR-IOV ネットワークデバイスの設定
SR-IOV Network Operator は SriovNetworkNodePolicy.sriovnetwork.openshift.io CustomResourceDefinition を OpenShift Container Platform に追加します。SR-IOV ネットワークデバイスは、SriovNetworkNodePolicy カスタムリソース (CR) を作成して設定できます。
SriovNetworkNodePolicy オブジェクトで指定された設定を適用する際に、SR-IOV Operator はノードをドレイン (解放) する可能性があり、場合によってはノードの再起動を行う場合があります。
設定の変更が適用されるまでに数分かかる場合があります。
前提条件
-
OpenShift CLI (
oc) がインストールされている。 -
cluster-adminロールを持つユーザーとしてクラスターにアクセスできる。 - SR-IOV Network Operator がインストールされている。
- ドレイン (解放) されたノードからエビクトされたワークロードを処理するために、クラスター内に利用可能な十分なノードがあること。
- SR-IOV ネットワークデバイス設定についてコントロールプレーンノードを選択していないこと。
手順
-
SriovNetworkNodePolicyオブジェクトを作成してから、YAML を<name>-sriov-node-network.yamlファイルに保存します。<name>をこの設定の名前に置き換えます。 -
オプション: SR-IOV 対応のクラスターノードにまだラベルが付いていない場合は、
SriovNetworkNodePolicy.Spec.NodeSelectorでラベルを付けます。ノードのラベル付けについて、詳しくはノードのラベルを更新する方法についてを参照してください。
SriovNetworkNodePolicyオブジェクトを作成します。$ oc create -f <name>-sriov-node-network.yamlここで、
<name>はこの設定の名前を指定します。設定の更新が適用された後に、
sriov-network-operatornamespace のすべての Pod がRunningステータスに移行します。SR-IOV ネットワークデバイスが設定されていることを確認するには、以下のコマンドを実行します。
<node_name>を、設定したばかりの SR-IOV ネットワークデバイスを持つノードの名前に置き換えます。$ oc get sriovnetworknodestates -n openshift-sriov-network-operator <node_name> -o jsonpath='{.status.syncStatus}'
13.4.3. SR-IOV 設定のトラブルシューティング
SR-IOV ネットワークデバイスの設定の手順を実行した後に、以下のセクションではエラー状態の一部に対応します。
ノードの状態を表示するには、以下のコマンドを実行します。
$ oc get sriovnetworknodestates -n openshift-sriov-network-operator <node_name>
ここで、<node_name> は SR-IOV ネットワークデバイスを持つノードの名前を指定します。
エラー出力: Cannot allocate memory
"lastSyncError": "write /sys/bus/pci/devices/0000:3b:00.1/sriov_numvfs: cannot allocate memory"ノードがメモリーを割り当てることができないことを示す場合は、以下の項目を確認します。
- ノードの BIOS でグローバル SR-IOV 設定が有効になっていることを確認します。
- ノードの BIOS で VT-d が有効であることを確認します。
13.4.4. SR-IOV ネットワークの VRF への割り当て
CNI VRF プラグインはテクノロジープレビュー機能としてのみご利用いただけます。テクノロジープレビュー機能は Red Hat の実稼働環境でのサービスレベルアグリーメント (SLA) ではサポートされていないため、Red Hat では実稼働環境での使用を推奨していません。Red Hat は実稼働環境でこれらを使用することを推奨していません。テクノロジープレビューの機能は、最新の製品機能をいち早く提供して、開発段階で機能のテストを行いフィードバックを提供していただくことを目的としています。
Red Hat のテクノロジープレビュー機能のサポート範囲に関する詳細は、テクノロジープレビュー機能のサポート範囲 を参照してください。
クラスター管理者は、CNI VRF プラグインを使用して、SR-IOV ネットワークインターフェイスを VRF ドメインに割り当てることができます。
これを実行するには、VRF 設定を SriovNetwork リソースのオプションの metaPlugins パラメーターに追加します。
VRF を使用するアプリケーションを特定のデバイスにバインドする必要があります。一般的な使用方法として、ソケットに SO_BINDTODEVICE オプションを使用できます。SO_BINDTODEVICE は、渡されるインターフェイス名で指定されているデバイスにソケットをバインドします (例: eth1)。SO_BINDTODEVICE を使用するには、アプリケーションに CAP_NET_RAW 機能がある必要があります。
13.4.4.1. CNI VRF プラグインを使用した追加 SR-IOV ネットワーク割り当ての作成
SR-IOV Network Operator は追加ネットワークの定義を管理します。作成する追加ネットワークを指定する場合、SR-IOV Network Operator は NetworkAttachmentDefinition カスタムリソース (CR) を自動的に作成します。
SR-IOV Network Operator が管理する NetworkAttachmentDefinition カスタムリソースは編集しないでください。これを実行すると、追加ネットワークのネットワークトラフィックが中断する可能性があります。
CNI VRF プラグインで追加の SR-IOV ネットワーク割り当てを作成するには、以下の手順を実行します。
前提条件
- OpenShift Container Platform CLI (oc) をインストールします。
- cluster-admin 権限を持つユーザーとして OpenShift Container Platform クラスターにログインします。
手順
追加の SR-IOV ネットワーク割り当て用の
SriovNetworkカスタムリソース (CR) を作成し、以下のサンプル CR のようにmetaPlugins設定を挿入します。YAML をsriov-network-attachment.yamlファイルとして保存します。apiVersion: sriovnetwork.openshift.io/v1 kind: SriovNetwork metadata: name: example-network namespace: additional-sriov-network-1 spec: ipam: | { "type": "host-local", "subnet": "10.56.217.0/24", "rangeStart": "10.56.217.171", "rangeEnd": "10.56.217.181", "routes": [{ "dst": "0.0.0.0/0" }], "gateway": "10.56.217.1" } vlan: 0 resourceName: intelnics metaPlugins : | { "type": "vrf",1 "vrfname": "example-vrf-name"2 }SriovNetworkリソースを作成します。$ oc create -f sriov-network-attachment.yaml
NetworkAttachmentDefinition CR が正常に作成されることの確認
以下のコマンドを実行して、SR-IOV Network Operator が
NetworkAttachmentDefinitionCR を作成していることを確認します。$ oc get network-attachment-definitions -n <namespace>1 - 1
<namespace>を、ネットワーク割り当ての設定時に指定した namespace に置き換えます (例:additional-sriov-network-1)。
出力例
NAME AGE additional-sriov-network-1 14m注記SR-IOV Network Operator が CR を作成するまでに遅延が生じる可能性があります。
追加の SR-IOV ネットワーク割り当てが正常であることの確認
VRF CNI が正しく設定され、追加の SR-IOV ネットワーク割り当てが接続されていることを確認するには、以下を実行します。
- VRF CNI を使用する SR-IOV ネットワークを作成します。
- ネットワークを Pod に割り当てます。
Pod のネットワーク割り当てが SR-IOV の追加ネットワークに接続されていることを確認します。Pod にリモートシェルを実行し、以下のコマンドを実行します。
$ ip vrf show出力例
Name Table ----------------------- red 10VRF インターフェイスがセカンダリーインターフェイスのマスターであることを確認します。
$ ip link出力例
... 5: net1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master red state UP mode ...
13.4.5. 次のステップ
13.5. SR-IOV イーサネットネットワーク割り当ての設定
クラスター内の Single Root I/O Virtualization (SR-IOV) デバイスのイーサネットネットワーク割り当てを設定できます。
13.5.1. イーサネットデバイス設定オブジェクト
イーサネットネットワークデバイスは、SriovNetwork オブジェクトを定義して設定できます。
以下の YAML は SriovNetwork オブジェクトについて説明しています。
apiVersion: sriovnetwork.openshift.io/v1
kind: SriovNetwork
metadata:
name: <name>
namespace: openshift-sriov-network-operator
spec:
resourceName: <sriov_resource_name>
networkNamespace: <target_namespace>
vlan: <vlan>
spoofChk: "<spoof_check>"
ipam: |-
{}
linkState: <link_state>
maxTxRate: <max_tx_rate>
minTxRate: <min_tx_rate>
vlanQoS: <vlan_qos>
trust: "<trust_vf>"
capabilities: <capabilities> - 1
- オブジェクトの名前。SR-IOV Network Operator は、同じ名前を持つ
NetworkAttachmentDefinitionオブジェクトを作成します。 - 2
- SR-IOV Network Operator がインストールされている namespace を指定します。
- 3
- この追加ネットワークの SR-IOV ハードウェアを定義する
SriovNetworkNodePolicyオブジェクトのspec.resourceNameパラメーターの値。 - 4
SriovNetworkオブジェクトのターゲット namespace。ターゲット namespace の Pod のみを追加ネットワークに割り当てることができます。- 5
- オプション: 追加ネットワークの仮想 LAN (VLAN) ID。整数値は
0から4095である必要があります。デフォルト値は0です。 - 6
- オプション: VF の spoof チェックモード。許可される値は、文字列の
"on"および"off"です。重要指定する値を引用符で囲む必要があります。そうしないと、オブジェクトは SR-IOV ネットワーク Operator によって拒否されます。
- 7
- YAML ブロックスケーラーとしての IPAM CNI プラグインの設定オブジェクトプラグインは、割り当て定義についての IP アドレスの割り当てを管理します。
- 8
- オプション: Virtual Function (VF) のリンク状態。許可される値は、
enable、disable、およびautoです。 - 9
- オプション: VF の最大伝送レート (Mbps)。
- 10
- オプション: VF の最小伝送レート (Mbps)。この値は、最大伝送レート以下である必要があります。注記
Intel NIC は
minTxRateパラメーターをサポートしません。詳細は、BZ#1772847 を参照してください。 - 11
- オプション: VF の IEEE 802.1p 優先度レベル。デフォルト値は
0です。 - 12
- オプション: VF の信頼モード。許可される値は、文字列の
"on"および"off"です。重要指定する値を引用符で囲む必要があります。囲まないと、SR-IOV Network Operator はオブジェクトを拒否します。
- 13
- オプション: この追加ネットワークに設定する機能。IP アドレスのサポートを有効にするには、
"{ "ips": true }"を指定できます。または、MAC アドレスのサポートを有効にするには"{ "mac": true }"を指定します。
13.5.1.1. 追加ネットワークの IP アドレス割り当ての設定
IPAM (IP アドレス管理) Container Network Interface (CNI) プラグインは、他の CNI プラグインの IP アドレスを提供します。
以下の IP アドレスの割り当てタイプを使用できます。
- 静的割り当て。
- DHCP サーバーを使用した動的割り当て。指定する DHCP サーバーは、追加のネットワークから到達可能である必要があります。
- Whereabouts IPAM CNI プラグインを使用した動的割り当て。
13.5.1.1.1. 静的 IP アドレス割り当ての設定
以下の表は、静的 IP アドレスの割り当ての設定について説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
IPAM のアドレスタイプ。値 |
|
|
| 仮想インターフェイスに割り当てる IP アドレスを指定するオブジェクトの配列。IPv4 と IPv6 の IP アドレスの両方がサポートされます。 |
|
|
| Pod 内で設定するルートを指定するオブジェクトの配列です。 |
|
|
| オプション: DNS の設定を指定するオブジェクトの配列です。 |
addressesの配列には、以下のフィールドのあるオブジェクトが必要です。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
指定する IP アドレスおよびネットワーク接頭辞。たとえば、 |
|
|
| egress ネットワークトラフィックをルーティングするデフォルトのゲートウェイ。 |
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
CIDR 形式の IP アドレス範囲 ( |
|
|
| ネットワークトラフィックがルーティングされるゲートウェイ。 |
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
| DNS クエリーの送信先となる 1 つ以上の IP アドレスの配列。 |
|
|
|
ホスト名に追加するデフォルトのドメイン。たとえば、ドメインが |
|
|
|
DNS ルックアップのクエリー時に非修飾ホスト名に追加されるドメイン名の配列 (例: |
静的 IP アドレス割り当ての設定例
{
"ipam": {
"type": "static",
"addresses": [
{
"address": "191.168.1.7/24"
}
]
}
}13.5.1.1.2. 動的 IP アドレス (DHCP) 割り当ての設定
以下の JSON は、DHCP を使用した動的 IP アドレスの割り当ての設定について説明しています。
Pod は、作成時に元の DHCP リースを取得します。リースは、クラスターで実行している最小限の DHCP サーバーデプロイメントで定期的に更新する必要があります。
SR-IOV ネットワーク Operator は DHCP サーバーデプロイメントを作成しません。Cluster Network Operator は最小限の DHCP サーバーデプロイメントを作成します。
DHCP サーバーのデプロイメントをトリガーするには、以下の例にあるように Cluster Network Operator 設定を編集して shim ネットワーク割り当てを作成する必要があります。
shim ネットワーク割り当ての定義例
apiVersion: operator.openshift.io/v1
kind: Network
metadata:
name: cluster
spec:
additionalNetworks:
- name: dhcp-shim
namespace: default
type: Raw
rawCNIConfig: |-
{
"name": "dhcp-shim",
"cniVersion": "0.3.1",
"type": "bridge",
"ipam": {
"type": "dhcp"
}
}
# ...| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
IPAM のアドレスタイプ。値 |
動的 IP アドレス (DHCP) 割り当ての設定例
{
"ipam": {
"type": "dhcp"
}
}13.5.1.1.3. Whereabouts を使用した動的 IP アドレス割り当ての設定
Whereabouts CNI プラグインにより、DHCP サーバーを使用せずに IP アドレスを追加のネットワークに動的に割り当てることができます。
以下の表は、Whereabouts を使用した動的 IP アドレス割り当ての設定について説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
IPAM のアドレスタイプ。値 |
|
|
| IP アドレスと範囲を CIDR 表記。IP アドレスは、この範囲内のアドレスから割り当てられます。 |
|
|
| オプション: CIDR 表記の IP アドレスと範囲 (0 個以上) の一覧。除外されたアドレス範囲内の IP アドレスは割り当てられません。 |
Whereabouts を使用する動的 IP アドレス割り当ての設定例
{
"ipam": {
"type": "whereabouts",
"range": "192.0.2.192/27",
"exclude": [
"192.0.2.192/30",
"192.0.2.196/32"
]
}
}13.5.2. SR-IOV の追加ネットワークの設定
SriovNetwork オブジェクト を作成して、SR-IOV ハードウェアを使用する追加のネットワークを設定できます。SriovNetwork オブジェクトの作成時に、SR-IOV Operator は NetworkAttachmentDefinition オブジェクトを自動的に作成します。
SriovNetwork オブジェクトが running 状態の Pod に割り当てられている場合、これを変更したり、削除したりしないでください。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
SriovNetworkオブジェクトを作成してから、YAML を<name>.yamlファイルに保存します。<name>はこの追加ネットワークの名前になります。オブジェクト仕様は以下の例のようになります。apiVersion: sriovnetwork.openshift.io/v1 kind: SriovNetwork metadata: name: attach1 namespace: openshift-sriov-network-operator spec: resourceName: net1 networkNamespace: project2 ipam: |- { "type": "host-local", "subnet": "10.56.217.0/24", "rangeStart": "10.56.217.171", "rangeEnd": "10.56.217.181", "gateway": "10.56.217.1" }オブジェクトを作成するには、以下のコマンドを入力します。
$ oc create -f <name>.yamlここで、
<name>は追加ネットワークの名前を指定します。オプション: 以下のコマンドを実行して、直前の手順で作成した
SriovNetworkオブジェクトに関連付けられたNetworkAttachmentDefinitionオブジェクトが存在することを確認するには、以下のコマンドを入力します。<namespace>をSriovNetworkオブジェクトで指定した networkNamespace に置き換えます。$ oc get net-attach-def -n <namespace>
13.5.3. 次のステップ
13.6. SR-IOV InfiniBand ネットワーク割り当ての設定
クラスター内の Single Root I/O Virtualization (SR-IOV) デバイスの InfiniBand (IB) ネットワーク割り当てを設定できます。
13.6.1. InfiniBand デバイス設定オブジェクト
SriovIBNetwork オブジェクトを定義することで、InfiniBand (IB) ネットワークデバイスを設定できます。
以下の YAML は、SriovIBNetwork オブジェクトについて説明しています。
apiVersion: sriovnetwork.openshift.io/v1
kind: SriovIBNetwork
metadata:
name: <name>
namespace: openshift-sriov-network-operator
spec:
resourceName: <sriov_resource_name>
networkNamespace: <target_namespace>
ipam: |-
{}
linkState: <link_state>
capabilities: <capabilities> - 1
- オブジェクトの名前。SR-IOV Network Operator は、同じ名前を持つ
NetworkAttachmentDefinitionオブジェクトを作成します。 - 2
- SR-IOV Operator がインストールされている namespace。
- 3
- この追加ネットワークの SR-IOV ハードウェアを定義する
SriovNetworkNodePolicyオブジェクトのspec.resourceNameパラメーターの値。 - 4
SriovIBNetworkオブジェクトのターゲット namespace。ターゲット namespace の Pod のみをネットワークデバイスに割り当てることができます。- 5
- オプション: YAML ブロックスケーラーとしての IPAM CNI プラグインの設定オブジェクト。プラグインは、割り当て定義についての IP アドレスの割り当てを管理します。
- 6
- オプション: Virtual Function (VF) のリンク状態。許可される値は、
enable、disable、およびautoです。 - 7
- オプション: このネットワークに設定する機能。
"{ "ips": true }"を指定して IP アドレスのサポートを有効にするか、"{ "infinibandGUID": true }"を指定して IB Global Unique Identifier (GUID) サポートを有効にします。
13.6.1.1. 追加ネットワークの IP アドレス割り当ての設定
IPAM (IP アドレス管理) Container Network Interface (CNI) プラグインは、他の CNI プラグインの IP アドレスを提供します。
以下の IP アドレスの割り当てタイプを使用できます。
- 静的割り当て。
- DHCP サーバーを使用した動的割り当て。指定する DHCP サーバーは、追加のネットワークから到達可能である必要があります。
- Whereabouts IPAM CNI プラグインを使用した動的割り当て。
13.6.1.1.1. 静的 IP アドレス割り当ての設定
以下の表は、静的 IP アドレスの割り当ての設定について説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
IPAM のアドレスタイプ。値 |
|
|
| 仮想インターフェイスに割り当てる IP アドレスを指定するオブジェクトの配列。IPv4 と IPv6 の IP アドレスの両方がサポートされます。 |
|
|
| Pod 内で設定するルートを指定するオブジェクトの配列です。 |
|
|
| オプション: DNS の設定を指定するオブジェクトの配列です。 |
addressesの配列には、以下のフィールドのあるオブジェクトが必要です。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
指定する IP アドレスおよびネットワーク接頭辞。たとえば、 |
|
|
| egress ネットワークトラフィックをルーティングするデフォルトのゲートウェイ。 |
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
CIDR 形式の IP アドレス範囲 ( |
|
|
| ネットワークトラフィックがルーティングされるゲートウェイ。 |
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
| DNS クエリーの送信先となる 1 つ以上の IP アドレスの配列。 |
|
|
|
ホスト名に追加するデフォルトのドメイン。たとえば、ドメインが |
|
|
|
DNS ルックアップのクエリー時に非修飾ホスト名に追加されるドメイン名の配列 (例: |
静的 IP アドレス割り当ての設定例
{
"ipam": {
"type": "static",
"addresses": [
{
"address": "191.168.1.7/24"
}
]
}
}13.6.1.1.2. 動的 IP アドレス (DHCP) 割り当ての設定
以下の JSON は、DHCP を使用した動的 IP アドレスの割り当ての設定について説明しています。
Pod は、作成時に元の DHCP リースを取得します。リースは、クラスターで実行している最小限の DHCP サーバーデプロイメントで定期的に更新する必要があります。
DHCP サーバーのデプロイメントをトリガーするには、以下の例にあるように Cluster Network Operator 設定を編集して shim ネットワーク割り当てを作成する必要があります。
shim ネットワーク割り当ての定義例
apiVersion: operator.openshift.io/v1
kind: Network
metadata:
name: cluster
spec:
additionalNetworks:
- name: dhcp-shim
namespace: default
type: Raw
rawCNIConfig: |-
{
"name": "dhcp-shim",
"cniVersion": "0.3.1",
"type": "bridge",
"ipam": {
"type": "dhcp"
}
}
# ...| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
IPAM のアドレスタイプ。値 |
動的 IP アドレス (DHCP) 割り当ての設定例
{
"ipam": {
"type": "dhcp"
}
}13.6.1.1.3. Whereabouts を使用した動的 IP アドレス割り当ての設定
Whereabouts CNI プラグインにより、DHCP サーバーを使用せずに IP アドレスを追加のネットワークに動的に割り当てることができます。
以下の表は、Whereabouts を使用した動的 IP アドレス割り当ての設定について説明しています。
| フィールド | タイプ | 説明 |
|---|---|---|
|
|
|
IPAM のアドレスタイプ。値 |
|
|
| IP アドレスと範囲を CIDR 表記。IP アドレスは、この範囲内のアドレスから割り当てられます。 |
|
|
| オプション: CIDR 表記の IP アドレスと範囲 (0 個以上) の一覧。除外されたアドレス範囲内の IP アドレスは割り当てられません。 |
Whereabouts を使用する動的 IP アドレス割り当ての設定例
{
"ipam": {
"type": "whereabouts",
"range": "192.0.2.192/27",
"exclude": [
"192.0.2.192/30",
"192.0.2.196/32"
]
}
}13.6.2. SR-IOV の追加ネットワークの設定
SriovIBNetwork オブジェクトを作成して、SR-IOV ハードウェアを使用する追加のネットワークを設定できます。SriovIBNetwork オブジェクトの作成時に、SR-IOV Operator は NetworkAttachmentDefinition オブジェクトを自動的に作成します。
SriovIBNetwork オブジェクトが、running 状態の Pod に割り当てられている場合、これを変更したり、削除したりしないでください。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
SriovIBNetworkCR を作成してから、YAML を<name>.yamlファイルに保存します。<name>は、この追加ネットワークの名前になります。オブジェクト仕様は以下の例のようになります。apiVersion: sriovnetwork.openshift.io/v1 kind: SriovIBNetwork metadata: name: attach1 namespace: openshift-sriov-network-operator spec: resourceName: net1 networkNamespace: project2 ipam: |- { "type": "host-local", "subnet": "10.56.217.0/24", "rangeStart": "10.56.217.171", "rangeEnd": "10.56.217.181", "gateway": "10.56.217.1" }オブジェクトを作成するには、以下のコマンドを入力します。
$ oc create -f <name>.yamlここで、
<name>は追加ネットワークの名前を指定します。オプション: 以下のコマンドを実行して、直前の手順で作成した
SriovIBNetworkオブジェクトに関連付けられたNetworkAttachmentDefinitionオブジェクトが存在することを確認します。<namespace>をSriovIBNetworkオブジェクトで指定した networkNamespace に置き換えます。$ oc get net-attach-def -n <namespace>
13.6.3. 次のステップ
13.7. Pod の SR-IOV の追加ネットワークへの追加
Pod を既存の Single Root I/O Virtualization (SR-IOV) ネットワークに追加できます。
13.7.1. ネットワーク割り当てのランタイム設定
Pod を追加のネットワークに割り当てる場合、ランタイム設定を指定して Pod の特定のカスタマイズを行うことができます。たとえば、特定の MAC ハードウェアアドレスを要求できます。
Pod 仕様にアノテーションを設定して、ランタイム設定を指定します。アノテーションキーは k8s.v1.cni.cncf.io/networks で、ランタイム設定を記述する JSON オブジェクトを受け入れます。
13.7.1.1. イーサネットベースの SR-IOV 割り当てのランタイム設定
以下の JSON は、イーサネットベースの SR-IOV ネットワーク割り当て用のランタイム設定オプションを説明しています。
[
{
"name": "<name>",
"mac": "<mac_address>",
"ips": ["<cidr_range>"]
}
]- 1
- SR-IOV ネットワーク割り当て定義 CR の名前。
- 2
- オプション: SR-IOV ネットワーク割り当て定義 CR で定義されるリソースタイプから割り当てられる SR-IOV デバイスの MAC アドレス。この機能を使用するには、
SriovNetworkオブジェクトで{ "mac": true }も指定する必要があります。 - 3
- オプション: SR-IOV ネットワーク割り当て定義 CR で定義されるリソースタイプから割り当てられる SR-IOV デバイスの IP アドレス。IPv4 と IPv6 アドレスの両方がサポートされます。この機能を使用するには、
SriovNetworkオブジェクトで{ "ips": true }も指定する必要があります。
ランタイム設定の例
apiVersion: v1
kind: Pod
metadata:
name: sample-pod
annotations:
k8s.v1.cni.cncf.io/networks: |-
[
{
"name": "net1",
"mac": "20:04:0f:f1:88:01",
"ips": ["192.168.10.1/24", "2001::1/64"]
}
]
spec:
containers:
- name: sample-container
image: <image>
imagePullPolicy: IfNotPresent
command: ["sleep", "infinity"]13.7.1.2. InfiniBand ベースの SR-IOV 割り当てのランタイム設定
以下の JSON は、InfiniBand ベースの SR-IOV ネットワーク割り当て用のランタイム設定オプションを説明しています。
[
{
"name": "<network_attachment>",
"infiniband-guid": "<guid>",
"ips": ["<cidr_range>"]
}
]ランタイム設定の例
apiVersion: v1
kind: Pod
metadata:
name: sample-pod
annotations:
k8s.v1.cni.cncf.io/networks: |-
[
{
"name": "ib1",
"infiniband-guid": "c2:11:22:33:44:55:66:77",
"ips": ["192.168.10.1/24", "2001::1/64"]
}
]
spec:
containers:
- name: sample-container
image: <image>
imagePullPolicy: IfNotPresent
command: ["sleep", "infinity"]13.7.2. Pod の追加ネットワークへの追加
Pod を追加のネットワークに追加できます。Pod は、デフォルトネットワークで通常のクラスター関連のネットワークトラフィックを継続的に送信します。
Pod が作成されると、追加のネットワークが割り当てられます。ただし、Pod がすでに存在する場合は、追加のネットワークをこれに割り当てることはできません。
Pod が追加ネットワークと同じ namespace にあること。
SR-IOV Network Resource Injector は、Pod の最初のコンテナーに resource フィールドを自動的に追加します。
データプレーン開発キット (DPDK) モードでインテル製のネットワークインターフェイスコントローラー (NIC) を使用している場合には、Pod 内の最初のコンテナーのみが NIC にアクセスできるように設定されています。SR-IOV 追加ネットワークは、Sriov Network Node Policy オブジェクトで device Type が vfio-pci に設定されてる場合は DPDK モードに設定されます。
この問題は、NIC にアクセスする必要のあるコンテナーが Pod オブジェクトで定義された最初のコンテナーであることを確認するか、Network Resource Injector を無効にすることで回避できます。詳細は、BZ#1990953 を参照してください。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 - クラスターにログインする。
- SR-IOV Operator のインストール。
-
Pod を割り当てる
SriovNetworkオブジェクトまたはSriovIBNetworkオブジェクトのいずれかを作成する。
手順
アノテーションを
Podオブジェクトに追加します。以下のアノテーション形式のいずれかのみを使用できます。カスタマイズせずに追加ネットワークを割り当てるには、以下の形式でアノテーションを追加します。
<network>を、Pod に関連付ける追加ネットワークの名前に置き換えます。metadata: annotations: k8s.v1.cni.cncf.io/networks: <network>[,<network>,...]1 - 1
- 複数の追加ネットワークを指定するには、各ネットワークをコンマで区切ります。コンマの間にはスペースを入れないでください。同じ追加ネットワークを複数回指定した場合、Pod は複数のネットワークインターフェイスをそのネットワークに割り当てます。
カスタマイズして追加のネットワークを割り当てるには、以下の形式でアノテーションを追加します。
metadata: annotations: k8s.v1.cni.cncf.io/networks: |- [ { "name": "<network>",1 "namespace": "<namespace>",2 "default-route": ["<default-route>"]3 } ]
Pod を作成するには、以下のコマンドを入力します。
<name>を Pod の名前に置き換えます。$ oc create -f <name>.yamlオプション: アノテーションが
PodCR に存在することを確認するには、<name>を Pod の名前に置き換えて、以下のコマンドを入力します。$ oc get pod <name> -o yaml以下の例では、
example-podPod が追加ネットワークのnet1に割り当てられています。$ oc get pod example-pod -o yaml apiVersion: v1 kind: Pod metadata: annotations: k8s.v1.cni.cncf.io/networks: macvlan-bridge k8s.v1.cni.cncf.io/networks-status: |-1 [{ "name": "openshift-sdn", "interface": "eth0", "ips": [ "10.128.2.14" ], "default": true, "dns": {} },{ "name": "macvlan-bridge", "interface": "net1", "ips": [ "20.2.2.100" ], "mac": "22:2f:60:a5:f8:00", "dns": {} }] name: example-pod namespace: default spec: ... status: ...- 1
k8s.v1.cni.cncf.io/networks-statusパラメーターは、オブジェクトの JSON 配列です。各オブジェクトは、Pod に割り当てられる追加のネットワークのステータスについて説明します。アノテーションの値はプレーンテキストの値として保存されます。
13.7.3. Non-Uniform Memory Access (NUMA) で配置された SR-IOV Pod の作成
NUMA で配置された SR-IOV Pod は、restricted または single-numa-node Topology Manager ポリシーで同じ NUMA ノードから割り当てられる SR-IOV および CPU リソースを制限することによって作成できます。
前提条件
-
OpenShift CLI (
oc) がインストールされている。 -
CPU マネージャーのポリシーを
staticに設定している。CPU マネージャーの詳細は、関連情報セクションを参照してください。 Topology Manager ポリシーを
single-numa-nodeに設定している。注記single-numa-nodeが要求を満たさない場合は、Topology Manager ポリシーをrestrictedにするように設定できます 。
手順
以下の SR-IOV Pod 仕様を作成してから、YAML を
<name>-sriov-pod.yamlファイルに保存します。<name>をこの Pod の名前に置き換えます。以下の例は、SR-IOV Pod 仕様を示しています。
apiVersion: v1 kind: Pod metadata: name: sample-pod annotations: k8s.v1.cni.cncf.io/networks: <name>1 spec: containers: - name: sample-container image: <image>2 command: ["sleep", "infinity"] resources: limits: memory: "1Gi"3 cpu: "2"4 requests: memory: "1Gi" cpu: "2"以下のコマンドを実行して SR-IOV Pod のサンプルを作成します。
$ oc create -f <filename>1 - 1
<filename>を、先の手順で作成したファイルの名前に置き換えます。
sample-podが Guaranteed QoS を指定して設定されていることを確認します。$ oc describe pod sample-podsample-podが排他的 CPU を指定して割り当てられていることを確認します。$ oc exec sample-pod -- cat /sys/fs/cgroup/cpuset/cpuset.cpussample-podに割り当てられる SR-IOV デバイスと CPU が同じ NUMA ノード上にあることを確認します。$ oc exec sample-pod -- cat /sys/fs/cgroup/cpuset/cpuset.cpus
13.8. 高パフォーマンスのマルチキャストの使用
Single Root I/O Virtualization (SR-IOV) ハードウェアネットワーク上でマルチキャストを使用できます。
13.8.1. 高パフォーマンスのマルチキャスト
OpenShift SDN デフォルト Container Network Interface (CNI) ネットワークプロバイダーは、デフォルトネットワーク上の Pod 間のマルチキャストをサポートします。これは低帯域幅の調整またはサービスの検出での使用に最も適しており、高帯域幅のアプリケーションには適していません。インターネットプロトコルテレビ (IPTV) やマルチポイントビデオ会議など、ストリーミングメディアなどのアプリケーションでは、Single Root I/O Virtualization (SR-IOV) ハードウェアを使用してネイティブに近いパフォーマンスを提供できます。
マルチキャストに追加の SR-IOV インターフェイスを使用する場合:
- マルチキャストパッケージは、追加の SR-IOV インターフェイス経由で Pod によって送受信される必要があります。
- SR-IOV インターフェイスに接続する物理ネットワークは、OpenShift Container Platform で制御されないマルチキャストルーティングとトポロジーを判別します。
13.8.2. マルチキャストでの SR-IOV インターフェイスの設定
以下の手順では、サンプルのマルチキャスト用の SR-IOV インターフェイスを作成します。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-adminロールを持つユーザーとしてクラスターにログインする必要があります。
手順
SriovNetworkNodePolicyオブジェクトを作成します。apiVersion: sriovnetwork.openshift.io/v1 kind: SriovNetworkNodePolicy metadata: name: policy-example namespace: openshift-sriov-network-operator spec: resourceName: example nodeSelector: feature.node.kubernetes.io/network-sriov.capable: "true" numVfs: 4 nicSelector: vendor: "8086" pfNames: ['ens803f0'] rootDevices: ['0000:86:00.0']SriovNetworkオブジェクトを作成します。apiVersion: sriovnetwork.openshift.io/v1 kind: SriovNetwork metadata: name: net-example namespace: openshift-sriov-network-operator spec: networkNamespace: default ipam: |1 { "type": "host-local",2 "subnet": "10.56.217.0/24", "rangeStart": "10.56.217.171", "rangeEnd": "10.56.217.181", "routes": [ {"dst": "224.0.0.0/5"}, {"dst": "232.0.0.0/5"} ], "gateway": "10.56.217.1" } resourceName: exampleマルチキャストアプリケーションで Pod を作成します。
apiVersion: v1 kind: Pod metadata: name: testpmd namespace: default annotations: k8s.v1.cni.cncf.io/networks: nic1 spec: containers: - name: example image: rhel7:latest securityContext: capabilities: add: ["NET_ADMIN"]1 command: [ "sleep", "infinity"]- 1
NET_ADMIN機能は、アプリケーションがマルチキャスト IP アドレスを SR-IOV インターフェイスに割り当てる必要がある場合にのみ必要です。それ以外の場合は省略できます。
13.9. DPDK および RDMA モードでの仮想機能 (VF) の使用
Single Root I/O Virtualization (SR-IOV) ネットワークハードウェアは、Data Plane Development Kit (DPDK) および Remote Direct Memory Access (RDMA) で利用できます。
Data Plane Development Kit (DPDK) はテクノロジープレビュー機能です。テクノロジープレビュー機能は Red Hat の実稼働環境でのサービスレベルアグリーメント (SLA) ではサポートされていないため、Red Hat では実稼働環境での使用を推奨していません。Red Hat は実稼働環境でこれらを使用することを推奨していません。テクノロジープレビューの機能は、最新の製品機能をいち早く提供して、開発段階で機能のテストを行いフィードバックを提供していただくことを目的としています。
Red Hat のテクノロジープレビュー機能のサポート範囲についての詳細は、https://access.redhat.com/ja/support/offerings/techpreview/ を参照してください。
13.9.1. NIC を使用した DPDK モードでの仮想機能の使用
前提条件
-
OpenShift CLI (
oc) をインストールしている。 - SR-IOV Network Operator をインストールします。
-
cluster-admin権限を持つユーザーとしてログインしている。
手順
以下の
SriovNetworkNodePolicyオブジェクトを作成してから、YAML をintel-dpdk-node-policy.yamlファイルに保存します。apiVersion: sriovnetwork.openshift.io/v1 kind: SriovNetworkNodePolicy metadata: name: intel-dpdk-node-policy namespace: openshift-sriov-network-operator spec: resourceName: intelnics nodeSelector: feature.node.kubernetes.io/network-sriov.capable: "true" priority: <priority> numVfs: <num> nicSelector: vendor: "8086" deviceID: "158b" pfNames: ["<pf_name>", ...] rootDevices: ["<pci_bus_id>", "..."] deviceType: vfio-pci1 - 1
- 仮想機能 (VF) のドライバータイプを
vfio-pciに指定します。
注記SriovNetworkNodePolicyの各オプションに関する詳細は、SR-IOV ネットワークデバイスの設定セクションを参照してください。SriovNetworkNodePolicyオブジェクトで指定された設定を適用する際に、SR-IOV Operator はノードをドレイン (解放) する可能性があり、場合によってはノードの再起動を行う場合があります。設定の変更が適用されるまでに数分の時間がかかる場合があります。エビクトされたワークロードを処理するために、クラスター内に利用可能なノードが十分にあることを前もって確認します。設定の更新が適用された後に、
openshift-sriov-network-operatornamespace のすべての Pod がRunningステータスに変更されます。以下のコマンドを実行して
SriovNetworkNodePolicyオブジェクトを作成します。$ oc create -f intel-dpdk-node-policy.yaml以下の
SriovNetworkオブジェクトを作成してから、YAML をintel-dpdk-network.yamlファイルに保存します。apiVersion: sriovnetwork.openshift.io/v1 kind: SriovNetwork metadata: name: intel-dpdk-network namespace: openshift-sriov-network-operator spec: networkNamespace: <target_namespace> ipam: "{}"1 vlan: <vlan> resourceName: intelnics- 1
- IPAM CNI プラグインの空のオブジェクト
"{}"を指定します。DPDK はユーザー空間モードで機能し、IP アドレスは必要ありません。
注記SriovNetworkの各オプションに関する詳細は、SR-IOV の追加ネットワークの設定セクションを参照してください。以下のコマンドを実行して、
SriovNetworkオブジェクトを作成します。$ oc create -f intel-dpdk-network.yaml以下の
Pod仕様を作成してから、YAML をintel-dpdk-pod.yamlファイルに保存します。apiVersion: v1 kind: Pod metadata: name: dpdk-app namespace: <target_namespace>1 annotations: k8s.v1.cni.cncf.io/networks: intel-dpdk-network spec: containers: - name: testpmd image: <DPDK_image>2 securityContext: runAsUser: 0 capabilities: add: ["IPC_LOCK","SYS_RESOURCE","NET_RAW"]3 volumeMounts: - mountPath: /dev/hugepages4 name: hugepage resources: limits: openshift.io/intelnics: "1"5 memory: "1Gi" cpu: "4"6 hugepages-1Gi: "4Gi"7 requests: openshift.io/intelnics: "1" memory: "1Gi" cpu: "4" hugepages-1Gi: "4Gi" command: ["sleep", "infinity"] volumes: - name: hugepage emptyDir: medium: HugePages- 1
SriovNetworkオブジェクトのintel-dpdk-networkが作成される同じtarget_namespaceを指定します。Pod を異なる namespace に作成する場合、target_namespaceをPod仕様およびSriovNetowrkオブジェクトの両方で変更します。- 2
- アプリケーションとアプリケーションが使用する DPDK ライブラリーが含まれる DPDK イメージを指定します。
- 3
- hugepage の割り当て、システムリソースの割り当て、およびネットワークインターフェイスアクセス用のコンテナー内のアプリケーションに必要な追加機能を指定します。
- 4
- hugepage ボリュームを、
/dev/hugepagesの下にある DPDK Pod にマウントします。hugepage ボリュームは、medium がHugepagesに指定されている emptyDir ボリュームタイプでサポートされます。 - 5
- オプション: DPDK Pod に割り当てられる DPDK デバイスの数を指定します。このリソース要求および制限は、明示的に指定されていない場合、SR-IOV ネットワークリソースインジェクターによって自動的に追加されます。SR-IOV ネットワークリソースインジェクターは、SR-IOV Operator によって管理される受付コントローラーコンポーネントです。これはデフォルトで有効にされており、デフォルト
SriovOperatorConfigCR でenableInjectorオプションをfalseに設定して無効にすることができます。 - 6
- CPU の数を指定します。DPDK Pod には通常、kubelet から排他的 CPU を割り当てる必要があります。これは、CPU マネージャーポリシーを
staticに設定し、GuaranteedQoS を持つ Pod を作成して実行されます。 - 7
- hugepage サイズ
hugepages-1Giまたはhugepages-2Miを指定し、DPDK Pod に割り当てられる hugepage の量を指定します。2Miおよび1Gihugepage を別々に設定します。1Gihugepage を設定するには、カーネル引数をノードに追加する必要があります。たとえば、カーネル引数default_hugepagesz=1GB、hugepagesz=1Gおよびhugepages=16を追加すると、16*1Gihugepage がシステムの起動時に割り当てられます。
以下のコマンドを実行して DPDK Pod を作成します。
$ oc create -f intel-dpdk-pod.yaml
13.9.2. Mellanox NIC を使用した DPDK モードでの Virtual Function の使用
前提条件
-
OpenShift CLI (
oc) をインストールしている。 - SR-IOV Network Operator をインストールします。
-
cluster-admin権限を持つユーザーとしてログインしている。
手順
以下の
