Chapter 4. Pipelines
4.1. Red Hat OpenShift Pipelines release notes
Red Hat OpenShift Pipelines is a cloud-native CI/CD experience based on the Tekton project which provides:
- Standard Kubernetes-native pipeline definitions (CRDs).
- Serverless pipelines with no CI server management overhead.
- Extensibility to build images using any Kubernetes tool, such as S2I, Buildah, JIB, and Kaniko.
- Portability across any Kubernetes distribution.
- Powerful CLI for interacting with pipelines.
- Integrated user experience with the Developer perspective of the OpenShift Container Platform web console.
For an overview of Red Hat OpenShift Pipelines, see Understanding OpenShift Pipelines.
4.1.1. Compatibility and support matrix
Some features in this release are currently in Technology Preview. These experimental features are not intended for production use.
In the table, features are marked with the following statuses:
| TP | Technology Preview |
| GA | General Availability |
| Red Hat OpenShift Pipelines Version | Component Version | OpenShift Version | Support Status | ||||||
|---|---|---|---|---|---|---|---|---|---|
| Operator | Pipelines | Triggers | CLI | Catalog | Chains | Hub | Pipelines as Code | ||
| 1.7 | 0.33.x | 0.19.x | 0.23.x | 0.33 | 0.8.0 (TP) | 1.7.0 (TP) | 0.5.x (TP) | 4.9, 4.10, 4.11 | GA |
| 1.6 | 0.28.x | 0.16.x | 0.21.x | 0.28 | N/A | N/A | N/A | 4.9 | GA |
| 1.5 | 0.24.x | 0.14.x (TP) | 0.19.x | 0.24 | N/A | N/A | N/A | 4.8 | GA |
| 1.4 | 0.22.x | 0.12.x (TP) | 0.17.x | 0.22 | N/A | N/A | N/A | 4.7 | GA |
In Red Hat OpenShift Pipelines 1.6, Triggers 0.16.x transitioned to GA status. In earlier versions, Triggers was available as a technology preview feature.
For questions and feedback, you can send an email to the product team at pipelines-interest@redhat.com.
4.1.2. Making open source more inclusive
Red Hat is committed to replacing problematic language in our code, documentation, and web properties. We are beginning with these four terms: master, slave, blacklist, and whitelist. Because of the enormity of this endeavor, these changes will be implemented gradually over several upcoming releases. For more details, see our CTO Chris Wright’s message.
4.1.3. Release notes for Red Hat OpenShift Pipelines General Availability 1.7
With this update, Red Hat OpenShift Pipelines General Availability (GA) 1.7 is available on OpenShift Container Platform 4.9, 4.10, and 4.11.
4.1.3.1. New features
In addition to the fixes and stability improvements, the following sections highlight what is new in Red Hat OpenShift Pipelines 1.7.
4.1.3.1.1. Pipelines
With this update,
pipelines-<version>is the default channel to install the Red Hat OpenShift Pipelines Operator. For example, the default channel to install the Pipelines Operator version1.7ispipelines-1.7. Cluster administrators can also use thelatestchannel to install the most recent stable version of the Operator.NoteThe
previewandstablechannels will be deprecated and removed in a future release.When you run a command in a user namespace, your container runs as
root(user id0) but has user privileges on the host. With this update, to run pods in the user namespace, you must pass the annotations that CRI-O expects.-
To add these annotations for all users, run the
oc edit clustertask buildahcommand and edit thebuildahcluster task. - To add the annotations to a specific namespace, export the cluster task as a task to that namespace.
-
To add these annotations for all users, run the
Before this update, if certain conditions were not met, the
whenexpression skipped aTaskobject and its dependent tasks. With this update, you can scope thewhenexpression to guard theTaskobject only, not its dependent tasks. To enable this update, set thescope-when-expressions-to-taskflag totruein theTektonConfigCRD.NoteThe
scope-when-expressions-to-taskflag is deprecated and will be removed in a future release. As a best practice for Pipelines, usewhenexpressions scoped to the guardedTaskonly.-
With this update, you can use variable substitution in the
subPathfield of a workspace within a task. With this update, you can reference parameters and results by using a bracket notation with single or double quotes. Prior to this update, you could only use the dot notation. For example, the following are now equivalent:
$(param.myparam),$(param['myparam']), and$(param["myparam"]).You can use single or double quotes to enclose parameter names that contain problematic characters, such as
".". For example,$(param['my.param'])and$(param["my.param"]).
-
With this update, you can include the
onErrorparameter of a step in the task definition without enabling theenable-api-fieldsflag.
4.1.3.1.2. Triggers
-
With this update, the
feature-flag-triggersconfig map has a new fieldlabels-exclusion-pattern. You can set the value of this field to a regular expression (regex) pattern. The controller filters out labels that match the regex pattern from propagating from the event listener to the resources created for the event listener. -
With this update, the
TriggerGroupsfield is added to theEventListenerspecification. Using this field, you can specify a set of interceptors to run before selecting and running a group of triggers. To enable this feature, set theenable-api-fieldsflag in thefeature-flags-triggersconfig map toalpha. -
With this update,
Triggerresources support custom runs defined by aTriggerTemplatetemplate. -
With this update, Triggers support emitting Kubernetes events from an
EventListenerpod. -
With this update, count metrics are available for the following objects:
ClusterInteceptor,EventListener,TriggerTemplate,ClusterTriggerBinding, andTriggerBinding. -
This update adds the
ServicePortspecification to Kubernetes resource. You can use this specification to modify which port exposes the event listener service. The default port is8080. -
With this update, you can use the
targetURIfield in theEventListenerspecification to send cloud events during trigger processing. To enable this feature, set theenable-api-fieldsflag in thefeature-flags-triggersconfig map toalpha. -
With this update, the
tekton-triggers-eventlistener-rolesobject now has apatchverb, in addition to thecreateverb that already exists. -
With this update, the
securityContext.runAsUserparameter is removed from event listener deployment.
4.1.3.1.3. CLI
With this update, the
tkn [pipeline | pipelinerun] exportcommand exports a pipeline or pipeline run as a YAML file. For example:Export a pipeline named
test_pipelinein theopenshift-pipelinesnamespace:$ tkn pipeline export test_pipeline -n openshift-pipelinesExport a pipeline run named
test_pipeline_runin theopenshift-pipelinesnamespace:$ tkn pipelinerun export test_pipeline_run -n openshift-pipelines
-
With this update, the
--graceoption is added to thetkn pipelinerun cancel. Use the--graceoption to terminate a pipeline run gracefully instead of forcing the termination. To enable this feature, set theenable-api-fieldsflag in thefeature-flagsconfig map toalpha. This update adds the Operator and Chains versions to the output of the
tkn versioncommand.ImportantTekton Chains is a Technology Preview feature.
-
With this update, the
tkn pipelinerun describecommand displays all canceled task runs, when you cancel a pipeline run. Before this fix, only one task run was displayed. -
With this update, you can skip supplying the asking specifications for optional workspace when you run the
tkn [t | p | ct] startcommand skips with the--skip-optional-workspaceflag. You can also skip it when running in interactive mode. With this update, you can use the
tkn chainscommand to manage Tekton Chains. You can also use the--chains-namespaceoption to specify the namespace where you want to install Tekton Chains.ImportantTekton Chains is a Technology Preview feature.
4.1.3.1.4. Operator
With this update, you can use the Red Hat OpenShift Pipelines Operator to install and deploy Tekton Hub and Tekton Chains.
ImportantTekton Chains and deployment of Tekton Hub on a cluster are Technology Preview features.
With this update, you can find and use Pipelines as Code (PAC) as an add-on option.
ImportantPipelines as Code is a Technology Preview feature.
With this update, you can now disable the installation of community cluster tasks by setting the
communityClusterTasksparameter tofalse. For example:... spec: profile: all targetNamespace: openshift-pipelines addon: params: - name: clusterTasks value: "true" - name: pipelineTemplates value: "true" - name: communityClusterTasks value: "false" ...With this update, you can disable the integration of Tekton Hub with the Developer perspective by setting the
enable-devconsole-integrationflag in theTektonConfigcustom resource tofalse. For example:... hub: params: - name: enable-devconsole-integration value: "true" ...-
With this update, the
operator-config.yamlconfig map enables the output of thetkn versioncommand to display of the Operator version. -
With this update, the version of the
argocd-task-sync-and-waittasks is modified tov0.2. -
With this update to the
TektonConfigCRD, theoc get tektonconfigcommand displays the OPerator version. - With this update, service monitor is added to the Triggers metrics.
4.1.3.1.5. Hub
Deploying Tekton Hub on a cluster is a Technology Preview feature.
Tekton Hub helps you discover, search, and share reusable tasks and pipelines for your CI/CD workflows. A public instance of Tekton Hub is available at hub.tekton.dev.
Staring with Red Hat OpenShift Pipelines 1.7, cluster administrators can also install and deploy a custom instance of Tekton Hub on enterprise clusters. You can curate a catalog with reusable tasks and pipelines specific to your organization.
4.1.3.1.6. Chains
Tekton Chains is a Technology Preview feature.
Tekton Chains is a Kubernetes Custom Resource Definition (CRD) controller. You can use it to manage the supply chain security of the tasks and pipelines created using Red Hat OpenShift Pipelines.
By default, Tekton Chains monitors the task runs in your OpenShift Container Platform cluster. Chains takes snapshots of completed task runs, converts them to one or more standard payload formats, and signs and stores all artifacts.
Tekton Chains supports the following features:
-
You can sign task runs, task run results, and OCI registry images with cryptographic key types and services such as
cosign. -
You can use attestation formats such as
in-toto. - You can securely store signatures and signed artifacts using OCI repository as a storage backend.
4.1.3.1.7. Pipelines as Code (PAC)
Pipelines as Code is a Technology Preview feature.
With Pipelines as Code, cluster administrators and users with the required privileges can define pipeline templates as part of source code Git repositories. When triggered by a source code push or a pull request for the configured Git repository, the feature runs the pipeline and reports status.
Pipelines as Code supports the following features:
- Pull request status. When iterating over a pull request, the status and control of the pull request is exercised on the platform hosting the Git repository.
- GitHub checks the API to set the status of a pipeline run, including rechecks.
- GitHub pull request and commit events.
-
Pull request actions in comments, such as
/retest. - Git events filtering, and a separate pipeline for each event.
- Automatic task resolution in Pipelines for local tasks, Tekton Hub, and remote URLs.
- Use of GitHub blobs and objects API for retrieving configurations.
-
Access Control List (ACL) over a GitHub organization, or using a Prow-style
OWNERfile. -
The
tkn-pacplugin for thetknCLI tool, which you can use to manage Pipelines as Code repositories and bootstrapping. - Support for GitHub Application, GitHub Webhook, Bitbucket Server, and Bitbucket Cloud.
4.1.3.2. Deprecated features
-
Breaking change: This update removes the
disable-working-directory-overwriteanddisable-home-env-overwritefields from theTektonConfigcustom resource (CR). As a result, theTektonConfigCR no longer automatically sets the$HOMEenvironment variable andworkingDirparameter. You can still set the$HOMEenvironment variable andworkingDirparameter by using theenvandworkingDirfields in theTaskcustom resource definition (CRD).
-
The
Conditionscustom resource definition (CRD) type is deprecated and planned to be removed in a future release. Instead, use the recommendedWhenexpression.
-
Breaking change: The
Triggersresource validates the templates and generates an error if you do not specify theEventListenerandTriggerBindingvalues.
4.1.3.3. Known issues
When you run Maven and Jib-Maven cluster tasks, the default container image is supported only on Intel (x86) architecture. Therefore, tasks will fail on IBM Power Systems (ppc64le), IBM Z, and LinuxONE (s390x) clusters. As a workaround, you can specify a custom image by setting the
MAVEN_IMAGEparameter value tomaven:3.6.3-adoptopenjdk-11.TipBefore you install tasks based on the Tekton Catalog on IBM Power Systems (ppc64le), IBM Z, and LinuxONE (s390x) using
tkn hub, verify if the task can be executed on these platforms. To check ifppc64leands390xare listed in the "Platforms" section of the task information, you can run the following command:tkn hub info task <name>-
On IBM Power Systems, IBM Z, and LinuxONE, the
s2i-dotnetcluster task is unsupported. You cannot use the
nodejs:14-ubi8-minimalimage stream because doing so generates the following errors:STEP 7: RUN /usr/libexec/s2i/assemble /bin/sh: /usr/libexec/s2i/assemble: No such file or directory subprocess exited with status 127 subprocess exited with status 127 error building at STEP "RUN /usr/libexec/s2i/assemble": exit status 127 time="2021-11-04T13:05:26Z" level=error msg="exit status 127"
-
Implicit parameter mapping incorrectly passes parameters from the top-level
PipelineorPipelineRundefinitions to thetaskReftasks. Mapping should only occur from a top-level resource to tasks with in-linetaskSpecspecifications. This issue only affects users who have set theenable-api-fieldsfeature flag toalpha.
4.1.3.4. Fixed issues
-
With this update, if metadata such as
labelsandannotationsare present in bothPipelineandPipelineRunobject definitions, the values in thePipelineRuntype takes precedence. You can observe similar behavior forTaskandTaskRunobjects. -
With this update, if the
timeouts.tasksfield or thetimeouts.finallyfield is set to0, then thetimeouts.pipelineis also set to0. -
With this update, the
-xset flag is removed from scripts that do not use a shebang. The fix reduces potential data leak from script execution. -
With this update, any backslash character present in the usernames in Git credentials is escaped with an additional backslash in the
.gitconfigfile.
-
With this update, the
finalizerproperty of theEventListenerobject is not necessary for cleaning up logging and config maps. - With this update, the default HTTP client associated with the event listener server is removed, and a custom HTTP client added. As a result, the timeouts have improved.
- With this update, the Triggers cluster role now works with owner references.
- With this update, the race condition in the event listener does not happen when multiple interceptors return extensions.
-
With this update, the
tkn pr deletecommand does not delete the pipeline runs with theignore-runningflag.
- With this update, the Operator pods do not continue restarting when you modify any add-on parameters.
-
With this update, the
tkn serveCLI pod is scheduled on infra nodes, if not configured in the subscription and config custom resources. - With this update, cluster tasks with specified versions are not deleted during upgrade.
4.1.3.5. Release notes for Red Hat OpenShift Pipelines General Availability 1.7.1
With this update, Red Hat OpenShift Pipelines General Availability (GA) 1.7.1 is available on OpenShift Container Platform 4.9, 4.10, and 4.11.
4.1.3.5.1. Fixed issues
- Before this update, upgrading the Red Hat OpenShift Pipelines Operator deleted the data in the database associated with Tekton Hub and installed a new database. With this update, an Operator upgrade preserves the data.
- Before this update, only cluster administrators could access pipeline metrics in the OpenShift Container Platform console. With this update, users with other cluster roles also can access the pipeline metrics.
-
Before this update, pipeline runs failed for pipelines containing tasks that emit large termination messages. The pipeline runs failed because the total size of termination messages of all containers in a pod cannot exceed 12 KB. With this update, the
place-toolsandstep-initinitialization containers that uses the same image are merged to reduce the number of containers running in each tasks’s pod. The solution reduces the chance of failed pipeline runs by minimizing the number of containers running in a task’s pod. However, it does not remove the limitation of the maximum allowed size of a termination message. -
Before this update, attempts to access resource URLs directly from the Tekton Hub web console resulted in an Nginx
404error. With this update, the Tekton Hub web console image is fixed to allow accessing resource URLs directly from the Tekton Hub web console. - Before this update, for each namespace the resource pruner job created a separate container to prune resources. With this update, the resource pruner job runs commands for all namespaces as a loop in one container.
4.1.3.6. Release notes for Red Hat OpenShift Pipelines General Availability 1.7.2
With this update, Red Hat OpenShift Pipelines General Availability (GA) 1.7.2 is available on OpenShift Container Platform 4.9, 4.10, and the upcoming version.
4.1.3.6.1. Known issues
-
The
chains-configconfig map for Tekton Chains in theopenshift-pipelinesnamespace is automatically reset to default after upgrading the Red Hat OpenShift Pipelines Operator. Currently, there is no workaround for this issue.
4.1.3.6.2. Fixed issues
-
Before this update, tasks on Pipelines 1.7.1 failed on using
initas the first argument, followed by two or more arguments. With this update, the flags are parsed correctly and the task runs are successful. Before this update, installation of the Red Hat OpenShift Pipelines Operator on OpenShift Container Platform 4.9 and 4.10 failed due to invalid role binding, with the following error message:
error updating rolebinding openshift-operators-prometheus-k8s-read-binding: RoleBinding.rbac.authorization.k8s.io "openshift-operators-prometheus-k8s-read-binding" is invalid: roleRef: Invalid value: rbac.RoleRef{APIGroup:"rbac.authorization.k8s.io", Kind:"Role", Name:"openshift-operator-read"}: cannot change roleRefWith this update, the Red Hat OpenShift Pipelines Operator installs with distinct role binding namespaces to avoid conflict with installation of other Operators.
Before this update, upgrading the Operator triggered a reset of the
signing-secretssecret key for Tekton Chains to its default value. With this update, the custom secret key persists after you upgrade the Operator.NoteUpgrading to Red Hat OpenShift Pipelines 1.7.2 resets the key. However, when you upgrade to future releases, the key is expected to persist.
Before this update, all S2I build tasks failed with an error similar to the following message:
Error: error writing "0 0 4294967295\n" to /proc/22/uid_map: write /proc/22/uid_map: operation not permitted time="2022-03-04T09:47:57Z" level=error msg="error writing \"0 0 4294967295\\n\" to /proc/22/uid_map: write /proc/22/uid_map: operation not permitted" time="2022-03-04T09:47:57Z" level=error msg="(unable to determine exit status)"With this update, the
pipelines-sccsecurity context constraint (SCC) is compatible with theSETFCAPcapability necessary forBuildahandS2Icluster tasks. As a result, theBuildahandS2Ibuild tasks can run successfully.To successfully run the
Buildahcluster task andS2Ibuild tasks for applications written in various languages and frameworks, add the following snippet for appropriatestepsobjects such asbuildandpush:securityContext: capabilities: add: ["SETFCAP"]
4.1.3.7. Release notes for Red Hat OpenShift Pipelines General Availability 1.7.3
With this update, Red Hat OpenShift Pipelines General Availability (GA) 1.7.3 is available on OpenShift Container Platform 4.9, 4.10, and 4.11.
4.1.3.7.1. Fixed issues
-
Before this update, the Operator failed when creating RBAC resources if any namespace was in a
Terminatingstate. With this update, the Operator ignores namespaces in aTerminatingstate and creates the RBAC resources. -
Previously, upgrading the Red Hat OpenShift Pipelines Operator caused the
pipelineservice account to be recreated, which meant that the secrets linked to the service account were lost. This update fixes the issue. During upgrades, the Operator no longer recreates thepipelineservice account. As a result, secrets attached to thepipelineservice account persist after upgrades, and the resources (tasks and pipelines) continue to work correctly.
4.1.4. Release notes for Red Hat OpenShift Pipelines General Availability 1.6
With this update, Red Hat OpenShift Pipelines General Availability (GA) 1.6 is available on OpenShift Container Platform 4.9.
4.1.4.1. New features
In addition to the fixes and stability improvements, the following sections highlight what is new in Red Hat OpenShift Pipelines 1.6.
-
With this update, you can configure a pipeline or task
startcommand to return a YAML or JSON-formatted string by using the--output <string>, where<string>isyamlorjson. Otherwise, without the--outputoption, thestartcommand returns a human-friendly message that is hard for other programs to parse. Returning a YAML or JSON-formatted string is useful for continuous integration (CI) environments. For example, after a resource is created, you can useyqorjqto parse the YAML or JSON-formatted message about the resource and wait until that resource is terminated without using theshowlogoption. -
With this update, you can authenticate to a registry using the
auth.jsonauthentication file of Podman. For example, you can usetkn bundle pushto push to a remote registry using Podman instead of Docker CLI. -
With this update, if you use the
tkn [taskrun | pipelinerun] delete --allcommand, you can preserve runs that are younger than a specified number of minutes by using the new--keep-since <minutes>option. For example, to keep runs that are less than five minutes old, you entertkn [taskrun | pipelinerun] delete -all --keep-since 5. -
With this update, when you delete task runs or pipeline runs, you can use the
--parent-resourceand--keep-sinceoptions together. For example, thetkn pipelinerun delete --pipeline pipelinename --keep-since 5command preserves pipeline runs whose parent resource is namedpipelinenameand whose age is five minutes or less. Thetkn tr delete -t <taskname> --keep-since 5andtkn tr delete --clustertask <taskname> --keep-since 5commands work similarly for task runs. -
This update adds support for the triggers resources to work with
v1beta1resources.
-
This update adds an
ignore-runningoption to thetkn pipelinerun deleteandtkn taskrun deletecommands. -
This update adds a
createsubcommand to thetkn taskandtkn clustertaskcommands. -
With this update, when you use the
tkn pipelinerun delete --allcommand, you can use the new--label <string>option to filter the pipeline runs by label. Optionally, you can use the--labeloption with=and==as equality operators, or!=as an inequality operator. For example, thetkn pipelinerun delete --all --label asdfandtkn pipelinerun delete --all --label==asdfcommands both delete all the pipeline runs that have theasdflabel. - With this update, you can fetch the version of installed Tekton components from the config map or, if the config map is not present, from the deployment controller.
-
With this update, triggers support the
feature-flagsandconfig-defaultsconfig map to configure feature flags and to set default values respectively. -
This update adds a new metric,
eventlistener_event_count, that you can use to count events received by theEventListenerresource. This update adds
v1beta1Go API types. With this update, triggers now support thev1beta1API version.With the current release, the
v1alpha1features are now deprecated and will be removed in a future release. Begin using thev1beta1features instead.
In the current release, auto-prunning of resources is enabled by default. In addition, you can configure auto-prunning of task run and pipeline run for each namespace separately, by using the following new annotations:
-
operator.tekton.dev/prune.schedule: If the value of this annotation is different from the value specified at theTektonConfigcustom resource definition, a new cron job in that namespace is created. -
operator.tekton.dev/prune.skip: When set totrue, the namespace for which it is configured will not be prunned. -
operator.tekton.dev/prune.resources: This annotation accepts a comma-separated list of resources. To prune a single resource such as a pipeline run, set this annotation to"pipelinerun". To prune multiple resources, such as task run and pipeline run, set this annotation to"taskrun, pipelinerun". -
operator.tekton.dev/prune.keep: Use this annotation to retain a resource without prunning. operator.tekton.dev/prune.keep-since: Use this annotation to retain resources based on their age. The value for this annotation must be equal to the age of the resource in minutes. For example, to retain resources which were created not more than five days ago, setkeep-sinceto7200.NoteThe
keepandkeep-sinceannotations are mutually exclusive. For any resource, you must configure only one of them.-
operator.tekton.dev/prune.strategy: Set the value of this annotation to eitherkeeporkeep-since.
-
-
Administrators can disable the creation of the
pipelineservice account for the entire cluster, and prevent privilege escalation by misusing the associated SCC, which is very similar toanyuid. -
You can now configure feature flags and components by using the
TektonConfigcustom resource (CR) and the CRs for individual components, such asTektonPipelineandTektonTriggers. This level of granularity helps customize and test alpha features such as the Tekton OCI bundle for individual components. -
You can now configure optional
Timeoutsfield for thePipelineRunresource. For example, you can configure timeouts separately for a pipeline run, each task run, and thefinallytasks. -
The pods generated by the
TaskRunresource now sets theactiveDeadlineSecondsfield of the pods. This enables OpenShift to consider them as terminating, and allows you to use specifically scopedResourceQuotaobject for the pods. - You can use configmaps to eliminate metrics tags or labels type on a task run, pipeline run, task, and pipeline. In addition, you can configure different types of metrics for measuring duration, such as a histogram, gauge, or last value.
-
You can define requests and limits on a pod coherently, as Tekton now fully supports the
LimitRangeobject by considering theMin,Max,Default, andDefaultRequestfields. The following alpha features are introduced:
A pipeline run can now stop after running the
finallytasks, rather than the previous behavior of stopping the execution of all task run directly. This update adds the followingspec.statusvalues:-
StoppedRunFinallywill stop the currently running tasks after they are completed, and then run thefinallytasks. -
CancelledRunFinallywill immediately cancel the running tasks, and then run thefinallytasks. Cancelledwill retain the previous behavior provided by thePipelineRunCancelledstatus.NoteThe
Cancelledstatus replaces the deprecatedPipelineRunCancelledstatus, which will be removed in thev1version.
-
-
You can now use the
oc debugcommand to put a task run into debug mode, which pauses the execution and allows you to inspect specific steps in a pod. -
When you set the
onErrorfield of a step tocontinue, the exit code for the step is recorded and passed on to subsequent steps. However, the task run does not fail and the execution of the rest of the steps in the task continues. To retain the existing behavior, you can set the value of theonErrorfield tostopAndFail. - Tasks can now accept more parameters than are actually used. When the alpha feature flag is enabled, the parameters can implicitly propagate to inlined specs. For example, an inlined task can access parameters of its parent pipeline run, without explicitly defining each parameter for the task.
-
If you enable the flag for the alpha features, the conditions under
Whenexpressions will only apply to the task with which it is directly associated, and not the dependents of the task. To apply theWhenexpressions to the associated task and its dependents, you must associate the expression with each dependent task separately. Note that, going forward, this will be the default behavior of theWhenexpressions in any new API versions of Tekton. The existing default behavior will be deprecated in favor of this update.
The current release enables you to configure node selection by specifying the
nodeSelectorandtolerationsvalues in theTektonConfigcustom resource (CR). The Operator adds these values to all the deployments that it creates.-
To configure node selection for the Operator’s controller and webhook deployment, you edit the
config.nodeSelectorandconfig.tolerationsfields in the specification for theSubscriptionCR, after installing the Operator. -
To deploy the rest of the control plane pods of OpenShift Pipelines on an infrastructure node, update the
TektonConfigCR with thenodeSelectorandtolerationsfields. The modifications are then applied to all the pods created by Operator.
-
To configure node selection for the Operator’s controller and webhook deployment, you edit the
4.1.4.2. Deprecated features
-
In CLI 0.21.0, support for all
v1alpha1resources forclustertask,task,taskrun,pipeline, andpipelineruncommands are deprecated. These resources are now deprecated and will be removed in a future release.
In Tekton Triggers v0.16.0, the redundant
statuslabel is removed from the metrics for theEventListenerresource.ImportantBreaking change: The
statuslabel has been removed from theeventlistener_http_duration_seconds_*metric. Remove queries that are based on thestatuslabel.-
With the current release, the
v1alpha1features are now deprecated and will be removed in a future release. With this update, you can begin using thev1beta1Go API types instead. Triggers now supports thev1beta1API version. With the current release, the
EventListenerresource sends a response before the triggers finish processing.ImportantBreaking change: With this change, the
EventListenerresource stops responding with a201 Createdstatus code when it creates resources. Instead, it responds with a202 Acceptedresponse code.The current release removes the
podTemplatefield from theEventListenerresource.ImportantBreaking change: The
podTemplatefield, which was deprecated as part of #1100, has been removed.The current release removes the deprecated
replicasfield from the specification for theEventListenerresource.ImportantBreaking change: The deprecated
replicasfield has been removed.
In Red Hat OpenShift Pipelines 1.6, the values of
HOME="/tekton/home"andworkingDir="/workspace"are removed from the specification of theStepobjects.Instead, Red Hat OpenShift Pipelines sets
HOMEandworkingDirto the values defined by the containers running theStepobjects. You can override these values in the specification of yourStepobjects.To use the older behavior, you can change the
disable-working-directory-overwriteanddisable-home-env-overwritefields in theTektonConfigCR tofalse:apiVersion: operator.tekton.dev/v1alpha1 kind: TektonConfig metadata: name: config spec: pipeline: disable-working-directory-overwrite: false disable-home-env-overwrite: false ...ImportantThe
disable-working-directory-overwriteanddisable-home-env-overwritefields in theTektonConfigCR are now deprecated and will be removed in a future release.
4.1.4.3. Known issues
-
When you run Maven and Jib-Maven cluster tasks, the default container image is supported only on Intel (x86) architecture. Therefore, tasks will fail on IBM Power Systems (ppc64le), IBM Z, and LinuxONE (s390x) clusters. As a workaround, you can specify a custom image by setting the
MAVEN_IMAGEparameter value tomaven:3.6.3-adoptopenjdk-11. -
On IBM Power Systems, IBM Z, and LinuxONE, the
s2i-dotnetcluster task is unsupported. -
Before you install tasks based on the Tekton Catalog on IBM Power Systems (ppc64le), IBM Z, and LinuxONE (s390x) using
tkn hub, verify if the task can be executed on these platforms. To check ifppc64leands390xare listed in the "Platforms" section of the task information, you can run the following command:tkn hub info task <name> You cannot use the
nodejs:14-ubi8-minimalimage stream because doing so generates the following errors:STEP 7: RUN /usr/libexec/s2i/assemble /bin/sh: /usr/libexec/s2i/assemble: No such file or directory subprocess exited with status 127 subprocess exited with status 127 error building at STEP "RUN /usr/libexec/s2i/assemble": exit status 127 time="2021-11-04T13:05:26Z" level=error msg="exit status 127"
4.1.4.4. Fixed issues
-
The
tkn hubcommand is now supported on IBM Power Systems, IBM Z, and LinuxONE.
-
Before this update, the terminal was not available after the user ran a
tkncommand, and the pipeline run was done, even ifretrieswere specified. Specifying a timeout in the task run or pipeline run had no effect. This update fixes the issue so that the terminal is available after running the command. -
Before this update, running
tkn pipelinerun delete --allwould delete all resources. This update prevents the resources in the running state from getting deleted. -
Before this update, using the
tkn version --component=<component>command did not return the component version. This update fixes the issue so that this command returns the component version. -
Before this update, when you used the
tkn pr logscommand, it displayed the pipelines output logs in the wrong task order. This update resolves the issue so that logs of completedPipelineRunsare listed in the appropriateTaskRunexecution order.
