11.5. Configuring automated unlocking using a Tang key in the web console
Configure automated unlocking of a LUKS-encrypted storage device using a key provided by a Tang server.
Conditions préalables
La console web RHEL 9 a été installée.
Pour plus de détails, voir Installation de la console web.
-
Le paquetage
cockpit-storagedest installé sur votre système. -
The
cockpit.socketservice is running at port 9090. -
The
clevis,tang, andclevis-dracutpackages are installed. - A Tang server is running.
Procédure
Open the RHEL web console by entering the following address in a web browser:
https://localhost:9090Replace the localhost part by the remote server’s host name or IP address when you connect to a remote system.
- Provide your credentials and click . Click to expand details of the encrypted device you want to unlock using the Tang server, and click .
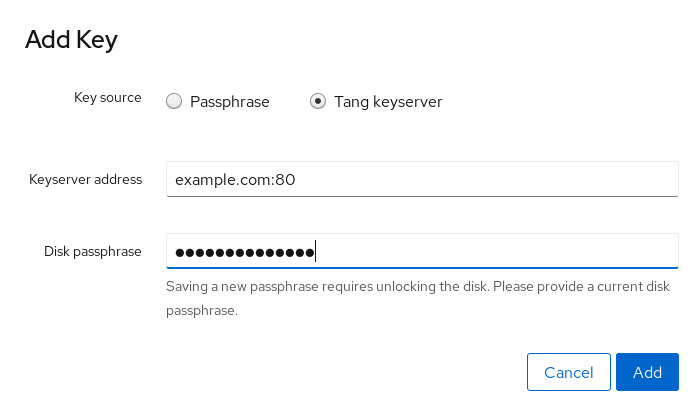
Click in the Keys section to add a Tang key:

Provide the address of your Tang server and a password that unlocks the LUKS-encrypted device. Click to confirm:
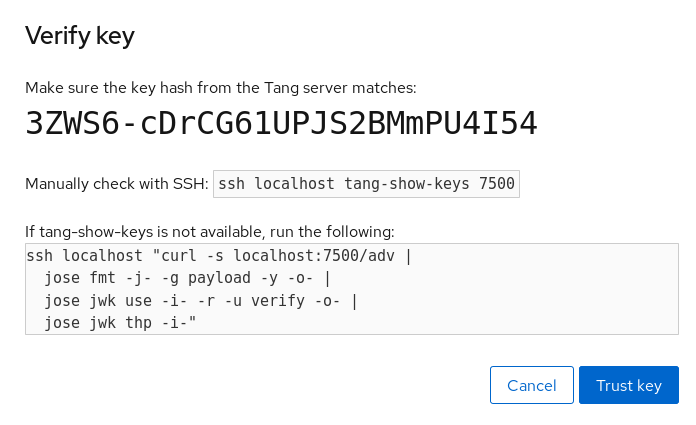
The following dialog window provides a command to verify that the key hash matches.
In a terminal on the Tang server, use the
tang-show-keyscommand to display the key hash for comparison. In this example, the Tang server is running on the port 7500:# tang-show-keys 7500 fM-EwYeiTxS66X3s1UAywsGKGnxnpll8ig0KOQmr9CMClick when the key hashes in the web console and in the output of previously listed commands are the same:
To enable the early boot system to process the disk binding, click at the bottom of the left navigation bar and enter the following commands:
# dnf install clevis-dracut # grubby --update-kernel=ALL --args="rd.neednet=1" # dracut -fv --regenerate-all
Vérification
Check that the newly added Tang key is now listed in the Keys section with the
Keyservertype:
Verify that the bindings are available for the early boot, for example:
# lsinitrd | grep clevis clevis clevis-pin-sss clevis-pin-tang clevis-pin-tpm2 -rwxr-xr-x 1 root root 1600 Feb 11 16:30 usr/bin/clevis -rwxr-xr-x 1 root root 1654 Feb 11 16:30 usr/bin/clevis-decrypt ... -rwxr-xr-x 2 root root 45 Feb 11 16:30 usr/lib/dracut/hooks/initqueue/settled/60-clevis-hook.sh -rwxr-xr-x 1 root root 2257 Feb 11 16:30 usr/libexec/clevis-luks-askpass
Ressources supplémentaires