SriovNetworkNodePolicyオブジェクトを作成してから、YAML をmlx-dpdk-node-policy.yamlファイルに保存します。apiVersion: sriovnetwork.openshift.io/v1 kind: SriovNetworkNodePolicy metadata: name: mlx-dpdk-node-policy namespace: openshift-sriov-network-operator spec: resourceName: mlxnics nodeSelector: feature.node.kubernetes.io/network-sriov.capable: "true" priority: <priority> numVfs: <num> nicSelector: vendor: "15b3" deviceID: "1015"1 pfNames: ["<pf_name>", ...] rootDevices: ["<pci_bus_id>", "..."] deviceType: netdevice2 isRdma: true3 注記SriovNetworkNodePolicyの各オプションに関する詳細は、SR-IOV ネットワークデバイスの設定セクションを参照してください。SriovNetworkNodePolicyオブジェクトで指定された設定を適用する際に、SR-IOV Operator はノードをドレイン (解放) する可能性があり、場合によってはノードの再起動を行う場合があります。設定の変更が適用されるまでに数分の時間がかかる場合があります。エビクトされたワークロードを処理するために、クラスター内に利用可能なノードが十分にあることを前もって確認します。設定の更新が適用された後に、
openshift-sriov-network-operatornamespace のすべての Pod がRunningステータスに変更されます。以下のコマンドを実行して
SriovNetworkNodePolicyオブジェクトを作成します。$ oc create -f mlx-dpdk-node-policy.yaml以下の
SriovNetworkオブジェクトを作成してから、YAML をmlx-dpdk-network.yamlファイルに保存します。apiVersion: sriovnetwork.openshift.io/v1 kind: SriovNetwork metadata: name: mlx-dpdk-network namespace: openshift-sriov-network-operator spec: networkNamespace: <target_namespace> ipam: |-1 ... vlan: <vlan> resourceName: mlxnics- 1
- IPAM CNI プラグインの設定オブジェクトを YAML ブロックスケーラーとして指定します。プラグインは、割り当て定義についての IP アドレスの割り当てを管理します。
注記SriovNetworkの各オプションに関する詳細は、SR-IOV の追加ネットワークの設定セクションを参照してください。以下のコマンドを実行して
SriovNetworkNodePolicyオブジェクトを作成します。$ oc create -f mlx-dpdk-network.yaml以下の
Pod仕様を作成してから、YAML をmlx-dpdk-pod.yamlファイルに保存します。apiVersion: v1 kind: Pod metadata: name: dpdk-app namespace: <target_namespace>1 annotations: k8s.v1.cni.cncf.io/networks: mlx-dpdk-network spec: containers: - name: testpmd image: <DPDK_image>2 securityContext: runAsUser: 0 capabilities: add: ["IPC_LOCK","SYS_RESOURCE","NET_RAW"]3 volumeMounts: - mountPath: /dev/hugepages4 name: hugepage resources: limits: openshift.io/mlxnics: "1"5 memory: "1Gi" cpu: "4"6 hugepages-1Gi: "4Gi"7 requests: openshift.io/mlxnics: "1" memory: "1Gi" cpu: "4" hugepages-1Gi: "4Gi" command: ["sleep", "infinity"] volumes: - name: hugepage emptyDir: medium: HugePages- 1
SriovNetworkオブジェクトのmlx-dpdk-networkが作成される同じtarget_namespaceを指定します。Pod を異なる namespace に作成する場合、target_namespaceをPod仕様およびSriovNetowrkオブジェクトの両方で変更します。- 2
- アプリケーションとアプリケーションが使用する DPDK ライブラリーが含まれる DPDK イメージを指定します。
- 3
- hugepage の割り当て、システムリソースの割り当て、およびネットワークインターフェイスアクセス用のコンテナー内のアプリケーションに必要な追加機能を指定します。
- 4
- hugepage ボリュームを、
/dev/hugepagesの下にある DPDK Pod にマウントします。hugepage ボリュームは、medium がHugepagesに指定されている emptyDir ボリュームタイプでサポートされます。 - 5
- オプション: DPDK Pod に割り当てられる DPDK デバイスの数を指定します。このリソース要求および制限は、明示的に指定されていない場合、SR-IOV ネットワークリソースインジェクターによって自動的に追加されます。SR-IOV ネットワークリソースインジェクターは、SR-IOV Operator によって管理される受付コントローラーコンポーネントです。これはデフォルトで有効にされており、デフォルト
SriovOperatorConfigCR でenableInjectorオプションをfalseに設定して無効にすることができます。 - 6
- CPU の数を指定します。DPDK Pod には通常、kubelet から排他的 CPU を割り当てる必要があります。これは、CPU マネージャーポリシーを
staticに設定し、GuaranteedQoS を持つ Pod を作成して実行されます。 - 7
- hugepage サイズ
hugepages-1Giまたはhugepages-2Miを指定し、DPDK Pod に割り当てられる hugepage の量を指定します。2Miおよび1Gihugepage を別々に設定します。1Gihugepage を設定するには、カーネル引数をノードに追加する必要があります。
以下のコマンドを実行して DPDK Pod を作成します。
$ oc create -f mlx-dpdk-pod.yaml
13.9.3. Mellanox NIC を使用した RDMA モードでの仮想機能の使用
RoCE (RDMA over Converged Ethernet) は、OpenShift Container Platform で RDMA を使用する場合に唯一サポートされているモードです。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 - SR-IOV Network Operator をインストールします。
-
cluster-admin権限を持つユーザーとしてログインしている。
手順
以下の
SriovNetworkNodePolicyオブジェクトを作成してから、YAML をmlx-rdma-node-policy.yamlファイルに保存します。apiVersion: sriovnetwork.openshift.io/v1 kind: SriovNetworkNodePolicy metadata: name: mlx-rdma-node-policy namespace: openshift-sriov-network-operator spec: resourceName: mlxnics nodeSelector: feature.node.kubernetes.io/network-sriov.capable: "true" priority: <priority> numVfs: <num> nicSelector: vendor: "15b3" deviceID: "1015"1 pfNames: ["<pf_name>", ...] rootDevices: ["<pci_bus_id>", "..."] deviceType: netdevice2 isRdma: true3 注記SriovNetworkNodePolicyの各オプションに関する詳細は、SR-IOV ネットワークデバイスの設定セクションを参照してください。SriovNetworkNodePolicyオブジェクトで指定された設定を適用する際に、SR-IOV Operator はノードをドレイン (解放) する可能性があり、場合によってはノードの再起動を行う場合があります。設定の変更が適用されるまでに数分の時間がかかる場合があります。エビクトされたワークロードを処理するために、クラスター内に利用可能なノードが十分にあることを前もって確認します。設定の更新が適用された後に、
openshift-sriov-network-operatornamespace のすべての Pod がRunningステータスに変更されます。以下のコマンドを実行して
SriovNetworkNodePolicyオブジェクトを作成します。$ oc create -f mlx-rdma-node-policy.yaml以下の
SriovNetworkオブジェクトを作成してから、YAML をmlx-rdma-network.yamlファイルに保存します。apiVersion: sriovnetwork.openshift.io/v1 kind: SriovNetwork metadata: name: mlx-rdma-network namespace: openshift-sriov-network-operator spec: networkNamespace: <target_namespace> ipam: |-1 ... vlan: <vlan> resourceName: mlxnics- 1
- IPAM CNI プラグインの設定オブジェクトを YAML ブロックスケーラーとして指定します。プラグインは、割り当て定義についての IP アドレスの割り当てを管理します。
注記SriovNetworkの各オプションに関する詳細は、SR-IOV の追加ネットワークの設定セクションを参照してください。以下のコマンドを実行して
SriovNetworkNodePolicyオブジェクトを作成します。$ oc create -f mlx-rdma-network.yaml以下の
Pod仕様を作成してから、YAML をmlx-rdma-pod.yamlファイルに保存します。apiVersion: v1 kind: Pod metadata: name: rdma-app namespace: <target_namespace>1 annotations: k8s.v1.cni.cncf.io/networks: mlx-rdma-network spec: containers: - name: testpmd image: <RDMA_image>2 securityContext: runAsUser: 0 capabilities: add: ["IPC_LOCK","SYS_RESOURCE","NET_RAW"]3 volumeMounts: - mountPath: /dev/hugepages4 name: hugepage resources: limits: memory: "1Gi" cpu: "4"5 hugepages-1Gi: "4Gi"6 requests: memory: "1Gi" cpu: "4" hugepages-1Gi: "4Gi" command: ["sleep", "infinity"] volumes: - name: hugepage emptyDir: medium: HugePages- 1
SriovNetworkオブジェクトのmlx-rdma-networkが作成される同じtarget_namespaceを指定します。Pod を異なる namespace に作成する場合、target_namespaceをPod仕様およびSriovNetowrkオブジェクトの両方で変更します。- 2
- アプリケーションとアプリケーションが使用する RDMA ライブラリーが含まれる RDMA イメージを指定します。
- 3
- hugepage の割り当て、システムリソースの割り当て、およびネットワークインターフェイスアクセス用のコンテナー内のアプリケーションに必要な追加機能を指定します。
- 4
- hugepage ボリュームを、
/dev/hugepagesの下にある RDMA Pod にマウントします。hugepage ボリュームは、medium がHugepagesに指定されている emptyDir ボリュームタイプでサポートされます。 - 5
- CPU の数を指定します。RDMA Pod には通常、kubelet から排他的 CPU を割り当てる必要があります。これは、CPU マネージャーポリシーを
staticに設定し、GuaranteedQoS を持つ Pod を作成して実行されます。 - 6
- hugepage サイズ
hugepages-1Giまたはhugepages-2Miを指定し、RDMA Pod に割り当てられる hugepage の量を指定します。2Miおよび1Gihugepage を別々に設定します。1Gihugepage を設定するには、カーネル引数をノードに追加する必要があります。
以下のコマンドを実行して RDMA Pod を作成します。
$ oc create -f mlx-rdma-pod.yaml
13.10. SR-IOV Network Operator のインストール
SR-IOV Network Operator をアンインストールするには、実行中の SR-IOV ワークロードをすべて削除し、Operator をアンインストールして、Operator が使用した Webhook を削除する必要があります。
13.10.1. SR-IOV Network Operator のインストール
クラスター管理者は、SR-IOV Network Operator をアンインストールできます。
前提条件
-
cluster-adminパーミッションを持つアカウントを使用して OpenShift Container Platform クラスターにアクセスできる。 - SR-IOV Network Operator がインストールされている。
手順
すべての SR-IOV カスタムリソース (CR) を削除します。
$ oc delete sriovnetwork -n openshift-sriov-network-operator --all$ oc delete sriovnetworknodepolicy -n openshift-sriov-network-operator --all$ oc delete sriovibnetwork -n openshift-sriov-network-operator --all- クラスターからの Operator の削除セクションに記載された手順に従い、クラスターから SR-IOV Network Operator を削除します。
SR-IOV Network Operator のアンインストール後にクラスターに残っている SR-IOV カスタムリソース定義を削除します。
$ oc delete crd sriovibnetworks.sriovnetwork.openshift.io$ oc delete crd sriovnetworknodepolicies.sriovnetwork.openshift.io$ oc delete crd sriovnetworknodestates.sriovnetwork.openshift.io$ oc delete crd sriovnetworkpoolconfigs.sriovnetwork.openshift.io$ oc delete crd sriovnetworks.sriovnetwork.openshift.io$ oc delete crd sriovoperatorconfigs.sriovnetwork.openshift.ioSR-IOV Webhook を削除します。
$ oc delete mutatingwebhookconfigurations network-resources-injector-config$ oc delete MutatingWebhookConfiguration sriov-operator-webhook-config$ oc delete ValidatingWebhookConfiguration sriov-operator-webhook-configSR-IOV Network Operator の namespace を削除します。
$ oc delete namespace openshift-sriov-network-operator
第14章 OpenShift SDN デフォルト CNI ネットワークプロバイダー
14.1. OpenShift SDN デフォルト CNI ネットワークプロバイダーについて
OpenShift Container Platform は、Software Defined Networking (SDN) アプローチを使用して、クラスターのネットワークを統合し、OpenShift Container Platform クラスターの Pod 間の通信を可能にします。OpenShift SDN により、このような Pod ネットワークが確立され、メンテナンスされます。 OpenShift SDN は Open vSwitch (OVS) を使用してオーバーレイネットワークを設定します。
14.1.1. OpenShift SDN ネットワーク分離モード
OpenShift SDN では以下のように、Pod ネットワークを設定するための SDN モードを 3 つ提供します。
-
ネットワークポリシーモードは、プロジェクト管理者が
NetworkPolicyオブジェクトを使用して独自の分離ポリシーを設定することを可能にします。ネットワークポリシーは、OpenShift Container Platform 4.7 のデフォルトモードです。 - マルチテナント モードは、Pod およびサービスのプロジェクトレベルの分離を可能にします。異なるプロジェクトの Pod は、別のプロジェクトの Pod およびサービスとパケットの送受信をすることができなくなります。プロジェクトの分離を無効にし、クラスター全体のすべての Pod およびサービスにネットワークトラフィックを送信したり、それらの Pod およびサービスからネットワークトラフィックを受信したりすることができます。
- サブネット モードは、すべての Pod が他のすべての Pod およびサービスと通信できる Pod ネットワークを提供します。ネットワークポリシーモードは、サブネットモードと同じ機能を提供します。
14.1.2. サポートされるデフォルトの CNI ネットワークプロバイダー機能マトリクス
OpenShift Container Platform は、OpenShift SDN と OVN-Kubernetes の 2 つのサポート対象のオプションをデフォルトの Container Network Interface (CNI) ネットワークプロバイダーに提供します。以下の表は、両方のネットワークプロバイダーの現在の機能サポートをまとめたものです。
| 機能 | OpenShift SDN | OVN-Kubernetes |
|---|---|---|
| Egress IP | サポート対象 | サポート対象 |
| Egress ファイアウォール [1] | サポート対象 | サポート対象 |
| Egress ルーター | サポート対象 | 一部サポート対象 [3] |
| IPsec 暗号化 | サポート対象外 | サポート対象 |
| Kubernetes ネットワークポリシー | 一部サポート対象 [2] | サポート対象 |
| マルチキャスト | サポート対象 | サポート対象 |
- egress ファイアウォールは、OpenShift SDN では egress ネットワークポリシーとしても知られています。これはネットワークポリシーの egress とは異なります。
-
OpenShift SDN のネットワークポリシーは、egress ルールおよび一部の
ipBlockルールをサポートしません。 - OVN-Kubernetes の egress ルーターはリダイレクトモードのみをサポートします。
14.2. プロジェクトの egress IP の設定
クラスター管理者は、OpenShift SDN デフォルト Container Network Interface (CNI) ネットワークプロバイダーが 1 つ以上の egress IP アドレスをプロジェクトに割り当てるように設定できます。
14.2.1. プロジェクトの egress トラフィックについての egress IP アドレスの割り当て
プロジェクトの egress IP アドレスを設定することにより、指定されたプロジェクトからのすべての外部送信接続が同じ固定ソース IP アドレスを共有します。外部リソースは、egress IP アドレスに基づいて特定のプロジェクトからのトラフィックを認識できます。プロジェクトに割り当てられる egress IP アドレスは、トラフィックを特定の宛先に送信するために使用される egress ルーターとは異なります。
egress IP アドレスは、ノードのプライマリーネットワークインターフェイスの追加 IP アドレスとして実装され、ノードのプライマリー IP アドレスと同じサブネットにある必要があります。
egress IP アドレスは、ifcfg-eth0 などのように Linux ネットワーク設定ファイルで設定することはできません。
Amazon Web Services (AWS)、Google Cloud Platform (GCP)、および Azure の Egress IP は、OpenShift Container Platform バージョン 4.10 以降でのみサポートされます。
一部の仮想マシンソリューションを使用する場合に、プライマリーネットワークインターフェイスで追加の IP アドレスを許可するには追加の設定が必要になる場合があります。
egress IP アドレスは、NetNamespace オブジェクトの egressIPs パラメーターを設定して namespace に割り当てることができます。egress IP がプロジェクトに関連付けられた後に、 OpenShift SDN は 2 つの方法で Egress IP をホストに割り当てることを可能にします。
- 自動的に割り当てる 方法では、egress IP アドレス範囲はノードに割り当てられます。
- 手動で割り当てる 方法では、1 つ以上の egress IP アドレスの一覧がノードに割り当てられます。
egress IP アドレスを要求する namespace は、それらの egress IP アドレスをホストできるノードに一致し、egress IP アドレスはそれらのノードに割り当てられます。egressIPs パラメーターが NetNamespace オブジェクトに設定されるものの、ノードがその egress IP アドレスをホストしない場合、namespace からの egress トラフィックはドロップされます。
ノードの高可用性は自動的に実行されます。egress IP アドレスをホストするノードが到達不可能であり、egress IP アドレスをホストできるノードがある場合、egress IP アドレスは新規ノードに移行します。到達不可能なノードが再びオンラインに戻ると、ノード間で egress IP アドレスのバランスを図るために egress IP アドレスは自動的に移行します。
OpenShift SDN クラスターネットワークプロバイダーで egress IP アドレスを使用する場合、以下の制限が適用されます。
- 手動で割り当てられた egress IP アドレスと、自動的に割り当てられた egress IP アドレスは同じノードで使用することができません。
- IP アドレス範囲から egress IP アドレスを手動で割り当てる場合、その範囲を自動の IP 割り当てで利用可能にすることはできません。
- OpenShift SDN egress IP アドレス実装を使用して、複数の namespace で egress IP アドレスを共有することはできません。複数の namespace 間で IP アドレスを共有する必要がある場合は、OVN-Kubernetes クラスターネットワークプロバイダーの egress IP アドレスの実装により、複数の namespace で IP アドレスを共有できます。
OpenShift SDN をマルチテナントモードで使用する場合、それらに関連付けられたプロジェクトによって別の namespace に参加している namespace と共に egress IP アドレスを使用することはできません。たとえば、project1 および project2 に oc adm pod-network join-projects --to=project1 project2 コマンドを実行して参加している場合、どちらもプロジェクトも egress IP アドレスを使用できません。詳細は、BZ#1645577 を参照してください。
14.2.1.1. 自動的に割り当てられた egress IP アドレスを使用する場合の考慮事項
egress IP アドレスの自動割り当て方法を使用する場合、以下の考慮事項が適用されます。
-
各ノードの
HostSubnetリソースのegressCIDRsパラメーターを設定して、ノードでホストできる egress IP アドレスの範囲を指定します。OpenShift Container Platform は、指定する IP アドレス範囲に基づいてHostSubnetリソースのegressIPsパラメーターを設定します。 - 自動割り当てモードを使用する場合、namespace ごとに単一の egress IP アドレスのみがサポートされます。
namespace の egress IP アドレスをホストするノードに到達できない場合、OpenShift Container Platform は互換性のある egress IP アドレス範囲を持つ別のノードに egress IP アドレスを再割り当てします。自動割り当て方法は、追加の IP アドレスをノードに関連付ける柔軟性のある環境にインストールされたクラスターに最も適しています。
14.2.1.2. 手動で割り当てられた egress IP アドレスを使用する場合の考慮事項
このアプローチは、パブリッククラウド環境など、追加の IP アドレスをノードに関連付ける際に制限がある可能性があるクラスターに使用されます。
egress IP アドレスに手動割り当て方法を使用する場合、以下の考慮事項が適用されます。
-
各ノードの
HostSubnetリソースのegressIPsパラメーターを設定して、ノードでホストできる IP アドレスを指定します。 - namespace ごとに複数の egress IP アドレスがサポートされます。
namespace に複数の egress IP アドレスがある場合、最初の egress IP アドレスをホストするノードに到達できない場合、OpenShift Container Platform は最初の egress IP アドレスが再び到達可能になるまで、次に利用可能な egress IP アドレスの使用に自動的に切り替えます。
14.2.2. namespace の自動的に割り当てられた egress IP アドレスの有効化
OpenShift Container Platform では、1 つ以上のノードで特定の namespace の egress IP アドレスの自動的な割り当てを有効にできます。
前提条件
-
cluster-adminロールを持つユーザーとしてクラスターにアクセスできる。 -
OpenShift CLI (
oc) がインストールされている。
手順
以下の JSON を使用して、
NetNamespaceオブジェクトを egress IP アドレスで更新します。$ oc patch netnamespace <project_name> --type=merge -p \1 '{ "egressIPs": [ "<ip_address>"2 ] }'たとえば、
project1を IP アドレスの 192.168.1.100 に、project2を IP アドレスの 192.168.1.101 に割り当てるには、以下を実行します。$ oc patch netnamespace project1 --type=merge -p \ '{"egressIPs": ["192.168.1.100"]}' $ oc patch netnamespace project2 --type=merge -p \ '{"egressIPs": ["192.168.1.101"]}'注記OpenShift SDN は
NetNamespaceオブジェクトを管理するため、既存のNetNamespaceオブジェクトを変更することによってのみ変更を加えることができます。新規NetNamespaceオブジェクトは作成しません。以下の JSON を使用して、各ホストの
egressCIDRsパラメーターを設定して egress IP アドレスをホストできるノードを示します。$ oc patch hostsubnet <node_name> --type=merge -p \1 '{ "egressCIDRs": [ "<ip_address_range_1>", "<ip_address_range_2>"2 ] }'たとえば、
node1およびnode2を、192.168.1.0 から 192.168.1.255 の範囲で egress IP アドレスをホストするように設定するには、以下を実行します。$ oc patch hostsubnet node1 --type=merge -p \ '{"egressCIDRs": ["192.168.1.0/24"]}' $ oc patch hostsubnet node2 --type=merge -p \ '{"egressCIDRs": ["192.168.1.0/24"]}'OpenShift Container Platform はバランスを取りながら特定の egress IP アドレスを利用可能なノードに自動的に割り当てます。この場合、egress IP アドレス 192.168.1.100 を
node1に、egress IP アドレス 192.168.1.101 をnode2に割り当て、その逆も行います。
14.2.3. namespace の手動で割り当てられた egress IP アドレスの設定
OpenShift Container Platform で、1 つ以上の egress IP アドレスを namespace に関連付けることができます。
前提条件
-
cluster-adminロールを持つユーザーとしてクラスターにアクセスできる。 -
OpenShift CLI (
oc) がインストールされている。
手順
以下の JSON オブジェクトを必要な IP アドレスで指定して、
NetNamespaceオブジェクトを更新します。$ oc patch netnamespace <project> --type=merge -p \1 '{ "egressIPs": [2 "<ip_address>" ] }'たとえば、
project1プロジェクトを192.168.1.100の IP アドレスに割り当てるには、以下を実行します。$ oc patch netnamespace project1 --type=merge \ -p '{"egressIPs": ["192.168.1.100"]}'egressIPsを異なるノードの 2 つ以上の IP アドレスに設定し、高可用性を確保することができます。複数の egress IP アドレスが設定される場合、Pod は egress の一覧にある最初の IP を使用しますが、IP アドレスをホストするノードが失敗する場合、Pod は短時間の遅延の後に一覧にある次の IP の使用に切り替えます。注記OpenShift SDN は
NetNamespaceオブジェクトを管理するため、既存のNetNamespaceオブジェクトを変更することによってのみ変更を加えることができます。新規NetNamespaceオブジェクトは作成しません。egress IP をノードホストに手動で割り当てます。
egressIPsパラメーターを、ノードホストのHostSubnetオブジェクトに設定します。以下の JSON を使用して、そのノードホストに割り当てる必要のある任意の数の IP を含めることができます。$ oc patch hostsubnet <node_name> --type=merge -p \1 '{ "egressIPs": [2 "<ip_address_1>", "<ip_address_N>" ] }'たとえば、
node1に Egress IP192.168.1.100、192.168.1.101、および192.168.1.102が設定されるように指定するには、以下を実行します。$ oc patch hostsubnet node1 --type=merge -p \ '{"egressIPs": ["192.168.1.100", "192.168.1.101", "192.168.1.102"]}'直前の例では、
project1のすべての egress トラフィックは、指定された egress IP をホストするノードにルーティングされてから、その IP アドレスに (NAT を使用して) 接続されます。
14.3. プロジェクトの egress ファイアウォールの設定
クラスター管理者は、OpenShift Container Platform クラスター外に出るプロジェクトのプロジェクについて、egress トラフィックを制限する egress ファイアウォールを作成できます。
14.3.1. egress ファイアウォールのプロジェクトでの機能
クラスター管理者は、 egress ファイアウォール を使用して、一部またはすべての Pod がクラスター内からアクセスできる外部ホストを制限できます。egress ファイアウォールポリシーは以下のシナリオをサポートします。
- Pod の接続を内部ホストに制限し、パブリックインターネットへの接続を開始できないようにする。
- Pod の接続をパブリックインターネットに制限し、OpenShift Container Platform クラスター外にある内部ホストへの接続を開始できないようにする。
- Pod は OpenShift Container Platform クラスター外の指定された内部サブネットまたはホストにアクセスできません。
- Pod は特定の外部ホストにのみ接続することができます。
たとえば、指定された IP 範囲へのあるプロジェクトへのアクセスを許可する一方で、別のプロジェクトへの同じアクセスを拒否することができます。または、アプリケーション開発者の (Python) pip mirror からの更新を制限したり、更新を承認されたソースからの更新のみに強制的に制限したりすることができます。
EgressNetworkPolicy カスタムリソース (CR) オブジェクトを作成して egress ファイアウォールポリシーを設定します。egress ファイアウォールは、以下のいずれかの基準を満たすネットワークトラフィックと一致します。
- CIDR 形式の IP アドレス範囲。
- IP アドレスに解決する DNS 名
egress ファイアウォールに 0.0.0.0/0 の拒否ルールが含まれる場合、OpenShift Container Platform API サーバーへのアクセスはブロックされます。Pod が OpenShift Container Platform API サーバーへのアクセスを継続できるようにするには、以下の例にあるように API サーバーが egress ファイアウォールルールでリッスンする IP アドレス範囲を含める必要があります。
apiVersion: network.openshift.io/v1
kind: EgressNetworkPolicy
metadata:
name: default
namespace: <namespace>
spec:
egress:
- to:
cidrSelector: <api_server_address_range>
type: Allow
# ...
- to:
cidrSelector: 0.0.0.0/0
type: Deny
API サーバーの IP アドレスを見つけるには、oc get ep kubernetes -n default を実行します。
詳細は、BZ#1988324 を参照してください。
egress ファイアウォールを設定するには、ネットワークポリシーまたはマルチテナントモードのいずれかを使用するように OpenShift SDN を設定する必要があります。
ネットワークポリシーモードを使用している場合、egress ファイアウォールは namespace ごとに 1 つのポリシーとのみ互換性を持ち、グローバルプロジェクトなどのネットワークを共有するプロジェクトでは機能しません。
egress ファイアウォールルールは、ルーターを通過するトラフィックには適用されません。ルート CR オブジェクトを作成するパーミッションを持つユーザーは、禁止されている宛先を参照するルートを作成することにより、egress ファイアウォールポリシールールをバイパスできます。
14.3.1.1. egress ファイアウォールの制限
egress ファイアウォールには以下の制限があります。
- いずれのプロジェクトも複数の EgressNetworkPolicy オブジェクトを持つことができません。
- 最大 1,000 のルールを持つ最大 1 つの EgressNetworkPolicy オブジェクトはプロジェクトごとに定義できます。
-
defaultプロジェクトは egress ファイアウォールを使用できません。 マルチテナントモードで OpenShift SDN デフォルト Container Network Interface (CNI) ネットワークプロバイダーを使用する場合、以下の制限が適用されます。
-
グローバルプロジェクトは egress ファイアウォールを使用できません。
oc adm pod-network make-projects-globalコマンドを使用して、プロジェクトをグローバルにすることができます。 -
oc adm pod-network join-projectsコマンドを使用してマージされるプロジェクトでは、結合されたプロジェクトのいずれでも egress ファイアウォールを使用することはできません。
-
グローバルプロジェクトは egress ファイアウォールを使用できません。
上記の制限のいずれかに違反すると、プロジェクトの egress ファイアウォールに障害が発生し、すべての外部ネットワークトラフィックがドロップされる可能性があります。
egress ファイアウォールリソースは、kube-node-lease、kube-public、kube-system、openshift、openshift- プロジェクトで作成できます。
14.3.1.2. egress ポリシールールのマッチング順序
egress ファイアウォールポリシールールは、最初から最後へと定義された順序で評価されます。Pod からの egress 接続に一致する最初のルールが適用されます。この接続では、後続のルールは無視されます。
14.3.1.3. DNS (Domain Name Server) 解決の仕組み
egress ファイアウォールポリシールールのいずれかで DNS 名を使用する場合、ドメイン名の適切な解決には、以下の制限が適用されます。
- ドメイン名の更新は、ローカルの非権威サーバーのドメインの TTL (time to live) 値に基づいてポーリングされます。
- Pod は、必要に応じて同じローカルネームサーバーからドメインを解決する必要があります。そうしない場合、egress ファイアウォールコントローラーと Pod によって認識されるドメインの IP アドレスが異なる可能性があります。ホスト名の IP アドレスが異なる場合、egress ファイアウォールは一貫して実行されないことがあります。
- egress ファイアウォールコントローラーおよび Pod は同じローカルネームサーバーを非同期にポーリングするため、Pod は egress コントローラーが実行する前に更新された IP アドレスを取得する可能性があります。これにより、競合状態が生じます。この現時点の制限により、EgressNetworkPolicy オブジェクトのドメイン名の使用は、IP アドレスの変更が頻繁に生じないドメインの場合にのみ推奨されます。
egress ファイアウォールは、DNS 解決用に Pod が置かれるノードの外部インターフェイスに Pod が常にアクセスできるようにします。
ドメイン名を egress ファイアウォールで使用し、DNS 解決がローカルノード上の DNS サーバーによって処理されない場合は、Pod でドメイン名を使用している場合には DNS サーバーの IP アドレスへのアクセスを許可する egress ファイアウォールを追加する必要があります。
14.3.2. EgressNetworkPolicy カスタムリソース (CR) オブジェクト
egress ファイアウォールのルールを 1 つ以上定義できます。ルールは、ルールが適用されるトラフィックを指定して Allow ルールまたは Deny ルールのいずれかになります。
以下の YAML は EgressNetworkPolicy CR オブジェクトについて説明しています。
EgressNetworkPolicy オブジェクト
apiVersion: network.openshift.io/v1
kind: EgressNetworkPolicy
metadata:
name: <name>
spec:
egress:
...14.3.2.1. EgressNetworkPolicy ルール
以下の YAML は egress ファイアウォールルールオブジェクトについて説明しています。egress スタンザは、単一または複数のオブジェクトの配列を予想します。
Egress ポリシールールのスタンザ
egress:
- type: <type>
to:
cidrSelector: <cidr>
dnsName: <dns_name> 14.3.2.2. EgressNetworkPolicy CR オブジェクトの例
以下の例では、複数の egress ファイアウォールポリシールールを定義します。
apiVersion: network.openshift.io/v1
kind: EgressNetworkPolicy
metadata:
name: default
spec:
egress:
- type: Allow
to:
cidrSelector: 1.2.3.0/24
- type: Allow
to:
dnsName: www.example.com
- type: Deny
to:
cidrSelector: 0.0.0.0/0- 1
- egress ファイアウォールポリシールールオブジェクトのコレクション。
14.3.3. egress ファイアウォールポリシーオブジェクトの作成
クラスター管理者は、プロジェクトの egress ファイアウォールポリシーオブジェクトを作成できます。
プロジェクトに EgressNetworkPolicy オブジェクトがすでに定義されている場合、既存のポリシーを編集して egress ファイアウォールルールを変更する必要があります。
前提条件
- OpenShift SDN デフォルト Container Network Interface (CNI) ネットワークプロバイダープラグインを使用するクラスター。
-
OpenShift CLI (
oc) をインストールしている。 - クラスター管理者としてクラスターにログインする必要があります。
手順
ポリシールールを作成します。
-
<policy_name>.yamlファイルを作成します。この場合、<policy_name>は egress ポリシールールを記述します。 - 作成したファイルで、egress ポリシーオブジェクトを定義します。
-
以下のコマンドを入力してポリシーオブジェクトを作成します。
<policy_name>をポリシーの名前に、<project>をルールが適用されるプロジェクトに置き換えます。$ oc create -f <policy_name>.yaml -n <project>以下の例では、新規の EgressNetworkPolicy オブジェクトが
project1という名前のプロジェクトに作成されます。$ oc create -f default.yaml -n project1出力例
egressnetworkpolicy.network.openshift.io/v1 created-
オプション: 後に変更できるように
<policy_name>.yamlファイルを保存します。
14.4. プロジェクトの egress ファイアウォールの編集
クラスター管理者は、既存の egress ファイアウォールのネットワークトラフィックルールを変更できます。
14.4.1. EgressNetworkPolicy オブジェクトの表示
クラスターで EgressNetworkPolicy オブジェクトを表示できます。
前提条件
- OpenShift SDN デフォルト Container Network Interface (CNI) ネットワークプロバイダープラグインを使用するクラスター。
-
ocとして知られる OpenShift コマンドラインインターフェイス (CLI) のインストール。 - クラスターにログインすること。
手順
オプション: クラスターで定義された EgressNetworkPolicy オブジェクトの名前を表示するには、以下のコマンドを入力します。
$ oc get egressnetworkpolicy --all-namespacesポリシーを検査するには、以下のコマンドを入力します。
<policy_name>を検査するポリシーの名前に置き換えます。$ oc describe egressnetworkpolicy <policy_name>出力例
Name: default Namespace: project1 Created: 20 minutes ago Labels: <none> Annotations: <none> Rule: Allow to 1.2.3.0/24 Rule: Allow to www.example.com Rule: Deny to 0.0.0.0/0
14.5. プロジェクトの egress ファイアウォールの編集
クラスター管理者は、既存の egress ファイアウォールのネットワークトラフィックルールを変更できます。
14.5.1. EgressNetworkPolicy オブジェクトの編集
クラスター管理者は、プロジェクトの egress ファイアウォールを更新できます。
前提条件
- OpenShift SDN デフォルト Container Network Interface (CNI) ネットワークプロバイダープラグインを使用するクラスター。
-
OpenShift CLI (
oc) をインストールしている。 - クラスター管理者としてクラスターにログインする必要があります。
手順
プロジェクトの EgressNetworkPolicy オブジェクトの名前を検索します。
<project>をプロジェクトの名前に置き換えます。$ oc get -n <project> egressnetworkpolicyオプション: egress ネットワークファイアウォールの作成時に EgressNetworkPolicy オブジェクトのコピーを保存しなかった場合には、以下のコマンドを入力してコピーを作成します。
$ oc get -n <project> egressnetworkpolicy <name> -o yaml > <filename>.yaml<project>をプロジェクトの名前に置き換えます。<name>をオブジェクトの名前に置き換えます。<filename>をファイルの名前に置き換え、YAML を保存します。ポリシールールに変更を加えたら、以下のコマンドを実行して EgressNetworkPolicy オブジェクトを置き換えます。
<filename>を、更新された EgressNetworkPolicy オブジェクトを含むファイルの名前に置き換えます。$ oc replace -f <filename>.yaml
14.6. プロジェクトからの egress ファイアウォールの削除
クラスター管理者は、プロジェクトから egress ファイアウォールを削除して、OpenShift Container Platform クラスター外に出るプロジェクトからネットワークトラフィックについてのすべての制限を削除できます。
14.6.1. EgressNetworkPolicy オブジェクトの削除
クラスター管理者は、プロジェクトから Egress ファイアウォールを削除できます。
前提条件
- OpenShift SDN デフォルト Container Network Interface (CNI) ネットワークプロバイダープラグインを使用するクラスター。
-
OpenShift CLI (
oc) をインストールしている。 - クラスター管理者としてクラスターにログインする必要があります。
手順
プロジェクトの EgressNetworkPolicy オブジェクトの名前を検索します。
<project>をプロジェクトの名前に置き換えます。$ oc get -n <project> egressnetworkpolicy以下のコマンドを入力し、EgressNetworkPolicy オブジェクトを削除します。
<project>をプロジェクトの名前に、<name>をオブジェクトの名前に置き換えます。$ oc delete -n <project> egressnetworkpolicy <name>
14.7. egress ルーター Pod の使用についての考慮事項
14.7.1. egress ルーター Pod について
OpenShift Container Platform egress ルーター Pod は、他の用途で使用されていないプライベートソース IP アドレスから指定されたリモートサーバーにトラフィックをリダイレクトします。egress ルーター Pod により、特定の IP アドレスからのアクセスのみを許可するように設定されたサーバーにネットワークトラフィックを送信できます。
egress ルーター Pod はすべての発信接続のために使用されることが意図されていません。多数の egress ルーター Pod を作成することで、ネットワークハードウェアの制限を引き上げられる可能性があります。たとえば、すべてのプロジェクトまたはアプリケーションに egress ルーター Pod を作成すると、ソフトウェアの MAC アドレスのフィルターに戻る前にネットワークインターフェイスが処理できるローカル MAC アドレス数の上限を超えてしまう可能性があります。
egress ルーターイメージには Amazon AWS, Azure Cloud またはレイヤー 2 操作をサポートしないその他のクラウドプラットフォームとの互換性がありません。 それらに macvlan トラフィックとの互換性がないためです。
14.7.1.1. Egress ルーターモード
リダイレクトモード では、egress ルーター Pod は、トラフィックを独自の IP アドレスから 1 つ以上の宛先 IP アドレスにリダイレクトするために iptables ルールをセットアップします。予約されたソース IP アドレスを使用する必要のあるクライアント Pod は、宛先 IP に直接接続するのでなく、egress ルーターに接続するように変更される必要があります。
HTTP プロキシーモードでは、egress ルーター Pod はポート 8080 で HTTP プロキシーとして実行されます。このモードは、HTTP または HTTPS ベースのサービスと通信するクライアントの場合にのみ機能しますが、通常それらを機能させるのにクライアント Pod への多くの変更は不要です。環境変数を設定することで、数多くのプログラムは HTTP プロキシーを使用するように指示されます。
DNS プロキシーモードでは、egress ルーター Pod は、トラフィックを独自の IP アドレスから 1 つ以上の宛先 IP アドレスに送信する TCP ベースのサービスの DNS プロキシーとして実行されます。予約されたソース IP アドレスを使用するには、クライアント Pod は、宛先 IP アドレスに直接接続するのでなく、egress ルーター Pod に接続するように変更される必要があります。この修正により、外部の宛先でトラフィックが既知のソースから送信されているかのように処理されます。
リダイレクトモードは、HTTP および HTTPS 以外のすべてのサービスで機能します。HTTP および HTTPS サービスの場合は、HTTP プロキシーモードを使用します。IP アドレスまたはドメイン名を持つ TCP ベースのサービスの場合は、DNS プロキシーモードを使用します。
14.7.1.2. egress ルーター Pod の実装
egress ルーター Pod の設定は、初期化コンテナーで実行されます。このコンテナーは特権付きコンテキストで実行され、macvlan インターフェイスを設定して iptables ルールを設定できます。初期化コンテナーが iptables ルールの設定を終了すると、終了します。次に、egress ルーター Pod はコンテナーを実行して egress ルーターのトラフィックを処理します。使用されるイメージは、egress ルーターモードによって異なります。
環境変数は、egress-router イメージが使用するアドレスを判別します。イメージは macvlan インターフェイスを、 EGRESS_SOURCE をその IP アドレスとして使用し、EGRESS_GATEWAY をゲートウェイの IP アドレスとして使用するように設定します。
ネットワークアドレス変換 (NAT) ルールは、TCP ポートまたは UDP ポート上の Pod のクラスター IP アドレスへの接続が EGRESS_DESTINATION 変数で指定される IP アドレスの同じポートにリダイレクトされるように設定されます。
クラスター内の一部のノードのみが指定されたソース IP アドレスを要求でき、指定されたゲートウェイを使用できる場合、受け入れ可能なノードを示す nodeName または nodeSelector を指定することができます。
14.7.1.3. デプロイメントに関する考慮事項
egress ルーター Pod は追加の IP アドレスおよび MAC アドレスをノードのプライマリーネットワークインターフェイスに追加します。その結果、ハイパーバイザーまたはクラウドプロバイダーを、追加のアドレスを許可するように設定する必要がある場合があります。
- Red Hat OpenStack Platform (RHOSP)
OpenShift Container Platform を RHOSP にデプロイする場合、OpenStack 環境の egress ルーター Pod の IP および MAC アドレスからのトラフィックを許可する必要があります。トラフィックを許可しないと、通信は失敗 します。
$ openstack port set --allowed-address \ ip_address=<ip_address>,mac_address=<mac_address> <neutron_port_uuid>- Red Hat Virtualization (RHV)
- RHV を使用している場合は、仮想インターフェイスカード (vNIC) に No Network Filter を選択する必要があります。
- VMware vSphere
- VMware vSphere を使用している場合は、vSphere 標準スイッチのセキュリティー保護についての VMware ドキュメント を参照してください。vSphere Web クライアントからホストの仮想スイッチを選択して、VMware vSphere デフォルト設定を表示し、変更します。
とくに、以下が有効にされていることを確認します。
14.7.1.4. フェイルオーバー設定
ダウンタイムを回避するには、以下の例のように Deployment リソースで egress ルーター Pod をデプロイできます。サンプルのデプロイメント用に新規 Service オブジェクトを作成するには、oc expose deployment/egress-demo-controller コマンドを使用します。
apiVersion: apps/v1
kind: Deployment
metadata:
name: egress-demo-controller
spec:
replicas: 1
selector:
matchLabels:
name: egress-router
template:
metadata:
name: egress-router
labels:
name: egress-router
annotations:
pod.network.openshift.io/assign-macvlan: "true"
spec:
initContainers:
...