-
Before this update, editing the specification of a running pipeline might prevent the pipeline run from stopping when it was complete. This update fixes the issue by fetching the definition only once and then using the specification stored in the status for verification. This change reduces the probability of a race condition when a
PipelineRunor aTaskRunrefers to aPipelineorTaskthat changes while it is running. -
Whenexpression values can now have array parameter references, such as:values: [$(params.arrayParam[*])].
4.1.4.5. Release notes for Red Hat OpenShift Pipelines General Availability 1.6.1
4.1.4.5.1. Known issues
After upgrading to Red Hat OpenShift Pipelines 1.6.1 from an older version, Pipelines might enter an inconsistent state where you are unable to perform any operations (create/delete/apply) on Tekton resources (tasks and pipelines). For example, while deleting a resource, you might encounter the following error:
Error from server (InternalError): Internal error occurred: failed calling webhook "validation.webhook.pipeline.tekton.dev": Post "https://tekton-pipelines-webhook.openshift-pipelines.svc:443/resource-validation?timeout=10s": service "tekton-pipelines-webhook" not found.
4.1.4.5.2. Fixed issues
The
SSL_CERT_DIRenvironment variable (/tekton-custom-certs) set by Red Hat OpenShift Pipelines will not override the following default system directories with certificate files:-
/etc/pki/tls/certs -
/etc/ssl/certs -
/system/etc/security/cacerts
-
- The Horizontal Pod Autoscaler can manage the replica count of deployments controlled by the Red Hat OpenShift Pipelines Operator. From this release onward, if the count is changed by an end user or an on-cluster agent, the Red Hat OpenShift Pipelines Operator will not reset the replica count of deployments managed by it. However, the replicas will be reset when you upgrade the Red Hat OpenShift Pipelines Operator.
-
The pod serving the
tknCLI will now be scheduled on nodes, based on the node selector and toleration limits specified in theTektonConfigcustom resource.
4.1.4.6. Release notes for Red Hat OpenShift Pipelines General Availability 1.6.2
4.1.4.6.1. Known issues
-
When you create a new project, the creation of the
pipelineservice account is delayed, and removal of existing cluster tasks and pipeline templates takes more than 10 minutes.
4.1.4.6.2. Fixed issues
-
Before this update, multiple instances of Tekton installer sets were created for a pipeline after upgrading to Red Hat OpenShift Pipelines 1.6.1 from an older version. With this update, the Operator ensures that only one instance of each type of
TektonInstallerSetexists after an upgrade. - Before this update, all the reconcilers in the Operator used the component version to decide resource recreation during an upgrade to Red Hat OpenShift Pipelines 1.6.1 from an older version. As a result, those resources were not recreated whose component versions did not change in the upgrade. With this update, the Operator uses the Operator version instead of the component version to decide resource recreation during an upgrade.
- Before this update, the pipelines webhook service was missing in the cluster after an upgrade. This was due to an upgrade deadlock on the config maps. With this update, a mechanism is added to disable webhook validation if the config maps are absent in the cluster. As a result, the pipelines webhook service persists in the cluster after an upgrade.
- Before this update, cron jobs for auto-pruning got recreated after any configuration change to the namespace. With this update, cron jobs for auto-pruning get recreated only if there is a relevant annotation change in the namespace.
The upstream version of Tekton Pipelines is revised to
v0.28.3, which has the following fixes:-
Fix
PipelineRunorTaskRunobjects to allow label or annotation propagation. For implicit params:
-
Do not apply the
PipelineSpecparameters to theTaskRefsobject. -
Disable implicit param behavior for the
Pipelineobjects.
-
Do not apply the
-
Fix
4.1.4.7. Release notes for Red Hat OpenShift Pipelines General Availability 1.6.3
4.1.4.7.1. Fixed issues
Before this update, the Red Hat OpenShift Pipelines Operator installed pod security policies from components such as Pipelines and Triggers. However, the pod security policies shipped as part of the components were deprecated in an earlier release. With this update, the Operator stops installing pod security policies from components. As a result, the following upgrade paths are affected:
- Upgrading from Pipelines 1.6.1 or 1.6.2 to Pipelines 1.6.3 deletes the pod security policies, including those from the Pipelines and Triggers components.
Upgrading from Pipelines 1.5.x to 1.6.3 retains the pod security policies installed from components. As a cluster administrator, you can delete them manually.
NoteWhen you upgrade to future releases, the Red Hat OpenShift Pipelines Operator will automatically delete all obsolete pod security policies.
- Before this update, only cluster administrators could access pipeline metrics in the OpenShift Container Platform console. With this update, users with other cluster roles also can access the pipeline metrics.
- Before this update, role-based access control (RBAC) issues with the Pipelines Operator caused problems upgrading or installing components. This update improves the reliability and consistency of installing various Red Hat OpenShift Pipelines components.
-
Before this update, setting the
clusterTasksandpipelineTemplatesfields tofalsein theTektonConfigCR slowed the removal of cluster tasks and pipeline templates. This update improves the speed of lifecycle management of Tekton resources such as cluster tasks and pipeline templates.
4.1.4.8. Release notes for Red Hat OpenShift Pipelines General Availability 1.6.4
4.1.4.8.1. Known issues
After upgrading from Red Hat OpenShift Pipelines 1.5.2 to 1.6.4, accessing the event listener routes returns a
503error.Workaround: Modify the target port in the YAML file for the event listener’s route.
Extract the route name for the relevant namespace.
$ oc get route -n <namespace>Edit the route to modify the value of the
targetPortfield.$ oc edit route -n <namespace> <el-route_name>Example: Existing event listener route
... spec: host: el-event-listener-q8c3w5-test-upgrade1.apps.ve49aws.aws.ospqa.com port: targetPort: 8000 to: kind: Service name: el-event-listener-q8c3w5 weight: 100 wildcardPolicy: None ...Example: Modified event listener route
... spec: host: el-event-listener-q8c3w5-test-upgrade1.apps.ve49aws.aws.ospqa.com port: targetPort: http-listener to: kind: Service name: el-event-listener-q8c3w5 weight: 100 wildcardPolicy: None ...
4.1.4.8.2. Fixed issues
-
Before this update, the Operator failed when creating RBAC resources if any namespace was in a
Terminatingstate. With this update, the Operator ignores namespaces in aTerminatingstate and creates the RBAC resources. - Before this update, the task runs failed or restarted due to absence of annotation specifying the release version of the associated Tekton controller. With this update, the inclusion of the appropriate annotations are automated, and the tasks run without failure or restarts.
4.1.5. Release notes for Red Hat OpenShift Pipelines General Availability 1.5
Red Hat OpenShift Pipelines General Availability (GA) 1.5 is now available on OpenShift Container Platform 4.8.
4.1.5.1. Compatibility and support matrix
Some features in this release are currently in Technology Preview. These experimental features are not intended for production use.
In the table, features are marked with the following statuses:
| TP | Technology Preview |
| GA | General Availability |
Note the following scope of support on the Red Hat Customer Portal for these features:
| Feature | Version | Support Status |
|---|---|---|
| Pipelines | 0.24 | GA |
| CLI | 0.19 | GA |
| Catalog | 0.24 | GA |
| Triggers | 0.14 | TP |
| Pipeline resources | - | TP |
For questions and feedback, you can send an email to the product team at pipelines-interest@redhat.com.
4.1.5.2. New features
In addition to the fixes and stability improvements, the following sections highlight what is new in Red Hat OpenShift Pipelines 1.5.
Pipeline run and task runs will be automatically pruned by a cron job in the target namespace. The cron job uses the
IMAGE_JOB_PRUNER_TKNenvironment variable to get the value oftkn image. With this enhancement, the following fields are introduced to theTektonConfigcustom resource:... pruner: resources: - pipelinerun - taskrun schedule: "*/5 * * * *" # cron schedule keep: 2 # delete all keeping n ...In OpenShift Container Platform, you can customize the installation of the Tekton Add-ons component by modifying the values of the new parameters
clusterTasksandpipelinesTemplatesin theTektonConfigcustom resource:apiVersion: operator.tekton.dev/v1alpha1 kind: TektonConfig metadata: name: config spec: profile: all targetNamespace: openshift-pipelines addon: params: - name: clusterTasks value: "true" - name: pipelineTemplates value: "true" ...The customization is allowed if you create the add-on using
TektonConfig, or directly by using Tekton Add-ons. However, if the parameters are not passed, the controller adds parameters with default values.Note-
If add-on is created using the
TektonConfigcustom resource, and you change the parameter values later in theAddoncustom resource, then the values in theTektonConfigcustom resource overwrites the changes. -
You can set the value of the
pipelinesTemplatesparameter totrueonly when the value of theclusterTasksparameter istrue.
-
If add-on is created using the
The
enableMetricsparameter is added to theTektonConfigcustom resource. You can use it to disable the service monitor, which is part of Tekton Pipelines for OpenShift Container Platform.apiVersion: operator.tekton.dev/v1alpha1 kind: TektonConfig metadata: name: config spec: profile: all targetNamespace: openshift-pipelines pipeline: params: - name: enableMetrics value: "true" ...- Eventlistener OpenCensus metrics, which captures metrics at process level, is added.
- Triggers now has label selector; you can configure triggers for an event listener using labels.
The
ClusterInterceptorcustom resource definition for registering interceptors is added, which allows you to register newInterceptortypes that you can plug in. In addition, the following relevant changes are made:-
In the trigger specifications, you can configure interceptors using a new API that includes a
reffield to refer to a cluster interceptor. In addition, you can use theparamsfield to add parameters that pass on to the interceptors for processing. -
The bundled interceptors CEL, GitHub, GitLab, and BitBucket, have been migrated. They are implemented using the new
ClusterInterceptorcustom resource definition. -
Core interceptors are migrated to the new format, and any new triggers created using the old syntax automatically switch to the new
reforparamsbased syntax.
-
In the trigger specifications, you can configure interceptors using a new API that includes a
-
To disable prefixing the name of the task or step while displaying logs, use the
--prefixoption forlogcommands. -
To display the version of a specific component, use the new
--componentflag in thetkn versioncommand. -
The
tkn hub check-upgradecommand is added, and other commands are revised to be based on the pipeline version. In addition, catalog names are displayed in thesearchcommand output. -
Support for optional workspaces are added to the
startcommand. -
If the plugins are not present in the
pluginsdirectory, they are searched in the current path. The
tkn start [task | clustertask | pipeline]command starts interactively and ask for theparamsvalue, even when you specify the default parameters are specified. To stop the interactive prompts, pass the--use-param-defaultsflag at the time of invoking the command. For example:$ tkn pipeline start build-and-deploy \ -w name=shared-workspace,volumeClaimTemplateFile=https://raw.githubusercontent.com/openshift/pipelines-tutorial/pipelines-1.7/01_pipeline/03_persistent_volume_claim.yaml \ -p deployment-name=pipelines-vote-api \ -p git-url=https://github.com/openshift/pipelines-vote-api.git \ -p IMAGE=image-registry.openshift-image-registry.svc:5000/pipelines-tutorial/pipelines-vote-api \ --use-param-defaults-
The
versionfield is added in thetkn task describecommand. -
The option to automatically select resources such as
TriggerTemplate, orTriggerBinding, orClusterTriggerBinding, orEventlistener, is added in thedescribecommand, if only one is present. -
In the
tkn pr describecommand, a section for skipped tasks is added. -
Support for the
tkn clustertask logsis added. -
The YAML merge and variable from
config.yamlis removed. In addition, therelease.yamlfile can now be more easily consumed by tools such askustomizeandytt. - The support for resource names to contain the dot character (".") is added.
-
The
hostAliasesarray in thePodTemplatespecification is added to the pod-level override of hostname resolution. It is achieved by modifying the/etc/hostsfile. -
A variable
$(tasks.status)is introduced to access the aggregate execution status of tasks. - An entry-point binary build for Windows is added.
4.1.5.3. Deprecated features
In the
whenexpressions, support for fields written is PascalCase is removed. Thewhenexpressions only support fields written in lowercase.NoteIf you had applied a pipeline with
whenexpressions in Tekton Pipelinesv0.16(Operatorv1.2.x), you have to reapply it.When you upgrade the Red Hat OpenShift Pipelines Operator to
v1.5, theopenshift-clientand theopenshift-client-v-1-5-0cluster tasks have theSCRIPTparameter. However, theARGSparameter and thegitresource are removed from the specification of theopenshift-clientcluster task. This is a breaking change, and only those cluster tasks that do not have a specific version in thenamefield of theClusterTaskresource upgrade seamlessly.To prevent the pipeline runs from breaking, use the
SCRIPTparameter after the upgrade because it moves the values previously specified in theARGSparameter into theSCRIPTparameter of the cluster task. For example:... - name: deploy params: - name: SCRIPT value: oc rollout status <deployment-name> runAfter: - build taskRef: kind: ClusterTask name: openshift-client ...When you upgrade from Red Hat OpenShift Pipelines Operator
v1.4tov1.5, the profile names in which theTektonConfigcustom resource is installed now change.Expand Table 4.3. Profiles for TektonConfig custom resource Profiles in Pipelines 1.5 Corresponding profile in Pipelines 1.4 Installed Tekton components All (default profile)
All (default profile)
Pipelines, Triggers, Add-ons
Basic
Default
Pipelines, Triggers
Lite
Basic
Pipelines
NoteIf you used
profile: allin theconfiginstance of theTektonConfigcustom resource, no change is necessary in the resource specification.However, if the installed Operator is either in the Default or the Basic profile before the upgrade, you must edit the
configinstance of theTektonConfigcustom resource after the upgrade. For example, if the configuration wasprofile: basicbefore the upgrade, ensure that it isprofile: liteafter upgrading to Pipelines 1.5.The
disable-home-env-overwriteanddisable-working-dir-overwritefields are now deprecated and will be removed in a future release. For this release, the default value of these flags is set totruefor backward compatibility.NoteIn the next release (Red Hat OpenShift Pipelines 1.6), the
HOMEenvironment variable will not be automatically set to/tekton/home, and the default working directory will not be set to/workspacefor task runs. These defaults collide with any value set by image Dockerfile of the step.-
The
ServiceTypeandpodTemplatefields are removed from theEventListenerspec. - The controller service account no longer requests cluster-wide permission to list and watch namespaces.
The status of the
EventListenerresource has a new condition calledReady.NoteIn the future, the other status conditions for the
EventListenerresource will be deprecated in favor of theReadystatus condition.-
The
eventListenerandnamespacefields in theEventListenerresponse are deprecated. Use theeventListenerUIDfield instead. The
replicasfield is deprecated from theEventListenerspec. Instead, thespec.replicasfield is moved tospec.resources.kubernetesResource.replicasin theKubernetesResourcespec.NoteThe
replicasfield will be removed in a future release.-
The old method of configuring the core interceptors is deprecated. However, it continues to work until it is removed in a future release. Instead, interceptors in a
Triggerresource are now configured using a newrefandparamsbased syntax. The resulting default webhook automatically switch the usages of the old syntax to the new syntax for new triggers. -
Use
rbac.authorization.k8s.io/v1instead of the deprecatedrbac.authorization.k8s.io/v1beta1for theClusterRoleBindingresource. -
In cluster roles, the cluster-wide write access to resources such as
serviceaccounts,secrets,configmaps, andlimitrangesare removed. In addition, cluster-wide access to resources such asdeployments,statefulsets, anddeployment/finalizersare removed. -
The
imagecustom resource definition in thecaching.internal.knative.devgroup is not used by Tekton anymore, and is excluded in this release.
4.1.5.4. Known issues
The git-cli cluster task is built off the alpine/git base image, which expects
/rootas the user’s home directory. However, this is not explicitly set in thegit-clicluster task.In Tekton, the default home directory is overwritten with
/tekton/homefor every step of a task, unless otherwise specified. This overwriting of the$HOMEenvironment variable of the base image causes thegit-clicluster task to fail.This issue is expected to be fixed in the upcoming releases. For Red Hat OpenShift Pipelines 1.5 and earlier versions, you can use any one of the following workarounds to avoid the failure of the
git-clicluster task:Set the
$HOMEenvironment variable in the steps, so that it is not overwritten.-
[OPTIONAL] If you installed Red Hat OpenShift Pipelines using the Operator, then clone the
git-clicluster task into a separate task. This approach ensures that the Operator does not overwrite the changes made to the cluster task. -
Execute the
oc edit clustertasks git-clicommand. Add the expected
HOMEenvironment variable to the YAML of the step:... steps: - name: git env: - name: HOME value: /root image: $(params.BASE_IMAGE) workingDir: $(workspaces.source.path) ...WarningFor Red Hat OpenShift Pipelines installed by the Operator, if you do not clone the
git-clicluster task into a separate task before changing theHOMEenvironment variable, then the changes are overwritten during Operator reconciliation.
-
[OPTIONAL] If you installed Red Hat OpenShift Pipelines using the Operator, then clone the
Disable overwriting the
HOMEenvironment variable in thefeature-flagsconfig map.-
Execute the
oc edit -n openshift-pipelines configmap feature-flagscommand. Set the value of the
disable-home-env-overwriteflag totrue.Warning- If you installed Red Hat OpenShift Pipelines using the Operator, then the changes are overwritten during Operator reconciliation.
-
Modifying the default value of the
disable-home-env-overwriteflag can break other tasks and cluster tasks, as it changes the default behavior for all tasks.
-
Execute the
Use a different service account for the
git-clicluster task, as the overwriting of theHOMEenvironment variable happens when the default service account for pipelines is used.- Create a new service account.
- Link your Git secret to the service account you just created.
- Use the service account while executing a task or a pipeline.
-
On IBM Power Systems, IBM Z, and LinuxONE, the
s2i-dotnetcluster task and thetkn hubcommand are unsupported. -
When you run Maven and Jib-Maven cluster tasks, the default container image is supported only on Intel (x86) architecture. Therefore, tasks will fail on IBM Power Systems (ppc64le), IBM Z, and LinuxONE (s390x) clusters. As a workaround, you can specify a custom image by setting the
MAVEN_IMAGEparameter value tomaven:3.6.3-adoptopenjdk-11.
4.1.5.5. Fixed issues
-
The
whenexpressions indagtasks are not allowed to specify the context variable accessing the execution status ($(tasks.<pipelineTask>.status)) of any other task. -
Use Owner UIDs instead of Owner names, as it helps avoid race conditions created by deleting a
volumeClaimTemplatePVC, in situations where aPipelineRunresource is quickly deleted and then recreated. -
A new Dockerfile is added for
pullrequest-initforbuild-baseimage triggered by non-root users. -
When a pipeline or task is executed with the
-foption and theparamin its definition does not have atypedefined, a validation error is generated instead of the pipeline or task run failing silently. -
For the
tkn start [task | pipeline | clustertask]commands, the description of the--workspaceflag is now consistent. - While parsing the parameters, if an empty array is encountered, the corresponding interactive help is displayed as an empty string now.
4.1.6. Release notes for Red Hat OpenShift Pipelines General Availability 1.4
Red Hat OpenShift Pipelines General Availability (GA) 1.4 is now available on OpenShift Container Platform 4.7.
In addition to the stable and preview Operator channels, the Red Hat OpenShift Pipelines Operator 1.4.0 comes with the ocp-4.6, ocp-4.5, and ocp-4.4 deprecated channels. These deprecated channels and support for them will be removed in the following release of Red Hat OpenShift Pipelines.
4.1.6.1. Compatibility and support matrix
Some features in this release are currently in Technology Preview. These experimental features are not intended for production use.
In the table, features are marked with the following statuses:
| TP | Technology Preview |
| GA | General Availability |
Note the following scope of support on the Red Hat Customer Portal for these features:
| Feature | Version | Support Status |
|---|---|---|
| Pipelines | 0.22 | GA |
| CLI | 0.17 | GA |
| Catalog | 0.22 | GA |
| Triggers | 0.12 | TP |
| Pipeline resources | - | TP |
For questions and feedback, you can send an email to the product team at pipelines-interest@redhat.com.
4.1.6.2. New features
In addition to the fixes and stability improvements, the following sections highlight what is new in Red Hat OpenShift Pipelines 1.4.
The custom tasks have the following enhancements:
- Pipeline results can now refer to results produced by custom tasks.
- Custom tasks can now use workspaces, service accounts, and pod templates to build more complex custom tasks.
The
finallytask has the following enhancements:-
The
whenexpressions are supported infinallytasks, which provides efficient guarded execution and improved reusability of tasks. A
finallytask can be configured to consume the results of any task within the same pipeline.NoteSupport for
whenexpressions andfinallytasks are unavailable in the OpenShift Container Platform 4.7 web console.
-
The
-
Support for multiple secrets of the type
dockercfgordockerconfigjsonis added for authentication at runtime. -
Functionality to support sparse-checkout with the
git-clonetask is added. This enables you to clone only a subset of the repository as your local copy, and helps you to restrict the size of the cloned repositories. - You can create pipeline runs in a pending state without actually starting them. In clusters that are under heavy load, this allows Operators to have control over the start time of the pipeline runs.
-
Ensure that you set the
SYSTEM_NAMESPACEenvironment variable manually for the controller; this was previously set by default. -
A non-root user is now added to the build-base image of pipelines so that
git-initcan clone repositories as a non-root user. - Support to validate dependencies between resolved resources before a pipeline run starts is added. All result variables in the pipeline must be valid, and optional workspaces from a pipeline can only be passed to tasks expecting it for the pipeline to start running.
- The controller and webhook runs as a non-root group, and their superfluous capabilities have been removed to make them more secure.
-
You can use the
tkn pr logscommand to see the log streams for retried task runs. -
You can use the
--clustertaskoption in thetkn tr deletecommand to delete all the task runs associated with a particular cluster task. -
Support for using Knative service with the
EventListenerresource is added by introducing a newcustomResourcefield. - An error message is displayed when an event payload does not use the JSON format.
-
The source control interceptors such as GitLab, BitBucket, and GitHub, now use the new
InterceptorRequestorInterceptorResponsetype interface. -
A new CEL function
marshalJSONis implemented so that you can encode a JSON object or an array to a string. -
An HTTP handler for serving the CEL and the source control core interceptors is added. It packages four core interceptors into a single HTTP server that is deployed in the
tekton-pipelinesnamespace. TheEventListenerobject forwards events over the HTTP server to the interceptor. Each interceptor is available at a different path. For example, the CEL interceptor is available on the/celpath. The
pipelines-sccSecurity Context Constraint (SCC) is used with the defaultpipelineservice account for pipelines. This new service account is similar toanyuid, but with a minor difference as defined in the YAML for SCC of OpenShift Container Platform 4.7:fsGroup: type: MustRunAs
4.1.6.3. Deprecated features
-
The
build-gcssub-type in the pipeline resource storage, and thegcs-fetcherimage, are not supported. -
In the
taskRunfield of cluster tasks, the labeltekton.dev/taskis removed. -
For webhooks, the value
v1beta1corresponding to the fieldadmissionReviewVersionsis removed. -
The
creds-inithelper image for building and deploying is removed. In the triggers spec and binding, the deprecated field
template.nameis removed in favor oftemplate.ref. You should update alleventListenerdefinitions to use thereffield.NoteUpgrade from Pipelines 1.3.x and earlier versions to Pipelines 1.4.0 breaks event listeners because of the unavailability of the
template.namefield. For such cases, use Pipelines 1.4.1 to avail the restoredtemplate.namefield.-
For
EventListenercustom resources/objects, the fieldsPodTemplateandServiceTypeare deprecated in favor ofResource. - The deprecated spec style embedded bindings is removed.
-
The
specfield is removed from thetriggerSpecBinding. - The event ID representation is changed from a five-character random string to a UUID.
4.1.6.4. Known issues
- In the Developer perspective, the pipeline metrics and triggers features are available only on OpenShift Container Platform 4.7.6 or later versions.
-
On IBM Power Systems, IBM Z, and LinuxONE, the
tkn hubcommand is not supported. -
When you run Maven and Jib Maven cluster tasks on an IBM Power Systems (ppc64le), IBM Z, and LinuxONE (s390x) clusters, set the
MAVEN_IMAGEparameter value tomaven:3.6.3-adoptopenjdk-11. Triggers throw error resulting from bad handling of the JSON format, if you have the following configuration in the trigger binding:
params: - name: github_json value: $(body)To resolve the issue:
-
If you are using triggers v0.11.0 and above, use the
marshalJSONCEL function, which takes a JSON object or array and returns the JSON encoding of that object or array as a string. If you are using older triggers version, add the following annotation in the trigger template:
annotations: triggers.tekton.dev/old-escape-quotes: "true"
-
If you are using triggers v0.11.0 and above, use the
- When upgrading from Pipelines 1.3.x to 1.4.x, you must recreate the routes.
4.1.6.5. Fixed issues
-
Previously, the
tekton.dev/tasklabel was removed from the task runs of cluster tasks, and thetekton.dev/clusterTasklabel was introduced. The problems resulting from that change is resolved by fixing theclustertask describeanddeletecommands. In addition, thelastrunfunction for tasks is modified, to fix the issue of thetekton.dev/tasklabel being applied to the task runs of both tasks and cluster tasks in older versions of pipelines. -
When doing an interactive
tkn pipeline start pipelinename, aPipelineResourceis created interactively. Thetkn p startcommand prints the resource status if the resource status is notnil. -
Previously, the
tekton.dev/task=namelabel was removed from the task runs created from cluster tasks. This fix modifies thetkn clustertask startcommand with the--lastflag to check for thetekton.dev/task=namelabel in the created task runs. -
When a task uses an inline task specification, the corresponding task run now gets embedded in the pipeline when you run the
tkn pipeline describecommand, and the task name is returned as embedded. -
The
tkn versioncommand is fixed to display the version of the installed Tekton CLI tool, without a configuredkubeConfiguration namespaceor access to a cluster. -
If an argument is unexpected or more than one arguments are used, the
tkn completioncommand gives an error. -
Previously, pipeline runs with the
finallytasks nested in a pipeline specification would lose thosefinallytasks, when converted to thev1alpha1version and restored back to thev1beta1version. This error occurring during conversion is fixed to avoid potential data loss. Pipeline runs with thefinallytasks nested in a pipeline specification is now serialized and stored on the alpha version, only to be deserialized later. -
Previously, there was an error in the pod generation when a service account had the
secretsfield as{}. The task runs failed withCouldntGetTaskbecause the GET request with an empty secret name returned an error, indicating that the resource name may not be empty. This issue is fixed by avoiding an empty secret name in thekubeclientGET request. -
Pipelines with the
v1beta1API versions can now be requested along with thev1alpha1version, without losing thefinallytasks. Applying the returnedv1alpha1version will store the resource asv1beta1, with thefinallysection restored to its original state. -
Previously, an unset
selfLinkfield in the controller caused an error in the Kubernetes v1.20 clusters. As a temporary fix, theCloudEventsource field is set to a value that matches the current source URI, without the value of the auto-populatedselfLinkfield. -
Previously, a secret name with dots such as
gcr.ioled to a task run creation failure. This happened because of the secret name being used internally as part of a volume mount name. The volume mount name conforms to the RFC1123 DNS label and disallows dots as part of the name. This issue is fixed by replacing the dot with a dash that results in a readable name. -
Context variables are now validated in the
finallytasks. -
Previously, when the task run reconciler was passed a task run that did not have a previous status update containing the name of the pod it created, the task run reconciler listed the pods associated with the task run. The task run reconciler used the labels of the task run, which were propagated to the pod, to find the pod. Changing these labels while the task run was running, caused the code to not find the existing pod. As a result, duplicate pods were created. This issue is fixed by changing the task run reconciler to only use the
tekton.dev/taskRunTekton-controlled label when finding the pod. - Previously, when a pipeline accepted an optional workspace and passed it to a pipeline task, the pipeline run reconciler stopped with an error if the workspace was not provided, even if a missing workspace binding is a valid state for an optional workspace. This issue is fixed by ensuring that the pipeline run reconciler does not fail to create a task run, even if an optional workspace is not provided.
- The sorted order of step statuses matches the order of step containers.
-
Previously, the task run status was set to
unknownwhen a pod encountered theCreateContainerConfigErrorreason, which meant that the task and the pipeline ran until the pod timed out. This issue is fixed by setting the task run status tofalse, so that the task is set as failed when the pod encounters theCreateContainerConfigErrorreason. -
Previously, pipeline results were resolved on the first reconciliation, after a pipeline run was completed. This could fail the resolution resulting in the
Succeededcondition of the pipeline run being overwritten. As a result, the final status information was lost, potentially confusing any services watching the pipeline run conditions. This issue is fixed by moving the resolution of pipeline results to the end of a reconciliation, when the pipeline run is put into aSucceededorTruecondition. - Execution status variable is now validated. This avoids validating task results while validating context variables to access execution status.
- Previously, a pipeline result that contained an invalid variable would be added to the pipeline run with the literal expression of the variable intact. Therefore, it was difficult to assess whether the results were populated correctly. This issue is fixed by filtering out the pipeline run results that reference failed task runs. Now, a pipeline result that contains an invalid variable will not be emitted by the pipeline run at all.
-
The
tkn eventlistener describecommand is fixed to avoid crashing without a template. It also displays the details about trigger references. -
Upgrades from Pipelines 1.3.x and earlier versions to Pipelines 1.4.0 breaks event listeners because of the unavailability of
template.name. In Pipelines 1.4.1, thetemplate.namehas been restored to avoid breaking event listeners in triggers. -
In Pipelines 1.4.1, the
ConsoleQuickStartcustom resource has been updated to align with OpenShift Container Platform 4.7 capabilities and behavior.
