40.10. Delegating access to hosts and services
By delegating access to hosts and services within an IdM domain, you can retrieve keytabs and certificates for another host or service.
Each host and service has a managedby entry that lists what hosts and services can manage it. By default, a host can manage itself and all of its services. You can configure a host to manage other hosts, or services on other hosts within the IdM domain.
When you delegate authority of a host to another host through a managedby entry, it does not automatically grant management rights for all services on that host. You must perform each delegation independently.
Host and service delegation 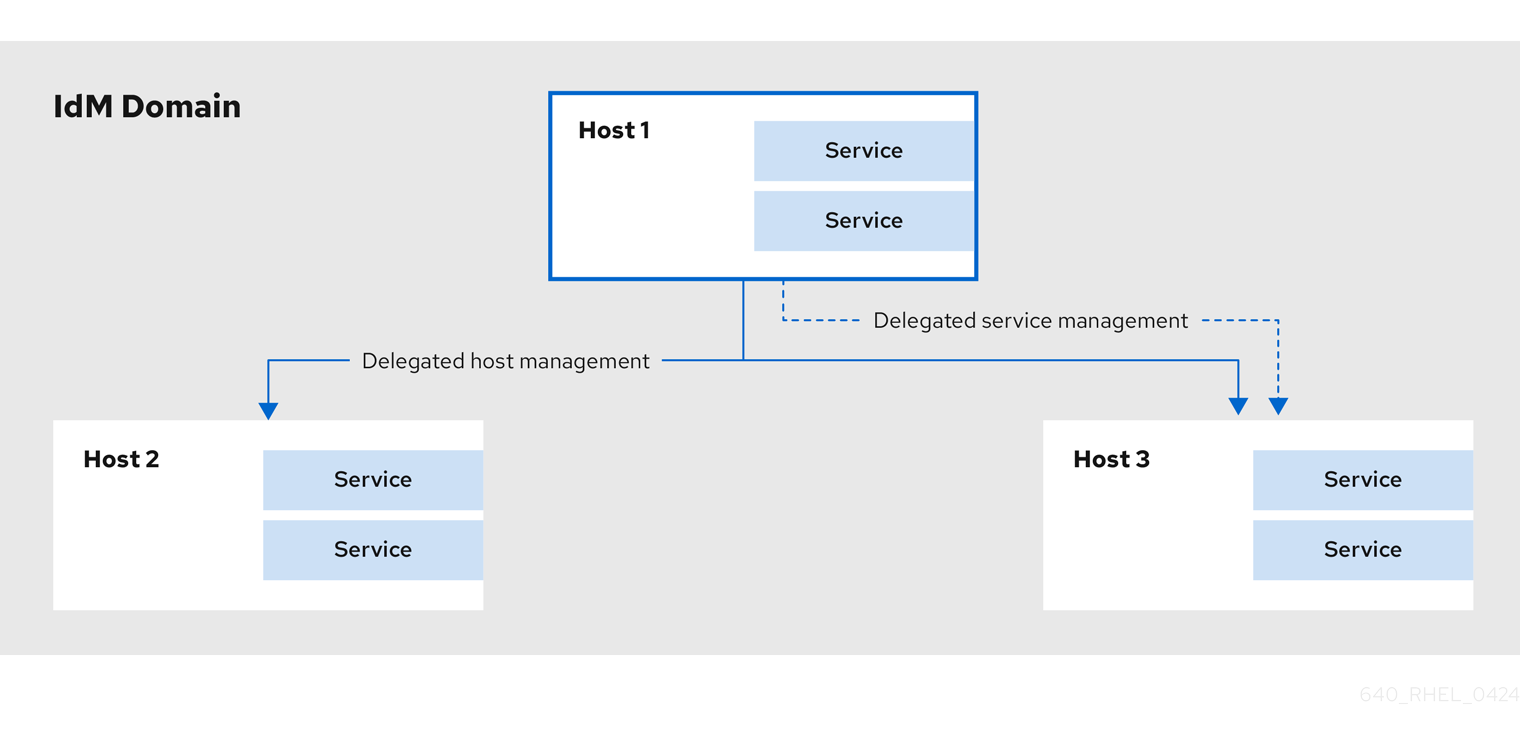
40.10.1. Delegating service management
You can delegate permissions to a host to manage a service on another host within the domain.
When you delegate permissions to a host to manage another host, it does not automatically include permissions to manage its services. You must delegate service management independently.
Procedure
Delegate the management of a service to a specific host by using the
service-add-hostcommand:ipa service-add-host principal --hosts=<hostname>You must specify the service principal using the
principalargument and the hosts with control using the--hostsoption.For example:
[root@server ~]# ipa service-add HTTP/web.example.com [root@server ~]# ipa service-add-host HTTP/web.example.com --hosts=client1.example.comOnce the host is delegated authority, the host principal can be used to manage the service:
[root@client1 ~]# kinit -kt /etc/krb5.keytab host/client1.example.com [root@client1 ~]# ipa-getkeytab -s server.example.com -k /tmp/test.keytab -p HTTP/web.example.com Keytab successfully retrieved and stored in: /tmp/test.keytabTo generate a certificate for the delegated service, create a certificate request on the host with the delegated authority:
[root@client1]# kinit -kt /etc/krb5.keytab host/client1.example.com [root@client1]# openssl req -newkey rsa:2048 -subj '/CN=web.example.com/O=EXAMPLE.COM' -keyout /etc/pki/tls/web.key -out /tmp/web.csr -nodes Generating a 2048 bit RSA private key .............................................................+++ ............................................................................................+++ Writing new private key to '/etc/pki/tls/private/web.key'Use the
cert-requestutility to submit the certificate request and load the certification information:[root@client1]# ipa cert-request --principal=HTTP/web.example.com web.csr Certificate: MIICETCCAXqgA...[snip] Subject: CN=web.example.com,O=EXAMPLE.COM Issuer: CN=EXAMPLE.COM Certificate Authority Not Before: Tue Feb 08 18:51:51 2011 UTC Not After: Mon Feb 08 18:51:51 2016 UTC Serial number: 1005
40.10.2. Delegating host management
You can delegate authority for a host to manage another host by using the host-add-managedby utility. This creates a managedby entry. After the managedby entry is created, the managing host can retrieve a keytab for the host it manages.
Procedure
Log in as the admin user:
[root@server ~]# kinit adminAdd the
managedbyentry. For example, this delegates authority over client2 to client1:[root@server ~]# ipa host-add-managedby client2.example.com --hosts=client1.example.comObtain a ticket as the host client1:
[root@client1 ~]# kinit -kt /etc/krb5.keytab host/client1.example.comRetrieve a keytab for client2:
[root@client1 ~]# ipa-getkeytab -s server.example.com -k /tmp/client2.keytab -p host/client2.example.com Keytab successfully retrieved and stored in: /tmp/client2.keytab
40.10.3. Accessing delegated services
When a client has delegated authority, it can obtain a keytab for the principal on the local machine for both services and hosts.
With the kinit command, use the -k option to load a keytab and the -t option to specify the keytab. The principal format is <principal>/hostname@REALM. For a service, replace <principal> with the service name, for example HTTP. For a host, use host as the principal.
Procedure
To access a host:
[root@server ~]# kinit -kt /etc/krb5.keytab host/ipa.example.com@EXAMPLE.COMTo access a service:
[root@server ~]# kinit -kt /etc/httpd/conf/krb5.keytab HTTP/ipa.example.com@EXAMPLE.COM