containers:
...14.8. リダイレクトモードでの egress ルーター Pod のデプロイ
クラスター管理者は、トラフィックを指定された宛先 IP アドレスにリダイレクトするように設定された egress ルーター Pod をデプロイできます。
14.8.1. リダイレクトモードの egress ルーター Pod 仕様
Pod オブジェクトで egress ルーター Pod の設定を定義します。以下の YAML は、リダイレクトモードでの egress ルーター Pod の設定のフィールドについて説明しています。
apiVersion: v1
kind: Pod
metadata:
name: egress-1
labels:
name: egress-1
annotations:
pod.network.openshift.io/assign-macvlan: "true"
spec:
initContainers:
- name: egress-router
image: registry.redhat.io/openshift4/ose-egress-router
securityContext:
privileged: true
env:
- name: EGRESS_SOURCE
value: <egress_router>
- name: EGRESS_GATEWAY
value: <egress_gateway>
- name: EGRESS_DESTINATION
value: <egress_destination>
- name: EGRESS_ROUTER_MODE
value: init
containers:
- name: egress-router-wait
image: registry.redhat.io/openshift4/ose-pod- 1
- このアノテーションは、OpenShift Container Platform に対して、プライマリーネットワークインターフェイスコントローラー (NIC) に macvlan ネットワークインターフェイスを作成し、その macvlan インターフェイスを Pod ネットワークの namespace に移動するよう指示します。引用符を
"true"値の周囲に含める必要があります。OpenShift Container Platform が別の NIC インターフェイスに macvlan インターフェイスを作成するには、アノテーションの値をそのインターフェイスの名前に設定します。たとえば、eth1を使用します。 - 2
- ノードが置かれている物理ネットワークの IP アドレスは egress ルーター Pod で使用するために予約されます。オプション: サブネットの長さ
/24接尾辞を組み込み、ローカルサブネットへの適切なルートがセットアップされるようにできます。サブネットの長さを指定しない場合、egress ルーターはEGRESS_GATEWAY変数で指定されたホストにのみアクセスでき、サブネットの他のホストにはアクセスできません。 - 3
- ノードで使用されるデフォルトゲートウェイと同じ値です。
- 4
- トラフィックの送信先となる外部サーバー。この例では、Pod の接続は
203.0.113.25にリダイレクトされます。 ソース IP アドレスは192.168.12.99です。
egress ルーター Pod 仕様の例
apiVersion: v1
kind: Pod
metadata:
name: egress-multi
labels:
name: egress-multi
annotations:
pod.network.openshift.io/assign-macvlan: "true"
spec:
initContainers:
- name: egress-router
image: registry.redhat.io/openshift4/ose-egress-router
securityContext:
privileged: true
env:
- name: EGRESS_SOURCE
value: 192.168.12.99/24
- name: EGRESS_GATEWAY
value: 192.168.12.1
- name: EGRESS_DESTINATION
value: |
80 tcp 203.0.113.25
8080 tcp 203.0.113.26 80
8443 tcp 203.0.113.26 443
203.0.113.27
- name: EGRESS_ROUTER_MODE
value: init
containers:
- name: egress-router-wait
image: registry.redhat.io/openshift4/ose-pod14.8.2. egress 宛先設定形式
egress ルーター Pod がリダイレクトモードでデプロイされる場合、以下のいずれかの形式を使用してリダイレクトルールを指定できます。
-
<port> <protocol> <ip_address>: 指定される<port>への着信接続が指定される<ip_address>の同じポートにリダイレクトされます。<protocol>はtcpまたはudpのいずれかになります。 -
<port> <protocol> <ip_address> <remote_port>: 接続が<ip_address>の別の<remote_port>にリダイレクトされるのを除き、上記と同じになります。 -
<ip_address>: 最後の行が単一 IP アドレスである場合、それ以外のポートの接続はその IP アドレスの対応するポートにリダイレクトされます。フォールバック IP アドレスがない場合、他のポートでの接続は拒否されます。
以下の例では、複数のルールが定義されます。
-
最初の行はローカルポート
80から203.0.113.25のポート80にトラフィックをリダイレクトします。 -
2 番目と 3 番目の行では、ローカルポート
8080および8443を、203.0.113.26のリモートポート80および443にリダイレクトします。 - 最後の行は、先のルールで指定されていないポートのトラフィックに一致します。
設定例
80 tcp 203.0.113.25
8080 tcp 203.0.113.26 80
8443 tcp 203.0.113.26 443
203.0.113.2714.8.3. リダイレクトモードでの egress ルーター Pod のデプロイ
リダイレクトモードでは、egress ルーター Pod は、トラフィックを独自の IP アドレスから 1 つ以上の宛先 IP アドレスにリダイレクトするために iptables ルールをセットアップします。予約されたソース IP アドレスを使用する必要のあるクライアント Pod は、宛先 IP に直接接続するのでなく、egress ルーターに接続するように変更される必要があります。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
- egress ルーター Pod の作成
他の Pod が egress ルーター Pod の IP アドレスを見つられるようにするには、以下の例のように、egress ルーター Pod を参照するサービスを作成します。
apiVersion: v1 kind: Service metadata: name: egress-1 spec: ports: - name: http port: 80 - name: https port: 443 type: ClusterIP selector: name: egress-1Pod がこのサービスに接続できるようになります。これらの接続は、予約された egress IP アドレスを使用して外部サーバーの対応するポートにリダイレクトされます。
14.9. HTTP プロキシーモードでの egress ルーター Pod のデプロイ
クラスター管理者は、トラフィックを指定された HTTP および HTTPS ベースのサービスにプロキシーするように設定された egress ルーター Pod をデプロイできます。
14.9.1. HTTP モードの egress ルーター Pod 仕様
Pod オブジェクトで egress ルーター Pod の設定を定義します。以下の YAML は、HTTP モードでの egress ルーター Pod の設定のフィールドについて説明しています。
apiVersion: v1
kind: Pod
metadata:
name: egress-1
labels:
name: egress-1
annotations:
pod.network.openshift.io/assign-macvlan: "true"
spec:
initContainers:
- name: egress-router
image: registry.redhat.io/openshift4/ose-egress-router
securityContext:
privileged: true
env:
- name: EGRESS_SOURCE
value: <egress-router>
- name: EGRESS_GATEWAY
value: <egress-gateway>
- name: EGRESS_ROUTER_MODE
value: http-proxy
containers:
- name: egress-router-pod
image: registry.redhat.io/openshift4/ose-egress-http-proxy
env:
- name: EGRESS_HTTP_PROXY_DESTINATION
value: |-
...
...- 1
- このアノテーションは、OpenShift Container Platform に対して、プライマリーネットワークインターフェイスコントローラー (NIC) に macvlan ネットワークインターフェイスを作成し、その macvlan インターフェイスを Pod ネットワークの namespace に移動するよう指示します。引用符を
"true"値の周囲に含める必要があります。OpenShift Container Platform が別の NIC インターフェイスに macvlan インターフェイスを作成するには、アノテーションの値をそのインターフェイスの名前に設定します。たとえば、eth1を使用します。 - 2
- ノードが置かれている物理ネットワークの IP アドレスは egress ルーター Pod で使用するために予約されます。オプション: サブネットの長さ
/24接尾辞を組み込み、ローカルサブネットへの適切なルートがセットアップされるようにできます。サブネットの長さを指定しない場合、egress ルーターはEGRESS_GATEWAY変数で指定されたホストにのみアクセスでき、サブネットの他のホストにはアクセスできません。 - 3
- ノードで使用されるデフォルトゲートウェイと同じ値です。
- 4
- プロキシーの設定方法を指定する文字列または YAML の複数行文字列です。これは、init コンテナーの他の環境変数ではなく、HTTP プロキシーコンテナーの環境変数として指定されることに注意してください。
14.9.2. egress 宛先設定形式
egress ルーター Pod が HTTP プロキシーモードでデプロイされる場合、以下の形式のいずれかを使用してリダイレクトルールを指定できます。これはすべてのリモート宛先への接続を許可することを意味します。 設定の各行には、許可または拒否する接続の 1 つのグループを指定します。
-
IP アドレス (例:
192.168.1.1) は該当する IP アドレスへの接続を許可します。 -
CIDR 範囲 (例:
192.168.1.0/24) は CIDR 範囲への接続を許可します。 -
ホスト名 (例:
www.example.com) は該当ホストへのプロキシーを許可します。 -
*.が前に付けられているドメイン名 (例:*.example.com) は該当ドメインおよびそのサブドメインのすべてへのプロキシーを許可します。 -
先の一致 (match) 式のいずれかの後に来る
!は接続を拒否します。 -
最後の行が
*の場合、明示的に拒否されていないすべてのものが許可されます。それ以外の場合、許可されないすべてのものが拒否されます。
* を使用してすべてのリモート宛先への接続を許可することもできます。
設定例
!*.example.com
!192.168.1.0/24
192.168.2.1
*14.9.3. HTTP プロキシーモードでの egress ルーター Pod のデプロイ
HTTP プロキシーモードでは、egress ルーター Pod はポート 8080 で HTTP プロキシーとして実行されます。このモードは、HTTP または HTTPS ベースのサービスと通信するクライアントの場合にのみ機能しますが、通常それらを機能させるのにクライアント Pod への多くの変更は不要です。環境変数を設定することで、数多くのプログラムは HTTP プロキシーを使用するように指示されます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
- egress ルーター Pod の作成
他の Pod が egress ルーター Pod の IP アドレスを見つられるようにするには、以下の例のように、egress ルーター Pod を参照するサービスを作成します。
apiVersion: v1 kind: Service metadata: name: egress-1 spec: ports: - name: http-proxy port: 80801 type: ClusterIP selector: name: egress-1- 1
httpポートが常に8080に設定されていることを確認します。
http_proxyまたはhttps_proxy変数を設定して、クライアント Pod (egress プロキシー Pod ではない) を HTTP プロキシーを使用するように設定します。apiVersion: v1 kind: Pod metadata: name: app-1 labels: name: app-1 spec: containers: env: - name: http_proxy value: http://egress-1:8080/1 - name: https_proxy value: http://egress-1:8080/ ...- 1
- 先の手順で作成したサービス。
注記すべてのセットアップに
http_proxyおよびhttps_proxy環境変数が必要になる訳ではありません。上記を実行しても作業用セットアップが作成されない場合は、Pod で実行しているツールまたはソフトウェアについてのドキュメントを参照してください。
14.10. DNS プロキシーモードでの egress ルーター Pod のデプロイ
クラスター管理者は、トラフィックを指定された DNS 名および IP アドレスにプロキシーするように設定された egress ルーター Pod をデプロイできます。
14.10.1. DNS モードの egress ルーター Pod 仕様
Pod オブジェクトで egress ルーター Pod の設定を定義します。以下の YAML は、DNS モードでの egress ルーター Pod の設定のフィールドについて説明しています。
apiVersion: v1
kind: Pod
metadata:
name: egress-1
labels:
name: egress-1
annotations:
pod.network.openshift.io/assign-macvlan: "true"
spec:
initContainers:
- name: egress-router
image: registry.redhat.io/openshift4/ose-egress-router
securityContext:
privileged: true
env:
- name: EGRESS_SOURCE
value: <egress-router>
- name: EGRESS_GATEWAY
value: <egress-gateway>
- name: EGRESS_ROUTER_MODE
value: dns-proxy
containers:
- name: egress-router-pod
image: registry.redhat.io/openshift4/ose-egress-dns-proxy
securityContext:
privileged: true
env:
- name: EGRESS_DNS_PROXY_DESTINATION
value: |-
...
- name: EGRESS_DNS_PROXY_DEBUG
value: "1"
...- 1
- このアノテーションは、OpenShift Container Platform に対して、プライマリーネットワークインターフェイスコントローラー (NIC) に macvlan ネットワークインターフェイスを作成し、その macvlan インターフェイスを Pod ネットワークの namespace に移動するよう指示します。引用符を
"true"値の周囲に含める必要があります。OpenShift Container Platform が別の NIC インターフェイスに macvlan インターフェイスを作成するには、アノテーションの値をそのインターフェイスの名前に設定します。たとえば、eth1を使用します。 - 2
- ノードが置かれている物理ネットワークの IP アドレスは egress ルーター Pod で使用するために予約されます。オプション: サブネットの長さ
/24接尾辞を組み込み、ローカルサブネットへの適切なルートがセットアップされるようにできます。サブネットの長さを指定しない場合、egress ルーターはEGRESS_GATEWAY変数で指定されたホストにのみアクセスでき、サブネットの他のホストにはアクセスできません。 - 3
- ノードで使用されるデフォルトゲートウェイと同じ値です。
- 4
- 1 つ以上のプロキシー宛先の一覧を指定します。
- 5
- オプション: DNS プロキシーログ出力を
stdoutに出力するために指定します。
14.10.2. egress 宛先設定形式
ルーターが DNS プロキシーモードでデプロイされる場合、ポートおよび宛先マッピングの一覧を指定します。宛先には、IP アドレスまたは DNS 名のいずれかを使用できます。
egress ルーター Pod は、ポートおよび宛先マッピングを指定するために以下の形式をサポートします。
- ポートおよびリモートアドレス
-
送信元ポートおよび宛先ホストは、2 つのフィールド形式 (
<port> <remote_address>) を使用して指定できます。
ホストには、IP アドレスまたは DNS 名を指定できます。DNS 名を指定すると、DNS 解決が起動時に行われます。特定のホストについては、プロキシーは、宛先ホスト IP アドレスへの接続時に、宛先ホストの指定された送信元ポートに接続されます。
ポートとリモートアドレスペアの例
80 172.16.12.11
100 example.com- ポート、リモートアドレス、およびリモートポート
-
送信元ポート、宛先ホスト、および宛先ポートは、
<port> <remote_address> <remote_port>の 3 つのフィールドからなる形式を使用して指定できます。
3 つのフィールド形式は、2 つのフィールドバージョンと同じように動作しますが、宛先ポートが送信元ポートとは異なる場合があります。
ポート、リモートアドレス、およびリモートポートの例
8080 192.168.60.252 80
8443 web.example.com 44314.10.3. DNS プロキシーモードでの egress ルーター Pod のデプロイ
DNS プロキシーモードでは、egress ルーター Pod は、トラフィックを独自の IP アドレスから 1 つ以上の宛先 IP アドレスに送信する TCP ベースのサービスの DNS プロキシーとして機能します。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
- egress ルーター Pod の作成
egress ルーター Pod のサービスを作成します。
以下の YAML 定義が含まれる
egress-router-service.yamlという名前のファイルを作成します。spec.portsを、EGRESS_DNS_PROXY_DESTINATION環境変数に先に定義したポートの一覧に設定します。apiVersion: v1 kind: Service metadata: name: egress-dns-svc spec: ports: ... type: ClusterIP selector: name: egress-dns-proxy以下に例を示します。
apiVersion: v1 kind: Service metadata: name: egress-dns-svc spec: ports: - name: con1 protocol: TCP port: 80 targetPort: 80 - name: con2 protocol: TCP port: 100 targetPort: 100 type: ClusterIP selector: name: egress-dns-proxyサービスを作成するには、以下のコマンドを入力します。
$ oc create -f egress-router-service.yamlPod がこのサービスに接続できるようになります。これらの接続は、予約された egress IP アドレスを使用して外部サーバーの対応するポートにプロキシー送信されます。
14.11. 設定マップからの egress ルーター Pod 宛先一覧の設定
クラスター管理者は、egress ルーター Pod の宛先マッピングを指定する ConfigMap オブジェクトを定義できます。設定の特定の形式は、egress ルーター Pod のタイプによって異なります。形式についての詳細は、特定の egress ルーター Pod のドキュメントを参照してください。
14.11.1. 設定マップを使用した egress ルーター宛先マッピングの設定
宛先マッピングのセットのサイズが大きいか、またはこれが頻繁に変更される場合、設定マップを使用して一覧を外部で維持できます。この方法の利点は、設定マップを編集するパーミッションを cluster-admin 権限を持たないユーザーに委任できることです。egress ルーター Pod には特権付きコンテナーを必要とするため、cluster-admin 権限を持たないユーザーは Pod 定義を直接編集することはできません。
egress ルーター Pod は、設定マップが変更されても自動的に更新されません。更新を取得するには、egress ルーター Pod を再起動する必要があります。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
以下の例のように、egress ルーター Pod のマッピングデータが含まれるファイルを作成します。
# Egress routes for Project "Test", version 3 80 tcp 203.0.113.25 8080 tcp 203.0.113.26 80 8443 tcp 203.0.113.26 443 # Fallback 203.0.113.27空の行とコメントをこのファイルに追加できます。
このファイルから
ConfigMapオブジェクトを作成します。$ oc delete configmap egress-routes --ignore-not-found$ oc create configmap egress-routes \ --from-file=destination=my-egress-destination.txt直前のコマンドで、
egress-routes値は、作成するConfigMapオブジェクトの名前で、my-egress-destination.txtはデータの読み取り元のファイルの名前です。egress ルーター Pod 定義を作成し、environment スタンザの
EGRESS_DESTINATIONフィールドにconfigMapKeyRefスタンザを指定します。... env: - name: EGRESS_DESTINATION valueFrom: configMapKeyRef: name: egress-routes key: destination ...
14.12. プロジェクトのマルチキャストの有効化
14.12.1. マルチキャストについて
IP マルチキャストを使用すると、データが多数の IP アドレスに同時に配信されます。
現時点で、マルチキャストは低帯域幅の調整またはサービスの検出での使用に最も適しており、高帯域幅のソリューションとしては適していません。
OpenShift Container Platform の Pod 間のマルチキャストトラフィックはデフォルトで無効にされます。OpenShift SDN デフォルト Container Network Interface (CNI) ネットワークプロバイダーを使用している場合、プロジェクトごとにマルチキャストを有効にできます。
networkpolicy 分離モードで OpenShift SDN ネットワークプラグインを使用する場合は、以下を行います。
-
Pod によって送信されるマルチキャストパケットは、
NetworkPolicyオブジェクトに関係なく、プロジェクトの他のすべての Pod に送信されます。Pod はユニキャストで通信できない場合でもマルチキャストで通信できます。 -
1 つのプロジェクトの Pod によって送信されるマルチキャストパケットは、
NetworkPolicyオブジェクトがプロジェクト間の通信を許可する場合であっても、それ以外のプロジェクトの Pod に送信されることはありません。
multinenant 分離モードで OpenShift SDN ネットワークプラグインを使用する場合は、以下を行います。
- Pod で送信されるマルチキャストパケットはプロジェクトにあるその他の全 Pod に送信されます。
- あるプロジェクトの Pod によって送信されるマルチキャストパケットは、各プロジェクトが結合し、マルチキャストが結合した各プロジェクトで有効にされている場合にのみ、他のプロジェクトの Pod に送信されます。
14.12.2. Pod 間のマルチキャストの有効化
プロジェクトの Pod でマルチキャストを有効にすることができます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-adminロールを持つユーザーとしてクラスターにログインする必要があります。
手順
以下のコマンドを実行し、プロジェクトのマルチキャストを有効にします。
<namespace>を、マルチキャストを有効にする必要のある namespace に置き換えます。$ oc annotate netnamespace <namespace> \ netnamespace.network.openshift.io/multicast-enabled=true
検証
マルチキャストがプロジェクトについて有効にされていることを確認するには、以下の手順を実行します。
現在のプロジェクトを、マルチキャストを有効にしたプロジェクトに切り替えます。
<project>をプロジェクト名に置き換えます。$ oc project <project>マルチキャストレシーバーとして機能する Pod を作成します。
$ cat <<EOF| oc create -f - apiVersion: v1 kind: Pod metadata: name: mlistener labels: app: multicast-verify spec: containers: - name: mlistener image: registry.access.redhat.com/ubi8 command: ["/bin/sh", "-c"] args: ["dnf -y install socat hostname && sleep inf"] ports: - containerPort: 30102 name: mlistener protocol: UDP EOFマルチキャストセンダーとして機能する Pod を作成します。
$ cat <<EOF| oc create -f - apiVersion: v1 kind: Pod metadata: name: msender labels: app: multicast-verify spec: containers: - name: msender image: registry.access.redhat.com/ubi8 command: ["/bin/sh", "-c"] args: ["dnf -y install socat && sleep inf"] EOF新しいターミナルウィンドウまたはタブで、マルチキャストリスナーを起動します。
Pod の IP アドレスを取得します。
$ POD_IP=$(oc get pods mlistener -o jsonpath='{.status.podIP}')次のコマンドを入力して、マルチキャストリスナーを起動します。
$ oc exec mlistener -i -t -- \ socat UDP4-RECVFROM:30102,ip-add-membership=224.1.0.1:$POD_IP,fork EXEC:hostname
マルチキャストトランスミッターを開始します。
Pod ネットワーク IP アドレス範囲を取得します。
$ CIDR=$(oc get Network.config.openshift.io cluster \ -o jsonpath='{.status.clusterNetwork[0].cidr}')マルチキャストメッセージを送信するには、以下のコマンドを入力します。
$ oc exec msender -i -t -- \ /bin/bash -c "echo | socat STDIO UDP4-DATAGRAM:224.1.0.1:30102,range=$CIDR,ip-multicast-ttl=64"マルチキャストが機能している場合、直前のコマンドは以下の出力を返します。
mlistener
14.13. プロジェクトのマルチキャストの無効化
14.13.1. Pod 間のマルチキャストの無効化
プロジェクトの Pod でマルチキャストを無効にすることができます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-adminロールを持つユーザーとしてクラスターにログインする必要があります。
手順
以下のコマンドを実行して、マルチキャストを無効にします。
$ oc annotate netnamespace <namespace> \1 netnamespace.network.openshift.io/multicast-enabled-- 1
- マルチキャストを無効にする必要のあるプロジェクトの
namespace。
14.14. OpenShift SDN を使用したネットワーク分離の設定
クラスターが OpenShift SDN CNI プラグインのマルチテナント分離モードを使用するように設定されている場合、各プロジェクトはデフォルトで分離されます。ネットワークトラフィックは、マルチテナント分離モードでは、異なるプロジェクトの Pod およびサービス間で許可されません。
プロジェクトのマルチテナント分離の動作を 2 つの方法で変更することができます。
- 1 つ以上のプロジェクトを結合し、複数の異なるプロジェクトの Pod とサービス間のネットワークトラフィックを可能にします。
- プロジェクトのネットワーク分離を無効にできます。これはグローバルにアクセスできるようになり、他のすべてのプロジェクトの Pod およびサービスからのネットワークトラフィックを受け入れます。グローバルにアクセス可能なプロジェクトは、他のすべてのプロジェクトの Pod およびサービスにアクセスできます。
14.14.1. 前提条件
- クラスターは、マルチテナント分離ノードで OpenShift SDN Container Network Interface (CNI) プラグインを使用するように設定されている必要があります。
14.14.2. プロジェクトの結合
2 つ以上のプロジェクトを結合し、複数の異なるプロジェクトの Pod とサービス間のネットワークトラフィックを可能にします。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-adminロールを持つユーザーとしてクラスターにログインする必要があります。
手順
以下のコマンドを使用して、プロジェクトを既存のプロジェクトネットワークに参加させます。
$ oc adm pod-network join-projects --to=<project1> <project2> <project3>または、特定のプロジェクト名を指定する代わりに
--selector=<project_selector>オプションを使用し、関連付けられたラベルに基づいてプロジェクトを指定できます。オプション: 以下のコマンドを実行し、結合した Pod ネットワークを表示します。
$ oc get netnamespaces同じ Pod ネットワークのプロジェクトには、NETID 列に同じネットワーク ID があります。
14.14.3. プロジェクトの分離
他のプロジェクトの Pod およびサービスがその Pod およびサービスにアクセスできないようにするためにプロジェクトを分離することができます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-adminロールを持つユーザーとしてクラスターにログインする必要があります。
手順
クラスターのプロジェクトを分離するには、以下のコマンドを実行します。
$ oc adm pod-network isolate-projects <project1> <project2>または、特定のプロジェクト名を指定する代わりに
--selector=<project_selector>オプションを使用し、関連付けられたラベルに基づいてプロジェクトを指定できます。
14.14.4. プロジェクトのネットワーク分離の無効化
プロジェクトのネットワーク分離を無効にできます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-adminロールを持つユーザーとしてクラスターにログインする必要があります。
手順
プロジェクトの以下のコマンドを実行します。
$ oc adm pod-network make-projects-global <project1> <project2>または、特定のプロジェクト名を指定する代わりに
--selector=<project_selector>オプションを使用し、関連付けられたラベルに基づいてプロジェクトを指定できます。
14.15. kube-proxy の設定
Kubernetes メットワークプロキシー (kube-proxy) は各ノードで実行され、Cluster Network Operator (CNO) で管理されます。kube-proxy は、サービスに関連付けられたエンドポイントの接続を転送するためのネットワークルールを維持します。
14.15.1. iptables ルールの同期について
同期の期間は、Kubernetes ネットワークプロキシー (kube-proxy) がノードで iptables ルールを同期する頻度を定めます。
同期は、以下のイベントのいずれかが生じる場合に開始します。
- サービスまたはエンドポイントのクラスターへの追加、またはクラスターからの削除などのイベントが発生する。
- 最後の同期以後の時間が kube-proxy に定義される同期期間を超過している。
14.15.2. kube-proxy 設定パラメーター
以下の kubeProxyConfig パラメーターを変更することができます。
OpenShift Container Platform 4.3 以降で強化されたパフォーマンスの向上により、iptablesSyncPeriod パラメーターを調整する必要はなくなりました。
| パラメーター | 説明 | 値 | デフォルト |
|---|---|---|---|
|
|
|
|
|
|
|
|
|
|
14.15.3. kube-proxy 設定の変化
クラスターの Kubernetes ネットワークプロキシー設定を変更することができます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-adminロールで実行中のクラスターにログインします。
手順
以下のコマンドを実行して、
Network.operator.openshift.ioカスタムリソース (CR) を編集します。$ oc edit network.operator.openshift.io cluster以下のサンプル CR のように、kube-proxy 設定への変更内容で、CR の
kubeProxyConfigパラメーターを変更します。apiVersion: operator.openshift.io/v1 kind: Network metadata: name: cluster spec: kubeProxyConfig: iptablesSyncPeriod: 30s proxyArguments: iptables-min-sync-period: ["30s"]ファイルを保存し、テキストエディターを編集します。
構文は、ファイルを保存し、エディターを終了する際に
ocコマンドによって検証されます。変更内容に構文エラーが含まれる場合、エディターはファイルを開き、エラーメッセージを表示します。以下のコマンドを実行して、設定の更新を確認します。
$ oc get networks.operator.openshift.io -o yaml出力例
apiVersion: v1 items: - apiVersion: operator.openshift.io/v1 kind: Network metadata: name: cluster spec: clusterNetwork: - cidr: 10.128.0.0/14 hostPrefix: 23 defaultNetwork: type: OpenShiftSDN kubeProxyConfig: iptablesSyncPeriod: 30s proxyArguments: iptables-min-sync-period: - 30s serviceNetwork: - 172.30.0.0/16 status: {} kind: Listオプション: 以下のコマンドを実行し、Cluster Network Operator が設定変更を受け入れていることを確認します。
$ oc get clusteroperator network出力例
NAME VERSION AVAILABLE PROGRESSING DEGRADED SINCE network 4.1.0-0.9 True False False 1m設定の更新が正常に適用されると、
AVAILABLEフィールドがTrueになります。
第15章 OVN-Kubernetes デフォルト CNI ネットワークプロバイダー
15.1. OVN-Kubernetes デフォルト Container Network Interface (CNI) ネットワークプロバイダーについて
OpenShift Container Platform クラスターは、Pod およびサービスネットワークに仮想化ネットワークを使用します。OVN-Kubernetes Container Network Interface (CNI) プラグインは、デフォルトのクラスターネットワークのネットワークプロバイダーです。OVN-Kubernetes は Open Virtual Network (OVN) をベースとしており、オーバーレイベースのネットワーク実装を提供します。OVN-Kubernetes ネットワークプロバイダーを使用するクラスターは、各ノードで Open vSwitch (OVS) も実行します。OVN は、宣言ネットワーク設定を実装するように各ノードで OVS を設定します。
15.1.1. OVN-Kubernetes の機能
OVN-Kubernetes Container Network Interface (CNI) クラスターネットワークプロバイダーは、以下の機能を実装します。
- Open Virtual Network (OVN) を使用してネットワークトラフィックフローを管理します。OVN はコミュニティーで開発され、ベンダーに依存しないネットワーク仮想化ソリューションです。
- ingress および egress ルールを含む Kubernetes ネットワークポリシーのサポートを実装します。
- ノード間にオーバーレイネットワークを作成するには、VXLAN ではなく GENEVE (Generic Network Virtualization Encapsulation) プロトコルを使用します。
15.1.2. サポートされるデフォルトの CNI ネットワークプロバイダー機能マトリクス
OpenShift Container Platform は、OpenShift SDN と OVN-Kubernetes の 2 つのサポート対象のオプションをデフォルトの Container Network Interface (CNI) ネットワークプロバイダーに提供します。以下の表は、両方のネットワークプロバイダーの現在の機能サポートをまとめたものです。
| 機能 | OVN-Kubernetes | OpenShift SDN |
|---|---|---|
| Egress IP | サポート対象 | サポート対象 |
| Egress ファイアウォール [1] | サポート対象 | サポート対象 |
| Egress ルーター | 一部サポート対象 [3] | サポート対象 |
| IPsec 暗号化 | サポート対象 | サポート対象外 |
| Kubernetes ネットワークポリシー | サポート対象 | 一部サポート対象 [2] |
| Multicast | サポート対象 | サポート対象 |
- egress ファイアウォールは、OpenShift SDN では egress ネットワークポリシーとしても知られています。これはネットワークポリシーの egress とは異なります。
-
OpenShift SDN のネットワークポリシーは、egress ルールおよび一部の
ipBlockルールをサポートしません。 - OVN-Kubernetes の egress ルーターはリダイレクトモードのみをサポートします。
15.1.3. OVN-Kubernetes の制限
OVN-Kubernetes Container Network Interface(CNI) クラスターネットワークプロバイダーには、トラフィックポリシーに関連する制限があります。ネットワークプロバイダーは、Kubernetes サービスの外部トラフィックポリシーまたは内部トラフィックポリシーを local に設定することをサポートしません。デフォルト値は cluster で、両方のパラメーターでサポートされます。この制限は、LoadBalancer タイプ、NodePort タイプのサービスを追加するか、外部 IP でサービスを追加する際に影響を受ける可能性があります。
15.2. OpenShift SDN クラスターネットワークプロバイダーからの移行
クラスター管理者は、OpenShift SDN CNI クラスターネットワークプロバイダーから OVN-Kubernetes Container Network Interface(CNI) クラスターネットワークプロバイダーに移行できます。
OVN-Kubernetes についての詳細は、OVN-Kubernetes ネットワークプロバイダーについて を参照してください。
15.2.1. OVN-Kubernetes ネットワークプロバイダーへの移行
OVN-Kubernetes Container Network Interface (CNI) クラスターネットワークプロバイダーへの移行は、クラスターに到達できなくなるダウンタイムも含まれる手動プロセスです。ロールバック手順が提供されますが、移行は一方向プロセスとなることが意図されています。
OVN-Kubernetes クラスターネットワークプロバイダーへの移行は、以下のプラットフォームのインストーラーでプロビジョニングされるクラスターでサポートされます。
- ベアメタルハードウェア
- Amazon Web Services (AWS)
- Google Cloud Platform (GCP)
- Microsoft Azure
- Red Hat OpenStack Platform (RHOSP)
- VMware vSphere
ユーザーによってプロビジョニングされるクラスターでの移行の実行はサポートされていません。
15.2.1.1. OVN-Kubernetes ネットワークプロバイダーへの移行についての考慮点
ノードに割り当てられたサブネット、および個々の Pod に割り当てられた IP アドレスは、移行時に保持されません。
OVN-Kubernetes ネットワークプロバイダーは OpenShift SDN ネットワークプロバイダーに存在する多くの機能を実装しますが、設定は同じではありません。
クラスターが以下の OpenShift SDN 機能のいずれかを使用する場合、OVN-Kubernetes で同じ機能を手動で設定する必要があります。
- namespace の分離
- Egress IP アドレス
- Egress ネットワークポリシー
- Egress ルーター Pod
- マルチキャスト
-
クラスターが
100.64.0.0/16IP アドレス範囲の一部を使用する場合、この IP アドレス範囲は内部で使用されるため、OVN-Kubernetes に移行することはできません。
以下のセクションでは、OVN-Kubernetes と OpenShift SDN の上記の機能間の設定の違いについて説明します。
namespace の分離
OVN-Kubernetes はネットワークポリシーの分離モードのみをサポートします。
クラスターがマルチテナントまたはサブネットの分離モードのいずれかで設定された OpenShift SDN を使用する場合、OVN-Kubernetes ネットワークプロバイダーに移行することはできません。
Egress IP アドレス
OVN-Kubernetes と OpenShift SDN との間に egress IP アドレスを設定する際の相違点は、以下の表で説明されています。
| OVN-Kubernetes | OpenShift SDN |
|---|---|
|
|
OVN-Kubernetes で egress IP アドレスを使用する方法についての詳細は、egress IP アドレスの設定について参照してください。
Egress ネットワークポリシー
OVN-Kubernetes と OpenShift SDN との間に egress ファイアウォールとしても知られる egress ネットワークポリシーの設定についての相違点は、以下の表に記載されています。
| OVN-Kubernetes | OpenShift SDN |
|---|---|
|
|
OVN-Kubernetes で egress ファイアウォールを使用する方法についての詳細は、プロジェクトの egress ファイアウォールの設定について参照してください。
Egress ルーター Pod
OVN-Kubernetes は、OpenShift Container Platform 4.7 での egress ルーター Pod の使用をサポートしません。
マルチキャスト
OVN-Kubernetes と OpenShift SDN でマルチキャストトラフィックを有効にする方法についての相違点は、以下の表で説明されています。
| OVN-Kubernetes | OpenShift SDN |
|---|---|
|
|
OVN-Kubernetes でのマルチキャストの使用についての詳細は、プロジェクトのマルチキャストの有効化を参照してください。
ネットワークポリシー
OVN-Kubernetes は、networking.k8s.io/v1 API グループで Kubernetes NetworkPolicy API を完全にサポートします。OpenShift SDN から移行する際に、ネットワークポリシーで変更を加える必要はありません。
15.2.1.2. 移行プロセスの仕組み
移行プロセスは以下のように動作します。
-
Cluster Network Operator (CNO) 設定オブジェクトに設定された一時的なアノテーションを設定します。このアノテーションは CNO をトリガーして、
defaultNetworkフィールドへの変更の有無を監視します。 - Machine Config Operator (MCO) を一時停止し、移行が中断されないようにします。
-
defaultNetworkフィールドを更新します。更新により、CNO は OpenShift SDN コントロールプレーン Pod を破棄し、OVN-Kubernetes コントロールプレーン Pod をデプロイします。さらに、新しいクラスターネットワークプロバイダーを反映するように Multus オブジェクトを更新します。 - クラスターの各ノードを再起動します。クラスターの既存 Pod はクラスターネットワークプロバイダーへの変更を認識しないため、各ノードを再起動すると、各ノードに Pod がドレイン (解放) されるようになります。新規 Pod は OVN-Kubernetes が提供する新規クラスターネットワークに割り当てられます。
- クラスターのすべてのノードが再起動した後に MCO を有効にします。MCO は移行の完了に必要な systemd 設定への更新をロールアウトします。MCO は、デフォルトでプールごとに一度に 1 つのマシンを更新するため、移行にかかる合計時間がクラスターのサイズと共に増加します。
15.2.2. OVN-Kubernetes デフォルト CNI ネットワークプロバイダーへの移行
クラスター管理者は、クラスターのデフォルトの Container Network Interface (CNI) ネットワークプロバイダーを OVN-Kubernetes に変更できます。移行時に、クラスター内のすべてのノードを再起動する必要があります。
移行の実行中はクラスターを利用できず、ワークロードが中断される可能性があります。サービスの中断が許容可能な場合にのみ移行を実行します。
前提条件
- インストーラーでプロビジョニングされるインフラストラクチャーにインストールされ、ネットワークポリシーの分離モードで OpenShift SDN デフォルト CNI ネットワークプロバイダーで設定されたクラスター。
-
OpenShift CLI (
oc) をインストールします。 -
cluster-adminロールを持つユーザーとしてクラスターにアクセスできる。 - etcd データベースの最新のバックアップが利用可能である。
- クラスターは既知の正常な状態にあり、エラーがないこと。
- 再起動は、ノードごとに手動でトリガーできます。
手順
クラスターネットワークの設定のバックアップを作成するには、以下のコマンドを入力します。
$ oc get Network.config.openshift.io cluster -o yaml > cluster-openshift-sdn.yaml移行を有効にするには、以下のコマンドを入力して Cluster Network Operator 設定オブジェクトにアノテーションを設定します。
$ oc annotate Network.operator.openshift.io cluster \ 'networkoperator.openshift.io/network-migration'=""Machine Config Operator (MCO) によって管理されるすべてのマシン設定プールを停止します。