4.1.7. Release notes for Red Hat OpenShift Pipelines Technology Preview 1.3
4.1.7.1. New features
Red Hat OpenShift Pipelines Technology Preview (TP) 1.3 is now available on OpenShift Container Platform 4.7. Red Hat OpenShift Pipelines TP 1.3 is updated to support:
- Tekton Pipelines 0.19.0
-
Tekton
tknCLI 0.15.0 - Tekton Triggers 0.10.2
- cluster tasks based on Tekton Catalog 0.19.0
- IBM Power Systems on OpenShift Container Platform 4.7
- IBM Z and LinuxONE on OpenShift Container Platform 4.7
In addition to the fixes and stability improvements, the following sections highlight what is new in Red Hat OpenShift Pipelines 1.3.
4.1.7.1.1. Pipelines
- Tasks that build images, such as S2I and Buildah tasks, now emit a URL of the image built that includes the image SHA.
-
Conditions in pipeline tasks that reference custom tasks are disallowed because the
Conditioncustom resource definition (CRD) has been deprecated. -
Variable expansion is now added in the
TaskCRD for the following fields:spec.steps[].imagePullPolicyandspec.sidecar[].imagePullPolicy. -
You can disable the built-in credential mechanism in Tekton by setting the
disable-creds-initfeature-flag totrue. -
Resolved when expressions are now listed in the
Skipped Tasksand theTask Runssections in theStatusfield of thePipelineRunconfiguration. -
The
git initcommand can now clone recursive submodules. -
A
TaskCR author can now specify a timeout for a step in theTaskspec. -
You can now base the entry point image on the
distroless/static:nonrootimage and give it a mode to copy itself to the destination, without relying on thecpcommand being present in the base image. -
You can now use the configuration flag
require-git-ssh-secret-known-hoststo disallow omitting known hosts in the Git SSH secret. When the flag value is set totrue, you must include theknown_hostfield in the Git SSH secret. The default value for the flag isfalse. - The concept of optional workspaces is now introduced. A task or pipeline might declare a workspace optional and conditionally change their behavior based on its presence. A task run or pipeline run might also omit that workspace, thereby modifying the task or pipeline behavior. The default task run workspaces are not added in place of an omitted optional workspace.
- Credentials initialization in Tekton now detects an SSH credential that is used with a non-SSH URL, and vice versa in Git pipeline resources, and logs a warning in the step containers.
- The task run controller emits a warning event if the affinity specified by the pod template is overwritten by the affinity assistant.
- The task run reconciler now records metrics for cloud events that are emitted once a task run is completed. This includes retries.
4.1.7.1.2. Pipelines CLI
-
Support for
--no-headers flagis now added to the following commands:tkn condition list,tkn triggerbinding list,tkn eventlistener list,tkn clustertask list,tkn clustertriggerbinding list. -
When used together, the
--lastor--useoptions override the--prefix-nameand--timeoutoptions. -
The
tkn eventlistener logscommand is now added to view theEventListenerlogs. -
The
tekton hubcommands are now integrated into thetknCLI. -
The
--nocolouroption is now changed to--no-color. -
The
--all-namespacesflag is added to the following commands:tkn triggertemplate list,tkn condition list,tkn triggerbinding list,tkn eventlistener list.
4.1.7.1.3. Triggers
-
You can now specify your resource information in the
EventListenertemplate. -
It is now mandatory for
EventListenerservice accounts to have thelistandwatchverbs, in addition to thegetverb for all the triggers resources. This enables you to useListersto fetch data fromEventListener,Trigger,TriggerBinding,TriggerTemplate, andClusterTriggerBindingresources. You can use this feature to create aSinkobject rather than specifying multiple informers, and directly make calls to the API server. -
A new
Interceptorinterface is added to support immutable input event bodies. Interceptors can now add data or fields to a newextensionsfield, and cannot modify the input bodies making them immutable. The CEL interceptor uses this newInterceptorinterface. -
A
namespaceSelectorfield is added to theEventListenerresource. Use it to specify the namespaces from where theEventListenerresource can fetch theTriggerobject for processing events. To use thenamespaceSelectorfield, the service account for theEventListenerresource must have a cluster role. -
The triggers
EventListenerresource now supports end-to-end secure connection to theeventlistenerpod. -
The escaping parameters behavior in the
TriggerTemplatesresource by replacing"with\"is now removed. -
A new
resourcesfield, supporting Kubernetes resources, is introduced as part of theEventListenerspec. - A new functionality for the CEL interceptor, with support for upper and lower-casing of ASCII strings, is added.
-
You can embed
TriggerBindingresources by using thenameandvaluefields in a trigger, or an event listener. -
The
PodSecurityPolicyconfiguration is updated to run in restricted environments. It ensures that containers must run as non-root. In addition, the role-based access control for using the pod security policy is moved from cluster-scoped to namespace-scoped. This ensures that the triggers cannot use other pod security policies that are unrelated to a namespace. -
Support for embedded trigger templates is now added. You can either use the
namefield to refer to an embedded template or embed the template inside thespecfield.
4.1.7.2. Deprecated features
-
Pipeline templates that use
PipelineResourcesCRDs are now deprecated and will be removed in a future release. -
The
template.namefield is deprecated in favor of thetemplate.reffield and will be removed in a future release. -
The
-cshorthand for the--checkcommand has been removed. In addition, globaltknflags are added to theversioncommand.
4.1.7.3. Known issues
-
CEL overlays add fields to a new top-level
extensionsfunction, instead of modifying the incoming event body.TriggerBindingresources can access values within this newextensionsfunction using the$(extensions.<key>)syntax. Update your binding to use the$(extensions.<key>)syntax instead of the$(body.<overlay-key>)syntax. -
The escaping parameters behavior by replacing
"with\"is now removed. If you need to retain the old escaping parameters behavior add thetekton.dev/old-escape-quotes: true"annotation to yourTriggerTemplatespecification. -
You can embed
TriggerBindingresources by using thenameandvaluefields inside a trigger or an event listener. However, you cannot specify bothnameandreffields for a single binding. Use thereffield to refer to aTriggerBindingresource and thenamefield for embedded bindings. -
An interceptor cannot attempt to reference a
secretoutside the namespace of anEventListenerresource. You must include secrets in the namespace of the `EventListener`resource. -
In Triggers 0.9.0 and later, if a body or header based
TriggerBindingparameter is missing or malformed in an event payload, the default values are used instead of displaying an error. -
Tasks and pipelines created with
WhenExpressionobjects using Tekton Pipelines 0.16.x must be reapplied to fix their JSON annotations. - When a pipeline accepts an optional workspace and gives it to a task, the pipeline run stalls if the workspace is not provided.
- To use the Buildah cluster task in a disconnected environment, ensure that the Dockerfile uses an internal image stream as the base image, and then use it in the same manner as any S2I cluster task.
4.1.7.4. Fixed issues
-
Extensions added by a CEL Interceptor are passed on to webhook interceptors by adding the
Extensionsfield within the event body. -
The activity timeout for log readers is now configurable using the
LogOptionsfield. However, the default behavior of timeout in 10 seconds is retained. -
The
logcommand ignores the--followflag when a task run or pipeline run is complete, and reads available logs instead of live logs. -
References to the following Tekton resources:
EventListener,TriggerBinding,ClusterTriggerBinding,Condition, andTriggerTemplateare now standardized and made consistent across all user-facing messages intkncommands. -
Previously, if you started a canceled task run or pipeline run with the
--use-taskrun <canceled-task-run-name>,--use-pipelinerun <canceled-pipeline-run-name>or--lastflags, the new run would be canceled. This bug is now fixed. -
The
tkn pr desccommand is now enhanced to ensure that it does not fail in case of pipeline runs with conditions. -
When you delete a task run using the
tkn tr deletecommand with the--taskoption, and a cluster task exists with the same name, the task runs for the cluster task also get deleted. As a workaround, filter the task runs by using theTaskRefKindfield. -
The
tkn triggertemplate describecommand would display only part of theapiVersionvalue in the output. For example, onlytriggers.tekton.devwas displayed instead oftriggers.tekton.dev/v1alpha1. This bug is now fixed. - The webhook, under certain conditions, would fail to acquire a lease and not function correctly. This bug is now fixed.
- Pipelines with when expressions created in v0.16.3 can now be run in v0.17.1 and later. After an upgrade, you do not need to reapply pipeline definitions created in previous versions because both the uppercase and lowercase first letters for the annotations are now supported.
-
By default, the
leader-election-hafield is now enabled for high availability. When thedisable-hacontroller flag is set totrue, it disables high availability support. - Issues with duplicate cloud events are now fixed. Cloud events are now sent only when a condition changes the state, reason, or message.
-
When a service account name is missing from a
PipelineRunorTaskRunspec, the controller uses the service account name from theconfig-defaultsconfig map. If the service account name is also missing in theconfig-defaultsconfig map, the controller now sets it todefaultin the spec. - Validation for compatibility with the affinity assistant is now supported when the same persistent volume claim is used for multiple workspaces, but with different subpaths.
4.1.8. Release notes for Red Hat OpenShift Pipelines Technology Preview 1.2
4.1.8.1. New features
Red Hat OpenShift Pipelines Technology Preview (TP) 1.2 is now available on OpenShift Container Platform 4.6. Red Hat OpenShift Pipelines TP 1.2 is updated to support:
- Tekton Pipelines 0.16.3
-
Tekton
tknCLI 0.13.1 - Tekton Triggers 0.8.1
- cluster tasks based on Tekton Catalog 0.16
- IBM Power Systems on OpenShift Container Platform 4.6
- IBM Z and LinuxONE on OpenShift Container Platform 4.6
In addition to the fixes and stability improvements, the following sections highlight what is new in Red Hat OpenShift Pipelines 1.2.
4.1.8.1.1. Pipelines
This release of Red Hat OpenShift Pipelines adds support for a disconnected installation.
NoteInstallations in restricted environments are currently not supported on IBM Power Systems, IBM Z, and LinuxONE.
-
You can now use the
whenfield, instead ofconditionsresource, to run a task only when certain criteria are met. The key components ofWhenExpressionresources areInput,Operator, andValues. If all the when expressions evaluate toTrue, then the task is run. If any of the when expressions evaluate toFalse, the task is skipped. - Step statuses are now updated if a task run is canceled or times out.
-
Support for Git Large File Storage (LFS) is now available to build the base image used by
git-init. -
You can now use the
taskSpecfield to specify metadata, such as labels and annotations, when a task is embedded in a pipeline. -
Cloud events are now supported by pipeline runs. Retries with
backoffare now enabled for cloud events sent by the cloud event pipeline resource. -
You can now set a default
Workspaceconfiguration for any workspace that aTaskresource declares, but that aTaskRunresource does not explicitly provide. -
Support is available for namespace variable interpolation for the
PipelineRunnamespace andTaskRunnamespace. -
Validation for
TaskRunobjects is now added to check that not more than one persistent volume claim workspace is used when aTaskRunresource is associated with an Affinity Assistant. If more than one persistent volume claim workspace is used, the task run fails with aTaskRunValidationFailedcondition. Note that by default, the Affinity Assistant is disabled in Red Hat OpenShift Pipelines, so you will need to enable the assistant to use it.
4.1.8.1.2. Pipelines CLI
The
tkn task describe,tkn taskrun describe,tkn clustertask describe,tkn pipeline describe, andtkn pipelinerun describecommands now:-
Automatically select the
Task,TaskRun,ClusterTask,PipelineandPipelineRunresource, respectively, if only one of them is present. -
Display the results of the
Task,TaskRun,ClusterTask,PipelineandPipelineRunresource in their outputs, respectively. -
Display workspaces declared in the
Task,TaskRun,ClusterTask,PipelineandPipelineRunresource in their outputs, respectively.
-
Automatically select the
-
You can now use the
--prefix-nameoption with thetkn clustertask startcommand to specify a prefix for the name of a task run. -
Interactive mode support has now been provided to the
tkn clustertask startcommand. -
You can now specify
PodTemplateproperties supported by pipelines using local or remote file definitions forTaskRunandPipelineRunobjects. -
You can now use the
--use-params-defaultsoption with thetkn clustertask startcommand to use the default values set in theClusterTaskconfiguration and create the task run. -
The
--use-param-defaultsflag for thetkn pipeline startcommand now prompts the interactive mode if the default values have not been specified for some of the parameters.
4.1.8.1.3. Triggers
-
The Common Expression Language (CEL) function named
parseYAMLhas been added to parse a YAML string into a map of strings. - Error messages for parsing CEL expressions have been improved to make them more granular while evaluating expressions and when parsing the hook body for creating the evaluation environment.
- Support is now available for marshaling boolean values and maps if they are used as the values of expressions in a CEL overlay mechanism.
The following fields have been added to the
EventListenerobject:-
The
replicasfield enables the event listener to run more than one pod by specifying the number of replicas in the YAML file. -
The
NodeSelectorfield enables theEventListenerobject to schedule the event listener pod to a specific node.
-
The
-
Webhook interceptors can now parse the
EventListener-Request-URLheader to extract parameters from the original request URL being handled by the event listener. - Annotations from the event listener can now be propagated to the deployment, services, and other pods. Note that custom annotations on services or deployment are overwritten, and hence, must be added to the event listener annotations so that they are propagated.
-
Proper validation for replicas in the
EventListenerspecification is now available for cases when a user specifies thespec.replicasvalues asnegativeorzero. -
You can now specify the
TriggerCRDobject inside theEventListenerspec as a reference using theTriggerReffield to create theTriggerCRDobject separately and then bind it inside theEventListenerspec. -
Validation and defaults for the
TriggerCRDobject are now available.
4.1.8.2. Deprecated features
-
$(params)parameters are now removed from thetriggertemplateresource and replaced by$(tt.params)to avoid confusion between theresourcetemplateandtriggertemplateresource parameters. -
The
ServiceAccountreference of the optionalEventListenerTrigger-based authentication level has changed from an object reference to aServiceAccountNamestring. This ensures that theServiceAccountreference is in the same namespace as theEventListenerTriggerobject. -
The
Conditionscustom resource definition (CRD) is now deprecated; use theWhenExpressionsCRD instead. -
The
PipelineRun.Spec.ServiceAccountNamesobject is being deprecated and replaced by thePipelineRun.Spec.TaskRunSpec[].ServiceAccountNameobject.
4.1.8.3. Known issues
- This release of Red Hat OpenShift Pipelines adds support for a disconnected installation. However, some images used by the cluster tasks must be mirrored for them to work in disconnected clusters.
-
Pipelines in the
openshiftnamespace are not deleted after you uninstall the Red Hat OpenShift Pipelines Operator. Use theoc delete pipelines -n openshift --allcommand to delete the pipelines. Uninstalling the Red Hat OpenShift Pipelines Operator does not remove the event listeners.
As a workaround, to remove the
EventListenerandPodCRDs:Edit the
EventListenerobject with theforegroundDeletionfinalizers:$ oc patch el/<eventlistener_name> -p '{"metadata":{"finalizers":["foregroundDeletion"]}}' --type=mergeFor example:
$ oc patch el/github-listener-interceptor -p '{"metadata":{"finalizers":["foregroundDeletion"]}}' --type=mergeDelete the
EventListenerCRD:$ oc patch crd/eventlisteners.triggers.tekton.dev -p '{"metadata":{"finalizers":[]}}' --type=merge
When you run a multi-arch container image task without command specification on an IBM Power Systems (ppc64le) or IBM Z (s390x) cluster, the
TaskRunresource fails with the following error:Error executing command: fork/exec /bin/bash: exec format errorAs a workaround, use an architecture specific container image or specify the sha256 digest to point to the correct architecture. To get the sha256 digest enter:
$ skopeo inspect --raw <image_name>| jq '.manifests[] | select(.platform.architecture == "<architecture>") | .digest'
4.1.8.4. Fixed issues
- A simple syntax validation to check the CEL filter, overlays in the Webhook validator, and the expressions in the interceptor has now been added.
- Triggers no longer overwrite annotations set on the underlying deployment and service objects.
-
Previously, an event listener would stop accepting events. This fix adds an idle timeout of 120 seconds for the
EventListenersink to resolve this issue. -
Previously, canceling a pipeline run with a
Failed(Canceled)state gave a success message. This has been fixed to display an error instead. -
The
tkn eventlistener listcommand now provides the status of the listed event listeners, thus enabling you to easily identify the available ones. -
Consistent error messages are now displayed for the
triggers listandtriggers describecommands when triggers are not installed or when a resource cannot be found. -
Previously, a large number of idle connections would build up during cloud event delivery. The
DisableKeepAlives: trueparameter was added to thecloudeventclientconfig to fix this issue. Thus, a new connection is set up for every cloud event. -
Previously, the
creds-initcode would write empty files to the disk even if credentials of a given type were not provided. This fix modifies thecreds-initcode to write files for only those credentials that have actually been mounted from correctly annotated secrets.
4.1.9. Release notes for Red Hat OpenShift Pipelines Technology Preview 1.1
4.1.9.1. New features
Red Hat OpenShift Pipelines Technology Preview (TP) 1.1 is now available on OpenShift Container Platform 4.5. Red Hat OpenShift Pipelines TP 1.1 is updated to support:
- Tekton Pipelines 0.14.3
-
Tekton
tknCLI 0.11.0 - Tekton Triggers 0.6.1
- cluster tasks based on Tekton Catalog 0.14
In addition to the fixes and stability improvements, the following sections highlight what is new in Red Hat OpenShift Pipelines 1.1.
4.1.9.1.1. Pipelines
- Workspaces can now be used instead of pipeline resources. It is recommended that you use workspaces in OpenShift Pipelines, as pipeline resources are difficult to debug, limited in scope, and make tasks less reusable. For more details on workspaces, see the Understanding OpenShift Pipelines section.
Workspace support for volume claim templates has been added:
- The volume claim template for a pipeline run and task run can now be added as a volume source for workspaces. The tekton-controller then creates a persistent volume claim (PVC) using the template that is seen as a PVC for all task runs in the pipeline. Thus you do not need to define the PVC configuration every time it binds a workspace that spans multiple tasks.
- Support to find the name of the PVC when a volume claim template is used as a volume source is now available using variable substitution.
Support for improving audits:
-
The
PipelineRun.Statusfield now contains the status of every task run in the pipeline and the pipeline specification used to instantiate a pipeline run to monitor the progress of the pipeline run. -
Pipeline results have been added to the pipeline specification and
PipelineRunstatus. -
The
TaskRun.Statusfield now contains the exact task specification used to instantiate theTaskRunresource.
-
The
- Support to apply the default parameter to conditions.
-
A task run created by referencing a cluster task now adds the
tekton.dev/clusterTasklabel instead of thetekton.dev/tasklabel. -
The kube config writer now adds the
ClientKeyDataand theClientCertificateDataconfigurations in the resource structure to enable replacement of the pipeline resource type cluster with the kubeconfig-creator task. -
The names of the
feature-flagsand theconfig-defaultsconfig maps are now customizable. - Support for the host network in the pod template used by the task run is now available.
- An Affinity Assistant is now available to support node affinity in task runs that share workspace volume. By default, this is disabled on OpenShift Pipelines.
-
The pod template has been updated to specify
imagePullSecretsto identify secrets that the container runtime should use to authorize container image pulls when starting a pod. - Support for emitting warning events from the task run controller if the controller fails to update the task run.
- Standard or recommended k8s labels have been added to all resources to identify resources belonging to an application or component.
-
The
Entrypointprocess is now notified for signals and these signals are then propagated using a dedicated PID Group of theEntrypointprocess. - The pod template can now be set on a task level at runtime using task run specs.
Support for emitting Kubernetes events:
-
The controller now emits events for additional task run lifecycle events -
taskrun startedandtaskrun running. - The pipeline run controller now emits an event every time a pipeline starts.
-
The controller now emits events for additional task run lifecycle events -
- In addition to the default Kubernetes events, support for cloud events for task runs is now available. The controller can be configured to send any task run events, such as create, started, and failed, as cloud events.
-
Support for using the
$context.<task|taskRun|pipeline|pipelineRun>.namevariable to reference the appropriate name when in pipeline runs and task runs. - Validation for pipeline run parameters is now available to ensure that all the parameters required by the pipeline are provided by the pipeline run. This also allows pipeline runs to provide extra parameters in addition to the required parameters.
-
You can now specify tasks within a pipeline that will always execute before the pipeline exits, either after finishing all tasks successfully or after a task in the pipeline failed, using the
finallyfield in the pipeline YAML file. -
The
git-clonecluster task is now available.
4.1.9.1.2. Pipelines CLI
-
Support for embedded trigger binding is now available to the
tkn evenlistener describecommand. - Support to recommend subcommands and make suggestions if an incorrect subcommand is used.
-
The
tkn task describecommand now auto selects the task if only one task is present in the pipeline. -
You can now start a task using default parameter values by specifying the
--use-param-defaultsflag in thetkn task startcommand. -
You can now specify a volume claim template for pipeline runs or task runs using the
--workspaceoption with thetkn pipeline startortkn task startcommands. -
The
tkn pipelinerun logscommand now displays logs for the final tasks listed in thefinallysection. -
Interactive mode support has now been provided to the
tkn task startcommand and thedescribesubcommand for the followingtknresources:pipeline,pipelinerun,task,taskrun,clustertask, andpipelineresource. -
The
tkn versioncommand now displays the version of the triggers installed in the cluster. -
The
tkn pipeline describecommand now displays parameter values and timeouts specified for tasks used in the pipeline. -
Support added for the
--lastoption for thetkn pipelinerun describeand thetkn taskrun describecommands to describe the most recent pipeline run or task run, respectively. -
The
tkn pipeline describecommand now displays the conditions applicable to the tasks in the pipeline. -
You can now use the
--no-headersand--all-namespacesflags with thetkn resource listcommand.
4.1.9.1.3. Triggers
The following Common Expression Language (CEL) functions are now available:
-
parseURLto parse and extract portions of a URL -
parseJSONto parse JSON value types embedded in a string in thepayloadfield of thedeploymentwebhook
-
- A new interceptor for webhooks from Bitbucket has been added.
-
Event listeners now display the
Address URLand theAvailable statusas additional fields when listed with thekubectl getcommand. -
trigger template params now use the
$(tt.params.<paramName>)syntax instead of$(params.<paramName>)to reduce the confusion between trigger template and resource templates params. -
You can now add
tolerationsin theEventListenerCRD to ensure that event listeners are deployed with the same configuration even if all nodes are tainted due to security or management issues. -
You can now add a Readiness Probe for event listener Deployment at
URL/live. -
Support for embedding
TriggerBindingspecifications in event listener triggers is now added. -
Trigger resources are now annotated with the recommended
app.kubernetes.iolabels.
4.1.9.2. Deprecated features
The following items are deprecated in this release:
-
The
--namespaceor-nflags for all cluster-wide commands, including theclustertaskandclustertriggerbindingcommands, are deprecated. It will be removed in a future release. -
The
namefield intriggers.bindingswithin an event listener has been deprecated in favor of thereffield and will be removed in a future release. -
Variable interpolation in trigger templates using
$(params)has been deprecated in favor of using$(tt.params)to reduce confusion with the pipeline variable interpolation syntax. The$(params.<paramName>)syntax will be removed in a future release. -
The
tekton.dev/tasklabel is deprecated on cluster tasks. -
The
TaskRun.Status.ResourceResults.ResourceReffield is deprecated and will be removed. -
The
tkn pipeline create,tkn task create, andtkn resource create -fsubcommands have been removed. -
Namespace validation has been removed from
tkncommands. -
The default timeout of
1hand the-tflag for thetkn ct startcommand have been removed. -
The
s2icluster task has been deprecated.
4.1.9.3. Known issues
- Conditions do not support workspaces.
-
The
--workspaceoption and the interactive mode is not supported for thetkn clustertask startcommand. -
Support of backward compatibility for
$(params.<paramName>)syntax forces you to use trigger templates with pipeline specific params as the trigger s webhook is unable to differentiate trigger params from pipelines params. -
Pipeline metrics report incorrect values when you run a promQL query for
tekton_taskrun_countandtekton_taskrun_duration_seconds_count. -
pipeline runs and task runs continue to be in the
RunningandRunning(Pending)states respectively even when a non existing PVC name is given to a workspace.
4.1.9.4. Fixed issues
-
Previously, the
tkn task delete <name> --trscommand would delete both the task and cluster task if the name of the task and cluster task were the same. With this fix, the command deletes only the task runs that are created by the task<name>. -
Previously the
tkn pr delete -p <name> --keep 2command would disregard the-pflag when used with the--keepflag and would delete all the pipeline runs except the latest two. With this fix, the command deletes only the pipeline runs that are created by the pipeline<name>, except for the latest two. -
The
tkn triggertemplate describeoutput now displays resource templates in a table format instead of YAML format. -
Previously the
buildahcluster task failed when a new user was added to a container. With this fix, the issue has been resolved.
4.1.10. Release notes for Red Hat OpenShift Pipelines Technology Preview 1.0
4.1.10.1. New features
Red Hat OpenShift Pipelines Technology Preview (TP) 1.0 is now available on OpenShift Container Platform 4.4. Red Hat OpenShift Pipelines TP 1.0 is updated to support:
- Tekton Pipelines 0.11.3
-
Tekton
tknCLI 0.9.0 - Tekton Triggers 0.4.0
- cluster tasks based on Tekton Catalog 0.11
In addition to the fixes and stability improvements, the following sections highlight what is new in Red Hat OpenShift Pipelines 1.0.
4.1.10.1.1. Pipelines
- Support for v1beta1 API Version.
- Support for an improved limit range. Previously, limit range was specified exclusively for the task run and the pipeline run. Now there is no need to explicitly specify the limit range. The minimum limit range across the namespace is used.
- Support for sharing data between tasks using task results and task params.
-
Pipelines can now be configured to not overwrite the
HOMEenvironment variable and the working directory of steps. -
Similar to task steps,
sidecarsnow support script mode. -
You can now specify a different scheduler name in task run
podTemplateresource. - Support for variable substitution using Star Array Notation.
- Tekton controller can now be configured to monitor an individual namespace.
- A new description field is now added to the specification of pipelines, tasks, cluster tasks, resources, and conditions.
- Addition of proxy parameters to Git pipeline resources.
4.1.10.1.2. Pipelines CLI
-
The
describesubcommand is now added for the followingtknresources:EventListener,Condition,TriggerTemplate,ClusterTask, andTriggerSBinding. -
Support added for
v1beta1to the following resources along with backward compatibility forv1alpha1:ClusterTask,Task,Pipeline,PipelineRun, andTaskRun. The following commands can now list output from all namespaces using the
--all-namespacesflag option:tkn task list,tkn pipeline list,tkn taskrun list,tkn pipelinerun listThe output of these commands is also enhanced to display information without headers using the
--no-headersflag option.-
You can now start a pipeline using default parameter values by specifying
--use-param-defaultsflag in thetkn pipelines startcommand. -
Support for workspace is now added to
tkn pipeline startandtkn task startcommands. -
A new
clustertriggerbindingcommand is now added with the following subcommands:describe,delete, andlist. -
You can now directly start a pipeline run using a local or remote
yamlfile. -
The
describesubcommand now displays an enhanced and detailed output. With the addition of new fields, such asdescription,timeout,param description, andsidecar status, the command output now provides more detailed information about a specifictknresource. -
The
tkn task logcommand now displays logs directly if only one task is present in the namespace.
4.1.10.1.3. Triggers
-
Triggers can now create both
v1alpha1andv1beta1pipeline resources. -
Support for new Common Expression Language (CEL) interceptor function -
compareSecret. This function securely compares strings to secrets in CEL expressions. - Support for authentication and authorization at the event listener trigger level.
4.1.10.2. Deprecated features
The following items are deprecated in this release:
The environment variable
$HOME, and variableworkingDirin theStepsspecification are deprecated and might be changed in a future release. Currently in aStepcontainer, theHOMEandworkingDirvariables are overwritten to/tekton/homeand/workspacevariables, respectively.In a later release, these two fields will not be modified, and will be set to values defined in the container image and the
TaskYAML. For this release, use thedisable-home-env-overwriteanddisable-working-directory-overwriteflags to disable overwriting of theHOMEandworkingDirvariables.-
The following commands are deprecated and might be removed in the future release:
tkn pipeline create,tkn task create. -
The
-fflag with thetkn resource createcommand is now deprecated. It might be removed in the future release. -
The
-tflag and the--timeoutflag (with seconds format) for thetkn clustertask createcommand are now deprecated. Only duration timeout format is now supported, for example1h30s. These deprecated flags might be removed in the future release.
4.1.10.3. Known issues
- If you are upgrading from an older version of Red Hat OpenShift Pipelines, you must delete your existing deployments before upgrading to Red Hat OpenShift Pipelines version 1.0. To delete an existing deployment, you must first delete Custom Resources and then uninstall the Red Hat OpenShift Pipelines Operator. For more details, see the uninstalling Red Hat OpenShift Pipelines section.
-
Submitting the same
v1alpha1tasks more than once results in an error. Use theoc replacecommand instead ofoc applywhen re-submitting av1alpha1task. The
buildahcluster task does not work when a new user is added to a container.When the Operator is installed, the
--storage-driverflag for thebuildahcluster task is not specified, therefore the flag is set to its default value. In some cases, this causes the storage driver to be set incorrectly. When a new user is added, the incorrect storage-driver results in the failure of thebuildahcluster task with the following error:useradd: /etc/passwd.8: lock file already used useradd: cannot lock /etc/passwd; try again later.As a workaround, manually set the
--storage-driverflag value tooverlayin thebuildah-task.yamlfile:Login to your cluster as a
cluster-admin:$ oc login -u <login> -p <password> https://openshift.example.com:6443Use the
oc editcommand to editbuildahcluster task:$ oc edit clustertask buildahThe current version of the
buildahclustertask YAML file opens in the editor set by yourEDITORenvironment variable.Under the
Stepsfield, locate the followingcommandfield:command: ['buildah', 'bud', '--format=$(params.FORMAT)', '--tls-verify=$(params.TLSVERIFY)', '--layers', '-f', '$(params.DOCKERFILE)', '-t', '$(resources.outputs.image.url)', '$(params.CONTEXT)']Replace the
commandfield with the following:command: ['buildah', '--storage-driver=overlay', 'bud', '--format=$(params.FORMAT)', '--tls-verify=$(params.TLSVERIFY)', '--no-cache', '-f', '$(params.DOCKERFILE)', '-t', '$(params.IMAGE)', '$(params.CONTEXT)']- Save the file and exit.
