21.6. NFS Server Configuration
There are three ways to configure an NFS server under Red Hat Enterprise Linux: using the NFS Server Configuration Tool (
system-config-nfs), manually editing its configuration file (/etc/exports), or using the /usr/sbin/exportfs command.
To use the NFS Server Configuration Tool, you must be running X Windows, have root privileges, and have the system-config-nfs RPM package installed. To start the application, click on > > > . You can also type the command
system-config-nfs in a terminal. The NFS Server Configuration tool window is illustrated below.

Figure 21.1. NFS Server Configuration Tool
Based on certain firewall settings, you may need to configure the NFS daemon processes to use specific networking ports. The NFS server settings allows you to specify the ports for each process instead of using the random ports assigned by the portmapper. You can set the NFS Server settings by clicking on the button. The figure below illustrates the NFS Server Settings window.

Figure 21.2. NFS Server Settings
21.6.1. Exporting or Sharing NFS File Systems
Copy linkLink copied to clipboard!
Sharing or serving files from an NFS server is known as exporting the directories. The NFS Server Configuration Tool can be used to configure a system as an NFS server.
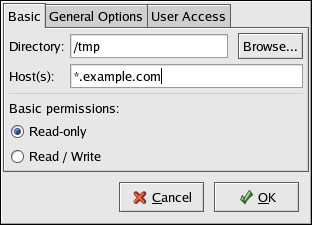
To add an NFS share, click the button. The dialog box shown in Figure 21.3, “Add Share” appears.
The Basic tab requires the following information:
- Directory — Specify the directory to share, such as
/tmp. - Host(s) — Specify the host(s) with which to share the directory. Refer to Section 21.6.4, “Hostname Formats” for an explanation of possible formats.
- Basic permissions — Specify whether the directory should have read-only or read/write permissions.
The General Options tab allows the following options to be configured:

Figure 21.4. NFS General Options
- Allow connections from port 1024 and higher — Services started on port numbers less than 1024 must be started as root. Select this option to allow the NFS service to be started by a user other than root. This option corresponds to
insecure. - Allow insecure file locking — Do not require a lock request. This option corresponds to
insecure_locks. - Disable subtree checking — If a subdirectory of a file system is exported, but the entire file system is not exported, the server checks to see if the requested file is in the subdirectory exported. This check is called subtree checking. Select this option to disable subtree checking. If the entire file system is exported, selecting to disable subtree checking can increase the transfer rate. This option corresponds to
no_subtree_check. - Sync write operations on request — Enabled by default, this option does not allow the server to reply to requests before the changes made by the request are written to the disk. This option corresponds to
sync. If this is not selected, theasyncoption is used.- Force sync of write operations immediately — Do not delay writing to disk. This option corresponds to
no_wdelay.
- Hide filesystems beneath turns the
nohideoption on or off. When thenohideoption is off, nested directories are revealed. The clients can therefore navigate through a filesystem from the parent without noticing any changes. - Export only if mounted sets the
mountpointoption which allows a directory to be exported only if it has been mounted. - Optional Mount Point specifies the path to an optional mount point. Click on the to navigate to the preferred mount point or type the path if known.
- Set explicit Filesystem ID: sets the
fsid=Xoption. This is mainly used in a clustered setup. Using a consistent filesystem ID in all clusters avoids having stale NFS filehandles.
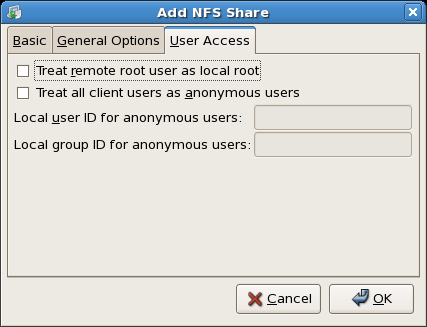
Figure 21.5. NFS User Access
The User Access tab allows the following options to be configured:
- Treat remote root user as local root — By default, the user and group IDs of the root user are both 0. Root squashing maps the user ID 0 and the group ID 0 to the user and group IDs of anonymous so that root on the client does not have root privileges on the NFS server. If this option is selected, root is not mapped to anonymous, and root on a client has root privileges to exported directories. Selecting this option can greatly decrease the security of the system. Do not select it unless it is absolutely necessary. This option corresponds to
no_root_squash. - Treat all client users as anonymous users — If this option is selected, all user and group IDs are mapped to the anonymous user. This option corresponds to
all_squash.- Specify local user ID for anonymous users — If Treat all client users as anonymous users is selected, this option lets you specify a user ID for the anonymous user. This option corresponds to
anonuid. - Specify local group ID for anonymous users — If Treat all client users as anonymous users is selected, this option lets you specify a group ID for the anonymous user. This option corresponds to
anongid.
To edit an existing NFS share, select the share from the list, and click the button. To delete an existing NFS share, select the share from the list, and click the button.
After clicking to add, edit, or delete an NFS share from the list, the changes take place immediately — the server daemon is restarted and the old configuration file is saved as
/etc/exports.bak. The new configuration is written to /etc/exports.
The NFS Server Configuration Tool reads and writes directly to the
/etc/exports configuration file. Thus, the file can be modified manually after using the tool, and the tool can be used after modifying the file manually (provided the file was modified with correct syntax).
The next this section discusses manually editing
/etc/exports and using the /usr/sbin/exportfs command to export NFS file systems.