マスター設定プールを停止します。
$ oc patch MachineConfigPool master --type='merge' --patch \ '{ "spec": { "paused": true } }'ワーカー設定プールを停止します。
$ oc patch MachineConfigPool worker --type='merge' --patch \ '{ "spec":{ "paused" :true } }'
以下のコマンドのいずれかを使用して、OVN-Kubernetes クラスターネットワークプロバイダーを設定します。
クラスターネットワークの IP アドレスブロックを変更せずにネットワークプロバイダーを指定するには、以下のコマンドを入力します。
$ oc patch Network.config.openshift.io cluster \ --type='merge' --patch '{ "spec": { "networkType": "OVNKubernetes" } }'別のクラスターネットワーク IP アドレスブロックを指定するには、以下のコマンドを入力します。
$ oc patch Network.config.openshift.io cluster \ --type='merge' --patch '{ "spec": { "clusterNetwork": [ { "cidr": "<cidr>", "hostPrefix": "<prefix>" } ], "networkType": "OVNKubernetes" } }'ここで、
cidrは CIDR ブロックであり、prefixはクラスター内の各ノードに割り当てられる CIDR ブロックのスライスです。OVN-Kubernetes ネットワークプロバイダーはこのブロックを内部で使用するため、100.64.0.0/16CIDR ブロックと重複する CIDR ブロックは使用できません。重要移行時に、サービスネットワークのアドレスブロックを変更することはできません。
オプション: ネットワークインフラストラクチャーの要件を満たすように OVN-Kubernetes の以下の設定をカスタマイズできます。
- Maximum transmission unit (MTU)
- Geneve (Generic Network Virtualization Encapsulation) オーバーレイネットワークポート
以前の設定のいずれかをカスタマイズするには、以下のコマンドを入力してカスタマイズします。デフォルト値を変更する必要がない場合は、パッチのキーを省略します。
$ oc patch Network.operator.openshift.io cluster --type=merge \
--patch '{
"spec":{
"defaultNetwork":{
"ovnKubernetesConfig":{
"mtu":<mtu>,
"genevePort":<port>
}}}}'+
mtu-
Geneve オーバーレイネットワークの MTU。この値は通常は自動的に設定されますが、クラスターにあるノードすべてが同じ MTU を使用しない場合、これを最小のノード MTU 値よりも
100小さく設定する必要があります。 port-
Geneve オーバーレイネットワークの UDP ポート。値が指定されない場合、デフォルトは
6081になります。ポートは、OpenShift SDN で使用される VXLAN ポートと同じにすることはできません。VXLAN ポートのデフォルト値は4789です。
+ mtu フィールドを更新するパッチコマンドの例
$ oc patch Network.operator.openshift.io cluster --type=merge \
--patch '{
"spec":{
"defaultNetwork":{
"ovnKubernetesConfig":{
"mtu":1200
}}}}'Multus デーモンセットのロールアウトが完了するまで待機します。
$ oc -n openshift-multus rollout status daemonset/multusMultus Pod の名前の形式は
multus-<xxxxx>です。ここで、<xxxxx>は文字のランダムなシーケンスになります。Pod が再起動するまでにしばらく時間がかかる可能性があります。出力例
Waiting for daemon set "multus" rollout to finish: 1 out of 6 new pods have been updated... ... Waiting for daemon set "multus" rollout to finish: 5 of 6 updated pods are available... daemon set "multus" successfully rolled out移行を完了するには、クラスター内の各ノードを再起動します。たとえば、以下のような bash スクリプトを使用できます。このスクリプトは、
sshを使用して各ホストに接続でき、sudoがパスワードを要求しないように設定されていることを前提としています。#!/bin/bash for ip in $(oc get nodes -o jsonpath='{.items[*].status.addresses[?(@.type=="InternalIP")].address}') do echo "reboot node $ip" ssh -o StrictHostKeyChecking=no core@$ip sudo shutdown -r -t 3 donessh アクセスが使用できない場合、インフラストラクチャープロバイダーの管理ポータルから各ノードを再起動できる場合があります。
クラスターのノードが再起動したら、すべてのマシン設定プールを起動します。
マスター設定プールを開始します。
$ oc patch MachineConfigPool master --type='merge' --patch \ '{ "spec": { "paused": false } }'ワーカー設定プールを開始します。
$ oc patch MachineConfigPool worker --type='merge' --patch \ '{ "spec": { "paused": false } }'
MCO が各設定プールのマシンを更新すると、各ノードを再起動します。
デフォルトで、MCO は一度にプールごとに単一のマシンを更新するため、移行が完了するまでに必要な時間がクラスターのサイズと共に増加します。
ホスト上の新規マシン設定のステータスを確認します。
マシン設定の状態と適用されたマシン設定の名前を一覧表示するには、以下のコマンドを入力します。
$ oc describe node | egrep "hostname|machineconfig"出力例
kubernetes.io/hostname=master-0 machineconfiguration.openshift.io/currentConfig: rendered-master-c53e221d9d24e1c8bb6ee89dd3d8ad7b machineconfiguration.openshift.io/desiredConfig: rendered-master-c53e221d9d24e1c8bb6ee89dd3d8ad7b machineconfiguration.openshift.io/reason: machineconfiguration.openshift.io/state: Done以下のステートメントが true であることを確認します。
-
machineconfiguration.openshift.io/stateフィールドの値はDoneです。 -
machineconfiguration.openshift.io/currentConfigフィールドの値は、machineconfiguration.openshift.io/desiredConfigフィールドの値と等しくなります。
-
マシン設定が正しいことを確認するには、以下のコマンドを入力します。
$ oc get machineconfig <config_name> -o yaml | grep ExecStartここで、
<config_name>は、machineconfiguration.openshift.io/currentConfigフィールドのマシン設定の名前になります。マシン設定には、systemd 設定に以下の更新を含める必要があります。
ExecStart=/usr/local/bin/configure-ovs.sh OVNKubernetes
移行が正常に完了したことを確認します。
デフォルトの CNI ネットワークプロバイダーが OVN-Kubernetes であることを確認するには、以下のコマンドを入力します。
status.networkTypeの値はOVNKubernetesである必要があります。$ oc get network.config/cluster -o jsonpath='{.status.networkType}{"\n"}'クラスターノードが
Ready状態にあることを確認するには、以下のコマンドを実行します。$ oc get nodesノードが
NotReady状態のままになっている場合、マシン設定デーモン Pod のログを調べ、エラーを解決します。Pod を一覧表示するには、以下のコマンドを入力します。
$ oc get pod -n openshift-machine-config-operator出力例
NAME READY STATUS RESTARTS AGE machine-config-controller-75f756f89d-sjp8b 1/1 Running 0 37m machine-config-daemon-5cf4b 2/2 Running 0 43h machine-config-daemon-7wzcd 2/2 Running 0 43h machine-config-daemon-fc946 2/2 Running 0 43h machine-config-daemon-g2v28 2/2 Running 0 43h machine-config-daemon-gcl4f 2/2 Running 0 43h machine-config-daemon-l5tnv 2/2 Running 0 43h machine-config-operator-79d9c55d5-hth92 1/1 Running 0 37m machine-config-server-bsc8h 1/1 Running 0 43h machine-config-server-hklrm 1/1 Running 0 43h machine-config-server-k9rtx 1/1 Running 0 43h設定デーモン Pod の名前は以下の形式になります。
machine-config-daemon-<seq><seq>値は、ランダムな 5 文字の英数字シーケンスになります。以下のコマンドを入力して、直前の出力に表示される最初のマシン設定デーモン Pod の Pod ログを表示します。
$ oc logs <pod> -n openshift-machine-config-operatorここで、
podはマシン設定デーモン Pod の名前になります。- 直前のコマンドの出力で示されるログ内のエラーを解決します。
Pod がエラー状態ではないことを確認するには、以下のコマンドを入力します。
$ oc get pods --all-namespaces -o wide --sort-by='{.spec.nodeName}'ノードの Pod がエラー状態にある場合は、そのノードを再起動します。
以下の手順は、移行に成功し、クラスターの状態が正常である場合にのみ実行します。
Cluster Network Operator 設定オブジェクトから移行アノテーションを削除するには、以下のコマンドを入力します。
$ oc annotate Network.operator.openshift.io cluster \ networkoperator.openshift.io/network-migration-OpenShift SDN ネットワークプロバイダー namespace を削除するには、以下のコマンドを入力します。
$ oc delete namespace openshift-sdn
15.3. OpenShift SDN ネットワークプロバイダーへのロールバック
クラスター管理者は、OVN-Kubernetes CNI クラスターのネットワークプロバイダーから OpenShift SDN クラスターの Container Network Interface (CNI) クラスターネットワークプロバイダーにロールバックできます (OVN-Kubernetes への移行に失敗した場合)。
15.3.1. デフォルトの CNI ネットワークプロバイダーの OpenShift SDN へのロールバック
クラスター管理者は、クラスターを OpenShift SDN デフォルト Container Network Interface (CNI) ネットワークプロバイダーにロールバックできます。ロールバック時に、クラスター内のすべてのノードを再起動する必要があります。
OVN-Kubernetes への移行に失敗した場合にのみ OpenShift SDN にロールバックします。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-adminロールを持つユーザーとしてのクラスターへのアクセス。 - OVN-Kubernetes デフォルト CNI ネットワークプロバイダーで設定されたインフラストラクチャーにクラスターがインストールされている。
手順
移行を有効にするには、以下のコマンドを入力して Cluster Network Operator 設定オブジェクトにアノテーションを設定します。
$ oc annotate Network.operator.openshift.io cluster \ 'networkoperator.openshift.io/network-migration'=""Machine Config Operator (MCO) によって管理されるすべてのマシン設定プールを停止します。
マスター設定プールを停止します。
$ oc patch MachineConfigPool master --type='merge' --patch \ '{ "spec": { "paused": true } }'ワーカー設定プールを停止します。
$ oc patch MachineConfigPool worker --type='merge' --patch \ '{ "spec":{ "paused" :true } }'
OpenShift SDN ネットワークプロバイダーを設定するには、以下のコマンドを入力します。
$ oc patch Network.config.openshift.io cluster \ --type='merge' --patch '{ "spec": { "networkType": "OpenShiftSDN" } }'オプション: ネットワークインフラストラクチャーの要件を満たすように OpenShift SDN の以下の設定をカスタマイズできます。
- Maximum transmission unit (MTU)
- VXLAN ポート
以前の設定のいずれかを両方をカスタマイズするには、カスタマイズし、以下のコマンドを入力します。デフォルト値を変更する必要がない場合は、パッチのキーを省略します。
$ oc patch Network.operator.openshift.io cluster --type=merge \ --patch '{ "spec":{ "defaultNetwork":{ "openshiftSDNConfig":{ "mtu":<mtu>, "vxlanPort":<port> }}}}'mtu-
VXLAN オーバーレイネットワークの MTU。この値は通常は自動的に設定されますが、クラスターにあるノードすべてが同じ MTU を使用しない場合、これを最小のノード MTU 値よりも
50小さく設定する必要があります。 port-
VXLAN オーバーレイネットワークの UDP ポート。値が指定されない場合は、デフォルトは
4789になります。ポートは OVN-Kubernetes で使用される Geneve ポートと同じにすることはできません。Geneve ポートのデフォルト値は6081です。
patch コマンドの例
$ oc patch Network.operator.openshift.io cluster --type=merge \ --patch '{ "spec":{ "defaultNetwork":{ "openshiftSDNConfig":{ "mtu":1200 }}}}'Multus デーモンセットのロールアウトが完了するまで待機します。
$ oc -n openshift-multus rollout status daemonset/multusMultus Pod の名前の形式は
multus-<xxxxx>です。ここで、<xxxxx>は文字のランダムなシーケンスになります。Pod が再起動するまでにしばらく時間がかかる可能性があります。出力例
Waiting for daemon set "multus" rollout to finish: 1 out of 6 new pods have been updated... ... Waiting for daemon set "multus" rollout to finish: 5 of 6 updated pods are available... daemon set "multus" successfully rolled outロールバックを完了するには、クラスター内の各ノードを再起動します。たとえば、以下のような bash スクリプトを使用できます。このスクリプトは、
sshを使用して各ホストに接続でき、sudoがパスワードを要求しないように設定されていることを前提としています。#!/bin/bash for ip in $(oc get nodes -o jsonpath='{.items[*].status.addresses[?(@.type=="InternalIP")].address}') do echo "reboot node $ip" ssh -o StrictHostKeyChecking=no core@$ip sudo shutdown -r -t 3 donessh アクセスが使用できない場合、インフラストラクチャープロバイダーの管理ポータルから各ノードを再起動できる場合があります。
クラスターのノードが再起動したら、すべてのマシン設定プールを起動します。
マスター設定プールを開始します。
$ oc patch MachineConfigPool master --type='merge' --patch \ '{ "spec": { "paused": false } }'ワーカー設定プールを開始します。
$ oc patch MachineConfigPool worker --type='merge' --patch \ '{ "spec": { "paused": false } }'
MCO が各設定プールのマシンを更新すると、各ノードを再起動します。
デフォルトで、MCO は一度にプールごとに単一のマシンを更新するため、移行が完了するまでに必要な時間がクラスターのサイズと共に増加します。
ホスト上の新規マシン設定のステータスを確認します。
マシン設定の状態と適用されたマシン設定の名前を一覧表示するには、以下のコマンドを入力します。
$ oc describe node | egrep "hostname|machineconfig"出力例
kubernetes.io/hostname=master-0 machineconfiguration.openshift.io/currentConfig: rendered-master-c53e221d9d24e1c8bb6ee89dd3d8ad7b machineconfiguration.openshift.io/desiredConfig: rendered-master-c53e221d9d24e1c8bb6ee89dd3d8ad7b machineconfiguration.openshift.io/reason: machineconfiguration.openshift.io/state: Done以下のステートメントが true であることを確認します。
-
machineconfiguration.openshift.io/stateフィールドの値はDoneです。 -
machineconfiguration.openshift.io/currentConfigフィールドの値は、machineconfiguration.openshift.io/desiredConfigフィールドの値と等しくなります。
-
マシン設定が正しいことを確認するには、以下のコマンドを入力します。
$ oc get machineconfig <config_name> -o yamlここで、
<config_name>は、machineconfiguration.openshift.io/currentConfigフィールドのマシン設定の名前になります。
移行が正常に完了したことを確認します。
デフォルトの CNI ネットワークプロバイダーが OVN-Kubernetes であることを確認するには、以下のコマンドを入力します。
status.networkTypeの値はOpenShiftSDNである必要があります。$ oc get network.config/cluster -o jsonpath='{.status.networkType}{"\n"}'クラスターノードが
Ready状態にあることを確認するには、以下のコマンドを実行します。$ oc get nodesノードが
NotReady状態のままになっている場合、マシン設定デーモン Pod のログを調べ、エラーを解決します。Pod を一覧表示するには、以下のコマンドを入力します。
$ oc get pod -n openshift-machine-config-operator出力例
NAME READY STATUS RESTARTS AGE machine-config-controller-75f756f89d-sjp8b 1/1 Running 0 37m machine-config-daemon-5cf4b 2/2 Running 0 43h machine-config-daemon-7wzcd 2/2 Running 0 43h machine-config-daemon-fc946 2/2 Running 0 43h machine-config-daemon-g2v28 2/2 Running 0 43h machine-config-daemon-gcl4f 2/2 Running 0 43h machine-config-daemon-l5tnv 2/2 Running 0 43h machine-config-operator-79d9c55d5-hth92 1/1 Running 0 37m machine-config-server-bsc8h 1/1 Running 0 43h machine-config-server-hklrm 1/1 Running 0 43h machine-config-server-k9rtx 1/1 Running 0 43h設定デーモン Pod の名前は以下の形式になります。
machine-config-daemon-<seq><seq>値は、ランダムな 5 文字の英数字シーケンスになります。直前の出力に表示されるそれぞれのマシン設定デーモン Pod の Pod ログを表示するには、以下のコマンドを入力します。
$ oc logs <pod> -n openshift-machine-config-operatorここで、
podはマシン設定デーモン Pod の名前になります。- 直前のコマンドの出力で示されるログ内のエラーを解決します。
Pod がエラー状態ではないことを確認するには、以下のコマンドを入力します。
$ oc get pods --all-namespaces -o wide --sort-by='{.spec.nodeName}'ノードの Pod がエラー状態にある場合は、そのノードを再起動します。
以下の手順は、移行に成功し、クラスターの状態が正常である場合にのみ実行します。
Cluster Network Operator 設定オブジェクトから移行アノテーションを削除するには、以下のコマンドを入力します。
$ oc annotate Network.operator.openshift.io cluster \ networkoperator.openshift.io/network-migration-OVN-Kubernetes ネットワークプロバイダー namespace を削除するには、以下のコマンドを入力します。
$ oc delete namespace openshift-ovn-kubernetes
15.4. IPsec 暗号化の設定
IPsec を有効にすると、OVN-Kubernetes Container Network Interface (CNI) クラスターネットワーク上のノード間のすべてのネットワークトラフィックは暗号化されたトンネルを通過します。
IPsec はデフォルトで無効にされています。
IPsec 暗号化はクラスターのインストール時にのみ有効にでき、有効にした後は無効にすることはできません。インストールのドキュメントについては、 クラスターインストール方法の選択およびその使用に向けた準備 について参照してください。
15.4.1. IPsec で暗号化したネットワークトラフィックフローのタイプ
IPsec を有効にすると、Pod 間の以下のネットワークトラフィックフローのみが暗号化されます。
- クラスターネットワーク上の複数の異なるノードの Pod 間のトラフィック
- ホストネットワークの Pod からクラスターネットワーク上の Pod へのトラフィック
以下のトラフィックフローは暗号化されません。
- クラスターネットワーク上の同じノードの Pod 間のトラフィック
- ホストネットワーク上の Pod 間のトラフィック
- クラスターネットワークの Pod からホストネットワークの Pod へのトラフィック
暗号化されていないフローと暗号化されていないフローを以下の図に示します。
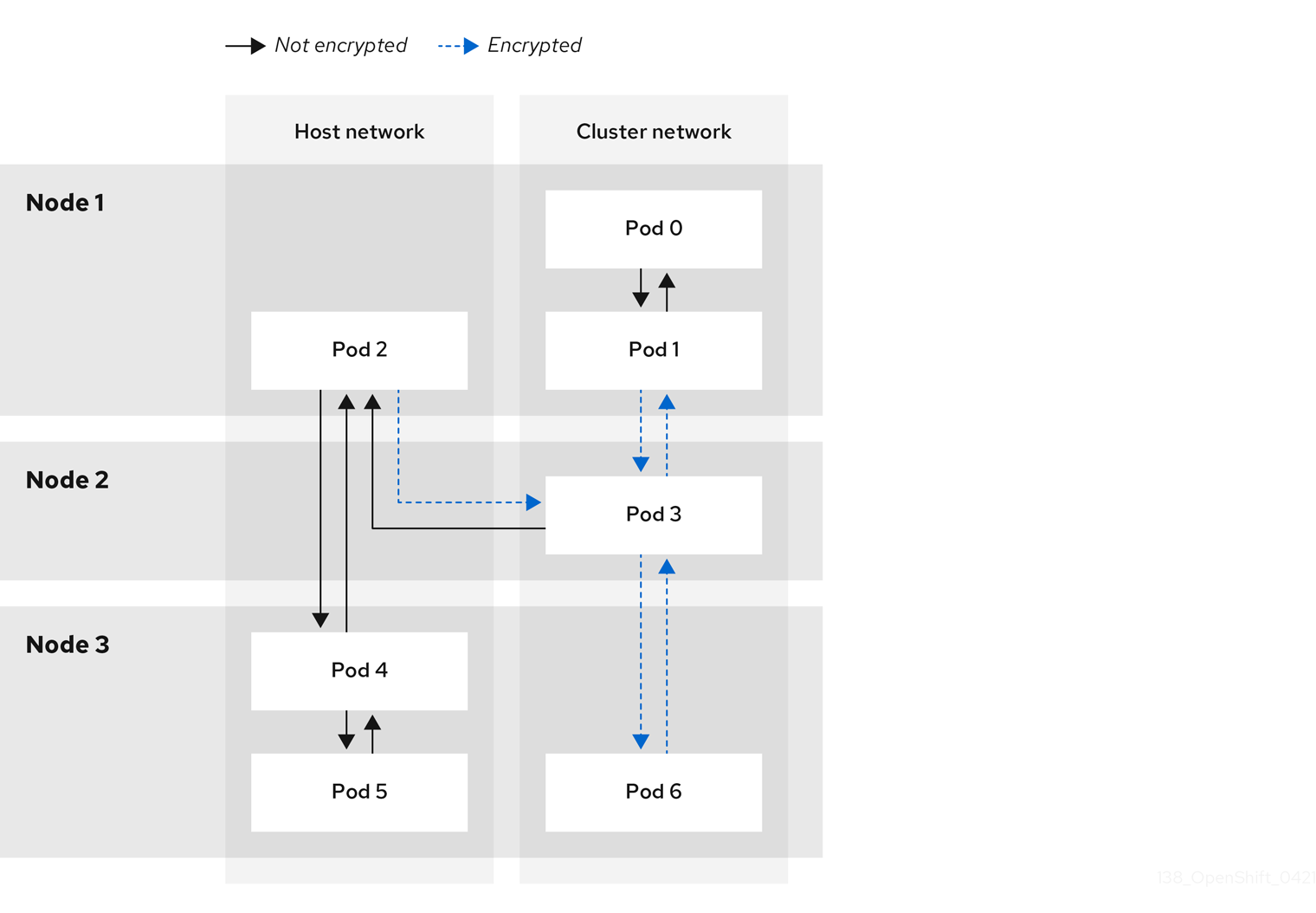
15.4.2. IPsec の暗号化プロトコルおよびトンネルモード
使用する暗号化は AES-GCM-16-256 です。整合性チェック値 (ICV) は 16 バイトです。鍵の長さは 256 ビットです。
使用する IPsec トンネルモードは、エンドツーエンドの通信を暗号化するモードである Transport モード です。
15.4.3. セキュリティー証明書の生成およびローテーション
Cluster Network Operator (CNO) は、暗号化用に IPsec によって使用される自己署名の X.509 認証局 (CA) を生成します。各ノードの証明書署名要求 (CSR) は、CNO によって自動的に満たされます。
この CA は 10 年間有効です。個別のノード証明書は 5 年間有効で、4 年半が経過すると自動的にローテーションされます。
15.5. プロジェクトの egress ファイアウォールの設定
クラスター管理者は、OpenShift Container Platform クラスター外に出るプロジェクトのプロジェクについて、egress トラフィックを制限する egress ファイアウォールを作成できます。
15.5.1. egress ファイアウォールのプロジェクトでの機能
クラスター管理者は、 egress ファイアウォール を使用して、一部またはすべての Pod がクラスター内からアクセスできる外部ホストを制限できます。egress ファイアウォールポリシーは以下のシナリオをサポートします。
- Pod の接続を内部ホストに制限し、パブリックインターネットへの接続を開始できないようにする。
- Pod の接続をパブリックインターネットに制限し、OpenShift Container Platform クラスター外にある内部ホストへの接続を開始できないようにする。
- Pod は OpenShift Container Platform クラスター外の指定された内部サブネットまたはホストにアクセスできません。
- Pod は特定の外部ホストにのみ接続することができます。
たとえば、指定された IP 範囲へのあるプロジェクトへのアクセスを許可する一方で、別のプロジェクトへの同じアクセスを拒否することができます。または、アプリケーション開発者の (Python) pip mirror からの更新を制限したり、更新を承認されたソースからの更新のみに強制的に制限したりすることができます。
EgressFirewall カスタムリソース (CR) オブジェクトを作成して egress ファイアウォールポリシーを設定します。egress ファイアウォールは、以下のいずれかの基準を満たすネットワークトラフィックと一致します。
- CIDR 形式の IP アドレス範囲。
- IP アドレスに解決する DNS 名
- ポート番号
- プロトコル。TCP、UDP、および SCTP のいずれかになります。
egress ファイアウォールに 0.0.0.0/0 の拒否ルールが含まれる場合、OpenShift Container Platform API サーバーへのアクセスはブロックされます。Pod が OpenShift Container Platform API サーバーへのアクセスを継続できるようにするには、以下の例にあるように API サーバーが egress ファイアウォールルールでリッスンする IP アドレス範囲を含める必要があります。
apiVersion: k8s.ovn.org/v1
kind: EgressFirewall
metadata:
name: default
namespace: <namespace>
spec:
egress:
- to:
cidrSelector: <api_server_address_range>
type: Allow
# ...
- to:
cidrSelector: 0.0.0.0/0
type: Deny
API サーバーの IP アドレスを見つけるには、oc get ep kubernetes -n default を実行します。
詳細は、BZ#1988324 を参照してください。
egress ファイアウォールルールは、ルーターを通過するトラフィックには適用されません。ルート CR オブジェクトを作成するパーミッションを持つユーザーは、禁止されている宛先を参照するルートを作成することにより、egress ファイアウォールポリシールールをバイパスできます。
15.5.1.1. egress ファイアウォールの制限
egress ファイアウォールには以下の制限があります。
- 複数の EgressFirewall オブジェクトを持つプロジェクトはありません。
- 最大 8,000 のルールを持つ最大 1 つの EgressFirewall オブジェクトはプロジェクトごとに定義できます。
上記の制限のいずれかに違反すると、プロジェクトの egress ファイアウォールに障害が発生し、すべての外部ネットワークトラフィックがドロップされる可能性があります。
egress ファイアウォールリソースは、kube-node-lease、kube-public、kube-system、openshift、openshift- プロジェクトで作成できます。
15.5.1.2. egress ポリシールールのマッチング順序
egress ファイアウォールポリシールールは、最初から最後へと定義された順序で評価されます。Pod からの egress 接続に一致する最初のルールが適用されます。この接続では、後続のルールは無視されます。
15.5.1.3. DNS (Domain Name Server) 解決の仕組み
egress ファイアウォールポリシールールのいずれかで DNS 名を使用する場合、ドメイン名の適切な解決には、以下の制限が適用されます。
- ドメイン名の更新は、ローカルの非権威サーバーのドメインの TTL (time to live) 値に基づいてポーリングされます。
- Pod は、必要に応じて同じローカルネームサーバーからドメインを解決する必要があります。そうしない場合、egress ファイアウォールコントローラーと Pod によって認識されるドメインの IP アドレスが異なる可能性があります。ホスト名の IP アドレスが異なる場合、egress ファイアウォールは一貫して実行されないことがあります。
- egress ファイアウォールコントローラーおよび Pod は同じローカルネームサーバーを非同期にポーリングするため、Pod は egress コントローラーが実行する前に更新された IP アドレスを取得する可能性があります。これにより、競合状態が生じます。この現時点の制限により、EgressFirewall オブジェクトのドメイン名の使用は、IP アドレスの変更が頻繁に生じないドメインの場合にのみ推奨されます。
egress ファイアウォールは、DNS 解決用に Pod が置かれるノードの外部インターフェイスに Pod が常にアクセスできるようにします。
ドメイン名を egress ファイアウォールで使用し、DNS 解決がローカルノード上の DNS サーバーによって処理されない場合は、Pod でドメイン名を使用している場合には DNS サーバーの IP アドレスへのアクセスを許可する egress ファイアウォールを追加する必要があります。
15.5.2. EgressFirewall カスタムリソース (CR) オブジェクト
egress ファイアウォールのルールを 1 つ以上定義できます。ルールは、ルールが適用されるトラフィックを指定して Allow ルールまたは Deny ルールのいずれかになります。
以下の YAML は EgressFirewall CR オブジェクトについて説明しています。
EgressFirewall オブジェクト
apiVersion: k8s.ovn.org/v1
kind: EgressFirewall
metadata:
name: <name>
spec:
egress:
...15.5.2.1. EgressFirewall ルール
以下の YAML は egress ファイアウォールルールオブジェクトについて説明しています。egress スタンザは、単一または複数のオブジェクトの配列を予想します。
Egress ポリシールールのスタンザ
egress:
- type: <type>
to:
cidrSelector: <cidr>
dnsName: <dns_name>
ports:
...ポートスタンザ
ports:
- port: <port>
protocol: <protocol> 15.5.2.2. EgressFirewall CR オブジェクトの例
以下の例では、複数の egress ファイアウォールポリシールールを定義します。
apiVersion: k8s.ovn.org/v1
kind: EgressFirewall
metadata:
name: default
spec:
egress:
- type: Allow
to:
cidrSelector: 1.2.3.0/24
- type: Deny
to:
cidrSelector: 0.0.0.0/0- 1
- egress ファイアウォールポリシールールオブジェクトのコレクション。
以下の例では、トラフィックが TCP プロトコルおよび宛先ポート 80 または任意のプロトコルと宛先ポート 443 のいずれかを使用している場合に、IP アドレス 172.16.1.1 でホストへのトラフィックを拒否するポリシールールを定義します。
apiVersion: k8s.ovn.org/v1
kind: EgressFirewall
metadata:
name: default
spec:
egress:
- type: Deny
to:
cidrSelector: 172.16.1.1
ports:
- port: 80
protocol: TCP
- port: 44315.5.3. egress ファイアウォールポリシーオブジェクトの作成
クラスター管理者は、プロジェクトの egress ファイアウォールポリシーオブジェクトを作成できます。
プロジェクトに EgressFirewall オブジェクトがすでに定義されている場合、既存のポリシーを編集して egress ファイアウォールルールを変更する必要があります。
前提条件
- OVN-Kubernetes デフォルト Container Network Interface (CNI) ネットワークプロバイダープラグインを使用するクラスター。
-
OpenShift CLI (
oc) をインストールしている。 - クラスター管理者としてクラスターにログインする必要があります。
手順
ポリシールールを作成します。
-
<policy_name>.yamlファイルを作成します。この場合、<policy_name>は egress ポリシールールを記述します。 - 作成したファイルで、egress ポリシーオブジェクトを定義します。
-
以下のコマンドを入力してポリシーオブジェクトを作成します。
<policy_name>をポリシーの名前に、<project>をルールが適用されるプロジェクトに置き換えます。$ oc create -f <policy_name>.yaml -n <project>以下の例では、新規の EgressFirewall オブジェクトが
project1という名前のプロジェクトに作成されます。$ oc create -f default.yaml -n project1出力例
egressfirewall.k8s.ovn.org/v1 created-
オプション: 後に変更できるように
<policy_name>.yamlファイルを保存します。
15.6. プロジェクトの egress ファイアウォールの表示
クラスター管理者は、既存の egress ファイアウォールの名前を一覧表示し、特定の egress ファイアウォールのトラフィックルールを表示できます。
15.6.1. EgressFirewall オブジェクトの表示
クラスターで EgressFirewall オブジェクトを表示できます。
前提条件
- OVN-Kubernetes デフォルト Container Network Interface (CNI) ネットワークプロバイダープラグインを使用するクラスター。
-
ocとして知られる OpenShift コマンドラインインターフェイス (CLI) のインストール。 - クラスターにログインすること。
手順
オプション: クラスターで定義された EgressFirewall オブジェクトの名前を表示するには、以下のコマンドを入力します。
$ oc get egressfirewall --all-namespacesポリシーを検査するには、以下のコマンドを入力します。
<policy_name>を検査するポリシーの名前に置き換えます。$ oc describe egressfirewall <policy_name>出力例
Name: default Namespace: project1 Created: 20 minutes ago Labels: <none> Annotations: <none> Rule: Allow to 1.2.3.0/24 Rule: Allow to www.example.com Rule: Deny to 0.0.0.0/0
15.7. プロジェクトの egress ファイアウォールの編集
クラスター管理者は、既存の egress ファイアウォールのネットワークトラフィックルールを変更できます。
15.7.1. EgressFirewall オブジェクトの編集
クラスター管理者は、プロジェクトの egress ファイアウォールを更新できます。
前提条件
- OVN-Kubernetes デフォルト Container Network Interface (CNI) ネットワークプロバイダープラグインを使用するクラスター。
-
OpenShift CLI (
oc) をインストールしている。 - クラスター管理者としてクラスターにログインする必要があります。
手順
プロジェクトの EgressFirewall オブジェクトの名前を検索します。
<project>をプロジェクトの名前に置き換えます。$ oc get -n <project> egressfirewallオプション: egress ネットワークファイアウォールの作成時に EgressFirewall オブジェクトのコピーを保存しなかった場合には、以下のコマンドを入力してコピーを作成します。
$ oc get -n <project> egressfirewall <name> -o yaml > <filename>.yaml<project>をプロジェクトの名前に置き換えます。<name>をオブジェクトの名前に置き換えます。<filename>をファイルの名前に置き換え、YAML を保存します。ポリシールールに変更を加えたら、以下のコマンドを実行して EgressFirewall オブジェクトを置き換えます。
<filename>を、更新された EgressFirewall オブジェクトを含むファイルの名前に置き換えます。$ oc replace -f <filename>.yaml
15.8. プロジェクトからの egress ファイアウォールの削除
クラスター管理者は、プロジェクトから egress ファイアウォールを削除して、OpenShift Container Platform クラスター外に出るプロジェクトからネットワークトラフィックについてのすべての制限を削除できます。
15.8.1. EgressFirewall オブジェクトの削除
クラスター管理者は、プロジェクトから Egress ファイアウォールを削除できます。
前提条件
- OVN-Kubernetes デフォルト Container Network Interface (CNI) ネットワークプロバイダープラグインを使用するクラスター。
-
OpenShift CLI (
oc) をインストールしている。 - クラスター管理者としてクラスターにログインする必要があります。
手順
プロジェクトの EgressFirewall オブジェクトの名前を検索します。
<project>をプロジェクトの名前に置き換えます。$ oc get -n <project> egressfirewall以下のコマンドを入力し、EgressFirewall オブジェクトを削除します。
<project>をプロジェクトの名前に、<name>をオブジェクトの名前に置き換えます。$ oc delete -n <project> egressfirewall <name>
15.9. egress IP アドレスの設定
クラスター管理者は、1 つ以上の egress IP アドレスを namespace に、または namespace 内の特定の pod に割り当てるように、OVN-Kubernetes デフォルト Container Network Interface (CNI) ネットワークプロバイダーを設定することができます。
15.9.1. Egress IP アドレスアーキテクチャーの設計および実装
OpenShift Container Platform の egress IP アドレス機能を使用すると、1 つ以上の namespace の 1 つ以上の Pod からのトラフィックに、クラスターネットワーク外のサービスに対する一貫したソース IP アドレスを持たせることができます。
たとえば、クラスター外のサーバーでホストされるデータベースを定期的にクエリーする Pod がある場合があります。サーバーにアクセス要件を適用するために、パケットフィルターリングデバイスは、特定の IP アドレスからのトラフィックのみを許可するよう設定されます。この特定の Pod のみからサーバーに確実にアクセスできるようにするには、サーバーに要求を行う Pod に特定の egress IP アドレスを設定できます。
egress IP アドレスは、ノードのプライマリーネットワークインターフェイスの追加 IP アドレスとして実装され、ノードのプライマリー IP アドレスと同じサブネットにある必要があります。追加の IP アドレスは、クラスター内の他のノードには割り当てないでください。
一部のクラスター設定では、アプリケーション Pod と Ingress ルーター Pod が同じノードで実行されます。このシナリオでアプリケーションプロジェクトの Egress IP を設定する場合、アプリケーションプロジェクトからルートに要求を送信するときに IP は使用されません。
15.9.1.1. プラットフォームサポート
各種のプラットフォームでの egress IP アドレス機能のサポートについては、以下の表で説明されています。
egress IP アドレスの実装は、Amazon Web Services (AWS)、Azure Cloud、または egress IP 機能で必要な自動レイヤー 2 ネットワーク操作と互換性のない他のパブリッククラウドプラットフォームと互換性がありません。
| プラットフォーム | サポート対象 |
|---|---|
| ベアメタル | はい |
| vSphere | はい |
| Red Hat OpenStack Platform (RHOSP) | いいえ |
| パブリッククラウド | いいえ |
15.9.1.2. egress IP の Pod への割り当て
1 つ以上の egress IP を namespace に、または namespace の特定の Pod に割り当てるには、以下の条件を満たす必要があります。
-
クラスター内の 1 つ以上のノードに
k8s.ovn.org/egress-assignable: ""ラベルがなければなりません。 -
EgressIPオブジェクトが存在し、これは namespace の Pod からクラスターを離脱するトラフィックのソース IP アドレスとして使用する 1 つ以上の egress IP アドレスを定義します。
egress IP の割り当て用にクラスター内のノードにラベルを付ける前に EgressIP オブジェクトを作成する場合、OpenShift Container Platform は k8s.ovn.org/egress-assignable: "" ラベルですべての egress IP アドレスを最初のノードに割り当てる可能性があります。
egress IP アドレスがクラスター内のノード全体に広く分散されるようにするには、EgressIP オブジェクトを作成する前に、egress IP アドレスをホストする予定のノードにラベルを常に適用します。
15.9.1.3. egress IP のノードへの割り当て
EgressIP オブジェクトを作成する場合、k8s.ovn.org/egress-assignable: "" ラベルのラベルが付いたノードに以下の条件が適用されます。
- egress IP アドレスは一度に複数のノードに割り当てられることはありません。
- egress IP アドレスは、egress IP アドレスをホストできる利用可能なノード間で均等に分散されます。
-
EgressIPオブジェクトのspec.EgressIPs配列が複数の IP アドレスを指定する場合、ノードが指定したアドレスを複数ホストすることはありません。 - ノードが利用不可の場合、そのノードに割り当てられる egress IP アドレスは自動的に再割り当てされます (前述の条件が適用されます)。
Pod が複数の EgressIP オブジェクトのセレクターに一致する場合、EgressIP オブジェクトに指定される egress IP アドレスのどれが Pod の egress IP アドレスとして割り当てられるのかという保証はありません。
さらに、EgressIP オブジェクトが複数の送信 IP アドレスを指定する場合、どの送信 IP アドレスが使用されるかは保証されません。たとえば、Pod が 10.10.20.1 と 10.10.20.2 の 2 つの egress IP アドレスを持つ EgressIP オブジェクトのセレクターと一致する場合、各 TCP 接続または UDP 会話にいずれかが使用される可能性があります。
15.9.1.4. egress IP アドレス設定のアーキテクチャー図
以下の図は、egress IP アドレス設定を示しています。この図では、クラスターの 3 つのノードで実行される 2 つの異なる namespace の 4 つの Pod について説明します。ノードには、ホストネットワークの 192.168.126.0/18 CIDR ブロックから IP アドレスが割り当てられます。
ノード 1 とノード 3 の両方に k8s.ovn.org/egress-assignable: "" というラベルが付けられるため、egress IP アドレスの割り当てに利用できます。
図の破線は、pod1、pod2、および pod3 からのトラフィックフローが Pod ネットワークを通過し、クラスターがノード 1 およびノード 3 から出る様子を示しています。外部サービスが、EgressIP オブジェクトの例で選択した Pod からトラフィックを受信する場合、ソース IP アドレスは 192.168.126.10 または 192.168.126.102 のいずれかになります。
図にある次のリソースの詳細を以下に示します。
Namespaceオブジェクトnamespace は以下のマニフェストで定義されます。
namespace オブジェクト
apiVersion: v1 kind: Namespace metadata: name: namespace1 labels: env: prod --- apiVersion: v1 kind: Namespace metadata: name: namespace2 labels: env: prodEgressIPオブジェクト以下の
EgressIPオブジェクトは、envラベルがprodに設定される namespace のすべての Pod を選択する設定を説明しています。選択された Pod の egress IP アドレスは192.168.126.10および192.168.126.102です。EgressIPオブジェクトapiVersion: k8s.ovn.org/v1 kind: EgressIP metadata: name: egressips-prod spec: egressIPs: - 192.168.126.10 - 192.168.126.102 namespaceSelector: matchLabels: env: prod status: assignments: - node: node1 egressIP: 192.168.126.10 - node: node3 egressIP: 192.168.126.102直前の例の設定の場合、OpenShift Container Platform は両方の egress IP アドレスを利用可能なノードに割り当てます。
statusフィールドは、egress IP アドレスの割り当ての有無および割り当てられる場所を反映します。
15.9.2. EgressIP オブジェクト
以下の YAML は、EgressIP オブジェクトの API について説明しています。オブジェクトの範囲はクラスター全体です。これは namespace では作成されません。
apiVersion: k8s.ovn.org/v1
kind: EgressIP
metadata:
name: <name>
spec:
egressIPs:
- <ip_address>
namespaceSelector:
...