Alternatively, you can also modify the
buildahcluster task YAML file directly on the web console by navigating to PipelinesCluster Tasks buildah. Select Edit Cluster Task from the Actions menu and replace the commandfield as shown in the previous procedure.
4.1.10.4. Fixed issues
-
Previously, the
DeploymentConfigtask triggered a new deployment build even when an image build was already in progress. This caused the deployment of the pipeline to fail. With this fix, thedeploy taskcommand is now replaced with theoc rollout statuscommand which waits for the in-progress deployment to finish. -
Support for
APP_NAMEparameter is now added in pipeline templates. -
Previously, the pipeline template for Java S2I failed to look up the image in the registry. With this fix, the image is looked up using the existing image pipeline resources instead of the user provided
IMAGE_NAMEparameter. - All the OpenShift Pipelines images are now based on the Red Hat Universal Base Images (UBI).
-
Previously, when the pipeline was installed in a namespace other than
tekton-pipelines, thetkn versioncommand displayed the pipeline version asunknown. With this fix, thetkn versioncommand now displays the correct pipeline version in any namespace. -
The
-cflag is no longer supported for thetkn versioncommand. - Non-admin users can now list the cluster trigger bindings.
-
The event listener
CompareSecretfunction is now fixed for the CEL Interceptor. -
The
list,describe, andstartsubcommands for tasks and cluster tasks now correctly display the output in case a task and cluster task have the same name. - Previously, the OpenShift Pipelines Operator modified the privileged security context constraints (SCCs), which caused an error during cluster upgrade. This error is now fixed.
-
In the
tekton-pipelinesnamespace, the timeouts of all task runs and pipeline runs are now set to the value ofdefault-timeout-minutesfield using the config map. - Previously, the pipelines section in the web console was not displayed for non-admin users. This issue is now resolved.
4.2. Understanding OpenShift Pipelines
Red Hat OpenShift Pipelines is a cloud-native, continuous integration and continuous delivery (CI/CD) solution based on Kubernetes resources. It uses Tekton building blocks to automate deployments across multiple platforms by abstracting away the underlying implementation details. Tekton introduces a number of standard custom resource definitions (CRDs) for defining CI/CD pipelines that are portable across Kubernetes distributions.
4.2.1. Key features
- Red Hat OpenShift Pipelines is a serverless CI/CD system that runs pipelines with all the required dependencies in isolated containers.
- Red Hat OpenShift Pipelines are designed for decentralized teams that work on microservice-based architecture.
- Red Hat OpenShift Pipelines use standard CI/CD pipeline definitions that are easy to extend and integrate with the existing Kubernetes tools, enabling you to scale on-demand.
- You can use Red Hat OpenShift Pipelines to build images with Kubernetes tools such as Source-to-Image (S2I), Buildah, Buildpacks, and Kaniko that are portable across any Kubernetes platform.
- You can use the OpenShift Container Platform Developer console to create Tekton resources, view logs of pipeline runs, and manage pipelines in your OpenShift Container Platform namespaces.
4.2.2. OpenShift Pipeline Concepts
This guide provides a detailed view of the various pipeline concepts.
4.2.2.1. Tasks
Tasks are the building blocks of a pipeline and consists of sequentially executed steps. It is essentially a function of inputs and outputs. A task can run individually or as a part of the pipeline. Tasks are reusable and can be used in multiple Pipelines.
Steps are a series of commands that are sequentially executed by the task and achieve a specific goal, such as building an image. Every task runs as a pod, and each step runs as a container within that pod. Because steps run within the same pod, they can access the same volumes for caching files, config maps, and secrets.
The following example shows the apply-manifests task.
apiVersion: tekton.dev/v1beta1
kind: Task
metadata:
name: apply-manifests
spec:
workspaces:
- name: source
params:
- name: manifest_dir
description: The directory in source that contains yaml manifests
type: string
default: "k8s"
steps:
- name: apply
image: image-registry.openshift-image-registry.svc:5000/openshift/cli:latest
workingDir: /workspace/source
command: ["/bin/bash", "-c"]
args:
- |-
echo Applying manifests in $(params.manifest_dir) directory
oc apply -f $(params.manifest_dir)
echo -----------------------------------This task starts the pod and runs a container inside that pod using the specified image to run the specified commands.
Starting with Pipelines 1.6, the following defaults from the step YAML file are removed:
-
The
HOMEenvironment variable does not default to the/tekton/homedirectory -
The
workingDirfield does not default to the/workspacedirectory
Instead, the container for the step defines the HOME environment variable and the workingDir field. However, you can override the default values by specifying the custom values in the YAML file for the step.
As a temporary measure, to maintain backward compatibility with the older Pipelines versions, you can set the following fields in the TektonConfig custom resource definition to false:
spec:
pipeline:
disable-working-directory-overwrite: false
disable-home-env-overwrite: false4.2.2.2. When expression
When expressions guard task execution by setting criteria for the execution of tasks within a pipeline. They contain a list of components that allows a task to run only when certain criteria are met. When expressions are also supported in the final set of tasks that are specified using the finally field in the pipeline YAML file.
The key components of a when expression are as follows:
-
input: Specifies static inputs or variables such as a parameter, task result, and execution status. You must enter a valid input. If you do not enter a valid input, its value defaults to an empty string. -
operator: Specifies the relationship of an input to a set ofvalues. Enterinornotinas your operator values. -
values: Specifies an array of string values. Enter a non-empty array of static values or variables such as parameters, results, and a bound state of a workspace.
The declared when expressions are evaluated before the task is run. If the value of a when expression is True, the task is run. If the value of a when expression is False, the task is skipped.
You can use the when expressions in various use cases. For example, whether:
- The result of a previous task is as expected.
- A file in a Git repository has changed in the previous commits.
- An image exists in the registry.
- An optional workspace is available.
The following example shows the when expressions for a pipeline run. The pipeline run will execute the create-file task only if the following criteria are met: the path parameter is README.md, and the echo-file-exists task executed only if the exists result from the check-file task is yes.
apiVersion: tekton.dev/v1beta1
kind: PipelineRun
metadata:
generateName: guarded-pr-
spec:
serviceAccountName: 'pipeline'
pipelineSpec:
params:
- name: path
type: string
description: The path of the file to be created
workspaces:
- name: source
description: |
This workspace is shared among all the pipeline tasks to read/write common resources
tasks:
- name: create-file
when:
- input: "$(params.path)"
operator: in
values: ["README.md"]
workspaces:
- name: source
workspace: source
taskSpec:
workspaces:
- name: source
description: The workspace to create the readme file in
steps:
- name: write-new-stuff
image: ubuntu
script: 'touch $(workspaces.source.path)/README.md'
- name: check-file
params:
- name: path
value: "$(params.path)"
workspaces:
- name: source
workspace: source
runAfter:
- create-file
taskSpec:
params:
- name: path
workspaces:
- name: source
description: The workspace to check for the file
results:
- name: exists
description: indicates whether the file exists or is missing
steps:
- name: check-file
image: alpine
script: |
if test -f $(workspaces.source.path)/$(params.path); then
printf yes | tee /tekton/results/exists
else
printf no | tee /tekton/results/exists
fi
- name: echo-file-exists
when:
- input: "$(tasks.check-file.results.exists)"
operator: in
values: ["yes"]
taskSpec:
steps:
- name: echo
image: ubuntu
script: 'echo file exists'
...
- name: task-should-be-skipped-1
when:
- input: "$(params.path)"
operator: notin
values: ["README.md"]
taskSpec:
steps:
- name: echo
image: ubuntu
script: exit 1
...
finally:
- name: finally-task-should-be-executed
when:
- input: "$(tasks.echo-file-exists.status)"
operator: in
values: ["Succeeded"]
- input: "$(tasks.status)"
operator: in
values: ["Succeeded"]
- input: "$(tasks.check-file.results.exists)"
operator: in
values: ["yes"]
- input: "$(params.path)"
operator: in
values: ["README.md"]
taskSpec:
steps:
- name: echo
image: ubuntu
script: 'echo finally done'
params:
- name: path
value: README.md
workspaces:
- name: source
volumeClaimTemplate:
spec:
accessModes:
- ReadWriteOnce
resources:
requests:
storage: 16Mi- 1
- Specifies the type of Kubernetes object. In this example,
PipelineRun. - 2
- Task
create-fileused in the Pipeline. - 3
whenexpression that specifies to execute theecho-file-existstask only if theexistsresult from thecheck-filetask isyes.- 4
whenexpression that specifies to skip thetask-should-be-skipped-1task only if thepathparameter isREADME.md.- 5
whenexpression that specifies to execute thefinally-task-should-be-executedtask only if the execution status of theecho-file-existstask and the task status isSucceeded, theexistsresult from thecheck-filetask isyes, and thepathparameter isREADME.md.
The Pipeline Run details page of the OpenShift Container Platform web console shows the status of the tasks and when expressions as follows:
- All the criteria are met: Tasks and the when expression symbol, which is represented by a diamond shape are green.
- Any one of the criteria are not met: Task is skipped. Skipped tasks and the when expression symbol are grey.
- None of the criteria are met: Task is skipped. Skipped tasks and the when expression symbol are grey.
- Task run fails: Failed tasks and the when expression symbol are red.
4.2.2.3. Finally tasks
The finally tasks are the final set of tasks specified using the finally field in the pipeline YAML file. A finally task always executes the tasks within the pipeline, irrespective of whether the pipeline runs are executed successfully. The finally tasks are executed in parallel after all the pipeline tasks are run, before the corresponding pipeline exits.
You can configure a finally task to consume the results of any task within the same pipeline. This approach does not change the order in which this final task is run. It is executed in parallel with other final tasks after all the non-final tasks are executed.
The following example shows a code snippet of the clone-cleanup-workspace pipeline. This code clones the repository into a shared workspace and cleans up the workspace. After executing the pipeline tasks, the cleanup task specified in the finally section of the pipeline YAML file cleans up the workspace.
apiVersion: tekton.dev/v1beta1
kind: Pipeline
metadata:
name: clone-cleanup-workspace
spec:
workspaces:
- name: git-source
tasks:
- name: clone-app-repo
taskRef:
name: git-clone-from-catalog
params:
- name: url
value: https://github.com/tektoncd/community.git
- name: subdirectory
value: application
workspaces:
- name: output
workspace: git-source
finally:
- name: cleanup
taskRef:
name: cleanup-workspace
workspaces:
- name: source
workspace: git-source
- name: check-git-commit
params:
- name: commit
value: $(tasks.clone-app-repo.results.commit)
taskSpec:
params:
- name: commit
steps:
- name: check-commit-initialized
image: alpine
script: |
if [[ ! $(params.commit) ]]; then
exit 1
fi- 1
- Unique name of the Pipeline.
- 2
- The shared workspace where the git repository is cloned.
- 3
- The task to clone the application repository to the shared workspace.
- 4
- The task to clean-up the shared workspace.
- 5
- A reference to the task that is to be executed in the TaskRun.
- 6
- A shared storage volume that a Task in a Pipeline needs at runtime to receive input or provide output.
- 7
- A list of parameters required for a task. If a parameter does not have an implicit default value, you must explicitly set its value.
- 8
- Embedded task definition.
4.2.2.4. TaskRun
A TaskRun instantiates a Task for execution with specific inputs, outputs, and execution parameters on a cluster. It can be invoked on its own or as part of a PipelineRun for each Task in a pipeline.
A Task consists of one or more Steps that execute container images, and each container image performs a specific piece of build work. A TaskRun executes the Steps in a Task in the specified order, until all Steps execute successfully or a failure occurs. A TaskRun is automatically created by a PipelineRun for each Task in a Pipeline.
The following example shows a TaskRun that runs the apply-manifests Task with the relevant input parameters:
apiVersion: tekton.dev/v1beta1
kind: TaskRun
metadata:
name: apply-manifests-taskrun
spec:
serviceAccountName: pipeline
taskRef:
kind: Task
name: apply-manifests
workspaces:
- name: source
persistentVolumeClaim:
claimName: source-pvc- 1
- TaskRun API version
v1beta1. - 2
- Specifies the type of Kubernetes object. In this example,
TaskRun. - 3
- Unique name to identify this TaskRun.
- 4
- Definition of the TaskRun. For this TaskRun, the Task and the required workspace are specified.
- 5
- Name of the Task reference used for this TaskRun. This TaskRun executes the
apply-manifestsTask. - 6
- Workspace used by the TaskRun.
4.2.2.5. Pipelines
A Pipeline is a collection of Task resources arranged in a specific order of execution. They are executed to construct complex workflows that automate the build, deployment and delivery of applications. You can define a CI/CD workflow for your application using pipelines containing one or more tasks.
A Pipeline resource definition consists of a number of fields or attributes, which together enable the pipeline to accomplish a specific goal. Each Pipeline resource definition must contain at least one Task resource, which ingests specific inputs and produces specific outputs. The pipeline definition can also optionally include Conditions, Workspaces, Parameters, or Resources depending on the application requirements.
The following example shows the build-and-deploy pipeline, which builds an application image from a Git repository using the buildah ClusterTask resource:
apiVersion: tekton.dev/v1beta1
kind: Pipeline
metadata:
name: build-and-deploy
spec:
workspaces:
- name: shared-workspace
params:
- name: deployment-name
type: string
description: name of the deployment to be patched
- name: git-url
type: string
description: url of the git repo for the code of deployment
- name: git-revision
type: string
description: revision to be used from repo of the code for deployment
default: "pipelines-1.7"
- name: IMAGE
type: string
description: image to be built from the code
tasks:
- name: fetch-repository
taskRef:
name: git-clone
kind: ClusterTask
workspaces:
- name: output
workspace: shared-workspace
params:
- name: url
value: $(params.git-url)
- name: subdirectory
value: ""
- name: deleteExisting
value: "true"
- name: revision
value: $(params.git-revision)
- name: build-image
taskRef:
name: buildah
kind: ClusterTask
params:
- name: TLSVERIFY
value: "false"
- name: IMAGE
value: $(params.IMAGE)
workspaces:
- name: source
workspace: shared-workspace
runAfter:
- fetch-repository
- name: apply-manifests
taskRef:
name: apply-manifests
workspaces:
- name: source
workspace: shared-workspace
runAfter:
- build-image
- name: update-deployment
taskRef:
name: update-deployment
workspaces:
- name: source
workspace: shared-workspace
params:
- name: deployment
value: $(params.deployment-name)
- name: IMAGE
value: $(params.IMAGE)
runAfter:
- apply-manifests- 1
- Pipeline API version
v1beta1. - 2
- Specifies the type of Kubernetes object. In this example,
Pipeline. - 3
- Unique name of this Pipeline.
- 4
- Specifies the definition and structure of the Pipeline.
- 5
- Workspaces used across all the Tasks in the Pipeline.
- 6
- Parameters used across all the Tasks in the Pipeline.
- 7
- Specifies the list of Tasks used in the Pipeline.
- 8
- Task
build-image, which uses thebuildahClusterTask to build application images from a given Git repository. - 9
- Task
apply-manifests, which uses a user-defined Task with the same name. - 10
- Specifies the sequence in which Tasks are run in a Pipeline. In this example, the
apply-manifestsTask is run only after thebuild-imageTask is completed.
The Red Hat OpenShift Pipelines Operator installs the Buildah cluster task and creates the pipeline service account with sufficient permission to build and push an image. The Buildah cluster task can fail when associated with a different service account with insufficient permissions.
4.2.2.6. PipelineRun
A PipelineRun is a type of resource that binds a pipeline, workspaces, credentials, and a set of parameter values specific to a scenario to run the CI/CD workflow.
A pipeline run is the running instance of a pipeline. It instantiates a pipeline for execution with specific inputs, outputs, and execution parameters on a cluster. It also creates a task run for each task in the pipeline run.
The pipeline runs the tasks sequentially until they are complete or a task fails. The status field tracks and the progress of each task run and stores it for monitoring and auditing purposes.
The following example runs the build-and-deploy pipeline with relevant resources and parameters:
apiVersion: tekton.dev/v1beta1
kind: PipelineRun
metadata:
name: build-deploy-api-pipelinerun
spec:
pipelineRef:
name: build-and-deploy
params:
- name: deployment-name
value: vote-api
- name: git-url
value: https://github.com/openshift-pipelines/vote-api.git
- name: IMAGE
value: image-registry.openshift-image-registry.svc:5000/pipelines-tutorial/vote-api
workspaces:
- name: shared-workspace
volumeClaimTemplate:
spec:
accessModes:
- ReadWriteOnce
resources:
requests:
storage: 500Mi- 1
- Pipeline run API version
v1beta1. - 2
- The type of Kubernetes object. In this example,
PipelineRun. - 3
- Unique name to identify this pipeline run.
- 4
- Name of the pipeline to be run. In this example,
build-and-deploy. - 5
- The list of parameters required to run the pipeline.
- 6
- Workspace used by the pipeline run.
4.2.2.7. Workspaces
It is recommended that you use Workspaces instead of PipelineResources in OpenShift Pipelines, as PipelineResources are difficult to debug, limited in scope, and make Tasks less reusable.
Workspaces declare shared storage volumes that a Task in a Pipeline needs at runtime to receive input or provide output. Instead of specifying the actual location of the volumes, Workspaces enable you to declare the filesystem or parts of the filesystem that would be required at runtime. A Task or Pipeline declares the Workspace and you must provide the specific location details of the volume. It is then mounted into that Workspace in a TaskRun or a PipelineRun. This separation of volume declaration from runtime storage volumes makes the Tasks reusable, flexible, and independent of the user environment.
With Workspaces, you can:
- Store Task inputs and outputs
- Share data among Tasks
- Use it as a mount point for credentials held in Secrets
- Use it as a mount point for configurations held in ConfigMaps
- Use it as a mount point for common tools shared by an organization
- Create a cache of build artifacts that speed up jobs
You can specify Workspaces in the TaskRun or PipelineRun using:
- A read-only ConfigMaps or Secret
- An existing PersistentVolumeClaim shared with other Tasks
- A PersistentVolumeClaim from a provided VolumeClaimTemplate
- An emptyDir that is discarded when the TaskRun completes
The following example shows a code snippet of the build-and-deploy Pipeline, which declares a shared-workspace Workspace for the build-image and apply-manifests Tasks as defined in the Pipeline.
apiVersion: tekton.dev/v1beta1
kind: Pipeline
metadata:
name: build-and-deploy
spec:
workspaces:
- name: shared-workspace
params:
...
tasks:
- name: build-image
taskRef:
name: buildah
kind: ClusterTask
params:
- name: TLSVERIFY
value: "false"
- name: IMAGE
value: $(params.IMAGE)
workspaces:
- name: source
workspace: shared-workspace
runAfter:
- fetch-repository
- name: apply-manifests
taskRef:
name: apply-manifests
workspaces:
- name: source
workspace: shared-workspace
runAfter:
- build-image
...- 1
- List of Workspaces shared between the Tasks defined in the Pipeline. A Pipeline can define as many Workspaces as required. In this example, only one Workspace named
shared-workspaceis declared. - 2
- Definition of Tasks used in the Pipeline. This snippet defines two Tasks,
build-imageandapply-manifests, which share a common Workspace. - 3
- List of Workspaces used in the
build-imageTask. A Task definition can include as many Workspaces as it requires. However, it is recommended that a Task uses at most one writable Workspace. - 4
- Name that uniquely identifies the Workspace used in the Task. This Task uses one Workspace named
source. - 5
- Name of the Pipeline Workspace used by the Task. Note that the Workspace
sourcein turn uses the Pipeline Workspace namedshared-workspace. - 6
- List of Workspaces used in the
apply-manifestsTask. Note that this Task shares thesourceWorkspace with thebuild-imageTask.
Workspaces help tasks share data, and allow you to specify one or more volumes that each task in the pipeline requires during execution. You can create a persistent volume claim or provide a volume claim template that creates a persistent volume claim for you.
The following code snippet of the build-deploy-api-pipelinerun PipelineRun uses a volume claim template to create a persistent volume claim for defining the storage volume for the shared-workspace Workspace used in the build-and-deploy Pipeline.
apiVersion: tekton.dev/v1beta1
kind: PipelineRun
metadata:
name: build-deploy-api-pipelinerun
spec:
pipelineRef:
name: build-and-deploy
params:
...
workspaces:
- name: shared-workspace
volumeClaimTemplate:
spec:
accessModes:
- ReadWriteOnce
resources:
requests:
storage: 500Mi- 1
- Specifies the list of Pipeline Workspaces for which volume binding will be provided in the PipelineRun.
- 2
- The name of the Workspace in the Pipeline for which the volume is being provided.
- 3
- Specifies a volume claim template that creates a persistent volume claim to define the storage volume for the workspace.
4.2.2.8. Triggers
Use Triggers in conjunction with pipelines to create a full-fledged CI/CD system where Kubernetes resources define the entire CI/CD execution. Triggers capture the external events, such as a Git pull request, and process them to extract key pieces of information. Mapping this event data to a set of predefined parameters triggers a series of tasks that can then create and deploy Kubernetes resources and instantiate the pipeline.
For example, you define a CI/CD workflow using Red Hat OpenShift Pipelines for your application. The pipeline must start for any new changes to take effect in the application repository. Triggers automate this process by capturing and processing any change event and by triggering a pipeline run that deploys the new image with the latest changes.
Triggers consist of the following main resources that work together to form a reusable, decoupled, and self-sustaining CI/CD system:
The
TriggerBindingresource extracts the fields from an event payload and stores them as parameters.The following example shows a code snippet of the
TriggerBindingresource, which extracts the Git repository information from the received event payload:apiVersion: triggers.tekton.dev/v1beta11 kind: TriggerBinding2 metadata: name: vote-app3 spec: params:4 - name: git-repo-url value: $(body.repository.url) - name: git-repo-name value: $(body.repository.name) - name: git-revision value: $(body.head_commit.id)- 1
- The API version of the
TriggerBindingresource. In this example,v1beta1. - 2
- Specifies the type of Kubernetes object. In this example,
TriggerBinding. - 3
- Unique name to identify the
TriggerBindingresource. - 4
- List of parameters which will be extracted from the received event payload and passed to the
TriggerTemplateresource. In this example, the Git repository URL, name, and revision are extracted from the body of the event payload.
The
TriggerTemplateresource acts as a standard for the way resources must be created. It specifies the way parameterized data from theTriggerBindingresource should be used. A trigger template receives input from the trigger binding, and then performs a series of actions that results in creation of new pipeline resources, and initiation of a new pipeline run.The following example shows a code snippet of a
TriggerTemplateresource, which creates a pipeline run using the Git repository information received from theTriggerBindingresource you just created:apiVersion: triggers.tekton.dev/v1beta11 kind: TriggerTemplate2 metadata: name: vote-app3 spec: params:4 - name: git-repo-url description: The git repository url - name: git-revision description: The git revision default: pipelines-1.7 - name: git-repo-name description: The name of the deployment to be created / patched resourcetemplates:5 - apiVersion: tekton.dev/v1beta1 kind: PipelineRun metadata: name: build-deploy-$(tt.params.git-repo-name)-$(uid) spec: serviceAccountName: pipeline pipelineRef: name: build-and-deploy params: - name: deployment-name value: $(tt.params.git-repo-name) - name: git-url value: $(tt.params.git-repo-url) - name: git-revision value: $(tt.params.git-revision) - name: IMAGE value: image-registry.openshift-image-registry.svc:5000/pipelines-tutorial/$(tt.params.git-repo-name) workspaces: - name: shared-workspace volumeClaimTemplate: spec: accessModes: - ReadWriteOnce resources: requests: storage: 500Mi- 1
- The API version of the
TriggerTemplateresource. In this example,v1beta1. - 2
- Specifies the type of Kubernetes object. In this example,
TriggerTemplate. - 3
- Unique name to identify the
TriggerTemplateresource. - 4
- Parameters supplied by the
TriggerBindingresource. - 5
- List of templates that specify the way resources must be created using the parameters received through the
TriggerBindingorEventListenerresources.
The
Triggerresource combines theTriggerBindingandTriggerTemplateresources, and optionally, theinterceptorsevent processor.Interceptors process all the events for a specific platform that runs before the
TriggerBindingresource. You can use interceptors to filter the payload, verify events, define and test trigger conditions, and implement other useful processing. Interceptors use secret for event verification. Once the event data passes through an interceptor, it then goes to the trigger before you pass the payload data to the trigger binding. You can also use an interceptor to modify the behavior of the associated trigger referenced in theEventListenerspecification.The following example shows a code snippet of a
Triggerresource, namedvote-triggerthat connects theTriggerBindingandTriggerTemplateresources, and theinterceptorsevent processor.apiVersion: triggers.tekton.dev/v1beta11 kind: Trigger2 metadata: name: vote-trigger3 spec: serviceAccountName: pipeline4 interceptors: - ref: name: "github"5 params:6 - name: "secretRef" value: secretName: github-secret secretKey: secretToken - name: "eventTypes" value: ["push"] bindings: - ref: vote-app7 template:8 ref: vote-app --- apiVersion: v1 kind: Secret9 metadata: name: github-secret type: Opaque stringData: secretToken: "1234567"- 1
- The API version of the
Triggerresource. In this example,v1beta1. - 2
- Specifies the type of Kubernetes object. In this example,
Trigger. - 3
- Unique name to identify the
Triggerresource. - 4
- Service account name to be used.
- 5
- Interceptor name to be referenced. In this example,
github. - 6
- Desired parameters to be specified.
- 7
- Name of the
TriggerBindingresource to be connected to theTriggerTemplateresource. - 8
- Name of the
TriggerTemplateresource to be connected to theTriggerBindingresource. - 9
- Secret to be used to verify events.
The
EventListenerresource provides an endpoint, or an event sink, that listens for incoming HTTP-based events with a JSON payload. It extracts event parameters from eachTriggerBindingresource, and then processes this data to create Kubernetes resources as specified by the correspondingTriggerTemplateresource. TheEventListenerresource also performs lightweight event processing or basic filtering on the payload using eventinterceptors, which identify the type of payload and optionally modify it. Currently, pipeline triggers support five types of interceptors: Webhook Interceptors, GitHub Interceptors, GitLab Interceptors, Bitbucket Interceptors, and Common Expression Language (CEL) Interceptors.The following example shows an
EventListenerresource, which references theTriggerresource namedvote-trigger.apiVersion: triggers.tekton.dev/v1beta11 kind: EventListener2 metadata: name: vote-app3 spec: serviceAccountName: pipeline4 triggers: - triggerRef: vote-trigger5 - 1
- The API version of the
EventListenerresource. In this example,v1beta1. - 2
- Specifies the type of Kubernetes object. In this example,
EventListener. - 3
- Unique name to identify the
EventListenerresource. - 4
- Service account name to be used.
- 5
- Name of the
Triggerresource referenced by theEventListenerresource.
4.3. Installing OpenShift Pipelines
This guide walks cluster administrators through the process of installing the Red Hat OpenShift Pipelines Operator to an OpenShift Container Platform cluster.
Prerequisites
-
You have access to an OpenShift Container Platform cluster using an account with
cluster-adminpermissions. -
You have installed
ocCLI. -
You have installed OpenShift Pipelines (
tkn) CLI on your local system.
4.3.1. Installing the Red Hat OpenShift Pipelines Operator in web console
You can install Red Hat OpenShift Pipelines using the Operator listed in the OpenShift Container Platform OperatorHub. When you install the Red Hat OpenShift Pipelines Operator, the custom resources (CRs) required for the pipelines configuration are automatically installed along with the Operator.
The default Operator custom resource definition (CRD) config.operator.tekton.dev is now replaced by tektonconfigs.operator.tekton.dev. In addition, the Operator provides the following additional CRDs to individually manage OpenShift Pipelines components: tektonpipelines.operator.tekton.dev, tektontriggers.operator.tekton.dev and tektonaddons.operator.tekton.dev.
If you have OpenShift Pipelines already installed on your cluster, the existing installation is seamlessly upgraded. The Operator will replace the instance of config.operator.tekton.dev on your cluster with an instance of tektonconfigs.operator.tekton.dev and additional objects of the other CRDs as necessary.
If you manually changed your existing installation, such as, changing the target namespace in the config.operator.tekton.dev CRD instance by making changes to the resource name - cluster field, then the upgrade path is not smooth. In such cases, the recommended workflow is to uninstall your installation and reinstall the Red Hat OpenShift Pipelines Operator.
The Red Hat OpenShift Pipelines Operator now provides the option to choose the components that you want to install by specifying profiles as part of the TektonConfig CR. The TektonConfig CR is automatically installed when the Operator is installed. The supported profiles are:
- Lite: This installs only Tekton Pipelines.
- Basic: This installs Tekton Pipelines and Tekton Triggers.
-
All: This is the default profile used when the
TektonConfigCR is installed. This profile installs all of the Tekton components: Tekton Pipelines, Tekton Triggers, Tekton Addons (which includeClusterTasks,ClusterTriggerBindings,ConsoleCLIDownload,ConsoleQuickStartandConsoleYAMLSampleresources).
Procedure
-
In the Administrator perspective of the web console, navigate to Operators
OperatorHub. -
Use the Filter by keyword box to search for
Red Hat OpenShift PipelinesOperator in the catalog. Click the Red Hat OpenShift Pipelines Operator tile. - Read the brief description about the Operator on the Red Hat OpenShift Pipelines Operator page. Click Install.
On the Install Operator page:
-
Select All namespaces on the cluster (default) for the Installation Mode. This mode installs the Operator in the default
openshift-operatorsnamespace, which enables the Operator to watch and be made available to all namespaces in the cluster. - Select Automatic for the Approval Strategy. This ensures that the future upgrades to the Operator are handled automatically by the Operator Lifecycle Manager (OLM). If you select the Manual approval strategy, OLM creates an update request. As a cluster administrator, you must then manually approve the OLM update request to update the Operator to the new version.
