Ce contenu n'est pas disponible dans la langue sélectionnée.
11.5. Setting up Cross-Realm Kerberos Trusts
11.5.1. A Trust Relationship
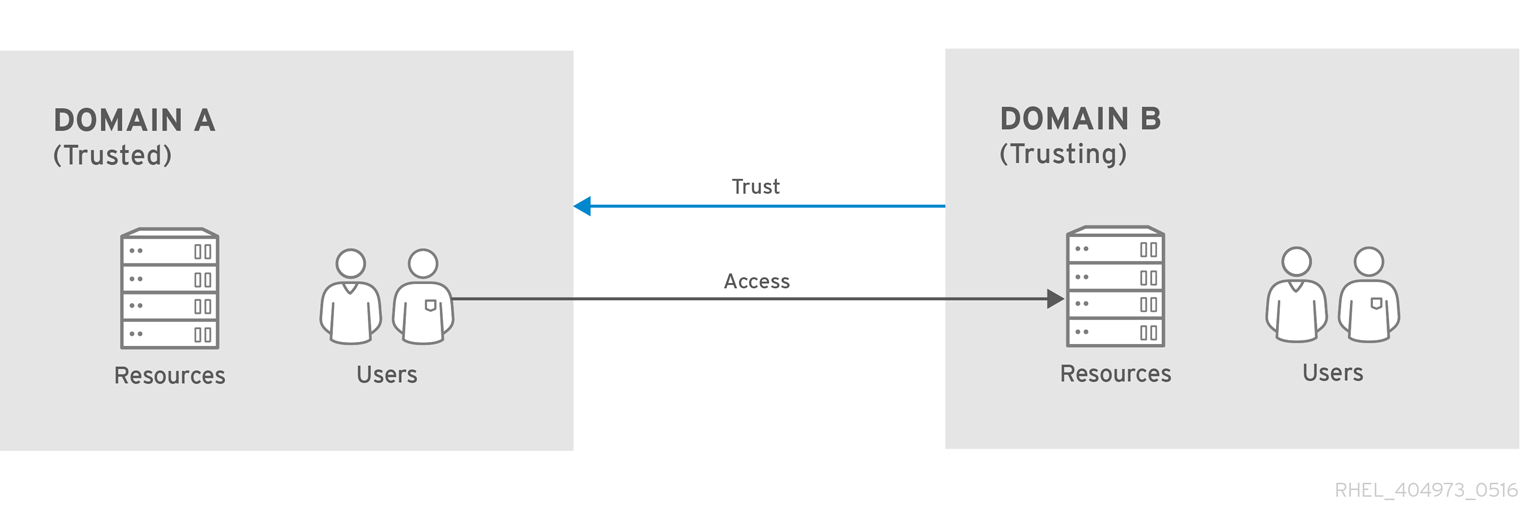
Figure 11.2. Basic Trust
krbtgt/B.EXAMPLE.COM@A.EXAMPLE.COM). When that principal is also added to Domain A, then the clients in Domain A can access the resources in Domain B. The configured principal exists in both realms. That shared principal has three characteristics:
- It exists in both realms.
- When a key is created, the same password is used in both realms.
- The key has the same key version number (
kvno).
B.EXAMPLE.COM realm are trusted to authenticate to services in the A.EXAMPLE.COM realm. To establish trust in the other direction, both realms would need to share keys for the krbtgt/A.EXAMPLE.COM@B.EXAMPLE.COM service — an entry with a reverse mapping from the previous example.
