Chapter 26. Managing Certificates and Certificate Authorities
26.1. Lightweight Sub-CAs
Copy linkLink copied to clipboard!
If your IdM installation is configured with the integrated Certificate System (CS) certificate authority (CA), you are able to create lightweight sub-CAs. They enable you to configure services, like virtual private network (VPN) gateways, to accept only certificates issued by one sub-CA. At the same time, you can configure other services to accept only certificates issued by a different sub-CA or the root CA.
If you revoke the intermediate certificate of a sub-CA, all certificates issued by this sub-CA are automatically invalid.
If you set up IdM using the integrated CA, the automatically created
ipa CA is the root CA of the certificate system. All sub-CAs you create, are subordinated to this root CA.
26.1.1. Creating a Lightweight Sub-CA
Copy linkLink copied to clipboard!
For details on creating a sub-CA, see
Creating a Sub-CA from the Web UI
To create a new sub-CA named vpn-ca:
- Open the Authentication tab, and select the Certificates subtab.
- Select Certificate Authorities and click .
- Enter the name and subject DN for the CA.
Figure 26.1. Adding a CA
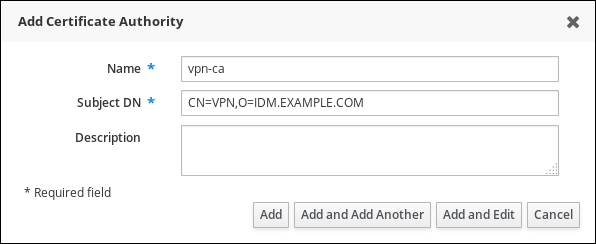 The subject DN must be unique in the IdM CA infrastructure.
The subject DN must be unique in the IdM CA infrastructure.
Creating a Sub-CA from the Command Line
To create a new sub-CA named vpn-ca, enter:
[root@ipaserver ~]# ipa ca-add vpn-ca --subject="CN=VPN,O=IDM.EXAMPLE.COM"
-------------------
Created CA "vpn-ca"
-------------------
Name: vpn-ca
Authority ID: ba83f324-5e50-4114-b109-acca05d6f1dc
Subject DN: CN=VPN,O=IDM.EXAMPLE.COM
Issuer DN: CN=Certificate Authority,O=IDM.EXAMPLE.COM- Name
- Name of the CA.
- Authority ID
- Automatically created, individual ID for the CA.
- Subject DN
- Subject distinguished name (DN). The subject DN must be unique in the IdM CA infrastructure.
- Issuer DN
- Parent CA that issued the sub-CA certificate. All sub-CAs are created as a child of the IdM root CA.
To verify that the new CA signing certificate has been successfully added to the IdM database, run:
[root@ipaserver ~]# certutil -d /etc/pki/pki-tomcat/alias/ -L
Certificate Nickname Trust Attributes
SSL,S/MIME,JAR/XPI
caSigningCert cert-pki-ca CTu,Cu,Cu
Server-Cert cert-pki-ca u,u,u
auditSigningCert cert-pki-ca u,u,Pu
caSigningCert cert-pki-ca ba83f324-5e50-4114-b109-acca05d6f1dc u,u,u
ocspSigningCert cert-pki-ca u,u,u
subsystemCert cert-pki-ca u,u,uNote
The new CA certificate is automatically transferred to all replicas when they have a certificate system instance installed.
26.1.2. Removing a Lightweight Sub-CA
Copy linkLink copied to clipboard!
For details on deleting a sub-CA, see
Removing a Sub-CA from the Web UI
- Open the Authentication tab, and select the Certificates subtab.
- Select Certificate Authorities.
- Select the sub-CA to remove and click .
- Click to confirm.
Removing a Sub-CA from the Command Line
To delete a sub-CA, enter:
[root@ipaserver ~]# ipa ca-del vpn-ca
-------------------
Deleted CA "vpn-ca"
-------------------