Select an Update Channel.
- The stable channel enables installation of the latest stable and supported release of the Red Hat OpenShift Pipelines Operator.
- The preview channel enables installation of the latest preview version of the Red Hat OpenShift Pipelines Operator, which may contain features that are not yet available from the stable channel and is not supported.
-
Select All namespaces on the cluster (default) for the Installation Mode. This mode installs the Operator in the default
Click Install. You will see the Operator listed on the Installed Operators page.
NoteThe Operator is installed automatically into the
openshift-operatorsnamespace.Verify that the Status is set to Succeeded Up to date to confirm successful installation of Red Hat OpenShift Pipelines Operator.
WarningThe success status may show as Succeeded Up to date even if installation of other components is in-progress. Therefore, it is important to verify the installation manually in the terminal.
Verify that all components of the Red Hat OpenShift Pipelines Operator were installed successfully. Login to the cluster on the terminal, and run the following command:
$ oc get tektonconfig configExample output
NAME VERSION READY REASON config 1.9.2 TrueIf the READY condition is True, the Operator and its components have been installed successfully.
Additonally, check the components' versions by running the following command:
$ oc get tektonpipeline,tektontrigger,tektonaddon,pacExample output
NAME VERSION READY REASON tektonpipeline.operator.tekton.dev/pipeline v0.41.1 True NAME VERSION READY REASON tektontrigger.operator.tekton.dev/trigger v0.22.2 True NAME VERSION READY REASON tektonaddon.operator.tekton.dev/addon 1.9.2 True NAME VERSION READY REASON openshiftpipelinesascode.operator.tekton.dev/pipelines-as-code v0.15.5 True
4.3.2. Installing the OpenShift Pipelines Operator using the CLI
You can install Red Hat OpenShift Pipelines Operator from the OperatorHub using the CLI.
Procedure
Create a Subscription object YAML file to subscribe a namespace to the Red Hat OpenShift Pipelines Operator, for example,
sub.yaml:Example Subscription
apiVersion: operators.coreos.com/v1alpha1 kind: Subscription metadata: name: openshift-pipelines-operator namespace: openshift-operators spec: channel: <channel name>1 name: openshift-pipelines-operator-rh2 source: redhat-operators3 sourceNamespace: openshift-marketplace4 Create the Subscription object:
$ oc apply -f sub.yamlThe Red Hat OpenShift Pipelines Operator is now installed in the default target namespace
openshift-operators.
4.3.3. Red Hat OpenShift Pipelines Operator in a restricted environment
The Red Hat OpenShift Pipelines Operator enables support for installation of pipelines in a restricted network environment.
The Operator installs a proxy webhook that sets the proxy environment variables in the containers of the pod created by tekton-controllers based on the cluster proxy object. It also sets the proxy environment variables in the TektonPipelines, TektonTriggers, Controllers, Webhooks, and Operator Proxy Webhook resources.
By default, the proxy webhook is disabled for the openshift-pipelines namespace. To disable it for any other namespace, you can add the operator.tekton.dev/disable-proxy: true label to the namespace object.
4.3.4. Disabling the automatic creation of RBAC resources
The default installation of the Red Hat OpenShift Pipelines Operator creates multiple role-based access control (RBAC) resources for all namespaces in the cluster, except the namespaces matching the ^(openshift|kube)-* regular expression pattern. Among these RBAC resources, the pipelines-scc-rolebinding security context constraint (SCC) role binding resource is a potential security issue, because the associated pipelines-scc SCC has the RunAsAny privilege.
To disable the automatic creation of cluster-wide RBAC resources after the Red Hat OpenShift Pipelines Operator is installed, cluster administrators can set the createRbacResource parameter to false in the cluster-level TektonConfig custom resource (CR).
Example TektonConfig CR
apiVersion: operator.tekton.dev/v1alpha1
kind: TektonConfig
metadata:
name: config
spec:
params:
- name: createRbacResource
value: "false"
profile: all
targetNamespace: openshift-pipelines
addon:
params:
- name: clusterTasks
value: "true"
- name: pipelineTemplates
value: "true"
...
As a cluster administrator or an user with appropriate privileges, when you disable the automatic creation of RBAC resources for all namespaces, the default ClusterTask resource does not work. For the ClusterTask resource to function, you must create the RBAC resources manually for each intended namespace.
4.4. Uninstalling OpenShift Pipelines
Uninstalling the Red Hat OpenShift Pipelines Operator is a two-step process:
- Delete the Custom Resources (CRs) that were added by default when you installed the Red Hat OpenShift Pipelines Operator.
- Uninstall the Red Hat OpenShift Pipelines Operator.
Uninstalling only the Operator will not remove the Red Hat OpenShift Pipelines components created by default when the Operator is installed.
4.4.1. Deleting the Red Hat OpenShift Pipelines components and Custom Resources
Delete the Custom Resources (CRs) created by default during installation of the Red Hat OpenShift Pipelines Operator.
Procedure
-
In the Administrator perspective of the web console, navigate to Administration
Custom Resource Definition. -
Type
config.operator.tekton.devin the Filter by name box to search for the Red Hat OpenShift Pipelines Operator CRs. - Click CRD Config to see the Custom Resource Definition Details page.
Click the Actions drop-down menu and select Delete Custom Resource Definition.
NoteDeleting the CRs will delete the Red Hat OpenShift Pipelines components, and all the Tasks and Pipelines on the cluster will be lost.
- Click Delete to confirm the deletion of the CRs.
4.4.2. Uninstalling the Red Hat OpenShift Pipelines Operator
Procedure
-
From the Operators
OperatorHub page, use the Filter by keyword box to search for Red Hat OpenShift Pipelines Operator. - Click the OpenShift Pipelines Operator tile. The Operator tile indicates it is installed.
- In the OpenShift Pipelines Operator descriptor page, click Uninstall.
4.5. Creating CI/CD solutions for applications using OpenShift Pipelines
With Red Hat OpenShift Pipelines, you can create a customized CI/CD solution to build, test, and deploy your application.
To create a full-fledged, self-serving CI/CD pipeline for an application, perform the following tasks:
- Create custom tasks, or install existing reusable tasks.
- Create and define the delivery pipeline for your application.
Provide a storage volume or filesystem that is attached to a workspace for the pipeline execution, using one of the following approaches:
- Specify a volume claim template that creates a persistent volume claim
- Specify a persistent volume claim
-
Create a
PipelineRunobject to instantiate and invoke the pipeline. - Add triggers to capture events in the source repository.
This section uses the pipelines-tutorial example to demonstrate the preceding tasks. The example uses a simple application which consists of:
-
A front-end interface,
pipelines-vote-ui, with the source code in thepipelines-vote-uiGit repository. -
A back-end interface,
pipelines-vote-api, with the source code in thepipelines-vote-apiGit repository. -
The
apply-manifestsandupdate-deploymenttasks in thepipelines-tutorialGit repository.
4.5.1. Prerequisites
- You have access to an OpenShift Container Platform cluster.
- You have installed OpenShift Pipelines using the Red Hat OpenShift Pipelines Operator listed in the OpenShift OperatorHub. After it is installed, it is applicable to the entire cluster.
- You have installed OpenShift Pipelines CLI.
-
You have forked the front-end
pipelines-vote-uiand back-endpipelines-vote-apiGit repositories using your GitHub ID, and have administrator access to these repositories. -
Optional: You have cloned the
pipelines-tutorialGit repository.
4.5.2. Creating a project and checking your pipeline service account
Procedure
Log in to your OpenShift Container Platform cluster:
$ oc login -u <login> -p <password> https://openshift.example.com:6443Create a project for the sample application. For this example workflow, create the
pipelines-tutorialproject:$ oc new-project pipelines-tutorialNoteIf you create a project with a different name, be sure to update the resource URLs used in the example with your project name.
View the
pipelineservice account:Red Hat OpenShift Pipelines Operator adds and configures a service account named
pipelinethat has sufficient permissions to build and push an image. This service account is used by thePipelineRunobject.$ oc get serviceaccount pipeline
4.5.3. Creating pipeline tasks
Procedure
Install the
apply-manifestsandupdate-deploymenttask resources from thepipelines-tutorialrepository, which contains a list of reusable tasks for pipelines:$ oc create -f https://raw.githubusercontent.com/openshift/pipelines-tutorial/pipelines-1.7/01_pipeline/01_apply_manifest_task.yaml $ oc create -f https://raw.githubusercontent.com/openshift/pipelines-tutorial/pipelines-1.7/01_pipeline/02_update_deployment_task.yamlUse the
tkn task listcommand to list the tasks you created:$ tkn task listThe output verifies that the
apply-manifestsandupdate-deploymenttask resources were created:NAME DESCRIPTION AGE apply-manifests 1 minute ago update-deployment 48 seconds agoUse the
tkn clustertasks listcommand to list the Operator-installed additional cluster tasks such asbuildahands2i-python:NoteTo use the
buildahcluster task in a restricted environment, you must ensure that the Dockerfile uses an internal image stream as the base image.$ tkn clustertasks listThe output lists the Operator-installed
ClusterTaskresources:NAME DESCRIPTION AGE buildah 1 day ago git-clone 1 day ago s2i-python 1 day ago tkn 1 day ago
4.5.4. Assembling a pipeline
A pipeline represents a CI/CD flow and is defined by the tasks to be executed. It is designed to be generic and reusable in multiple applications and environments.
A pipeline specifies how the tasks interact with each other and their order of execution using the from and runAfter parameters. It uses the workspaces field to specify one or more volumes that each task in the pipeline requires during execution.
In this section, you will create a pipeline that takes the source code of the application from GitHub, and then builds and deploys it on OpenShift Container Platform.
The pipeline performs the following tasks for the back-end application pipelines-vote-api and front-end application pipelines-vote-ui:
-
Clones the source code of the application from the Git repository by referring to the
git-urlandgit-revisionparameters. -
Builds the container image using the
buildahcluster task. -
Pushes the image to the internal image registry by referring to the
imageparameter. -
Deploys the new image on OpenShift Container Platform by using the
apply-manifestsandupdate-deploymenttasks.
Procedure
Copy the contents of the following sample pipeline YAML file and save it:
apiVersion: tekton.dev/v1beta1 kind: Pipeline metadata: name: build-and-deploy spec: workspaces: - name: shared-workspace params: - name: deployment-name type: string description: name of the deployment to be patched - name: git-url type: string description: url of the git repo for the code of deployment - name: git-revision type: string description: revision to be used from repo of the code for deployment default: "pipelines-1.7" - name: IMAGE type: string description: image to be built from the code tasks: - name: fetch-repository taskRef: name: git-clone kind: ClusterTask workspaces: - name: output workspace: shared-workspace params: - name: url value: $(params.git-url) - name: subdirectory value: "" - name: deleteExisting value: "true" - name: revision value: $(params.git-revision) - name: build-image taskRef: name: buildah kind: ClusterTask params: - name: IMAGE value: $(params.IMAGE) workspaces: - name: source workspace: shared-workspace runAfter: - fetch-repository - name: apply-manifests taskRef: name: apply-manifests workspaces: - name: source workspace: shared-workspace runAfter: - build-image - name: update-deployment taskRef: name: update-deployment params: - name: deployment value: $(params.deployment-name) - name: IMAGE value: $(params.IMAGE) runAfter: - apply-manifestsThe pipeline definition abstracts away the specifics of the Git source repository and image registries. These details are added as
paramswhen a pipeline is triggered and executed.Create the pipeline:
$ oc create -f <pipeline-yaml-file-name.yaml>Alternatively, you can also execute the YAML file directly from the Git repository:
$ oc create -f https://raw.githubusercontent.com/openshift/pipelines-tutorial/pipelines-1.7/01_pipeline/04_pipeline.yamlUse the
tkn pipeline listcommand to verify that the pipeline is added to the application:$ tkn pipeline listThe output verifies that the
build-and-deploypipeline was created:NAME AGE LAST RUN STARTED DURATION STATUS build-and-deploy 1 minute ago --- --- --- ---
4.5.5. Mirroring images to run pipelines in a restricted environment
To run OpenShift Pipelines in a disconnected cluster or a cluster provisioned in a restricted environment, ensure that either the Samples Operator is configured for a restricted network, or a cluster administrator has created a cluster with a mirrored registry.
The following procedure uses the pipelines-tutorial example to create a pipeline for an application in a restricted environment using a cluster with a mirrored registry. To ensure that the pipelines-tutorial example works in a restricted environment, you must mirror the respective builder images from the mirror registry for the front-end interface, pipelines-vote-ui; back-end interface, pipelines-vote-api; and the cli.
Procedure
Mirror the builder image from the mirror registry for the front-end interface,
pipelines-vote-ui.Verify that the required images tag is not imported:
$ oc describe imagestream python -n openshiftExample output
Name: python Namespace: openshift [...] 3.8-ubi8 (latest) tagged from registry.redhat.io/ubi8/python-38:latest prefer registry pullthrough when referencing this tag Build and run Python 3.8 applications on UBI 8. For more information about using this builder image, including OpenShift considerations, see https://github.com/sclorg/s2i-python-container/blob/master/3.8/README.md. Tags: builder, python Supports: python:3.8, python Example Repo: https://github.com/sclorg/django-ex.git [...]Mirror the supported image tag to the private registry:
$ oc image mirror registry.redhat.io/ubi8/python-38:latest <mirror-registry>:<port>/ubi8/python-38Import the image:
$ oc tag <mirror-registry>:<port>/ubi8/python-38 python:latest --scheduled -n openshiftYou must periodically re-import the image. The
--scheduledflag enables automatic re-import of the image.Verify that the images with the given tag have been imported:
$ oc describe imagestream python -n openshiftExample output
Name: python Namespace: openshift [...] latest updates automatically from registry <mirror-registry>:<port>/ubi8/python-38 * <mirror-registry>:<port>/ubi8/python-38@sha256:3ee3c2e70251e75bfeac25c0c33356add9cc4abcbc9c51d858f39e4dc29c5f58 [...]
Mirror the builder image from the mirror registry for the back-end interface,
pipelines-vote-api.Verify that the required images tag is not imported:
$ oc describe imagestream golang -n openshiftExample output
Name: golang Namespace: openshift [...] 1.14.7-ubi8 (latest) tagged from registry.redhat.io/ubi8/go-toolset:1.14.7 prefer registry pullthrough when referencing this tag Build and run Go applications on UBI 8. For more information about using this builder image, including OpenShift considerations, see https://github.com/sclorg/golang-container/blob/master/README.md. Tags: builder, golang, go Supports: golang Example Repo: https://github.com/sclorg/golang-ex.git [...]Mirror the supported image tag to the private registry:
$ oc image mirror registry.redhat.io/ubi8/go-toolset:1.14.7 <mirror-registry>:<port>/ubi8/go-toolsetImport the image:
$ oc tag <mirror-registry>:<port>/ubi8/go-toolset golang:latest --scheduled -n openshiftYou must periodically re-import the image. The
--scheduledflag enables automatic re-import of the image.Verify that the images with the given tag have been imported:
$ oc describe imagestream golang -n openshiftExample output
Name: golang Namespace: openshift [...] latest updates automatically from registry <mirror-registry>:<port>/ubi8/go-toolset * <mirror-registry>:<port>/ubi8/go-toolset@sha256:59a74d581df3a2bd63ab55f7ac106677694bf612a1fe9e7e3e1487f55c421b37 [...]
Mirror the builder image from the mirror registry for the
cli.Verify that the required images tag is not imported:
$ oc describe imagestream cli -n openshiftExample output
Name: cli Namespace: openshift [...] latest updates automatically from registry quay.io/openshift-release-dev/ocp-v4.0-art-dev@sha256:65c68e8c22487375c4c6ce6f18ed5485915f2bf612e41fef6d41cbfcdb143551 * quay.io/openshift-release-dev/ocp-v4.0-art-dev@sha256:65c68e8c22487375c4c6ce6f18ed5485915f2bf612e41fef6d41cbfcdb143551 [...]Mirror the supported image tag to the private registry:
$ oc image mirror quay.io/openshift-release-dev/ocp-v4.0-art-dev@sha256:65c68e8c22487375c4c6ce6f18ed5485915f2bf612e41fef6d41cbfcdb143551 <mirror-registry>:<port>/openshift-release-dev/ocp-v4.0-art-dev:latestImport the image:
$ oc tag <mirror-registry>:<port>/openshift-release-dev/ocp-v4.0-art-dev cli:latest --scheduled -n openshiftYou must periodically re-import the image. The
--scheduledflag enables automatic re-import of the image.Verify that the images with the given tag have been imported:
$ oc describe imagestream cli -n openshiftExample output
Name: cli Namespace: openshift [...] latest updates automatically from registry <mirror-registry>:<port>/openshift-release-dev/ocp-v4.0-art-dev * <mirror-registry>:<port>/openshift-release-dev/ocp-v4.0-art-dev@sha256:65c68e8c22487375c4c6ce6f18ed5485915f2bf612e41fef6d41cbfcdb143551 [...]
4.5.6. Running a pipeline
A PipelineRun resource starts a pipeline and ties it to the Git and image resources that should be used for the specific invocation. It automatically creates and starts the TaskRun resources for each task in the pipeline.
Procedure
Start the pipeline for the back-end application:
$ tkn pipeline start build-and-deploy \ -w name=shared-workspace,volumeClaimTemplateFile=https://raw.githubusercontent.com/openshift/pipelines-tutorial/pipelines-1.7/01_pipeline/03_persistent_volume_claim.yaml \ -p deployment-name=pipelines-vote-api \ -p git-url=https://github.com/openshift/pipelines-vote-api.git \ -p IMAGE=image-registry.openshift-image-registry.svc:5000/pipelines-tutorial/pipelines-vote-api \ --use-param-defaultsThe previous command uses a volume claim template, which creates a persistent volume claim for the pipeline execution.
To track the progress of the pipeline run, enter the following command::
$ tkn pipelinerun logs <pipelinerun_id> -fThe <pipelinerun_id> in the above command is the ID for the
PipelineRunthat was returned in the output of the previous command.Start the pipeline for the front-end application:
$ tkn pipeline start build-and-deploy \ -w name=shared-workspace,volumeClaimTemplateFile=https://raw.githubusercontent.com/openshift/pipelines-tutorial/pipelines-1.7/01_pipeline/03_persistent_volume_claim.yaml \ -p deployment-name=pipelines-vote-ui \ -p git-url=https://github.com/openshift/pipelines-vote-ui.git \ -p IMAGE=image-registry.openshift-image-registry.svc:5000/pipelines-tutorial/pipelines-vote-ui \ --use-param-defaultsTo track the progress of the pipeline run, enter the following command:
$ tkn pipelinerun logs <pipelinerun_id> -fThe <pipelinerun_id> in the above command is the ID for the
PipelineRunthat was returned in the output of the previous command.After a few minutes, use
tkn pipelinerun listcommand to verify that the pipeline ran successfully by listing all the pipeline runs:$ tkn pipelinerun listThe output lists the pipeline runs:
NAME STARTED DURATION STATUS build-and-deploy-run-xy7rw 1 hour ago 2 minutes Succeeded build-and-deploy-run-z2rz8 1 hour ago 19 minutes SucceededGet the application route:
$ oc get route pipelines-vote-ui --template='http://{{.spec.host}}'Note the output of the previous command. You can access the application using this route.
To rerun the last pipeline run, using the pipeline resources and service account of the previous pipeline, run:
$ tkn pipeline start build-and-deploy --last
4.5.7. Adding triggers to a pipeline
Triggers enable pipelines to respond to external GitHub events, such as push events and pull requests. After you assemble and start a pipeline for the application, add the TriggerBinding, TriggerTemplate, Trigger, and EventListener resources to capture the GitHub events.
Procedure
Copy the content of the following sample
TriggerBindingYAML file and save it:apiVersion: triggers.tekton.dev/v1beta1 kind: TriggerBinding metadata: name: vote-app spec: params: - name: git-repo-url value: $(body.repository.url) - name: git-repo-name value: $(body.repository.name) - name: git-revision value: $(body.head_commit.id)Create the
TriggerBindingresource:$ oc create -f <triggerbinding-yaml-file-name.yaml>Alternatively, you can create the
TriggerBindingresource directly from thepipelines-tutorialGit repository:$ oc create -f https://raw.githubusercontent.com/openshift/pipelines-tutorial/pipelines-1.7/03_triggers/01_binding.yamlCopy the content of the following sample
TriggerTemplateYAML file and save it:apiVersion: triggers.tekton.dev/v1beta1 kind: TriggerTemplate metadata: name: vote-app spec: params: - name: git-repo-url description: The git repository url - name: git-revision description: The git revision default: pipelines-1.7 - name: git-repo-name description: The name of the deployment to be created / patched resourcetemplates: - apiVersion: tekton.dev/v1beta1 kind: PipelineRun metadata: generateName: build-deploy-$(tt.params.git-repo-name)- spec: serviceAccountName: pipeline pipelineRef: name: build-and-deploy params: - name: deployment-name value: $(tt.params.git-repo-name) - name: git-url value: $(tt.params.git-repo-url) - name: git-revision value: $(tt.params.git-revision) - name: IMAGE value: image-registry.openshift-image-registry.svc:5000/pipelines-tutorial/$(tt.params.git-repo-name) workspaces: - name: shared-workspace volumeClaimTemplate: spec: accessModes: - ReadWriteOnce resources: requests: storage: 500MiThe template specifies a volume claim template to create a persistent volume claim for defining the storage volume for the workspace. Therefore, you do not need to create a persistent volume claim to provide data storage.
Create the
TriggerTemplateresource:$ oc create -f <triggertemplate-yaml-file-name.yaml>Alternatively, you can create the
TriggerTemplateresource directly from thepipelines-tutorialGit repository:$ oc create -f https://raw.githubusercontent.com/openshift/pipelines-tutorial/pipelines-1.7/03_triggers/02_template.yamlCopy the contents of the following sample
TriggerYAML file and save it:apiVersion: triggers.tekton.dev/v1beta1 kind: Trigger metadata: name: vote-trigger spec: serviceAccountName: pipeline bindings: - ref: vote-app template: ref: vote-appCreate the
Triggerresource:$ oc create -f <trigger-yaml-file-name.yaml>Alternatively, you can create the
Triggerresource directly from thepipelines-tutorialGit repository:$ oc create -f https://raw.githubusercontent.com/openshift/pipelines-tutorial/pipelines-1.7/03_triggers/03_trigger.yamlCopy the contents of the following sample
EventListenerYAML file and save it:apiVersion: triggers.tekton.dev/v1beta1 kind: EventListener metadata: name: vote-app spec: serviceAccountName: pipeline triggers: - triggerRef: vote-triggerAlternatively, if you have not defined a trigger custom resource, add the binding and template spec to the
EventListenerYAML file, instead of referring to the name of the trigger:apiVersion: triggers.tekton.dev/v1beta1 kind: EventListener metadata: name: vote-app spec: serviceAccountName: pipeline triggers: - bindings: - ref: vote-app template: ref: vote-appCreate the
EventListenerresource by performing the following steps:To create an
EventListenerresource using a secure HTTPS connection:Add a label to enable the secure HTTPS connection to the
Eventlistenerresource:$ oc label namespace <ns-name> operator.tekton.dev/enable-annotation=enabledCreate the
EventListenerresource:$ oc create -f <eventlistener-yaml-file-name.yaml>Alternatively, you can create the
EvenListenerresource directly from thepipelines-tutorialGit repository:$ oc create -f https://raw.githubusercontent.com/openshift/pipelines-tutorial/pipelines-1.7/03_triggers/04_event_listener.yamlCreate a route with the re-encrypt TLS termination:
$ oc create route reencrypt --service=<svc-name> --cert=tls.crt --key=tls.key --ca-cert=ca.crt --hostname=<hostname>Alternatively, you can create a re-encrypt TLS termination YAML file to create a secured route.
Example Re-encrypt TLS Termination YAML of the Secured Route
apiVersion: route.openshift.io/v1 kind: Route metadata: name: route-passthrough-secured1 spec: host: <hostname> to: kind: Service name: frontend2 tls: termination: reencrypt3 key: [as in edge termination] certificate: [as in edge termination] caCertificate: [as in edge termination] destinationCACertificate: |-4 -----BEGIN CERTIFICATE----- [...] -----END CERTIFICATE------ 1 2
- The name of the object, which is limited to 63 characters.
- 3
- The
terminationfield is set toreencrypt. This is the only requiredtlsfield. - 4
- Required for re-encryption.
destinationCACertificatespecifies a CA certificate to validate the endpoint certificate, securing the connection from the router to the destination pods. If the service is using a service signing certificate, or the administrator has specified a default CA certificate for the router and the service has a certificate signed by that CA, this field can be omitted.
See
oc create route reencrypt --helpfor more options.
To create an
EventListenerresource using an insecure HTTP connection:-
Create the
EventListenerresource. Expose the
EventListenerservice as an OpenShift Container Platform route to make it publicly accessible:$ oc expose svc el-vote-app
-
Create the
4.5.8. Configuring event listeners to serve multiple namespaces
You can skip this section if you want to create a basic CI/CD pipeline. However, if your deployment strategy involves multiple namespaces, you can configure event listeners to serve multiple namespaces.
To increase reusability of EvenListener objects, cluster administrators can configure and deploy them as multi-tenant event listeners that serve multiple namespaces.
Procedure
Configure cluster-wide fetch permission for the event listener.
Set a service account name to be used in the
ClusterRoleBindingandEventListenerobjects. For example,el-sa.Example
ServiceAccount.yamlapiVersion: v1 kind: ServiceAccount metadata: name: el-sa ---In the
rulessection of theClusterRole.yamlfile, set appropriate permissions for every event listener deployment to function cluster-wide.Example
ClusterRole.yamlkind: ClusterRole apiVersion: rbac.authorization.k8s.io/v1 metadata: name: el-sel-clusterrole rules: - apiGroups: ["triggers.tekton.dev"] resources: ["eventlisteners", "clustertriggerbindings", "clusterinterceptors", "triggerbindings", "triggertemplates", "triggers"] verbs: ["get", "list", "watch"] - apiGroups: [""] resources: ["configmaps", "secrets"] verbs: ["get", "list", "watch"] - apiGroups: [""] resources: ["serviceaccounts"] verbs: ["impersonate"] ...Configure cluster role binding with the appropriate service account name and cluster role name.
Example
ClusterRoleBinding.yamlapiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRoleBinding metadata: name: el-mul-clusterrolebinding subjects: - kind: ServiceAccount name: el-sa namespace: default roleRef: apiGroup: rbac.authorization.k8s.io kind: ClusterRole name: el-sel-clusterrole ...
In the
specparameter of the event listener, add the service account name, for exampleel-sa. Fill thenamespaceSelectorparameter with names of namespaces where event listener is intended to serve.Example
EventListener.yamlapiVersion: triggers.tekton.dev/v1beta1 kind: EventListener metadata: name: namespace-selector-listener spec: serviceAccountName: el-sa namespaceSelector: matchNames: - default - foo ...Create a service account with the necessary permissions, for example
foo-trigger-sa. Use it for role binding the triggers.Example
ServiceAccount.yamlapiVersion: v1 kind: ServiceAccount metadata: name: foo-trigger-sa namespace: foo ...Example
RoleBinding.yamlapiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: triggercr-rolebinding namespace: foo subjects: - kind: ServiceAccount name: foo-trigger-sa namespace: foo roleRef: apiGroup: rbac.authorization.k8s.io kind: ClusterRole name: tekton-triggers-eventlistener-roles ...Create a trigger with the appropriate trigger template, trigger binding, and service account name.
Example
Trigger.yamlapiVersion: triggers.tekton.dev/v1beta1 kind: Trigger metadata: name: trigger namespace: foo spec: serviceAccountName: foo-trigger-sa interceptors: - ref: name: "github" params: - name: "secretRef" value: secretName: github-secret secretKey: secretToken - name: "eventTypes" value: ["push"] bindings: - ref: vote-app template: ref: vote-app ...
4.5.9. Creating webhooks
Webhooks are HTTP POST messages that are received by the event listeners whenever a configured event occurs in your repository. The event payload is then mapped to trigger bindings, and processed by trigger templates. The trigger templates eventually start one or more pipeline runs, leading to the creation and deployment of Kubernetes resources.
In this section, you will configure a webhook URL on your forked Git repositories pipelines-vote-ui and pipelines-vote-api. This URL points to the publicly accessible EventListener service route.
Adding webhooks requires administrative privileges to the repository. If you do not have administrative access to your repository, contact your system administrator for adding webhooks.
Procedure
Get the webhook URL:
For a secure HTTPS connection:
$ echo "URL: $(oc get route el-vote-app --template='https://{{.spec.host}}')"For an HTTP (insecure) connection:
$ echo "URL: $(oc get route el-vote-app --template='http://{{.spec.host}}')"Note the URL obtained in the output.
Configure webhooks manually on the front-end repository:
-
Open the front-end Git repository
pipelines-vote-uiin your browser. -
Click Settings
Webhooks Add Webhook On the Webhooks/Add Webhook page:
- Enter the webhook URL from step 1 in Payload URL field
- Select application/json for the Content type
- Specify the secret in the Secret field
- Ensure that the Just the push event is selected
- Select Active
- Click Add Webhook
-
Open the front-end Git repository
-
Repeat step 2 for the back-end repository
pipelines-vote-api.
4.5.10. Triggering a pipeline run
Whenever a push event occurs in the Git repository, the configured webhook sends an event payload to the publicly exposed EventListener service route. The EventListener service of the application processes the payload, and passes it to the relevant TriggerBinding and TriggerTemplate resource pairs. The TriggerBinding resource extracts the parameters, and the TriggerTemplate resource uses these parameters and specifies the way the resources must be created. This may rebuild and redeploy the application.
In this section, you push an empty commit to the front-end pipelines-vote-ui repository, which then triggers the pipeline run.
