15.4. Specifying Default User and Group Attributes
Identity Management uses a template when it creates new entries.
For users, the template is very specific. Identity Management uses default values for several core attributes for IdM user accounts. These defaults can define actual values for user account attributes (such as the home directory location) or it can define the format of attribute values, such as the user name length. These settings also define the object classes assigned to users.
For groups, the template only defines the assigned object classes.
These default definitions are all contained in a single configuration entry for the IdM server, cn=ipaconfig,cn=etc,dc=example,dc=com.
The configuration can be changed using the ipa config-mod command.
| Field | Command-Line Option | Descriptions |
|---|---|---|
| Maximum user name length | --maxusername | Sets the maximum number of characters for user names. The default value is 32. |
| Root for home directories | --homedirectory | Sets the default directory to use for user home directories. The default value is /home. |
| Default shell | --defaultshell | Sets the default shell to use for users. The default value is /bin/sh. |
| Default user group | --defaultgroup | Sets the default group to which all newly created accounts are added. The default value is ipausers, which is automatically created during the IdM server installation process. |
| Default e-mail domain | --emaildomain | Sets the email domain to use to create email addresses based on the new accounts. The default is the IdM server domain. |
| Search time limit | --searchtimelimit | Sets the maximum amount of time, in seconds, to spend on a search before the server returns results. |
| Search size limit | --searchrecordslimit | Sets the maximum number of records to return in a search. |
| User search fields | --usersearch | Sets the fields in a user entry that can be used as a search string. Any attribute listed has an index kept for that attribute, so setting too many attributes could affect server performance. |
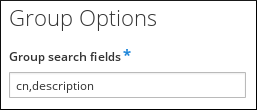
| Group search fields | --groupsearch | Sets the fields in a group entry that can be used as a search string. |
| Certificate subject base | Sets the base DN to use when creating subject DNs for client certificates. This is configured when the server is set up. | |
| Default user object classes | --userobjectclasses | Defines an object class that is used to create IdM user accounts. This can be invoked multiple times. The complete list of object classes must be given because the list is overwritten when the command is run. |
| Default group object classes | --groupobjectclasses | Defines an object class that is used to create IdM group accounts. This can be invoked multiple times. The complete list of object classes must be given because the list is overwritten when the command is run. |
| Password expiration notification | --pwdexpnotify | Sets how long, in days, before a password expires for the server to send a notification. |
| Password plug-in features | Sets the format of passwords that are allowed for users. |
15.4.1. Viewing Attributes from the Web UI
Copy linkLink copied to clipboard!
- Open the IPA Server tab.
- Select the Configuration subtab.
- The complete configuration entry is shown in three sections, one for all search limits, one for user templates, and one for group templates.
Figure 15.4. Setting Search Limits
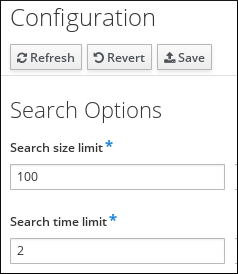
Figure 15.5. User Attributes

Figure 15.6. Group Attributes
15.4.2. Viewing Attributes from the Command Line
Copy linkLink copied to clipboard!
The config-show command shows the current configuration which applies to all new user accounts. By default, only the most common attributes are displayed; use the
--all option to show the complete configuration.
[bjensen@server ~]$ kinit admin
[bjensen@server ~]$ ipa config-show --all
dn: cn=ipaConfig,cn=etc,dc=example,dc=com
Maximum username length: 32
Home directory base: /home
Default shell: /bin/sh
Default users group: ipausers
Default e-mail domain: example.com
Search time limit: 2
Search size limit: 100
User search fields: uid,givenname,sn,telephonenumber,ou,title
Group search fields: cn,description
Enable migration mode: FALSE
Certificate Subject base: O=EXAMPLE.COM
Default group objectclasses: top, groupofnames, nestedgroup, ipausergroup, ipaobject
Default user objectclasses: top, person, organizationalperson, inetorgperson, inetuser, posixaccount, krbprincipalaux, krbticketpolicyaux, ipaobject, ipasshuser
Password Expiration Notification (days): 4
Password plugin features: AllowNThash
SELinux user map order: guest_u:s0$xguest_u:s0$user_u:s0$staff_u:s0-s0:c0.c1023$unconfined_u:s0-s0:c0.c1023
Default SELinux user: unconfined_u:s0-s0:c0.c1023
Default PAC types: MS-PAC, nfs:NONE
cn: ipaConfig
objectclass: nsContainer, top, ipaGuiConfig, ipaConfigObject