第2章 Identity Management サービスの表示、開始、および停止
ドメインの可用性を確保し、システムに加えた変更を適用するために、Identity Management (IdM) サービスを監視します。systemctl および ipactl ユーティリティーを使用することで、サービスステータスを確認したり、手動で設定を変更した後にコンポーネントを再起動したり、システムの中断から復旧したりできます。
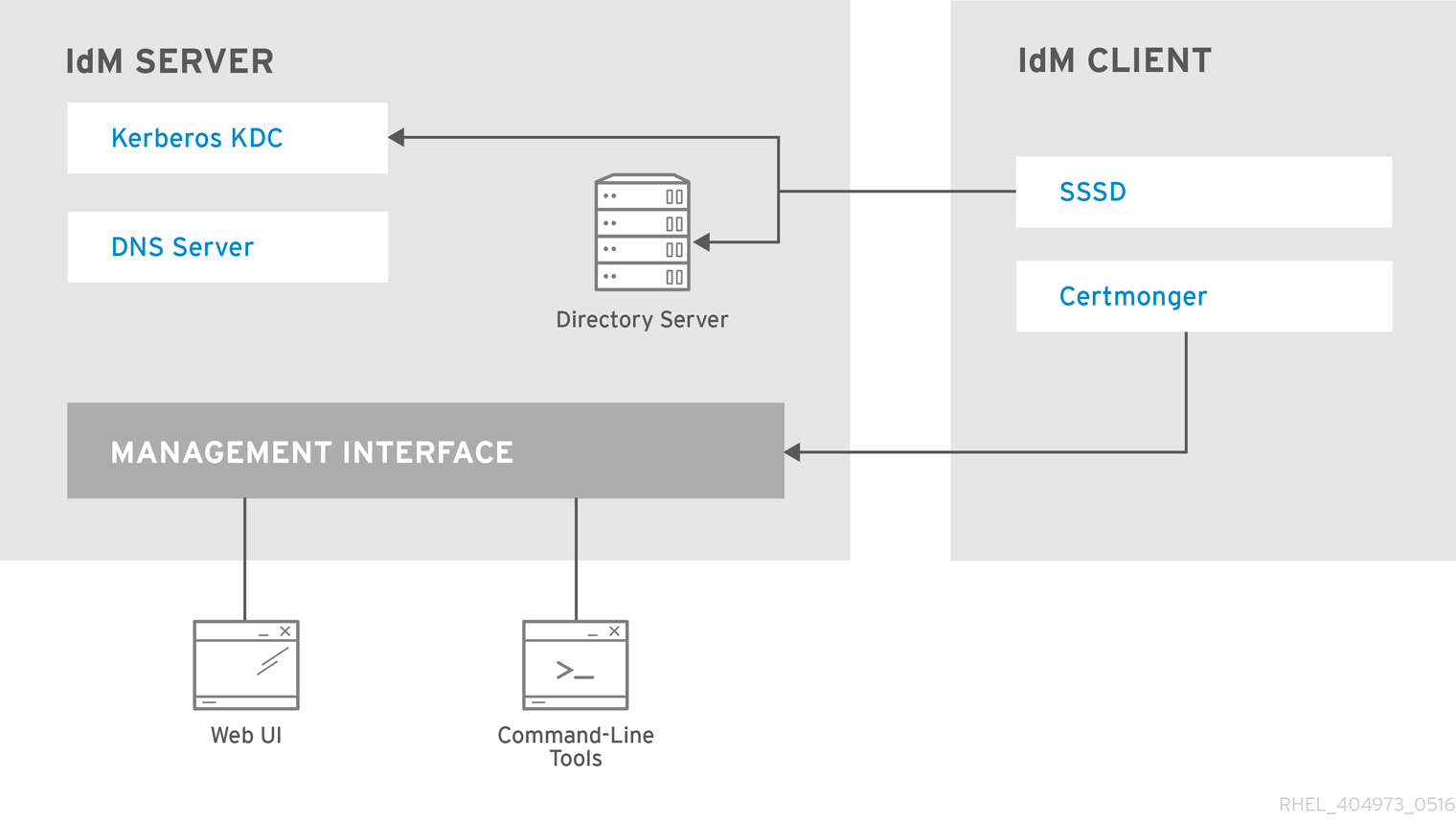
2.1. IdM サーバーおよびクライアントサービスの概要
Identity Management (IdM) サーバーおよびクライアント上で動作するコアシステムサービスを特定します。認証、ディレクトリーストレージ、証明書管理などの IdM 機能と、それらに対応するシステムデーモンとの関係を理解します。
2.1.1. IdM サーバーがホストするサービスのリスト
以下のサービスの多くは、IdM サーバーへのインストールが必須というわけではありません。たとえば、認証局 (CA) や DNS サーバーなどのサービスは、IdM ドメイン内にない外部サーバーにインストールできます。
-
Kerberos:
krb5kdcおよびkadminサービス。
IdM は、シングルサインオンに対応する Kerberos プロトコルを使用します。Kerberos では、正しいユーザー名とパスワードを一度提示するだけで済み、システムから認証情報を再度求められることなく IdM サービスにアクセスできます。
Kerberos は 2 つの部分に分類されます。
-
krb5kdcサービス。Kerberos 認証サービスおよびキー配布センター (KDC) デーモンです。 -
kadminサービス。Kerberos V5 データベース管理プログラムです。
IdM で Kerberos を使用して認証する方法は、コマンドラインからの Identity Management へのログイン を参照してください。
Web UI で IdM にログイン: Kerberos チケットの使用
-
LDAP ディレクトリーサーバー:
dirsrvサービス。
IdM の LDAP ディレクトリーサーバー インスタンスは、Kerberos、ユーザーアカウント、ホストエントリー、サービス、ポリシー、DNS などの情報をはじめとした、IdM 情報をすべて保存します。LDAP ディレクトリーサーバーインスタンスは、Red Hat Directory Server と同じテクノロジーをベースにしています。ただし、IdM 固有のタスクに合わせて調整されます。
-
認証局:
pki-tomcatdサービス。
統合 認証局 (CA) は、Red Hat Certificate System と同じテクノロジーをベースにしています。pki は、Certificate System サービスにアクセスするためのコマンドラインです。
必要な証明書をすべて単独で作成して提供する場合は、統合 CA なしでサーバーをインストールすることもできます。
詳細は、CA サービスの計画 を参照してください。
-
Domain Name System (DNS):
namedサービス。