Procedure
From the terminal, clone your forked Git repository
pipelines-vote-ui:$ git clone git@github.com:<your GitHub ID>/pipelines-vote-ui.git -b pipelines-1.7Push an empty commit:
$ git commit -m "empty-commit" --allow-empty && git push origin pipelines-1.7Check if the pipeline run was triggered:
$ tkn pipelinerun listNotice that a new pipeline run was initiated.
4.5.11. Enabling monitoring of event listeners for Triggers for user-defined projects
As a cluster administrator, to gather event listener metrics for the Triggers service in a user-defined project and display them in the OpenShift Container Platform web console, you can create a service monitor for each event listener. On receiving an HTTP request, event listeners for the Triggers service return three metrics — eventlistener_http_duration_seconds, eventlistener_event_count, and eventlistener_triggered_resources.
Prerequisites
- You have logged in to the OpenShift Container Platform web console.
- You have installed the Red Hat OpenShift Pipelines Operator.
- You have enabled monitoring for user-defined projects.
Procedure
For each event listener, create a service monitor. For example, to view the metrics for the
github-listenerevent listener in thetestnamespace, create the following service monitor:apiVersion: monitoring.coreos.com/v1 kind: ServiceMonitor metadata: labels: app.kubernetes.io/managed-by: EventListener app.kubernetes.io/part-of: Triggers eventlistener: github-listener annotations: networkoperator.openshift.io/ignore-errors: "" name: el-monitor namespace: test spec: endpoints: - interval: 10s port: http-metrics jobLabel: name namespaceSelector: matchNames: - test selector: matchLabels: app.kubernetes.io/managed-by: EventListener app.kubernetes.io/part-of: Triggers eventlistener: github-listener ...Test the service monitor by sending a request to the event listener. For example, push an empty commit:
$ git commit -m "empty-commit" --allow-empty && git push origin main-
On the OpenShift Container Platform web console, navigate to Administrator
Observe Metrics. -
To view a metric, search by its name. For example, to view the details of the
eventlistener_http_resourcesmetric for thegithub-listenerevent listener, search using theeventlistener_http_resourceskeyword.
4.6. Managing non-versioned and versioned cluster tasks
As a cluster administrator, installing the Red Hat OpenShift Pipelines Operator creates variants of each default cluster task known as versioned cluster tasks (VCT) and non-versioned cluster tasks (NVCT). For example, installing the Red Hat OpenShift Pipelines Operator v1.7 creates a buildah-1-7-0 VCT and a buildah NVCT.
Both NVCT and VCT have the same metadata, behavior, and specifications, including params, workspaces, and steps. However, they behave differently when you disable them or upgrade the Operator.
4.6.1. Differences between non-versioned and versioned cluster tasks
Non-versioned and versioned cluster tasks have different naming conventions. And, the Red Hat OpenShift Pipelines Operator upgrades them differently.
| Non-versioned cluster task | Versioned cluster task | |
|---|---|---|
| Nomenclature |
The NVCT only contains the name of the cluster task. For example, the name of the NVCT of Buildah installed with Operator v1.7 is |
The VCT contains the name of the cluster task, followed by the version as a suffix. For example, the name of the VCT of Buildah installed with Operator v1.7 is |
| Upgrade | When you upgrade the Operator, it updates the non-versioned cluster task with the latest changes. The name of the NVCT remains unchanged. |
Upgrading the Operator installs the latest version of the VCT and retains the earlier version. The latest version of a VCT corresponds to the upgraded Operator. For example, installing Operator 1.7 installs |
4.6.2. Advantages and disadvantages of non-versioned and versioned cluster tasks
Before adopting non-versioned or versioned cluster tasks as a standard in production environments, cluster administrators might consider their advantages and disadvantages.
| Cluster task | Advantages | Disadvantages |
|---|---|---|
| Non-versioned cluster task (NVCT) |
| If you deploy pipelines that use NVCT, they might break after an Operator upgrade if the automatically upgraded cluster tasks are not backward-compatible. |
| Versioned cluster task (VCT) |
|
|
4.6.3. Disabling non-versioned and versioned cluster tasks
As a cluster administrator, you can disable cluster tasks that the Pipelines Operator installed.
Procedure
To delete all non-versioned cluster tasks and latest versioned cluster tasks, edit the
TektonConfigcustom resource definition (CRD) and set theclusterTasksparameter inspec.addon.paramstofalse.Example
TektonConfigCRapiVersion: operator.tekton.dev/v1alpha1 kind: TektonConfig metadata: name: config spec: params: - name: createRbacResource value: "false" profile: all targetNamespace: openshift-pipelines addon: params: - name: clusterTasks value: "false" ...When you disable cluster tasks, the Operator removes all the non-versioned cluster tasks and only the latest version of the versioned cluster tasks from the cluster.
NoteRe-enabling cluster tasks installs the non-versioned cluster tasks.
Optional: To delete earlier versions of the versioned cluster tasks, use any one of the following methods:
To delete individual earlier versioned cluster tasks, use the
oc delete clustertaskcommand followed by the versioned cluster task name. For example:$ oc delete clustertask buildah-1-6-0To delete all versioned cluster tasks created by an old version of the Operator, you can delete the corresponding installer set. For example:
$ oc delete tektoninstallerset versioned-clustertask-1-6-k98asImportantIf you delete an old versioned cluster task, you cannot restore it. You can only restore versioned and non-versioned cluster tasks that the current version of the Operator has created.
4.7. Using Tekton Hub with OpenShift Pipelines
Tekton Hub is a Technology Preview feature only. Technology Preview features are not supported with Red Hat production service level agreements (SLAs) and might not be functionally complete. Red Hat does not recommend using them in production. These features provide early access to upcoming product features, enabling customers to test functionality and provide feedback during the development process.
For more information about the support scope of Red Hat Technology Preview features, see Technology Preview Features Support Scope.
Tekton Hub helps you discover, search, and share reusable tasks and pipelines for your CI/CD workflows. A public instance of Tekton Hub is available at hub.tekton.dev. Cluster administrators can also install and deploy a custom instance of Tekton Hub for enterprise use.
4.7.1. Installing and deploying Tekton Hub on a OpenShift Container Platform cluster
Tekton Hub is an optional component; cluster administrators cannot install it using the TektonConfig custom resource (CR). To install and manage Tekton Hub, use the TektonHub CR.
If you are using Github Enterprise or Gitlab Enterprise, install and deploy Tekton Hub in the same network as the enterprise server. For example, if the enterprise server is running behind a VPN, deploy Tekton Hub on a cluster that is also behind the VPN.
Prerequisites
-
Ensure that the Red Hat OpenShift Pipelines Operator is installed in the default
openshift-pipelinesnamespace on the cluster.
Procedure
- Create a fork of the Tekton Hub repository.
- Clone the forked repository.
Update the
config.yamlfile to include at least one user with the following scopes:-
A user with
agent:createscope who can set up a cron job that refreshes the Tekton Hub database after an interval, if there are any changes in the catalog. -
A user with the
catalog:refreshscope who can refresh the catalog and all resources in the database of the Tekton Hub. A user with the
config:refreshscope who can get additional scopes.... scopes: - name: agent:create users: <username_registered_with_the_Git_repository_hosting_service_provider> - name: catalog:refresh users: <username_registered_with_the_Git_repository_hosting_service_provider> - name: config:refresh users: <username_registered_with_the_Git_repository_hosting_service_provider> ...The supported service providers are GitHub, GitLab, and BitBucket.
-
A user with
Create an OAuth application with your Git repository hosting provider, and note the Client ID and Client Secret.
-
For a GitHub OAuth application, set the
Homepage URLand theAuthorization callback URLas<auth-route>. -
For a GitLab OAuth application, set the
REDIRECT_URIas<auth-route>/auth/gitlab/callback. -
For a BitBucket OAuth application, set the
Callback URLas<auth-route>.
-
For a GitHub OAuth application, set the
Edit the following fields in the
<tekton_hub_repository>/config/02-api/20-api-secret.yamlfile for the Tekton Hub API secret:-
GH_CLIENT_ID: The Client ID from the OAuth application created with the Git repository hosting service provider. -
GH_CLIENT_SECRET: The Client Secret from the OAuth application created with the Git repository hosting service provider. -
GHE_URL: GitHub Enterprise URL, if you are authenticating using GitHub Enterprise. Do not provide the URL to the catalog as a value for this field. -
GL_CLIENT_ID: The Client ID from the GitLab OAuth application. -
GL_CLIENT_SECRET: The Client Secret from the GitLab OAuth application. -
GLE_URL: GitLab Enterprise URL, if you are authenticating using GitLab Enterprise. Do not provide the URL to the catalog as a value for this field. -
BB_CLIENT_ID: The Client ID from the BitBucket OAuth application. -
BB_CLIENT_SECRET: The Client Secret from the BitBucket OAuth application. -
JWT_SIGNING_KEY: A long, random string used to sign the JSON Web Token (JWT) created for users. -
ACCESS_JWT_EXPIRES_IN: Add the time limit after which the access token expires. For example,1m, wheremdenotes minutes. The supported units of time are seconds (s), minutes (m), hours (h), days (d), and weeks (w). -
REFRESH_JWT_EXPIRES_IN: Add the time limit after which the refresh token expires. For example,1m, wheremdenotes minutes. The supported units of time are seconds (s), minutes (m), hours (h), days (d), and weeks (w). Ensure that the expiry time set for token refresh is greater than the expiry time set for token access. AUTH_BASE_URL: Route URL for the OAuth application.Note- Use the fields related to Client ID and Client Secret for any one of the supported Git repository hosting service providers.
-
The account credentials registered with the Git repository hosting service provider enables the users with
catalog: refreshscope to authenticate and load all catalog resources to the database.
-
- Commit and push the changes to your forked repository.
Ensure that the
TektonHubCR is similar to the following example:apiVersion: operator.tekton.dev/v1alpha1 kind: TektonHub metadata: name: hub spec: targetNamespace: openshift-pipelines1 api: hubConfigUrl: https://raw.githubusercontent.com/tektoncd/hub/main/config.yaml2 Install the Tekton Hub.
$ oc apply -f TektonHub.yaml1 - 1
- The file name or path of the
TektonConfigCR.
Check the status of the installation.
$ oc get tektonhub.operator.tekton.dev NAME VERSION READY REASON APIURL UIURL hub v1.7.2 True https://api.route.url/ https://ui.route.url/
4.7.1.1. Manually refreshing the catalog in Tekton Hub
When you install and deploy Tekton Hub on a OpenShift Container Platform cluster, a Postgres database is also installed. Initially, the database is empty. To add the tasks and pipelines available in the catalog to the database, cluster administrators must refresh the catalog.
Prerequisites
-
Ensure that you are in the
<tekton_hub_repository>/config/directory.
Procedure
In the Tekton Hub UI, click Login -→ Sign In With GitHub.
NoteGitHub is used as an example from the publicly available Tekton Hub UI. For custom installation on your cluster, all Git repository hosting service providers for which you have provided Client ID and Client Secret are listed.
- On the home page, click the user profile and copy the token.
Call the Catalog Refresh API.
To refresh a catalog with a specific name, run the following command:
$ curl -X POST -H "Authorization: <jwt-token>" \1 <api-url>/catalog/<catalog_name>/refresh2 Sample output:
[{"id":1,"catalogName":"tekton","status":"queued"}]To refresh all catalogs, run the following command:
$ curl -X POST -H "Authorization: <jwt-token>" \1 <api-url>/catalog/refresh2
- Refresh the page in the browser.
4.7.1.2. Optional: Setting a cron job for refreshing catalog in Tekton Hub
Cluster administrators can optionally set up a cron job to refresh the database after a fixed interval, so that changes in the catalog appear in the Tekton Hub web console.
If resources are added to the catalog or updated, refreshing the catalog displays these changes in the Tekton Hub UI. However, if a resource is deleted from the catalog, refreshing the catalog does not remove the resource from the database. The Tekton Hub UI continues displaying the deleted resource.
Prerequisites
-
Ensure that you are in the
<project_root>/config/directory, where<project_root>is the top level directory of the cloned Tekton Hub repository. - Ensure that you have a JSON web token (JWT) token with a scope of refreshing the catalog.
Procedure
Create an agent-based JWT token for longer use.
$ curl -X PUT --header "Content-Type: application/json" \ -H "Authorization: <access-token>" \1 --data '{"name":"catalog-refresh-agent","scopes": ["catalog:refresh"]}' \ <api-route>/system/user/agent- 1
- The JWT token.
The agent token with the necessary scopes are returned in the
{"token":"<agent_jwt_token>"}format. Note the returned token and preserve it for the catalog refresh cron job.Edit the
05-catalog-refresh-cj/50-catalog-refresh-secret.yamlfile to set theHUB_TOKENparameter to the<agent_jwt_token>returned in the previous step.apiVersion: v1 kind: Secret metadata: name: catalog-refresh type: Opaque stringData: HUB_TOKEN: <hub_token>1 - 1
- The
<agent_jwt_token>returned in the previous step.
Apply the modified YAML files.
$ oc apply -f 05-catalog-refresh-cj/ -n openshift-pipelines.Optional: By default, the cron job is configured to run every 30 minutes. To change the interval, modify the value of the
scheduleparameter in the05-catalog-refresh-cj/51-catalog-refresh-cronjob.yamlfile.apiVersion: batch/v1 kind: CronJob metadata: name: catalog-refresh labels: app: tekton-hub-api spec: schedule: "*/30 * * * *" ...
4.7.1.3. Optional: Adding new users in Tekton Hub configuration
Procedure
Depending on the intended scope, cluster administrators can add new users in the
config.yamlfile.... scopes: - name: agent:create users: [<username_1>, <username_2>]1 - name: catalog:refresh users: [<username_3>, <username_4>] - name: config:refresh users: [<username_5>, <username_6>] default: scopes: - rating:read - rating:write ...- 1
- The usernames registered with the Git repository hosting service provider.
NoteWhen any user logs in for the first time, they will have only the default scope even if they are added in the
config.yaml. To activate additional scopes, ensure the user has logged in at least once.-
Ensure that in the
config.yamlfile, you have theconfig-refreshscope. Refresh the configuration.
$ curl -X POST -H "Authorization: <access-token>" \1 --header "Content-Type: application/json" \ --data '{"force": true} \ <api-route>/system/config/refresh- 1
- The JWT token.
4.7.2. Opting out of Tekton Hub in the Developer perspective
Cluster administrators can opt out of displaying Tekton Hub resources, such as tasks and pipelines, in the Pipeline builder page of the Developer perspective of an OpenShift Container Platform cluster.
Prerequisite
-
Ensure that the Red Hat OpenShift Pipelines Operator is installed on the cluster, and the
occommand line tool is available.
Procedure
To opt of displaying Tekton Hub resources in the Developer perspective, set the value of the
enable-devconsole-integrationfield in theTektonConfigcustom resource (CR) tofalse.apiVersion: operator.tekton.dev/v1alpha1 kind: TektonConfig metadata: name: config spec: targetNamespace: openshift-pipelines ... hub: params: - name: enable-devconsole-integration value: "false" ...By default, the
TektonConfigCR does not include theenable-devconsole-integrationfield, and the Red Hat OpenShift Pipelines Operator assumes that the value istrue.
4.8. Using Pipelines as Code
Pipelines as Code is a Technology Preview feature only. Technology Preview features are not supported with Red Hat production service level agreements (SLAs) and might not be functionally complete. Red Hat does not recommend using them in production. These features provide early access to upcoming product features, enabling customers to test functionality and provide feedback during the development process.
For more information about the support scope of Red Hat Technology Preview features, see Technology Preview Features Support Scope.
With Pipelines as Code, cluster administrators and users with the required privileges can define pipeline templates as part of source code Git repositories. When triggered by a source code push or a pull request for the configured Git repository, the feature runs the pipeline and reports the status.
4.8.1. Key features
Pipelines as Code supports the following features:
- Pull request status and control on the platform hosting the Git repository.
- GitHub Checks API to set the status of a pipeline run, including rechecks.
- GitHub pull request and commit events.
-
Pull request actions in comments, such as
/retest. - Git events filtering and a separate pipeline for each event.
- Automatic task resolution in Pipelines, including local tasks, Tekton Hub, and remote URLs.
- Retrieval of configurations using GitHub blobs and objects API.
-
Access Control List (ACL) over a GitHub organization, or using a Prow style
OWNERfile. -
The
tkn-pacCLI plugin for managing bootstrapping and Pipelines as Code repositories. - Support for GitHub App, GitHub Webhook, Bitbucket Server, and Bitbucket Cloud.
4.8.2. Installing Pipelines as Code on an OpenShift Container Platform
Pipelines as Code is installed by default when you install the Red Hat OpenShift Pipelines Operator. If you are using Pipelines 1.7 or later versions, skip the procedure for manual installation of Pipelines as Code.
However, if you want to disable the default installation of Pipelines as Code with the Red Hat OpenShift Pipelines Operator, set the value of the enablePipelinesAsCode field as false in the TektonConfig custom resource.
...
spec:
addon:
enablePipelinesAsCode: false
...
To install Pipelines as Code using the Operator, set the value of the enablePipelinesAsCode field to true.
Procedure
To manually install Pipelines as Code on a OpenShift Container Platform cluster instead of the default installation with the Red Hat OpenShift Pipelines Operator, run the following command:
$ VERSION=0.5.4 $ oc apply -f https://raw.githubusercontent.com/openshift-pipelines/pipelines-as-code/release-$VERSION/release-$VERSION.yamlNoteFor the latest stable version, check the release page. In addition, check the Red Hat OpenShift Pipelines release notes to ensure that the Pipelines as Code version is compatible with the Red Hat OpenShift Pipelines version.
This command installs Pipelines as Code in the
pipelines-as-codenamespace and creates user roles and the route URL for the Pipelines as Code event listener.Note the route URL for the Pipelines as Code controller created on the cluster:
$ echo https://$(oc get route -n pipelines-as-code el-pipelines-as-code-interceptor -o jsonpath='{.spec.host}')This URL will be needed later when you configure the Git repository hosting service provider.
(Optional) To allow non-administrative users to create repository custom resource definitions (CRDs) in their respective namespaces, create a
RoleBindingobject with the nameopenshift-pipeline-as-code-clusterrolein the namespace. For example, to allow a user to create a repository CRD in theuser-cinamespace, run the following command:$ oc adm policy add-role-to-user openshift-pipeline-as-code-clusterrole user -n user-ciAlternatively, apply the following YAML file using the
oc apply -f <RoleBinding.yaml>command:apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: openshift-pipeline-as-code-clusterrole namespace: user-ci roleRef: apiGroup: rbac.authorization.k8s.io kind: ClusterRole name: openshift-pipeline-as-code-clusterrole subjects: - apiGroup: rbac.authorization.k8s.io kind: User name: user
4.8.3. Installing Pipelines as Code CLI
Cluster administrators can use the tkn-pac CLI tool on local machines or as containers for testing. The tkn-pac CLI tool is installed automatically when you install the tkn CLI for Red Hat OpenShift Pipelines.
You can also install the tkn-pac tkn-pac version 0.23.1 binaries for the supported platforms:
- Linux (x86_64, amd64)
- Linux on IBM Z and LinuxONE (s390x)
- Linux on IBM Power Systems (ppc64le)
- Mac
- Note
The binaries are compatible with
tknversion0.23.1.
4.8.4. Configuring Pipelines as Code for a Git repository hosting service provider
After installing Pipelines as Code, cluster administrators can configure a Git repository hosting service provider. Currently, the following services are supported:
- Github App
- Github Webhook
- Bitbucket Server
- Bitbucket Cloud
GitHub App is the recommended service for using Pipelines as Code.
4.8.4.1. Configuring Pipelines as Code for a GitHub App
GitHub Apps act as a point of integration with Red Hat OpenShift Pipelines and bring the advantage of Git-based workflows to OpenShift Pipelines. Cluster administrators can configure a single GitHub App for all cluster users. For GitHub Apps to work with Pipelines as Code, ensure that the webhook of the GitHub App points to the Pipelines as Code event listener route (or ingress endpoint) that listens for GitHub events.
4.8.4.1.1. Configuring a GitHub App
Cluster administrators can create a GitHub App by running the following command:
$ tkn pac bootstrap github-app
If the tkn pac CLI plugin is not installed, you can create the GitHub App manually.
Procedure
To create and configure a GitHub App manually for Pipelines as Code, perform the following steps:
- Sign in to your GitHub account.
- Go to Settings -→ Developer settings -→ GitHub Apps, and click New GitHub App.
Provide the following information in the GitHub App form:
-
GitHub Application Name:
OpenShift Pipelines - Homepage URL: OpenShift Console URL
Webhook URL: The Pipelines as Code route or ingress URL. You can find it by executing the command
echo https://$(oc get route -n pipelines-as-code el-pipelines-as-code-interceptor -o jsonpath='{.spec.host}').NoteFor Pipelines as Code installated by default using the Red Hat OpenShift Pipelines Operator, use the
openshift-pipelinesnamespace instead ofpipelines-as-code.-
Webhook secret: An arbitrary secret. You can generate a secret by executing the command
openssl rand -hex 20.
-
GitHub Application Name:
Select the following Repository permissions:
-
Checks:
Read & Write -
Contents:
Read & Write -
Issues:
Read & Write -
Metadata:
Read-only -
Pull request:
Read & Write
-
Checks:
Select the following Organization permissions:
-
Members:
Readonly -
Plan:
Readonly
-
Members:
Select the following User permissions:
- Commit comment
- Issue comment
- Pull request
- Pull request review
- Pull request review comment
- Push
- Click Create GitHub App.
- On the Details page of the newly created GitHub App, note the App ID displayed at the top.
- In the Private keys section, click Generate Private key to automatically generate and download a private key for the GitHub app. Securely store the private key for future reference and usage.
4.8.4.1.2. Configuring Pipelines as Code to access a GitHub App
To configure Pipelines as Code to access the newly created GitHub App, execute the following command:
+
$ oc -n <pipelines-as-code> create secret generic pipelines-as-code-secret \
--from-literal github-private-key="$(cat <PATH_PRIVATE_KEY>)" \
--from-literal github-application-id="<APP_ID>" \
--from-literal webhook.secret="<WEBHOOK_SECRET>" - 1
- For Pipelines as Code installated by default using the Red Hat OpenShift Pipelines Operator, use the
openshift-pipelinesnamespace instead ofpipelines-as-code. - 2
- The path to the private key you downloaded while configuring the GitHub App.
- 3
- The App ID of the GitHub App.
- 4
- The webhook secret provided when you created the GitHub App.
Pipelines as Code works automatically with GitHub Enterprise by detecting the header set from GitHub Enterprise and using it for the GitHub Enterprise API authorization URL.
4.8.5. Pipelines as Code command reference
The tkn-pac CLI tool offers the following capabilities:
- Bootstrap Pipelines as Code installation and configuration.
- Create a new Pipelines as Code repository.
- List all Pipelines as Code repositories.
- Describe a Pipelines as Code repository and the associated runs.
- Generate a simple pipeline run to get started.
- Resolve a pipeline run as if it was executed by Pipelines as Code.
You can use the commands corresponding to the capabilities for testing and experimentation, so that you don’t have to make changes to the Git repository containing the application source code.
4.8.5.1. Basic syntax
$ tkn pac [command or options] [arguments]4.8.5.2. Global options
$ tkn pac --help4.8.5.3. Utility commands
4.8.5.3.1. bootstrap
| Command | Description |
|---|---|
|
| Installs and configures Pipelines as Code for Git repository hosting service providers, such as GitHub and GitHub Enterprise. |
|
| Installs the nightly build of Pipelines as Code. |
|
| Overrides the OpenShift route URL.
By default, If you do not have an OpenShift Container Platform cluster, it asks you for the public URL that points to the ingress endpoint. |
|
|
Create a GitHub application and secrets in the |
4.8.5.3.2. repository
| Command | Description |
|---|---|
|
| Creates a new Pipelines as Code repository and a namespace based on the pipeline run template. |
|
| Lists all the Pipelines as Code repositories and displays the last status of the associated runs. |
|
| Describes a Pipelines as Code repository and the associated runs. |
4.8.5.3.3. generate
| Command | Description |
|---|---|
|
| Generates a simple pipeline run. When executed from the directory containing the source code, it automatically detects current Git information. In addition, it uses basic language detection capability and adds extra tasks depending on the language.
For example, if it detects a |
4.8.5.3.4. resolve
| Command | Description |
|---|---|
|
| Executes a pipeline run as if it is owned by the Pipelines as Code on service. |
|
|
Displays the status of a live pipeline run that uses the template in Combined with a Kubernetes installation running on your local machine, you can observe the pipeline run without generating a new commit. If you run the command from a source code repository, it attempts to detect the current Git information and automatically resolve parameters such as current revision or branch. |
|
| Executes a pipeline run by overriding default parameter values derived from the Git repository.
The
You can override the default information gathered from the Git repository by specifying parameter values using the |
4.8.6. Customizing Pipelines as Code configuration
To customize Pipelines as Code, cluster administrators can configure the following parameters using the pipelines-as-code config map in the pipelines-as-code namespace:
| Parameter | Description | Default |
|---|---|---|
|
| The name of the application. For example, the name displayed in the GitHub Checks labels. |
|
|
|
The number of the days for which the executed pipeline runs are kept in the Note that this configmap setting does not affect the cleanups of a user’s pipeline runs, which are controlled by the annotations on the pipeline run definition in the user’s GitHub repository. | |
|
| Indicates whether or not a secret should be automatically created using the token generated in the GitHub application. This secret can then be used with private repositories. |
|
|
| When enabled, allows remote tasks from pipeline run annotations. |
|
|
| The base URL for the Tekton Hub API. |
4.9. Working with Red Hat OpenShift Pipelines using the Developer perspective
You can use the Developer perspective of the OpenShift Container Platform web console to create CI/CD pipelines for your software delivery process.
In the Developer perspective:
-
Use the Add
Pipeline Pipeline builder option to create customized pipelines for your application. -
Use the Add
From Git option to create pipelines using operator-installed pipeline templates and resources while creating an application on OpenShift Container Platform.
After you create the pipelines for your application, you can view and visually interact with the deployed pipelines in the Pipelines view. You can also use the Topology view to interact with the pipelines created using the From Git option. You must apply custom labels to pipelines created using the Pipeline builder to see them in the Topology view.
Prerequisites
- You have access to an OpenShift Container Platform cluster and have switched to the Developer perspective.
- You have the OpenShift Pipelines Operator installed in your cluster.
- You are a cluster administrator or a user with create and edit permissions.
- You have created a project.
4.9.1. Constructing Pipelines using the Pipeline builder
In the Developer perspective of the console, you can use the +Add
- Configure pipelines using either the Pipeline builder or the YAML view.
- Construct a pipeline flow using existing tasks and cluster tasks. When you install the OpenShift Pipelines Operator, it adds reusable pipeline cluster tasks to your cluster.
- Specify the type of resources required for the pipeline run, and if required, add additional parameters to the pipeline.
- Reference these pipeline resources in each of the tasks in the pipeline as input and output resources.
- If required, reference any additional parameters added to the pipeline in the task. The parameters for a task are prepopulated based on the specifications of the task.
- Use the Operator-installed, reusable snippets and samples to create detailed pipelines.
Procedure
- In the +Add view of the Developer perspective, click the Pipeline tile to see the Pipeline builder page.
Configure the pipeline using either the Pipeline builder view or the YAML view.
NoteThe Pipeline builder view supports a limited number of fields whereas the YAML view supports all available fields. Optionally, you can also use the Operator-installed, reusable snippets and samples to create detailed Pipelines.
Figure 4.1. YAML view

Configure your pipeline by using Pipeline builder:
- In the Name field, enter a unique name for the pipeline.
In the Tasks section:
- Click Add task.
- Search for a task using the quick search field and select the required task from the displayed list.
Click Add or Install and add. In this example, use the s2i-nodejs task.
NoteThe search list contains all the Tekton Hub tasks and tasks available in the cluster. Also, if a task is already installed it will show Add to add the task whereas it will show Install and add to install and add the task. It will show Update and add when you add the same task with an updated version.
To add sequential tasks to the pipeline:
-
Click the plus icon to the right or left of the task
click Add task. - Search for a task using the quick search field and select the required task from the displayed list.
Click Add or Install and add.