podSelector:
...以下の YAML は namespace セレクターのスタンザについて説明しています。
namespace セレクタースタンザ
namespaceSelector:
matchLabels:
<label_name>: <label_value>- 1
- namespace の 1 つ以上のマッチングルール。複数のマッチングルールを指定すると、一致するすべての namespace が選択されます。
以下の YAML は Pod セレクターのオプションのスタンザについて説明しています。
Pod セレクタースタンザ
podSelector:
matchLabels:
<label_name>: <label_value>- 1
- オプション: 指定された
namespaceSelectorルールに一致する、namespace の Pod の 1 つ以上のマッチングルール。これが指定されている場合、一致する Pod のみが選択されます。namespace の他の Pod は選択されていません。
以下の例では、EgressIP オブジェクトは 192.168.126.11 および 192.168.126.102 egress IP アドレスを、app ラベルが web に設定されており、env ラベルが prod に設定されている namespace にある Pod に関連付けます。
EgressIP オブジェクトの例
apiVersion: k8s.ovn.org/v1
kind: EgressIP
metadata:
name: egress-group1
spec:
egressIPs:
- 192.168.126.11
- 192.168.126.102
podSelector:
matchLabels:
app: web
namespaceSelector:
matchLabels:
env: prod
以下の例では、EgressIP オブジェクトは、192.168.127.30 および 192.168.127.40 egress IP アドレスを、environment ラベルが development に設定されていない Pod に関連付けます。
EgressIP オブジェクトの例
apiVersion: k8s.ovn.org/v1
kind: EgressIP
metadata:
name: egress-group2
spec:
egressIPs:
- 192.168.127.30
- 192.168.127.40
namespaceSelector:
matchExpressions:
- key: environment
operator: NotIn
values:
- development15.9.3. egress IP アドレスをホストするノードのラベル付け
OpenShift Container Platform が 1 つ以上の egress IP アドレスをノードに割り当てることができるように、k8s.ovn.org/egress-assignable="" ラベルをクラスター内のノードに適用することができます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 - クラスター管理者としてクラスターにログインします。
手順
1 つ以上の egress IP アドレスをホストできるようにノードにラベルを付けるには、以下のコマンドを入力します。
$ oc label nodes <node_name> k8s.ovn.org/egress-assignable=""1 - 1
- ラベルを付けるノードの名前。
15.9.4. 次のステップ
15.10. egress IP アドレスの割り当て
クラスター管理者は、namespace または namespace の特定の Pod からクラスターを出るトラフィックに egress IP アドレスを割り当てることができます。
15.10.1. egress IP アドレスの namespace への割り当て
1 つ以上の egress IP アドレスを namespace または namespace の特定の Pod に割り当てることができます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 - クラスター管理者としてクラスターにログインします。
- egress IP アドレスをホストするように 1 つ以上のノードを設定します。
手順
EgressIPオブジェクトを作成します。-
<egressips_name>.yamlファイルを作成します。<egressips_name>はオブジェクトの名前になります。 作成したファイルで、以下の例のように
EgressIPsオブジェクトを定義します。apiVersion: k8s.ovn.org/v1 kind: EgressIP metadata: name: egress-project1 spec: egressIPs: - 192.168.127.10 - 192.168.127.11 namespaceSelector: matchLabels: env: qa
-
オブジェクトを作成するには、以下のコマンドを入力します。
$ oc apply -f <egressips_name>.yaml1 - 1
<egressips_name>をオブジェクトの名前に置き換えます。
出力例
egressips.k8s.ovn.org/<egressips_name> created-
オプション: 後に変更できるように
<egressips_name>.yamlファイルを保存します。 egress IP アドレスを必要とする namespace にラベルを追加します。手順 1 で定義した
Egress IPオブジェクトの namespace にラベルを追加するには、以下のコマンドを実行します。$ oc label ns <namespace> env=qa1 - 1
<namespace>は、egress IP アドレスを必要とする namespace に置き換えてください。
15.11. egress ルーター Pod の使用についての考慮事項
15.11.1. egress ルーター Pod について
OpenShift Container Platform egress ルーター Pod は、他の用途で使用されていないプライベートソース IP アドレスから指定されたリモートサーバーにトラフィックをリダイレクトします。egress ルーター Pod により、特定の IP アドレスからのアクセスのみを許可するように設定されたサーバーにネットワークトラフィックを送信できます。
egress ルーター Pod はすべての発信接続のために使用されることが意図されていません。多数の egress ルーター Pod を作成することで、ネットワークハードウェアの制限を引き上げられる可能性があります。たとえば、すべてのプロジェクトまたはアプリケーションに egress ルーター Pod を作成すると、ソフトウェアの MAC アドレスのフィルターに戻る前にネットワークインターフェイスが処理できるローカル MAC アドレス数の上限を超えてしまう可能性があります。
egress ルーターイメージには Amazon AWS, Azure Cloud またはレイヤー 2 操作をサポートしないその他のクラウドプラットフォームとの互換性がありません。 それらに macvlan トラフィックとの互換性がないためです。
15.11.1.1. Egress ルーターモード
リダイレクトモード では、egress ルーター Pod は、トラフィックを独自の IP アドレスから 1 つ以上の宛先 IP アドレスにリダイレクトするために iptables ルールをセットアップします。予約されたソース IP アドレスを使用する必要のあるクライアント Pod は、宛先 IP に直接接続するのでなく、egress ルーターに接続するように変更される必要があります。
egress ルーター CNI プラグインはリダイレクトモードのみをサポートします。これは、OpenShift SDN でデプロイできる egress ルーター実装の相違点です。OpenShift SDN の egress ルーターとは異なり、egress ルーター CNI プラグインは HTTP プロキシーモード または DNS プロキシーモード をサポートしません。
15.11.1.2. egress ルーター Pod の実装
egress ルーターの実装では、egress ルーターの Container Network Interface (CNI) プラグインを使用します。プラグインはセカンダリーネットワークインターフェイスを Pod に追加します。
egress ルーターは、2 つのネットワークインターフェイスを持つ Pod です。たとえば、Pod には、eth0 および net1 ネットワークインターフェイスを使用できます。eth0 インターフェイスはクラスターネットワークにあり、Pod は通常のクラスター関連のネットワークトラフィックにこのインターフェイスを引き続き使用します。net1 インターフェイスはセカンダリーネットワークにあり、そのネットワークの IP アドレスとゲートウェイを持ちます。OpenShift Container Platform クラスターの他の Pod は egress ルーターサービスにアクセスでき、サービスにより Pod が外部サービスにアクセスできるようになります。egress ルーターは、Pod と外部システム間のブリッジとして機能します。
egress ルーターから出るトラフィックはノードで終了しますが、パケットには egress ルーター Pod からの net1 インターフェイスの MAC アドレスがあります。
15.11.1.3. デプロイメントに関する考慮事項
egress ルーター Pod は追加の IP アドレスおよび MAC アドレスをノードのプライマリーネットワークインターフェイスに追加します。その結果、ハイパーバイザーまたはクラウドプロバイダーを、追加のアドレスを許可するように設定する必要がある場合があります。
- Red Hat OpenStack Platform (RHOSP)
OpenShift Container Platform を RHOSP にデプロイする場合、OpenStack 環境の egress ルーター Pod の IP および MAC アドレスからのトラフィックを許可する必要があります。トラフィックを許可しないと、通信は失敗 します。
$ openstack port set --allowed-address \ ip_address=<ip_address>,mac_address=<mac_address> <neutron_port_uuid>- Red Hat Virtualization (RHV)
- RHV を使用している場合は、仮想インターフェイスカード (vNIC) に No Network Filter を選択する必要があります。
- VMware vSphere
- VMware vSphere を使用している場合は、vSphere 標準スイッチのセキュリティー保護についての VMware ドキュメント を参照してください。vSphere Web クライアントからホストの仮想スイッチを選択して、VMware vSphere デフォルト設定を表示し、変更します。
とくに、以下が有効にされていることを確認します。
15.11.1.4. フェイルオーバー設定
ダウンタイムを回避するには、以下の例のように Deployment リソースで egress ルーター Pod をデプロイできます。サンプルのデプロイメント用に新規 Service オブジェクトを作成するには、oc expose deployment/egress-demo-controller コマンドを使用します。
apiVersion: apps/v1
kind: Deployment
metadata:
name: egress-demo-controller
spec:
replicas: 1
selector:
matchLabels:
name: egress-router
template:
metadata:
name: egress-router
labels:
name: egress-router
annotations:
k8s.v1.cni.cncf.io/networks: egress-router-redirect
spec:
containers:
- name: egress-router-redirect
image: registry.redhat.io/openshift3/ose-pod15.12. リダイレクトモードでの egress ルーター Pod のデプロイ
クラスター管理者は、トラフィックを予約されたソース IP アドレスから指定された宛先 IP アドレスにリダイレクトするように egress ルーター Pod をデプロイできます。
egress ルーターの実装では、egress ルーターの Container Network Interface (CNI) プラグインを使用します。
egress ルーター CNI プラグインはテクノロジープレビュー機能としてのみご利用いただけます。テクノロジープレビュー機能は Red Hat の実稼働環境でのサービスレベルアグリーメント (SLA) ではサポートされていないため、Red Hat では実稼働環境での使用を推奨していません。Red Hat は実稼働環境でこれらを使用することを推奨していません。テクノロジープレビューの機能は、最新の製品機能をいち早く提供して、開発段階で機能のテストを行いフィードバックを提供していただくことを目的としています。
Red Hat のテクノロジープレビュー機能のサポート範囲についての詳細は、https://access.redhat.com/ja/support/offerings/techpreview/ を参照してください。
15.12.1. リダイレクトモードでの egress ルーターのネットワーク接続定義
Pod が egress ルーターとして機能する前に、ネットワークインターフェイス設定を NetworkAttachmentDefinition オブジェクトとして指定する必要があります。オブジェクトは、egress ルーター Pod、ネットワークの宛先、およびネットワークゲートウェイに割り当てる IP アドレスなどの情報を指定します。egress ルーターの Pod が起動すると、Multus はネットワーク接続定義を使用して、指定されたプロパティーを持つネットワークインターフェイスを Pod に追加します。
ネットワーク接続定義の例
apiVersion: "k8s.cni.cncf.io/v1"
kind: NetworkAttachmentDefinition
metadata:
name: egress-router-redirect
spec:
config: '{
"cniVersion": "0.4.0",
"type": "egress-router",
"name": "egress-router",
"ip": {
"addresses": [
"192.168.12.99/24"
],
"destinations": [
"192.168.12.91/32"
],
"gateway": "192.168.12.1"
}
}'- 1
- ネットワーク接続定義の名前は、後に egress ルーター Pod の仕様で使用されます。
- 2
addressesキーは、追加のネットワークインターフェイスで使用する予約されたソース IP アドレスを指定します。192.168.12.99/24などの CIDR 表記で単一 IP アドレスを指定します。- 3
destinationsキーは、egress ルーターがパケットを送信する CIDR 表記の単一 IP アドレスを指定します。egress ルーター Pod のネットワークアドレス変換 (NAT) 表は、Pod のクラスター IP アドレスへの接続が宛先 IP アドレスの同じポートにリダイレクトされるように設定されます。この例では、Pod への接続は192.168.12.91にリダイレクトされます。 ソース IP アドレスは192.168.12.99です。- 4
gatewayキーは、ネットワークゲートウェイの IP アドレスを指定します。
15.12.2. リダイレクトモードの egress ルーター Pod 仕様
ネットワーク接続定義の作成後に、定義を参照する Pod を追加します。
egress ルーター Pod 仕様の例
apiVersion: v1
kind: Pod
metadata:
name: egress-router-pod
annotations:
k8s.v1.cni.cncf.io/networks: egress-router-redirect
spec:
containers:
- name: egress-router-pod
image: registry.redhat.com/openshift3/ose-pod- 1
- 指定されたネットワークはネットワーク接続定義の名前と一致する必要があります。
<namespace> /<network>@<interface>パターンの値を置き換えて、namespace、インターフェイス名、またはその両方を指定することができます。デフォルトで、Multus はnet1、net2などの名前でセカンダリーネットワークインターフェイスを Pod に追加します。
15.12.3. リダイレクトモードでの egress ルーター Pod のデプロイ
egress ルーター Pod は、トラフィックを独自の予約されたソース IP アドレスから 1 つ以上の宛先 IP アドレスにリダイレクトするためにデプロイできます。
egress ルーター Pod を追加した後に、予約されたソース IP アドレスを使用する必要のあるクライアント Pod は、宛先 IP に直接接続するのでなく、egress ルーターに接続するように変更される必要があります。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-admin権限を持つユーザーとしてログインしている。
手順
- ネットワーク接続定義の作成
- egress ルーター Pod の作成
他の Pod が egress ルーター Pod の IP アドレスを見つられるようにするには、以下の例のように、egress ルーター Pod を使用するサービスを作成します。
apiVersion: v1 kind: Service metadata: name: egress-1 spec: ports: - name: database protocol: TCP port: 3306 type: ClusterIP selector: name: egress-router-podサービスの作成後に、Pod はサービスに接続できます。egress ルーター Pod は、接続を宛先 IP アドレスの対応するポートにリダイレクトします。接続は、予約されたソース IP アドレスを起点とします。
検証
egress ルーター Pod が起動し、セカンダリーネットワークインターフェイスがあることを確認するには、以下の手順を実行します。
egress ルーター Pod のイベントを表示します。
$ oc get events --field-selector involvedObject.name=egress-router-podPod がネットワーク接続定義を参照する場合、直前のコマンドは以下のような出力を返します。
出力例
LAST SEEN TYPE REASON OBJECT MESSAGE 5m4s Normal Scheduled pod/egress-router-pod Successfully assigned default/egress-router-pod to ci-ln-9x2bnsk-f76d1-j2v6g-worker-c-24g65 5m3s Normal AddedInterface pod/egress-router-pod Add eth0 [10.129.2.31/23] 5m3s Normal AddedInterface pod/egress-router-pod Add net1 [192.168.12.99/24] from default/egress-router-redirectオプション: egress ルーター Pod のルーティングテーブルを表示します。
egress ルーター Pod のノード名を取得します。
$ POD_NODENAME=$(oc get pod egress-router-pod -o jsonpath="{.spec.nodeName}")ターゲットノードのデバッグセッションに入ります。この手順は、
<node_name>-debugというデバッグ Pod をインスタンス化します。$ oc debug node/$POD_NODENAME/hostをデバッグシェル内の root ディレクトリーとして設定します。デバッグ Pod は、Pod 内の/hostにホストのルートファイルシステムをマウントします。ルートディレクトリーを/hostに変更すると、ホストの実行可能パスに含まれるバイナリーを実行できます。# chroot /hostchroot環境コンソール内で、コンテナー ID を取得します。# crictl ps --name egress-router-redirect | awk '{print $1}'出力例
CONTAINER bac9fae69ddb6コンテナーのプロセス ID を判別します。この例では、コンテナー ID は
bac9fae69ddb6です。# crictl inspect -o yaml bac9fae69ddb6 | grep 'pid:' | awk '{print $2}'出力例
68857コンテナーのネットワーク namespace を入力します。
# nsenter -n -t 68857ルーティングテーブルを表示します。
# ip route以下の出力例では、
net1ネットワークインターフェイスはデフォルトのルートです。クラスターネットワークのトラフィックはeth0ネットワークインターフェイスを使用します。192.168.12.0/24ネットワークのトラフィックは、net1ネットワークインターフェイスを使用し、予約されたソース IP アドレス192.168.12.99を起点とします。Pod は他のすべてのトラフィックを IP アドレス192.168.12.1のゲートウェイにルーティングします。サービスネットワークのルーティングは表示されません。出力例
default via 192.168.12.1 dev net1 10.129.2.0/23 dev eth0 proto kernel scope link src 10.129.2.31 192.168.12.0/24 dev net1 proto kernel scope link src 192.168.12.99 192.168.12.1 dev net1
15.13. プロジェクトのマルチキャストの有効化
15.13.1. マルチキャストについて
IP マルチキャストを使用すると、データが多数の IP アドレスに同時に配信されます。
現時点で、マルチキャストは低帯域幅の調整またはサービスの検出での使用に最も適しており、高帯域幅のソリューションとしては適していません。
OpenShift Container Platform の Pod 間のマルチキャストトラフィックはデフォルトで無効にされます。OVN-Kubernetes デフォルト Container Network Interface (CNI) ネットワークプロバイダーを使用している場合には、プロジェクトごとにマルチキャストを有効にすることができます。
15.13.2. Pod 間のマルチキャストの有効化
プロジェクトの Pod でマルチキャストを有効にすることができます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-adminロールを持つユーザーとしてクラスターにログインする必要があります。
手順
以下のコマンドを実行し、プロジェクトのマルチキャストを有効にします。
<namespace>を、マルチキャストを有効にする必要のある namespace に置き換えます。$ oc annotate namespace <namespace> \ k8s.ovn.org/multicast-enabled=true
検証
マルチキャストがプロジェクトについて有効にされていることを確認するには、以下の手順を実行します。
現在のプロジェクトを、マルチキャストを有効にしたプロジェクトに切り替えます。
<project>をプロジェクト名に置き換えます。$ oc project <project>マルチキャストレシーバーとして機能する Pod を作成します。
$ cat <<EOF| oc create -f - apiVersion: v1 kind: Pod metadata: name: mlistener labels: app: multicast-verify spec: containers: - name: mlistener image: registry.access.redhat.com/ubi8 command: ["/bin/sh", "-c"] args: ["dnf -y install socat hostname && sleep inf"] ports: - containerPort: 30102 name: mlistener protocol: UDP EOFマルチキャストセンダーとして機能する Pod を作成します。
$ cat <<EOF| oc create -f - apiVersion: v1 kind: Pod metadata: name: msender labels: app: multicast-verify spec: containers: - name: msender image: registry.access.redhat.com/ubi8 command: ["/bin/sh", "-c"] args: ["dnf -y install socat && sleep inf"] EOF新しいターミナルウィンドウまたはタブで、マルチキャストリスナーを起動します。
Pod の IP アドレスを取得します。
$ POD_IP=$(oc get pods mlistener -o jsonpath='{.status.podIP}')次のコマンドを入力して、マルチキャストリスナーを起動します。
$ oc exec mlistener -i -t -- \ socat UDP4-RECVFROM:30102,ip-add-membership=224.1.0.1:$POD_IP,fork EXEC:hostname
マルチキャストトランスミッターを開始します。
Pod ネットワーク IP アドレス範囲を取得します。
$ CIDR=$(oc get Network.config.openshift.io cluster \ -o jsonpath='{.status.clusterNetwork[0].cidr}')マルチキャストメッセージを送信するには、以下のコマンドを入力します。
$ oc exec msender -i -t -- \ /bin/bash -c "echo | socat STDIO UDP4-DATAGRAM:224.1.0.1:30102,range=$CIDR,ip-multicast-ttl=64"マルチキャストが機能している場合、直前のコマンドは以下の出力を返します。
mlistener
15.14. プロジェクトのマルチキャストの無効化
15.14.1. Pod 間のマルチキャストの無効化
プロジェクトの Pod でマルチキャストを無効にすることができます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-adminロールを持つユーザーとしてクラスターにログインする必要があります。
手順
以下のコマンドを実行して、マルチキャストを無効にします。
$ oc annotate namespace <namespace> \1 k8s.ovn.org/multicast-enabled-- 1
- マルチキャストを無効にする必要のあるプロジェクトの
namespace。
15.15. ハイブリッドネットワークの設定
クラスター管理者は、OVN-Kubernetes Container Network Interface (CNI) クラスターネットワークプロバイダーを、Linux および Windows ノードがそれぞれ Linux および Windows ワークロードをできるように設定できます。
15.15.1. OVN-Kubernetes を使用したハイブリッドネットワークの設定
OVN-Kubernetes でハイブリッドネットワークを使用するようにクラスターを設定できます。これにより、異なるノードのネットワーク設定をサポートするハイブリッドクラスターが可能になります。たとえば、これはクラスター内の Linux ノードと Windows ノードの両方を実行するために必要です。
クラスターのインストール時に OVN-Kubernetes クラスタープロバイダーを使用してハイブリッドネットワークを設定する必要があります。インストールプロセス後に、ハイブリッドネットワークに切り替えることはできません。
さらに、ハイブリッド OVN-Kubernetes クラスターネットワークプロバイダーは、Windows Machine Config Operator (WMCO) の要件です。
前提条件
-
install-config.yamlファイルでnetworking.networkTypeパラメーターのOVNKubernetesを定義していること。詳細は、選択したクラウドプロバイダーでの OpenShift Container Platform ネットワークのカスタマイズの設定についてのインストールドキュメントを参照してください。
手順
インストールプログラムが含まれるディレクトリーに切り替え、マニフェストを作成します。
$ ./openshift-install create manifests --dir <installation_directory>ここでは、以下のようになります。
<installation_directory>-
クラスターの
install-config.yamlファイルが含まれるディレクトリーの名前を指定します。
cluster-network-03-config.ymlという名前の、高度なネットワーク設定用のスタブマニフェストファイルを<installation_directory>/manifests/ディレクトリーに作成します。$ cat <<EOF > <installation_directory>/manifests/cluster-network-03-config.yml apiVersion: operator.openshift.io/v1 kind: Network metadata: name: cluster spec: EOFここでは、以下のようになります。
<installation_directory>-
クラスターの
manifests/ディレクトリーが含まれるディレクトリー名を指定します。
cluster-network-03-config.ymlファイルをエディターで開き、以下の例のようにハイブリッドネットワークで OVN-Kubernetes を設定します。ハイブリッドネットワーク設定の指定
apiVersion: operator.openshift.io/v1 kind: Network metadata: name: cluster spec: defaultNetwork: ovnKubernetesConfig: hybridOverlayConfig: hybridClusterNetwork:1 - cidr: 10.132.0.0/14 hostPrefix: 23 hybridOverlayVXLANPort: 98982 - 1
- 追加のオーバーレイネットワーク上のノードに使用される CIDR 設定を指定します。
hybridClusterNetworkCIDR はclusterNetworkCIDR と重複できません。 - 2
- 追加のオーバーレイネットワークのカスタム VXLAN ポートを指定します。これは、vSphere にインストールされたクラスターで Windows ノードを実行するために必要であり、その他のクラウドプロバイダー用に設定することはできません。カスタムポートには、デフォルトの
4789ポートを除くいずれかのオープンポートを使用できます。この要件についての詳細は、Microsoft ドキュメントの Pod-to-pod connectivity between hosts is broken を参照してください。
注記Windows Server Long-Term Servicing Channel (LTSC): Windows Server 2019 は、カスタムの VXLAN ポートの選択をサポートしないため、カスタムの
hybridOverlayVXLANPort値を持つクラスターではサポートされません。-
cluster-network-03-config.ymlファイルを保存し、テキストエディターを終了します。 -
オプション:
manifests/cluster-network-03-config.ymlファイルをバックアップします。インストールプログラムは、クラスターの作成時にmanifests/ディレクトリーを削除します。
追加のインストール設定を完了してから、クラスターを作成します。インストールプロセスが終了すると、ハイブリッドネットワークが有効になります。
第16章 ルートの作成
16.1. ルート設定
16.1.1. HTTP ベースのルートの作成
ルートを使用すると、公開された URL でアプリケーションをホストできます。これは、アプリケーションのネットワークセキュリティー設定に応じて、セキュリティー保護または保護なしを指定できます。HTTP ベースのルートとは、セキュアではないルートで、基本的な HTTP ルーティングプロトコルを使用してセキュリティー保護されていないアプリケーションポートでサービスを公開します。
以下の手順では、hello-openshift アプリケーションを例に、Web アプリケーションへのシンプルな HTTP ベースのルートを作成する方法を説明します。
前提条件
-
OpenShift CLI (
oc) がインストールされている。 - 管理者としてログインしている。
- あるポートを公開する Web アプリケーションと、そのポートでトラフィックをリッスンする TCP エンドポイントがあります。
手順
次のコマンドを実行して、
hello-openshiftというプロジェクトを作成します。$ oc new-project hello-openshift以下のコマンドを実行してプロジェクトに Pod を作成します。
$ oc create -f https://raw.githubusercontent.com/openshift/origin/master/examples/hello-openshift/hello-pod.json以下のコマンドを実行して、
hello-openshiftというサービスを作成します。$ oc expose pod/hello-openshift次のコマンドを実行して、
hello-openshiftアプリケーションに対して、セキュアではないルートを作成します。$ oc expose svc hello-openshift結果として生成される
Routeリソースを検査すると、以下のようになります。上記で作成されたセキュアでないルートの YAML 定義
apiVersion: route.openshift.io/v1 kind: Route metadata: name: hello-openshift spec: host: hello-openshift-hello-openshift.<Ingress_Domain>1 port: targetPort: 8080 to: kind: Service name: hello-openshift- 1
<Ingress_Domain>はデフォルトの Ingress ドメイン名です。
注記デフォルトの ingress ドメインを表示するには、以下のコマンドを実行します。
$ oc get ingresses.config/cluster -o jsonpath={.spec.domain}
16.1.2. ルートのタイムアウトの設定
Service Level Availability (SLA) で必要とされる、低タイムアウトが必要なサービスや、バックエンドでの処理速度が遅いケースで高タイムアウトが必要なサービスがある場合は、既存のルートに対してデフォルトのタイムアウトを設定することができます。
前提条件
- 実行中のクラスターでデプロイ済みの Ingress コントローラーが必要になります。
手順
oc annotateコマンドを使用して、ルートにタイムアウトを追加します。$ oc annotate route <route_name> \ --overwrite haproxy.router.openshift.io/timeout=<timeout><time_unit>1 - 1
- サポートされる時間単位は、マイクロ秒 (us)、ミリ秒 (ms)、秒 (s)、分 (m)、時間 (h)、または日 (d) です。
以下の例では、2 秒のタイムアウトを
myrouteという名前のルートに設定します。$ oc annotate route myroute --overwrite haproxy.router.openshift.io/timeout=2s
16.1.3. HTTP Strict Transport Security の有効化
HTTP Strict Transport Security (HSTS) ポリシーは、ホストで HTTPS トラフィックのみを許可するセキュリティーの拡張機能です。デフォルトで、すべての HTTP 要求はドロップされます。これは、web サイトとの対話の安全性を確保したり、ユーザーのためにセキュアなアプリケーションを提供するのに役立ちます。
HSTS が有効にされると、HSTS はサイトから Strict Transport Security ヘッダーを HTTPS 応答に追加します。リダイレクトするルートで insecureEdgeTerminationPolicy 値を使用し、HTTP を HTTPS に送信するようにします。ただし、HSTS が有効にされている場合は、要求の送信前にクライアントがすべての要求を HTTP URL から HTTPS に変更するためにリダイレクトの必要がなくなります。これはクライアントでサポートされる必要はなく、max-age=0 を設定することで無効にできます。
HSTS はセキュアなルート (edge termination または re-encrypt) でのみ機能します。この設定は、HTTP またはパススルールートには適していません。
手順
ルートに対して HSTS を有効にするには、
haproxy.router.openshift.io/hsts_header値を edge termination または re-encrypt ルートに追加します。apiVersion: v1 kind: Route metadata: annotations: haproxy.router.openshift.io/hsts_header: max-age=31536000;includeSubDomains;preload1 2 3 - 1
max-ageは唯一の必須パラメーターです。これは、HSTS ポリシーが有効な期間 (秒単位) を測定します。クライアントは、ホストから HSTS ヘッダーのある応答を受信する際には常にmax-ageを更新します。max-ageがタイムアウトになると、クライアントはポリシーを破棄します。- 2
includeSubDomainsはオプションです。これが含まれる場合、クライアントに対し、ホストのすべてのサブドメインがホストと同様に処理されるように指示します。- 3
preloadはオプションです。max-ageが 0 より大きい場合、preloadをhaproxy.router.openshift.io/hsts_headerに組み込むことにより、外部サービスはこのサイトをそれぞれの HSTS プリロード一覧に含めることができます。たとえば、Google などのサイトはpreloadが設定されているサイトの一覧を作成します。ブラウザーはこれらの一覧を使用し、サイトと対話する前でも HTTPS 経由で通信できるサイトを判別できます。preload設定がない場合、ブラウザーはヘッダーを取得するために HTTPS 経由でサイトと通信している必要があります。
16.1.4. スループット関連の問題のトラブルシューティング
OpenShift Container Platform でデプロイされるアプリケーションでは、特定のサービス間で非常に長い待ち時間が発生するなど、ネットワークのスループットの問題が生じることがあります。
Pod のログが問題の原因を指摘しない場合は、以下の方法を使用してパフォーマンスの問題を分析します。
ping または tcpdump などのパケットアナライザーを使用して Pod とそのノード間のトラフィックを分析します。
たとえば、問題を生じさせる動作を再現している間に各 Pod で tcpdump ツールを実行します。両サイトでキャプチャーしたデータを確認し、送信および受信タイムスタンプを比較して Pod への/からのトラフィックの待ち時間を分析します。待ち時間は、ノードのインターフェイスが他の Pod やストレージデバイス、またはデータプレーンからのトラフィックでオーバーロードする場合に OpenShift Container Platform で発生する可能性があります。
$ tcpdump -s 0 -i any -w /tmp/dump.pcap host <podip 1> && host <podip 2>1 - 1
podipは Pod の IP アドレスです。oc get pod <pod_name> -o wideコマンドを実行して Pod の IP アドレスを取得します。
tcpdump は 2 つの Pod 間のすべてのトラフィックが含まれる
/tmp/dump.pcapのファイルを生成します。理想的には、ファイルサイズを最小限に抑えるために問題を再現するすぐ前と問題を再現したすぐ後ににアナライザーを実行することが良いでしょう。以下のようにノード間でパケットアナライザーを実行することもできます (式から SDN を排除する)。$ tcpdump -s 0 -i any -w /tmp/dump.pcap port 4789ストリーミングのスループットおよび UDP スループットを測定するために iperf などの帯域幅測定ツールを使用します。ボトルネックの特定を試行するには、最初に Pod から、次にノードからツールを実行します。
- iperf のインストールおよび使用についての詳細は、こちらの Red Hat ソリューション を参照してください。
16.1.5. Cookie に使用によるルートのステートフル性の維持
OpenShift Container Platform は、すべてのトラフィックを同じエンドポイントにヒットさせることによりステートフルなアプリケーションのトラフィックを可能にするスティッキーセッションを提供します。ただし、エンドポイント Pod が再起動、スケーリング、または設定の変更などによって終了する場合、このステートフル性はなくなります。
OpenShift Container Platform は Cookie を使用してセッションの永続化を設定できます。Ingress コントローラーはユーザー要求を処理するエンドポイントを選択し、そのセッションの Cookie を作成します。Cookie は要求の応答として戻され、ユーザーは Cookie をセッションの次の要求と共に送り返します。Cookie は Ingress コントローラーに対し、セッションを処理しているエンドポイントを示し、クライアント要求が Cookie を使用して同じ Pod にルーティングされるようにします。
cookie は、HTTP トラフィックを表示できないので、パススルールートで設定できません。代わりに、ソース IP アドレスをベースに数が計算され、バックエンドを判断します。
バックエンドが変わると、トラフィックが間違ったサーバーに転送されてしまい、スティッキーではなくなります。ソース IP を非表示にするロードバランサーを使用している場合は、すべての接続に同じ番号が設定され、トラフィックは同じ Pod に送られます。
16.1.5.1. Cookie を使用したルートのアノテーション
ルート用に自動生成されるデフォルト名を上書きするために Cookie 名を設定できます。これにより、ルートトラフィックを受信するアプリケーションが Cookie 名を認識できるようになります。Cookie を削除すると、次の要求でエンドポイントの再選択が強制的に実行される可能性があります。そのためサーバーがオーバーロードしている場合には、クライアントからの要求を取り除き、それらの再分配を試行します。
手順
指定される cookie 名でルートにアノテーションを付けます。
$ oc annotate route <route_name> router.openshift.io/cookie_name="<cookie_name>"ここでは、以下のようになります。
<route_name>- Pod の名前を指定します。
<cookie_name>- cookie の名前を指定します。
たとえば、ルート
my_routeに cookie 名my_cookieでアノテーションを付けるには、以下を実行します。$ oc annotate route my_route router.openshift.io/cookie_name="my_cookie"変数でルートのホスト名を取得します。
$ ROUTE_NAME=$(oc get route <route_name> -o jsonpath='{.spec.host}')ここでは、以下のようになります。
<route_name>- Pod の名前を指定します。
cookie を保存してからルートにアクセスします。
$ curl $ROUTE_NAME -k -c /tmp/cookie_jarルートに接続する際に、直前のコマンドによって保存される cookie を使用します。
$ curl $ROUTE_NAME -k -b /tmp/cookie_jar
16.1.6. パスベースのルート
パスベースのルートは、URL に対して比較できるパスコンポーネントを指定します。この場合、ルートのトラフィックは HTTP ベースである必要があります。そのため、それぞれが異なるパスを持つ同じホスト名を使用して複数のルートを提供できます。ルーターは、最も具体的なパスの順に基づいてルートと一致する必要があります。ただし、これはルーターの実装によって異なります。
以下の表は、ルートのサンプルおよびそれらのアクセシビリティーを示しています。
| ルート | 比較対象 | アクセス可能 |
|---|---|---|
| www.example.com/test | www.example.com/test | はい |
| www.example.com | いいえ | |
| www.example.com/test および www.example.com | www.example.com/test | はい |
| www.example.com | はい | |
| www.example.com | www.example.com/text | Yes (ルートではなく、ホストで一致) |
| www.example.com | はい |
パスが 1 つでセキュリティー保護されていないルート
apiVersion: route.openshift.io/v1
kind: Route
metadata:
name: route-unsecured
spec:
host: www.example.com
path: "/test"
to:
kind: Service
name: service-name- 1
- パスは、パスベースのルートに唯一追加される属性です。
ルーターは TLS を終了させず、要求のコンテンツを読み込みことができないので、パスベースのルーティングは、パススルー TLS を使用する場合には利用できません。
16.1.7. ルート固有のアノテーション
Ingress コントローラーは、公開するすべてのルートのデフォルトオプションを設定できます。個別のルートは、アノテーションに個別の設定を指定して、デフォルトの一部を上書きできます。Red Hat では、ルートアノテーションの Operator 管理ルートへの追加はサポートしません。
複数のソース IP またはサブネットのホワイトリストを作成するには、スペースで区切られたリストを使用します。他の区切りタイプを使用すると、一覧が警告やエラーメッセージなしに無視されます。
| 変数 | 説明 | デフォルトで使用される環境変数 |
|---|---|---|
|
|
ロードバランシングアルゴリズムを設定します。使用できるオプションは |
パススルールートの |
|
|
関連の接続を追跡する cookie の使用を無効にします。 | |
|
| このルートに使用するオプションの cookie を指定します。名前は、大文字、小文字、数字、"_" または "-" を任意に組み合わせて指定する必要があります。デフォルトは、ルートのハッシュ化された内部キー名です。 | |
|
|
ルーターからバッキングされる Pod に対して許容される接続最大数を設定します。 | |
|
|
| |
|
|
同じソース IP アドレスで行われる同時 TCP 接続の数を制限します。数値を受け入れます。 | |
|
|
同じソース IP アドレスを持つクライアントが HTTP 要求を実行できるレートを制限します。数値を受け入れます。 | |
|
|
同じソース IP アドレスを持つクライアントが TCP 接続を確立するレートを制限します。数値を受け入れます。 | |
|
| ルートのサーバー側のタイムアウトを設定します。(TimeUnits) |
|
|
| このタイムアウトは、クリアテキスト、エッジ、再暗号化、またはパススルーのルートを介した Web Socket などトンネル接続に適用されます。cleartext、edge、または reencrypt のルートタイプでは、このアノテーションは、タイムアウト値がすでに存在するタイムアウトトンネルとして適用されます。パススルーのルートタイプでは、アノテーションは既存のタイムアウト値の設定よりも優先されます。 |
|
|
|
設定できるのは、Ingress Controller または ingress config です。このアノテーションでは、ルーターを再デプロイし、HA プロキシーが haproxy |
|
|
| バックエンドのヘルスチェックの間隔を設定します。(TimeUnits) |
|
|
| ルートのホワイトリストを設定します。ホワイトリストは、承認したソースアドレスの IP アドレスおよび CIDR 範囲の一覧をスペース区切りにします。ホワイトリストに含まれていない IP アドレスからの要求は破棄されます。 ホワイトリストの許可される IP アドレスおよび CIDR 範囲の最大数は 61 です。 | |
|
| edge terminated または re-encrypt ルートの Strick-Transport-Security ヘッダーを設定します。 | |
|
|
Syslog ヘッダーの | |
|
| バックエンドの要求の書き換えパスを設定します。 | |
|
| Cookie を制限するために値を設定します。値は以下のようになります。
この値は、re-encrypt および edge ルートにのみ適用されます。詳細は、SameSite cookie のドキュメント を参照してください。 | |
|
|
ルートごとに
|
|
環境変数を編集することはできません。
ルータータイムアウト変数
TimeUnits は数字、その後に単位を指定して表現します。 us *(マイクロ秒)、ms (ミリ秒、デフォルト)、s (秒)、m (分)、h *(時間)、d (日)
正規表現: [1-9][0-9]*(us\|ms\|s\|m\|h\|d)
| 変数 | デフォルト | 説明 |
|---|---|---|
|
|
| バックエンドでの後続の liveness チェックの時間の長さ。 |
|
|
| クライアントがルートに接続する場合の TCP FIN タイムアウトの期間を制御します。接続切断のために送信された FIN が指定の時間内に応答されない場合は、HAProxy が接続を切断します。小さい値を設定し、ルーターでリソースをあまり使用していない場合には、リスクはありません。 |
|
|
| クライアントがデータを確認するか、送信するための時間の長さ。 |
|
|
| 最大接続時間。 |
|
|
| ルーターからルートをバッキングする Pod の TCP FIN タイムアウトを制御します。 |
|
|
| サーバーがデータを確認するか、送信するための時間の長さ。 |
|
|
| TCP または WebSocket 接続が開放された状態で保つ時間数。このタイムアウト期間は、HAProxy が再読み込みされるたびにリセットされます。 |
|
|
|
新しい HTTP 要求が表示されるまで待機する最大時間を設定します。この値が低すぎる場合には、ブラウザーおよびアプリケーションの
有効なタイムアウト値には、想定した個別のタイムアウトではなく、特定の変数を合計した値に指定することができます。たとえば、 |
|
|
| HTTP 要求の伝送にかかる時間。 |
|
|
| ルーターがリロードし、新規の変更を受け入れる最小の頻度を許可します。 |
|
|
| HAProxy メトリクスの収集タイムアウト。 |
ルート設定のカスタムタイムアウト
apiVersion: route.openshift.io/v1
kind: Route
metadata:
annotations:
haproxy.router.openshift.io/timeout: 5500ms
...- 1
- HAProxy 対応の単位 (
us、ms、s、m、h、d) で新規のタイムアウトを指定します。単位が指定されていない場合は、msがデフォルトになります。
パススルールートのサーバー側のタイムアウト値を低く設定し過ぎると、WebSocket 接続がそのルートで頻繁にタイムアウトする可能性があります。
特定の IP アドレスを 1 つだけ許可するルート
metadata:
annotations:
haproxy.router.openshift.io/ip_whitelist: 192.168.1.10複数の IP アドレスを許可するルート
metadata:
annotations:
haproxy.router.openshift.io/ip_whitelist: 192.168.1.10 192.168.1.11 192.168.1.12IP アドレスの CIDR ネットワークを許可するルート
metadata:
annotations:
haproxy.router.openshift.io/ip_whitelist: 192.168.1.0/24IP アドレスと IP アドレスの CIDR ネットワークの両方を許可するルート
metadata:
annotations:
haproxy.router.openshift.io/ip_whitelist: 180.5.61.153 192.168.1.0/24 10.0.0.0/8書き換えターゲットを指定するルート
apiVersion: route.openshift.io/v1
kind: Route
metadata:
annotations:
haproxy.router.openshift.io/rewrite-target: /
...- 1
- バックエンドの要求の書き換えパスとして
/を設定します。
ルートに haproxy.router.openshift.io/rewrite-target アノテーションを設定すると、要求をバックエンドアプリケーションに転送する前に Ingress コントローラーがこのルートを使用して HTTP 要求のパスを書き換える必要があることを指定します。spec.path で指定されたパスに一致する要求パスの一部は、アノテーションで指定された書き換えターゲットに置き換えられます。
以下の表は、spec.path、要求パス、および書き換えターゲットの各種の組み合わせについてのパスの書き換え動作の例を示しています。
| Route.spec.path | 要求パス | 書き換えターゲット | 転送された要求パス |
|---|---|---|---|
| /foo | /foo | / | / |
| /foo | /foo/ | / | / |
| /foo | /foo/bar | / | /bar |
| /foo | /foo/bar/ | / | /bar/ |
| /foo | /foo | /bar | /bar |
| /foo | /foo/ | /bar | /bar/ |
| /foo | /foo/bar | /baz | /baz/bar |
| /foo | /foo/bar/ | /baz | /baz/bar/ |
| /foo/ | /foo | / | 該当なし (要求パスがルートパスに一致しない) |
| /foo/ | /foo/ | / | / |
| /foo/ | /foo/bar | / | /bar |
16.1.8. ルートの受付ポリシーの設定
管理者およびアプリケーション開発者は、同じドメイン名を持つ複数の namespace でアプリケーションを実行できます。これは、複数のチームが同じホスト名で公開されるマイクロサービスを開発する組織を対象としています。
複数の namespace での要求の許可は、namespace 間の信頼のあるクラスターに対してのみ有効にする必要があります。有効にしないと、悪意のあるユーザーがホスト名を乗っ取る可能性があります。このため、デフォルトの受付ポリシーは複数の namespace 間でのホスト名の要求を許可しません。
前提条件
- クラスター管理者の権限。
手順
以下のコマンドを使用して、
ingresscontrollerリソース変数の.spec.routeAdmissionフィールドを編集します。$ oc -n openshift-ingress-operator patch ingresscontroller/default --patch '{"spec":{"routeAdmission":{"namespaceOwnership":"InterNamespaceAllowed"}}}' --type=mergeイメージコントローラー設定例
spec: routeAdmission: namespaceOwnership: InterNamespaceAllowed ...