IdM は、動的サービス検出に DNS を使用します。IdM クライアントのインストールユーティリティーは、DNS からの情報を使用して、クライアントマシンを自動的に設定できます。クライアントを IdM ドメインに登録したら、クライアントは DNS を使用してドメイン内の IdM サーバーおよびサービスを検索します。Red Hat Enterprise Linux の DNS (Domain Name System) プロトコルの BIND (Berkeley Internet Name Domain) 実装には、named の DNS サーバーが含まれています。
詳細は、DNS サービスとホスト名の計画 を参照してください。
-
Apache HTTP サーバー:
httpdサービス。
Apache HTTP Web サーバー には、IdM Web UI があり、認証局とその他の IdM サービスの間の通信も管理します。
-
Samba/Winbind:
smbおよびwinbindサービス。
Samba は、Red Hat Enterprise Linux に、Common Internet File System (CIFS) プロトコルとも呼ばれる Server Message Block (SMB) プロトコルを実装します。smb サービス経由で SMB プロトコルを使用すると、ファイル共有や共有プリンターなどのサーバーのリソースにアクセスできます。Active Directory (AD) 環境で信頼を設定している場合には、`Winbind` サービスが IdM サーバーと AD サーバー間の通信を管理します。
-
ワンタイムパスワード (OTP) 認証:
ipa-otpdサービス。
ワンタイムパスワード (OTP) は、2 要素認証の一部として、認証トークンがセッション 1 回だけ使用できるように生成するパスワードです。OTP 認証は、ipa-otpd サービスを介して Red Hat Enterprise Linux に実装されています。
詳細は、ワンタイムパスワードを使用した Identity Management Web UI へのログイン を参照してください。
-
OpenDNSSEC:
ipa-dnskeysyncdサービス。
OpenDNSSEC は、DNSSEC (DNS Security Extensions) キーおよびゾーンの署名の記録プロセスを自動化する DNS マネージャーです。ipa-dnskeysyncd サービスは、IdM Directory Server と OpenDNSSEC との間の同期を管理します。

DNSSEC は、IdM ではテクノロジープレビューとしてのみ利用できます。
2.1.2. IdM クライアントがホストするサービスのリスト
-
System Security Services Daemon:
sssdサービス
SSSD (System Security Services Daemon) は、ユーザー認証およびキャッシュ認証情報を管理するクライアント側のアプリケーションです。キャッシュを使用すると、IdM サーバーが利用できなくなったり、クライアントがオフラインになったりした場合に、ローカルシステムが通常の認証操作を継続できるようになります。
詳細は、SSSD とその利点について を参照してください。
-
certmonger:
certmongerサービス
certmonger サービスは、クライアント上の証明書を監視、更新します。このサービスは、システム上のサービスに対して新しい証明書を要求できます。
詳細は、certmonger を使用したサービスの IdM 証明書の取得 を参照してください。