Figure 4.2. Pipeline builder
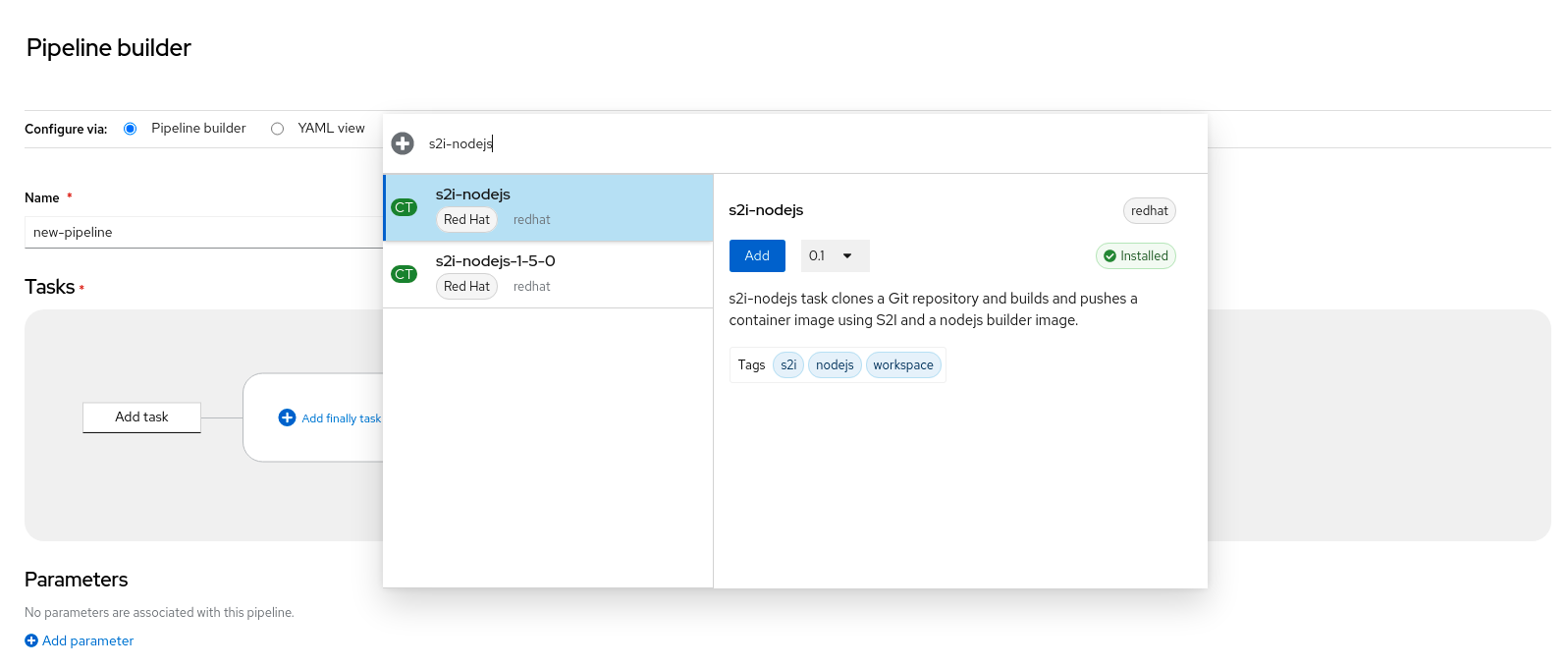
-
Click the plus icon to the right or left of the task
To add a final task:
-
Click the Add finally task
Click Add task. - Search for a task using the quick search field and select the required task from the displayed list.
- Click Add or Install and add.
-
Click the Add finally task
In the Resources section, click Add Resources to specify the name and type of resources for the pipeline run. These resources are then used by the tasks in the pipeline as inputs and outputs. For this example:
-
Add an input resource. In the Name field, enter
Source, and then from the Resource Type drop-down list, select Git. Add an output resource. In the Name field, enter
Img, and then from the Resource Type drop-down list, select Image.NoteA red icon appears next to the task if a resource is missing.
-
Add an input resource. In the Name field, enter
- Optional: The Parameters for a task are pre-populated based on the specifications of the task. If required, use the Add Parameters link in the Parameters section to add additional parameters.
- In the Workspaces section, click Add workspace and enter a unique workspace name in the Name field. You can add multiple workspaces to the pipeline.
In the Tasks section, click the s2i-nodejs task to see the side panel with details for the task. In the task side panel, specify the resources and parameters for the s2i-nodejs task:
- If required, in the Parameters section, add more parameters to the default ones, by using the $(params.<param-name>) syntax.
-
In the Image section, enter
Imgas specified in the Resources section. - Select a workspace from the source drop-down under Workspaces section.
- Add resources, parameters, and workspaces to the openshift-client task.
- Click Create to create and view the pipeline in the Pipeline Details page.
- Click the Actions drop-down menu then click Start, to see the Start Pipeline page.
- The Workspaces section lists the workspaces you created earlier. Use the respective drop-down to specify the volume source for your workspace. You have the following options: Empty Directory, Config Map, Secret, PersistentVolumeClaim, or VolumeClaimTemplate.
4.9.2. Creating applications with OpenShift Pipelines
To create pipelines along with applications, use the From Git option in the Add view of the Developer perspective. For more information, see Creating applications using the Developer perspective.
4.9.3. Interacting with pipelines using the Developer perspective
The Pipelines view in the Developer perspective lists all the pipelines in a project, along with the following details:
- The namespace in which the pipeline was created
- The last pipeline run
- The status of the tasks in the pipeline run
- The status of the pipeline run
- The creation time of the last pipeline run
Procedure
- In the Pipelines view of the Developer perspective, select a project from the Project drop-down list to see the pipelines in that project.
Click the required pipeline to see the Pipeline details page.
By default, the Details tab displays a visual representation of all the all the serial tasks, parallel tasks,
finallytasks, and when expressions in the pipeline. The tasks and thefinallytasks are listed in the lower right portion of the page. Click the listed Tasks and Finally tasks to view the task details.Figure 4.3. Pipeline details
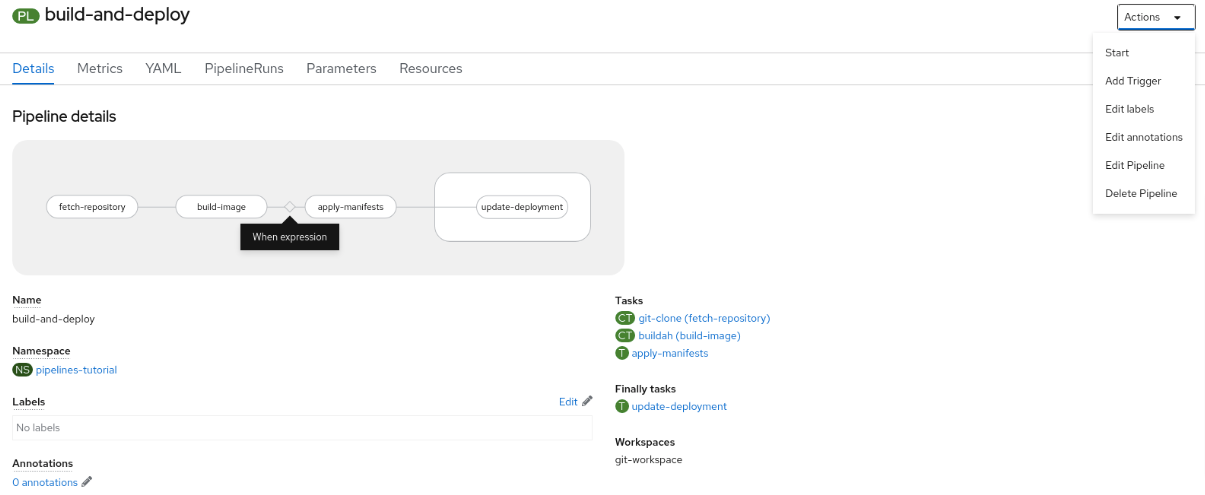
Optional: On the Pipeline details page, click the Metrics tab to see the following information about pipelines:
- Pipeline Success Ratio
- Number of Pipeline Runs
- Pipeline Run Duration
Task Run Duration
You can use this information to improve the pipeline workflow and eliminate issues early in the pipeline lifecycle.
- Optional: Click the YAML tab to edit the YAML file for the pipeline.
Optional: Click the Pipeline Runs tab to see the completed, running, or failed runs for the pipeline.
The Pipeline Runs tab provides details about the pipeline run, the status of the task, and a link to debug failed pipeline runs. Use the Options menu
 to stop a running pipeline, to rerun a pipeline using the same parameters and resources as that of the previous pipeline execution, or to delete a pipeline run.
to stop a running pipeline, to rerun a pipeline using the same parameters and resources as that of the previous pipeline execution, or to delete a pipeline run.
Click the required pipeline run to see the Pipeline Run details page. By default, the Details tab displays a visual representation of all the serial tasks, parallel tasks,
finallytasks, and when expressions in the pipeline run. The results for successful runs are displayed under the Pipeline Run results pane at the bottom of the page.NoteThe Details section of the Pipeline Run Details page displays a Log Snippet of the failed pipeline run. Log Snippet provides a general error message and a snippet of the log. A link to the Logs section provides quick access to the details about the failed run.
On the Pipeline Run details page, click the Task Runs tab to see the completed, running, and failed runs for the task.
The Task Runs tab provides information about the task run along with the links to its task and pod, and also the status and duration of the task run. Use the Options menu
 to delete a task run.
to delete a task run.
Click the required task run to see the Task Run details page. The results for successful runs are displayed under the Task Run results pane at the bottom of the page.
NoteThe Details section of the Task Run details page displays a Log Snippet of the failed task run. Log Snippet provides a general error message and a snippet of the log. A link to the Logs section provides quick access to the details about the failed task run.
- Click the Parameters tab to see the parameters defined in the pipeline. You can also add or edit additional parameters, as required.
- Click the Resources tab to see the resources defined in the pipeline. You can also add or edit additional resources, as required.
4.9.4. Using a custom pipeline template for creating and deploying an application from a Git repository
As a cluster administrator, to create and deploy an application from a Git repository, you can use custom pipeline templates that override the default pipeline templates provided by Red Hat OpenShift Pipelines 1.5 and later.
This feature is unavailable in Red Hat OpenShift Pipelines 1.4 and earlier versions.
Prerequisites
Ensure that the Red Hat OpenShift Pipelines 1.5 or later is installed and available in all namespaces.
Procedure
- Log in to the OpenShift Container Platform web console as a cluster administrator.
In the Administrator perspective, use the left navigation panel to go to the Pipelines section.
-
From the Project drop-down, select the openshift project. This ensures that the subsequent steps are performed in the
openshiftnamespace. From the list of available pipelines, select a pipeline that is appropriate for building and deploying your application. For example, if your application requires a
node.jsruntime environment, select the s2i-nodejs pipeline.NoteDo not edit the default pipeline template. It may become incompatible with the UI and the back-end.
- Under the YAML tab of the selected pipeline, click Download and save the YAML file to your local machine. If your custom configuration file fails, you can use this copy to restore a working configuration.
-
From the Project drop-down, select the openshift project. This ensures that the subsequent steps are performed in the
Disable (delete) the default pipeline templates:
-
Use the left navigation panel to go to Operators
Installed Operators. -
Click Red Hat OpenShift Pipelines
Tekton Configuration tab config YAML tab. To disable (delete) the default pipeline templates in the
openshiftnamespace, set thepipelineTemplatesparameter tofalsein theTektonConfigcustom resource YAML, and save it.apiVersion: operator.tekton.dev/v1alpha1 kind: TektonConfig metadata: name: config spec: profile: all targetNamespace: openshift-pipelines addon: params: - name: clusterTasks value: "true" - name: pipelineTemplates value: "false" ...NoteIf you manually delete the default pipeline templates, the Operator restores the defaults during an upgrade.
WarningAs a cluster admin, you can disable the installation of the default pipeline templates in the Operator configuration. However, such a configuration deletes all default pipeline templates, not just the one you want to customize.
-
Use the left navigation panel to go to Operators
Create a custom pipeline template:
- Use the left navigation panel to go to the Pipelines section.
- From the Create drop-down, select Pipeline.
Create the required pipeline in the
openshiftnamespace. Give it a different name than the default one (for example,custom-nodejs). You can use the downloaded default pipeline template as a starting point and customize it.NoteBecause
openshiftis the default namespace used by the operator-installed pipeline templates, you must create the custom pipeline template in theopenshiftnamespace. When an application uses a pipeline template, the template is automatically copied to the respective project’s namespace.Under the Details tab of the created pipeline, ensure that the Labels in the custom template match the labels in the default pipeline. The custom pipeline template must have the correct labels for the runtime, type, and strategy of the application. For example, the required labels for a
node.jsapplication deployed on OpenShift Container Platform are as follows:... pipeline.openshift.io/runtime: nodejs pipeline.openshift.io/type: openshift ...NoteYou can use only one pipeline template for each combination of runtime environment and deployment type.
-
In the Developer perspective, use the +Add
Git Repository From Git option to select the kind of application you want to create and deploy. Based on the required runtime and type of the application, your custom template is automatically selected.
4.9.5. Starting pipelines
After you create a pipeline, you need to start it to execute the included tasks in the defined sequence. You can start a pipeline from the Pipelines view, the Pipeline Details page, or the Topology view.
Procedure
To start a pipeline using the Pipelines view:
-
In the Pipelines view of the Developer perspective, click the Options
 menu adjoining a pipeline, and select Start.
menu adjoining a pipeline, and select Start.
The Start Pipeline dialog box displays the Git Resources and the Image Resources based on the pipeline definition.
NoteFor pipelines created using the From Git option, the Start Pipeline dialog box also displays an
APP_NAMEfield in the Parameters section, and all the fields in the dialog box are prepopulated by the pipeline template.- If you have resources in your namespace, the Git Resources and the Image Resources fields are prepopulated with those resources. If required, use the drop-downs to select or create the required resources and customize the pipeline run instance.
Optional: Modify the Advanced Options to add the credentials that authenticate the specified private Git server or the image registry.
- Under Advanced Options, click Show Credentials Options and select Add Secret.
In the Create Source Secret section, specify the following:
- A unique Secret Name for the secret.
- In the Designated provider to be authenticated section, specify the provider to be authenticated in the Access to field, and the base Server URL.
Select the Authentication Type and provide the credentials:
For the Authentication Type
Image Registry Credentials, specify the Registry Server Address that you want to authenticate, and provide your credentials in the Username, Password, and Email fields.Select Add Credentials if you want to specify an additional Registry Server Address.
-
For the Authentication Type
Basic Authentication, specify the values for the UserName and Password or Token fields. For the Authentication Type
SSH Keys, specify the value of the SSH Private Key field.NoteFor basic authentication and SSH authentication, you can use annotations such as:
-
tekton.dev/git-0: https://github.com -
tekton.dev/git-1: https://gitlab.com.
-
- Select the check mark to add the secret.
You can add multiple secrets based upon the number of resources in your pipeline.
- Click Start to start the pipeline.
The Pipeline Run Details page displays the pipeline being executed. After the pipeline starts, the tasks and steps within each task are executed. You can:
- Hover over the tasks to see the time taken to execute each step.
- Click on a task to see the logs for each step in the task.
- Click the Logs tab to see the logs relating to the execution sequence of the tasks. You can also expand the pane and download the logs individually or in bulk, by using the relevant button.
Click the Events tab to see the stream of events generated by a pipeline run.
You can use the Task Runs, Logs, and Events tabs to assist in debugging a failed pipeline run or a failed task run.
Figure 4.4. Pipeline run details
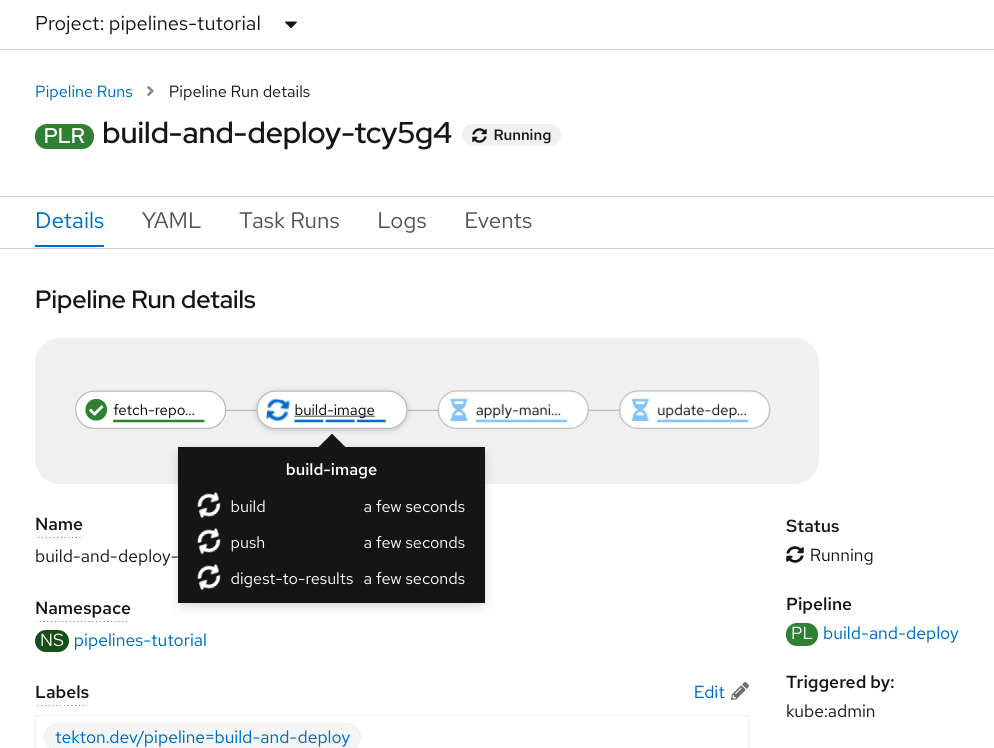
For pipelines created using the From Git option, you can use the Topology view to interact with pipelines after you start them:
NoteTo see the pipelines created using the Pipeline Builder in the Topology view, customize the pipeline labels to link the pipeline with the application workload.
- On the left navigation panel, click Topology, and click on the application to see the pipeline runs listed in the side panel.
In the Pipeline Runs section, click Start Last Run to start a new pipeline run with the same parameters and resources as the previous one. This option is disabled if a pipeline run has not been initiated.
Figure 4.5. Pipelines in Topology view

In the Topology page, hover to the left of the application to see the status of the pipeline run for the application.
NoteThe side panel of the application node in the Topology page displays a Log Snippet when a pipeline run fails on a specific task run. You can view the Log Snippet in the Pipeline Runs section, under the Resources tab. Log Snippet provides a general error message and a snippet of the log. A link to the Logs section provides quick access to the details about the failed run.
4.9.6. Editing Pipelines
You can edit the Pipelines in your cluster using the Developer perspective of the web console:
Procedure
- In the Pipelines view of the Developer perspective, select the Pipeline you want to edit to see the details of the Pipeline. In the Pipeline Details page, click Actions and select Edit Pipeline.
On the Pipeline builder page, you can perform the following tasks:
- Add additional Tasks, parameters, or resources to the Pipeline.
- Click the Task you want to modify to see the Task details in the side panel and modify the required Task details, such as the display name, parameters, and resources.
- Alternatively, to delete the Task, click the Task, and in the side panel, click Actions and select Remove Task.
- Click Save to save the modified Pipeline.
4.9.7. Deleting Pipelines
You can delete the Pipelines in your cluster using the Developer perspective of the web console.
Procedure
-
In the Pipelines view of the Developer perspective, click the Options
 menu adjoining a Pipeline, and select Delete Pipeline.
menu adjoining a Pipeline, and select Delete Pipeline.
- In the Delete Pipeline confirmation prompt, click Delete to confirm the deletion.
4.10. Reducing resource consumption of OpenShift Pipelines
If you use clusters in multi-tenant environments you must control the consumption of CPU, memory, and storage resources for each project and Kubernetes object. This helps prevent any one application from consuming too many resources and affecting other applications.
To define the final resource limits that are set on the resulting pods, Red Hat OpenShift Pipelines use resource quota limits and limit ranges of the project in which they are executed.
To restrict resource consumption in your project, you can:
- Set and manage resource quotas to limit the aggregate resource consumption.
- Use limit ranges to restrict resource consumption for specific objects, such as pods, images, image streams, and persistent volume claims.
4.10.1. Understanding resource consumption in pipelines
Each task consists of a number of required steps to be executed in a particular order defined in the steps field of the Task resource. Every task runs as a pod, and each step runs as a container within that pod.
Steps are executed one at a time. The pod that executes the task only requests enough resources to run a single container image (step) in the task at a time, and thus does not store resources for all the steps in the task.
The Resources field in the steps spec specifies the limits for resource consumption. By default, the resource requests for the CPU, memory, and ephemeral storage are set to BestEffort (zero) values or to the minimums set through limit ranges in that project.
Example configuration of resource requests and limits for a step
spec:
steps:
- name: <step_name>
resources:
requests:
memory: 2Gi
cpu: 600m
limits:
memory: 4Gi
cpu: 900m
When the LimitRange parameter and the minimum values for container resource requests are specified in the project in which the pipeline and task runs are executed, Red Hat OpenShift Pipelines looks at all the LimitRange values in the project and uses the minimum values instead of zero.
Example configuration of limit range parameters at a project level
apiVersion: v1
kind: LimitRange
metadata:
name: <limit_container_resource>
spec:
limits:
- max:
cpu: "600m"
memory: "2Gi"
min:
cpu: "200m"
memory: "100Mi"
default:
cpu: "500m"
memory: "800Mi"
defaultRequest:
cpu: "100m"
memory: "100Mi"
type: Container
...4.10.2. Mitigating extra resource consumption in pipelines
When you have resource limits set on the containers in your pod, OpenShift Container Platform sums up the resource limits requested as all containers run simultaneously.
To consume the minimum amount of resources needed to execute one step at a time in the invoked task, Red Hat OpenShift Pipelines requests the maximum CPU, memory, and ephemeral storage as specified in the step that requires the most amount of resources. This ensures that the resource requirements of all the steps are met. Requests other than the maximum values are set to zero.
However, this behavior can lead to higher resource usage than required. If you use resource quotas, this could also lead to unschedulable pods.
For example, consider a task with two steps that uses scripts, and that does not define any resource limits and requests. The resulting pod has two init containers (one for entrypoint copy, the other for writing scripts) and two containers, one for each step.
OpenShift Container Platform uses the limit range set up for the project to compute required resource requests and limits. For this example, set the following limit range in the project:
apiVersion: v1
kind: LimitRange
metadata:
name: mem-min-max-demo-lr
spec:
limits:
- max:
memory: 1Gi
min:
memory: 500Mi
type: ContainerIn this scenario, each init container uses a request memory of 1Gi (the max limit of the limit range), and each container uses a request memory of 500Mi. Thus, the total memory request for the pod is 2Gi.
If the same limit range is used with a task of ten steps, the final memory request is 5Gi, which is higher than what each step actually needs, that is 500Mi (since each step runs after the other).
Thus, to reduce resource consumption of resources, you can:
- Reduce the number of steps in a given task by grouping different steps into one bigger step, using the script feature, and the same image. This reduces the minimum requested resource.
- Distribute steps that are relatively independent of each other and can run on their own to multiple tasks instead of a single task. This lowers the number of steps in each task, making the request for each task smaller, and the scheduler can then run them when the resources are available.
4.11. Setting compute resource quota for OpenShift Pipelines
A ResourceQuota object in Red Hat OpenShift Pipelines controls the total resource consumption per namespace. You can use it to limit the quantity of objects created in a namespace, based on the type of the object. In addition, you can specify a compute resource quota to restrict the total amount of compute resources consumed in a namespace.
However, you might want to limit the amount of compute resources consumed by pods resulting from a pipeline run, rather than setting quotas for the entire namespace. Currently, Red Hat OpenShift Pipelines does not enable you to directly specify the compute resource quota for a pipeline.
4.11.1. Alternative approaches for limiting compute resource consumption in OpenShift Pipelines
To attain some degree of control over the usage of compute resources by a pipeline, consider the following alternative approaches:
Set resource requests and limits for each step in a task.
Example: Set resource requests and limits for each step in a task.
... spec: steps: - name: step-with-limts resources: requests: memory: 1Gi cpu: 500m limits: memory: 2Gi cpu: 800m ...-
Set resource limits by specifying values for the
LimitRangeobject. For more information onLimitRange, refer to Restrict resource consumption with limit ranges. - Reduce pipeline resource consumption.
- Set and manage resource quotas per project.
- Ideally, the compute resource quota for a pipeline should be same as the total amount of compute resources consumed by the concurrently running pods in a pipeline run. However, the pods running the tasks consume compute resources based on the use case. For example, a Maven build task might require different compute resources for different applications that it builds. As a result, you cannot predetermine the compute resource quotas for tasks in a generic pipeline. For greater predictability and control over usage of compute resources, use customized pipelines for different applications.
When using Red Hat OpenShift Pipelines in a namespace configured with a ResourceQuota object, the pods resulting from task runs and pipeline runs might fail with an error, such as: failed quota: <quota name> must specify cpu, memory.
To avoid this error, do any one of the following:
- (Recommended) Specify a limit range for the namespace.
- Explicitly define requests and limits for all containers.
For more information, refer to the issue and the resolution.
If your use case is not addressed by these approaches, you can implement a workaround by using a resource quota for a priority class.
4.11.2. Specifying pipelines resource quota using priority class
A PriorityClass object maps priority class names to the integer values that indicates their relative priorities. Higher values increase the priority of a class. After you create a priority class, you can create pods that specify the priority class name in their specifications. In addition, you can control a pod’s consumption of system resources based on the pod’s priority.
Specifying resource quota for a pipeline is similar to setting a resource quota for the subset of pods created by a pipeline run. The following steps provide an example of the workaround by specifying resource quota based on priority class.
Procedure
Create a priority class for a pipeline.
Example: Priority class for a pipeline
apiVersion: scheduling.k8s.io/v1 kind: PriorityClass metadata: name: pipeline1-pc value: 1000000 description: "Priority class for pipeline1"Create a resource quota for a pipeline.
Example: Resource quota for a pipeline
apiVersion: v1 kind: ResourceQuota metadata: name: pipeline1-rq spec: hard: cpu: "1000" memory: 200Gi pods: "10" scopeSelector: matchExpressions: - operator : In scopeName: PriorityClass values: ["pipeline1-pc"]Verify the resource quota usage for the pipeline.
Example: Verify resource quota usage for the pipeline
$ oc describe quotaSample output
Name: pipeline1-rq Namespace: default Resource Used Hard -------- ---- ---- cpu 0 1k memory 0 200Gi pods 0 10Because pods are not running, the quota is unused.
Create the pipelines and tasks.
Example: YAML for the pipeline
apiVersion: tekton.dev/v1alpha1 kind: Pipeline metadata: name: maven-build spec: workspaces: - name: local-maven-repo resources: - name: app-git type: git tasks: - name: build taskRef: name: mvn resources: inputs: - name: source resource: app-git params: - name: GOALS value: ["package"] workspaces: - name: maven-repo workspace: local-maven-repo - name: int-test taskRef: name: mvn runAfter: ["build"] resources: inputs: - name: source resource: app-git params: - name: GOALS value: ["verify"] workspaces: - name: maven-repo workspace: local-maven-repo - name: gen-report taskRef: name: mvn runAfter: ["build"] resources: inputs: - name: source resource: app-git params: - name: GOALS value: ["site"] workspaces: - name: maven-repo workspace: local-maven-repoExample: YAML for a task in the pipeline
apiVersion: tekton.dev/v1alpha1 kind: Task metadata: name: mvn spec: workspaces: - name: maven-repo inputs: params: - name: GOALS description: The Maven goals to run type: array default: ["package"] resources: - name: source type: git steps: - name: mvn image: gcr.io/cloud-builders/mvn workingDir: /workspace/source command: ["/usr/bin/mvn"] args: - -Dmaven.repo.local=$(workspaces.maven-repo.path) - "$(inputs.params.GOALS)" priorityClassName: pipeline1-pcNoteEnsure that all tasks in the pipeline belongs to the same priority class.
Create and start the pipeline run.
Example: YAML for a pipeline run
apiVersion: tekton.dev/v1alpha1 kind: PipelineRun metadata: generateName: petclinic-run- spec: pipelineRef: name: maven-build resources: - name: app-git resourceSpec: type: git params: - name: url value: https://github.com/spring-projects/spring-petclinicAfter the pods are created, verify the resource quota usage for the pipeline run.
Example: Verify resource quota usage for the pipeline
$ oc describe quotaSample output
Name: pipeline1-rq Namespace: default Resource Used Hard -------- ---- ---- cpu 500m 1k memory 10Gi 200Gi pods 1 10The output indicates that you can manage the combined resource quota for all concurrent running pods belonging to a priority class, by specifying the resource quota per priority class.
4.12. Automatic pruning of task run and pipeline run
Stale TaskRun and PipelineRun objects and their executed instances occupy physical resources that can be used for the active runs. To prevent this waste, Red Hat OpenShift Pipelines provides annotations that cluster administrators can use to automatically prune the unused objects and their instances in various namespaces.
- Starting with Red Hat OpenShift Pipelines 1.6, auto-pruning is enabled by default.
- Configuring automatic pruning by specifying annotations affects the entire namespace. You cannot selectively auto-prune individual task runs and pipeline runs in a namespace.
4.12.1. Annotations for automatically pruning task runs and pipeline runs
To automatically prune task runs and pipeline runs in a namespace, you can set the following annotations in the namespace:
-
operator.tekton.dev/prune.schedule: If the value of this annotation is different from the value specified in theTektonConfigcustom resource definition, a new cron job in that namespace is created. -
operator.tekton.dev/prune.skip: When set totrue, the namespace for which it is configured is not pruned. -
operator.tekton.dev/prune.resources: This annotation accepts a comma-separated list of resources. To prune a single resource such as a pipeline run, set this annotation to"pipelinerun". To prune multiple resources, such as task run and pipeline run, set this annotation to"taskrun, pipelinerun". -
operator.tekton.dev/prune.keep: Use this annotation to retain a resource without pruning. operator.tekton.dev/prune.keep-since: Use this annotation to retain resources based on their age. The value for this annotation must be equal to the age of the resource in minutes. For example, to retain resources which were created not more than five days ago, setkeep-sinceto7200.NoteThe
keepandkeep-sinceannotations are mutually exclusive. For any resource, you must configure only one of them.-
operator.tekton.dev/prune.strategy: Set the value of this annotation to eitherkeeporkeep-since.
For example, consider the following annotations that retain all task runs and pipeline runs created in the last five days, and deletes the older resources:
Example of auto-pruning annotations
...
annotations:
operator.tekton.dev/prune.resources: "taskrun, pipelinerun"
operator.tekton.dev/prune.keep-since: 7200
...4.12.2. Additional resources
- For information on manual pruning of various objects, see Pruning objects to reclaim resources.
4.13. Using pods in a privileged security context
The default configuration of OpenShift Pipelines 1.3.x and later versions does not allow you to run pods with privileged security context, if the pods result from pipeline run or task run. For such pods, the default service account is pipeline, and the security context constraint (SCC) associated with the pipelines service account is pipelines-scc. The pipelines-scc SCC is similar to the anyuid SCC, but with a minor difference as defined in the YAML file for the SCC of pipelines:
Example SecurityContextConstraints object
apiVersion: security.openshift.io/v1
kind: SecurityContextConstraints
...
fsGroup:
type: MustRunAs
...