16.1.9. Ingress オブジェクトを使用したルートの作成
一部のエコシステムコンポーネントには Ingress リソースとの統合機能がありますが、ルートリソースとは統合しません。これに対応するために、OpenShift Container Platform は Ingress オブジェクトの作成時に管理されるルートオブジェクトを自動的に作成します。これらのルートオブジェクトは、対応する Ingress オブジェクトが削除されると削除されます。
手順
OpenShift Container Platform コンソールで Ingress オブジェクトを定義するか、または oc
createコマンドを実行します。Ingress の YAML 定義
apiVersion: networking.k8s.io/v1 kind: Ingress metadata: name: frontend annotations: route.openshift.io/termination: "reencrypt"1 spec: rules: - host: www.example.com http: paths: - backend: service: name: frontend port: number: 443 path: / pathType: Prefix tls: - hosts: - www.example.com secretName: example-com-tls-certificate- 1
route.openshift.io/terminationアノテーションは、Routeのspec.tls.terminationフィールドを設定するために使用できます。Ingressにはこのフィールドがありません。許可される値はedge、passthrough、およびreencryptです。その他のすべての値は警告なしに無視されます。アノテーション値が設定されていない場合は、edgeがデフォルトルートになります。デフォルトのエッジルートを実装するには、TLS 証明書の詳細をテンプレートファイルで定義する必要があります。route.openshift.io/terminationアノテーションでpassthroughの値を指定する場合は、仕様でpathを''に設定し、pathTypeをImplementationSpecificに設定します。spec: rules: - host: www.example.com http: paths: - path: '' pathType: ImplementationSpecific backend: service: name: frontend port: number: 443
$ oc apply -f ingress.yamlルートを一覧表示します。
$ oc get routes結果には、
frontend-で始まる名前の自動生成ルートが含まれます。NAME HOST/PORT PATH SERVICES PORT TERMINATION WILDCARD frontend-gnztq www.example.com frontend 443 reencrypt/Redirect Noneこのルートを検査すると、以下のようになります。
自動生成されるルートの YAML 定義
apiVersion: route.openshift.io/v1 kind: Route metadata: name: frontend-gnztq ownerReferences: - apiVersion: networking.k8s.io/v1 controller: true kind: Ingress name: frontend uid: 4e6c59cc-704d-4f44-b390-617d879033b6 spec: host: www.example.com path: / port: targetPort: https tls: certificate: | -----BEGIN CERTIFICATE----- [...] -----END CERTIFICATE----- insecureEdgeTerminationPolicy: Redirect key: | -----BEGIN RSA PRIVATE KEY----- [...] -----END RSA PRIVATE KEY----- termination: reencrypt to: kind: Service name: frontend
16.2. セキュリティー保護されたルート
セキュアなルートは、複数の TLS 終端タイプを使用してクライアントに証明書を提供できます。以下のセクションでは、カスタム証明書を使用して re-encrypt、edge、および passthrough ルートを作成する方法を説明します。
パブリックエンドポイントを使用して Microsoft Azure にルートを作成する場合、リソース名は制限されます。特定の用語を使用するリソースを作成することはできません。Azure が制限する語の一覧は、Azure ドキュメントの Resolve reserved resource name errors を参照してください。
16.2.1. カスタム証明書を使用した re-encrypt ルートの作成
oc create route コマンドを使用し、カスタム証明書と共に reencrypt TLS termination を使用してセキュアなルートを設定できます。
前提条件
- PEM エンコードされたファイルに証明書/キーのペアがなければなりません。 ここで、証明書はルートホストに対して有効である必要があります。
- 証明書チェーンを完了する PEM エンコードされたファイルの別の CA 証明書が必要です。
- PEM エンコードされたファイルの別の宛先 CA 証明書が必要です。
- 公開する必要のあるサービスが必要です。
パスワードで保護されるキーファイルはサポートされません。キーファイルからパスフレーズを削除するには、以下のコマンドを使用します。
$ openssl rsa -in password_protected_tls.key -out tls.key手順
この手順では、カスタム証明書および reencrypt TLS termination を使用して Route リソースを作成します。以下では、証明書/キーのペアが現在の作業ディレクトリーの tls.crt および tls.key ファイルにあることを前提としています。また、Ingress コントローラーがサービスの証明書を信頼できるように宛先 CA 証明書を指定する必要もあります。必要な場合には、証明書チェーンを完了するために CA 証明書を指定することもできます。tls.crt、 tls.key、cacert.crt、および (オプションで) ca.crt を実際のパス名に置き換えます。frontend を、公開する必要のある Service リソースに置き換えます。www.example.com を適切な名前に置き換えます。
reencrypt TLS 終端およびカスタム証明書を使用してセキュアな
Routeリソースを作成します。$ oc create route reencrypt --service=frontend --cert=tls.crt --key=tls.key --dest-ca-cert=destca.crt --ca-cert=ca.crt --hostname=www.example.com結果として生成される
Routeリソースを検査すると、以下のようになります。セキュアなルートの YAML 定義
apiVersion: route.openshift.io/v1 kind: Route metadata: name: frontend spec: host: www.example.com to: kind: Service name: frontend tls: termination: reencrypt key: |- -----BEGIN PRIVATE KEY----- [...] -----END PRIVATE KEY----- certificate: |- -----BEGIN CERTIFICATE----- [...] -----END CERTIFICATE----- caCertificate: |- -----BEGIN CERTIFICATE----- [...] -----END CERTIFICATE----- destinationCACertificate: |- -----BEGIN CERTIFICATE----- [...] -----END CERTIFICATE-----他のオプションについては、
oc create route reencrypt --helpを参照してください。
16.2.2. カスタム証明書を使用した edge ルートの作成
oc create route コマンドを使用し、edge TLS termination とカスタム証明書を使用してセキュアなルートを設定できます。edge ルートの場合、Ingress コントローラーは、トラフィックを宛先 Pod に転送する前に TLS 暗号を終了します。ルートは、Ingress コントローラーがルートに使用する TLS 証明書およびキーを指定します。
前提条件
- PEM エンコードされたファイルに証明書/キーのペアがなければなりません。 ここで、証明書はルートホストに対して有効である必要があります。
- 証明書チェーンを完了する PEM エンコードされたファイルの別の CA 証明書が必要です。
- 公開する必要のあるサービスが必要です。
パスワードで保護されるキーファイルはサポートされません。キーファイルからパスフレーズを削除するには、以下のコマンドを使用します。
$ openssl rsa -in password_protected_tls.key -out tls.key手順
この手順では、カスタム証明書および edge TLS termination を使用して Route リソースを作成します。以下では、証明書/キーのペアが現在の作業ディレクトリーの tls.crt および tls.key ファイルにあることを前提としています。必要な場合には、証明書チェーンを完了するために CA 証明書を指定することもできます。tls.crt、 tls.key、および (オプションで) ca.crt を実際のパス名に置き換えます。frontend を、公開する必要のあるサービスの名前に置き換えます。www.example.com を適切な名前に置き換えます。
edge TLS termination およびカスタム証明書を使用して、セキュアな
Routeリソースを作成します。$ oc create route edge --service=frontend --cert=tls.crt --key=tls.key --ca-cert=ca.crt --hostname=www.example.com結果として生成される
Routeリソースを検査すると、以下のようになります。セキュアなルートの YAML 定義
apiVersion: route.openshift.io/v1 kind: Route metadata: name: frontend spec: host: www.example.com to: kind: Service name: frontend tls: termination: edge key: |- -----BEGIN PRIVATE KEY----- [...] -----END PRIVATE KEY----- certificate: |- -----BEGIN CERTIFICATE----- [...] -----END CERTIFICATE----- caCertificate: |- -----BEGIN CERTIFICATE----- [...] -----END CERTIFICATE-----他のオプションについては、
oc create route edge --helpを参照してください。
16.2.3. passthrough ルートの作成
oc create route コマンドを使用し、passthrough termination を使用してセキュアなルートを設定できます。passthrough termination では、暗号化されたトラフィックが TLS 終端を提供するルーターなしに宛先に直接送信されます。そのため、ルートでキーや証明書は必要ありません。
前提条件
- 公開する必要のあるサービスが必要です。
手順
Routeリソースを作成します。$ oc create route passthrough route-passthrough-secured --service=frontend --port=8080結果として生成される
Routeリソースを検査すると、以下のようになります。passthrough termination を使用したセキュリティー保護されたルート
apiVersion: route.openshift.io/v1 kind: Route metadata: name: route-passthrough-secured1 spec: host: www.example.com port: targetPort: 8080 tls: termination: passthrough2 insecureEdgeTerminationPolicy: None3 to: kind: Service name: frontend宛先 Pod は、エンドポイントでトラフィックに証明書を提供します。これは、必須となるクライアント証明書をサポートするための唯一の方法です (相互認証とも呼ばれる)。
第17章 ingress クラスタートラフィックの設定
17.1. ingress クラスタートラフィックの設定の概要
OpenShift Container Platform は、クラスター内で実行されるサービスを使ってクラスター外からの通信を可能にする以下の方法を提供します。
以下の方法が推奨されます。以下は、これらの方法の優先される順です。
- HTTP/HTTPS を使用する場合は Ingress コントローラーを使用する。
- HTTPS 以外の TLS で暗号化されたプロトコルを使用する場合、たとえば、SNI ヘッダーを使用する TLS の場合は、Ingress コントローラーを使用します。
-
それ以外の場合は、ロードバランサー、外部 IP、または
NodePortを使用します。
| 方法 | 目的 |
|---|---|
| HTTP/HTTPS トラフィックおよび HTTPS 以外の TLS で暗号化されたプロトコル (TLS と SNI ヘッダーの使用など) へのアクセスを許可します。 | |
| プールから割り当てられた IP アドレスを使った非標準ポートへのトラフィックを許可します。 | |
| 特定の IP アドレスを使った非標準ポートへのトラフィックを許可します。 | |
| クラスターのすべてのノードでサービスを公開します。 |
17.2. サービスの ExternalIP の設定
クラスター管理者は、トラフィックをクラスター内のサービスに送信できるクラスター外の IP アドレスブロックを指定できます。
この機能は通常、ベアメタルハードウェアにインストールされているクラスターに最も役立ちます。
17.2.1. 前提条件
- ネットワークインフラストラクチャーは、外部 IP アドレスのトラフィックをクラスターにルーティングする必要があります。
17.2.2. ExternalIP について
クラウド以外の環境では、OpenShift Container Platform は ExternalIP 機能を使用して外部 IP アドレスの Service オブジェクトの spec.externalIPs[] フィールドへの割り当てをサポートします。このフィールドを設定すると、OpenShift Container Platform は追加の仮想 IP アドレスをサービスに割り当てます。IP アドレスは、クラスターに定義されたサービスネットワーク外に指定できます。type=NodePort が設定されたサービスと同様に ExternalIP 機能で設定されたサービスにより、トラフィックを負荷分散のためにローカルノードに転送することができます。
ネットワークインフラストラクチャーを設定し、定義する外部 IP アドレスブロックがクラスターにルーティングされるようにする必要があります。
OpenShift Container Platform は以下の機能を追加して Kubernetes の ExternalIP 機能を拡張します。
- 設定可能なポリシーでの、ユーザーによる外部 IP アドレスの使用の制限
- 要求時の外部 IP アドレスのサービスへの自動割り当て
ExternalIP 機能の使用はデフォルトで無効にされます。これは、外部 IP アドレスへのクラスター内のトラフィックがそのサービスにダイレクトされるため、セキュリティー上のリスクを生じさせる可能性があります。これにより、クラスターユーザーは外部リソースについての機密性の高いトラフィックをインターセプトできるようになります。
この機能は、クラウド以外のデプロイメントでのみサポートされます。クラウドデプロイメントの場合、クラウドの自動デプロイメントのためにロードバランサーサービスを使用し、サービスのエンドポイントをターゲットに設定します。
以下の方法で外部 IP アドレスを割り当てることができます。
- 外部 IP の自動割り当て
-
OpenShift Container Platform は、
spec.type=LoadBalancerを設定してServiceオブジェクトを作成する際に、IP アドレスをautoAssignCIDRsCIDR ブロックからspec.externalIPs[]配列に自動的に割り当てます。この場合、OpenShift Container Platform はロードバランサーサービスタイプのクラウド以外のバージョンを実装し、IP アドレスをサービスに割り当てます。自動割り当てはデフォルトで無効にされており、以下のセクションで説明されているように、これはクラスター管理者が設定する必要があります。 - 外部 IP の手動割り当て
-
OpenShift Container Platform は
Serviceオブジェクトの作成時にspec.externalIPs[]配列に割り当てられた IP アドレスを使用します。別のサービスによってすでに使用されている IP アドレスを指定することはできません。
17.2.2.1. ExternalIP の設定
OpenShift Container Platform での外部 IP アドレスの使用は、cluster という名前の Network.config.openshift.io CR の以下のフィールドで管理されます。
-
spec.externalIP.autoAssignCIDRsは、サービスの外部 IP アドレスを選択する際にロードバランサーによって使用される IP アドレスブロックを定義します。OpenShift Container Platform は、自動割り当て用の単一 IP アドレスブロックのみをサポートします。これは、ExternalIP をサービスに手動で割り当てる際に、制限された数の共有 IP アドレスのポート領域を管理しなくてはならない場合よりも単純になります。自動割り当てが有効な場合には、spec.type=LoadBalancerが設定されたServiceオブジェクトには外部 IP アドレスが割り当てられます。 -
spec.externalIP.policyは、IP アドレスを手動で指定する際に許容される IP アドレスブロックを定義します。OpenShift Container Platform は、spec.externalIP.autoAssignCIDRsで定義される IP アドレスブロックにポリシールールを適用しません。
ルーティングが正しく行われると、設定された外部 IP アドレスブロックからの外部トラフィックは、サービスが公開する TCP ポートまたは UDP ポートを介してサービスのエンドポイントに到達できます。
割り当てる IP アドレスブロックがクラスター内の 1 つ以上のノードで終了することを確認する必要があります。
OpenShift Container Platform は IP アドレスの自動および手動割り当ての両方をサポートしており、それぞれのアドレスは 1 つのサービスの最大数に割り当てられることが保証されます。これにより、各サービスは、ポートが他のサービスで公開されているかによらず、自らの選択したポートを公開できます。
OpenShift Container Platform の autoAssignCIDRs で定義された IP アドレスブロックを使用するには、ホストのネットワークに必要な IP アドレスの割り当ておよびルーティングを設定する必要があります。
以下の YAML は、外部 IP アドレスが設定されたサービスについて説明しています。
spec.externalIPs[] が設定された Service オブジェクトの例
apiVersion: v1
kind: Service
metadata:
name: http-service
spec:
clusterIP: 172.30.163.110
externalIPs:
- 192.168.132.253
externalTrafficPolicy: Cluster
ports:
- name: highport
nodePort: 31903
port: 30102
protocol: TCP
targetPort: 30102
selector:
app: web
sessionAffinity: None
type: LoadBalancer
status:
loadBalancer:
ingress:
- ip: 192.168.132.25317.2.2.2. 外部 IP アドレスの割り当ての制限
クラスター管理者は、IP アドレスブロックを指定して許可および拒否できます。
制限は、cluster-admin 権限を持たないユーザーにのみ適用されます。クラスター管理者は、サービスの spec.externalIPs[] フィールドを任意の IP アドレスに常に設定できます。
spec.ExternalIP.policy フィールドを指定して、policy オブジェクトが定義された IP アドレスポリシーを設定します。ポリシーオブジェクトには以下の形があります。
{
"policy": {
"allowedCIDRs": [],
"rejectedCIDRs": []
}
}ポリシーの制限を設定する際に、以下のルールが適用されます。
-
policy={}が設定される場合、spec.ExternalIPs[]が設定されているServiceオブジェクトの作成は失敗します。これは OpenShift Container Platform のデフォルトです。policy=nullが設定される動作は同一です。 policyが設定され、policy.allowedCIDRs[]またはpolicy.rejectedCIDRs[]のいずれかが設定される場合、以下のルールが適用されます。-
allowedCIDRs[]とrejectedCIDRs[]の両方が設定される場合、rejectedCIDRs[]がallowedCIDRs[]よりも優先されます。 -
allowedCIDRs[]が設定される場合、spec.ExternalIPs[]が設定されているServiceオブジェクトの作成は、指定された IP アドレスが許可される場合にのみ正常に実行されます。 -
rejectedCIDRs[]が設定される場合、spec.ExternalIPs[]が設定されているServiceオブジェクトの作成は、指定された IP アドレスが拒否されていない場合にのみ正常に実行されます。
-
17.2.2.3. ポリシーオブジェクトの例
以下に続く例では、複数のポリシー設定の例を示します。
以下の例では、ポリシーは OpenShift Container Platform が外部 IP アドレスが指定されたサービスを作成するのを防ぎます。
Serviceオブジェクトのspec.externalIPs[]に指定された値を拒否するポリシーの例apiVersion: config.openshift.io/v1 kind: Network metadata: name: cluster spec: externalIP: policy: {} ...以下の例では、
allowedCIDRsおよびrejectedCIDRsフィールドの両方が設定されます。許可される、および拒否される CIDR ブロックの両方を含むポリシーの例
apiVersion: config.openshift.io/v1 kind: Network metadata: name: cluster spec: externalIP: policy: allowedCIDRs: - 172.16.66.10/23 rejectedCIDRs: - 172.16.66.10/24 ...以下の例では、
policyはnullに設定されます。nullに設定されている場合、oc get networks.config.openshift.io -o yamlを入力して設定オブジェクトを検査する際に、policyフィールドは出力に表示されません。Serviceオブジェクトのspec.externalIPs[]に指定された値を許可するポリシーの例apiVersion: config.openshift.io/v1 kind: Network metadata: name: cluster spec: externalIP: policy: null ...
17.2.3. ExternalIP アドレスブロックの設定
ExternalIP アドレスブロックの設定は、cluster という名前の Network カスタムリソース (CR) で定義されます。ネットワーク CR は config.openshift.io API グループに含まれます。
クラスターのインストール時に、Cluster Version Operator (CVO) は cluster という名前のネットワーク CR を自動的に作成します。このタイプのその他の CR オブジェクトの作成はサポートされていません。
以下の YAML は ExternalIP 設定について説明しています。
cluster という名前の network.config.openshift.io CR
apiVersion: config.openshift.io/v1
kind: Network
metadata:
name: cluster
spec:
externalIP:
autoAssignCIDRs: []
policy:
...
以下の YAML は、policy スタンザのフィールドについて説明しています。
Network.config.openshift.io policy スタンザ
policy:
allowedCIDRs: []
rejectedCIDRs: [] 外部 IP 設定の例
外部 IP アドレスプールの予想される複数の設定が以下の例で表示されています。
以下の YAML は、自動的に割り当てられた外部 IP アドレスを有効にする設定について説明しています。
spec.externalIP.autoAssignCIDRsが設定された設定例apiVersion: config.openshift.io/v1 kind: Network metadata: name: cluster spec: ... externalIP: autoAssignCIDRs: - 192.168.132.254/29以下の YAML は、許可された、および拒否された CIDR 範囲のポリシールールを設定します。
spec.externalIP.policyが設定された設定例apiVersion: config.openshift.io/v1 kind: Network metadata: name: cluster spec: ... externalIP: policy: allowedCIDRs: - 192.168.132.0/29 - 192.168.132.8/29 rejectedCIDRs: - 192.168.132.7/32
17.2.4. クラスターの外部 IP アドレスブロックの設定
クラスター管理者は、以下の ExternalIP を設定できます。
-
Serviceオブジェクトのspec.clusterIPフィールドを自動的に設定するために OpenShift Container Platform によって使用される ExternalIP アドレスブロック。 -
IP アドレスを制限するポリシーオブジェクトは
Serviceオブジェクトのspec.clusterIP配列に手動で割り当てられます。
前提条件
-
OpenShift CLI (
oc) をインストールしている。 -
cluster-adminロールを持つユーザーとしてクラスターにアクセスできる。
手順
オプション: 現在の外部 IP 設定を表示するには、以下のコマンドを入力します。
$ oc describe networks.config cluster設定を編集するには、以下のコマンドを入力します。
$ oc edit networks.config cluster以下の例のように ExternalIP 設定を変更します。
apiVersion: config.openshift.io/v1 kind: Network metadata: name: cluster spec: ... externalIP:1 ...- 1
externalIPスタンザの設定を指定します。
更新された ExternalIP 設定を確認するには、以下のコマンドを入力します。
$ oc get networks.config cluster -o go-template='{{.spec.externalIP}}{{"\n"}}'
17.2.5. 次のステップ
17.3. Ingress コントローラーを使用した Ingress クラスターの設定
OpenShift Container Platform は、クラスター内で実行されるサービスを使ってクラスター外からの通信を可能にする方法を提供します。この方法は Ingress コントローラーを使用します。
17.3.1. Ingress コントローラーおよびルートの使用
Ingress Operator は Ingress コントローラーおよびワイルドカード DNS を管理します。
Ingress コントローラーの使用は、OpenShift Container Platform クラスターへの外部アクセスを許可するための最も一般的な方法です。
Ingress コントローラーは外部要求を許可し、設定されたルートに基づいてそれらをプロキシー送信するよう設定されます。これは、HTTP、SNI を使用する HTTPS、SNI を使用する TLS に限定されており、SNI を使用する TLS で機能する Web アプリケーションやサービスには十分な設定です。
管理者と連携して Ingress コントローラーを設定します。外部要求を許可し、設定されたルートに基づいてそれらをプロキシー送信するように Ingress コントローラーを設定します。
管理者はワイルドカード DNS エントリーを作成してから Ingress コントローラーを設定できます。その後は管理者に問い合わせることなく edge Ingress コントローラーと連携できます。
デフォルトで、クラスター内のすべての Ingress コントローラーはクラスター内の任意のプロジェクトで作成されたすべてのルートを許可します。
Ingress コントローラー:
- デフォルトでは 2 つのレプリカがあるので、これは 2 つのワーカーノードで実行する必要があります。
- 追加のノードにレプリカを組み込むためにスケールアップすることができます。
このセクションの手順では、クラスターの管理者が事前に行っておく必要のある前提条件があります。
17.3.2. 前提条件
以下の手順を開始する前に、管理者は以下の条件を満たしていることを確認する必要があります。
- 要求がクラスターに到達できるように、クラスターネットワーク環境に対して外部ポートをセットアップします。
クラスター管理者ロールを持つユーザーが 1 名以上いることを確認します。このロールをユーザーに追加するには、以下のコマンドを実行します。
$ oc adm policy add-cluster-role-to-user cluster-admin username- OpenShift Container Platform クラスターを、1 つ以上のマスターと 1 つ以上のノード、およびクラスターへのネットワークアクセスのあるクラスター外のシステムと共に用意します。この手順では、外部システムがクラスターと同じサブセットにあることを前提とします。別のサブセットの外部システムに必要な追加のネットワーク設定については、このトピックでは扱いません。
17.3.3. プロジェクトおよびサービスの作成
公開するプロジェクトおよびサービスが存在しない場合、最初にプロジェクトを作成し、次にサービスを作成します。
プロジェクトおよびサービスがすでに存在する場合は、サービスを公開してルートを作成する手順に進みます。
前提条件
-
クラスター管理者として
ocCLI をインストールし、ログインします。
手順
oc new-projectコマンドを実行して、サービス用の新しいプロジェクトを作成します。$ oc new-project myprojectoc new-appコマンドを使用してサービスを作成します。$ oc new-app nodejs:12~https://github.com/sclorg/nodejs-ex.gitサービスが作成されたことを確認するには、以下のコマンドを実行します。
$ oc get svc -n myproject出力例
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE nodejs-ex ClusterIP 172.30.197.157 <none> 8080/TCP 70sデフォルトで、新規サービスには外部 IP アドレスがありません。
17.3.4. ルートの作成によるサービスの公開
oc expose コマンドを使用して、サービスをルートとして公開することができます。
手順
サービスを公開するには、以下を実行します。
- OpenShift Container Platform にログインします。
公開するサービスが置かれているプロジェクトにログインします。
$ oc project myprojectoc expose serviceコマンドを実行して、ルートを公開します。$ oc expose service nodejs-ex出力例
route.route.openshift.io/nodejs-ex exposedサービスが公開されていることを確認するには、cURL などのツールを使って、クラスター外からサービスにアクセスできることを確認します。
ルートのホスト名を調べるには、
oc get routeコマンドを使用します。$ oc get route出力例
NAME HOST/PORT PATH SERVICES PORT TERMINATION WILDCARD nodejs-ex nodejs-ex-myproject.example.com nodejs-ex 8080-tcp NonecURL を使用して、ホストが GET 要求に応答することを確認します。
$ curl --head nodejs-ex-myproject.example.com出力例
HTTP/1.1 200 OK ...
17.3.5. ルートラベルを使用した Ingress コントローラーのシャード化の設定
ルートラベルを使用した Ingress コントローラーのシャード化とは、Ingress コントローラーがルートセレクターによって選択される任意 namespace の任意のルートを提供することを意味します。
Ingress コントローラーのシャード化は、一連の Ingress コントローラー間で着信トラフィックの負荷を分散し、トラフィックを特定の Ingress コントローラーに分離する際に役立ちます。たとえば、Company A のトラフィックをある Ingress コントローラーに指定し、Company B を別の Ingress コントローラーに指定できます。
手順
router-internal.yamlファイルを編集します。# cat router-internal.yaml apiVersion: v1 items: - apiVersion: operator.openshift.io/v1 kind: IngressController metadata: name: sharded namespace: openshift-ingress-operator spec: domain: <apps-sharded.basedomain.example.net> nodePlacement: nodeSelector: matchLabels: node-role.kubernetes.io/worker: "" routeSelector: matchLabels: type: sharded status: {} kind: List metadata: resourceVersion: "" selfLink: ""Ingress コントローラーの
router-internal.yamlファイルを適用します。# oc apply -f router-internal.yamlIngress コントローラーは、
type: shardedというラベルのある namespace のルートを選択します。
17.3.6. namespace ラベルを使用した Ingress コントローラーのシャード化の設定
namespace ラベルを使用した Ingress コントローラーのシャード化とは、Ingress コントローラーが namespace セレクターによって選択される任意の namespace の任意のルートを提供することを意味します。
Ingress コントローラーのシャード化は、一連の Ingress コントローラー間で着信トラフィックの負荷を分散し、トラフィックを特定の Ingress コントローラーに分離する際に役立ちます。たとえば、Company A のトラフィックをある Ingress コントローラーに指定し、Company B を別の Ingress コントローラーに指定できます。
Keepalived Ingress VIP をデプロイする場合は、endpoint Publishing Strategy パラメーターに Host Network の値が割り当てられた、デフォルト以外の Ingress Controller をデプロイしないでください。デプロイしてしまうと、問題が発生する可能性があります。endpoint Publishing Strategy に Host Network ではなく、Node Port という値を使用してください。
手順
router-internal.yamlファイルを編集します。# cat router-internal.yaml出力例
apiVersion: v1 items: - apiVersion: operator.openshift.io/v1 kind: IngressController metadata: name: sharded namespace: openshift-ingress-operator spec: domain: <apps-sharded.basedomain.example.net> nodePlacement: nodeSelector: matchLabels: node-role.kubernetes.io/worker: "" namespaceSelector: matchLabels: type: sharded status: {} kind: List metadata: resourceVersion: "" selfLink: ""Ingress コントローラーの
router-internal.yamlファイルを適用します。# oc apply -f router-internal.yamlIngress コントローラーは、
type: shardedというラベルのある namespace セレクターによって選択される namespace のルートを選択します。
17.4. ロードバランサーを使用した ingress クラスターの設定
OpenShift Container Platform は、クラスター内で実行されるサービスを使ってクラスター外からの通信を可能にする方法を提供します。この方法では、ロードバランサーを使用します。
17.4.1. ロードバランサーを使用したトラフィックのクラスターへの送信
特定の外部 IP アドレスを必要としない場合、ロードバランサーサービスを OpenShift Container Platform クラスターへの外部アクセスを許可するよう設定することができます。
ロードバランサーサービスは固有の IP を割り当てます。ロードバランサーには単一の edge ルーター IP があります (これは仮想 IP (VIP) の場合もありますが、初期の負荷分散では単一マシンになります。
プールが設定される場合、これはクラスター管理者によってではなく、インフラストラクチャーレベルで実行されます。
このセクションの手順では、クラスターの管理者が事前に行っておく必要のある前提条件があります。
17.4.2. 前提条件
以下の手順を開始する前に、管理者は以下の条件を満たしていることを確認する必要があります。
- 要求がクラスターに到達できるように、クラスターネットワーク環境に対して外部ポートをセットアップします。
クラスター管理者ロールを持つユーザーが 1 名以上いることを確認します。このロールをユーザーに追加するには、以下のコマンドを実行します。
$ oc adm policy add-cluster-role-to-user cluster-admin username- OpenShift Container Platform クラスターを、1 つ以上のマスターと 1 つ以上のノード、およびクラスターへのネットワークアクセスのあるクラスター外のシステムと共に用意します。この手順では、外部システムがクラスターと同じサブセットにあることを前提とします。別のサブセットの外部システムに必要な追加のネットワーク設定については、このトピックでは扱いません。
17.4.3. プロジェクトおよびサービスの作成
公開するプロジェクトおよびサービスが存在しない場合、最初にプロジェクトを作成し、次にサービスを作成します。
プロジェクトおよびサービスがすでに存在する場合は、サービスを公開してルートを作成する手順に進みます。
前提条件
-
クラスター管理者として
ocCLI をインストールし、ログインします。
手順
oc new-projectコマンドを実行して、サービス用の新しいプロジェクトを作成します。$ oc new-project myprojectoc new-appコマンドを使用してサービスを作成します。$ oc new-app nodejs:12~https://github.com/sclorg/nodejs-ex.gitサービスが作成されたことを確認するには、以下のコマンドを実行します。
$ oc get svc -n myproject出力例
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE nodejs-ex ClusterIP 172.30.197.157 <none> 8080/TCP 70sデフォルトで、新規サービスには外部 IP アドレスがありません。
17.4.4. ルートの作成によるサービスの公開
oc expose コマンドを使用して、サービスをルートとして公開することができます。
手順
サービスを公開するには、以下を実行します。
- OpenShift Container Platform にログインします。
公開するサービスが置かれているプロジェクトにログインします。
$ oc project myprojectoc expose serviceコマンドを実行して、ルートを公開します。$ oc expose service nodejs-ex出力例
route.route.openshift.io/nodejs-ex exposedサービスが公開されていることを確認するには、cURL などのツールを使って、クラスター外からサービスにアクセスできることを確認します。
ルートのホスト名を調べるには、
oc get routeコマンドを使用します。$ oc get route出力例
NAME HOST/PORT PATH SERVICES PORT TERMINATION WILDCARD nodejs-ex nodejs-ex-myproject.example.com nodejs-ex 8080-tcp NonecURL を使用して、ホストが GET 要求に応答することを確認します。
$ curl --head nodejs-ex-myproject.example.com出力例
HTTP/1.1 200 OK ...
