Chapitre 2. Gestion des comptes d'utilisateurs à l'aide de la ligne de commande
Ce chapitre comprend une description de base du cycle de vie de l'utilisateur dans le cadre de la gestion de l'identité (IdM). Les sections suivantes vous montrent comment :
- Créer des comptes d'utilisateurs
- Activer les comptes d'utilisateurs de l'étape
- Préserver les comptes d'utilisateurs
- Supprimer des comptes d'utilisateurs actifs, d'étape ou préservés
- Restaurer les comptes d'utilisateurs conservés
2.1. Cycle de vie de l'utilisateur
La gestion des identités (IdM) prend en charge trois états de compte utilisateur :
- Stage les utilisateurs ne sont pas autorisés à s'authentifier. Il s'agit d'un état initial. Certaines propriétés du compte utilisateur requises pour les utilisateurs actifs ne peuvent pas être définies, par exemple l'appartenance à un groupe.
- Active les utilisateurs sont autorisés à s'authentifier. Toutes les propriétés requises du compte utilisateur doivent être définies dans cet état.
- Preserved sont d'anciens utilisateurs actifs qui sont considérés comme inactifs et ne peuvent pas s'authentifier auprès de l'IdM. Les utilisateurs préservés conservent la plupart des propriétés du compte qu'ils avaient en tant qu'utilisateurs actifs, mais ils ne font partie d'aucun groupe d'utilisateurs.
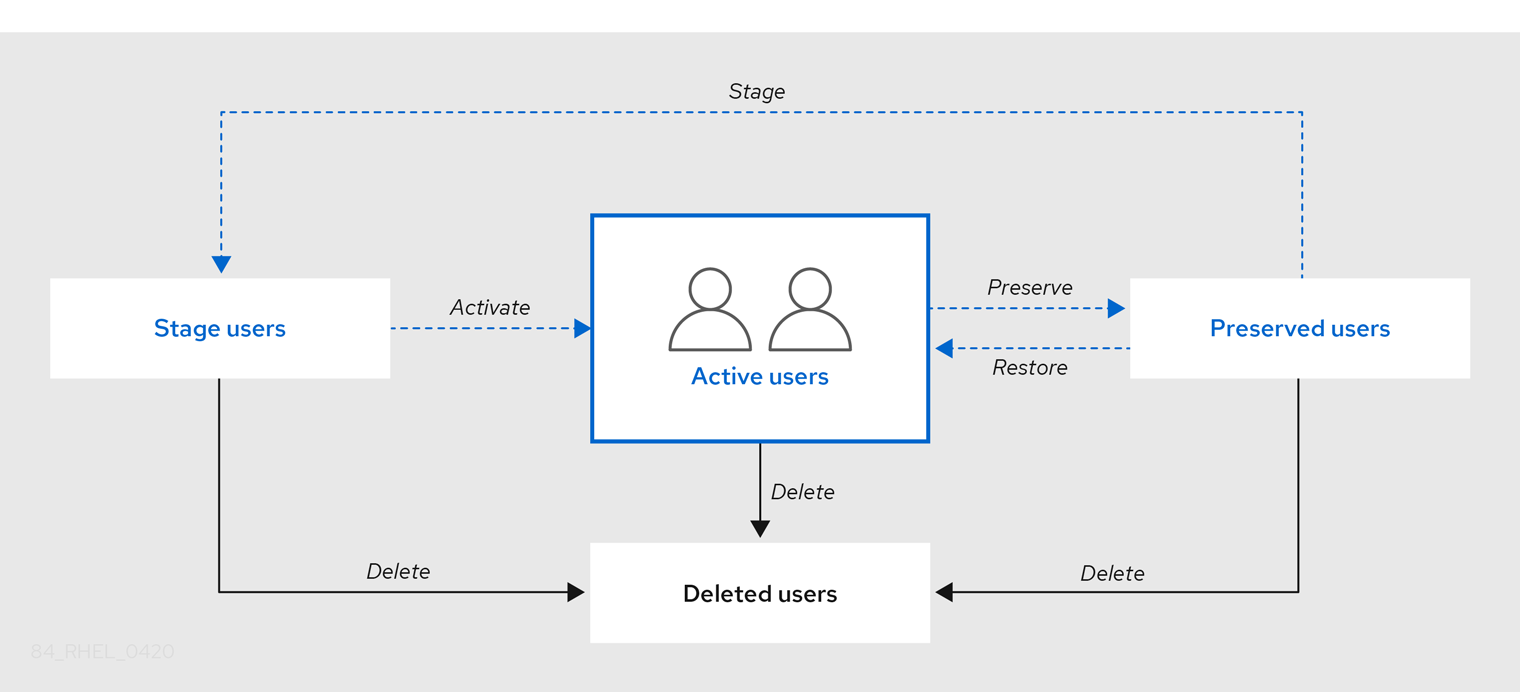
Vous pouvez supprimer définitivement les entrées utilisateur de la base de données IdM.
Les comptes d'utilisateurs supprimés ne peuvent pas être restaurés. Lorsque vous supprimez un compte d'utilisateur, toutes les informations associées à ce compte sont définitivement perdues.
Un nouvel administrateur ne peut être créé que par un utilisateur disposant de droits d'administrateur, tel que l'utilisateur admin par défaut. Si vous supprimez accidentellement tous les comptes d'administrateur, le gestionnaire de répertoire doit créer manuellement un nouvel administrateur dans le serveur de répertoire.
Ne pas supprimer l'utilisateur admin. Comme admin est un utilisateur prédéfini requis par l'IdM, cette opération pose des problèmes avec certaines commandes. Si vous souhaitez définir et utiliser un autre utilisateur administrateur, désactivez l'utilisateur prédéfini admin avec ipa user-disable admin après avoir accordé des droits d'administrateur à au moins un autre utilisateur.
N'ajoutez pas d'utilisateurs locaux à IdM. Le commutateur de service de noms (NSS) résout toujours les utilisateurs et les groupes IdM avant de résoudre les utilisateurs et les groupes locaux. Cela signifie, par exemple, que l'appartenance à un groupe IdM ne fonctionne pas pour les utilisateurs locaux.