In addition, the Buildah cluster task, shipped as part of the OpenShift Pipelines, uses vfs as the default storage driver.
4.13.1. Running pipeline run and task run pods with privileged security context
Procedure
To run a pod (resulting from pipeline run or task run) with the privileged security context, do the following modifications:
Configure the associated user account or service account to have an explicit SCC. You can perform the configuration using any of the following methods:
Run the following command:
$ oc adm policy add-scc-to-user <scc-name> -z <service-account-name>Alternatively, modify the YAML files for
RoleBinding, andRoleorClusterRole:Example
RoleBindingobjectapiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: service-account-name1 namespace: default roleRef: apiGroup: rbac.authorization.k8s.io kind: ClusterRole name: pipelines-scc-clusterrole2 subjects: - kind: ServiceAccount name: pipeline namespace: defaultExample
ClusterRoleobjectapiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRole metadata: name: pipelines-scc-clusterrole1 rules: - apiGroups: - security.openshift.io resourceNames: - nonroot resources: - securitycontextconstraints verbs: - use- 1
- Substitute with an appropriate cluster role based on the role binding you use.
NoteAs a best practice, create a copy of the default YAML files and make changes in the duplicate file.
-
If you do not use the
vfsstorage driver, configure the service account associated with the task run or the pipeline run to have a privileged SCC, and set the security context asprivileged: true.
4.13.2. Running pipeline run and task run by using a custom SCC and a custom service account
When using the pipelines-scc security context constraint (SCC) associated with the default pipelines service account, the pipeline run and task run pods may face timeouts. This happens because in the default pipelines-scc SCC, the fsGroup.type parameter is set to MustRunAs.
For more information about pod timeouts, see BZ#1995779.
To avoid pod timeouts, you can create a custom SCC with the fsGroup.type parameter set to RunAsAny, and associate it with a custom service account.
As a best practice, use a custom SCC and a custom service account for pipeline runs and task runs. This approach allows greater flexibility and does not break the runs when the defaults are modified during an upgrade.
Procedure
Define a custom SCC with the
fsGroup.typeparameter set toRunAsAny:Example: Custom SCC
apiVersion: security.openshift.io/v1 kind: SecurityContextConstraints metadata: annotations: kubernetes.io/description: my-scc is a close replica of anyuid scc. pipelines-scc has fsGroup - RunAsAny. name: my-scc allowHostDirVolumePlugin: false allowHostIPC: false allowHostNetwork: false allowHostPID: false allowHostPorts: false allowPrivilegeEscalation: true allowPrivilegedContainer: false allowedCapabilities: null defaultAddCapabilities: null fsGroup: type: RunAsAny groups: - system:cluster-admins priority: 10 readOnlyRootFilesystem: false requiredDropCapabilities: - MKNOD runAsUser: type: RunAsAny seLinuxContext: type: MustRunAs supplementalGroups: type: RunAsAny volumes: - configMap - downwardAPI - emptyDir - persistentVolumeClaim - projected - secretCreate the custom SCC:
Example: Create the
my-sccSCC$ oc create -f my-scc.yamlCreate a custom service account:
Example: Create a
fsgroup-runasanyservice account$ oc create serviceaccount fsgroup-runasanyAssociate the custom SCC with the custom service account:
Example: Associate the
my-sccSCC with thefsgroup-runasanyservice account$ oc adm policy add-scc-to-user my-scc -z fsgroup-runasanyIf you want to use the custom service account for privileged tasks, you can associate the
privilegedSCC with the custom service account by running the following command:Example: Associate the
privilegedSCC with thefsgroup-runasanyservice account$ oc adm policy add-scc-to-user privileged -z fsgroup-runasanyUse the custom service account in the pipeline run and task run:
Example: Pipeline run YAML with
fsgroup-runasanycustom service accountapiVersion: tekton.dev/v1beta1 kind: PipelineRun metadata: name: <pipeline-run-name> spec: pipelineRef: name: <pipeline-cluster-task-name> serviceAccountName: 'fsgroup-runasany'Example: Task run YAML with
fsgroup-runasanycustom service accountapiVersion: tekton.dev/v1beta1 kind: TaskRun metadata: name: <task-run-name> spec: taskRef: name: <cluster-task-name> serviceAccountName: 'fsgroup-runasany'
4.14. Securing webhooks with event listeners
As an administrator, you can secure webhooks with event listeners. After creating a namespace, you enable HTTPS for the Eventlistener resource by adding the operator.tekton.dev/enable-annotation=enabled label to the namespace. Then, you create a Trigger resource and a secured route using the re-encrypted TLS termination.
Triggers in Red Hat OpenShift Pipelines support insecure HTTP and secure HTTPS connections to the Eventlistener resource. HTTPS secures connections within and outside the cluster.
Red Hat OpenShift Pipelines runs a tekton-operator-proxy-webhook pod that watches for the labels in the namespace. When you add the label to the namespace, the webhook sets the service.beta.openshift.io/serving-cert-secret-name=<secret_name> annotation on the EventListener object. This, in turn, creates secrets and the required certificates.
service.beta.openshift.io/serving-cert-secret-name=<secret_name>
In addition, you can mount the created secret into the Eventlistener pod to secure the request.
4.14.1. Providing secure connection with OpenShift routes
To create a route with the re-encrypted TLS termination, run:
$ oc create route reencrypt --service=<svc-name> --cert=tls.crt --key=tls.key --ca-cert=ca.crt --hostname=<hostname>Alternatively, you can create a re-encrypted TLS termination YAML file to create a secure route.
Example re-encrypt TLS termination YAML to create a secure route
apiVersion: route.openshift.io/v1
kind: Route
metadata:
name: route-passthrough-secured
spec:
host: <hostname>
to:
kind: Service
name: frontend
tls:
termination: reencrypt
key: [as in edge termination]
certificate: [as in edge termination]
caCertificate: [as in edge termination]
destinationCACertificate: |-
-----BEGIN CERTIFICATE-----
[...]
-----END CERTIFICATE------ 1 2
- The name of the object, which is limited to only 63 characters.
- 3
- The termination field is set to
reencrypt. This is the only required TLS field. - 4
- This is required for re-encryption. The
destinationCACertificatefield specifies a CA certificate to validate the endpoint certificate, thus securing the connection from the router to the destination pods. You can omit this field in either of the following scenarios:- The service uses a service signing certificate.
- The administrator specifies a default CA certificate for the router, and the service has a certificate signed by that CA.
You can run the oc create route reencrypt --help command to display more options.
4.14.2. Creating a sample EventListener resource using a secure HTTPS connection
This section uses the pipelines-tutorial example to demonstrate creation of a sample EventListener resource using a secure HTTPS connection.
Procedure
Create the
TriggerBindingresource from the YAML file available in the pipelines-tutorial repository:$ oc create -f https://raw.githubusercontent.com/openshift/pipelines-tutorial/master/03_triggers/01_binding.yamlCreate the
TriggerTemplateresource from the YAML file available in the pipelines-tutorial repository:$ oc create -f https://raw.githubusercontent.com/openshift/pipelines-tutorial/master/03_triggers/02_template.yamlCreate the
Triggerresource directly from the pipelines-tutorial repository:$ oc create -f https://raw.githubusercontent.com/openshift/pipelines-tutorial/master/03_triggers/03_trigger.yamlCreate an
EventListenerresource using a secure HTTPS connection:Add a label to enable the secure HTTPS connection to the
Eventlistenerresource:$ oc label namespace <ns-name> operator.tekton.dev/enable-annotation=enabledCreate the
EventListenerresource from the YAML file available in the pipelines-tutorial repository:$ oc create -f https://raw.githubusercontent.com/openshift/pipelines-tutorial/master/03_triggers/04_event_listener.yamlCreate a route with the re-encrypted TLS termination:
$ oc create route reencrypt --service=<svc-name> --cert=tls.crt --key=tls.key --ca-cert=ca.crt --hostname=<hostname>
4.15. Authenticating pipelines using git secret
A Git secret consists of credentials to securely interact with a Git repository, and is often used to automate authentication. In Red Hat OpenShift Pipelines, you can use Git secrets to authenticate pipeline runs and task runs that interact with a Git repository during execution.
A pipeline run or a task run gains access to the secrets through the associated service account. Pipelines support the use of Git secrets as annotations (key-value pairs) for basic authentication and SSH-based authentication.
4.15.1. Credential selection
A pipeline run or task run might require multiple authentications to access different Git repositories. Annotate each secret with the domains where Pipelines can use its credentials.
A credential annotation key for Git secrets must begin with tekton.dev/git-, and its value is the URL of the host for which you want Pipelines to use that credential.
In the following example, Pipelines uses a basic-auth secret, which relies on a username and password, to access repositories at github.com and gitlab.com.
Example: Multiple credentials for basic authentication
apiVersion: v1
kind: Secret
metadata:
annotations:
tekton.dev/git-0: github.com
tekton.dev/git-1: gitlab.com
type: kubernetes.io/basic-auth
stringData:
username:
password:
You can also use an ssh-auth secret (private key) to access a Git repository.
Example: Private key for SSH based authentication
apiVersion: v1
kind: Secret
metadata:
annotations:
tekton.dev/git-0: https://github.com
type: kubernetes.io/ssh-auth
stringData:
ssh-privatekey: - 1
- Name of the file containing the SSH private key string.
4.15.2. Configuring basic authentication for Git
For a pipeline to retrieve resources from password-protected repositories, you must configure the basic authentication for that pipeline.
To configure basic authentication for a pipeline, update the secret.yaml, serviceaccount.yaml, and run.yaml files with the credentials from the Git secret for the specified repository. When you complete this process, Pipelines can use that information to retrieve the specified pipeline resources.
For GitHub, authentication using plain password is deprecated. Instead, use a personal access token.
Procedure
In the
secret.yamlfile, specify the username and password or GitHub personal access token to access the target Git repository.apiVersion: v1 kind: Secret metadata: name: basic-user-pass1 annotations: tekton.dev/git-0: https://github.com type: kubernetes.io/basic-auth stringData: username:2 password:3 In the
serviceaccount.yamlfile, associate the secret with the appropriate service account.apiVersion: v1 kind: ServiceAccount metadata: name: build-bot1 secrets: - name: basic-user-pass2 In the
run.yamlfile, associate the service account with a task run or a pipeline run.Associate the service account with a task run:
apiVersion: tekton.dev/v1beta1 kind: TaskRun metadata: name: build-push-task-run-21 spec: serviceAccountName: build-bot2 taskRef: name: build-push3 Associate the service account with a
PipelineRunresource:apiVersion: tekton.dev/v1beta1 kind: PipelineRun metadata: name: demo-pipeline1 namespace: default spec: serviceAccountName: build-bot2 pipelineRef: name: demo-pipeline3
Apply the changes.
$ oc apply --filename secret.yaml,serviceaccount.yaml,run.yaml
4.15.3. Configuring SSH authentication for Git
For a pipeline to retrieve resources from repositories configured with SSH keys, you must configure the SSH-based authentication for that pipeline.
To configure SSH-based authentication for a pipeline, update the secret.yaml, serviceaccount.yaml, and run.yaml files with the credentials from the SSH private key for the specified repository. When you complete this process, Pipelines can use that information to retrieve the specified pipeline resources.
Consider using SSH-based authentication rather than basic authentication.
Procedure
-
Generate an SSH private key, or copy an existing private key, which is usually available in the
~/.ssh/id_rsafile. In the
secret.yamlfile, set the value ofssh-privatekeyto the name of the SSH private key file, and set the value ofknown_hoststo the name of the known hosts file.apiVersion: v1 kind: Secret metadata: name: ssh-key1 annotations: tekton.dev/git-0: github.com type: kubernetes.io/ssh-auth stringData: ssh-privatekey:2 known_hosts:3 ImportantIf you omit the private key, Pipelines accepts the public key of any server.
-
Optional: To specify a custom SSH port, add
:<port number>to the end of theannotationvalue. For example,tekton.dev/git-0: github.com:2222. In the
serviceaccount.yamlfile, associate thessh-keysecret with thebuild-botservice account.apiVersion: v1 kind: ServiceAccount metadata: name: build-bot1 secrets: - name: ssh-key2 In the
run.yamlfile, associate the service account with a task run or a pipeline run.Associate the service account with a task run:
apiVersion: tekton.dev/v1beta1 kind: TaskRun metadata: name: build-push-task-run-21 spec: serviceAccountName: build-bot2 taskRef: name: build-push3 Associate the service account with a pipeline run:
apiVersion: tekton.dev/v1beta1 kind: PipelineRun metadata: name: demo-pipeline1 namespace: default spec: serviceAccountName: build-bot2 pipelineRef: name: demo-pipeline3
Apply the changes.
$ oc apply --filename secret.yaml,serviceaccount.yaml,run.yaml
4.15.4. Using SSH authentication in git type tasks
When invoking Git commands, you can use SSH authentication directly in the steps of a task. SSH authentication ignores the $HOME variable and only uses the user’s home directory specified in the /etc/passwd file. So each step in a task must symlink the /tekton/home/.ssh directory to the home directory of the associated user.
However, explicit symlinks are not necessary when you use a pipeline resource of the git type, or the git-clone task available in the Tekton catalog.
As an example of using SSH authentication in git type tasks, refer to authenticating-git-commands.yaml.
4.15.5. Using secrets as a non-root user
You might need to use secrets as a non-root user in certain scenarios, such as:
- The users and groups that the containers use to execute runs are randomized by the platform.
- The steps in a task define a non-root security context.
- A task specifies a global non-root security context, which applies to all steps in a task.
In such scenarios, consider the following aspects of executing task runs and pipeline runs as a non-root user:
-
SSH authentication for Git requires the user to have a valid home directory configured in the
/etc/passwddirectory. Specifying a UID that has no valid home directory results in authentication failure. -
SSH authentication ignores the
$HOMEenvironment variable. So you must or symlink the appropriate secret files from the$HOMEdirectory defined by Pipelines (/tekton/home), to the non-root user’s valid home directory.
In addition, to configure SSH authentication in a non-root security context, refer to the example for authenticating git commands.
4.15.6. Limiting secret access to specific steps
By default, the secrets for Pipelines are stored in the $HOME/tekton/home directory, and are available for all the steps in a task.
To limit a secret to specific steps, use the secret definition to specify a volume, and mount the volume in specific steps.
4.16. Using Tekton Chains for OpenShift Pipelines supply chain security
Tekton Chains is a Technology Preview feature only. Technology Preview features are not supported with Red Hat production service level agreements (SLAs) and might not be functionally complete. Red Hat does not recommend using them in production. These features provide early access to upcoming product features, enabling customers to test functionality and provide feedback during the development process.
For more information about the support scope of Red Hat Technology Preview features, see Technology Preview Features Support Scope.
Tekton Chains is a Kubernetes Custom Resource Definition (CRD) controller. You can use it to manage the supply chain security of the tasks and pipelines created using Red Hat OpenShift Pipelines.
By default, Tekton Chains observes all task run executions in your OpenShift Container Platform cluster. When the task runs complete, Tekton Chains takes a snapshot of the task runs. It then converts the snapshot to one or more standard payload formats, and finally signs and stores all artifacts.
To capture information about task runs, Tekton Chains uses the Result and PipelineResource objects. When the objects are unavailable, Tekton Chains the URLs and qualified digests of the OCI images.
The PipelineResource object is deprecated and will be removed in a future release; for manual use, the Results object is recommended.
4.16.1. Key features
-
You can sign task runs, task run results, and OCI registry images with cryptographic key types and services such as
cosign. -
You can use attestation formats such as
in-toto. - You can securely store signatures and signed artifacts using OCI repository as a storage backend.
4.16.2. Installing Tekton Chains using the Red Hat OpenShift Pipelines Operator
Cluster administrators can use the TektonChain custom resource (CR) to install and manage Tekton Chains.
Tekton Chains is an optional component of Red Hat OpenShift Pipelines. Currently, you cannot install it using the TektonConfig CR.
Prerequisites
-
Ensure that the Red Hat OpenShift Pipelines Operator is installed in the
openshift-pipelinesnamespace on your cluster.
Procedure
Create the
TektonChainCR for your OpenShift Container Platform cluster.apiVersion: operator.tekton.dev/v1alpha1 kind: TektonChain metadata: name: chain spec: targetNamespace: openshift-pipelinesApply the
TektonChainCR.$ oc apply -f TektonChain.yaml1 - 1
- Substitute with the file name of the
TektonChainCR.
Check the status of the installation.
$ oc get tektonchains.operator.tekton.dev
4.16.3. Configuring Tekton Chains
Tekton Chains uses a ConfigMap object named chains-config in the openshift-pipelines namespace for configuration.
To configure Tekton Chains, use the following example:
Example: Configuring Tekton Chains
$ oc patch configmap chains-config -n openshift-pipelines -p='{"data":{"artifacts.oci.storage": "", "artifacts.taskrun.format":"tekton", "artifacts.taskrun.storage": "tekton"}}' - 1
- Use a combination of supported key-value pairs in the JSON payload.
4.16.3.1. Supported keys for Tekton Chains configuration
Cluster administrators can use various supported keys and values to configure specifications about task runs, OCI images, and storage.
4.16.3.1.1. Supported keys for task run
| Supported keys | Description | Supported values | Default values |
|---|---|---|---|
|
| The format to store task run payloads. |
|
|
|
|
The storage backend for task run signatures. You can specify multiple backends as a comma-separated list, such as |
|
|
|
| The signature backend to sign task run payloads. |
|
|
4.16.3.1.2. Supported keys for OCI
| Supported keys | Description | Supported values | Default values |
|---|---|---|---|
|
| The format to store OCI payloads. |
|
|
|
|
The storage backend to for OCI signatures. You can specify multiple backends as a comma-separated list, such as |
|
|
|
| The signature backend to sign OCI payloads. |
|
|
4.16.3.1.3. Supported keys for storage
| Supported keys | Description | Supported values | Default values |
|---|---|---|---|
|
| The OCI repository to store OCI signatures. | Currently, Chains support only the internal OpenShift OCI registry; other popular options such as Quay is not supported. |
4.16.4. Signing secrets in Tekton Chains
Cluster administrators can generate a key pair and use Tekton Chains to sign artifacts using a Kubernetes secret. For Tekton Chains to work, a private key and a password for encrypted keys must exist as part of the signing-secrets Kubernetes secret, in the openshift-pipelines namespace.
Currently, Tekton Chains supports the x509 and cosign signature schemes.
Use only one of the supported signature schemes.
4.16.4.1. Signing using x509
To use the x509 signing scheme with Tekton Chains, store the x509.pem private key of the ed25519 or ecdsa type in the signing-secrets Kubernetes secret. Ensure that the key is stored as an unencrypted PKCS8 PEM file (BEGIN PRIVATE KEY).
4.16.4.2. Signing using cosign
To use the cosign signing scheme with Tekton Chains:
- Install cosign.
Generate the
cosign.keyandcosign.pubkey pairs.$ cosign generate-key-pair k8s://openshift-pipelines/signing-secretsCosign prompts you for a password, and creates a Kubernetes secret.
-
Store the encrypted
cosign.keyprivate key and thecosign.passworddecryption password in thesigning-secretsKubernetes secret. Ensure that the private key is stored as an encrypted PEM file of theENCRYPTED COSIGN PRIVATE KEYtype.
4.16.4.3. Troubleshooting signing
If the signing secrets are already populated, you might get the following error:
Error from server (AlreadyExists): secrets "signing-secrets" already existsTo resolve the error:
Delete the secrets:
$ oc delete secret signing-secrets -n openshift-pipelines- Recreate the key pairs and store them in the secrets using your preferred signing scheme.
4.16.5. Authenticating to an OCI registry
Before pushing signatures to an OCI registry, cluster administrators must configure Tekton Chains to authenticate with the registry. The Tekton Chains controller uses the same service account under which the task runs execute. To set up a service account with the necessary credentials for pushing signatures to an OCI registry, perform the following steps:
Procedure
Set the namespace and name of the Kubernetes service account.
$ export NAMESPACE=<namespace>1 $ export SERVICE_ACCOUNT_NAME=<service_account>2 Create a Kubernetes secret.
$ oc create secret registry-credentials \ --from-file=.dockerconfigjson \1 --type=kubernetes.io/dockerconfigjson \ -n $NAMESPACE- 1
- Substitute with the path to your Docker config file. Default path is
~/.docker/config.json.
Give the service account access to the secret.
$ oc patch serviceaccount $SERVICE_ACCOUNT_NAME \ -p "{\"imagePullSecrets\": [{\"name\": \"registry-credentials\"}]}" -n $NAMESPACEIf you patch the default
pipelineservice account that Red Hat OpenShift Pipelines assigns to all task runs, the Red Hat OpenShift Pipelines Operator will override the service account. As a best practice, you can perform the following steps:Create a separate service account to assign to user’s task runs.
$ oc create serviceaccount <service_account_name>Associate the service account to the task runs by setting the value of the
serviceaccountnamefield in the task run template.apiVersion: tekton.dev/v1beta1 kind: TaskRun metadata: name: build-push-task-run-2 spec: serviceAccountName: build-bot1 taskRef: name: build-push ...- 1
- Substitute with the name of the newly created service account.
4.16.5.1. Creating and verifying task run signatures without any additional authentication
To verify signatures of task runs using Tekton Chains with any additional authentication, perform the following tasks:
- Create an encrypted x509 key pair and save it as a Kubernetes secret.
- Configure the Tekton Chains backend storage.
- Create a task run, sign it, and store the signature and the payload as annotations on the task run itself.
- Retrieve the signature and payload from the signed task run.
- Verify the signature of the task run.
Prerequisites
Ensure that the following are installed on the cluster:
- Red Hat OpenShift Pipelines Operator
- Tekton Chains
- Cosign
Procedure
Create an encrypted x509 key pair and save it as a Kubernetes secret:
$ cosign generate-key-pair k8s://openshift-pipelines/signing-secretsProvide a password when prompted. Cosign stores the resulting private key as part of the
signing-secretsKubernetes secret in theopenshift-pipelinesnamespace.In the Tekton Chains configuration, disable the OCI storage, and set the task run storage and format to
tekton.$ oc patch configmap chains-config -n openshift-pipelines -p='{"data":{"artifacts.oci.storage": "", "artifacts.taskrun.format":"tekton", "artifacts.taskrun.storage": "tekton"}}'Restart the Tekton Chains controller to ensure that the modified configuration is applied.
$ oc delete po -n openshift-pipelines -l app=tekton-chains-controllerCreate a task run.
$ oc create -f https://raw.githubusercontent.com/tektoncd/chains/main/examples/taskruns/task-output-image.yaml1 taskrun.tekton.dev/build-push-run-output-image-qbjvh created- 1
- Substitute with the URI or file path pointing to your task run.
Check the status of the steps, and wait till the process finishes.
$ tkn tr describe --last [...truncated output...] NAME STATUS ∙ create-dir-builtimage-9467f Completed ∙ git-source-sourcerepo-p2sk8 Completed ∙ build-and-push Completed ∙ echo Completed ∙ image-digest-exporter-xlkn7 CompletedRetrieve the signature and payload from the object stored as
base64encoded annotations:$ export TASKRUN_UID=$(tkn tr describe --last -o jsonpath='{.metadata.uid}') $ tkn tr describe --last -o jsonpath="{.metadata.annotations.chains\.tekton\.dev/signature-taskrun-$TASKRUN_UID}" > signature $ tkn tr describe --last -o jsonpath="{.metadata.annotations.chains\.tekton\.dev/payload-taskrun-$TASKRUN_UID}" | base64 -d > payloadVerify the signature.
$ cosign verify-blob --key k8s://openshift-pipelines/signing-secrets --signature ./signature ./payload Verified OK
4.16.6. Using Tekton Chains to sign and verify image and provenance
Cluster administrators can use Tekton Chains to sign and verify images and provenances, by performing the following tasks:
- Create an encrypted x509 key pair and save it as a Kubernetes secret.
- Set up authentication for the OCI registry to store images, image signatures, and signed image attestations.
- Configure Tekton Chains to generate and sign provenance.
- Create an image with Kaniko in a task run.
- Verify the signed image and the signed provenance.
Prerequisites
Ensure that the following are installed on the cluster:
Procedure
Create an encrypted x509 key pair and save it as a Kubernetes secret:
$ cosign generate-key-pair k8s://openshift-pipelines/signing-secretsProvide a password when prompted. Cosign stores the resulting private key as part of the
signing-secretsKubernetes secret in theopenshift-pipelinesnamespace, and writes the public key to thecosign.publocal file.Configure authentication for the image registry.
- To configure the Tekton Chains controller for pushing signature to an OCI registry, use the credentials associated with the service account of the task run. For detailed information, see the "Authenticating to an OCI registry" section.
To configure authentication for a Kaniko task that builds and pushes image to the registry, create a Kubernetes secret of the docker
config.jsonfile containing the required credentials.$ oc create secret generic <docker_config_secret_name> \1 --from-file <path_to_config.json>2
Configure Tekton Chains by setting the
artifacts.taskrun.format,artifacts.taskrun.storage, andtransparency.enabledparameters in thechains-configobject:$ oc patch configmap chains-config -n openshift-pipelines -p='{"data":{"artifacts.taskrun.format": "in-toto"}}' $ oc patch configmap chains-config -n openshift-pipelines -p='{"data":{"artifacts.taskrun.storage": "oci"}}' $ oc patch configmap chains-config -n openshift-pipelines -p='{"data":{"transparency.enabled": "true"}}'Start the Kaniko task.
Apply the Kaniko task to the cluster.
$ oc apply -f examples/kaniko/kaniko.yaml1 - 1
- Substitute with the URI or file path to your Kaniko task.
Set the appropriate environment variables.
$ export REGISTRY=<url_of_registry>1 $ export DOCKERCONFIG_SECRET_NAME=<name_of_the_secret_in_docker_config_json>2 Start the Kaniko task.
$ tkn task start --param IMAGE=$REGISTRY/kaniko-chains --use-param-defaults --workspace name=source,emptyDir="" --workspace name=dockerconfig,secret=$DOCKERCONFIG_SECRET_NAME kaniko-chainsObserve the logs of this task until all steps are complete. On successful authentication, the final image will be pushed to
$REGISTRY/kaniko-chains.
Wait for a minute to allow Tekton Chains to generate the provenance and sign it, and then check the availability of the
chains.tekton.dev/signed=trueannotation on the task run.$ oc get tr <task_run_name> \1 -o json | jq -r .metadata.annotations { "chains.tekton.dev/signed": "true", ... }- 1
- Substitute with the name of the task run.
Verify the image and the attestation.
$ cosign verify --key cosign.pub $REGISTRY/kaniko-chains $ cosign verify-attestation --key cosign.pub $REGISTRY/kaniko-chainsFind the provenance for the image in Rekor.
- Get the digest of the $REGISTRY/kaniko-chains image. You can search for it ing the task run, or pull the image to extract the digest.
Search Rekor to find all entries that match the
sha256digest of the image.$ rekor-cli search --sha <image_digest>1 <uuid_1>2 <uuid_2>3 ...The search result displays UUIDs of the matching entries. One of those UUIDs holds the attestation.
Check the attestation.
$ rekor-cli get --uuid <uuid> --format json | jq -r .Attestation | base64 --decode | jq
4.17. Viewing pipeline logs using the OpenShift Logging Operator
The logs generated by pipeline runs, task runs, and event listeners are stored in their respective pods. It is useful to review and analyze logs for troubleshooting and audits.
However, retaining the pods indefinitely leads to unnecessary resource consumption and cluttered namespaces.
To eliminate any dependency on the pods for viewing pipeline logs, you can use the OpenShift Elasticsearch Operator and the OpenShift Logging Operator. These Operators help you to view pipeline logs by using the Elasticsearch Kibana stack, even after you have deleted the pods that contained the logs.
4.17.1. Prerequisites
Before trying to view pipeline logs in a Kibana dashboard, ensure the following:
- The steps are performed by a cluster administrator.
- Logs for pipeline runs and task runs are available.
- The OpenShift Elasticsearch Operator and the OpenShift Logging Operator are installed.
4.17.2. Viewing pipeline logs in Kibana
To view pipeline logs in the Kibana web console:
Procedure
- Log in to OpenShift Container Platform web console as a cluster administrator.
-
In the top right of the menu bar, click the grid icon
Observability Logging. The Kibana web console is displayed. Create an index pattern:
- On the left navigation panel of the Kibana web console, click Management.
- Click Create index pattern.
-
Under Step 1 of 2: Define index pattern
Index pattern, enter a *pattern and click Next Step. -
Under Step 2 of 2: Configure settings
Time filter field name, select @timestamp from the drop-down menu, and click Create index pattern.
Add a filter:
- On the left navigation panel of the Kibana web console, click Discover.
Click Add a filter +
Edit Query DSL. Note- For each of the example filters that follows, edit the query and click Save.
- The filters are applied one after another.
Filter the containers related to pipelines:
Example query to filter pipelines containers
{ "query": { "match": { "kubernetes.flat_labels": { "query": "app_kubernetes_io/managed-by=tekton-pipelines", "type": "phrase" } } } }Filter all containers that are not
place-toolscontainer. As an illustration of using the graphical drop-down menus instead of editing the query DSL, consider the following approach:Figure 4.6. Example of filtering using the drop-down fields

Filter
pipelinerunin labels for highlighting:Example query to filter
pipelinerunin labels for highlighting{ "query": { "match": { "kubernetes.flat_labels": { "query": "tekton_dev/pipelineRun=", "type": "phrase" } } } }Filter
pipelinein labels for highlighting:Example query to filter
pipelinein labels for highlighting{ "query": { "match": { "kubernetes.flat_labels": { "query": "tekton_dev/pipeline=", "type": "phrase" } } } }
From the Available fields list, select the following fields:
-
kubernetes.flat_labels messageEnsure that the selected fields are displayed under the Selected fields list.
-
The logs are displayed under the message field.
Figure 4.7. Filtered messages