17.4.5. ロードバランサーサービスの作成
以下の手順を使用して、ロードバランサーサービスを作成します。
前提条件
- 公開するプロジェクトとサービスがあること。
手順
ロードバランサーサービスを作成するには、以下を実行します。
- OpenShift Container Platform にログインします。
公開するサービスが置かれているプロジェクトを読み込みます。
$ oc project project1コントロールプレーンノード (別名マスターノード) でテキストファイルを開き、以下のテキストを貼り付け、必要に応じてファイルを編集します。
ロードバランサー設定ファイルのサンプル
apiVersion: v1 kind: Service metadata: name: egress-21 spec: ports: - name: db port: 33062 loadBalancerIP: loadBalancerSourceRanges:3 - 10.0.0.0/8 - 192.168.0.0/16 type: LoadBalancer4 selector: name: mysql5 注記ロードバランサーを介して特定の IP アドレスへのトラフィックを制限するには、
loadBalancerSourceRangesフィールドを設定するのではなく、service.beta.kubernetes.io/load-balancer-source-rangesアノテーションを使用することが推奨されます。アノテーションを使用すると、OpenShift API により簡単に移行でき、今後のリリースで実装されます。- ファイルを保存し、終了します。
以下のコマンドを実行してサービスを作成します。
$ oc create -f <file-name>以下に例を示します。
$ oc create -f mysql-lb.yaml以下のコマンドを実行して新規サービスを表示します。
$ oc get svc出力例
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE egress-2 LoadBalancer 172.30.22.226 ad42f5d8b303045-487804948.example.com 3306:30357/TCP 15m有効にされたクラウドプロバイダーがある場合、サービスには外部 IP アドレスが自動的に割り当てられます。
マスターで cURL などのツールを使用し、パブリック IP アドレスを使用してサービスに到達できることを確認します。
$ curl <public-ip>:<port>以下に例を示します。
$ curl 172.29.121.74:3306このセクションの例では、クライアントアプリケーションを必要とする MySQL サービスを使用しています。
Got packets out of orderのメッセージと共に文字ストリングを取得する場合は、このサービスに接続していることになります。MySQL クライアントがある場合は、標準 CLI コマンドでログインします。
$ mysql -h 172.30.131.89 -u admin -p出力例
Enter password: Welcome to the MariaDB monitor. Commands end with ; or \g. MySQL [(none)]>
17.5. ネットワークロードバランサーを使用した AWS での ingress クラスタートラフィックの設定
OpenShift Container Platform は、クラスター内で実行されるサービスを使ってクラスター外からの通信を可能にする方法を提供します。この方法では、クライアントの IP アドレスをノードに転送する Network Load Balancer (NLB) を使用します。NLB を新規または既存の AWS クラスターに設定することができます。
17.5.1. Ingress Controller Classic Load Balancer の Network Load Balancer への置き換え
Classic Load Balancer (CLB) を使用している Ingress Controller は、AWS の Network Load Balancer (NLB) を使用している Ingress Controller に置き換えることができます。
この手順を実行すると、新しい DNS レコードの伝搬、新しいロードバランサーのプロビジョニングなどの要因により、数分間にわたる障害が発生することが予想されます。この手順を適用すると、Ingress Controller ロードバランサーの IP アドレスや正規名が変更になる場合があります。
手順
新しいデフォルトの Ingress Controller を含むファイルを作成します。以下の例では、デフォルトの Ingress Controller の範囲が
Externalで、その他のカスタマイズをしていないことを想定しています。ingresscontroller.ymlファイルの例apiVersion: operator.openshift.io/v1 kind: IngressController metadata: creationTimestamp: null name: default namespace: openshift-ingress-operator spec: endpointPublishingStrategy: loadBalancer: scope: External providerParameters: type: AWS aws: type: NLB type: LoadBalancerServiceデフォルトの Ingress Controller が他にカスタマイズされている場合には、それに応じてファイルを修正してください。
Ingress Controller の YAML ファイルを強制的に置き換えます。
$ oc replace --force --wait -f ingresscontroller.ymlIngress Controller の置き換えが完了するまでお待ちください。数分ほど、サービスが停止します。
17.5.2. 既存 AWS クラスターでの Ingress コントローラーネットワークロードバランサーの設定
AWS Network Load Balancer (NLB) がサポートする Ingress コントローラーを既存のクラスターに作成できます。
前提条件
- AWS クラスターがインストールされている。
インフラストラクチャーリソースの
PlatformStatusは AWS である必要があります。PlatformStatusが AWS であることを確認するには、以下を実行します。$ oc get infrastructure/cluster -o jsonpath='{.status.platformStatus.type}' AWS
手順
既存のクラスターの AWS NLB がサポートする Ingress コントローラーを作成します。
Ingress コントローラーのマニフェストを作成します。
$ cat ingresscontroller-aws-nlb.yaml出力例
apiVersion: operator.openshift.io/v1 kind: IngressController metadata: name: $my_ingress_controller1 namespace: openshift-ingress-operator spec: domain: $my_unique_ingress_domain2 endpointPublishingStrategy: type: LoadBalancerService loadBalancer: scope: External3 providerParameters: type: AWS aws: type: NLBクラスターにリソースを作成します。
$ oc create -f ingresscontroller-aws-nlb.yaml
新規 AWS クラスターで Ingress コントローラー NLB を設定する前に、インストール設定ファイルの作成 手順を実行する必要があります。
17.5.3. 新規 AWS クラスターでの Ingress コントローラーネットワークロードバランサーの設定
新規クラスターに AWS Network Load Balancer (NLB) がサポートする Ingress コントローラーを作成できます。
前提条件
-
install-config.yamlファイルを作成し、これに対する変更を完了します。
手順
新規クラスターの AWS NLB がサポートする Ingress コントローラーを作成します。
インストールプログラムが含まれるディレクトリーに切り替え、マニフェストを作成します。
$ ./openshift-install create manifests --dir <installation_directory>1 - 1
<installation_directory>については、クラスターのinstall-config.yamlファイルが含まれるディレクトリーの名前を指定します。
cluster-ingress-default-ingresscontroller.yamlという名前のファイルを<installation_directory>/manifests/ディレクトリーに作成します。$ touch <installation_directory>/manifests/cluster-ingress-default-ingresscontroller.yaml1 - 1
<installation_directory>については、クラスターのmanifests/ディレクトリーが含まれるディレクトリー名を指定します。
ファイルの作成後は、以下のようにいくつかのネットワーク設定ファイルが
manifests/ディレクトリーに置かれます。$ ls <installation_directory>/manifests/cluster-ingress-default-ingresscontroller.yaml出力例
cluster-ingress-default-ingresscontroller.yamlエディターで
cluster-ingress-default-ingresscontroller.yamlファイルを開き、必要な Operator 設定を記述するカスタムリソース (CR) を入力します。apiVersion: operator.openshift.io/v1 kind: IngressController metadata: creationTimestamp: null name: default namespace: openshift-ingress-operator spec: endpointPublishingStrategy: loadBalancer: scope: External providerParameters: type: AWS aws: type: NLB type: LoadBalancerService-
cluster-ingress-default-ingresscontroller.yamlファイルを保存し、テキストエディターを終了します。 -
オプション:
manifests/cluster-ingress-default-ingresscontroller.yamlファイルをバックアップします。インストールプログラムは、クラスターの作成時にmanifests/ディレクトリーを削除します。
17.6. サービスの外部 IP を使用した ingress クラスタートラフィックの設定
外部 IP アドレスをサービスに割り当てることで、これをクラスター外のトラフィックで使用できるようにします。通常、これはベアメタルハードウェアにインストールされているクラスターの場合にのみ役立ちます。外部ネットワークインフラストラクチャーは、トラフィックをサービスにルーティングするように正しく設定される必要があります。
17.6.1. 前提条件
- クラスターは ExternalIP が有効にされた状態で設定されます。詳細は、サービスの ExternalIP の設定 について参照してください。
17.6.2. ExternalIP のサービスへの割り当て
ExternalIP をサービスに割り当てることができます。クラスターが ExternalIP を自動的に割り当てするように設定されている場合、ExternalIP をサービスに手動で割り当てる必要がない場合があります。
手順
オプション: ExternalIP で使用するために設定される IP アドレス範囲を確認するには、以下のコマンドを入力します。
$ oc get networks.config cluster -o jsonpath='{.spec.externalIP}{"\n"}'autoAssignCIDRsが設定されている場合、spec.externalIPsフィールドが指定されていない場合、 OpenShift Container Platform は ExternalIP を新規Serviceオブジェクトに自動的に割り当てます。ExternalIP をサービスに割り当てます。
新規サービスを作成する場合は、
spec.externalIPsフィールドを指定し、1 つ以上の有効な IP アドレスの配列を指定します。以下に例を示します。apiVersion: v1 kind: Service metadata: name: svc-with-externalip spec: ... externalIPs: - 192.174.120.10ExternalIP を既存のサービスに割り当てる場合は、以下のコマンドを入力します。
<name>をサービス名に置き換えます。<ip_address>を有効な ExternalIP アドレスに置き換えます。コンマで区切られた複数の IP アドレスを指定できます。$ oc patch svc <name> -p \ '{ "spec": { "externalIPs": [ "<ip_address>" ] } }'以下に例を示します。
$ oc patch svc mysql-55-rhel7 -p '{"spec":{"externalIPs":["192.174.120.10"]}}'出力例
"mysql-55-rhel7" patched
ExternalIP アドレスがサービスに割り当てられていることを確認するには、以下のコマンドを入力します。新規サービスに ExternalIP を指定した場合、まずサービスを作成する必要があります。
$ oc get svc出力例
NAME CLUSTER-IP EXTERNAL-IP PORT(S) AGE mysql-55-rhel7 172.30.131.89 192.174.120.10 3306/TCP 13m
17.7. NodePort を使用した ingress クラスタートラフィックの設定
OpenShift Container Platform は、クラスター内で実行されるサービスを使ってクラスター外からの通信を可能にする方法を提供します。この方法は NodePort を使用します。
17.7.1. NodePort を使用したトラフィックのクラスターへの送信
NodePort-type Service リソースを使用して、クラスター内のすべてのノードの特定のポートでサービスを公開します。ポートは Service リソースの .spec.ports[*].nodePort フィールドで指定されます。
ノードポートを使用するには、追加のポートリソースが必要です。
NodePort は、ノードの IP アドレスの静的ポートでサービスを公開します。NodePort はデフォルトで 30000 から 32767 の範囲に置かれます。つまり、 NodePort はサービスの意図されるポートに一致しないことが予想されます。たとえば、ポート 8080 はノードのポート 31020 として公開できます。
管理者は、外部 IP アドレスがノードにルーティングされることを確認する必要があります。
NodePort および外部 IP は独立しており、両方を同時に使用できます。
このセクションの手順では、クラスターの管理者が事前に行っておく必要のある前提条件があります。
17.7.2. 前提条件
以下の手順を開始する前に、管理者は以下の条件を満たしていることを確認する必要があります。
- 要求がクラスターに到達できるように、クラスターネットワーク環境に対して外部ポートをセットアップします。
クラスター管理者ロールを持つユーザーが 1 名以上いることを確認します。このロールをユーザーに追加するには、以下のコマンドを実行します。
$ oc adm policy add-cluster-role-to-user cluster-admin <user_name>- OpenShift Container Platform クラスターを、1 つ以上のマスターと 1 つ以上のノード、およびクラスターへのネットワークアクセスのあるクラスター外のシステムと共に用意します。この手順では、外部システムがクラスターと同じサブセットにあることを前提とします。別のサブセットの外部システムに必要な追加のネットワーク設定については、このトピックでは扱いません。
17.7.3. プロジェクトおよびサービスの作成
公開するプロジェクトおよびサービスが存在しない場合、最初にプロジェクトを作成し、次にサービスを作成します。
プロジェクトおよびサービスがすでに存在する場合は、サービスを公開してルートを作成する手順に進みます。
前提条件
-
クラスター管理者として
ocCLI をインストールし、ログインします。
手順
oc new-projectコマンドを実行して、サービス用の新しいプロジェクトを作成します。$ oc new-project myprojectoc new-appコマンドを使用してサービスを作成します。$ oc new-app nodejs:12~https://github.com/sclorg/nodejs-ex.gitサービスが作成されたことを確認するには、以下のコマンドを実行します。
$ oc get svc -n myproject出力例
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE nodejs-ex ClusterIP 172.30.197.157 <none> 8080/TCP 70sデフォルトで、新規サービスには外部 IP アドレスがありません。
17.7.4. ルートの作成によるサービスの公開
oc expose コマンドを使用して、サービスをルートとして公開することができます。
手順
サービスを公開するには、以下を実行します。
- OpenShift Container Platform にログインします。
公開するサービスが置かれているプロジェクトにログインします。
$ oc project myprojectアプリケーションのノードポートを公開するには、以下のコマンドを入力します。OpenShift Container Platform は
30000-32767範囲の利用可能なポートを自動的に選択します。$ oc expose service nodejs-ex --type=NodePort --name=nodejs-ex-nodeport --generator="service/v2"出力例
service/nodejs-ex-nodeport exposedオプション: サービスが公開されるノードポートで利用可能なことを確認するには、以下のコマンドを入力します。
$ oc get svc -n myproject出力例
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE nodejs-ex ClusterIP 172.30.217.127 <none> 3306/TCP 9m44s nodejs-ex-ingress NodePort 172.30.107.72 <none> 3306:31345/TCP 39sオプション:
oc new-appコマンドによって自動的に作成されたサービスを削除するには、以下のコマンドを入力します。$ oc delete svc nodejs-ex
第18章 Kubernetes NMState
18.1. Kubernetes NMState Operator について
Kubernetes NMState Operator は、NMState の OpenShift Container Platform クラスターのノード間でステートドリブンのネットワーク設定を実行するための Kubernetes API を提供します。Kubernetes NMState Operator は、ユーザーに対して、クラスターノードの各種のネットワークインターフェイスタイプ、DNS、およびルーティングを設定する機能を提供します。さらに、クラスターノードのデーモンは、各ノードの API サーバーへのネットワークインターフェイスの状態の定期的な報告を行います。
Kubernetes NMState Operator はテクノロジープレビュー機能としてのみご利用いただけます。テクノロジープレビュー機能は、Red Hat 製品のサービスレベルアグリーメント (SLA) の対象外であり、機能的に完全ではないことがあります。Red Hat は実稼働環境でこれらを使用することを推奨していません。テクノロジープレビューの機能は、最新の製品機能をいち早く提供して、開発段階で機能のテストを行いフィードバックを提供していただくことを目的としています。
Red Hat のテクノロジープレビュー機能のサポート範囲についての詳細は、https://access.redhat.com/ja/support/offerings/techpreview/ を参照してください。
OpenShift Container Platform で NMState を使用する前に、Kubernetes NMState Operator をインストールする必要があります。
18.1.1. Kubernetes NMState Operator のインストール
管理者権限でログインし、OpenShift Web コンソールから Kubernetes NMState Operator をインストールする必要があります。インストールが完了すると、Operator はすべてのクラスターノードに NMState State Controller をデーモンセットとしてデプロイできます。
手順
- Operators → OperatorHub を選択します。
-
All Items の下の検索フィールドに、
nmstateと入力し、Enter をクリックして Kubernetes NMState Operator を検索します。 - Kubernetes NMState Operator の検索結果をクリックします。
- Install をクリックして、Install Operator ウィンドウを開きます。
-
Installed Namespace で、namespace が
openshift-nmstateであることを確認します。openshift-nmstateがコンボボックスに存在しない場合は、Create Namespace をクリックし、ダイアログボックスの Name フィールドにopenshift-nmstateを入力し、Create を押します。 - Install をクリックして Operator をインストールします。
- Operator のインストールが完了したら、View Operator をクリックします。
-
Provided APIs で Create Instance をクリックし、
kubernetes-nmstateのインスタンスを作成するダイアログボックスを開きます。 ダイアログボックスの Name フィールドで、インスタンスの名前が
nmstateであることを確認します。注記名前の制限は既知の問題です。インスタンスはクラスター全体のシングルトンです。
- デフォルト設定を受け入れ、Create をクリックしてインスタンスを作成します。
概要
完了後に、Operator はすべてのクラスターノードに NMState State Controller をデーモンセットとしてデプロイしています。
18.2. ノードのネットワーク状態の確認
ノードのネットワーク状態は、クラスター内のすべてのノードのネットワーク設定です。
18.2.1. nmstate について
OpenShift Container Platform は nmstate を使用して、ノードネットワークの状態を報告し、これを設定します。これにより、単一の設定マニフェストをクラスターに適用して、すべてのノードに Linux ブリッジを作成するなどして、ネットワークポリシーの設定を変更することができます。
ノードのネットワークは、以下のオブジェクトによって監視され更新されます。
NodeNetworkState- そのノード上のネットワークの状態を報告します。
NodeNetworkConfigurationPolicy-
ノードで要求されるネットワーク設定について説明します。
NodeNetworkConfigurationPolicyマニフェストをクラスターに適用して、インターフェイスの追加および削除など、ノードネットワーク設定を更新します。 NodeNetworkConfigurationEnactment- 各ノードに制定されたネットワークポリシーを報告します。
OpenShift Container Platform は、以下の nmstate インターフェイスタイプの使用をサポートします。
- Linux Bridge
- VLAN
- Bond
- イーサネット
OpenShift Container Platform クラスターが OVN-Kubernetes をデフォルトの Container Network Interface (CNI) プロバイダーとして使用する場合、OVN-Kubernetes のホストネットワークトポロジーの変更により、Linux ブリッジまたはボンディングをホストのデフォルトインターフェイスに割り当てることはできません。回避策として、ホストに接続されたセカンダリーネットワークインターフェイスを使用するか、OpenShift SDN デフォルト CNI プロバイダーに切り替えることができます。
18.2.2. ノードのネットワーク状態の表示
NodeNetworkState オブジェクトはクラスター内のすべてのノードにあります。このオブジェクトは定期的に更新され、ノードのネットワークの状態を取得します。
手順
クラスターのすべての
NodeNetworkStateオブジェクトを一覧表示します。$ oc get nnsNodeNetworkStateオブジェクトを検査して、そのノードにネットワークを表示します。この例の出力は、明確にするために編集されています。$ oc get nns node01 -o yaml出力例
apiVersion: nmstate.io/v1beta1 kind: NodeNetworkState metadata: name: node011 status: currentState:2 dns-resolver: ... interfaces: ... route-rules: ... routes: ... lastSuccessfulUpdateTime: "2020-01-31T12:14:00Z"3
18.3. ノードのネットワーク設定の更新
NodeNetworkConfigurationPolicy マニフェストをクラスターに適用して、ノードからのインターフェイスの追加または削除など、ノードネットワーク設定を更新できます。
18.3.1. nmstate について
OpenShift Container Platform は nmstate を使用して、ノードネットワークの状態を報告し、これを設定します。これにより、単一の設定マニフェストをクラスターに適用して、すべてのノードに Linux ブリッジを作成するなどして、ネットワークポリシーの設定を変更することができます。
ノードのネットワークは、以下のオブジェクトによって監視され更新されます。
NodeNetworkState- そのノード上のネットワークの状態を報告します。
NodeNetworkConfigurationPolicy-
ノードで要求されるネットワーク設定について説明します。
NodeNetworkConfigurationPolicyマニフェストをクラスターに適用して、インターフェイスの追加および削除など、ノードネットワーク設定を更新します。 NodeNetworkConfigurationEnactment- 各ノードに制定されたネットワークポリシーを報告します。
OpenShift Container Platform は、以下の nmstate インターフェイスタイプの使用をサポートします。
- Linux Bridge
- VLAN
- Bond
- イーサネット
OpenShift Container Platform クラスターが OVN-Kubernetes をデフォルトの Container Network Interface (CNI) プロバイダーとして使用する場合、OVN-Kubernetes のホストネットワークトポロジーの変更により、Linux ブリッジまたはボンディングをホストのデフォルトインターフェイスに割り当てることはできません。回避策として、ホストに接続されたセカンダリーネットワークインターフェイスを使用するか、OpenShift SDN デフォルト CNI プロバイダーに切り替えることができます。
18.3.2. ノード上でのインターフェイスの作成
NodeNetworkConfigurationPolicy マニフェストをクラスターに適用してクラスター内のノード上にインターフェイスを作成します。マニフェストには、インターフェイスの要求された設定の詳細が含まれます。
デフォルトでは、マニフェストはクラスター内のすべてのノードに適用されます。インターフェイスを特定ノードに追加するには、ノードセレクターの spec: nodeSelector パラメーターおよび適切な <key>:<value> を追加します。
手順
NodeNetworkConfigurationPolicyマニフェストを作成します。以下の例は、すべてのワーカーノードで Linux ブリッジを設定します。apiVersion: nmstate.io/v1beta1 kind: NodeNetworkConfigurationPolicy metadata: name: <br1-eth1-policy>1 spec: nodeSelector:2 node-role.kubernetes.io/worker: ""3 desiredState: interfaces: - name: br1 description: Linux bridge with eth1 as a port4 type: linux-bridge state: up ipv4: dhcp: true enabled: true bridge: options: stp: enabled: false port: - name: eth1ノードのネットワークポリシーを作成します。
$ oc apply -f <br1-eth1-policy.yaml>1 - 1
- ノードネットワーク設定ポリシーマニフェストのファイル名。
関連情報
18.3.3. ノード上でのノードネットワークポリシー更新の確認
NodeNetworkConfigurationPolicy マニフェストは、クラスターのノードについて要求されるネットワーク設定を記述します。ノードネットワークポリシーには、要求されたネットワーク設定と、クラスター全体でのポリシーの実行ステータスが含まれます。
ノードネットワークポリシーを適用する際に、NodeNetworkConfigurationEnactment オブジェクトがクラスター内のすべてのノードについて作成されます。ノードネットワーク設定の enactment (実行) は、そのノードでのポリシーの実行ステータスを表す読み取り専用オブジェクトです。ポリシーがノードに適用されない場合、そのノードの enactment (実行) にはトラブルシューティングのためのトレースバックが含まれます。
手順
ポリシーがクラスターに適用されていることを確認するには、ポリシーとそのステータスを一覧表示します。
$ oc get nncpオプション: ポリシーの設定に想定されている以上の時間がかかる場合は、特定のポリシーの要求される状態とステータスの状態を検査できます。
$ oc get nncp <policy> -o yamlオプション: ポリシーのすべてのノード上での設定に想定されている以上の時間がかかる場合は、クラスターの enactment (実行) のステータスを一覧表示できます。
$ oc get nnceオプション: 特定の enactment (実行) の設定 (失敗した設定のエラーレポートを含む) を表示するには、以下を実行します。
$ oc get nnce <node>.<policy> -o yaml
18.3.4. ノードからインターフェイスの削除
NodeNetworkConfigurationPolicy オブジェクトを編集し、インターフェイスの state を absent に設定して、クラスターの 1 つ以上のノードからインターフェイスを削除できます。
ノードからインターフェイスを削除しても、ノードのネットワーク設定は以前の状態に自動的に復元されません。以前の状態に復元する場合、そのノードのネットワーク設定をポリシーで定義する必要があります。
ブリッジまたはボンディングインターフェイスを削除すると、そのブリッジまたはボンディングインターフェイスに以前に接続されたか、またはそれらの下位にあるノード NIC は down の状態になり、到達できなくなります。接続が失われないようにするには、同じポリシーでノード NIC を設定し、ステータスを up にし、DHCP または静的 IP アドレスのいずれかになるようにします。
インターフェイスを追加したポリシーを削除しても、ノード上のポリシーの設定は変更されません。NodeNetworkConfigurationPolicy はクラスターのオブジェクトですが、これは要求される設定のみを表します。
同様に、インターフェイスを削除してもポリシーは削除されません。
手順
インターフェイスの作成に使用する
NodeNetworkConfigurationPolicyマニフェストを更新します。以下の例は Linux ブリッジを削除し、接続が失われないように DHCP でeth1NIC を設定します。apiVersion: nmstate.io/v1beta1 kind: NodeNetworkConfigurationPolicy metadata: name: <br1-eth1-policy>1 spec: nodeSelector:2 node-role.kubernetes.io/worker: ""3 desiredState: interfaces: - name: br1 type: linux-bridge state: absent4 - name: eth15 type: ethernet6 state: up7 ipv4: dhcp: true8 enabled: true9 - 1
- ポリシーの名前。
- 2
- オプション:
nodeSelectorパラメーターを含めない場合、ポリシーはクラスター内のすべてのノードに適用されます。 - 3
- この例では
node-role.kubernetes.io/worker: ""ノードセレクターを使用し、クラスター内のすべてのワーカーノードを選択します。 - 4
- 状態を
absentに変更すると、インターフェイスが削除されます。 - 5
- ブリッジインターフェイスから接続が解除されるインターフェイスの名前。
- 6
- インターフェイスのタイプ。この例では、イーサネットネットワークインターフェイスを作成します。
- 7
- インターフェイスの要求された状態。
- 8
- オプション:
dhcpを使用しない場合は、静的 IP を設定するか、IP アドレスなしでインターフェイスを出ることができます。 - 9
- この例では
ipv4を有効にします。
ノード上でポリシーを更新し、インターフェイスを削除します。
$ oc apply -f <br1-eth1-policy.yaml>1 - 1
- ポリシーマニフェストのファイル名。
18.3.5. 異なるインターフェイスのポリシー設定の例
18.3.5.1. 例: Linux ブリッジインターフェイスノードネットワーク設定ポリシー
NodeNetworkConfigurationPolicy マニフェストをクラスターに適用してクラスター内のノード上に Linux ブリッジインターフェイスを作成します。
以下の YAML ファイルは、Linux ブリッジインターフェイスのマニフェストの例です。これには、独自の情報で置き換える必要のあるサンプルの値が含まれます。
apiVersion: nmstate.io/v1beta1
kind: NodeNetworkConfigurationPolicy
metadata:
name: br1-eth1-policy
spec:
nodeSelector:
kubernetes.io/hostname: <node01>
desiredState:
interfaces:
- name: br1
description: Linux bridge with eth1 as a port
type: linux-bridge
state: up
ipv4:
dhcp: true
enabled: true
bridge:
options:
stp:
enabled: false
port:
- name: eth1 - 1
- ポリシーの名前。
- 2
- オプション:
nodeSelectorパラメーターを含めない場合、ポリシーはクラスター内のすべてのノードに適用されます。 - 3
- この例では、
hostnameノードセレクターを使用します。 - 4
- インターフェイスの名前。
- 5
- オプション: 人間が判読できるインターフェイスの説明。
- 6
- インターフェイスのタイプ。この例では、ブリッジを作成します。
- 7
- 作成後のインターフェイスの要求された状態。
- 8
- オプション:
dhcpを使用しない場合は、静的 IP を設定するか、IP アドレスなしでインターフェイスを出ることができます。 - 9
- この例では
ipv4を有効にします。 - 10
- この例では
stpを無効にします。 - 11
- ブリッジが接続されるノードの NIC。
18.3.5.2. 例: VLAN インターフェイスノードネットワークの設定ポリシー
NodeNetworkConfigurationPolicy マニフェストをクラスターに適用してクラスター内のノード上に VLAN インターフェイスを作成します。
以下の YAML ファイルは、VLAN インターフェイスのマニフェストの例です。これには、独自の情報で置き換える必要のあるサンプルの値が含まれます。
apiVersion: nmstate.io/v1beta1
kind: NodeNetworkConfigurationPolicy
metadata:
name: vlan-eth1-policy
spec:
nodeSelector:
kubernetes.io/hostname: <node01>
desiredState:
interfaces:
- name: eth1.102
description: VLAN using eth1
type: vlan
state: up
vlan:
base-iface: eth1
id: 102 18.3.5.3. 例: ボンドインターフェイスノードネットワークの設定ポリシー
NodeNetworkConfigurationPolicy マニフェストをクラスターに適用してノード上にボンドインターフェイスを作成します。
OpenShift Container Platform は以下の bond モードのみをサポートします。
-
mode=1 active-backup
-
mode=2 balance-xor
-
mode=4 802.3ad
-
mode=5 balance-tlb
- mode=6 balance-alb
以下の YAML ファイルは、ボンドインターフェイスのマニフェストの例です。これには、独自の情報で置き換える必要のあるサンプルの値が含まれます。
apiVersion: nmstate.io/v1beta1
kind: NodeNetworkConfigurationPolicy
metadata:
name: bond0-eth1-eth2-policy
spec:
nodeSelector:
kubernetes.io/hostname: <node01>
desiredState:
interfaces:
- name: bond0
description: Bond enslaving eth1 and eth2
type: bond
state: up
ipv4:
dhcp: true
enabled: true
link-aggregation:
mode: active-backup
options:
miimon: '140'
slaves:
- eth1
- eth2
mtu: 1450 - 1
- ポリシーの名前。
- 2
- オプション:
nodeSelectorパラメーターを含めない場合、ポリシーはクラスター内のすべてのノードに適用されます。 - 3
- この例では、
hostnameノードセレクターを使用します。 - 4
- インターフェイスの名前。
- 5
- オプション: 人間が判読できるインターフェイスの説明。
- 6
- インターフェイスのタイプ。この例では、ボンドを作成します。
- 7
- 作成後のインターフェイスの要求された状態。
- 8
- オプション:
dhcpを使用しない場合は、静的 IP を設定するか、IP アドレスなしでインターフェイスを出ることができます。 - 9
- この例では
ipv4を有効にします。 - 10
- ボンドのドライバーモード。この例では、アクティブなバックアップモードを使用します。
- 11
- オプション: この例では、miimon を使用して 140ms ごとにボンドリンクを検査します。
- 12
- ボンド内の下位ノードの NIC。
- 13
- オプション: ボンドの Maximum transmission unit (MTU)指定がない場合、この値はデフォルトで
1500に設定されます。
18.3.5.4. 例: イーサネットインターフェイスノードネットワークの設定ポリシー
NodeNetworkConfigurationPolicy マニフェストをクラスターに適用してクラスター内のノードにイーサネットインターフェイスを作成します。
以下の YAML ファイルは、イーサネットインターフェイスのマニフェストの例です。これには、独自の情報で置き換える必要のあるサンプルの値が含まれます。
apiVersion: nmstate.io/v1beta1
kind: NodeNetworkConfigurationPolicy
metadata:
name: eth1-policy
spec:
nodeSelector:
kubernetes.io/hostname: <node01>
desiredState:
interfaces:
- name: eth1
description: Configuring eth1 on node01
type: ethernet
state: up
ipv4:
dhcp: true
enabled: true - 1
- ポリシーの名前。
- 2
- オプション:
nodeSelectorパラメーターを含めない場合、ポリシーはクラスター内のすべてのノードに適用されます。 - 3
- この例では、
hostnameノードセレクターを使用します。 - 4
- インターフェイスの名前。
- 5
- オプション: 人間が判読できるインターフェイスの説明。
- 6
- インターフェイスのタイプ。この例では、イーサネットネットワークインターフェイスを作成します。
- 7
- 作成後のインターフェイスの要求された状態。
- 8
- オプション:
dhcpを使用しない場合は、静的 IP を設定するか、IP アドレスなしでインターフェイスを出ることができます。 - 9
- この例では
ipv4を有効にします。
18.3.5.5. 例: 同じノードネットワーク設定ポリシーでの複数のインターフェイス
同じノードネットワーク設定ポリシーで複数のインターフェイスを作成できます。これらのインターフェイスは相互に参照でき、単一のポリシーマニフェストを使用してネットワーク設定をビルドし、デプロイできます。
以下のスニペット例では、2 つの NIC 間に bond10 という名前のボンドと、ボンドに接続する br1 という名前の Linux ブリッジを作成します。
...
interfaces:
- name: bond10
description: Bonding eth2 and eth3 for Linux bridge
type: bond
state: up
link-aggregation:
slaves:
- eth2
- eth3
- name: br1
description: Linux bridge on bond
type: linux-bridge
state: up
bridge:
port:
- name: bond10
...18.3.6. 例: IP 管理
以下の設定スニペットの例は、さまざまな IP 管理方法を示しています。
これらの例では、ethernet インターフェイスタイプを使用して、ポリシー設定に関連するコンテキストを表示しつつ、サンプルを単純化します。これらの IP 管理のサンプルは、他のインターフェイスタイプでも使用できます。
18.3.6.1. 静的
以下のスニペットは、イーサネットインターフェイスで IP アドレスを静的に設定します。
...
interfaces:
- name: eth1
description: static IP on eth1
type: ethernet
state: up
ipv4:
address:
- ip: 192.168.122.250
prefix-length: 24
enabled: true
...- 1
- この値を、インターフェイスの静的 IP アドレスに置き換えます。
18.3.6.2. IP アドレスなし
以下のスニペットでは、インターフェイスに IP アドレスがないことを確認できます。
...
interfaces:
- name: eth1
description: No IP on eth1
type: ethernet
state: up
ipv4:
enabled: false
...18.3.6.3. 動的ホストの設定
以下のスニペットは、動的 IP アドレス、ゲートウェイアドレス、および DNS を使用するイーサネットインターフェイスを設定します。
...
interfaces:
- name: eth1
description: DHCP on eth1
type: ethernet
state: up
ipv4:
dhcp: true
enabled: true
...以下のスニペットは、動的 IP アドレスを使用しますが、動的ゲートウェイアドレスまたは DNS を使用しないイーサネットインターフェイスを設定します。
...
interfaces:
- name: eth1
description: DHCP without gateway or DNS on eth1
type: ethernet
state: up
ipv4:
dhcp: true
auto-gateway: false
auto-dns: false
enabled: true
...18.3.6.4. DNS
以下のスニペットは、ホストに DNS 設定を設定します。
...
interfaces:
...
dns-resolver:
config:
search:
- example.com
- example.org
server:
- 8.8.8.8
...18.3.6.5. 静的ルーティング
以下のスニペットは、インターフェイス eth1 に静的ルートおよび静的 IP を設定します。
...