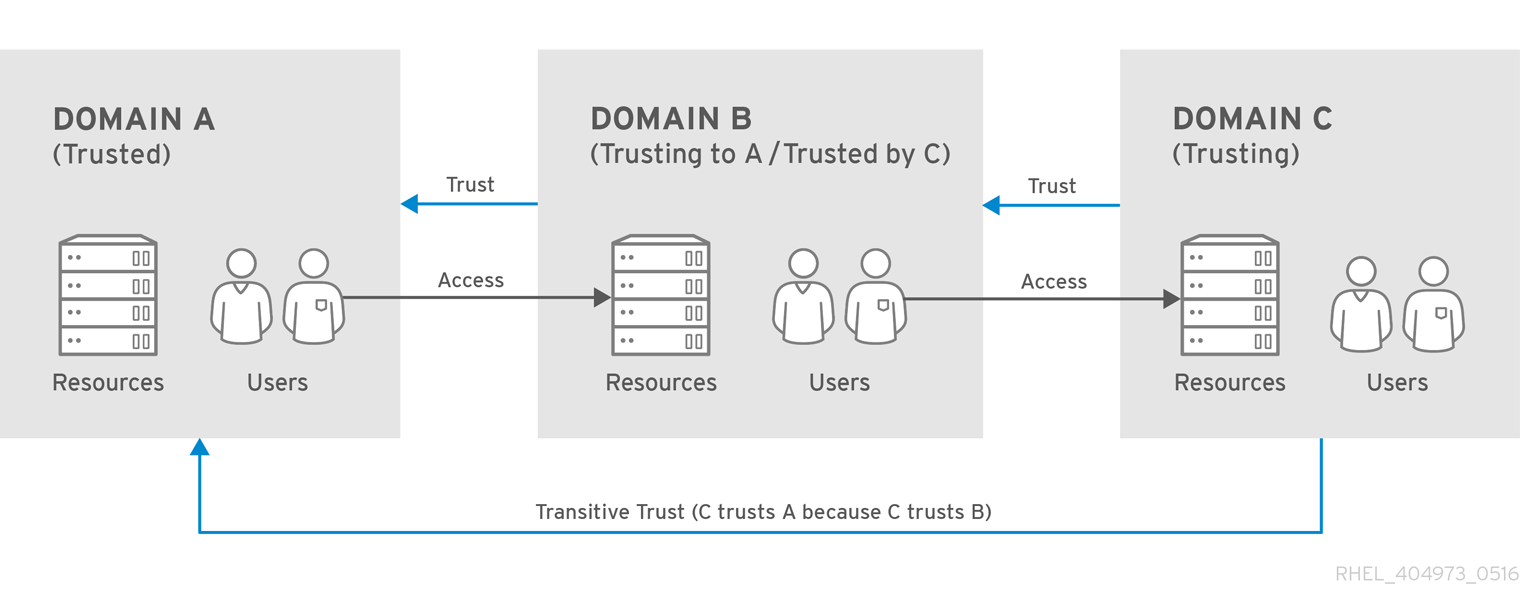
Figure 11.3. Transitive Trust
[domain_realm] section of the /etc/krb5.conf file. With implicit mapping, the domain name is converted to upper case; the converted name is then assumed to be the Kerberos realm to search.
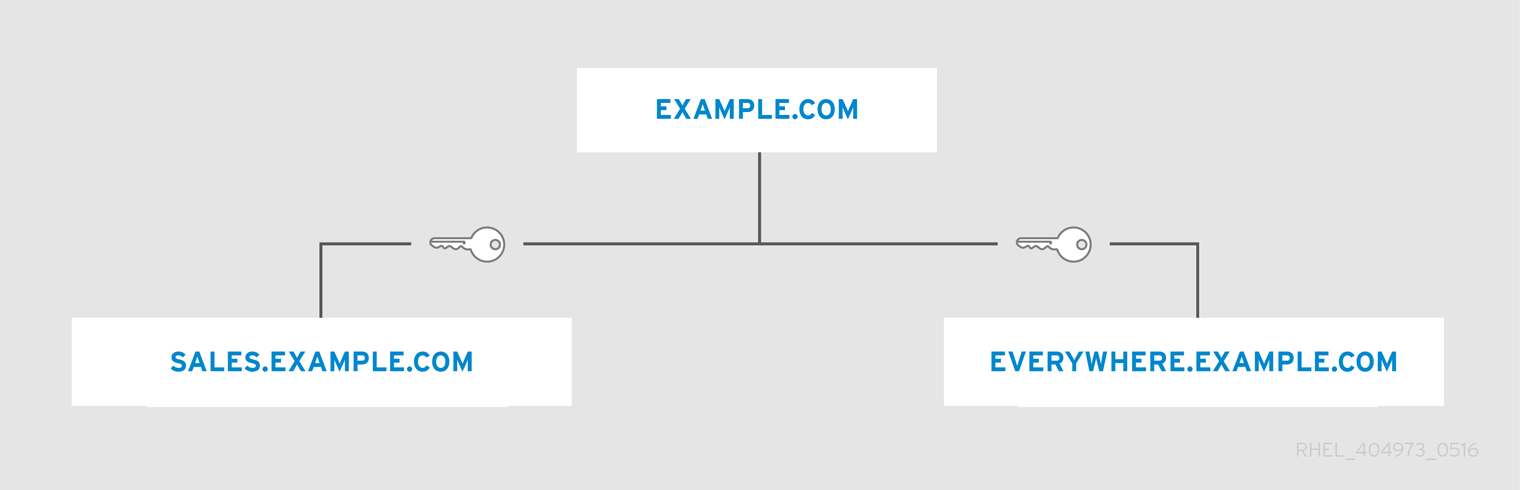
Figure 11.4. Trusts in the Same Domain
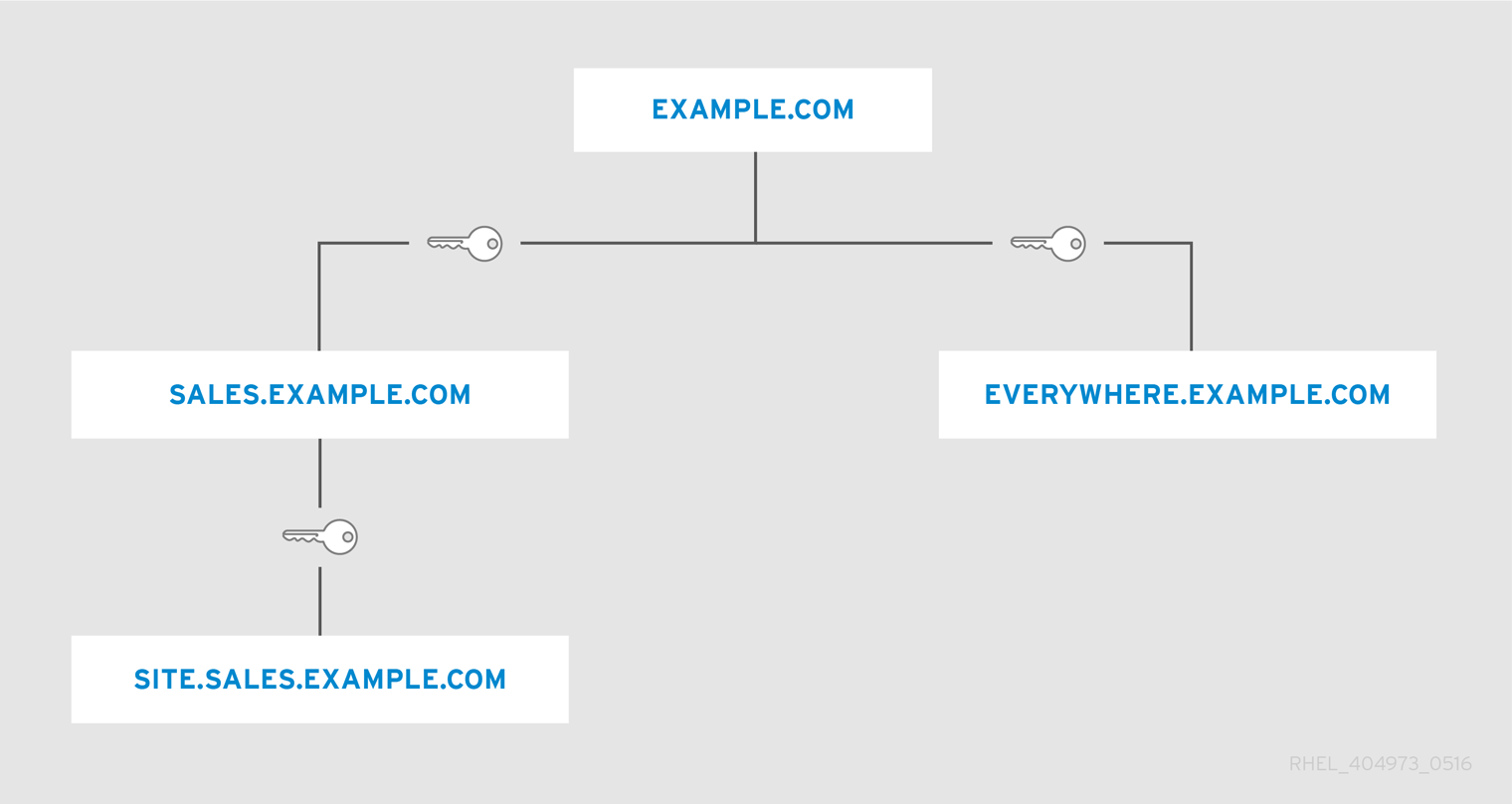
Figure 11.5. Child/Parent Trusts in the Same Domain
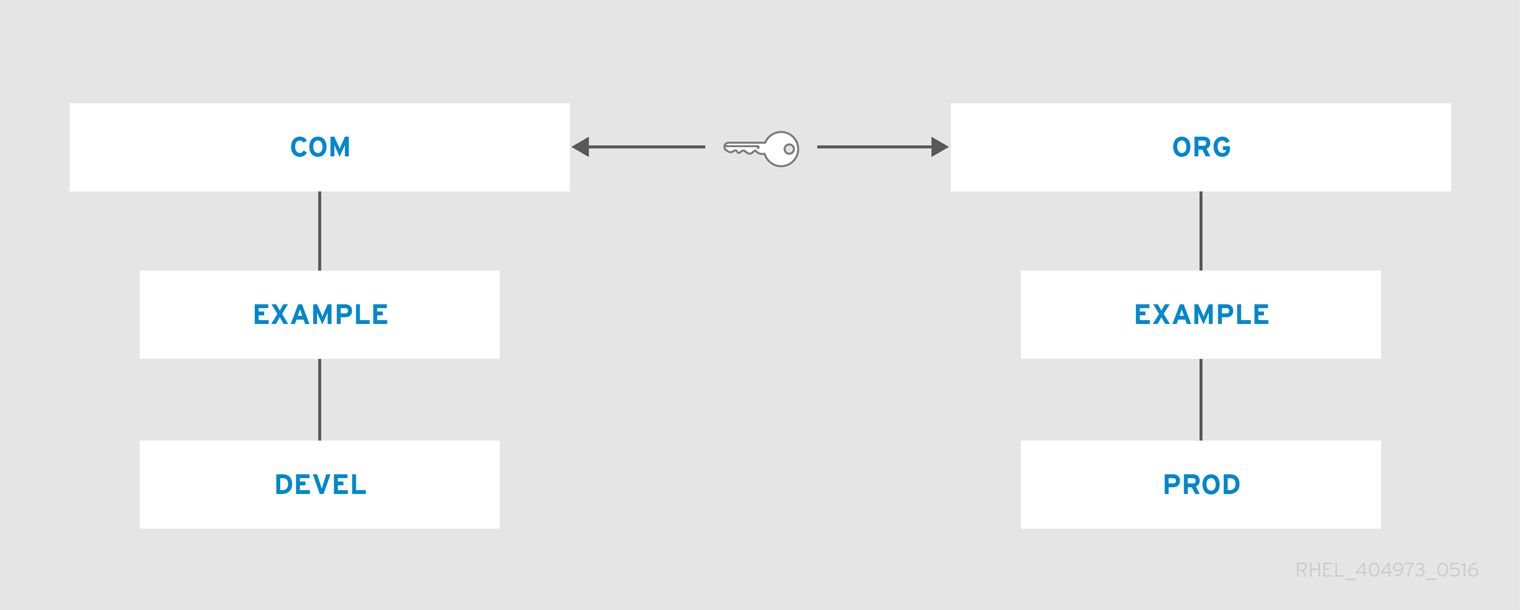
Figure 11.6. Trusts in Different Domains
The [capaths] section
[capaths] section of the /etc/krb5.conf file defines the trust flow between different realms.
[capaths] section is relatively straightforward: there is a main entry for each realm where a client has a principal, and then inside each realm section is a list of intermediate realms from which the client must obtain credentials.
[capaths] can be used to specify the following process for obtaining credentials:
- With credentials from Realm A, the client obtains a
