46.2.2. Using the Kernel Dump Configuration Utility
To start the Kernel Dump Configuration utility, select
system-config-kdump at a shell prompt. Unless you are already authenticated, you will be prompted to enter the root password.
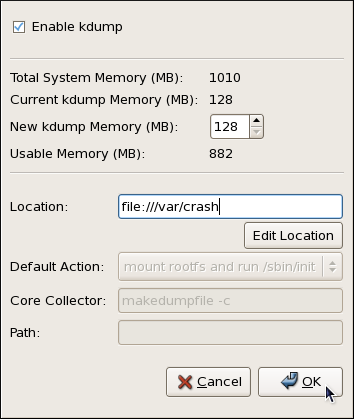
Figure 46.2. The Kernel Dump Configuration utility
The utility allows you to configure
kdump as well as to enable or disable starting the service at boot time. When you are done, click to save the changes. The system reboot will be requested.
Important
Unless the system has enough memory, the Kernel Dump Configuration utility will not start and you will be presented with an error message. For information on minimum memory requirements, refer to the Red Hat Enterprise Linux comparison chart. When the
kdump crash recovery is enabled, the minimum memory requirements increase by the amount of memory reserved for it. This value is determined by the user and on x86, AMD64, and Intel 64 architectures, it defaults to 128 MB plus 64 MB for each TB of physical memory (that is, a total of 192 MB for a system with 1 TB of physical memory).
46.2.2.1. Enabling the Service
Copy linkLink copied to clipboard!
To start the
kdump daemon at boot time, select the Enable kdump checkbox. This will enable the service for runlevels 2, 3, 4, and 5, and start it for the current session. Similarly, clearing the checkbox will disable it for all runlevels and stop the service immediately.