interfaces:
- name: eth1
description: Static routing on eth1
type: ethernet
state: up
ipv4:
address:
- ip: 192.0.2.251
prefix-length: 24
enabled: true
routes:
config:
- destination: 198.51.100.0/24
metric: 150
next-hop-address: 192.0.2.1
next-hop-interface: eth1
table-id: 254
...18.4. ノードのネットワーク設定のトラブルシューティング
ノードのネットワーク設定で問題が発生した場合には、ポリシーが自動的にロールバックされ、enactment (実行) レポートは失敗します。これには、以下のような問題が含まれます。
- ホストで設定を適用できません。
- ホストはデフォルトゲートウェイへの接続を失います。
- ホストは API サーバーへの接続を失います。
18.4.1. 正確でないノードネットワーク設定のポリシー設定のトラブルシューティング
ノードネットワーク設定ポリシーを適用し、クラスター全体でノードのネットワーク設定への変更を適用することができます。正確でない設定を適用する場合、以下の例を使用して、失敗したノードネットワークポリシーのトラブルシューティングと修正を行うことができます。
この例では、Linux ブリッジポリシーは、3 つのコントロールプレーンノード (マスター) と 3 つのコンピュート (ワーカー) ノードを持つクラスターのサンプルに適用されます。ポリシーは正しくないインターフェイスを参照するために、適用することができません。エラーを確認するには、利用可能な NMState リソースを調べます。その後に、正しい設定でポリシーを更新できます。
手順
ポリシーを作成し、これをクラスターに適用します。以下の例では、
ens01インターフェイスに単純なブリッジを作成します。apiVersion: nmstate.io/v1beta1 kind: NodeNetworkConfigurationPolicy metadata: name: ens01-bridge-testfail spec: desiredState: interfaces: - name: br1 description: Linux bridge with the wrong port type: linux-bridge state: up ipv4: dhcp: true enabled: true bridge: options: stp: enabled: false port: - name: ens01$ oc apply -f ens01-bridge-testfail.yaml出力例
nodenetworkconfigurationpolicy.nmstate.io/ens01-bridge-testfail created以下のコマンドを実行してポリシーのステータスを確認します。
$ oc get nncpこの出力は、ポリシーが失敗したことを示しています。
出力例
NAME STATUS ens01-bridge-testfail FailedToConfigureただし、ポリシーのステータスのみでは、すべてのノードで失敗したか、またはノードのサブセットで失敗したかを確認することはできません。
ノードのネットワーク設定の enactment (実行) を一覧表示し、ポリシーがいずれかのノードで成功したかどうかを確認します。このポリシーがノードのサブセットに対してのみ失敗した場合は、問題が特定のノード設定にあることが示唆されます。このポリシーがすべてのノードで失敗した場合には、問題はポリシーに関連するものであることが示唆されます。
$ oc get nnceこの出力は、ポリシーがすべてのノードで失敗したことを示しています。
出力例
NAME STATUS control-plane-1.ens01-bridge-testfail FailedToConfigure control-plane-2.ens01-bridge-testfail FailedToConfigure control-plane-3.ens01-bridge-testfail FailedToConfigure compute-1.ens01-bridge-testfail FailedToConfigure compute-2.ens01-bridge-testfail FailedToConfigure compute-3.ens01-bridge-testfail FailedToConfigure失敗した enactment (実行) のいずれかを表示し、トレースバックを確認します。以下のコマンドは、出力ツール
jsonpathを使用して出力をフィルターします。$ oc get nnce compute-1.ens01-bridge-testfail -o jsonpath='{.status.conditions[?(@.type=="Failing")].message}'このコマンドは、簡潔にするために編集されている大きなトレースバックを返します。
出力例
error reconciling NodeNetworkConfigurationPolicy at desired state apply: , failed to execute nmstatectl set --no-commit --timeout 480: 'exit status 1' '' ... libnmstate.error.NmstateVerificationError: desired ======= --- name: br1 type: linux-bridge state: up bridge: options: group-forward-mask: 0 mac-ageing-time: 300 multicast-snooping: true stp: enabled: false forward-delay: 15 hello-time: 2 max-age: 20 priority: 32768 port: - name: ens01 description: Linux bridge with the wrong port ipv4: address: [] auto-dns: true auto-gateway: true auto-routes: true dhcp: true enabled: true ipv6: enabled: false mac-address: 01-23-45-67-89-AB mtu: 1500 current ======= --- name: br1 type: linux-bridge state: up bridge: options: group-forward-mask: 0 mac-ageing-time: 300 multicast-snooping: true stp: enabled: false forward-delay: 15 hello-time: 2 max-age: 20 priority: 32768 port: [] description: Linux bridge with the wrong port ipv4: address: [] auto-dns: true auto-gateway: true auto-routes: true dhcp: true enabled: true ipv6: enabled: false mac-address: 01-23-45-67-89-AB mtu: 1500 difference ========== --- desired +++ current @@ -13,8 +13,7 @@ hello-time: 2 max-age: 20 priority: 32768 - port: - - name: ens01 + port: [] description: Linux bridge with the wrong port ipv4: address: [] line 651, in _assert_interfaces_equal\n current_state.interfaces[ifname],\nlibnmstate.error.NmstateVerificationError:NmstateVerificationErrorは、desiredポリシー設定、ノード上のポリシーのcurrent設定、および一致しないパラメーターを強調表示するdifferenceを一覧表示します。この例では、portはdifferenceに組み込まれ、これは問題がポリシーのポート設定に関連するものであることを示唆します。ポリシーが適切に設定されていることを確認するには、
NodeNetworkStateオブジェクトを要求して、1 つまたはすべてのノードのネットワーク設定を表示します。以下のコマンドは、control-plane-1ノードのネットワーク設定を返します。$ oc get nns control-plane-1 -o yaml出力は、ノード上のインターフェイス名は
ens1であるものの、失敗したポリシーがens01を誤って使用していることを示します。出力例
- ipv4: ... name: ens1 state: up type: ethernet既存のポリシーを編集してエラーを修正します。
$ oc edit nncp ens01-bridge-testfail... port: - name: ens1ポリシーを保存して修正を適用します。
ポリシーのステータスをチェックして、更新が正常に行われたことを確認します。
$ oc get nncp出力例
NAME STATUS ens01-bridge-testfail SuccessfullyConfigured
更新されたポリシーは、クラスターのすべてのノードで正常に設定されました。
第19章 クラスター全体のプロキシーの設定
実稼働環境では、インターネットへの直接アクセスを拒否し、代わりに HTTP または HTTPS プロキシーを使用することができます。既存クラスターのプロキシーオブジェクトを変更 するか、または新規クラスターの install-config.yaml ファイルでプロキシー設定を行うことにより、OpenShift Container Platform をプロキシーを使用するように設定できます。
19.1. 前提条件
クラスターがアクセスする必要のあるサイト を確認し、プロキシーをバイパスする必要があるかどうかを判断します。デフォルトで、すべてのクラスターシステムの egress トラフィック (クラスターをホストするクラウドのクラウドプロバイダー API に対する呼び出しを含む) はプロキシーされます。システム全体のプロキシーは、ユーザーのワークロードではなく、システムコンポーネントにのみ影響を与えます。プロキシーオブジェクトの
spec.noProxyフィールドにサイトを追加し、必要に応じてプロキシーをバイパスします。注記Proxy オブジェクトの
status.noProxyフィールドには、インストール設定のnetworking.machineNetwork[].cidr、networking.clusterNetwork[].cidr、およびnetworking.serviceNetwork[]フィールドの値が設定されます。Amazon Web Services (AWS)、Google Cloud Platform (GCP)、Microsoft Azure、および Red Hat OpenStack Platform (RHOSP) へのインストールの場合、
Proxyオブジェクトのstatus.noProxyフィールドには、インスタンスメタデータのエンドポイント (169.254.169.254) も設定されます。
19.2. クラスター全体のプロキシーの有効化
プロキシーオブジェクトは、クラスター全体の egress プロキシーを管理するために使用されます。プロキシーを設定せずにクラスターがインストールまたはアップグレードされると、プロキシーオブジェクトは引き続き生成されますが、spec は設定されません。以下に例を示します。
apiVersion: config.openshift.io/v1
kind: Proxy
metadata:
name: cluster
spec:
trustedCA:
name: ""
status:
クラスター管理者は、この cluster プロキシーオブジェクトを変更して OpenShift Container Platform のプロキシーを設定できます。
cluster という名前のプロキシーオブジェクトのみがサポートされ、追加のプロキシーは作成できません。
前提条件
- クラスター管理者のパーミッション。
-
OpenShift Container Platform
ocCLI ツールがインストールされている。
手順
HTTPS 接続のプロキシーに必要な追加の CA 証明書が含まれる ConfigMap を作成します。
注記プロキシーのアイデンティティー証明書が RHCOS 信頼バンドルからの認証局によって署名される場合は、これを省略できます。
以下の内容で
user-ca-bundle.yamlというファイルを作成して、PEM でエンコードされた証明書の値を指定します。apiVersion: v1 data: ca-bundle.crt: |1 <MY_PEM_ENCODED_CERTS>2 kind: ConfigMap metadata: name: user-ca-bundle3 namespace: openshift-config4 このファイルから ConfigMap を作成します。
$ oc create -f user-ca-bundle.yaml
oc editコマンドを使用してプロキシーオブジェクトを変更します。$ oc edit proxy/clusterプロキシーに必要なフィールドを設定します。
apiVersion: config.openshift.io/v1 kind: Proxy metadata: name: cluster spec: httpProxy: http://<username>:<pswd>@<ip>:<port>1 httpsProxy: http://<username>:<pswd>@<ip>:<port>2 noProxy: example.com3 readinessEndpoints: - http://www.google.com4 - https://www.google.com trustedCA: name: user-ca-bundle5 - 1
- クラスター外の HTTP 接続を作成するために使用するプロキシー URL。URL スキームは
httpである必要があります。 - 2
- クラスター外で HTTPS 接続を作成するために使用するプロキシー URL。
- 3
- プロキシーを除外するための宛先ドメイン名、ドメイン、IP アドレス、または他のネットワーク CIDR のコンマ区切りの一覧。
サブドメインのみと一致するように、ドメインの前に
.を付けます。たとえば、.y.comはx.y.comに一致しますが、y.comには一致しません。*を使用し、すべての宛先のプロキシーをバイパスします。インストール設定でnetworking.machineNetwork[].cidrフィールドで定義されるネットワークに含まれていないワーカーをスケールアップする場合、それらをこの一覧に追加し、接続の問題を防ぐ必要があります。httpProxyまたはhttpsProxyフィールドのいずれも設定されていない場合に、このフィールドは無視されます。 - 4
httpProxyおよびhttpsProxyの値をステータスに書き込む前の readiness チェックに使用するクラスター外の 1 つ以上の URL。- 5
- HTTPS 接続のプロキシーに必要な追加の CA 証明書が含まれる、
openshift-confignamespace の ConfigMap の参照。ここで参照する前に ConfigMap が存在している必要があります。このフィールドは、プロキシーのアイデンティティー証明書が RHCOS 信頼バンドルからの認証局によって署名されない限り必要になります。
- 変更を適用するためにファイルを保存します。
19.3. クラスター全体のプロキシーの削除
cluster プロキシーオブジェクトは削除できません。クラスターからプロキシーを削除するには、プロキシーオブジェクトからすべての spec フィールドを削除します。
前提条件
- クラスター管理者のパーミッション。
-
OpenShift Container Platform
ocCLI ツールがインストールされている。
手順
oc editコマンドを使用してプロキシーを変更します。$ oc edit proxy/clusterプロキシーオブジェクトからすべての
specフィールドを削除します。以下に例を示します。apiVersion: config.openshift.io/v1 kind: Proxy metadata: name: cluster spec: {} status: {}- 変更を適用するためにファイルを保存します。
関連情報
第20章 カスタム PKI の設定
Web コンソールなどの一部のプラットフォームコンポーネントは、通信にルートを使用し、それらと対話するために他のコンポーネントの証明書を信頼する必要があります。カスタムのパブリックキーインフラストラクチャー (PKI) を使用している場合は、プライベートに署名された CA 証明書がクラスター全体で認識されるようにこれを設定する必要があります。
プロキシー API を使用して、クラスター全体で信頼される CA 証明書を追加できます。インストール時またはランタイム時にこれを実行する必要があります。
インストール 時に、クラスター全体のプロキシーを設定します。プライベートに署名された CA 証明書は、
install-config.yamlファイルのadditionalTrustBundle設定で定義する必要があります。インストールプログラムは、定義した追加の CA 証明書が含まれる
user-ca-bundleという名前の ConfigMap を生成します。次に Cluster Network Operator は、これらの CA 証明書を Red Hat Enterprise Linux CoreOS (RHCOS) 信頼バンドルにマージするtrusted-ca-bundleConfigMap を作成し、この ConfigMap はプロキシーオブジェクトのtrustedCAフィールドで参照されます。-
ランタイム 時に、デフォルトのプロキシーオブジェクトを変更して、プライベートに署名された CA 証明書を追加 します (これは、クラスターのプロキシー有効化のワークフローの一部です)。これには、クラスターで信頼される必要があるプライベートに署名された CA 証明書が含まれる ConfigMap を作成し、次にプライベートに署名された証明書の ConfigMap を参照する
trustedCAでプロキシーリソースを変更することが関係します。
インストーラー設定の additionalTrustBundle フィールドおよびプロキシーリソースの trustedCA フィールドは、クラスター全体の信頼バンドルを管理するために使用されます。 additionalTrustBundle はインストール時に使用され、プロキシーの trustedCA がランタイム時に使用されます。
trustedCA フィールドは、クラスターコンポーネントによって使用されるカスタム証明書とキーのペアを含む ConfigMap の参照です。
20.1. インストール時のクラスター全体のプロキシーの設定
実稼働環境では、インターネットへの直接アクセスを拒否し、代わりに HTTP または HTTPS プロキシーを使用することができます。プロキシー設定を install-config.yaml ファイルで行うことにより、新規の OpenShift Container Platform クラスターをプロキシーを使用するように設定できます。
前提条件
-
既存の
install-config.yamlファイルがある。 クラスターがアクセスする必要のあるサイトを確認済みで、それらのいずれかがプロキシーをバイパスする必要があるかどうかを判別している。デフォルトで、すべてのクラスター egress トラフィック (クラスターをホストするクラウドについてのクラウドプロバイダー API に対する呼び出しを含む) はプロキシーされます。プロキシーを必要に応じてバイパスするために、サイトを
Proxyオブジェクトのspec.noProxyフィールドに追加している。注記Proxyオブジェクトのstatus.noProxyフィールドには、インストール設定のnetworking.machineNetwork[].cidr、networking.clusterNetwork[].cidr、およびnetworking.serviceNetwork[]フィールドの値が設定されます。Amazon Web Services (AWS)、Google Cloud Platform (GCP)、Microsoft Azure、および Red Hat OpenStack Platform (RHOSP) へのインストールの場合、
Proxyオブジェクトのstatus.noProxyフィールドには、インスタンスメタデータのエンドポイント (169.254.169.254) も設定されます。
手順
install-config.yamlファイルを編集し、プロキシー設定を追加します。以下に例を示します。apiVersion: v1 baseDomain: my.domain.com proxy: httpProxy: http://<username>:<pswd>@<ip>:<port>1 httpsProxy: https://<username>:<pswd>@<ip>:<port>2 noProxy: example.com3 additionalTrustBundle: |4 -----BEGIN CERTIFICATE----- <MY_TRUSTED_CA_CERT> -----END CERTIFICATE----- ...- 1
- クラスター外の HTTP 接続を作成するために使用するプロキシー URL。URL スキームは
httpである必要があります。 - 2
- クラスター外で HTTPS 接続を作成するために使用するプロキシー URL。
- 3
- プロキシーから除外するための宛先ドメイン名、IP アドレス、または他のネットワーク CIDR のコンマ区切りの一覧。サブドメインのみと一致するように、ドメインの前に
.を付けます。たとえば、.y.comはx.y.comに一致しますが、y.comには一致しません。*を使用し、すべての宛先のプロキシーをバイパスします。 - 4
- 指定されている場合には、インストールプログラムは、
openshift-confignamespace にuser-ca-bundleという名前の設定魔府を生成して、追加の CA 証明書を保存します。additionalTrustBundleと少なくとも 1 つのプロキシー設定を指定した場合には、Proxyオブジェクトはtrusted CAフィールドでuser-ca-bundle設定マップを参照するように設定されます。その後、Cluster Network Operator は、trustedCAパラメーターに指定されたコンテンツを RHCOS トラストバンドルにマージするtrusted-ca-bundle設定マップを作成します。additionalTrustBundleフィールドは、プロキシーのアイデンティティー証明書が RHCOS 信頼バンドルからの認証局によって署名されない限り必要になります。
注記インストールプログラムは、プロキシーの
readinessEndpointsフィールドをサポートしません。- ファイルを保存し、OpenShift Container Platform のインストール時にこれを参照します。
インストールプログラムは、指定の install-config.yaml ファイルのプロキシー設定を使用する cluster という名前のクラスター全体のプロキシーを作成します。プロキシー設定が指定されていない場合、cluster Proxy オブジェクトが依然として作成されますが、これには spec がありません。
cluster という名前の Proxy オブジェクトのみがサポートされ、追加のプロキシーを作成することはできません。
20.2. クラスター全体のプロキシーの有効化
プロキシーオブジェクトは、クラスター全体の egress プロキシーを管理するために使用されます。プロキシーを設定せずにクラスターがインストールまたはアップグレードされると、プロキシーオブジェクトは引き続き生成されますが、spec は設定されません。以下に例を示します。
apiVersion: config.openshift.io/v1
kind: Proxy
metadata:
name: cluster
spec:
trustedCA:
name: ""
status:
クラスター管理者は、この cluster プロキシーオブジェクトを変更して OpenShift Container Platform のプロキシーを設定できます。
cluster という名前のプロキシーオブジェクトのみがサポートされ、追加のプロキシーは作成できません。
前提条件
- クラスター管理者のパーミッション。
-
OpenShift Container Platform
ocCLI ツールがインストールされている。
手順
HTTPS 接続のプロキシーに必要な追加の CA 証明書が含まれる ConfigMap を作成します。
注記プロキシーのアイデンティティー証明書が RHCOS 信頼バンドルからの認証局によって署名される場合は、これを省略できます。
以下の内容で
user-ca-bundle.yamlというファイルを作成して、PEM でエンコードされた証明書の値を指定します。apiVersion: v1 data: ca-bundle.crt: |1 <MY_PEM_ENCODED_CERTS>2 kind: ConfigMap metadata: name: user-ca-bundle3 namespace: openshift-config4 このファイルから ConfigMap を作成します。
$ oc create -f user-ca-bundle.yaml
oc editコマンドを使用してプロキシーオブジェクトを変更します。$ oc edit proxy/clusterプロキシーに必要なフィールドを設定します。
apiVersion: config.openshift.io/v1 kind: Proxy metadata: name: cluster spec: httpProxy: http://<username>:<pswd>@<ip>:<port>1 httpsProxy: http://<username>:<pswd>@<ip>:<port>2 noProxy: example.com3 readinessEndpoints: - http://www.google.com4 - https://www.google.com trustedCA: name: user-ca-bundle5 - 1
- クラスター外の HTTP 接続を作成するために使用するプロキシー URL。URL スキームは
httpである必要があります。 - 2
- クラスター外で HTTPS 接続を作成するために使用するプロキシー URL。
- 3
- プロキシーを除外するための宛先ドメイン名、ドメイン、IP アドレス、または他のネットワーク CIDR のコンマ区切りの一覧。
サブドメインのみと一致するように、ドメインの前に
.を付けます。たとえば、.y.comはx.y.comに一致しますが、y.comには一致しません。*を使用し、すべての宛先のプロキシーをバイパスします。インストール設定でnetworking.machineNetwork[].cidrフィールドで定義されるネットワークに含まれていないワーカーをスケールアップする場合、それらをこの一覧に追加し、接続の問題を防ぐ必要があります。httpProxyまたはhttpsProxyフィールドのいずれも設定されていない場合に、このフィールドは無視されます。 - 4
httpProxyおよびhttpsProxyの値をステータスに書き込む前の readiness チェックに使用するクラスター外の 1 つ以上の URL。- 5
- HTTPS 接続のプロキシーに必要な追加の CA 証明書が含まれる、
openshift-confignamespace の ConfigMap の参照。ここで参照する前に ConfigMap が存在している必要があります。このフィールドは、プロキシーのアイデンティティー証明書が RHCOS 信頼バンドルからの認証局によって署名されない限り必要になります。
- 変更を適用するためにファイルを保存します。
20.3. Operator を使用した証明書の挿入
カスタム CA 証明書が ConfigMap 経由でクラスターに追加されると、Cluster Network Operator はユーザーによってプロビジョニングされる CA 証明書およびシステム CA 証明書を単一バンドルにマージし、信頼バンドルの挿入を要求する Operator にマージされたバンドルを挿入します。
Operator は、以下のラベルの付いた空の ConfigMap を作成してこの挿入を要求します。
config.openshift.io/inject-trusted-cabundle="true"空の ConfigMap の例:
apiVersion: v1
data: {}
kind: ConfigMap
metadata:
labels:
config.openshift.io/inject-trusted-cabundle: "true"
name: ca-inject
namespace: apache- 1
- 空の ConfigMap 名を指定します。
Operator は、この ConfigMap をコンテナーのローカル信頼ストアにマウントします。
信頼された CA 証明書の追加は、証明書が Red Hat Enterprise Linux CoreOS (RHCOS) 信頼バンドルに含まれない場合にのみ必要になります。
証明書の挿入は Operator に制限されません。Cluster Network Operator は、空の ConfigMap が config.openshift.io/inject-trusted-cabundle=true ラベルを使用して作成される場合に、すべての namespace で証明書を挿入できます。
ConfigMap はすべての namespace に置くことができますが、ConfigMap はカスタム CA を必要とする Pod 内の各コンテナーに対してボリュームとしてマウントされる必要があります。以下に例を示します。
apiVersion: apps/v1
kind: Deployment
metadata:
name: my-example-custom-ca-deployment
namespace: my-example-custom-ca-ns
spec:
...
spec:
...
containers:
- name: my-container-that-needs-custom-ca
volumeMounts:
- name: trusted-ca
mountPath: /etc/pki/ca-trust/extracted/pem
readOnly: true
volumes:
- name: trusted-ca
configMap:
name: trusted-ca
items:
- key: ca-bundle.crt
path: tls-ca-bundle.pem 第21章 RHOSP での負荷分散
21.1. Kuryr SDN を使用した Octavia OVN ロードバランサープロバイダードライバーの使用
OpenShift Container Platform クラスターが Kuryr を使用し、これが後に RHOSP 16 にアップグレードされた Red Hat OpenStack Platform (RHOSP) 13 クラウドにインストールされている場合、これを Octavia OVN プロバイダードライバーを使用するように設定できます。
Kuryr はプロバイダードライバーの変更後に既存のロードバランサーを置き換えます。このプロセスにより、ダウンタイムが生じます。
前提条件
-
RHOSP CLI の
openstackをインストールします。 -
OpenShift Container Platform CLI の
ocをインストールします。 RHOSP の Octavia OVN ドライバーが有効になっていることを確認します。
ヒント利用可能な Octavia ドライバーの一覧を表示するには、コマンドラインで
openstack loadbalancer provider listを入力します。ovnドライバーはコマンドの出力に表示されます。
手順
Octavia Amphora プロバイダードライバーから Octavia OVN に変更するには、以下を実行します。
kuryr-configConfigMap を開きます。コマンドラインで、以下を実行します。$ oc -n openshift-kuryr edit cm kuryr-configConfigMap で、
kuryr-octavia-provider: defaultが含まれる行を削除します。以下に例を示します。... kind: ConfigMap metadata: annotations: networkoperator.openshift.io/kuryr-octavia-provider: default1 ...- 1
- この行を削除します。クラスターは、
ovnを値としてこれを再生成します。
Cluster Network Operator が変更を検出し、
kuryr-controllerおよびkuryr-cniPod を再デプロイするのを待機します。このプロセスには数分の時間がかかる可能性があります。kuryr-configConfigMap アノテーションでovnをその値として表示されていることを確認します。コマンドラインで、以下を実行します。$ oc -n openshift-kuryr edit cm kuryr-configovnプロバイダーの値は出力に表示されます。... kind: ConfigMap metadata: annotations: networkoperator.openshift.io/kuryr-octavia-provider: ovn ...RHOSP がそのロードバランサーを再作成していることを確認します。
コマンドラインで、以下を実行します。
$ openstack loadbalancer list | grep amphora単一の Amphora ロードバランサーが表示されます。以下に例を示します。
a4db683b-2b7b-4988-a582-c39daaad7981 | ostest-7mbj6-kuryr-api-loadbalancer | 84c99c906edd475ba19478a9a6690efd | 172.30.0.1 | ACTIVE | amphora以下を入力して
ovnロードバランサーを検索します。$ openstack loadbalancer list | grep ovnovnタイプの残りのロードバランサーが表示されます。以下に例を示します。2dffe783-98ae-4048-98d0-32aa684664cc | openshift-apiserver-operator/metrics | 84c99c906edd475ba19478a9a6690efd | 172.30.167.119 | ACTIVE | ovn 0b1b2193-251f-4243-af39-2f99b29d18c5 | openshift-etcd/etcd | 84c99c906edd475ba19478a9a6690efd | 172.30.143.226 | ACTIVE | ovn f05b07fc-01b7-4673-bd4d-adaa4391458e | openshift-dns-operator/metrics | 84c99c906edd475ba19478a9a6690efd | 172.30.152.27 | ACTIVE | ovn
21.2. Octavia を使用したアプリケーショントラフィック用のクラスターのスケーリング
Red Hat OpenStack Platform (RHOSP) で実行される OpenShift Container Platform クラスターでは、Octavia 負荷分散サービスを使用して、複数の仮想マシン (VM) または Floating IP アドレスにトラフィックを分散することができます。この機能は、単一マシンまたはアドレスが生じさせるボトルネックを軽減します。
クラスターで Kuryr を使用する場合、Cluster Network Operator はデプロイメント時に内部 Octavia ロードバランサーを作成していました。アプリケーションネットワークのスケーリングには、このロードバランサーを使用できます。
クラスターで Kuryr を使用しない場合、アプリケーションのネットワークのスケーリングに使用する独自の Octavia ロードバランサーを作成する必要があります。
21.2.1. Octavia を使用したクラスターのスケーリング
複数の API ロードバランサーを使用する場合や、クラスターが Kuryr を使用しない場合、Octavia ロードバランサーを作成してから、クラスターをこれを使用するように設定します。
前提条件
- Octavia は Red Hat OpenStack Platform (RHOSP) デプロイメントで利用できます。
手順
コマンドラインから、Amphora ドライバーを使用する Octavia ロードバランサーを作成します。
$ openstack loadbalancer create --name API_OCP_CLUSTER --vip-subnet-id <id_of_worker_vms_subnet>API_OCP_CLUSTERの代わりに、任意の名前を使用することができます。ロードバランサーがアクティブになったら、リスナーを作成します。
$ openstack loadbalancer listener create --name API_OCP_CLUSTER_6443 --protocol HTTPS--protocol-port 6443 API_OCP_CLUSTER注記ロードバランサーのステータスを表示するには、
openstack loadbalancer listと入力します。ラウンドロビンアルゴリズムを使用し、セッションの永続性が有効にされているプールを作成します。
$ openstack loadbalancer pool create --name API_OCP_CLUSTER_pool_6443 --lb-algorithm ROUND_ROBIN --session-persistence type=<source_IP_address> --listener API_OCP_CLUSTER_6443 --protocol HTTPSコントロールプレーンマシンが利用可能であることを確認するには、ヘルスモニターを作成します。
$ openstack loadbalancer healthmonitor create --delay 5 --max-retries 4 --timeout 10 --type TCP API_OCP_CLUSTER_pool_6443コントロールプレーンマシンをロードバランサープールのメンバーとして追加します。
$ for SERVER in $(MASTER-0-IP MASTER-1-IP MASTER-2-IP) do openstack loadbalancer member create --address $SERVER --protocol-port 6443 API_OCP_CLUSTER_pool_6443 doneオプション: クラスター API の Floating IP アドレスを再利用するには、設定を解除します。
$ openstack floating ip unset $API_FIP設定を解除された
API_FIP、または新規アドレスを、作成されたロードばランサー VIP に追加します。$ openstack floating ip set --port $(openstack loadbalancer show -c <vip_port_id> -f value API_OCP_CLUSTER) $API_FIP
クラスターは、負荷分散に Octavia を使用するようになりました。
Kuryr が Octavia Amphora ドライバーを使用する場合、すべてのトラフィックは単一の Amphora 仮想マシン (VM) 経由でルーティングされます。
この手順を繰り返して追加のロードバランサーを作成します。これにより、ボトルネックを軽減することができます。
21.2.2. Octavia の使用による Kuryr を使用するクラスターのスケーリング
クラスターで Kuryr を使用する場合は、クラスターの API Floating IP アドレスを既存の Octavia ロードバランサーに関連付けます。
前提条件
- OpenShift Container Platform クラスターは Kuryr を使用します。
- Octavia は Red Hat OpenStack Platform (RHOSP) デプロイメントで利用できます。
手順
オプション: コマンドラインからクラスター API の Floating IP アドレスを再利用するには、この設定を解除します。
$ openstack floating ip unset $API_FIP設定を解除された
API_FIP、または新規アドレスを、作成されたロードばランサー VIP に追加します。$ openstack floating ip set --port $(openstack loadbalancer show -c <vip_port_id> -f value ${OCP_CLUSTER}-kuryr-api-loadbalancer) $API_FIP
クラスターは、負荷分散に Octavia を使用するようになりました。
Kuryr が Octavia Amphora ドライバーを使用する場合、すべてのトラフィックは単一の Amphora 仮想マシン (VM) 経由でルーティングされます。
この手順を繰り返して追加のロードバランサーを作成します。これにより、ボトルネックを軽減することができます。
21.3. RHOSP Octavia を使用した ingress トラフィックのスケーリング
Octavia ロードバランサーを使用して、Kuryr を使用するクラスターで Ingress コントローラーをスケーリングできます。
前提条件
- OpenShift Container Platform クラスターは Kuryr を使用します。
- Octavia は RHOSP デプロイメントで利用できます。
手順
現在の内部ルーターサービスをコピーするには、コマンドラインで以下を入力します。
$ oc -n openshift-ingress get svc router-internal-default -o yaml > external_router.yamlexternal_router.yamlファイルで、metadata.nameおよびspec.typeの値をLoadBalancerに変更します。ルーターファイルの例
apiVersion: v1 kind: Service metadata: labels: ingresscontroller.operator.openshift.io/owning-ingresscontroller: default name: router-external-default1 namespace: openshift-ingress spec: ports: - name: http port: 80 protocol: TCP targetPort: http - name: https port: 443 protocol: TCP targetPort: https - name: metrics port: 1936 protocol: TCP targetPort: 1936 selector: ingresscontroller.operator.openshift.io/deployment-ingresscontroller: default sessionAffinity: None type: LoadBalancer2
ロードバランシングと関連性のないタイムスタンプやその他の情報を削除できます。
コマンドラインで、
external_router.yamlファイルからサービスを作成します。$ oc apply -f external_router.yamlサービスの外部 IP アドレスがロードバランサーに関連付けられているものと同じであることを確認します。
コマンドラインで、サービスの外部 IP アドレスを取得します。
$ oc -n openshift-ingress get svc出力例
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE router-external-default LoadBalancer 172.30.235.33 10.46.22.161 80:30112/TCP,443:32359/TCP,1936:30317/TCP 3m38s router-internal-default ClusterIP 172.30.115.123 <none> 80/TCP,443/TCP,1936/TCP 22hロードバランサーの IP アドレスを取得します。
$ openstack loadbalancer list | grep router-external出力例
| 21bf6afe-b498-4a16-a958-3229e83c002c | openshift-ingress/router-external-default | 66f3816acf1b431691b8d132cc9d793c | 172.30.235.33 | ACTIVE | octavia |直前のステップで取得したアドレスが、Floating IP の一覧で相互に関連付けられていることを確認します。
$ openstack floating ip list | grep 172.30.235.33出力例
| e2f80e97-8266-4b69-8636-e58bacf1879e | 10.46.22.161 | 172.30.235.33 | 655e7122-806a-4e0a-a104-220c6e17bda6 | a565e55a-99e7-4d15-b4df-f9d7ee8c9deb | 66f3816acf1b431691b8d132cc9d793c |
EXTERNAL-IP の値を新規 Ingress アドレスとして使用できるようになりました。
Kuryr が Octavia Amphora ドライバーを使用する場合、すべてのトラフィックは単一の Amphora 仮想マシン (VM) 経由でルーティングされます。
この手順を繰り返して追加のロードバランサーを作成します。これにより、ボトルネックを軽減することができます。
21.4. 外部ロードバランサーの設定
Red Hat OpenStack Platform (RHOSP) の OpenShift Container Platform クラスターを、デフォルトのロードバランサーの代わりに外部ロードバランサーを使用するように設定できます。
前提条件
- ロードバランサーでは、システムの任意のユーザーが TCP をポート 6443、443、および 80 が利用できる必要があります。
- それぞれのコントロールプレーンノード間で API ポート 6443 を負荷分散します。
- すべてのコンピュートノード間でアプリケーションポート 443 と 80 を負荷分散します。
- ロードバランサーでは、Ignition 起動設定をノードに提供するために使用されるポート 22623 はクラスター外に公開されません。
ロードバランサーはクラスター内のすべてのマシンにアクセスできる必要があります。このアクセスを許可する方法には、以下が含まれます。
- ロードバランサーをクラスターのマシンのサブネットに割り当てます。
- ロードバランサーを使用するマシンに Floating IP アドレスを割り当てます。
手順
ポート 6443、443、および 80 でロードバランサーからクラスターへのアクセスを有効にします。
たとえば、以下の HAProxy 設定に留意してください。
サンプル HAProxy 設定のセクション
... listen my-cluster-api-6443 bind 0.0.0.0:6443 mode tcp balance roundrobin server my-cluster-master-2 192.0.2.2:6443 check server my-cluster-master-0 192.0.2.3:6443 check server my-cluster-master-1 192.0.2.1:6443 check listenmy-cluster-apps-443 bind 0.0.0.0:443 mode tcp balance roundrobin server my-cluster-worker-0 192.0.2.6:443 check server my-cluster-worker-1 192.0.2.5:443 check server my-cluster-worker-2 192.0.2.4:443 check listenmy-cluster-apps-80 bind 0.0.0.0:80 mode tcp balance roundrobin server my-cluster-worker-0 192.0.2.7:80 check server my-cluster-worker-1 192.0.2.9:80 check server my-cluster-worker-2 192.0.2.8:80 checkロードバランサーでクラスター API およびアプリケーションの DNS サーバーにレコードを追加します。以下に例を示します。
<load_balancer_ip_address> api.<cluster_name>.<base_domain> <load_balancer_ip_address> apps.<cluster_name>.<base_domain>コマンドラインで
curlを使用して、外部ロードバランサーおよび DNS 設定が機能することを確認します。クラスター API がアクセス可能であることを確認します。
$ curl https://<loadbalancer_ip_address>:6443/version --insecure設定が正しい場合は、応答として JSON オブジェクトを受信します。
{ "major": "1", "minor": "11+", "gitVersion": "v1.11.0+ad103ed", "gitCommit": "ad103ed", "gitTreeState": "clean", "buildDate": "2019-01-09T06:44:10Z", "goVersion": "go1.10.3", "compiler": "gc", "platform": "linux/amd64" }クラスターアプリケーションがアクセス可能であることを確認します。
注記Web ブラウザーで OpenShift Container Platform コンソールを開き、アプリケーションのアクセスを確認することもできます。
$ curl http://console-openshift-console.apps.<cluster_name>.<base_domain> -I -L --insecure設定が正しい場合は、HTTP 応答を受信します。
HTTP/1.1 302 Found content-length: 0 location: https://console-openshift-console.apps.<cluster-name>.<base domain>/ cache-control: no-cacheHTTP/1.1 200 OK referrer-policy: strict-origin-when-cross-origin set-cookie: csrf-token=39HoZgztDnzjJkq/JuLJMeoKNXlfiVv2YgZc09c3TBOBU4NI6kDXaJH1LdicNhN1UsQWzon4Dor9GWGfopaTEQ==; Path=/; Secure x-content-type-options: nosniff x-dns-prefetch-control: off x-frame-options: DENY x-xss-protection: 1; mode=block date: Tue, 17 Nov 2020 08:42:10 GMT content-type: text/html; charset=utf-8 set-cookie: 1e2670d92730b515ce3a1bb65da45062=9b714eb87e93cf34853e87a92d6894be; path=/; HttpOnly; Secure; SameSite=None cache-control: private
第22章 セカンダリーインターフェイスメトリクスのネットワーク割り当てへの関連付け
22.1. セカンダリーインターフェイスメトリクスのネットワーク割り当てへの関連付け
セカンダリーデバイス (インターフェイス) は、各種の用途に合わせて使用されます。セカンダリーデバイスのメトリクスを同じ分類で集計するために、それらを分類する方法を確保する必要があります。
公開されるメトリクスにはインターフェイスが含まれますが、インターフェイスの出所は指定されません。これは、追加のインターフェイスがない場合に役に立ちますが、セカンダリーインターフェイスが追加されると、インターフェイス名のみを識別子として使用してインターフェイスを識別することは困難であるため、メトリクスを使用することは難しくなります。
セカンダリーインターフェイスを追加する場合、その名前は追加された順序によって異なります。また、異なるセカンダリーインターフェイスが異なるネットワークに属し、これらを異なる目的に使用できます。
pod_network_name_info を使用すると、現在のメトリクスをインターフェイスタイプを識別する追加情報を使用して拡張できます。このようにして、メトリクスを集約し、特定のインターフェイスタイプに特定のアラームを追加できます。
ネットワークタイプは、関連する NetworkAttachmentDefinition の名前を使用して生成されます。この名前は、セカンダリーネットワークの異なるクラスを区別するために使用されます。たとえば、異なるネットワークに属するインターフェイスや、異なる CNI を使用するインターフェイスは、異なるネットワーク割り当て定義名を使用します。
22.1.1. Network Metrics Daemon
Network Metrics Daemon は、ネットワーク関連のメトリクスを収集し、公開するデーモンコンポーネントです。
kubelet はすでに確認できるネットワーク関連のメトリクスを公開しています。以下は、これらのメトリクスになります。
-
container_network_receive_bytes_total -
container_network_receive_errors_total -
container_network_receive_packets_total -
container_network_receive_packets_dropped_total -
container_network_transmit_bytes_total -
container_network_transmit_errors_total -
container_network_transmit_packets_total -
container_network_transmit_packets_dropped_total
これらのメトリクスのラベルには、とくに以下が含まれます。
- Pod の名前
- Pod の namespace
-
インターフェイス名 (例:
eth0)
これらのメトリクスは、Multus を使用して新規インターフェイスが Pod に追加されるまで正常に機能します。インターフェイス名が何を参照しているか明確ではないためです。
インターフェイスのラベルはインターフェイス名を参照しますが、そのインターフェイスの用途は明確ではありません。多くの異なるインターフェイスがある場合、監視しているメトリクスが参照するネットワークを把握することはできません。
これには、以降のセクションで説明する新規の pod_network_name_info を導入して対応できます。
22.1.2. ネットワーク名を持つメトリクス
この daemonset は、固定の値が 0 の pod_network_name_info 測定メトリクスを公開します。
pod_network_name_info{interface="net0",namespace="namespacename",network_name="nadnamespace/firstNAD",pod="podname"} 0ネットワーク名ラベルは、Multus によって追加されるアノテーションを使用して生成されます。これは、ネットワークの割り当て定義が属する namespace の連結と、ネットワーク割り当て定義の名前です。
新しいメトリクスのみでは十分な値が提供されませんが、ネットワーク関連の container_network_* メトリクスと組み合わせて、セカンダリーネットワークの監視に対するサポートを強化します。
以下のような promql クエリーを使用すると、k8s.v1.cni.cncf.io/networks-status アノテーションから取得した値とネットワーク名を含む新規のメトリクスを取得できます。
(container_network_receive_bytes_total) + on(namespace,pod,interface) group_left(network_name) ( pod_network_name_info )
(container_network_receive_errors_total) + on(namespace,pod,interface) group_left(network_name) ( pod_network_name_info )
(container_network_receive_packets_total) + on(namespace,pod,interface) group_left(network_name) ( pod_network_name_info )
(container_network_receive_packets_dropped_total) + on(namespace,pod,interface) group_left(network_name) ( pod_network_name_info )
(container_network_transmit_bytes_total) + on(namespace,pod,interface) group_left(network_name) ( pod_network_name_info )
(container_network_transmit_errors_total) + on(namespace,pod,interface) group_left(network_name) ( pod_network_name_info )
(container_network_transmit_packets_total) + on(namespace,pod,interface) group_left(network_name) ( pod_network_name_info )
(container_network_transmit_packets_dropped_total) + on(namespace,pod,interface) group_left(network_name)