krbtgt/A@Aticket from the KDC of Realm A. Using this ticket, the client then asks for thekrbtgt/B@Aticket.Thekrbtgt/B@Aticket issued by the KDC of Realm A is a cross-realm ticket granting ticket. It allows the client to ask the KDC of Realm B for a ticket to a service principal of Realm B. - With the
krbtgt/B@Aticket, the client asks for thekrbtgt/C@Bcross-realm ticket. - With the
krbtgt/C@Bticket issued by the KDC of Realm B, the client asks for thekrbtgt/D@Ccross-realm ticket. - With the
krbtgt/D@Cticket issued by the KDC of Realm C, the client asks the KDC of Realm D for a ticket to a service principal in Realm D.
krbtgt/A@A, krbtgt/B@A, krbtgt/C@B, krbtgt/D@C, and service/hostname@D. To obtain the service/hostname@D ticket, it was required to obtain the three intermediate cross-realm tickets.
[capaths] section, including examples of the [capaths] configuration, see the krb5.conf(5) man page.
11.5.2. Setting up a Realm Trust
A.EXAMPLE.COM and B.EXAMPLE.COM.
kadmin.
[root@server ~]# kadmin -r A.EXAMPLE.COM
kadmin: add_principal krbtgt/B.EXAMPLE.COM@A.EXAMPLE.COM
Enter password for principal "krbtgt/B.EXAMPLE.COM@A.EXAMPLE.COM":
Re-enter password for principal "krbtgt/B.EXAMPLE.COM@A.EXAMPLE.COM":
Principal "krbtgt/B.EXAMPLE.COM@A.EXAMPLE.COM" created.
quitImportant
kadmin.
[root@server ~]# kadmin -r B.EXAMPLE.COM
kadmin: add_principal krbtgt/A.EXAMPLE.COM@B.EXAMPLE.COM
Enter password for principal "krbtgt/A.EXAMPLE.COM@B.EXAMPLE.COM":
Re-enter password for principal "krbtgt/A.EXAMPLE.COM@B.EXAMPLE.COM":
Principal "krbtgt/A.EXAMPLE.COM@B.EXAMPLE.COM" created.
quitget_principal command to verify that both entries have matching key version numbers (kvno values) and encryption types.
Important
add_principal command's -randkey option to assign a random key instead of a password, dump the new entry from the database of the first realm, and import it into the second. This will not work unless the master keys for the realm databases are identical, as the keys contained in a database dump are themselves encrypted using the master key.