Chapter 13. Managing User and Host Groups
13.1. How User and Host Groups Work in IdM
Copy linkLink copied to clipboard!
13.1.1. What User and Host Groups Are
Copy linkLink copied to clipboard!
A user group is a set of users with common privileges, password policies, and other characteristics.
A host group is a set of IdM hosts with common access control rules and other characteristics.
For example, you can define groups around company departments, physical locations, or access control requirements.
13.1.2. Supported Group Members
Copy linkLink copied to clipboard!
A user group in IdM can include:
- IdM users
- other IdM user groups
- external users, which are users that exist outside IdM
A host group in IdM can include:
- IdM servers and clients
- other IdM host groups
13.1.3. Direct and Indirect Group Members
Copy linkLink copied to clipboard!
User and host group attributes in IdM apply to both direct and indirect members: when group B is a member of group A, all users in group B are considered members of group A.
For example, in Figure 13.1, “Direct and Indirect Group Membership”:
- User 1 and User 2 are direct members of group A.
- User 3, User 4, and User 5 are indirect members of group A.
Figure 13.1. Direct and Indirect Group Membership
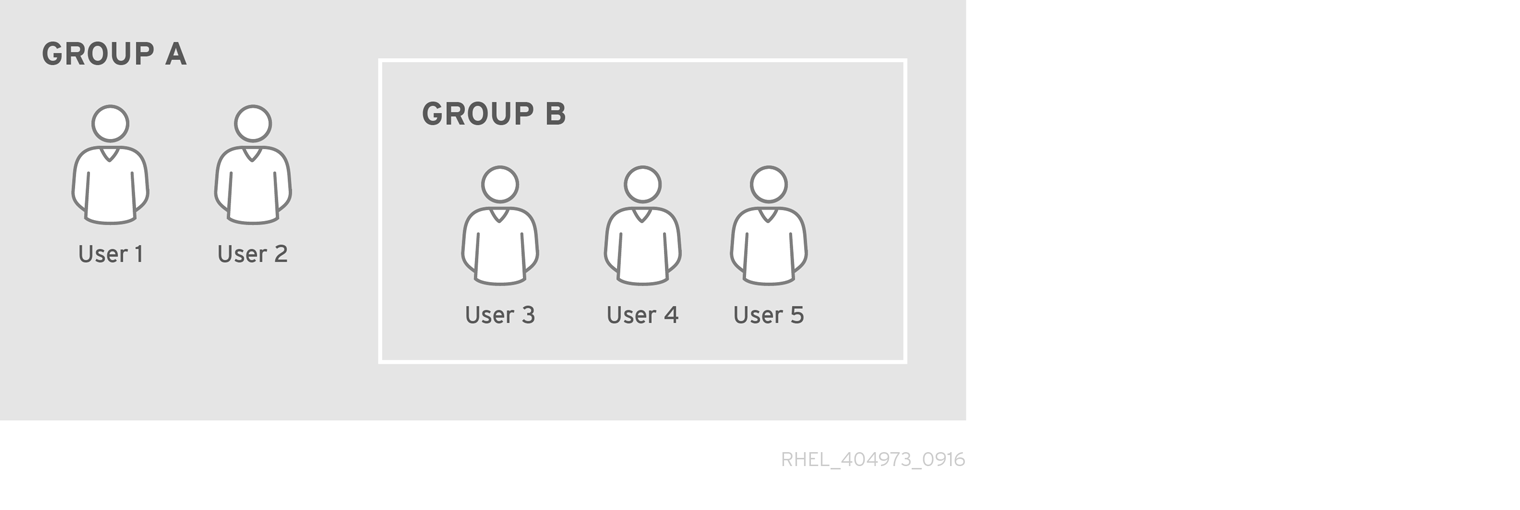
If you set a password policy for user group A, the policy applies to all users in user group B as well.
Example 13.1. Viewing Direct and Indirect Group Members
- Create two groups:
group_Aandgroup_B. See Section 13.2, “Adding and Removing User or Host Groups”. - Add:
- one user as a member of
group_A - another user as a member of
group_B group_Bas a member ofgroup_A
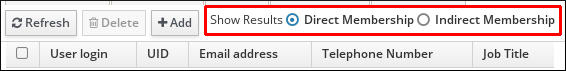
- In the web UI: Select
. From the individual group types which are listed in a side bar on the left, select , and click the name of group_A. Switch between Direct Membership and Indirect Membership. - From the command line: Use the ipa group-show command:
$ ipa group-show group_A ... Member users: user_1 Member groups: group_B Indirect Member users: user_2
The list of indirect members does not include external users from trusted Active Directory domains. The Active Directory trust user objects are not visible in the IdM interface because they do not exist as LDAP objects within IdM.
13.1.4. User Group Types in IdM
Copy linkLink copied to clipboard!
- POSIX groups (the default)
- POSIX groups support POSIX attributes for their members. Note that groups that interact with Active Directory cannot use POSIX attributes.
- Non-POSIX groups
- All group members of this type of group must belong to the IdM domain.
- External groups
- External groups allow adding group members that exist in an identity store outside of the IdM domain. The external store can be a local system, an Active Directory domain, or a directory service.
Non-POSIX and external groups do not support POSIX attributes. For example, these groups do not have a GID defined.
Example 13.2. Searching for Different Types of User Groups
- Run the ipa group-find command to display all user groups.
- Run the ipa group-find --posix command to display all POSIX groups.
- Run the ipa group-find --nonposix command to display all non-POSIX groups.
- Run the ipa group-find --external command to display all external groups.
13.1.5. User and Host Groups Created by Default
Copy linkLink copied to clipboard!
| Group Name | User or Host | Default Group Members |
|---|---|---|
ipausers | User group | All IdM users |
admins | User group | Users with administrative privileges, initially the default admin user |
editors | User group | Users allowed to edit other IdM users in the web UI, without all the rights of an administrative user |
trust admins | User group | Users with privileges to manage Active Directory trusts |
ipaservers | Host group | All IdM server hosts |
Adding a user to a user group applies the privileges and policies associated with the group. For example, adding a user to the
admins group grants the user administrative privileges.
Warning
Do not delete the
admins group. As admins is a pre-defined group required by IdM, this operation causes problems with certain commands.
Warning
Be careful when adding hosts to the
ipaservers host group. All hosts in ipaservers have the ability to promote themselves to an IdM server.
In addition, IdM creates user private groups by default whenever a new user is created in IdM.
- The user private group has the same name as the user for which it was created.
- The user is the only member of the user private group.
- GID of the private groups matches the UID of the user.
Example 13.3. Viewing User Private Groups
Run the ipa group-find --private command to display all user private groups:
$ ipa group-find --private
----------------
2 groups matched
----------------
Group name: user1
Description: User private group for user1
GID: 830400006
Group name: user2
Description: User private group for user2
GID: 830400004
----------------------------
Number of entries returned 2
----------------------------
In some situations, it is better to avoid creating user private groups, such as when a NIS group or another system group already uses the GID that would be assigned to the user private group. See Section 13.4, “Disabling User Private Groups”.